Privacy-Aware Cost-Effective Scheduling Considering Non-Schedulable Appliances in Smart Home
A Smart Home provides integrating and electronic information services to help residential users manage their energy usage and bill cost but also exposes users to significant privacy risks due to fine-grained information collected by smart meters. Tak…
Authors: Boyang Li, Jie Wu, Yiyu Shi
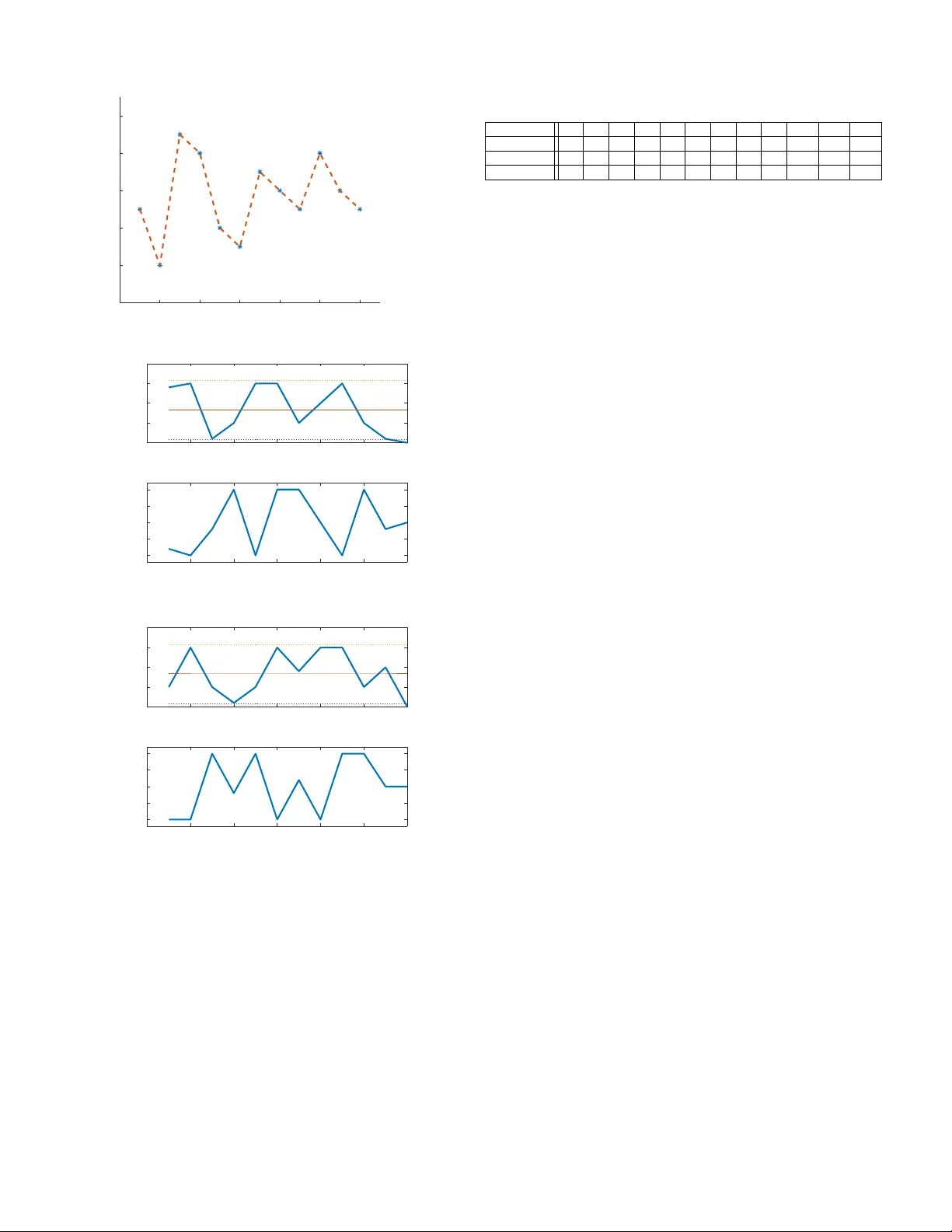
Pri v ac y-A ware Cost-Ef fecti v e Scheduling Considering Non-Schedulable Appliances in Smart Home Boyang Li, Student Member , IEEE, Jie W u, and Y iyu Shi, Senior Member , IEEE Abstract —A Smart home provides integrating and electronic information services to help r esidential users manage their energy usage and bill cost, but also exposes users to significant pri vacy risks due to fine-grained information collected by smart meters. T aking account of users’ priv acy concer ns, this paper f ocuses on cost-effective runtime scheduling designed for schedulable and non-schedulable appliances. T o alleviate the influence of oper - ation uncertainties introduced by non-schedulable appliances, we formulate the problem by minimizing the expected sum of electricity cost under the worst privacy situation. Inventing the iterative alternativ e algorithm, we effectively schedule the appliances and rechar geable battery in a cost-effective way while satisfying users’ privacy requirement. Experimental evaluation based on real-w orld data demonstrates the effectiveness of the proposed algorithm. Index T erms —Smart Homes, Non-schedulable scheduling. I . I N T RO D U C T I O N W ith the dev elopment of Internet of Things (IoT) [21] [20] [18] [19] [22], smart home, managed by intelligent devices [3] [4], have provided tangible benefits for customers to control and lower their electricity costs. For instance, smart meters, which are used for energy efficiency , are being aggressiv ely deployed in homes and businesses as a critical component in smart grids. Each customer can control the energy consumption by shifting the operation of appliances from high price hours to low price hours in order to reduce electricity e xpense and the peak-to-av erage ratio [13] [25]. Howe ver , attack ers can manipulate smart devices, generate fake electricity price, and identify consumers’ personal be- havior patterns by monitoring the po wer consumption peaks to cause physical, psychological, and financial harm [12] [24] [10]. A straightforward idea to handle such attacks is to add extra uncertainty in the individual load information by perturbing the aggregate load measurement [14] [9]. Howe ver , this approach has to modify the metering infrastructure which might not be practical because millions of smart meters hav e already been installed. In addition, applying uncertainty into customers’ power consumption results in inaccurate billing cost. It is thus important to carefully consider customers’ priv acy in energy scheduling design for smart homes. B. Li and Y . Shi are with the Department of Computer Science and Engineering, University of Notre Dame, Notre Dame, IN 46556 USA (e-mail: bli1@nd.edu; yshi4@nd.edu). J. W u was with the Department of Computer Science and Engineering, Uni- versity of Notre Dame, IN 46556 USA (e-mail: jane.dream.wu@gmail.com) This paper is supported in part by a Luksic Family Grant. Recently , se veral studies ha ve paid attention to customers’ priv acy in power consumption scheduling design. T an et al. [15] proposed a po wer consumption scheduling strategy to balance the consumers’ priv acy and energy efficienc y by using an energy harvesting technique. Kalogridis et al. [7] proposed a power mixing algorithm against po wer load changes by introducing a rechargeable battery . The goal of the proposed algorithm is to maintain the current load equal to the previous load. McLaughlin et al. [11] proposed a non-intrusive load lev eling (NILL) algorithm to combat potential in vasions of priv acy . The proposed NILL algorithm adopted an in-residence battery to of fset the power consumed by appliances, to le vel the load profile to a constant target load, and to mask the appliance features. Chen et al. [6] explored the trade-off between the electricity payment and electric priv acy protection using Monte Carlo simulation. Y ang et al. [23] proposed a scheduling framew ork for smart home appliances to minimize electricity cost and protect the priv acy of smart meter data using a rechar geable battery . Liu et al. [8] explored a stochastic gradient method to minimize the weighed sum of financial cost and the deviation from the load profile. All these existing works assume the acti vity of every appliance can be precisely scheduled and focus on scheduling algorithm design to trade off between the electricity cost and the customers’ priv acy protection for schedulable household appliances. Howe ver , acti ve operations of household appliances are not always schedulable all the time. They can be classified into two groups in terms of controllability: schedulable appliances and non-schedulable appliances. The operation time of schedulable appliances can be postponed to later time during the period under consideration, like a laundry and dish washer . These appliances can be scheduled and turned on/off by a scheduler . The non-schedulable appliances are those that their usages are determined by the user and are not negotiable, like a TV , laptop and ov en. These appliances must be turned on immediately upon the users’ request and cannot be scheduled ahead of time. Non-schedulable appliances introduce operation uncertainties. None of the existing work have considered the influence of the uncertainties of non-schedulable appliances on customers’ pri- vac y and the corresponding customers’ comfort. Our previous work W u et al. [16] [17] formulated the scheduling problem by minimizing the expected sum of electricity cost and achieving acceptable priv acy protection. T o further consider , we provide a runtime scheduling framew ork to comprehensiv ely consider the impact of non- schedulable appliances on customers’ pri v acy and their com- fort. T o our best knowledge, this is the first work addressing non-schedulable appliances comprehensi vely . The proposed framew ork adopts a novel iterativ e algorithm for efficient characterization of non-schedulable appliances’ ef fects. It opti- mizes the electricity costs by incorporating customers’ priv acy for both schedulable and non-schedulable appliances as well as the rechargeable battery . The proposed algorithm is e valuated using real-world household data. The results demonstrate that the design of non-schedulable module and runtime scheduling framew ork will propose an operation solution of schedulable appliances to prepare the worst pri v acy scenarios, minimize electricity cost, and provide priv acy protection guarantee when non-schedulable appliances operate in any situation. I I . B AC K G R O U N D A N D M O T I V AT I O N This section presents an overvie ws of the smart home system model and introduces the impact of non-schedulable appliances on customers’ priv acy and their comfort. A. Smart Home System Overview W e use a well-known smart home system as discussed in [16]. Both schedulable and non-schedulable appliances as well as energy storage device, like rechargeable batteries, receiv e po wer from utility provider via a smart meter de vice and managed by a power management unit (PMU). In this paper , we adopt the same load models, rechargeable battery model, customers’ priv acy model, and price model in [16]. The models are briefly summarized belo w . 1) Load model for appliances: Load model f or schedula- ble appliances: Let p i be the av erage po wer consumption of i -th appliance ( i = 1 , 2 , · · · , N , where N is the total number of schedulable appliances). r i ( t ) and r i ( t + 1) be the remaining operation duration of i -th appliance at time slot t and t + 1 , respectiv ely . W e denote y ( t ) as the total energy consumption of appliances at each time slot t ( t = 1 , 2 , · · · , τ ) and τ is a scheduling horizon denoted by y(t) can be obtained as y ( t ) = P N i =1 p i · ( r i ( t ) − r i ( t + 1)) ∀ i ∈ { 1 , 2 , · · · , N } , (1) The v alue of r i ( t ) and r i ( t + 1) satisfies 0 ≤ r i ( t ) ≤ r i ( t + 1) ≤ E i /p i . E i is the kno wn work load of i -th appliance. r i ( t +1) can be computed as r i ( t + 1) = max r i ( t ) − P t j =1 x i ( j ) , 0 , (2) where r i (1) = E i /p i is the initial i -th appliance state. P τ t =1 x i ( t ) = 1 , ∀ i ∈ { 1 , 2 , · · · , N } , (3) where x i ( t ) is a binary variable. If x i ( t ) = 1 , the i -th schedu- lable appliance start its operation at time slot t . Otherwise, x i ( t ) = 0 . Load model f or non-schedulable appliances: Since the duration of a non-schedulable appliance is unknown, we use a single parameter , w ( t ) to represent the total power consumption of all operating non-schedulable appliances at time slot t . 2) Rechar geable Battery Model: Let B ( t ) be the bat- tery state at time slot t , which is a function of battery charge/dischar ge po wer ( z ( t ) ). The battery state at time slot t + 1 can be expressed as B ( t + 1) = B ( t ) + z ( t ) , t = 1 , 2 , · · · . (4) where B (1) is the initial battery state. B ( t ) must satisfy 0 ≤ B ( t ) ≤ B max , t = 1 , 2 , · · · , τ . (5) where B max is the maximum battery capacity . From the per - spectiv e of the PMU, it schedules the action variable z ( t ) and decides how much power should be charged to or discharged from the battery . 3) Customers’ Privacy Model: Let l ( t ) denote the total aggregated load ov er the scheduling horizon τ and l ( t ) can be computed by l ( t ) = y ( t ) + z ( t ) + w ( t ) = N X i =1 p i min t X j =1 x i ( j ) , r i ( t ) + z ( t ) + w ( t ) = p T min ( V ( t ) , R ( t )) + w ( t ) , (6) where V ( t ) = h P t j =1 x 1 ( j ) , · · · , P t j =1 x N ( j ) , z ( t ) i T is a ( N + 1) × 1 vector; p = [ p 1 , p 2 , · · · , p N , 1] T is a ( N + 1) × 1 vector; R ( t ) = [ r 1 ( t ) , r 2 (2) , · · · , r N ( t ) , + ∞ , ] T is a ( N + 1) × 1 vector; [ · ] T is the transpose operation. If the aggregated load profile is kno wn, the customers’ priv acy information, such as in-house acti v atiate, can be ob- tained. T o mask such priv acy information, we use λ to flatten aggregated load profile. Using the concept of running av erage historical load ( l ), which is defined as l = 1 τ P τ t =1 l ( t ) , the customers’ priv acy requirement is described as − λ ≤ l ( t ) − l ≤ λ, (7) where λ ≥ 0 is a bounding parameter used to guarantee the priv acy . The larger the v alue of λ , the more flexible it is for the customers’ pri v acy requirement. 4) Price Model: Let c ( t ) be the per-unit electricity cost receiv ed from the utility provider at time slot t . The time- varying price value of c ( t ) follows the price discussed in [16]. B. Impacts of Non-Schedulable Appliances T o analyze the impacts of non-schedulable appliances, we consider a simple example with two schedulable appliances ( α 1 and α 2 ), e.g. laundry and one non-schedulable appliance ( β ), e.g. a TV . Let scheduling horizon τ = 4 and pri v acy bound λ = 40 . For α 1 and α 2 , we set E α 1 = 60 kW , E α 2 = 80 kW , p α 1 = 40 kW , and p α 2 = 30 kW . Fig. 1 illustrates the scheduled operations of the two schedulable appliances, household electricity usage, and priv acy ( l ( t ) − l ) without considering non-schedulable appliances. In real-world, customers may turn on the non-schedulable appliance at anytime. W e assume that the non-schedulable appliance β operates at time slot t = 2 and t = 3 with a high 1 2 3 4 0 1 1 2 3 4 0 1 1 2 3 4 0 20 40 60 80 A 1 A 1 A 2 A 2 Electricity Usage (KW) Hours (h) Hours (h) Hours (h) W/O non-schedulable appliance 1 2 3 4 -60 -40 -20 0 20 Privacy Hours (h) 40 60 Fig. 1. The Operations of α 1 and α 2 , household electricity usage, and priv acy . 1 2 3 4 -60 -40 -20 0 20 Privacy Hours (h) 40 60 with non-schedulable appliance 1 2 3 0 20 40 60 80 Electricity Usage (KW) Hours (h) 100 4 Fig. 2. The household electricity usage and privac y within a non-schedulable appliance. possibility based on customers’ historical behaviors. Fig. 2 il- lustrates the household electricity usage and priv acy including the non-schedulable appliance operation. Comparing Fig. 1 and Fig. 2, one can see that the priv acy breach occurs when a non-schedulable appliance operates in the scheduling horizon. Fig. 1 and Fig. 2 also demonstrates the trade-off between customers’ priv acy and contentment requirements. In order to fit the priv acy constrain, it is necessary to re-schedule the runtime of schedulable appliances and charging/dischar ging time of battery . Therefore, to ensure the customers’ priv acy protection, understanding of the influence of non-schedulable appliance becomes essential. I I I . R U N T I M E A P P L I A N C E S C H E D U L E R In this section, we present our approach to runtime cost- effecti ve appliance scheduling to satisfy both priv acy and contentment within considering the ef fect of non-schedulable appliance. Specifically , Section III-A describes the hierarchical structure of Runtime Appliance Scheduler, RAS. Section III-B introduces the specific scheduling problem to be be solved. Section III-C discusses the algorithm design for solving this problem. A. RAS Overview The overall structure of RAS is shown in Fig. 3. The input components of the RAS is the schedule table and the current operation states of both schedulable and non- schedulable appliances as well as the battery state. Given these two input components, RAS can easily lookup the schedule table and find the optimal scheduling solution in real time. Among these input components, building the schedule table at the beginning of scheduling horizon plays the key role in RAS design. B. Scheduling Pr oblem F ormulation The power management unit (PMU), utilizing models in Section II, is designed to schedule the battery and appliances A t th e Be gi n n i n g of S c h e d u l i n g H or i z on O n l i n e Look u p S c h e d u l e T ab l e S ol ve S c h e d u l i n g P r ob l e m Bu i l d S c h e d u l e T ab l e O p e r ati on S tate of S c h e d u l ab l e A p p l i an c e s O p e r ati on S tate of N on -S c h e d u l ab l e A p p l i an c e s Batte r y S tate + + Find Optimal Scheduling Solution Fig. 3. The overall structure of the runtime appliance scheduler . operation. x i ( t ) ( i = { 1 , 2 , · · · , N } ) for all schedulable appli- ances and z ( t ) for the rechargeable battery . This optimization problem ( SP ) can be expressed as S P : min. E { τ X t =1 C ( V ( t )) } = E { τ X t =1 ( c ( t ) l ( t )) } = E { τ X t =1 c ( t ) p T min ( V ( t ) , R ( t )) + w ( t ) } (8a) s.t. − λ ≤ p T min ( V ( t ) , R ( t )) + w ( t ) − l ≤ λ, (8b) r i ( t + 1) = max r i ( t ) − t X j =1 x i ( j ) , 0 , (8c) τ X t =1 x i ( t ) = 1 , x i ( t ) ∈ { 0 , 1 } , ∀ i ∈ { 1 , 2 , · · · , N } , (8d) B ( t + 1) = B ( t ) + z ( t ) , 0 ≤ B ( t ) ≤ B max (8e) z min ≤ z ( t ) ≤ z max (8f) t = 1 , · · · , τ . where C ( V ( t )) = c ( t ) p T min ( V ( t ) , R ( t )) + w ( t ) . z min is the maximum discharged power , which is also the minimum charged power; z max is the maximum charged power . E {·} represents the expectation function. V ( t ) is the vector of de- cision variables for scheduling both the schedulable appliances and the rechargeable battery over the scheduling horizon. The expectation function is needed in the objectiv e function abov e due to operation uncertainties of non-schedulable appliances. Balancing electricity cost within a scheduling horizon in the presence of uncertainties of power consumption by non- schedulable appliances is thus a dynamic process. Howe ver , solving the optimization problem ( SP ) at each time slot would be too time consuming. T o address this issue, we present a hybrid approach. C. Scheduler Algorithm Design In this subsection, we introduce a hybrid approach to solve the optimization problem SP in (8). In the problem SP , the uncertainty ef fects introduced by non-schedulable appliances need to be carefully considered in the priv acy constraint (8b), Because the immediately active operations by non-schedulable appliances lead to high peak load profiles and leak the appli- ance features. Lacking a comprehensive consideration of the influence of non-schedulable appliances can leak customers’ priv acy . T o handle this issue, we consider the worst influences of non-schedulable appliances’ operation in the customers’ priv acy constraint (8b). W e define a time zone of a peak load profile ov er the scheduling horizon as a worst priv acy scenario. Mathematically , we define ϕ = [ t l , t u ] as a time zone for worst pri v acy scenario. t l and t u are a lower bound and a upper bound of time slot, separately . T o guarantee the scheduler satisfies the priv acy constraint (8b) even when the non-schedulable appliances operate in the worst scenario, we present a hybrid approach to handle it. First, we assume that non-schedulable appliances are activ e at the worst pri v acy scenario. Once the non-schedulable ap- pliances are assigned, we apply a dynamic programming like algorithm to solve the optimization problem SP and b uild a schedule table at the beginning of each scheduling horizon. This table contains τ columns where τ is the total number of time slots in the scheduling horizon, and a number of rows corresponding to the different states (described by the r i ( t ) and B ( t ) values). Each entry in the table for time slot t and state s contains the assignment to x i ( t ) and z ( t ) for a giv en set of r i ( t ) and B ( t ) v alues. Note that we determine the assignment of x i ( t ) and z ( t ) by consulting the table entry for time t and state s at the beginning of each time slot t . Second, we iterativ ely update worst priv acy scenario after each schedule table building. Once the worst pri v acy scenario does not change anymore, we collect all these priv acy scenarios as a potential set of operation time zone for non-schedulable appliances. And then, we re-apply a dynamic programming like algorithm to find the optimal assignment for schedulable appliances and rechargeable battery . This hybrid approach effecti vely takes into consideration of both non-schedulable and schedulable appliances. 1) A Dynamic Pr ogramming Algorithm Design: Giv en the operation assignments of non-schedulable appliances at the worst priv acy scenario, the schedule table can be obtained by solving optimization problem SP . T o ensure that the size of a schedule table is manageable, we assume that the remaining operation duration r i ( t ) ( ∀ i ) and the battery state B ( t ) are gen- erally discretized to finite sets: r i ( t ) ∈ H = ( H i, 1 , · · · , H i,S i ) where S i = E i /p i ( ∀ i ), and B ( t ) ∈ B = ( B 1 , · · · , B M ) . Here H is the S -element remaining operation duration set for the i -th schedulable appliance, and B is the M -element battery state set. Let G be the state set with M × Q N i =1 S i elements including battery state set B and remaining operation duration set H ( ∀ i ). Then, the structure of a schedule table can be shown as T able I. That is, a schedule table consists of τ sub-tables (corresponding to the columns in T able I), each of which is for a specific time slot t from 1 to τ . Each sub-table consists of M × Q N i =1 S i entries (corresponding to the state set), each of which contains the assignment to x ( t ) = [ x 1 ( t ) , x 2 ( t ) , · · · , x N ( t )] T . The formulation (8) in Section III forms the basis for con- structing the schedule table. Specifically , we adopt a backward recursiv e approach to solve problem SP . Given the initial state G 1 at time slot 1 , ( G 1 ∈ G ), we denote F 1 ( G 1 ) as the optimal value of (8), which can be obtained recursively due to the principle of optimality [5]. Because the value of C ( V ( t )) can be precisely determined since the operation states of both schedulable and non-schedulable appliances as well as the battery states prior to t are kno wn. Only the future states are not known. Thus we can rewrite (8) as S P : F 1 ( G 1 ) = min ( C ( V (1)) + E G ( τ X t = 2 C ( V ( t )) )) (9a) s.t. − λ ≤ p T min ( V ( t ) , R ( t )) + w ( t ) − l ≤ λ, (9b) r i ( t + 1) = d max( r i ( t ) − t X j =1 x i ( j ) , 0) e r i ( t ) , r i ( t + 1) ∈ H (9c) B ( t + 1) = B ( t ) + z ( t ) , B ( t ) , B ( t + 1) ∈ B , (9d) τ X t =1 x i ( t ) = 1 , x i ( t ) ∈ { 0 , 1 } , (9e) z min ≤ z ( t ) ≤ z max (9f) t = τ − 1 , τ − 2 , · · · , 1 , i = 1 , 2 , · · · , N where V (1) corresponds to those x i (1) and z (1) that result in state G 1 at time t = 1 . E G describes the expectation operation over the all possible states G . Furthermore, (9c) denotes the state transition of remaining operation duration for all schedulable appliances, which is constrained in the finite set H . The (9d) denotes the battery state transition that is also constrained in the finite set B . In a nutshell, the optimal values for arbitrary time slots ( t ) to 1 are determined in a backward recursiv e manner by considering state transitions from all possible state G t +1 at t + 1 to G t at t ( G t , G t +1 ∈ G ) and the constraints in (9), which is sho wn as follows. F t ( G t ) = min { C ( V ( t )) + E G {F t + 1 ( G t + 1 ) } , (10) where C ( V ( t )) is the electricity cost value in state G t at time slot t , which corresponds to those x i ( t ) and z ( t ) . G t and G t +1 are the state at time slot t and t + 1 , respecti vely . E G {F t + 1 ( G t + 1 ) } is the expected sum of the minimal cost value o ver all possible states G for time slots t + 1 , t + 2 , · · · , τ . Note that, the backward recursive approach firstly calculates the optimal value F τ ( G τ ) for time slot τ with the kno wn state G τ , which is shown as follow . F τ ( G τ ) = min C ( V ( τ )) . (11) These processes are summarized in Algorithm 1. 2) Privacy-A ware Scheduler Design: In the description of Algorithm 1, the assignment of activ e operations of non- schedulable appliances are known before the dynamic pro- cess. Considering multiple worst priv acy scenarios, we itera- tiv ely assign non-schedulable appliances into worst scenario T ABLE I S T RU CT U R E O F T H E S C HE D U L E TA B LE . State ( B ( t ) , r 1 ( t ) , r 2 ( t ) , · · · , r N ( t ) ) T ime Slot 1 2 · · · τ B 1 , H 1 , 1 , H 2 , 1 , · · · , H N , 1 x (1) x (2) · · · x ( τ ) B 2 , H 1 , 1 , H 2 , 1 , · · · , H N , 1 x (1) · · · x ( t ) · · · · · · · · · · · · · · · B M , H 1 ,S 1 , H 2 ,S 2 , · · · , H N ,S N x (1) x (2) · · · x ( τ ) Algorithm 1 : A Dynamic Programming Algorithm Design 1: Initialization 2: Given initial state G 1 , M -element battery state set B , S -element remaining operation duration set H for i - th schedulable appliance ( ∀ i ), number of time slots τ , and the assignment acti ve operations of non-schedulable appliances 3: Recursive calculation 4: for t = τ to 1 5: for G t = G 1 to G M × Q N i =1 S i 6: if t = τ , Calculate F τ ( G τ ) by (11); 7: else , Calculate F t ( G t ) by solving (10) until F 1 ( G 1 ) is obtained. 8: Return Optimal value F 1 ( G 1 ) , and its corresponding x i ( t ) ( ∀ i ) and z ( t ) for each time slot t ( ∀ t ∈ τ ). and generate it as a ne w pri vacy constraint, and then use assignment activ e operations of non-schedulable appliances. Finally , the problem SP in (9) is solved. T o simplify the problem, we assume that the power consumption of any non-schedulable appliance within each time slot during the appliance’ s activ e operation is a constant value, defined as p j ( ∀ j = 1 , 2 , · · · , W ). W is the total number of non-schedulable appliances. Associated with the set of time zone for worst priv acy scenarios ( Ω ), we define a binary variable h j ( t, ϕ ) . If h j ( t, ϕ ) = 1 , the j -th non-schedulable appliance activ es its operation at time slot t in worst priv acy scenario ϕ . Otherwise h j ( t, ϕ ) = 0 . The definition of h j ( t, ϕ ) is shown as follo ws. h j ( t, ϕ ) = ( 1 if t ∈ ϕ ( ϕ ∈ Ω) , 0 else Otherwise , ∀ j = 1 , 2 , · · · , M . (12) Thus, we re-write the load model for non-schedulable appli- ances. The total power consumptions of all non-schedulable appliances at time slot t is expressed as w ( t, ϕ ) = W X j =1 h j ( t, ϕ ) p j . (13) According to (6) and (13), the updated priv acy model can be re-written as − λ ≤ g ( V ( t ) , ϕ ) ≤ λ, ∀ ϕ ∈ Ω , (14) where g ( V ( t ) , ϕ ) = p T min ( V ( t ) , R ( t ))+ w ( t, ϕ ) − l . T aking account of the set of worst priv acy scenarios ( Ω ) and updated priv acy constraint (14), the scheduling problem ( SP ( Ω )) is expressed as SP ( Ω ) : F 1 ( G 1 ) = min ( C ( V (1)) + E G ( τ X t = 2 C ( V ( t )) )) (15a) s.t. − λ ≤ g ( V ( t ) , ϕ ) ≤ λ, ∀ ϕ ∈ Ω (15b) r i ( t + 1) = max r i ( t ) − t X j =1 x i ( j ) , 0 , (15c) τ X t =1 x i ( t ) = 1 , x i ( t ) ∈ { 0 , 1 } , ∀ i ∈ { 1 , 2 , · · · , N } , (15d) B ( t + 1) = B ( t ) + z ( t ) , 0 ≤ B ( t ) ≤ B max (15e) z min ≤ z ( t ) ≤ z max (15f) t = 1 , · · · , τ . In the optimization problem SP ( Ω ) , (15b) includes the set of worst priv acy scenarios Ω , which consists of infinite constraints. Inspired by semi-infinite programming technique, we introduce a hybrid approach to solve the problem SP ( Ω ) , which is summarized in Algorithm 2. In Algorithm 2, we denote V ∗ k and V ∗ k − 1 as the feasible solutions of prob- lem SP ( Ω k ) and SP ( Ω k − 1 ) , respectively . Note That at the k -th iteration of the Algorithm 2, we update the priv acy constraint (15b) using Ω k = Ω k − 1 ∪ { ϕ k } . And then we solve a subproblem SP ( Ω k ) with ϕ k satisfying worst pri v acy scenario requirement. Meanwhile, the Algorithm 2 con verges after se veral iterations and produces an approximate optimal solution for SP ( Ω ) if the worst priv acy scenario doesn’t change anymore. Con vergence analysis: Let V denote the feasible re- gion of problem SP . At the k -th iteration, when con- straints (15c), (15d), (15e) and (15f) are satisfied, the feasible region of problem SP ( Ω k ) with worst priv acy scenarios Ω k is expressed as follows. V k := { V | − λ ≤ g ( V , ϕ ) ≤ λ, ∀ ϕ ∈ Ω k } (16) T o prov e Algorithm 2 con ver ge to an optimal solution when k → ∞ , the following two lemmas are needed. Lemma 1 F or each k ≥ 1 , if Algorithm 2 does not stop at this iteration, V k ⊆ V k − 1 holds, where V k − 1 and V k ar e the feasible r e gions of optimization problem SP ( Ω k − 1 ) and SP ( Ω k ) , respectively . Proof By contradiction, suppose this Lemma is false: for each k ≥ 1 , if Algorithm 2 does not stop at this iteration, the V k * V k − 1 . This means that a feasible r e gion V k − 1 is a subset of V k . Therefor e, V k − 1 is also the feasible re gions of pr oblem SP ( Ω k ) , which satisfies privacy constraint (15b) . Based on the definition of feasible r e gion, the following equation (17) holds. V k − 1 := { V | − λ ≤ g ( V , ϕ ) ≤ λ, ∀ ϕ ∈ Ω k } (17) Meanwhile, V k − 1 is also the feasible r e gions of pr oblem SP ( Ω k − 1 ) . Ther efore , V k * V k − 1 yields Ω k = Ω k − 1 . However , Ω k := Ω k − 1 ∪ { ϕ k } holds and ϕ k exists, because Algorithm 2 : Iterative Alternative Algorithm 1: Initialization 2: Apply the Algorithm 1 to solve the problem SP without considering non-schedulable appliances 3: Find the worst priv acy scenario ϕ 0 . Set Ω 0 := { ϕ 0 } 4: Iterative pr ogramming calculation 5: Apply the Algorithm 1 to solve SP ( Ω 0 ) and obtain an optimal scheduling v ariable V ∗ 0 6: Set k := 1 7: Find the worst priv acy scenario ϕ k 8: if ϕ k = ϕ k − 1 , then STOP , retur n optimal scheduling variable V ∗ k 9: else , let Ω k := Ω k − 1 ∪ { ϕ k } 10: Apply the Algorithm 1 to solve problem SP ( Ω k ) to obtain an optimal scheduling variable V ∗ k 11: Set k := k + 1 and got to Step 7 Algorithm 2 does not stop at k -th iteration, contradicting our assumption. Thus, this lemma holds. Lemma 2 F or k ≥ 1 , if k → ∞ , the subpr oblem SP ( Ω k ) has an optimal solution. Proof When k → ∞ , the set of worst privacy scenarios Ω k → Φ , wher e Φ is the set of all possible worst privacy scenarios. Once Ω k r eaches Φ , the feasible r e gion V k of SP ( Ω k ) becomes a unique and smallest feasible r e gion due to lemma 1. Thus, the subpr oblem SP ( Ω k ) has an optimal solution. I V . N U M E R I C A L S I M U L A T I O N S This section ev aluates the proposed runtime scheduling framew ork using real-world household data. The proposed iterativ e alternative algorithm conducts the worst scenario optimization to effecti vely generate cost-efficient schedul- ing solution with priv acy protection guarantee. Section IV -A demonstrates scheduling results based on real world power consumption. Section IV -B campares the ev aluation results of the system without a non-schedulable appliance to the system with a non-schedulable appliance. Section IV -C demonstrates the impacts of battery capacity on the scheduler behavior . A. Real world benchmark W e first summarize the simulation-based e xperimental settings. Appliance data sets and types: W e have selected fi ve household appliances data from a ECO data set [2]. This ECO data set includes aggregate and plug-in appliances’ power consumptions of households in Switzerland ov er a period of 8 months. These data were collected customer daily usage with 86 , 400 measurements per day . T wo types of appliances are considered: schedulable appliances (i.e., clothes dryer , washing machine, dishwasher , stov e, and refrigerator) and non-schedulable appliances (i.e., PC, stereo, TV , and laptop). T o demonstrate the proposed approach, we consider a household having three schedulable appliances and two non- schedulable appliances. W e set the entire work load and power consumptions of three schedulable appliances ( 1 , 2 , and 3 ) as 123456789 10 11 12 Hours (h) 0 0.1 0.2 0.3 0.4 0.5 0.6 Power Consumption (kw) Scheduled Upper boundary Lower boundary Original Fig. 4. Real world scheduling result. follows: ( E 1 = 70 . 7 W , p 1 = 35 . 38 W h ), ( E 2 = 313 . 2 W , p 2 = 156 . 59 W h ), and ( E 3 = 230 . 2 W , p 3 = 76 . 73 W h ). For the two non-schedulable appliances ( 4 and 5 ), the entire work load E 4 = 106 . 97 W and E 5 = 33 . 73 W . Based on the ECO data set [2], the appliance 4 and 5 usually operates at time slot t = [7 , 12] and t = [1 , 6] with a high possibility , respecti vely . The remaining operation duration set H is discretized as H = { 0 , 1 , · · · , d E i /p i e} . The electricity price is adopted by the public released data from Ameren Corporation [1]. Rechargeable battery parameters: The maximum battery ca- pacity B max = 750 Wh and the initial state of battery ( B (1) ) is 0. T o apply the proposed iterativ e alternativ e algorithm, we discretized the state set B of battery as B = { 0 , 1 , 2 , · · · , B max } . The battery charged/dischar ged power set Z = { z | 50 W h ≤ z ≤ 250 W h } . T o speed up the table building process, a local version of the algorithm was used in experiment where z was not discretized. In terms of pri v acy concerns, we set λ = 80 . Scheduling horizon: The length of the scheduling time slot is one hour . The overall scheduling horizon is set to be 12 hours. The simulation result is shown in Fig. 4. It can be observed that the original power consumption curve exceeded the pravic y constrain and the shape peak is sensitiv e to be detected by attacker . The scheduled po wer consumption curve followed the priv acy constrain between the upper boundary and lower boundary and the curve is relative smooth. T ABLE II E V A L UA T I O N E NV I RO N M EN T S E T TI N G Battery total capacity 0.2 kW Battery charging/discharging rate 0 kW to 0.1 kW Non-schedulable appliances Runtime 1 (hours) B. Scheduler Evaluation T ABLE III S C HE D U L AB L E M OD U L E E V A LU A T I O N R ES U L T S T ime Slot 1 2 3 4 5 6 7 8 9 10 11 12 App 1 0 0 0 0 0 1 1 1 1 1 0 0 App 2 0 0 0 1 1 1 0 0 0 0 0 0 App 3 1 1 0 0 0 0 0 0 0 0 0 0 Section IV -B will ev aluate the system using the setting as shown in T able II. Considering the real-world scenario, the 0 hours 2 hours 4 hours 6 hours 8 hours 10 hours 12 hours time slot $0.00 $0.20 $0.40 $0.60 $0.80 $1.00 Electricity Price /kWh Real Time Price 1 Fig. 5. The real time price for performance ev aluation. 0 hour s2 hour s4 hour s6 hour s8 hours 10 hours 12 hours time slot 0 kW/ h 10 kW /h 20 kW /h 30 kW /h 40 kW /h power consumption 0 hour s2 hour s4 hour s6 hour s8 hours 10 hours 12 hours time slot -10 kW/ h -5 kW /h 0 kW/ h 5 kW/ h 10 kW /h battery operation (charge/discharge) 0 kW/ 0.1kW/ 0.2kW/ 0.3kW/ 0.4kW/ power consumption -0.1kW/ -0.05kW/ 0kW/ 0.05kW/ 0.1kW/ battery operation (charge/discharge) Fig. 6. Scheduling results for schedulable module. 0 hour s2 hour s4 hour s6 hour s8 hours 10 hours 12 hours time slot 0 kW/h 0.1kW/h 0.2kW/h 0.3kW/h 0.4kW/h power consumption 0 hour s2 hour s4 hour s6 hour s8 hours 10 hours 12 hours time slot -0.1kW/h -0.05kW/h 0kW/h 0.05kW/h 0.1kW/h battery operation (charge/discharge) Fig. 7. Scheduling results for non-schedulable module. charging/dischar ging rate of a battery varies in the scheduling horizon. Giv en the unknown starting time of non-schedulable appliance, the scheduler system defines a certain range of time as the potential starting time of non-schedulable appliance based on its historical usage pattern. In this test, there are three assumptions made. First, each appliance is allowed to run only once and it will stop when its runtime finished. Second, the po wer consumption of any schedulable appliances within each time slot during the appliances acti ve is a constant value. Third, all appliances hav e to be finished before the end. Fig. 5 illustrates the real-time electricity price over 12 hours scheduling horizon. Giv en the real-time electricity price, online scheduler decides on the actual appliance usage pattern. T ABLE IV N O N - S C H ED U L AB L E M O DU L E E V A L UA T IO N R E S ULT S T ime Slot 1 2 3 4 5 6 7 8 9 10 11 12 App 1 0 0 0 0 1 1 1 1 1 0 0 0 App 2 0 0 0 0 0 0 0 0 1 1 1 0 App 3 0 1 1 0 0 0 0 0 0 0 0 0 T able III and Fig. 6 demonstrate the proposed operation of schedulable module and the operation of battery and real time power consumption, respectiv ely . It can be noticed that the power consumption followed the priv acy constraint which successfully protect the behavior of all appliance. In the battery operation, the battery will gain energy at the positiv e v alue and release energy at negativ e value in the battery operation as shown in Fig. 6. The non-schedulable module ev aluation results are shown in T able IV and Fig. 7, respectively . In the T able III and T able IV, for each appliance, the digits ’1’ represent that the appliance is switched on and the digits ’0’ represent that the appliance is switched off. In this scheduling results, the non-schedulable appliance did not run. But the system prepared for it between the first six hours which define as the non-schedulable time zone in this instance. The battery will reserve enough energy for the unpredictable appliance, thus it will follow the priv acy constrain. In this module, the system will prepare for the worst case of priv acy risk and also find the lo west electricity billing price solution. C. Sensitivity analysis of battery capacity and billing price In this section, we analyze the effect of electricity price and battery capacity on the scheduler the system. The exper- iment setup of system remains the same as discussed in the Section IV -B. Fig. 8, marked as the second price, is modified from Fig. 5. The minimum electricity price was switched out from the non-schedulable time zone in Fig. 8. T o ev aluate the effect of price, the test will be repeated with the second price. The ev aluation results is shown in Fig. 9. The X coordinate represents the battery size and Y coordinate represents the amount of billing price in the U.S. Dollar . As increasing the battery capacity , the billing price conv er ges to a constant value and it indicted the battery capacitor is sufficient in this certain scenario. As shown in Fig. 9, the system is v ery sensitive when the battery capacity is relative small. Because the battery is not sufficient to reserve enough energy in a lower price time slot, the billing price drop rapidly when the capacity increase from 8 kW to 20 kW . For the non-schedulable module, it can be noticed that the battery must reserve electricity for the non- schedulable appliance, thus the the total price is slightly higher than the price for a schedulable module. In the second price instance, the minimum price is out of non-schedulable activ e time range and the system will schedule the battery to reserve energy to prepare for the non-schedulable appliance at higher price time slot. Hence, the total price will increase since the scheduler has to follow the pri v acy constrain. Therefore, the price drops more when the battery capacity increases in non- schedulable module. The scheduler is able to protect the appliance beha vior information and also able to obtain a better price solution. 0 hours 2 hours 4 hours 6 hours 8 hours 10 hours 12 hours time slot $0.00 $0.20 $0.40 $0.60 $0.80 $1.00 Electricity Price /kWh Real Time Price 2 Fig. 8. Modified real time price for sensitivity analysis. schedulable (1st price) non-schedulable (1st price) schedulable (2nd price) non-schedulable (2nd price) 1.10 1.05 1.00 0.95 1.02 1.00 0.98 0.96 0.05 0.1 0.15 0.20 0.25 0.30 0.35 0.40 0.45 0.50 T otal batter y capacity (kW) T otal batter y capacity (kW) T otal billing pr ic e ($) T otal billing pr ic e ($) 0.05 0.1 0.15 0.20 0.25 0.30 0.35 0.40 0.45 0.50 Fig. 9. T otal billing price VS total battery capacity sizes. The scheduler is build with high flexibility and it can han- dle more complex scenarios, such as flexible battery charg- ing/discharging rate, a smart home system with a large number of schedulable appliances and non-schedulable appliances. V . S U M M A RY A N D F U T U R E W O R K Smart homes promise many potentials but also raise new priv acy concerns. This paper considers the effects of fak e guideline electricity price and non-schedulable appliances’ op- eration uncertainties in appliance scheduling for smart homes. Different from existing research, this work aims to not only minimize electricity cost but also protect customers’ priv acy . The proposed framework, P A CES , is e v aluated using publicly released households’ data sets. Our experimental study shows that P A CES can effecti vely protect customers’ priv acy and satisfy their immediate service requirement with a small increase in electricity cost. P A CES can be somewhat time consuming if a household has a large number of appliances. There are great research opportunities in the area of priv acy protection and cost reduction for smart homes. R E F E R E N C E S [1] Ameren day-ahead prices. https://www2.ameren.com/RetailEnergy/ RealT imePrices. [2] Electricity consumption and occupancy . http://data- archiv e.ethz.ch/ deliv ery/Deli veryManagerServlet?dps pid=IE594964. [3] K. Al-Jabery , D. C. W unsch, J. Xiong, and Y . Shi. A nov el grid load management technique using electric water heaters and q-learning. In 2014 IEEE International Confer ence on Smart Grid Communications (SmartGridComm) , pages 776–781. IEEE, 2014. [4] K. Al-Jabery , Z. Xu, W . Y u, D. C. Wunsch, J. Xiong, and Y . Shi. Demand-side management of domestic electric water heaters using approximate dynamic programming. IEEE T ransactions on Computer- Aided Design of Inte grated Circuits and Systems , 36(5):775–788, 2017. [5] D. P . Bertsekas, D. P . Bertsekas, D. P . Bertsekas, and D. P . Bertsekas. Dynamic pr ogramming and optimal contr ol , v olume 1. Athena Scientific Belmont, MA, 1995. [6] Z. Chen and L. Wu. Residential appliance dr energy management with electric privac y protection by online stochastic optimization. IEEE T ransactions on Smart Grid , 4(4):1861–1869, 2013. [7] G. Kalogridis, C. Efthymiou, S. Z. Denic, T . A. Lewis, and R. Cepeda. Priv acy for smart meters: T owards undetectable appliance load signa- tures. In IEEE International Confer ence on Smart Grid Communica- tions , pages 232–237, 2010. [8] E. Liu, P . Y ou, and P . Cheng. Optimal privac y-preserving load schedul- ing in smart grid. In 2016 IEEE P ower and Energy Society General Meeting (PESGM) , pages 1–5, 2016. [9] Y . Liu, S. Hu, J. W u, Y . Shi, Y . Jin, Y . Hu, and X. Li. Impact assessment of net metering on smart home cyberattack detection. In Pr oceedings of the 52nd Annual Design Automation Confer ence , page 97. A CM, 2015. [10] Y . Liu, S. Hu, J. W u, Y . Shi, Y . Jin, Y . Hu, and X. Li. Smart home cybersecurity considering the integration of renewable energy . In Smart Cities and Homes , pages 173–189. Elsevier , 2016. [11] S. McLaughlin, P . McDaniel, and W . Aiello. Protecting consumer priv acy from electric load monitoring. In Proceedings of the 18th A CM confer ence on Computer and communications security , pages 87–98. A CM, 2011. [12] A. Molina-Markham, P . Shenoy , K. Fu, E. Cecchet, and D. Irwin. Priv ate memoirs of a smart meter . In ACM workshop on embedded sensing systems for energy-efficiency in building , pages 61–66, 2010. [13] P . Palensky and D. Dietrich. Demand side management: Demand response, intelligent energy systems, and smart loads. IEEE transactions on industrial informatics , 7(3):381–388, 2011. [14] L. Sankar, S. R. Rajagopalan, and S. Mohajer. Smart meter priv acy: A theoretical framework. IEEE T ransactions on Smart Grid , 4(2):837–846, 2013. [15] O. T an, D. Gunduz, and H. V . Poor . Increasing smart meter pri vac y through energy harvesting and storage devices. IEEE Journal on Selected Areas in Communications , 31(7):1331–1341, 2013. [16] J. W u, J. Liu, X. S. Hu, and Y . Shi. Privac y protection via appliance scheduling in smart homes. In 2016 IEEE/A CM International Confer- ence on Computer-Aided Design (ICCAD) , pages 1–6, 2016. [17] J. Wu, J. Xiong, and Y . Shi. Efficient location identification of multiple line outages with limited pmus in smart grids. IEEE T ransactions on P ower Systems , 30(4):1659–1668, 2015. [18] X. Xu, Y . Ding, S. X. Hu, M. Niemier , J. Cong, Y . Hu, and Y . Shi. Scaling for edge inference of deep neural networks. Nature Electr onics , 1(4):216, 2018. [19] X. Xu, F . Lin, A. W ang, X. Y ao, Q. Lu, W . Xu, Y . Shi, and Y . Hu. Accelerating dynamic time warping with memristor-based customized fabrics. IEEE T ransactions on Computer-Aided Design of Integr ated Cir cuits and Systems , 37(4):729–741, 2018. [20] X. Xu, F . Lin, W . Xu, X. Y ao, Y . Shi, D. Zeng, and Y . Hu. Mda: A reconfigurable memristor-based distance accelerator for time series mining on data centers. IEEE T ransactions on Computer-Aided Design of Integr ated Circuits and Systems , 2018. [21] X. Xu, Q. Lu, L. Y ang, S. Hu, D. Chen, Y . Hu, and Y . Shi. Quantization of fully conv olutional networks for accurate biomedical image segmen- tation. In Proceedings of the IEEE Conference on Computer V ision and P attern Recognition , pages 8300–8308, 2018. [22] X. Xu, D. Zeng, W . Xu, Y . Shi, and Y . Hu. An efficient memristor- based distance accelerator for time series data mining on data centers. In 2017 54th ACM/ED AC/IEEE Design Automation Conference (DA C) , pages 1–6. IEEE, 2017. [23] L. Y ang, X. Chen, J. Zhang, and H. V . Poor . Cost-ef fectiv e and privac y- preserving energy management for smart meters. IEEE T ransactions on Smart Grid , 6(1):486–495, 2015. [24] Y . Y uan, Z. Li, and K. Ren. Modeling load redistribution attacks in power systems. IEEE T ransactions on Smart Grid , 2(2):382–390, 2011. [25] S. Y ue, J. Chen, Y . Gu, C. W u, and Y . Shi. Dual-pricing policy for controller-side strategies in demand side management. In IEEE International Conference on Smart Grid Communications , pages 357– 362, 2011.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment