Novel Defense Strategy Against Zero-Dynamics Attack in Multi-Agent Systems
This paper considers the defense strategy of strategic topology switching for the second-order multi-agent system under zero-dynamics attack (ZDA) whose attack-starting time is allowed to be not the initial time. We first study the detectability of Z…
Authors: Yanbing Mao, Emrah Akyol, Ziang Zhang
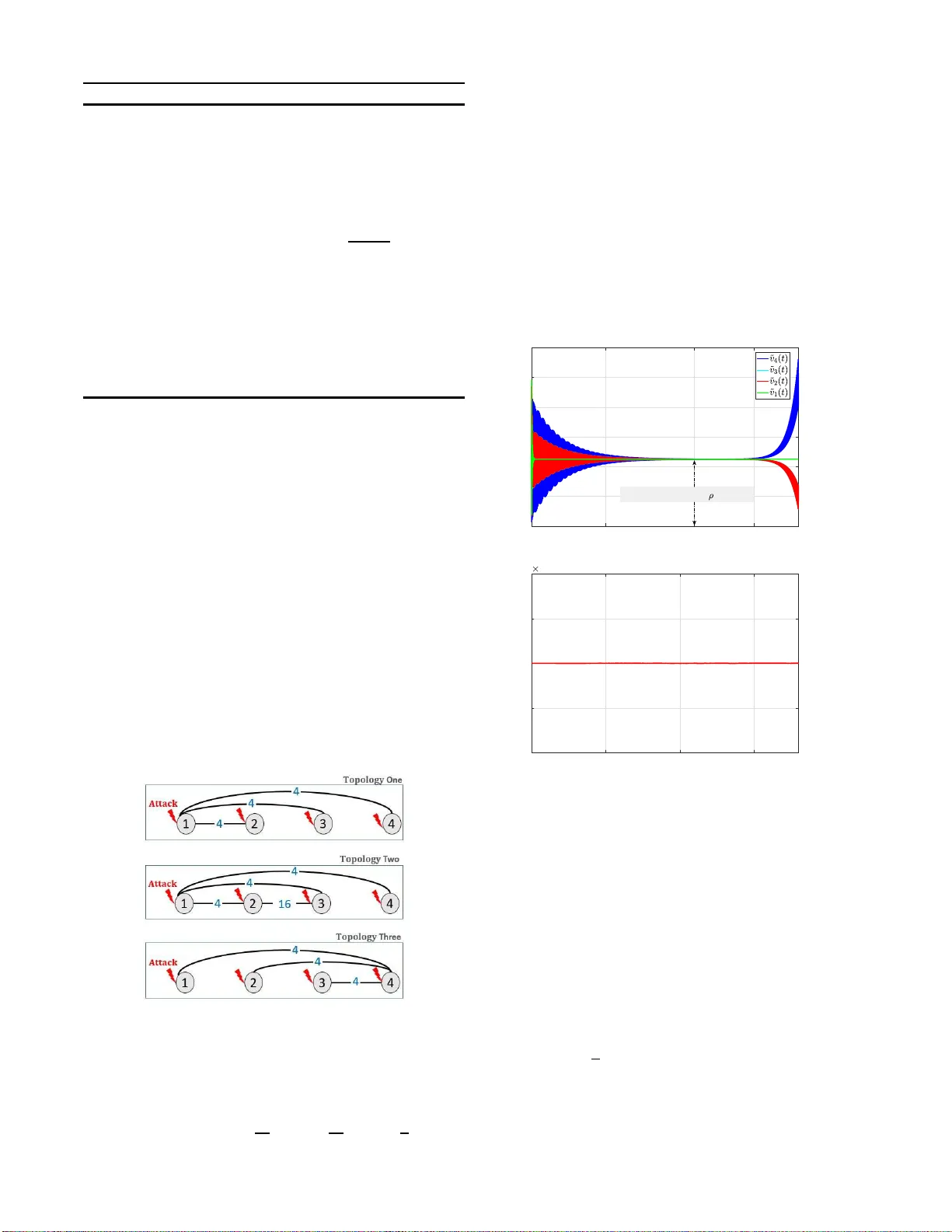
Nov el Defense Strategy Against Zer o-Dynamics Attack in Multi-Agent Systems Y anbing Mao, Emrah Akyol, and Ziang Zha n g Abstract — This paper considers the defense str ategy of strate- gic topology switching for the second-order multi-agent system under zer o-dynamics attack (ZD A) whose attack-starting time is allowed to be not the i nitial time. W e first study the detectability of ZD A, which is a sufficient and necessar y condition of switching topologies in detecting the attack. Based on th e detectability , a Luenberger observ er under switching topology is proposed to detect the stealthy attack. T he primary advantages of the attack-detection algorithm are tw ofold: (i) in d etectin g ZD A, the algorithm allows the defender (system o perator) to ha ve no knowledge of the attack-starting time and the misbehaving agents (i.e., agents under attack); (i i ) in tracking system i n t h e absence of attacks, Luenberger observ er has no constraint on the m agnitudes of observer gains and th e number of observ ed outputs, i.e., only one agent’ s ob served output is sufficient. Simulations are pro vid ed to verify the effectiv eness of the strategic topolog y-switching algorithm. I . I N T RO D U C T I O N Coordinatio n of multi-agen t systems with the first-o rder dynamics is a well-studied theoretical p r oblem with m any practical application s. Howe ver, curren t and em erging sys- tems, such as vehicle [1], spa c e craft [2], robot [ 3] and electrical p ower networks [4 ], rely on the second-o rder dynamics. A secon d-orde r multi-agen t system consists of a populatio n of n agents wh o se dynam ics are governed by the following equations: ˙ x i ( t ) = v i ( t ) , (1a) ˙ v i ( t ) = u i ( t ) , i = 1 , . . . , n (1b) where x i ( t ) ∈ R is the p o sition, v i ( t ) ∈ R is the ve- locity , and u i ( t ) ∈ R is the lo cal contro l in put. Recently , significant efforts have been d ev o ted to the co o rdination control o f the second-o rder multi-agent system (1), see e.g., flocking [5], velocity synchr o nization and regulatio n of relative distances [6], decentralized for m ation control of spacecrafts [7], and distributed con tinuous-tim e optimiza- tion [8], etc. The n umerou s real networked systems that can be represente d by (1) and th e broad app lications of its coordin ation contro l is the main mo tivation of this paper considerin g the mod el (1). For coordin ation con trol, th is paper con siders mor e repr esentativ e average consensu s. Security concerns r egarding networked cyber-physical sys- tems pose an existential threat to their wide-d e p loyment, see e.g., Stux n et malware attack and Mar oochy Shire Council Y . Mao, E. Ak yol and Z. Zhang are wit h the De- partment of Electri cal and Compute r Engineerin g, Bing- hamton Uni versit y–SUNY , Binghamto n, NY , 13902 USA { ymao3,eakyol,zh angzia } @binghamto n.edu. Sew a ge con tr ol incident [9]. The “networked” aspect exac- erbates the dif ficulty of d etecting and p rev enting aforemen- tioned a ttacks since cen tr alized measureme n t (sensing) an d control are no t f easible for such large- scale systems [1 0], and hence requires the de velo p ment of d ecentralized approaches, which are inheren tly pron e to attack s. While d ev eloping d e - fense strategies for ZDA have recently gained interest [10 ]– [14], the space of solutions is yet to be tho rough ly explo red. The most promine nt fe atures o f prior work are that they constrain the co nnectivity of network topo logy and the number of th e misbehaving agents (re ferred to agents under attack) [10]–[ 1 3] or requir e the knowledge o f the numb er of misbehaving agen ts and the attack-starting time at the defend e r (system ope rator) side for attack detection [10 ]– [12], [1 4]–[16 ]. The main objective of this work is to remove such co nstraints and unrealistic assumptio ns by utilizing a new appro ach fo r attack detection : inten tional topology switching. Recent experiment of stealthy false-data in jection attacks on networked con trol system [ 15] showed the changes in the system dynam ic s cou ld b e used to de tect stealthy attack. T o have c hanges in the system dynamics to detec t ZDA, T eixeira et al. [15] pro posed a m e thod of mo difying output m atrix throug h ad ding and removin g obser ved measu rements, or modify in g input matrix th rough addin g and removin g actua- tors or p erturbing the contro l input matrix. In mo re realistic situation where the attack ca n exactly infer sy stem dynamics and attack-startin g is designed to b e not the initial time and the def e nder (system opera to r) has no knowledge of the attac k -starting time , to detect ZDA the system dy namics must ha ve dynamic chang es, i.e. , some parameters of system dynamics ch a nges infin itely over infinite ti me. For the dyn amical networks, recent stud ies hav e h ig h- lighted th e imp ortant r ole play e d by the network top ology , and in recent se veral years, acti vely/strategically topology switching has re c ei ved significantly attention in the con trol theory , network science and g raph theory literatu res, see e.g., Ciftcioglu et al. [1 7] studied dynamic topo logy d esign in the adversary e nvironmen t where the network designer continually an d strategically chan ge network topolo gy to a denser state, while the adversary attemp ts to thwart the defense strategy simultane ously . Mo r eover , driv en by recent developments in mo bile co mputing , wireless co mmunica tio n, sensing, etc., it is mor e feasible to set communic a tio n to pol- ogy as a control variable [1 8], [19]. These m otiv ate us to consider the m ethod of top ology switching such that th e multi-agen t s ystem can have changes in its system dynamics to detect Z D A. The strate gy on switching times propo sed in [20] will be the building block of our defense strategy , wh ich answered the qu estion: when the topology of network should switch such that the occurring dynamic changes in system dynamics do not undermine the agent’ s ability of r eaching consensus in the absence o f atta cks . Based on the work in [20 ], this paper f ocuses on the strategy on switching topolog ie s that addresses the problem o f switching to what top ologies to detect ZDA . The contribution of this paper is threefold, which can b e summarized as follows. • The detectability of ZD A is obtained , which is a suffi- cient and necessary con dition of s witching topologies. • A sufficient and necessary cond itio n of switching topolog ies fo r Luen berger obser ver is deriv ed, which has n o constraint on the numbe r o f ob served outputs in tracking re al multi-ag ent system. • Throug h em ploying Luen berger o bserver , a stra tegic topolog y-switching algor ithm for attack detection is propo sed. Th e advantages o f the alg orithm are: i) in detecting ZD A, it allo ws the defender (system op erator) to h ave no knowledge of misbeh aving agen ts and the attack-starting time; ii) in trac king real sy stem s in the absence o f attac k s, it h as no co n straint on the mag ni- tudes of ob server gains an d th e n u mber o f o bserved outputs. I I . P R E L I M I N A R I E S A. Notation R n and R m × n denote the set of n -dimensional real vectors and the set of m × n -dimensional rea l matrices, respectively . Let C denote the set of com p lex number s. N re presents the set of the natural nu mbers and N 0 = N ∪ { 0 } . Let 1 n × n and 0 n × n be the n × n -dimensional identity matrix and zer o m atrix, resp ectiv ely . 1 n ∈ R n and 0 n ∈ R n denote the vector with all ones and the vector with all zeros, respectively . For a matrix M ∈ R n × n , λ i ( M ) denotes its i th eigenv alu e. The super script ‘ ⊤ ’ stands fo r matrix transpo se. ker ( Q ) , { y : Qy = 0 n , Q ∈ R n × n } . Also, |·| deno tes the cardinality of a set, o r the mod ulus of a numb er . V \ K describes the complement set of K with resp ect to V . Q denotes t he set of r ational numb ers. The interaction among n agen ts is m odeled by an und i- rected graph G , ( V , E ) , wh ere V , { 1 , 2 , . . . , n } is the set of vertices that rep resents n agents and E ⊆ V × V is th e set o f edge s o f th e gr a p h G . Th e weigh ted adjacency matrix A = [ a ij ] ∈ R n × n of th e gr aph G is defined as a ij = a j i > 0 if ( i, j ) ∈ E , and a ij = a j i = 0 otherwise. Assume that there are no self-loop s, i.e., for a ny i ∈ V , a ii = 0 . The Laplacian matrix of graph G is d efined as L , [ l ij ] ∈ R n × n , where l ii , n P j =1 a ij , and l ij , − a ij for i 6 = j . B. Attack Model As a class of stealthy attacks, ZD A is har d to de te c t, iden- tify , and then m itigate from a con trol theory p erspective [21]– [23]. Befo re reviewing its attack policy , let us first consider the follo wing system: ˙ z ( t ) = Az ( t ) , (2a) y ( t ) = C z ( t ) , (2b) where z ( t ) ∈ R ¯ n and y ( t ) ∈ R ¯ m denote sy stem state and observed o utput, respectively; A ∈ R ¯ n × ¯ n , C ∈ R ¯ m × ¯ n . Its correspo n ding version under attack is d escribed by ˙ ˜ z ( t ) = A ˜ z ( t ) + B g ( t ) , (3a) ˜ y ( t ) = C ˜ z ( t ) + D g ( t ) , (3b) where g ( t ) ∈ R ¯ o is attack signal, B ∈ R ¯ n × ¯ o and D ∈ R ¯ m × ¯ o . The policy of ZD A with intr o duction of attack-startin g time is presented in the following definition, which is differ - ent from the attack policie s studied in [10]– [12], [14]–[ 16], whose attack -starting times are the initial time. Definition 1 : [24] Th e attack signal g ( t ) = g e η ( t − ρ ) , t ∈ [ ρ, ∞ ) 0 ¯ o , t ∈ [0 , ρ ) (4) in system (3) is a zer o -dyna m ic s a ttack , if 0 ¯ n 6 = ˜ z (0) − z (0) ∈ R ¯ n , 0 ¯ o 6 = g ( ρ ) ∈ R ¯ o , ρ ≥ 0 and η ∈ C satisfy ˜ z (0) − z (0) ∈ ker ( O ) if ρ > 0 (5a) e Aρ ( ˜ z (0) − z (0 )) − g ( ρ ) ∈ k er η 1 ¯ n × ¯ n − A B − C D , (5b) where O , h C ⊤ ( C A ) ⊤ . . . C A ¯ n − 1 ⊤ i ⊤ . (6) Moreover , the states and o bserved outpu ts of systems (3) and ( 2) satisfy y ( t ) = ˜ y ( t ) , f or all t ≥ 0 (7) ˜ z ( t ) = e At ˜ z ( 0) , t ∈ [0 , ρ ] z ( t ) + ( ˜ z ( ρ ) − z ( ρ )) e η ( t − ρ ) , t ∈ ( ρ, ∞ ) . (8) Remark 1: Com p ared with other stealthy attacks, see e. g ., replay a ttac k [ 2 5] and covert attack [ 26], ZDA has m o re explicit attack o bjectives . The state so lu tion (8) shows that throug h ch oosing the p arameter η and also the attack-starting time ρ , the attac ker can achieve various o bjectiv es, see e.g. , • ρ = ∞ : alterin g the steady-state value while not affecting system stability ; • ρ < ∞ , Re ( η ) > 0 : m aking system unstable; • ρ < ∞ , Re ( η ) = 0 , Im ( η ) 6 = 0 : causing oscillatory behavior . The o u tput (7) indicates the undetectable/stealthy proper ty . C. Contr ol Objective W e recall the definition of secon d-orde r consensu s to revie w the control objecti ve. Definition 2 : [27 ] The second -order consensu s in the multi-agen t system (1) is achieved if for any initial condition: lim t →∞ | x i ( t ) − x j ( t ) | = 0 , (9a) lim t →∞ | v i ( t ) − v j ( t ) | = 0 , ∀ i, j = 1 , . . . , n. (9b) W e recall our proposed simplified co ntrol pr otocol that works for co nsensus in the environment of dynamic topo logy . u i ( t ) = X j ∈ V a σ ( t ) ij ( x j ( t ) − x i ( t )) , i ∈ V (10) where σ ( t ) : [ t 0 , ∞ ) → S , { 1 , . . . , s } , is the switch in g signal of the interaction topolo gy of the com munication net- work; a σ ( t ) ij is the entry of the weigh ted ad jacency matrix that describes th e activ ated top ology of communication graph . D. Strate gy on Switching T imes The following time-dep e ndent to pology switchin g is the building block of our d efense strategy . Lemma 1: [ 2 0] Consider the second -order multi-agen t system ( 1) with control pro tocol (10). F or the gi ven topo logy set S that satisfies ∀ r ∈ S : s λ i ( L r ) λ j ( L r ) ∈ Q , f o r ∀ i, j = 2 , . . . , | V | (11) and the scalars 1 > β > 0 , α > 0 and κ ∈ N , if the dwell times τ r , r ∈ S , satisfy τ r = b τ max + m T r 2 , m ∈ N (12) where 0 < b τ max < − l n β α , 0 < b τ max + m T r 2 − β − 1 κ − 1 κ α − ξ , ξ < α , ξ = max r ∈ S ,i =1 ,...,n { 1 − λ i ( L r ) , − 1 + λ i ( L r ) } an d T r = lcm 2 π √ λ i ( L r ) ; i = 2 , ..., n , the n the asymp totic second - order co nsensus (9) is achieved. Remark 2: For the control p rotocol, with und irected co m- munication to pology , that replies on both relativ e po sition s and velocities measur ements, its o bvious advantage is that there is no constrain t on the magnitudes o f coupling weights [1]. The switching schem e pr oposed in Le mma 1 almost maintains this ad vantage since it only req uires th e rations of no n-zero Laplacian eigen values to be rational n u mbers. I I I . S Y S T E M D E S C R I P T I O N For simplicity , we let the increa singly ordered set M , { 1 , 2 , . . . } ⊆ V d enote the set of observed outpu ts. W e usually refer to an agen t under attack as a misbehaving agent [12] . W e let K ⊆ V denote th e set o f misbehaving agents. Under time-d ependen t topo logy switching, the multi-agent system in (1) with th e control inp ut (10) in the pr esence of attack and the observed ou tp uts of positions can be written as ˙ ˜ x i ( t ) = ˜ v i ( t ) (13a) ˙ ˜ v i ( t ) = X i ∈ V a σ ( t ) ij ( ˜ x j ( t ) − ˜ x i ( t )) + ˜ g i ( t ) , i ∈ K 0 , i ∈ V \ K (13b) ˜ y i ( t ) = ˜ x i ( t ) .i ∈ M (13c) The system in (13) can b e equiv alently rewritten in the form of a switched system under attack: ˙ ˜ z ( t ) = A σ ( t ) ˜ z ( t ) + ˜ g ( t ) (14a) ˜ y ( t ) = C ˜ z ( t ) , (14b) where ˜ z ( t ) , ˜ x 1 ( t ) . . . ˜ x | V | ( t ) ˜ v 1 ( t ) . . . ˜ v | V | ( t ) ⊤ , ( 15a) A σ ( t ) , 0 | V |×| V | 1 | V |×| V | −L σ ( t ) 0 | V |×| V | , (15b) C , diag { 1 , . . . , 1 } 0 | M |× ( | V |−| M | ) , (15c) ˜ g ( t ) , h 0 ⊤ | V | ¯ g ⊤ ( t ) i ⊤ , (15d) [ ¯ g ( t )] i , ˜ g i ( t ) , i ∈ K 0 , i ∈ V \ K . (15e) In add ition, we consider the system (14) in th e ab sence of attacks, which is given by ˙ z ( t ) = A σ ( t ) z ( t ) , (16a) y ( t ) = C z ( t ) . (16b) T o end th is section, we make th e fo llowing assumptions on th e attacker and the defender (system operator) . Assumption 1: The a ttacker 1) knows the cur r ently activ ated topolo gy and its dwell time at switching time; 2) has th e memo ry of th e p ast switchin g s equen ces. Assumption 2: The d efender 1) designs th e switchin g sequ ences inclu ding switching times an d top ologies; 2) has n o kn owledge of t he attack-starting time; 3) has n o kn owledge of the numb er of misbehaving agents. I V . D E T E C TA B I L I T Y O F Z E RO - D Y N A M I C S A T TAC K This sectio n f ocuses on the detectability o f Z D A, wh ic h will answer th e question : what top ologies of multi-agent system (13) to strate gica lly switch to such th at the attack policy ( 5) is not feasible? T o better illu strate the strategy o n switching topo lo gies, we in troduce the definition of components in a g r aph. Definition 3 (Componen ts o f Graph [28 ]): Th e compon e nts of a graph G are its ma ximal conn ected subgrap h s. A comp onent is said to be trivial if it has no edges; o th erwise, it is a n ontrivial co mponen t . Remark 3: As illustrated by Difference Graph in Fig. 1, different comp o nents do ha ve any co mmon v ertex, otherwise they are in the same compon ent for m ed v ia that co mmon vertex. Definition 4 : Th e difference grap h G r s diff = ( V r s diff , E r s diff ) of two gra phs G r and G s is gen erated as V r s diff = V r ∪ V s ( i, j ) ∈ E r s diff , if a r ij − a s ij 6 = 0 Fig. 1. Components of differ ence graph (the weights of communica tions links a re uniformly set as ones). where V r and a r ij are the set of agents an d the en try of weighted adjac ency matrix o f the graph G r , r espectiv ely . W e define the u nion difference graph for switching differ- ence g r aphs: G diff , [ r,s ∈ S V r s diff , [ r,s ∈ S E r s diff . (17) W e use C i (G diff ) to den ote the set o f agents in the i th compon ent o f un io n difference graph G diff . Obviously , V = C 1 S C 2 S . . . S C d , a n d C p T C q = ∅ if p 6 = q , where d is the number of the co mponen t of difference graph G diff . The dete c tability of ZDA un der strategy on switching topolog ies a r e presen ted in the following theorem . Theor em 1: [24] Con sider the multi-ag ent system (14). Under time-depend e n t topolog y switching, the ZD A can be detected by defen d er without knowledge of misbehaving agents an d the attack -starting time, if and only if at least one ag ent in each comp onent of u nion dif f erence graph h a s observed outp ut, i.e., C i (G diff ) ∩ M 6 = ∅ , ∀ i = 1 , . . . d . (18) V . A T TAC K D E T E C T I O N A L G O R I T H M Based o n the obtain ed detectability of ZD A, this sectio n focus o n its detection algor ith m. A. Luenberg er Observer under Switching T op ology W e now present a Lu enberger ob server f or th e system (13): ˙ x i ( t ) = v i ( t ) (19a) ˙ v i ( t ) = X i ∈ V a σ ( t ) ij ( x j ( t ) − x i ( t )) − ψ i r i ( t ) + θ i ˙ r i ( t ) , i ∈ M 0 , i ∈ V \ M (19b) r i ( t ) = x i ( t ) − ˘ y i ( t ) , i ∈ M (19c) where ˜ y i ( t ) is the observed output in system (13), r i ( t ) is the attack- detection signal, ψ i and θ i are the o bserver gains designed b y the def ender (system operator). The strategy (16) in Th eorem 1 implies that if the union difference grap h is connected, i.e., the union difference graph has only one comp onent, using only one agent’ s ob served output is sufficient to detect ZD A. The f ollowing resu lt re- garding th e st ability of sy stem (19) will answer the q uestion: whether o nly o ne a gent’ s observed output is sufficient for the observer to asympto tica lly track th e system (14) in the a b sent of attac k ? Theor em 2: [24] Consider the fo llowing matrix: A s , 0 n × n 1 n × n −L s − Φ − Θ , (20) where Φ , diag { ψ 1 , . . . , ψ | M | , 0 , . . . , 0 } , (21a) Θ , d iag { θ 1 , . . . , θ | M | , 0 , . . . , 0 } . (21b) Giv en tha t L s is the Laplacian matrix of a connected graph and th e gain matrices Φ an d Θ satisfy 0 n × n 6 = Φ ≥ 0 , (22a) 0 n × n 6 = Θ ≥ 0 , (22b) then A s is Hurwitz for any | M | ≥ 1 , if and only if L s has distinct eigen values. B. Strate gic S witching T op ology F or Detection The strategic top ology-switch ing alg o rithm is de scribed by Algorithm 1 . Theor em 3: [24] Consider the multi-ag ent system (14) and th e observer (19), where the observer gain matrices Φ and Θ satisfy (22a) and ( 22b), and the top ology-switch ing signal ˜ σ ( t k ) of the observer (19) an d the system ( 14) are generated b y Algo rithm 1. i) W itho ut knowledge of th e misbehaving agents and the attack-starting time, the observer (1 9) is able to detect ZDA in system (14), i.e., r ( t ) ≡ 0 | M | does not holds, if and o nly if the set o f observed ou tputs and switch in g top o logies satisfy (18). ii) In the absence o f attack s, without c onstraint on the magnitudes of observer gains, the observer ( 19) asymptotically tr a c k the real system (13). iii) In the absence of attacks, the agents in system (14) achieve th e asympto tic second- order consensus. Algorithm 1: Strategic T opolog y-Switching Algo rithm Input: In itial in d ex k = 0 , initial time t k = 0 , an ordered topology set S that satisfies ∃ s ∈ S : L s has distinct eig e n values , (23) dwell times τ s , s ∈ S , gener ated by ( 12) that satisfy X s ∈ S ν s µ P ( A s ) < 0 , ν s = τ s P r ∈ S τ r . (24) 1 Run the multi-agent system (14) and the observer (19); 2 Switch topology of system (13) and its observer (19) at time t k + τ ˜ σ ( t k ) : ˜ σ ( t k ) ← S (mo d( k + 1 , | S | ) + 1) ; 3 Update topology-switching time: t k ← t k + τ ˜ σ ( t k ) ; 4 Update index: k ← k + 1 ; 5 Go to Step 2. V I . S I M U L AT I O N W e consider a system with n = 4 ag ents. The initial position and velocity condition s a re chosen rando mly a s x (0) = v (0) = [1 , 2 , 3 , 4] ⊤ . T he con sidered network top olo- gies with their couplin g weights are giv en in Fig. 2, which shows that all of the four agents are un der attack , i.e., K = { 1 , 2 , 3 , 4 } . W e let ag e nt 1 provide obser ved outpu t, i.e., M = { 1 } . W e set the observer gains significan tly s mall as Φ = Θ = diag { 10 − 6 , 0 , 0 , 0 } . W e note that in the w orking situation illustrated by Fig. 2 , the existing results [10] –[14] for th e mu lti- agent systems und e r fixed topo logy fail to detect ZD A. T his is mainly due to the misb e having-agents set | K | = 4 ; the connectivities of T opolo gies One, T wo and Three are as the same as 1 ; a n d the outpu t set | M | = 1 . All these violate the cond itions on th e con nectivity o f the commun ication network, the size of th e misbe having-agent set, an d the size of the output s et. Fig. 2. W orking si tuation. First, we consider the topolog y set S = { 1 , 2 } , and set the topolo gy switching sequence as 1 → 2 → 1 → 2 → . . . , period ically . W e verify from Fig. 2 that the topology set S = { 1 , 2 } satisfies (11) and ( 24). By L emma 1, we select the dwell times τ 1 = τ 2 = T 1 2 + 0 . 2 = T 2 2 + 0 . 2 = π 2 + 0 . 2 . It can be verified fr om T opolo gies One and T wo in Fig. 2 that their gen erated difference gr aph is discon nected. T hus, the set S = { 1 , 2 } do es no t satisfy (18) in Th eorem 1. Therefor e, the attacker can easily design a ZD A such th at Algorith m 1 fails to detect it. Following the policy (5), one of the stealthy attack strategies is designed as: • η = 0 . 0161 ; • modify the data of initial co n dition sent to observer (1 9) as b x (0) = [1 , 1 , 3 , 5] ⊤ and b v ( 0) = [1 , 1 , 4 , 4] ⊤ ; • choose attack- starting time ρ = 1097 . 4 ; • introduc e ZDA signal to system at ρ : g ( t ) = 1 0 − 3 0 , 7 . 3 e η ( t − ρ ) , 7 . 3 e η ( t − ρ ) , − 1 4 . 6 e η ( t − ρ ) ⊤ . 0 500 1097.4 1500 Time -2 0 2 4 6 8 10 (a) Attack-Starting Time = 1097.4 0 500 1000 1500 Time -1 -0.5 0 0.5 1 Attack-Detection Signal r(t) 10 -9 (b) Fig. 3. Sta tes ˜ v ( t ) : multi-agent system under attack is unstable; attac k- detec tion signal r ( t ) : th e atta cker keep st ealthy o ver ti me. The traje c tories of detection sign al r ( t ) designed in (19), and the velocities are shown in Fig. 3 , which illustrates that the attacker’ s g oal of making the system unstable witho ut being detected is ach iev ed under the topolo gy set S = { 1 , 2 } . T o detect the design ed stealthy attack, we now incorp orate T opology Three in Fig. 2 in to top ology set, i.e., S = { 1 , 2 , 3 } . W e le t th e topolog y switching sequ ence to be 1 → 2 → 3 → 1 → 2 → 3 → . . . , periodically . W e verify that the topo logy set S = { 1 , 2 , 3 } satisfies (11) and (24). Using Lem ma 1 , the dwell times ar e selected as τ 1 = τ 2 = τ 3 = π 2 +0 . 2 . It can be verified fro m Fig. 2 that the difference graph generated by T opologies One and Three, or T opologies T wo and Three is connected. Thus, by proper ty i) in T heorem 3, we c onclude that u sing only one agen t’ s observed o utput, th e strate gic topology-switching alg orithm– 0 200 400 600 800 1097.4 1400 Time -0.4 -0.2 0 0.2 0.4 Attack-Detection Signal r(t) Detect Mixed Stealthy Attacks Attack that modifies initial condition is detected. Attack-starting time of zero-dynamics attack is = 1097.4. Zero-dynamics attack is detected. Fig. 4. Attack- detecti on signal r ( t ) : using only one agent’ s observed outputs, t he designed ZD A is d etecte d. Algorithm 1, is able to detect the designed ZDA u nder the topolog y set S = { 1 , 2 , 3 } . The trajectory o f th e attack- detection signa l r ( t ) in Fig. 4 illustrates that with all of the agents being misbehaving, using o nly one agent’ s observed outputs, Alg orithm 1 succeeds in d etecting the mixed stealthy attacks. V I I . C O N C L U S I O N In this paper , we propose a s trategy on switching topo lo- gies that add resses th e problem : what topo logy to switch to, such that the ZD A can b e detected . Based on the strategy , a defense strategy is der ived. The the oretical results obtained in this pa p er imply a rather in teresting re su lt: for the dwell time of switching top o logies, there exist a tradeoff b etween th e switching cost and the du ration o f attack s goin g u ndetected, and the conver gence speed to consensus. Analyzing the trad e- off problems in the lights of game theo ry and multi-objective optimization c o nstitutes a part of o ur fu ture research . V I I I . A C K N O W L E D G M E N T This work has been suppo r ted in part by Bingham ton University–SUNY , Center for Collective Dynamics of Com- plex Systems ORC grant. R E F E R E N C E S [1] W . Ren a nd E. Atkins, “ Distribu ted multi-v ehicle coordinated contro l via l ocal informa tion excha nge, ” Internation al Journal of Robust and Nonline ar Contr ol , vol . 17, no . 10-11, p p. 1002–1 033, 2007. [2] A. Abdessameud and A. T ayebi, “ Attitude syn chroniza tion of a group of spacecr aft without veloc ity measurements, ” IEEE T ransactions on Automat ic Contr ol , vol. 54, no. 11, pp. 2642–2648, 2009. [3] S.-J. Chung and J.-J. E . Slotine , “Coopera ti ve robot control and concurre nt synchroniz ation of lagrang ian systems, ” IEEE T ransactions on Roboti cs , vol. 25, no. 3, pp. 686–700 , 2009. [4] B. B. Johnson, S. V . Dhople, A. O. Hamadeh, and P . T . Krein, “Synchroni zation of nonline ar oscillators in an lti elect rical powe r netw ork, ” IEE E T ransactions on Circui ts and Systems I: Re gular P apers , vol. 61, no. 3, pp. 834–844, 2014. [5] R. Olfati -Saber , “Flocking for multi-agent dynamic systems: Algo- rithms an d theory , ” IEEE T ransacti ons on automat ic contr ol , vol. 51, no. 3, pp. 401–420, 200 6. [6] H. G. T anner , A. Jadbabaie, and G. J. Pa ppas, “ Flocking in fixed and switchin g networks, ” IEEE T ransact ions on Automat ic contr ol , vol. 52, no. 5, pp. 863–868, 200 7. [7] W . Ren a nd R. Be ard, “Decentrali zed scheme for spacecraft fo rma- tion flying via the virtual structure approac h, ” J ournal of Guidance , Contr ol, and Dynamics , vol. 27, n o. 1, pp. 73–82, 2004 . [8] S. Rahil i and W . Ren, “Distrib uted cont inuous-time con ve x opti- mizatio n with time-v arying cost functions, ” IEEE T ransactions on Automat ic Contr ol , vol. 62, no. 4, p p. 1590–1 605, 2017. [9] A. A. C ´ ardenas, S. Am in, and S. Sastry , “ Research c hallenge s for the security of control systems. ” in HotSec , 2008. [10] F . Pasqual etti, F . D ¨ orfler , and F . Bullo, “ Attac k detecti on and identi- fication in cyb er-physi cal systems, ” IEEE T ransactions on Automatic Contr ol , vol. 58, no. 11, pp. 2715–2729, 2013. [11] S. Sund aram and C. N . Hadjicosti s, “Distrib uted function cal culati on via linear iterati ve strategie s in the presence of malicio us agents, ” IE E E T ransactions on Automatic Contr ol , vol. 5 6, no. 7, pp. 1495–1508, 2011. [12] F . P asqualet ti, A. Bicchi, and F . Bul lo, “Consensus comput ation in unrelia ble networks: A system theore tic approa ch, ” IEEE T ransactions on Aut omatic Cont r ol , vol . 57, no . 1, pp. 90–104, 2012. [13] S. W eerakkody , X. Liu, and B. Sinopoli, “Robust structu ral analysis and design of di stribut ed control syste ms to prev ent zero dynamics attac ks, ” in 56th IE EE Confere nce on Decision and Contr ol , pp. 1356– 1361, 2017. [14] J. Chen, J. W ei, W . Chen, H. Sandber g, K. H. Johansson, and J. Chen, “Protec ting positi ve and second-orde r systems against undetectab le attac ks, ” IF A C-P apersOnLi ne , vol. 50, no. 1, pp. 8373–8378, 2017. [15] A. T eixei ra, I. S hames, H. Sandberg, and K. H. Johansson, “Rev ealing stealt hy at tacks in control syst ems, ” in 50th A llerton Confer ence on Communicat ion, Contr ol, and Comp uting , pp. 1 806–1813, 2012. [16] ——, “ A sec ure control frame work for resource-li mited adve rsaries, ” Automat ica , vol. 51, pp. 135– 148, 2015. [17] E. N. Ciftciogl u, S. Pal, K. S. Chan, D. H. Canse ver , A. Swami, A. K. Singh, and P . Ba su, “T opology design games and dynamics in adv ersarial en vironments, ” IEEE J ournal on Selected Ar eas in Communicat ions , vol. 35, no. 3, pp . 628–642 , 2017. [18] H. Hartenste in, K. P . Laberte aux et al. , “ A tutorial survey on vehicula r ad hoc ne tworks, ” IEEE Co mmunicatio ns magazin e , v ol. 46, no. 6, p. 164, 2008. [19] S. K. Mazumder , W ir eless networking based contr ol . Springer , 2011. [20] Y . Mao, E. Akyol , and Z. Z hang, “Second-orde r consensus for multi- agent systems by time-de pendent topology switchi ng, ” in 57th IEEE Confer ence on Decision an d Contr ol , pp. 6151– 6156, 2018. [21] M. Naghna eian, N. Hirzallah, and P . G. V oulgaris, “Dural rate control for s ecurit y in cybe r-physic al systems, ” in 54th IEEE Annual Confer - ence on Decision and Con tr ol , pp. 14 15–1420, 2015. [22] H. J afa rnejadsani , H. Lee, N. Hov akimyan, and P . V oulgaris, “ A multirat e adapti ve control for mimo systems with applicatio n to cyb er- physical security , ” in 57th IEEE Conferen ce on Decision and Contr ol , pp. 66 20–6625, 2018. [23] N. H. Hirzallah an d P . G. V oulgaris, “On th e computation of worst attac ks: a lp framew ork, ” in 2018 American Contr ol Confere nce , pp. 4527–4532, 2018. [24] Y . Mao, E. Akyol, and Z. Z hang, “Strategi c topology switch- ing for security-p art II: Detection & switc hing topologies, ” https:// arxiv .or g/abs/1711 .11181 . [25] Y . Mo and B. Sinopol i, “Secure control against replay atta cks, ” in 47th annual Allerton confere nce on communication, contr ol, and computin g , pp. 911–918, 2009 . [26] A. O. de S ´ a, L. F . R. da Costa Carmo, and R. C. Machado , “Cov ert attac ks in cyber -physical control systems, ” IEEE T ransactions on Industrial Inf ormatics , vol. 13, no. 4 , pp. 164 1–1651, 2017. [27] W . Y u, G. Chen, and M. Cao, “Some n ecessary and suf ficient condi- tions for s econd-o rder consensus in m ulti-a gent dynamical systems, ” Automat ica , vol. 46, no. 6, pp. 1089–1095 , 2010. [28] M. Ne wman, Network s: an intr oduction . Oxford uni versity press, 2010.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment