Contention Intensity based Distributed Coordination for V2V Safety Message Broadcast
In this paper, we propose a contention intensity based distributed coordination (CIDC) scheme for safety message broadcast. By exploiting the high-frequency and periodical features of the safety message broadcast, the application-layer design of the …
Authors: Jie Gao, Mushu Li, Lian Zhao
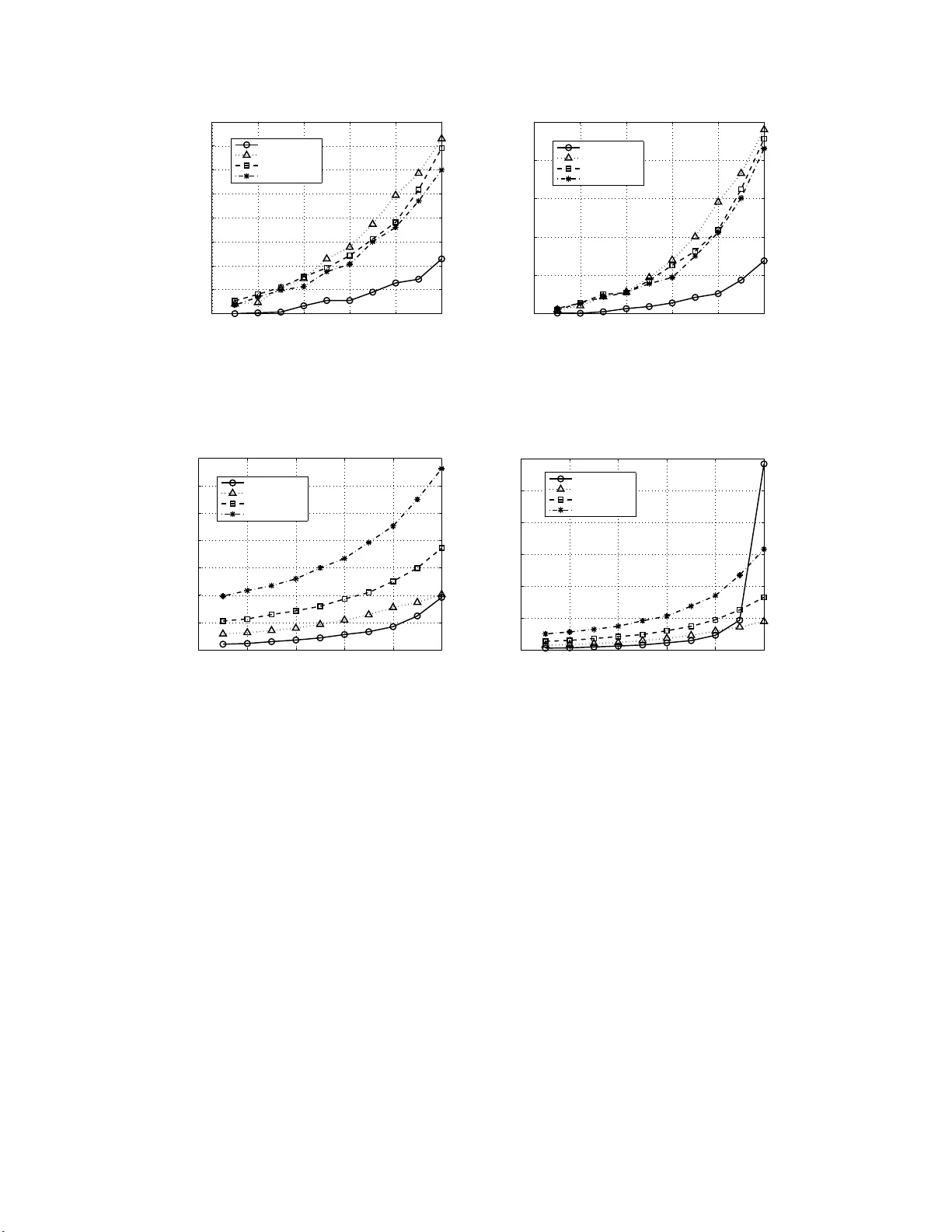
1 Contention Intensity based Distrib uted Coordination for V2V Safety Message Broadcast Jie Gao, Member , IEEE , Mush u Li, Student Member , IEEE , Lian Zhao, Se nior Membe r , IEEE , a nd Xuemin (Sherman) She n, F e llow , IEEE Abstract In this paper , we propose a contention intensity based distributed coordination (CIDC) scheme for safety message broadcast. By exploiting t he high-frequency and periodical features of the safety message broadcast, the application- layer design of t he CIDC enables each vehicle to estimate the instantaneous channel contention i ntensity in a fully distributed manner . With the contention intensity information, the MA C layer design of CIDC allows vehicles to adopt a better channel access st r ategy compared to the 802.11p. This is because CIDC selects the i nitial back-off counter for each new packet deterministically , i. e., based on the contention intensity , instead of randomly . The proposed CIDC is modeled, and key performance indicators i n terms of the packet collision probability and avera ge contention delay , are derived . It is shown that the proposed change i n the initial counter selection leads to a system model completely differe nt from the classic Marko v chain based model. Moreov er , the proposed C I D C , fully distributed and compatible with the 802.11p, can achiev e both a much lower collision probability and a smaller contention delay compared with 802.11p at the cost of a small communication and computation overhe ad. Extensive simulation results demonstrate the effecti veness of the CIDC in both of the accurate and the erroneous contention intensity estimation scenarios. Index T erms safety message broadcast, MAC design, 802.11p, DS RC, connected vehicles I . I N T R O D U C T I O N V ehicle-to-vehicle (V2V) com munication s are a cornerston e of connected vehicles (CV), which are eme rgin g as an important componen t of the next generatio n intellige nt transportation systems (IT S) [1]. The deployment of connec ted vehicles, combin ed with automated driving, is expected to significantly redu ce traffic a ccidents and the resulting econom ic loss thro ugh integrating co mmunicatio ns inclu ding V2V , vehicle-to-inf rastructure (V2I ), etc. and enabling an awareness of the surroun d ing traffic environment and events at a ll vehic les [2]. As an effort of J. Gao and L. Zhao are with the Department of E lectri cal and Computer E ngineer ing, Ryerson Univ ersity , T oronto, ON, M5B 2K3, Canada (e-mail: { j.gao, l5zhao } @ryerson.ca). M. Li and X. Shen are with the Department of Electrical and Computer E ngineer ing, Univ ersity of W aterloo, W aterl oo, ON, N2L 3G1, Canada (e-mail: { m475li, sshen } @uwat erloo.ca). September 10, 2019 DRAFT 2 deploying CV , technolog ies and stan d ards h av e b een ac tively developed. Ded ica ted shor t-range comm unications (DSRC) have been tested as an enabling tech nology f or V2V and V2I comm unications [ 3]. The DSRC stan dard adopts seven channels, i.e., on e dedicated contr o l chan nel fo r safety applicatio n s and six serv ice channels for n o n- safety app lications. The IEEE 802 .11p standard covers the ph ysical lay er a n d med ia acce ss co ntrol (MAC) layer designs of DSRC. The IEEE 160 9 standar d stack addresses the MAC , tran sport, and network layer s. The IEEE 802.1 1p an d IEEE 1 609 collectively fo r m the wireless access in vehicular environments (W A VE) standard s while the SAE J273 5 standa rd defines the message set to be utilized in th e a p plication laye r . In th e V 2 V com munication s for CV applications, a particularly , if not the mo st, impo r tant compo nent is the broadc a st of safety messages. Such br oadcast corre sp onds to the Basic Safety Message (BSM) in the SAE J27 35 standard in the US or th e Coopera tive A wareness Message (CAM) in the ITS standard of Euro pean T elecomm u- nications Stand a rds Institute [4]. The safety m essages are sing le-hop, perio dical ( i.e., time-dr i ven as opposed to ev ent-d riv en), and carr y safety -related status info rmation o f vehicles such as th eir speed, acceleration , po sition, an d direction. Thro ugh the bro a dcast of the safety messages, vehicles can be aware of each o ther’ s status, an d tr affic accidents can b e reduce d . As a result, the inform a tio n conve yed in the safety m essage broad cast is the fo undation to support all V2V safe ty application s [3]. Meanwhile, safety messages need to be exchanged at a high freq uency , e.g., 10 messages per second , to be ab le to su pport safety app lica tions in CV . Suc h a high freq uency r enders the safety message b roadcast the majo r data traffic load on the DSRC con trol chan nel. Ther e fore, th e safety message b roadcast is significant in V2V commu nications in terms of both its impo r tance and its data traffic volume. Accor dingly , a protoco l for V2 V commu nications sho uld incorpo rate elabo rate designs to sup port r eliable safety m e ssag e broad cast. In general, a protoco l design for V2V co m munication s faces a fundam ental trade-off: a better per f ormance is usually achieved at the cost of a larger overhea d [5]. For th e safety message bro adcast, the 802.1 1p has the a d vantage that it is fully distributed, re q uires no c o ordinatio n, and yields no overhead . Howe ver , the c h annel con tention d esign of 80 2.11p suffers from a hig h co llision p robability unde r a high network load [6]. Th us, the 802. 11p an d most works built on it can be considered a s design s that tr ade off perfo rmance improvement potentials for a small overhead. Other works in the literature, as will b e discussed in detail in Section II, aim to achieve a substantially improved p erforma n ce at the cost of m o re co o rdination and a larger overhead. The objective of this work is to d ev elop a distrib uted scheme for safety message b roadcast th at improves the perfor mance substantially com pared to the 80 2 .11p at the cost of a sma ll overhead. In or der to achieve this target, we exploit the u nique featu res of the safety message broad cast, i. e., hig h message f r equency , periodicity , an d un iform format, an d develop our d e signs b ased on these features. The co ntributions of th is work are as follows. First, we propo se a novel contention intensity ba sed distrib uted coord in ation (CIDC) scheme to imp r ove the perfor mance of safety message broadca st. The pro p osed de sig n is fully distributed an d c o mpatible with 8 02.11 p, features a small com munication a nd compu tation overhead, an d achieves a substantial per formanc e im p rovement as co mpared to 802 .11p. Second, the prop o sed CIDC is modeled and character iz e d, and insights regardin g the con tention delay and th e packet collision are found. Analy tical results on the contentio n d e la y and collision pro bability of the CIDC are derived. It is dem onstrated that a seem ingly simple modifica tio n of the 802 . 11p MAC by the pro p osed CIDC lead s September 10, 2019 DRAFT 3 to a very different system mo del and a different und erlying cause o f packet collision c ompared to the 80 2.11p. Third, the perfo rmance of th e prop osed CIDC is demonstra te d using extensive simulation s. T h e collision pr ob- ability and average dela y of the CIDC are co m pared to both the analy tic resu lts and those of the 802 .11p MA C. It is shown that the CIDC can sub stantially red uce both the co llision pr obability and the av erag e c o ntention delay in a wid e rang e of vehicle d ensity com pared to the 8 02.11 p MAC ev en when errors are intr oduced to accou nt for vehicle mob ility and other potential pra c tica l concer ns. I I . R E L A T E D W O R K S This sectio n revie ws the existing works related to safety message br o adcast in V 2 V commu nications in th e literature. W e categorize the related works in to two classes ba sed on their relation with the 802.1 1p. The first class of works fo c uses o n the perfor mance analysis of the 802.1 1p p rotocol, among which some studies propo se various par ameter adap tion sche m es f or th e perfo rmance optimiz a tio n of the 8 0 2.11p . The analy sis on the perfor mance o f 802 .11p can b e fo und in [7] - [1 3]. Han et al. p r oposed an analytical model for th e perfo rmance of 802.1 1p MA C in [8 ] with a foc us on different access categories. Ma et al. developed a characteriza tion o f the reliability of safety message broadcast u sing different transmitter-centric an d rec e i ver-centric metrics [9]. Y e et al. analy zed the b roadcast efficiency a n d reliability trade-off in 802 .11p in [ 1 0] and prop osed perfor mance optimization based on adap tin g th e co n tention win dow size or storing the message with a certain pro bability . Fallah et al. studied the p erform ance o f broa d cast in 802. 1 1p in a h ighway scenario and p r oposed congestion control based on a d justing the transmission p ower and me ssage freq uency [11]. Ha feez et al. de r i ved a p e rforman ce analysis conside r ing the mobility of vehicles and pr oposed pe r forman ce enhancem e nt based on adapting the message frequen cy , transmission power , and con tention window size [12]. Th e above works based on adaptin g th e par ameters of th e 80 2.11p aim to ach iev e a perfo rmance im provement while su staining a distributed structu re and sm a ll overhead. H owever , the a pproach based on param eter adaptio n may enco unter limitation s in p ractice. For instance, adapting the message frequ ency is no t always a f easible o ption as the req uirement on th e m e ssag e fr equency for supportin g safety applications can be too string ent to be practically ad ju stable. As fo r adapting th e conten tion window size, it e ssentially in tr oduces a trad e-off be tween the delay p erforman ce and the collision per forman c e instead of improving bo th . Th ere are also resear c h works built on the 8 02.11p tha t a r e not based o n p arameter adaption [14] - [16]. W u e t al. propo sed a deterministic cha n nel access fo r safety me ssage bro adcast based on p rotocol sequence s [15]. Park and Kim developed an applica tio n layer design based on a r andom offset in BSM ep och selection to improve the MAC layer perform ance of 802.1 1p when th e m essage freq uency is no t adaptab le [16]. Recognizing the per formanc e limitation of th e 80 2.11p un der a high n etwork load, the seco nd class of works aims to develop new protoco ls instead of improving the 80 2.11p. V ar io us MAC pro tocols for vehicu lar commu nications have been p roposed , in cluding b o th distributed an d centralized an d both co ntention- based and con tention-fr ee designs [5]. Omar et al. p roposed a distributed time division m ultiple access (TDMA)- b ased MAC Pro tocol in the scen ario of bi-directio nal traffic flow with vehicles eq uipped with two transceivers [17]. The pro to col can significan tly decrease th e co llision prob ability and improve throug h put as com pared to 802 .11p. As T D M A ba sed MAC lack s scalability with r e spect to the number o f vehicles, L yu et a l. de sig n ed a slot sharing T DMA ba sed MA C for September 10, 2019 DRAFT 4 safety message broad casting [18]. Bha rati et al. pr oposed a d istributed cooper a tio n based M AC in [19], in which vehicles fo rm clusters and a coop eration h eader is inserted into a packet when a vehicle decides to help o thers. Zhang et al. pro posed a cen tralized TDM A based MA C, in wh ich a road sid e u nit (RSU) is needed to co ordinate the commu nications of the vehicles [20]. A TDMA b ased MA C is also pr oposed in [24] for relay ing broadcast messages. For a scenario in wh ich mu ltiple cha nnels are av ailable an d each vehicle has two radio heads, Almotairi developed a frequ ency hopp ing b ased MA C [21]. Y e and Zhuan g prop osed an adap tive contro l M AC solu tion th a t switches between 802.1 1 p an d TDMA-based MAC d epending on the network load [22]. A study of the periodical broadc a st with geo lo cation-based access in L TE V2X can be f ound in [23]. It can b e seen that these works usually aim to achieve a significan t perf o rmance im p rovement at the c o st o f a larger overhead necessary for imp lementing an effective coordin ation in th e network. This work can b e categorized into th e first class. Howe ver , instead o f adapting the p arameters in th e 802.1 1p, we a im to achieve a significan t p erforma n ce imp rovement by exploiting th e unique featur e s of th e safety message broadc a st an d developing the de sig ns accor d ingly . I I I . T H E P RO P O S E D D E S I G N The p roposed CIDC exploits three u nique featu res of safety m essage bro adcast, as summ arized in T able I. First, while the high me ssage freq uency can lead to congestion , it enables vehicles to u p date their infor mation on surroun ding vehicles timely . Mor eover , a high message freq uency also imp lies that the imp act of vehicle mo bility in the duration of a m essage cycle is very limited. 1 Consequently , the impact of the m obility o n the top o logy of the vehicular network with in several m essage cycles can b e neglected. Second, as the safety messages ar e pe r iodical, th ere is a regular pa ttern regardin g the m essage arrival in stants of each vehicle, wh ic h c a n be observed by o ther vehicles th rough m essage exchange s. Such observations can be exploited to improve the ch a n nel acce ss strategy of the vehicles. Third, as the safety message has a unifo rm format and size, there is a regular pattern regarding the packet transmission duration , which can be exploited in the proto c ol design and m odeling. It should be no te d that the CIDC is d edicated to the time-d riv en safety m essage broad cast. Wh ile other types of messages a r e not covered, the propo sed design can be used as a building blo ck in a compr ehensive pr otocol that covers all types of V2 V comm u nications. For example, a pro to col can ado pt the CIDC fo r the broad cast on the DSRC c ontrol chan nel and the 802. 1 1p for th e unic a st on the service ch annels. A. Assump tions The f o llowing assump tions are made based on th e f e atures of safety messages: • Giv en the h igh freq uency of safety message b roadcast (e.g., λ = 10 messages p e r second), the variation in the set o f neigh bor vehicles du e to vehicle m obility is negligible dur ing several message perio ds. 1 W ith a 10Hz message frequenc y , the distanc e between two vehicl es drivi ng to ward each other at 60km/h reduces by only 3 m eters in a message cyc le. September 10, 2019 DRAFT 5 T ABLE I: Features of Safety Message Fea ture Implicati on High Message Frequenc y Information updated timely; Mobilit y not a major concern. Time -Driv en (Periodical) Regu larity in the message arriv al instants Uniform in Format and Size Regu larity in the transmission duration • V ehic le i has a un ique rando m offset σ i indepen d ently and unifo rmly drawn fro m [0 , 1 /λ ) . T his can prevent messages of different vehicles fro m arriving and co ntending fo r channel a c cess at the same instant. T he offset σ i can be fixed for each vehicle or refreshing at a freque ncy µ such th a t µ ≪ λ . In either case, the ran dom offset f or each vehicle is con stant for a sig n ificant nu mber of message cycles. • A n ew safety message expires and replaces an existing safety message that has no t b een sent. • The vehicle s h av e th e capab ility of pro cessing rea l- time info rmation, which is n ecessary to suppo rt any safety applications. T o facilitate the m o deling and analy sis of th e CIDC, the following assumption is also used: • Safety messag e s have a unifo r m size. Specifically , the duration o f a message tran smission plus a DCF In terframe Space (DIFS) is assumed to be a multiple of the dura tion of a time slot, i.e., T Tx + T DIFS = K T s , wher e T Tx , T DIFS , T s are the length of a m essage tran smission, the len gth o f a DIFS, and the len gth o f a time slot in th e DCF , respec tively . B. CIDC: the Mod el The term c ontention intensity refers to the nu mber of safety messages that are either waiting fo r cha n nel access or currently transmitting at a given time instant. The CIDC c onsists o f two par ts. The fir st p art is distributed co ntention intensity estimation , an ap plication layer function that facilitates informa tio n exchange for vehicles to estimate the channel contentio n inten sity . Th e seco nd part is the access strate gy , a MAC layer d esign built on the DCF of the 802.1 1p MAC but modified to exp lo it the contention intensity in formation . The ap plication-lay er desig n for the distributed conten tion in tensity estimation is as follows. • V ehic le i includ e s its o ffset σ i in its safety messages. • V ehic le i extracts the offsets σ j of vehicles { j | j 6 = i } with in its ran ge from received safety messages. • V ehic le i estimates the co ntention inte n sity at in stan ts wh e n a n ew safety packet is gene rated at its MA C layer . 2 The estimation of contentio n in tensity is illustrated in Fig. 1. In this example, there are 1 0 vehicles within each other’ s commun ication range , shown in th e bottom par t of Fig. 1 . The pe rspective o f vehic le 1 is u sed as an example. As shown in the top part o f Fig. 1 , vehicle 1 maintain s a timeline a nd mar k s the instants at which each vehicle 2 A MAC layer packet contains an applicat ion la yer message in its payload. In the rest of the paper , ‘pack et’ and ‘message’ are used interc hangeably when there is no confusion. September 10, 2019 DRAFT 6 1 / λ t c t t 0 9 7 2 4 1 3 5 6 8 10 σ 2 2 3 9 6 5 8 1 10 4 7 Roadway (Instant ) Timeline (V ehicle 1) t c Fig. 1: Illustration of con te n tion intensity estimation. in its commu nication r ange generates a safety message (sho wn as the hollow circles on th e timeline in Fig. 1) based o n the safety messages received in previous cycles. Wh e n a new safety message is r eceiv ed fr om a neigh bor vehicle, the co rrespon d ing mark is chang ed (shown as solid circles on the time lin e) to indicate that th e message is no longer conten ding for ch annel access. Then , the m essages tha t have been gener a ted by neig hbors and n ot yet received in the interval from the beginning o f this message cycle, marked as t 0 , till th e cur rent time instant, marked as t c , are conten ding fo r chann el access. Counting th e nu m ber of su ch messages g i ves the instantan eous conten tion intensity , wh ich is 3 in th e example given b y Fig. 1. Note that the beginnin g of message cycles sho uld be aligne d at all vehicles. For example, th e beginnin g can be determ ined based o n the GPS time. The MAC -laye r desig n o f the CIDC is based on the 80 2.11p MAC a n d in herits th e slot based structu re with carrier sensing , th e back -off counte r, and the DIFS. De tails regard ing the MAC la y er of the 80 2.11p can be found in many works (e.g., [12] a n d [ 25]) and thus are neglected here. The o n ly an d key mod ification in the MAC layer of the CIDC is regarding how the initial back- o ff coun ter of a packet is d etermined. I n the CIDC, the in itial back- off counter is determin ed based on the con tention intensity (as opp osed to a rand om selection in the 80 2.11p MAC) as fo llows: • For each new packet, its initial back -off cou nter is set to M times the contentio n intensity ( itself in cluded as a con te n ding packet when calcu lating the contention inten sity), where the proto col par ameter M is a positive integer . The ab ove access strategy is illu stra te d in Figs. 2 a and 2b. In b oth cases, M is set to 3 an d n = 2 existing packets are co ntending . Theref ore, if a n ew pac ket arrives at this instant, its en tr y po int is the ( n + 1) M = 9 th slot from the slot k . Packets at different vehicles con tending f or chann el access ca n be co nsidered as waiting in a virtual qu e u e. The new packet will either enter from the end of the v irtual que ue of conten ding packets (sh own in Fig. 2 a) or cut in line (shown in Fig. 2b). Assuming no more new arrivals in the n ext 11 slots, the n ew p a cket will be transmitted after the two existing p ackets in the case of Fig. 2a and between the two existing packets in the c a se of Fig. 2b. Note that, unlike the timeline in Fig. 1 which is shown f rom the persp e cti ve of one vehicle, Figs. 2a and 2b are sh own fr om th e perspective o f a virtual ob server which is a ssum ed to have real-time info rmation of the entire vehiclu la r network. September 10, 2019 DRAFT 7 k +1 +6 +8 +7 +9 +2 +3 +4 +5 +10 +12 +11 Entry Point M = 3 Current Slot Busy slot Idle slot (a) Illustration of initial back-off counter determination - entering from the end. k +1 +6 +8 +7 +9 +2 +3 +4 +5 +10 +12 +11 ,-../0123451 601.7285901 M 2:2( ;-<72<451 =>4/2<451 (b) Illustration of initia l back-of f counter determinat ion - cuttin g in line . Fig. 2: Conten tion intensity estimation and in itial b ack-off cou nter determin ation in the CIDC. For eac h vehicle, it ha s, th rough estimation, the inf ormation on th e numbe r of vehicles comm unicating with it an d the instantaneo us co ntention intensity , but not the v alue of th e back-o ff cou nters o f contend ing pac kets at oth er vehicles. Ther efore, the en try po ints in Fig s. 2a and 2b for a new p acket can be deter mined by th e co rrespond ing vehicle while the inform ation on which slots are busy is not av ailable to any veh icle but only the vir tu al n etwork observer . Similar to the 802 .11p MA C, the b ack-off co unter of any packet red uces by o ne after each idle slot, freezes whenever the chan n el is d etected busy , an d un freezes after the chan nel becom es id le f or the leng th of a D I FS. T he packet starts transmitting when its b ack-off cou nter reach e s zero. It can be seen th at the prop osed design is fu lly distributed and requires m in imum modification fr om the 802.1 1p MA C. Moreover, the overhead of the prop o sed design in either com munication o r co mputation is very small. Specifically , th e c o mmunica tio n overhead is in troduced as a result of adding the o ffset inf ormation σ i to the safe ty message. A 24-bit section is mor e than enou gh to conve y an offset inf o rmation to th e a c c uracy of a time slot T s (typically 13 × 10 − 6 s). Con sidering that a safety messag e pac ket is typically 2 00-30 0 Bytes in size at the physical layer [1 6], [26], th e commu nication ov erh e ad is thus mer ely 1% − 2% of the p a cket size. Regarding the computa tio n overhead , despite the fact that tracking the offset information of surroun ding vehicles appears to be a non-negligible computatio n load, it is important to note that safety applications generally and naturally rely on real-time extraction and pr ocessing o f th e status infor m ation from all received messages, which typic a lly yields comp licated calculation s (e.g. , trajecto ry pred iction). Th erefore, the co mputation load of estimating real-tim e contention inten sity , wh ich is mostly just coun ting th e number of received m essages, can be rea so nably considere d as in significant for the applicatio n layer compa red to the co mputation load ne c essary to sup port safety application s. Note that the pro posed design exploits informa tion fr om oth e r vehicles and impleme n ts coord ination in a one- hop scop e. Specifically , each vehicle extracts th e offset in formation of other vehic les wh ich are one-h op a p art and accesses the channe l based on estimating the instantaneou s co ntention intensity within one hop. Therefore, the design is no t targeted at add ressing the hidden terminal pr oblem, wh ich inv olves vehicles tw o hops apart fr om each other, but to inh erit the d istributed nature an d the low overhead of 802.1 1p while imp roving its perfor mance. Nev ertheless, it is po ssible to b uild on the pr oposed d e sign to mitiga te the hidden ter m inal problem. Howev er, implementin g inf ormation exchang e and coord in ation within a two-hop scope will inevitably in c rease the overhead of th e d esign. September 10, 2019 DRAFT 8 T ABLE II: List o f Symb ols λ the frequency of safety message broadcast σ i the random offset of vehicle i , σ i ∈ (0 , 1 /λ ] N number of vehicl es within communicatio n range M the CIDC protocol paramete r T s the duration of an idle time slot T Tx the duration of a packet transmission T DIFS the duration of a DIFS K ( T Tx + T DIFS )/ T s k [ s ] the s th mini-slot of slot k c ( k ) the contention intensity at the beginni ng of slot k h ( k ) indica tor , h ( k ) is 1(0) if slot k is busy (idle) e ( k [ s ]) initia l back-of f counter of a packet arrivi ng in k [ s ] n I ( k ) number of packet arri val s in slot k n o ( k ) number of pack et transmissions in slot k b max ( k ) the maximum back-off counter as slot k begins e v ( k [ s ]) the virtual entry point in slot k [ s ] υ ( k [ s ] ) the packet -to-slot ratio as mini-slot k [ s ] ends υ s the expected number of pack ets in a busy slot N sat the number of users at saturation point c s the expect ed c ( k ) in a steady state P col the collision probabil ity P UB col the upper bound of the collision probability P c k (0) the probability that c ( k ) = 0 d o the expect ed overa ll delay d c the expect ed contention delay C. CIDC: th e F ormulation In order to f ormulate the system model, the fo llowing definitions and deno tations are introd uced first. A list of symbols used in this pap er is given in T able II. Slot and mini-slot : A slot is the du ration in which the b ack-off counter of a p acket r e mains un changed . A mini- slot is a time d uration with the leng th o f T s . If th e ch annel is id le, a slot co nsists of on e mini-slot. Other wise, a slot has K mini-slots. The s th m ini-slot in slot k is deno ted as k [ s ] , and the set o f indexes of all mini-slo ts in slot k is d enoted as S k . Accor dingly , S k = { 1 } if slot k is idle, and S k = { 1 , . . . , K } if slot k is busy . Absolute and relative slot ind ex : The absolute slot index is an ind ex with respect to the beginnin g of the pro tocol execution. The relati ve slot in d ex is an index with respect to the curr e nt ab solute index. For example, the k in Figs. 2 a and 2b is an ab solute index while the 1 , 2 . . . a fter the “ + ” are the re lative slot in d exes and translate to k + 1 , k + 2 , . . . in absolute slot index. September 10, 2019 DRAFT 9 Denote the n umber of packets co ntending f or channel access measur e d a t the be ginn ing of slot k as c ( k ) . Le t h ( k ) = 1 and h ( k ) = 0 repr esent the events that slot k is busy and idle, r espectively . The in itial back -off coun ter of a p acket arr i ving at mini-slot k [ s ] , wh ic h depend s on the in stantaneous contentio n intensity , is deno te d as e ( k [ s ]) and refe r red to as the entry p oint o f this packet. Denote the numb er of pa ckets arrived in a m in i-slot k [ s ] m easured at the end o f the mini-slot and the numbe r of packets arrived in slot k me asured at th e end of the slot as n I ( k [ s ]) and n I ( k ) , respectively . Denote th e number of p ackets with their back -off co unter reduced to 0 in slot k as n o ( k ) . Note that h ( k ) = 1 if and only if n o ( k ) > 0 . The system implemen ting the CIDC is governed b y the following rules: c ( k + 1) = c ( k ) + X l ∈S k n I ( k [ l ]) − n o ( k ) (1a) e ( k [ s ]) = M c ( k ) + s X l =1 ,l ∈S k n I ( k [ l ]) , if n I ( k [ s ]) > 0 (1b) h ( k + e ( k [ s ])) = 1 , if n I ( k [ s ]) > 0 (1c) n o ( k + e ( k [ s ])) ← n o ( k + e ( k [ s ])) + 1 , if n I ( k [ s ]) > 0 (1d ) where ← denotes th e o p eration that assigns th e value of the expression on the rig ht-hand side to the variable o n the left-hand side. Equation (1a) c haracterizes th e change in th e contention in tensity af ter a slo t. Equ ation (1 b) char acterizes th e propo sed initial back-o ff cou nter selection r u le based on the c ontention intensity . Eq uations (1c) and (1d) reflect the c o nsequenc e of the b ack-off c o unter selectio n o n the system status at a futu re time instant, i.e., the chann el will be busy after e ( k [ s ]) slots and on e mo re p acket will b e sent in the co rrespon d ing slot. No te that h ( k ) and n o ( k ) shou ld be set to 0 for all k at initialization. In add ition, e ( k [ s ]) is only defined for the mini-slots with p acket arriv als. The event that mor e than one packet arrives in a mini-slot (i.e., 13 µ s) is neglected as the prob ability of such an event is extremely small. Correspon d ingly , n I ( k [ s ]) is equal to either zero or one. Another variable o f interest is the maximum back -off coun ter among all conte n ding packets me a sured at the be ginn ing o f slot k , deno ted as b max ( k ) . The maximu m bac k -off coun ter is governed by th e following rule: b max ( k + 1) = max b max ( k ) − 1 , 0 , if P l ∈S k n I ( k [ l ]) = 0 max max l ∈S k { e ( k [ l ]) } , b max ( k ) − 1 , else (2) From the equ ations ( 1) and (2), it can be seen th a t the initial back-off coun ter selection based o n the conten tion intensity in the CIDC has a significant imp act o n the system model. First, as sh own by eq uations (1a) an d ( 1b), the initial back -off counter of a packet arriving at slot k is no lon g er ran dom and in depend ently d ecided. In stead, it is deterministic an d decid ed b y the sy stem states throug h c ( k ) and n I ( k [ l ]) , ∀ l ∈ S k . This introdu ces a stro ng coupling amon g the b a ck-off co unters of contend ing packets at different veh icles. Seco nd, a s shown by eq uations (1c) an d (1d), th e imp act of the pr o posed initial b ack-off cou nter selection extend s, ag ain deterministically ra th er than rand o mly , to a fu tu re slot. Therefo re, the system state at any given instant is d ependen t on the system states and events at many previous instants (possibly infinitely m any p revious instan ts dep ending on the chann el lo ad). September 10, 2019 DRAFT 10 k +M ! M M M e ( k [ s ]) if c ( k [ s ]) = 3 if c ( k [ s ]) = 2 if c ( k [ s ]) = 1 if c ( k [ s ]) = 0 (a) Collision can only happen at slot k + xM , where x ∈ { 2 , 3 , . . . } . k 1 +1 +6 !$ !% !& !' +9 e 3 b 1 b 2 b 2 b 3 b 3 e 4 b 3 e 5 k 2 +1 +6 +2 +3 +7 +8 +9 k 3 +1 +6 +2 +3 +7 +8 +9 k 4 +1 +6 +2 +3 +7 +8 +9 b 4 Busy slot Idle slot Entry point Collision slot ( ii ) : S lot k 2 = k 1 + 2 ⇒ 2 slots after ( i ) ( i ) : Sl ot k 1 ( iv ) : Slot k 4 = k 3 + 4 ⇒ 7 slots after ( i ) ( iii ) : Slot k 3 = k 2 + 1 ⇒ 3 slots after ( i ) t (b) Collision can happen when c ( k ) has been reducing. Fig. 3: Illustra tion of the two basic featu res of the CIDC. The above co upling am ong the back -off counters at d ifferent vehicles and among the e vents acro ss the time domain cannot be char acterized by the classic packet-perspective Markov chain based modeling. Next, we will analyze the system perf ormance fr om a n e twork -perspective based on the concep ts of packet-to- slot ratio and contention intensity . I V . P E R F O R M A N C E A N A L Y S I S A. Ba sic F ea tur es The p roposed CIDC has two intu iti ve featu res. First, a packet collision can o n ly hap p en at cer tain slots. Specifically , since a packet ar riving at mini-slot k [ s ] sets its initial back -off coun ter based o n e ( k [ s ]) in (1b), a c o llision with existing packets can only ha p pen at slots k + 2 M , k + 3 M , . . . . This is illustrated in Fig . 3a, wher e c ( k [ s ]) = e ( k [ s ]) / M . Second, a packet collision can only h appen when th ere has been a dec rease in the co ntention inten sity c ( k ) . If the numbe r of p ackets contend ing f or ch a nnel access is constant o r stead ily incre asing, a collision cannot ha p pen. This is illustrated in Fig. 3b. In th is figu re, M = 3 , b i represents the back- off counter of the i th c ontendin g pac ket at the curren t in stant, and e i represents the initial b ack-off co unter of the i th contending p a c ket ar riving a t the September 10, 2019 DRAFT 11 current slot. At Step ( i ) , as there are two existing p a c kets w ith r emaining back- off cou nters at b 1 = 0 a n d b 2 = 2 , respectively , th e initial ba c k -off c o unter of the arriving new packet, deno ted by e 3 , is set to 9. At Step ( ii ), i.e., two slots after Step ( i ), the p acket co r respond in g to the back- o ff coun ter b 1 has been transmitted , an d the packet with the back-o ff co u nter b 2 is transmitting as b 2 has redu ced to 0. The rem aining back-off coun ter of the packet with the initial b ack-off cou nter e 3 , den oted by b 3 , is at 7. After ano ther slo t, i.e., at Step ( iii ) , a new packet arr i ves and sets its in itial bac k-off co unter e 4 to 6 sinc e ther e is only one existing p acket contend ing f or the channel access. Unfortu n ately , the back-off cou nter of the existing packet, i.e. , b 3 , also decreases to 6 at this slot. This causes a collision that will hap pen in 6 slots. At Step ( iv ), ano ther pac ket ar r i ves an d sets its in itial back-off cou nter e 5 to 9. It can be o bserved th a t th e co ntention intensity has b een decreasing from Steps ( i ) till before Step ( i ii ), which rend e rs the packet collision po ssible. By contrast, the co ntention inten sity in creases between Step ( iii ) and Step ( iv ), and thus the n ew packet arriving at Step ( iv ) d oes not en counter a collision. Next, we will characterize th e system given by ( 1) in detail. B. P acket-to-Slot Ratio As a network-pe rspectiv e parame ter , th e packet-to -slot ratio is introduced here to rep resent the number of simultaneou sly con tending pa c kets over the num ber of slots that accom m odate th e back-o ff counters of these contend in g packets. In the ca se of the 802.1 1p MAC, the p a cket-to-slot ratio can be simply d efined as th e n umber of p ackets in the fixed range [0 , W − 1] divided by W , where W is the c o ntention win dow . In the CIDC, there is no co ntention win dow and both the n umber o f packets a nd the r a nge of their back- off counters vary over time. In o rder to char acterize th e rang e of the back-off co unters, we intro duce the vir tual entry po int e v ( k [ s ]) f or any mini-slot d efined as: e v ( k [ s ]) = M c ( k ) + 1 , if h ( k ) = 0 M c ( k ) + s − 1 P l =1 ,l ∈S k n I ( k [ l ]) + 1 , else (3) Note that e v ( k [ s ]) is the en try point if a packet were to arrive at min i-slot k s and thus is defined for any k [ s ] ( By contrast, e ( k [ s ]) is o n ly defin ed for a k [ s ] if n I ( k [ s ]) > 0 ). The p acket-to-slot ratio, measured at th e en d of a mini-slot k [ s ] , is th en defin ed as follows: υ ( k [ s ]) = c ( k ) + s P l =1 ,l ∈S k n I ( k [ l ]) max { b max ( k ) , e v ( k [ s ]) } . (4) The above d efinition charac te r izes the average number o f p ackets per slot, which de p ends on N and λ . While the p rotocol param eter M is also expected to h av e an impac t on the packet-to- slot ratio , such imp act is not straightfor ward b ased on the equatio n (4). The fo llowing lemma shows that th e impact of M becomes evident as the system app roaches satura tio n. Lemma 1 : Th e packet-to- slot r atio υ ( k [ s ]) is bou n ded by 1 / M in the CIDC. Pr o of : See Section A in Ap p endix. Lemma 1 sh ows that th e packet-to- slo t ratio υ ( k [ s ]) saturate s at 1 / M f or the CIDC. Wh e n the c h annel load is small, υ ( k [ s ]) is determine d by the numb er of vehicles N , m essage frequen cy λ , etc. wh ile the par ameter M does September 10, 2019 DRAFT 12 not h av e a significa n t impact. A s the ch annel load increases, the impact of M on the packet-to -slot ratio b e comes more significant. This feature has a significant im pact o n the collision pr obability o f the CIDC an d will b e discussed in detail in Sub section IV -D. It can be sh own that the 1 / M busy ratio is a boun d that can n ot be achieved. Giv en M , N , and λ , the expected value of υ ( k [ s ]) in a steady state 3 , den oted as υ s , is given b y the fo llowing lemma . Lemma 2 : Given M , N , an d λ , th e expected p acket-to-slot ratio in a steady state is given b y: υ s = 1 1 − P ck (0) λN T s n s − λN ( K − 1 ) T s . (5) where P ck (0) d enotes th e pro bability of c ( k ) being 0 an d n s is the exp ected numb er of packets in a busy slot, i. e ., the expected value of n o ( k ) in the e q uation (1 a). Pr o of : See Section B in Appendix . Note that the imp act of M on υ s is man ifested th r ough n s . Based o n Lemm a 2, the numb er of vehicles N that leads to saturatio n satisfies N sat = n s λ ( M 1 − P ck (0) + K − 1 ) T s . (6) At saturation, as P ck (0) becomes very small, an app roximation of the above c a n be obtained by setting P ck (0) = 0 . The expected num ber of packets per busy slot, i.e., n s , is greater tha n 1 d ue to the p robability of packet collision. Specifically , it is conn ected to the p robability that l pac kets co llide in on e slot, deno ted as P l col , throu gh the following equation n s = 1 + X l ( l − 1 ) P l col . (7) Neglecting th e cases in which more than two packets collide, P col becomes P 2 col and the above equ ation reduces to n s = 1 + P col . (8) C. Contention I ntensity an d Contention Delay While the packet-to- slot ratio υ ( k [ s ]) can b e an indicator of the ch annel load , a fu ll characterizatio n of the system perfor mance re quires add itional metrics. For examp le, th e con tention d e la y of a packet dep ends on the exact num ber of p ackets contend ing f or ch a nnel acc e ss, i.e., the contention intensity c ( k ) . The conten tio n inten sity can be c haracterized by the one-slot pr obability transition matrix o f c ( k ) . Sp ecifically , giv en c ( k ) , the f o llowing cases of c ( k + 1) are possible: i the k th slot is busy an d there is n α ( k ) arriv als in the slot k , th en c ( k + 1) = c ( k ) + n α ( k ) − n o ( k ) i the k th slot is busy an d there is no ar riv al in the slot k , then c ( k + 1) = c ( k ) − n o ( k ) iii the k th slot is idle and there is n β ( k ) ar riv als in the slo t k , c ( k + 1) = c ( k ) + n β ( k ) iv the k th slo t is idle and there is n o arrival in the slot k , c ( k + 1) = c ( k ) . 3 The term steady state refers to the state when 1) the system is not over- saturated (an increa sing number of pack ets at the vehicles are expired by subsequent ne w pack ets in an ove r-saturat ed system); and 2) the protocol has been execu ted for a sufficie ntly long time with the fi xed N , λ , and M . September 10, 2019 DRAFT 13 Consider the event that c ( k ) = j packets in slot k and c ( k + 1) = i packets in slot k + 1 . Denote the pr obabilities o f such a n event given that slot k is idle and busy as P I k +1 ,k ( i, j ) and P B k +1 ,k ( i, j ) , respectively . Neglect the pr obability of more than 1 packet arriving in the same mini-slot. Then, P I k +1 ,k ( i, j ) a n d P B k +1 ,k ( i, j ) with i, j ∈ { 1 , . . . , N } are given by P I k +1 ,k ( i, j ) = 0 , if i < j P I ( i − j ) , els e (9) and P B k +1 ,k ( i, j ) = 0 , if i < j − 2 P col P B (0) , if i = j − 2 P col P B ( i − j + 2) + (1 − P col ) P B ( i − j + 1) , else (10) where P I ( x ) = N x ( λT s ) x (1 − λT s ) N − x , (11a) P B ( x ) = N x ( λK T s ) x (1 − λK T s ) N − x . (11b) Since a slot is busy with pro bability υ s , the overall one-slo t prob ability tra nsition ma tr ix of c ( k ) is given by P k +1 ,k = (1 − υ s ) P I k +1 ,k ( i, j ) + υ s P B k +1 ,k ( i, j ) i,j (12) Denote p c s = [ P ( c (0)) , . . . , P ( c ( N ))] T as th e vector of the stead y -state pro bability of c ( k ) , k = 0 , . . . , N . Then p c s satisfies ( P k +1 ,k − I ) p c s = 0 (13) Therefo re, p c s is in the null space of P k +1 ,k − I . The expected co ntention inten sity over all slots, i.e. , the expected c ( k ) de noted as c s , and its relatio n with th e av erage p acket delay given N , λ , and M are g iv en by the following theor em. Theorem 1 : The average contentio n in tensity c s and the average overall pa cket d elay d o of the CIDC c a n b e solved fro m the following equ ations: d o = c s + 1 − 1 − P c k (0) 2 K T s + M ( c s + 1) − c s T s (14a) N λd o = c s (14b) P c k (0) = 1 − c s N N . (14c) Pr o of : See Section C in Appendix . The overall packet d elay d o is the time dur ation between the in stant that a packet arrives an d th e instant that the packet transmission comp letes. T he contention delay d c is the time duration between th e in stant that a pa cket arrives and the instant that the p acket transmission begins. Th e relation betwee n the two delay metr ics is given b y: d c = d o − K T s + T DIFS . ( 15) September 10, 2019 DRAFT 14 Theorem 1 ch aracterizes th e relation between the expected overall delay d o , the expected nu mber of conten ding packets c s , and the probab ility of no packet conten ding fo r chann el access P c k (0) . In or d er to ob tain furthe r insigh t, approx imations f or c s in the cases of a small N and a large N can be derived, resp ecti vely . Lemma 3 : T h e sma ll- N and large- N ap proxima tions of the expect numb er of contend ing packets c s , deno ted as c L s and c H s , respectively , can be given as follows: c L s = N λ ( K + M ) T s 1 − N λ ( K + M − 1) T s (16a) c H s = N λ ( K/ 2 + M ) T s 1 − N λ ( K + M − 1) T s (16b) Pr o of : See Section D in Ap p endix. The delay in 802 .11p can be ob tained similar ly f or a comp arison. In fact, the overall delay in 8 02.11 p can be solved from (1 4a)-(14c) by substituting M ( c s + 1) with W / 2 where W is the co ntention window . T herefor e, with a p roper choice of M , the CIDC shou ld have a smaller delay than that in 8 02.11 p when c s , o r ultimately N and λ , is n ot too large. This will be verified in Section V Simulations. It should be noted that Theorem 1 hold s un der the assum p tion that the co llision prob ability is not so high th at it h as a significan t impact on the average delay . If the system is beyo nd satur ation, Theo rem 1 does not a pply . D. Collision Con ditions and Pr obability In this section, the instantan eous collision pro bability is analyz e d first. Th e n, the upp er bo und on the collision probab ility is der i ved in a closed fo rm. Consider the ev ent that packet B , which arrives at the mini-slot k 2 [ s 2 ] , collides with p acket A , which arrives a t mini-slot k 1 [ s 1 ] , wh ere k 1 < k 2 . L e t α = k 2 − k 1 . Supp o se there are β b usy slots in the in terval [ k 1 [ s 1 ] , k 2 [ s 2 ]) , in which τ packets ar e transmitted . Denote the number of p a cket arriv al in the interval [ k 1 [ s 1 ] , k 2 [ s 2 ]] as η . Lemma 4 : Packets A and B can co llide if and only if M ( τ − η ) = α. (17) Pr o of : See Section E in Ap pendix. Based on Lemma 4, if the gap between the arrival slot ind ex of the two p ackets is no t a multiple of M , the two packets have no chanc e to collide. Moreover , wheth e r a c ollision can happen o r not in the CIDC d epends on b oth the time instant of the arriv al and the numb er of recent transmission and arr i val events, as sugg e sted b y (1 7). The result is tha t co llision can happe n only at specific slots and under spe cific co nditions. Lemma 4 verifies the afo remention ed fea tu re that a dur ation with more tran smissions th an arriv als is necessary for a co llision to hap pen (as shown in Fig. 3b). Moreover , as th e g ap α increa ses, a larger difference b etween th e number of transmission a n d a rriv al events, i.e., a larger τ − η , is req uired for the collision to hap p en acco r ding to (17). Conside r ing the fact that the av erage pac ket transmission ra te and packet arriv al rate sho uld be equ al as long as the system is not beyond satur ation, a smaller collision pr o bability is implied for packets with a larger g ap between th eir arrival slot in dexes. This sug gests that the CIDC effecti vely limits th e collision range . By con tr ast, any two con tending packets can collide in th e case of 802.1 1 p MAC. September 10, 2019 DRAFT 15 The above insight reveals the difference in the u nderlyin g causes o f a p acket collision in the 80 2.11p and the CIDC. In the 80 2.11p , a packet collision is caused b y accommo dating contend in g packets in a fixed conten tion window . Co n sequently , the numbe r o f vehicles N h as a direct an d definitive imp act on the co llision pro bability . By contr a st, the cause of a p acket collision in the CIDC is th e uneven inter vals between successi ve packet arr i val instants in the random packet arr iv a l process. This unev enness b ecomes a limiting factor in the coordina tio n of packet tran smissions in a distributed app roach. The im pact of the n umber of vehic le s is no t d efinitiv e. For instance , a collision w ill not hap pen, r egardless of N , if the nu mber o f conten ding packets steadily increases. Howe ver , a larger N gen erally in creases the proba bility that co ndition (17) is satisfied and therefore leads to a larger co llision probab ility . A p acket can be inv olved in a co llision in two scenar io s. The first scenario is when the packet collid e s with an existing c o ntending packet upon its arriv al, referred to as for ward packet collision (e.g ., the pac ket cor r espondin g to e 4 in Step ( iii ) of Fig. 3b). The second scena rio is wh en th e pac ket is inv olved in a collision with a packet arriving after it durin g its back- off, referr ed to as a backward p acket collision (e. g., the packet corresp o nding to b 3 in Step ( ii i ) of Fig . 3b). Since a for ward p acket collision for one p acket must be a back ward c ollision fo r ano ther, the proba b ility of either type of co llision is iden tical. Consider a forward c ollision o f pa c ket B with packet A in th e example pre ceding Lemma 4 but with out assuming packet B ’ s ar r i val at a specific slot. Define c 1 = c ( k 1 ) + P l ≤ s 1 n I ( k 1 [ l ]) . The set of α so that p acket B can for ward- collide with packet A is { M , 2 M , . . . , ( c 1 − 2 ) M } . If p acket B arr i ves less than M slots after packet A arrives, th e condition (17) cann ot b e satisfied. If packet B arrives m ore than ( c 1 − 2) M slo ts after p acket A ar r iv es, th e back-o ff counter of packet A red uces to less than 2 M and collision c a nnot h appen either (subm itting α > ( c 1 − 2) M into (17) lead s to the r esult τ − η > c 1 − 1 , whic h can not b e satisfied.). For a g iv en α an d a g i ven c 1 , a fo rward co llision happen s when: 1) packet B ar riv es; and 2) the co ndition (17) is satisfied. Denote the p robability th at i packets are transmitted and j packets arrive in the α slots as P α T , A ( i, j ) . The for ward-collision pro bability given α and c 1 can be written as fo llows : P α,c 1 col ( τ , η ) = P k 2 A c ′ 1 X τ = α M P α T , A ( τ , τ − α M ) , (18) where c ′ 1 = c 1 − 2 and P k 2 A represents the pr obability of at lea st one arriv al ev ent occurr ing in slot k 2 . In eq uation (18), P k 2 A depend s on whether slot k 2 is busy o r no t. T he pr obability P α T , A ( τ , τ − α/ M ) d epends on two r andom pr ocesses, i.e., th e packet arriv al and tr a n smission pro cesses. The transmission p rocess is d ependen t on th e arriv al proce ss and can be considere d as the outpu t o f the ar riv al p rocess af te r go ing th rough the conten tion mechanism. The outpu t of an rand om process go ing throug h a gen eral nonlin ear system can be intr a ctable. Howe ver, despite the d ependen ce between the two p rocesses, the fo llowing two prop erties can be used to derive the p robability in (1 8). Fir st, excep t for r are cases, the number of transmissions in the α slots is d ecided by the n umber of ar r i vals in a non -overlapping duration . Due to the indep e n dent incremen t prope rty of the ran dom arriv al process, the numb er of tra n smissions and arrivals in the α slots c an be co n sidered as indep endent, i.e. , P α T , A ( τ , τ − α M ) = P α T ( τ ) P α A ( τ − α M ) (19) September 10, 2019 DRAFT 16 where P α T ( i ) and P α A ( j ) de n ote th e prob abilities that i p a c kets are transmitted an d that j pac kets arrive in the α slots, respectively . Secon d, the average packet transmission rate must be e qual to N λ u nless the sy stem is in a state beyo n d saturation . Based on the above, the probab ility P α T ( τ ) can be obtained b ased on an appro p riate approx imated p rocess. Define β = α/ M . The overall collision p robability is P col = 2 N X c ′ 1 =1 P ( c ′ 1 ) c ′ 1 X β =1 P α,c 1 col ( τ , η ) , (20) where P ( c ′ 1 ) can be foun d from the steady state pr o bability distribution o f c ( k ) , i.e., p c s in (13). In (20), th e summation over c ′ 1 starting f rom 1 is equ ivalent to a summation over c 1 starting f rom 3 as it can be shown that n o packet can for ward-collide with p acket A if the initial back-off counter o f packet A is M or 2 M , co rrespond ing to c 1 = 1 a n d c 1 = 2 , respectively . Note that th e equatio ns (5), (8), (13), and (2 0) fo rm a co mplete set of eq uations to find a so lu tion for υ s , n s , P col , an d p c s . A solutio n can be fo und numerica lly . However , as a nu meric solution only pr ovides lim ited insight, the following up per bou n d on the av erag e c o llision pr o bability in the CIDC is der i ved. Theorem 2 : Th e average collision pro bability of the CIDC, assuming th at the system is n ot beyon d saturation, is up per-bounded by P UB col = ( a 1 + 1 + b K − 1 ) 2 4 + b 1 ( a K − a 1 ) 1 − P c k (0) − ( a 1 + 1) b K − 1 1 2 + a 1 + 1 + b K − 1 2 − 1 (21) where P c k (0) c a n be fo und from equation s (1 4a)-(14c), b 1 = λN T s , b K − 1 = λN ( K − 1) T s , and a 1 = (1 − P c k (0))(1 − (1 − λT s ) N ) (22a) a K = (1 − P c k (0))(1 − (1 − λK T s ) N ) . (22b) Pr o of : See Section F in Append ix. V . S I M U L A T I O N S In this section , the pe rforman ce of the CIDC is demonstra te d and compar e d with b oth th e analytical results a n d the pe rforman ce o f the 8 02.11 p . First, th e collision pro bability and co n tention delay are simulated assuming an accurate e stimation of conten tio n intensity . Then, the ana lytical results are co mpared to the n umerical results. At last, the per forman ce is simu lated with erro rs in the estimated contentio n intensity cau sed b y factor s such as the vehicle mob ility . The f ollowing g eneral par ameter setting is used : the safety message bro adcast frequ ency λ is 10 Hz; the length of a DIFS T DIFS is 58 µ s; and the len g th of a time slot T s is 1 3 µ s. T wo pa cket transmission d urations are conside red: T Tx = 254 µ s ( K = 24 ) and T Tx = 332 µ s ( K = 30 ). Assuming a transmission data rate of 6Mb /s, these two transmission du r ations corresp ond to a physical-lay e r packet leng th of 190 Bytes an d 25 0 Bytes, respe c ti vely . The protoco l p arameter M is set to 2 in all simu lations. September 10, 2019 DRAFT 17 0 50 100 150 200 250 0 0.02 0.04 0.06 0.08 0.1 0.12 0.14 0.16 N Collisio n Probability Collisio n Probability v.s. Num ber of V ehicle s (T x = 2 54 µ s) Proposed 802.11p, W = 32 802.11p, W = 64 802.11p, W = 128 (a) Collisio n probability versus N ave raged ov er 10 rounds, T Tx = 254 µ s ( K = 24 ). 0 50 100 150 200 250 0 0.05 0.1 0.15 0.2 0.25 N Collisio n Probability Collisio n Probability v.s. Num ber of Veh ic les (Tx = 3 32 µ s) Proposed 802.11p, W = 32 802.11p, W = 64 802.11p, W = 128 (b) Collision probability versus N av eraged over 10 rounds, T Tx = 332 µ s ( K = 30 ). Fig. 4: Collision pr obability versus nu mber of vehicles un der two different p acket transmission tim e d urations. 0 50 100 150 200 250 0 0.5 1 1.5 2 2.5 3 3.5 Delay v. s. Number o f V ehicl es (T x = 2 54 µ s) N Delay (ms) Proposed 802.11p, W = 32 802.11p, W = 64 802.11p, W = 128 (a) Delay versus N avera ged ov er 10 rounds, T Tx = 254 µ s ( K = 24 ). 0 50 100 150 200 250 0 2 4 6 8 10 12 N Delay (ms) Delay v. s. Number o f V ehicle s (T x = 3 32 µ s) Proposed 802.11p, W = 32 802.11p, W = 64 802.11p, W = 128 (b) Delay versus N ave raged over 10 rounds, T Tx = 332 µ s ( K = 30 ). Fig. 5: Delay versus nu mber of vehicles un der two different packet tran smission time duration s. A. P erformance with Accurate Contention Inten sity Estimation The first example demo nstrates the collision an d d elay per forman c e of the CIDC and th e co m parison with th e 802.1 1p MAC. The r esults are averaged over 1 0 simu lation ro unds with 160 message cycles used in each roun d . The n umber o f vehicles varies fr o m 25 to 250. Figs. 4a and 4 b demonstrate th e average collision probab ility versus N fo r T Tx = 2 5 4 µ s ( K = 24 ) and T Tx = 332 µ s ( K = 30 ), respectively . In each plot, the co llision pr o bability of the CIDC is comp ared with that of 8 0 2.11p MA C with c o ntention wind ows W = 3 2 , W = 6 4 , and W = 128 , re sp ectiv ely . Fro m th e two figures, it can be seen that the CIDC has a substantially lower c o llision pro bability th a n that of 80 2.11p , r egardless of the cho sen contention window W , especially when N is large. Figs. 5a and 5b demon strate th e av erage delay versus N fo r T Tx = 2 54 µ s an d T Tx = 3 32 µ s, r espectiv ely . I n eac h plot, the d elay of the CIDC is comp ared with that o f 802 .11p MAC with con te n tion win dows W = 32 , W = 64 , and W = 12 8 , r e spectiv ely . From Fig. 5a, it can be seen that the delay of the CIDC is smaller than that o f 802.1 1p September 10, 2019 DRAFT 18 0 50 100 150 200 250 0 2 4 6 8 10 12 Analytica l and Numerical Delay vers us N N Delay (ms ) Simu la tion, T x = 25 4 µ s Simu la tion, T x = 33 2 µ s Analytica l, Tx = 254 µ s Analytica l, Tx = 332 µ s Fig. 6: Comparison o f the analytical and numerical r esults on the av erag e conten tion d elay versus N . for all three con ten tion window sizes W and all N . From Fig. 5b, it c an be seen that th e d elay perf ormance of the CIDC is be tter at all poin ts except fo r th e c ases of very large N , i.e., N = 225 an d N = 2 50 . For N = 225 , the delay of the CIDC is larger than that of 802. 11p with W = 32 but smaller than that of 802 .11p with W = 64 or W = 12 8 . For N = 250 , the delay of the CIDC is th e largest because the system is saturated an d a n in creasing number of packets are con ten ding for c h annel access un der the CIDC. This reflec ts the fact that, compa r ed with the 802.1 1p, the pro posed design tra d es off d e lay fo r a smaller collision pr obability wh en N is very large. Nev ertheless, it is worth noting that th e c ase of a vehicle simu ltaneously exchangin g messag e s with 2 50 o ther vehicles would be an extreme case in eith e r an ur b an or a h ighway scenario. Comparing Figs. 4 and 5, it can be ob served that the CIDC h as a better perf ormance in terms of both collision probab ility and delay over a wide ra n ge of N at the c o st o f a smaller saturation threshold in terms o f N . Since th e advantage of the CIDC hold s f or a ll W in [ 3 2, 128], it follows that the co n tention in te n sity based MAC outpe r forms a d esign solely based on adapting th e c ontention window W of th e 8 02.11 p . B. A Comp arison of Analytica l a nd Numerica l Re sults The secon d example compar es th e analytical results on the conten tion de lay fro m T heorem 1 and the collision probab ility up per b o und from Theor em 2 with the num e r ical results. Fig. 6 d emonstrates the an alytical an d nu merical results on the average con tention delay d c versus N for T Tx = 254 µ s and T Tx = 332 µ s. I t c an be seen tha t the analytical results m atch th e numerica l results. Mo reover , the match is exact f or small and mediu m N while a small gap a p pears for large N . Th e r eason is that the an alytical resu lts in The orem 1 are for an unsatu rated scen ario while th e system approa c hes saturatio n as N in c r eases. For the c a se T Tx = 33 2 µ s, the sy stem is beyond satura tio n a t N = 25 0 an d a solu tion cannot be fo und b ased o n Theorem 1 anymore. Figs. 7 a and 7b dem onstrate the analy tica l uppe r bou nd of the co llision p robability a nd the n umerical result on the co llision prob ability versus N for T Tx = 2 54 µ s an d T Tx = 332 µ s, r espectively . Fro m the figures, it can be seen September 10, 2019 DRAFT 19 0 50 100 150 200 250 0 0.02 0.04 0.06 0.08 0.1 0.12 0.14 0.16 0.18 N Collisio n Probability Collisio n Probabiliti es and Analytical Upperboun d (T x = 25 4 µ s ) Proposed Upperbound (proposed) 802.11p, W = 32 802.11p, W = 64 802.11p, W = 128 (a) Simulated collision probabil ity and the analytica l uppe r bound versus N , T Tx = 254 µ s ( K = 24 ). 0 50 100 150 200 250 0 0.05 0.1 0.15 0.2 0.25 N Collisio n Probability Collisio n Probabiliti es and Analytical Upperboun d (T x = 33 2 µ s ) Proposed Upperbound (proposed) 802.11p, W = 32 802.11p, W = 64 802.11p, W = 128 (b) Simulated collision probability and the analyt ical upper bound versus N , T Tx = 332 µ s ( K = 30 ). Fig. 7: Comparison o f the analytical and numerical r esults on the collision pro bability versu s N . that the analy tica l up per bo unds ar e valid although not very tight when N is large. Nevertheless, ev en the up p er bound in each figu re lies b elow the collision p robability o f the 802 .11p MA C fo r any W in th e e ntire range of N . C. P erformanc e und er Con tention Inten sity Estimation Err o rs The third example demo nstrates the p erforman ce of the CIDC with estimation err ors. The accu rate estimation of the co n tention in tensity based on information exchan ge and processing c a n be an ideal case. In practice, the estimation can be sub jec t to e rrors du e to the vehicle mobility . Consider a two-d irectional h ighway and vehicles moving at a speed of 80 km/h on eac h side. Assume a comm unication r a nge o f 500m on both sides. Con sider the extreme (worst) case that all o ther vehicles ar e moving towards th e op posite d irection o f the target veh icle . The density of the vehicles on the othe r side of the high way is assumed to b e con stant. Th en, the percen ta g e of vehicles that leave an d en ter the com m unication range o f the ta rget veh icle is 0 . 89 % of N within a message cycle of 100 m s. According ly , in th is simulation example, we use a parame te r δ to represent that δ percen t o f the neigh b or vehicles has cha n ged in a message cycle. Instead o f 0.89 , which is a lr eady calculate d fr om an extreme case, we further increase δ to 1 and 3 to acco m modate a margin f or o ther po ssibilities of error s. In Fig. 8 a, the collision probab ility o f the CIDC with error s is co mpared to that of th e CIDC withou t any er ror and the 802. 1 1p MA C with W = 6 4 . It can be seen that intro ducing erro r in the estimation o f con tention inten sity increases the co llision pro bability . Howe ver, the perfo rmance is still b etter than 802 .11p MA C with W = 64 even for δ = 3 . T he collision prob ability of the CIDC with err or wh e n δ = 1 is m uch smaller th an that of the 802 .11p MA C. In Fig. 8b, the average con tention delay o f the CIDC with errors is com pared to that of the CIDC with o ut any error and th e 802.1 1p MA C with W = 6 4 . I t can b e seen that the impact of estima tio n error on the con te n tion delay is insignificant especially wh e n N is small. When N is large, an e stima tio n erro r slightly reduces the contentio n delay d ue to an increase in the co llision pr obability . September 10, 2019 DRAFT 20 0 50 100 150 200 250 0 0.02 0.04 0.06 0.08 0.1 0.12 N Collisio n Probability Collisio n Probability v.s. Num ber of Veh ic les (Tx = 2 54 µ s) Proposed, δ = 3 Proposed, δ = 1 Proposed, no error 802 .1 1p, W = 64 (a) Collision probabili ty versus N with and without error in content ion intensity estimation, T Tx = 254 µ s ( K = 24 ). 0 50 100 150 200 250 0 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 Delay v. s. Number o f V ehicl es (T x = 2 54 µ s) N Delay (ms) Proposed, δ = 3 Proposed, δ = 1 Proposed, no error 802 .1 1p, W = 64 (b) Delay v ersus N with an d without error in cont ention intensi ty estimation, T Tx = 254 µ s ( K = 24 ). Fig. 8: Collision pr obability and contentio n delay with and withou t error in contention inten sity estimation. V I . C O N C L U S I O N S In this work , we have p roposed a CIDC with applicatio n-layer an d MAC -layer designs to improve the per f ormance of safety message bro adcast in V2V commun ications. Ex ploiting the uniqu e features of the consider ed scenario , the de velopmen t of the CIDC is an exploration of the perfo rmance-overhead trade -off an d an effort to achie ve a significant perfo r mance improvement with an overhead as small as po ssible in th e scenario of safety message broadc a st. As a result, the CIDC, wh ich is distributed an d co m patible with 802.1 1p, sub stan tially impr oves the perfor mance of safety m essage broad cast at the co st of a small commun ication an d compu tation overhead ev en when errors are introdu ced in the conten tion intensity estimation. W ith the a bove fe a tu res, the CIDC is a p r omising candidate as eith e r a building block in a comp rehensive proto col for V2 V co mmunicatio n s o r a gen eral pro tocol that addresses p eriodical br o adcast in a distributed n etwork with a fixed or slow-v arying top ology . A P P E N D I X A. Pr oof of Lemma 1 If h ( k ) = 0 , it follows f rom (4) that υ ( k [ s ]) = c ( k ) + n I ( k [1]) max { b max ( k ) , e v ( k [ s ]) } ≤ c ( k ) + n I ( k [1]) e v ( k [ s ]) ≤ c ( k ) + 1 e v ( k [ s ]) = 1 M . (23) September 10, 2019 DRAFT 21 Otherwise ( h ( k ) = 1 ), it f ollows fr o m (4) that υ ( k [ s ]) = c ( k ) + s P l =1 ,l ∈S k n I ( k [ l ]) max { b max ( k ) , e v ( k [ s ]) } ≤ c ( k ) + s P l =1 ,l ∈S k n I ( k [ l ]) e v ( k [ s ]) ≤ c ( k ) + s − 1 P l = k 1 , ∈S k n I ( k [ l ]) + 1 e v ( k [ s ]) = 1 M . (24) This conclud e s the proo f of L emma 1 . B. Pr oof of Lemma 2 The expec ted change o f c ( k ) in one slot is E { ∆ c ( k ) } = λN T s , if h ( k ) = 0 λN K T s − n s , else . (25) The p robability o f a slot being id le ( i.e., h ( k ) = 0 ) a n d busy (i.e ., h ( k ) = 1 ) are given by P ( h ( k ) = 0) = P ck (0) + (1 − P ck (0))(1 − υ s ) (26a) P ( h ( k ) = 1) = (1 − P ck (0)) υ s , (26b) respectively . There f ore, it must h old th at ( P ck (0) + (1 − P ck (0))(1 − υ s )) λN T s +(1 − P ck (0)) υ s ( λN K T s − n s ) = 0 (27) in a stead y state, which leads to ( 5). C. Pr o of of Theorem 1 Giv en the initial back -off coun ter selection r u le (1b), i.e, e ( k [ s ]) = ( c ( k [ s ]) + 1) M , where c ( k [ s ]) = c ( k ) + s − 1 X l =1 ,l ∈S k n I ( k [ l ]) , (28) the expected e ntry p oint in a steady state is e s = N X j =0 P c k ( j )( j + 1) M = ( c s + 1) M (29) where P c k ( j ) = P ( c ( k [ s ]) = j ) . When there are c ( k [ s ]) = j > 1 existing p ackets, the av erage nu mber of transmissions a new packet endur es ( including its own) till the comp le tio n o f its own transmission is 1 + j − 1 / 2 , in September 10, 2019 DRAFT 22 which 1 re fers to its own tra n smission an d − 1 / 2 correspo nds to the fact that the first pa c ket is half-way transmitted on average u pon the arrival of the n ew packet. T h erefore, the delay of a p acket d ue to busy slots (transmission s) is d busy o = 1 + N X j =1 P c k ( j )( j − 1 2 ) K T s = 1 + c s − 1 2 (1 − P c k (0)) K T s . (30) Note that qu eue jumpin g, wh ich can b e viewed a s a switch of transmission order, does not have an impact on th e av erage nu m ber of transmission s a packet need s to wait for . Since the p acket en ters from ( c ( k [ s ]) + 1) M and ther e are c ( k [ s ]) busy slots, the av erage d elay d u e to the numb er of em pty slots is d empty o = ( c s + 1) M − c s T s . (31) The overall du r ation of contend ing f or ch a nnel access and transmission of a packet is then d o = d busy o + d empty o , (32) which lea ds to the equa tion (14a). In a steady state, d o ≤ 1 /λ where strict inequ ality ho lds if the system is not satur ated. As a packet a rriv es ev ery 1 / λ secon d s, the prob ability th at a vehicle h as a conte n ding packet is P con = d o / (1 /λ ) = λd o . Given this individual contend ing p robability , the expected nu mber of conten ding packets shou ld satisfy N P con = c s , (33) which lea ds to the equa tion (14b). Giv en P con , th e pr obability that no p acket is co n tending for channe l access is (1 − P con ) N . T h erefore, it mu st hold that P c k (0) = (1 − P con ) N . (34) Substituting P con from (33) in to (34) gives th e equ ation (14c). This completes the pr oof of Theor e m 1. D. Pr oof of Lemma 3 From ( 14a) to (1 4 c) in Theor em 1, c s must satisfy c s 1 − N λT s ( K + M − 1 ) = N λ K + M − K 2 1 − 1 − c s N N T s . (35) For a small N , (1 − c s / N ) N can b e a pprox im ated b y 1 an d it g i ves the result ( 16a). For a large N , (1 − c s / N ) N approa c h es 0 and it gives the result (16b). September 10, 2019 DRAFT 23 E. Pr oof of Lemma 4 Using (1 b), th e entry poin t f or pa c kets A and B are e A ( k 1 [ s 1 ]) = M c ( k 1 ) + s 1 X l =1 n I ( k 1 [ l ]) (36a) e B ( k 2 [ s 2 ]) = M c ( k 2 ) + s 2 X l =1 n I ( k 2 [ l ]) . ( 36b) The back-o ff co unter o f A decreases by α from slot k 1 to slot k 2 . There f ore, f o r p ackets A and B to collide, it must hold M c ( k 1 ) + s 1 X l =1 n I ( k 1 [ l ]) − α = M c ( k 2 ) + s 2 X l =1 n I ( k 2 [ l ]) (37) Based o n the nu mber of transmitted and ar riv ed pac kets, it h olds that c ( k 2 ) + s 2 X l =1 n I ( k 2 [ l ]) = c ( k 1 ) + s 1 X l =1 n I ( k 1 [ l ]) + η − τ . (38) Therefo re, pa ckets A and B co llide only if M ( τ − η ) = α . F . Pr oof of Theor em 2 Unlike the packet-per sp ecti ve collision analysis for 802.1 1p, the p roof for the propo sed mo del is based on a slot perspective. Consider an arbitrary slot k , a collision is determ ined (an d will happe n in a later slot) in this slot unde r the following nece ssary con d itions: i. there is at least on e c ontendin g packet, i.e., c ( k ) > 0 . ii. the vir tual entr y poin t at the c u rrent mini- slot e υ ( k [ s ]) c o rrespon ds to a busy slot, i.e., h ( e υ ( k [ s ])) = 1 . iii. there is a new pac ket arr i val in slot k , i.e., n I ( k ) > 0 . The p robabilities that the above c onditions ar e satisfied are given as fo llows i. 1 − P c k (0) ii. 0 whe n e υ ( k [ s ]) > b max ( k ) and υ s when e υ ( k [ s ]) < b max ( k ) . iii. 1 − (1 − λT s ) N if slot k is idle and 1 − (1 − λK T s ) N if slot k is busy . Therefo re, the pro bability that a co llision is d etermined in slot k (and w ill h appen in a later slot) is upper-boun ded by P s I = υ s (1 − P c k (0)) 1 − (1 − λT s ) N (39) in an idle slot and P s B = υ s (1 − P c k (0)) 1 − (1 − λK T s ) N (40) in a busy slot. Since th e pa c ket-to-slot ratio is υ s , ea c h packet correspo nds to 1 / υ s equiv alent exclu sive slots on av erage , with 1 busy slots and 1 /υ s − 1 idle slots. Th erefore, the collision p robab ility fo r a packet is u p per-bounded by P UB col = P s B + 1 υ s − 1 P s I = υ s ( a K − a 1 ) + a 1 . (41) September 10, 2019 DRAFT 24 Using the re sult (8), it holds that n s − 1 < υ s ( a K − a 1 ) + a 1 , (42) Substituting (5 ) into the above equation , it h olds that n s − 1 < a K − a 1 1 − P ck (0) λN T s n s − λN ( K − 1) T s + a 1 . (43) Solving the ab ove inequ ality and using ( 8) ag ain gives (21). R E F E R E N C E S [1] N. Lu, N. Cheng, N. Z hang, X. Shen, and J. W . Mark, “Connected V ehicles: Solutions and Challen ges, ” IE EE Internet Things J. , vol. 1, no. 4, pp. 289–299, Aug. 2014. [2] K. Koc kelman, et. al, “Implicat ions of Connecte d and Automated V ehicles on the Safety and Operations of Roadway Networ ks: A Final Report, ” T echnical Report, 2016. A vaila ble online at: https:// library .ctr .utexas.edu/ctr-publications/0-6849-1.pdf. [3] J. B. Ke nney , “Dedicate d S hort-Range Communicati ons (DSRC) Standards in the United States, ” Pr oc. IEE E , vol. 99, no. 7, pp. 1162–1182, July 2011. [4] B. Kloiber , J. H rri, T . Strang, S. Sand, and C. R. Garca,“Random Tran smit Power Control for DSRC and its Applicatio n to Cooperati ve Safety , ” IEEE T rans. Dependable Secur e Comput. , vol. 13, no. 1, pp. 18–31, Jan.–Feb ., 2016. [5] M. Hadded, P . Muhlethaler , A. Laouiti, R. Z agrouba, and L. A. Saidane, “TDMA-Based MA C Protocols for V ehicular Ad Hoc Network s: A Surve y , Qualita tiv e Analysis, and Open Research Issues, ” IEEE Commun. Surve ys T uts. , vol. 17, no. 4, pp. 2461–2492, Fourthquart er 2015. [6] Y . Bi, H. Zhou, W . Zhuang, and H. Zhao. Safety Message Broadcast in V ehicul ar Networks. Springer , 2016. [7] C. Campolo, A. V inel, A. Molinaro, and Y . Kouch eryavy , “Modeli ng Broadca sting in IEE E 802.11p/W A VE V ehicul ar Networks, ” IEEE Commun. Letters , vol. 15, no. 2, pp. 199–201, Feb . 2011. [8] C. Han, M. Dianati, R. T afazolli , R. Kernch en, X. Shen, “ Analytical Study of the IEEE 802.11p MA C Sublayer in V ehicula r Networks, ” IEEE T rans Intell. T ransp. Syst. , vol. 13, no. 2, pp. 873–886, June 2012. [9] X. Ma, J. Zhang, and T . W u, “Reli ability Analysis of One-Hop Safety-Critic al Broadcast Services in V ANE Ts, ” IEEE T rans. V eh. T echnol . , vol. 60, no. 8, pp. 3933–3946, Oct. 2011. [10] F . Y e, R. Y im, S. Roy , and J. Zhang, “Effici ency and Reliabilit y of One-Hop Broadcasting in V ehicul ar Ad Hoc Networks, ” IEEE J . Sel. Area s Commun. , vol. 29, no. 1, pp. 151–160, Jan. 2011. [11] Y . P . Fallah, C. L. Huang, R. Sengupta, and H. Krishnan, “ Analysis of Information Disseminati on in V ehicular Ad-Hoc Networks W ith Applica tion to Cooperati ve V ehicle Safety Systems, ” IEEE T rans. V eh. T echnol. , vol. 60, no. 1, pp. 233–247, Jan. 2011. [12] K. A. Hafeez, L. Zhao, B. Ma, and J. W . Mark, “Performance Analysis and Enhancemen t of the DSRC for V ANET’ s Safety Applications, ” IEEE T rans. V eh. T ech nol. , vol. 62, no. 7, pp. 3069–3083, Sept. 2013. [13] K. A. Hafeez, A. Anpalagan, and L. Zhao, “Optimizing the Control Channel Interv al of the DSRC for V ehicula r Safety Applications, ” IEEE T rans. V eh. T ech nol. , vol. 65, no. 5, pp. 3377–3388, May 2016. [14] X. Ma, J . Zhang, X. Y in, and K. S. Tri vedi, “Design and Analysis of a Robust Broadcast Scheme for V ANET Safety-Rela ted Services, ” IEEE T rans. V eh. T ech nol. , vol. 61, no. 1, pp. 46–61, Jan. 2012. [15] Y . W u, K. W . Shum, W . S. W ong, and L. Shen, “Safety-Message Broadcast in V ehicula r Ad Hoc Networks Based on Protocol Sequences, ” IEEE T rans. V eh. T ech nol. , vol. 63, no. 3, pp. 1467–1479, Mar . 2014. [16] Y . Park and H. Kim, “Collision Control of Periodic Safety Messages with Strict Messaging Frequency Requirement s, ” IEEE T rans. V eh. T echnol. , vol. 62, no. 2, pp. 843–852, Feb. 2013. [17] H. A. Omar , W . Zhuang, and L. Li, “V eMA C: A TDMA-Based MA C Protocol for Relia ble Broadcast in V ANETs, ” IEEE T rans. Mobile Comput. , vol. 12, no. 9, pp. 1724–1736, Sept. 2013. [18] F . L yu et al., “SS-MA C: A Nov el Time Slot-Sharing MAC for Safety Messages Broadcasting in V ANETs, ” IEE E T rans. V eh. T echnol . , vol. 67, no. 4, pp. 3586–3597, Apr . 2018. [19] S. Bharati and W . Zhuang, “CAH-MA C: Cooperati ve ADHOC MA C for V ehicular Networks, ” IEEE J. Sel. Areas Commun. , vol. 31, no. 9, pp. 470–479, Sept. 2013. September 10, 2019 DRAFT 25 [20] R. Z hang, X. Cheng, L . Y ang, X. Shen, and B. Jiao, “ A Nove l Central ized TDMA-Based Scheduling Protocol for V ehicular Networks, ” IEEE T rans Intell. T ransp. Syst. , vol. 16, no. 1, pp. 411–416, Feb . 2015. [21] K. H. Almotairi and X. Shen, “ A Distrib uted Multi-Cha nnel MA C Protocol for Ad Hoc Wire less Networks, ” IEEE Tr ans. Mobile Comput. , vol. 14, no. 1, pp. 1–13, Jan. 2015. [22] Q. Y e, W . Zhuang, L. L i, and P . V igneron, “Traf fic-Load-Adapti ve Medium Access Control for Fully Connect ed Mobile Ad Hoc Networks, ” IEEE T rans. V eh. T ech nol. , vol. 65, no. 11, pp. 9358–9371, Nov . 2016. [23] F . J. Mart´ ın-V ega , B. Soret, M. C. Aguayo-T orres, I. Z. Kovcs, and G. Gm ez, “Geolocation -Based Access for V ehicular Communications: Analysis and Optimizati on via Stochasti c Geometry , ” IE EE Tr ans. V eh. T echnol. , vol. 67, no. 4, pp. 3069–3084, Apr . 2018. [24] S. Bharati and W . Zhuang, “CRB: Cooperati ve Relay Broadcasti ng for Safety Applicatio ns in V ehicul ar N etworks, ” IEEE T rans. V eh. T echnol. , vol. 65, no. 12, pp. 9542–9553, Dec. 2016. [25] K. Xu, D. Tipper , Y . Qian, and P . Krishnamurthy , “Time- Dependent Performance Analysis of IEE E 802.11p V ehicul ar Networks, ” IE EE T rans. V eh. T echnol. , vol. 65, no. 7, pp. 5637-5651, July 2016. [26] D. Jiang, V . T aliw al, A. Meier , W . Holfelde r, and R. Herrtwich , “Design of 5.9Ghz DSRC-based V ehicula r Safety Communicatio n, ” IEEE W irele ss Commun. , vol. 13, no. 5, pp. 36–43, Oct. 2006. September 10, 2019 DRAFT
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment