Analise de Seguranc{c}a Baseada em Roles para Fabricas de Software
Most software factories contain applications with sensitive information that needs to be protected against breaches of confidentiality and integrity, which can have serious consequences. In the context of large factories with complex applications, it is not feasible to manually analyze accesses to sensitive information without some form of safety mechanisms. This article presents a static analysis technique for software factories, based on role-based security policies. We start by synthesising a graph representation of the relevant software factories, based on the security policy defined by the user. Later the graph model is analysed to find access information where the security policy is breached, ensuring that all possible execution states are analysed. A proof of concept of our technique has been developed for the analysis of OutSystems software factories. The security reports generated by the tool allows developers to find and prioritise security breaches in their factories. The prototype was evaluated using large software factories, with strong safety requirements. Several security flaws were found, some serious ones that would be hard to be detected without our analysis.
💡 Research Summary
The paper addresses the problem of ensuring role‑based access control (RBAC) compliance across large software factories, with a focus on OutSystems‑based low‑code applications. Manual inspection of every entry point, sub‑routine, and data entity is infeasible in factories that contain hundreds of screens, thousands of REST/SOAP services, and a complex web of role assignments. To solve this, the authors propose a static analysis technique that automatically detects violations of a user‑defined RBAC policy throughout the entire factory.
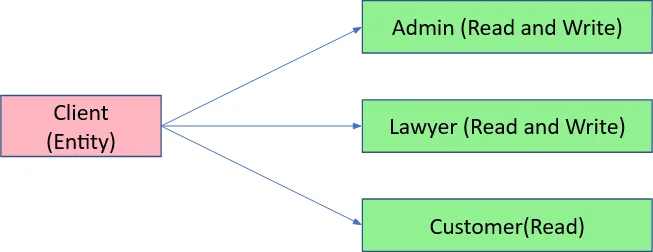
The approach consists of several stages. First, a security policy is supplied by the user, mapping each data entity (e.g., a database table) to two sets of roles: those allowed to read and those allowed to write. From this policy the tool synthesises a compact graph representation of the factory. The core of the representation is a call graph that captures all entry points (screens, REST endpoints, etc.), the sub‑routines they invoke, and the OutSystems primitive operations that manipulate roles (GrantRole, RevokeRole, CheckRole). The call graph also records every read/write operation on the entities.
In the initial pass the call graph is traversed with a depth‑first search to locate “potential breaches”: paths that lead from an entry point to a protected entity while the role set associated with the entry point does not contain any role authorized for that entity. Because the call graph alone lacks information about conditional role checks, many of these candidates may be false positives. To refine them, the algorithm expands each candidate path by inserting the control‑flow graph (CFG) of every sub‑routine involved. The combined graph now reflects the exact branching structure of role checks.
The final verification step performs a state‑based analysis on the expanded graph. A state records the current set of roles a user possesses and the set of roles permitted at the entry point. As the analysis walks through the CFG, it updates the state whenever GrantRole or RevokeRole is encountered and forks the state on each branch of a CheckRole conditional. When the traversal reaches a data‑entity node, the algorithm checks whether the current role set includes at least one of the roles authorized for the required operation (read or write). If not, a concrete security violation is reported. The method deliberately avoids redundant exploration by memoising already‑visited sub‑routine‑state pairs, which keeps the analysis tractable even for large factories.
The prototype was built specifically for the OutSystems platform, which provides a rich metadata API exposing screens, entities, roles, and the three RBAC primitives. The tool offers a web UI where developers define the policy, launch the analysis, and explore the results. The generated security report lists every entry point with violations, the exact call‑graph and CFG paths that lead to the breach, the sequence of role‑changing operations, and a risk score that helps prioritize remediation.
Empirical evaluation involved three factories. A small mock‑up representing a law‑firm management system was deliberately seeded with five security flaws; the tool detected all of them with zero false positives or negatives. A medium‑size client factory (≈30 modules, 200 screens, 200 entities, 35 roles) revealed numerous mis‑assigned roles that granted unauthorized access to sensitive entities. A large client factory (≈700 modules, >2 000 screens, >2 500 entities) exposed dozens of serious violations, including cases where non‑admin users could delete legal‑case records because a CheckRole guard was missing. Performance measurements showed that even for the largest factory the full analysis completed in roughly 12 minutes on an 8‑core machine, using 4–6 GB of RAM, which is acceptable for regular security‑gate checks.
The contributions of the work are: (1) a novel static analysis pipeline that combines call‑graph and control‑flow information to achieve precise RBAC violation detection across an entire software factory; (2) a concrete implementation for OutSystems that automates policy definition, analysis, and reporting; (3) empirical evidence that the technique scales to real‑world, large‑scale factories and uncovers security issues that would be extremely hard to find manually; (4) a discussion of future extensions, such as hybrid static‑dynamic analysis, support for attribute‑based policies, and adaptation to other low‑code platforms.
In summary, the paper demonstrates that systematic, graph‑based static analysis can effectively enforce role‑based security policies in complex, low‑code software factories, providing developers with actionable insights to harden their applications before deployment.
Comments & Academic Discussion
Loading comments...
Leave a Comment