Online Optimization of Wireless Powered Mobile-Edge Computing for Heterogeneous Industrial Internet of Things
A spurt of progress in wireless power transfer (WPT) and mobile edge computing (MEC) provides a promising approach for Industrial Internet of Things (IIoT) to enhance the quality and productivity of manufacturing. Scheduling in such a scenario is cha…
Authors: Hao Wu, Xinchen Lyu, Hui Tian
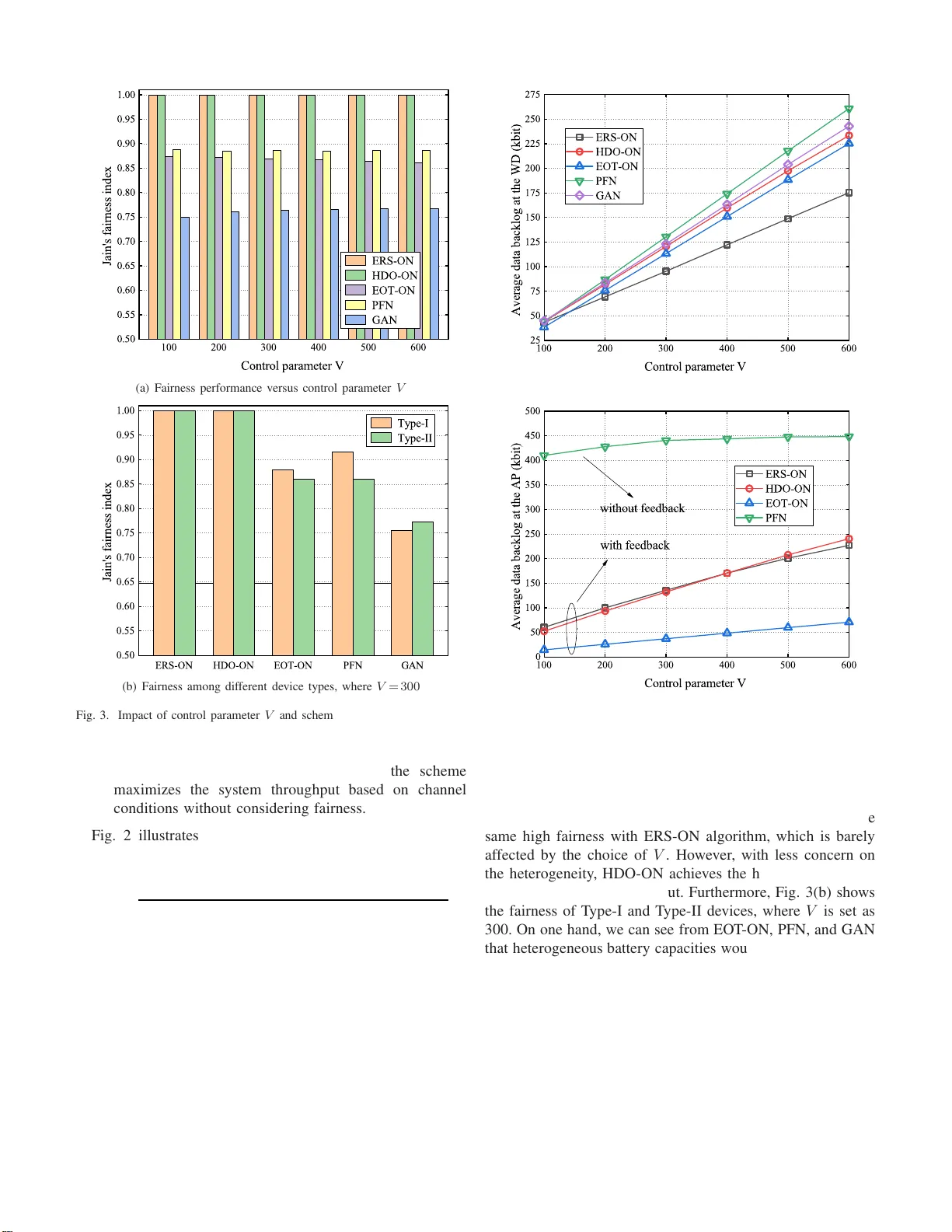
1 Online Optimizati on of W ireless Po wer ed Mobile-Edge Computing for Heterogeneous Industrial Internet of Things Hao W u 1 , Xinchen L yu 2 , and Hui T ian 1 1 State Key Laboratory of Networking and Switching T echnology , Beijing University of Po sts and T e lecommunications , Beijing, China, Email: wh94 0 5@bupt.edu.cn and tianhui@bupt.edu.cn. 2 National Enginee ring La boratory for Mobile Network T ec h nologies, Beijing Uni versity of Po sts and T e lecommunications , Beijing, China, Email: lvxinch e n@bupt.edu.cn. Abstract —A spurt of pro gress in wireless power trans- fer (WPT) and mobile edge computing (MEC) prov ides a promis- ing approach fo r Industrial Internet of Things (IIoT) to enhance the quality and productivity of manufacturing. Sched uling in such a scenario is challen gin g due to congested wireless chan nels, time-dependent energy constraints, complicated d evice hetero - geneity , a nd prohibitive signaling ov erheads. In this paper , we first p ropose an onl ine algo rithm, called energy-awar e resour ce scheduling (ERS), to maximize the system utili ty comprising throughput and fairness, with consideration on both system sustainability and stability . Based on L yapunov optimization and conv ex optimization techn iques, th e proposed algorithm achiev es asymptotic optimality for heterogeneous IIoT systems without p ri or knowledge of network state infor mation (NS I). Subsequen tly , we extend the ERS algorithm to a more re alistic scenario where the ov erhead and delay of NS I feedbacks are non- negligible. Th e optimal scheduling decisions of the scen ario are prov ided, and the optimality loss on system u tility under outdated NSI is analyzed. Simulations verify our theoretical claims and demonstrate the gains of our proposed ERS algorithm ov er alternativ e benchmark scheme s. Index T erms —Wireless po wer transfer , mobile edge computing, heterogeneous Industrial Internet of Things, outdated inform a- tion, L yapunov optimization. I . I N T R O D U C T I O N I NDUSTRIAL Internet of T h ings (IIoT) is regarded as a rev olutionary ap proach to o ptimize indu strial p roductio n processes and imp r ove econ o mic benefits [1]–[3]. Ubiquito us wireless d evices (WDs) in IIoT w ork as the sources to collect an enor mous amount of data from the amb ient en vironmen t. Analysis and extraction of th ose data can add value to the produ ction cycle, thu s imp roving the effi ciency and accuracy of m anufacturin g [4]. Generally , the data will be tran smitted to and pro c essed at a nea r by radio ac c e ss point (AP) to facilitate network model tr a ining and in telligent decision s, e . g., mach ine learning for feature extraction [5] and fuz z y Q-learning fo r load balancing [6]. T o this end, endowing APs with p owerful mobile edg e co mputing (MEC) func tio nalities will be a majo r form of I I oT scenarios [7]–[9]. A typical use case en a b led b y MEC in IIoT is warehou se en- vironm e ntal monitorin g . In suc h an app lication, different types of WDs are deployed arou nd the storeho use, responsible for collecting and transmitting data from surround ings to APs in order to ma in tain a fav orable storage environment. There fore, the system would prefer hig h through put with reliability and practicality but pays less attention to latency . Different fro m conv entional MEC n etworks wh ich focus on radio/com puting resources optimizatio n of hom o geneou s d evices with real-time network state information (NSI), sched uling in the c o nsidered IIoT scenario faces several technical challenges: 1) Sustain ability : The I IoT devices ar e increasingly emp ow- ered with wireless power transfer (WPT) capability , so as to harvest energy from wireless signals, recharge their limited battery , and prolo ng th e lifetimes of the devices. T his is critical to guarante e the sustainability with WPT capability since frequen t r eplacement of batteries for a massi ve num ber of devices would incur prohibitive operational/main tenance cost in IIoT . Howe ver , the transmission of wireless power consumes spectrum resource s and need s to be jo in tly optimized with th e decisions of data offloading and pr ocessing in the AP . 2) Heter ogeneity : The IIo T devices (such as ind ustrial sensors, actuato rs, and co ntrollers) have heterog eneous com- puting/stor age/battery capa bilities. Such inhomo g eneity would necessitate specific an d meticulous algorithms fo r different types of devices. 3) S calability : Given the stochastic and time-varying fea- tures o f the IIo T en vironm ent, real-time NSI is vital f or th e effecti veness o f resource alloca tio n. Howe ver, due to limited signaling resources, it may not be practical for the AP to acquire real-time N SI from a wide range o f I IoT d evices. The aforementio ned jo int d esign u n der h eterogen eous II oT en vironm ent is requir e d to be scaled to operate in the presence of outdated NSI. A. Related W ork These challenges have yet to be ad dressed in the liter- ature, especially in he te r ogeneo us IIoT . Althou gh th ere are extensi ve works about resour ce schedu ling in M EC [10]– [12], the joint o ptimization fo r ban d width, comp uting, and energy intake/output is of insufficient study . Of flin e algor ith m for th e joint o p timization w ould require com plete no n-causal informa tio n of networks and may suffer from the curse of dimensiona lity when the system is in large scale. T o address these issues, a pertur bed L yapu nov technique was employed to deco uple the spatial- and time-depende ncy of m ultiple resources in [1 3] an d [14]. Howev er , these analyses may n ot be suitable for IIoT , since their energy harvesting processes 2 were modeled as stochastic energy packet arrivals. The high ly variable of energy su pplies was unfav orable f or system contro l and manu al management. Recent years have witnessed the po ssibility of integrating WPT with MEC. WPT , especially in th e f o rm of w ir eless powered com m unication network (WPCN) [15]–[2 0], has been en visioned as an promising pa radigm to provide adaptive and sustainable energy supply for battery -powered devices. I n [ 2 1], a compu tation rate maximization problem was formulated in wireless po wered ME C with binary offloading, an d solved by developing two algorithms based on coo r dinate descent and alternating dir ection method of multipliers. Reference [22] explored the benefits of user co operatio n in min im izing WPT - MEC system energy b y solv ing a min-max pro blem thro ugh a two-phase method. For the scen ario with multi-antenn a AP , a semiclosed solution for AP’ s e n ergy consump tio n minimiza- tion was d erived unde r a computation latency con straint [23]. Howe ver, these algorithms imp licitly assumed th a t th e AP ha s sufficient com puting capab ility . I n contrast, th e optimal d esign for resou rce-limited AP , which is widespre ad in IIo T due to stringent pr oductio n cost c onsideration , and its sustainability analysis are lack o f study . There have b een separate studies over the optimization of WPT/MEC for the devices with limited [15], [ 23], [2 4] (referre d to as T y pe-I hereafter) o r sufficient [ 1 6]–[18], [2 2] (referre d to as T ype- I I in the sequel) battery sizes. T ype-I de- vices, with hig h self-discharge rate , c o nsume all the harvested energy for data offloading in ea c h time slot. Ther efore, its resource sche duling usually work s in a m yopic ma nner . On the contrar y , so lon g as the battery capacity allows, T y pe-II devices can store the unused energy harvested in the cu rrent slot for futur e use. Som e p apers n oticed the heter ogeneity and propo sed separate scheduling ap proach e s for the two types o f WDs [19], [20]. Howe ver , non e of the existing works can b e extended to the considered heterogen eous IIoT system, since the joint optim ization fo r T ype-I/II d evices is highly co u pled and depen dent on each other . The afo remention ed works all optimize their ob jectiv es under the assum p tion o f real-time NSI. It is generally im- practical d ue to systems’ stochasticity and un p redictability , partial feedbac k , and n o n-negligible transmission delay . In [13] an d [2 5], n ew analytic fr amew orks were proposed and applied to accomm o date o utdated NSI, wh ich were able to diminish the op timality loss asym ptotically . Chenshan et a l in [26] later extend ed those fram eworks to the scena r io of Internet of Thing s with finite d evice b uffers. Fur thermor e , a mu lti-timescale on line algor ithm was developed in [ 27], where the futur e queue backlo gs were ap proxim ated b y the current backlogs. H owever , all these works d id no t quantize the tradeo ff b etween feedback sign aling and per f ormanc e lo ss. B. Contributions Distinctiv ely d ifferent from the existing appro aches, this paper designs an asymptotically optimal scheduling method for h eterogen e o us IIoT , where WDs with d ifferent battery capabilities are powered by WPT . Our objective is to maximize a time-average system utility con sidering both thro ughp ut an d fairness, an d enable the optimization to be toleran t to par tial outdated NSI. The key con tributions of this pap er a r e as follows: • W e develop an energy -aware r esource sched u ling (ERS) algorithm to tackle time coupling amo ng data collection, energy transmission, and data offloading in IIoT by lev eraging L yap unov techniqu e. A stochastic optimization problem is formulated an d then transformed into a series of conve x issues with the aid of th e data b acklog analy sis from bo th th e AP and WDs. Moreover, we theoretically prove that the pro posed algorithm achieves close-to- optimal perfor m ance with a kn own deviation, presenting an [ O ( V ) , O (1 /V ) ]-tradeoff between utility and stability . • Th e pro posed ERS alg orithm is favorable for mu ltiple resource scheduling in IIoT by exploiting the diversity of heter ogeneo us d evices. The objective fun ctions of scheduling T ype-I an d T ype-I I devices are meticu lously formu late d into a similar form and are jointly o ptimized subject to da ta stability and energy sustainability . • W e extend th e pr oposed alg orithm to a mo re p ractical sce- nario wh ere o nly outdated NSI is av a ilab le fo r sche d uling optimization due to partial feed back and tran smission delay . Besides, we deriv e the optimal decision s for the scheduling process and analyze its optimality loss in the presence of stale NSI. Extensive simulatio n s verify th e theoretical analy ses of the propo sed online algorith m fo r he te r ogeneo us IIoT . It is shown that the p roposed app roach, with only pa r tial outdated NSI, can in crease the system th rough put while maintainin g fairness among T ype- I/II devices. Simu lations also r ev eal the im pact of feedback overhead and interval o n thro u ghpu t, thereb y providing guidelines for th e design of compulsor y f e edback interval in practical implemen tation. Note th at the selection of L yap unov o ptimization techniqu e s in this p a per is to design asym ptotically optimal and lo w- complexity resou rce scheduling approach , which is of p r actical importan ce since IIo T req u ires efficient r esource utilization and quick response. Apart fro m L yapu nov o ptimization, the heuristic, game- theoretic, submodular as well as reinf o rce- ment learning- based appr oaches can also be ap plied to solve the stochastic optimiz a tio n pr oblem. Howe ver, all these ap- proach e s can result in optimality loss due to myo p ic schedule (e.g., heuristic metho d) or high com plexity and learning time (e.g., Q-lear ning). As a resu lt, in the proposed algorithm , we first leverage L yapu nov optimization to de couple the time- and space- coup lings in scheduling decisions, and then efficiently solve the decoupled sub -prob lems by app lying conv ex o pti- mization techniqu e s. The r e st of th is p a per is organize d as f ollows. T he next section in tr oduces the sy stem mod el of th e con sidered IIoT and th e p roblem formulation. Section III proposes the online scheduling algorithm and analy zes its perfo rmance theoreti- cally . Sec tio n IV provid es the extension of the online algorithm for a m o re pr actical scenario. Simulatio n results are presented in Section V , followed b y the conclusio n in Section VI. 3 . . . AP WPT flow Offloading data flow WD 1 WD n WD N WD n+1 Type-I 1 1 Type-II 2 2 . . . h 1 (t) h n (t) h n+1 (t) h N (t) Q 1 (t) Q n (t) Q n+1 (t) Q N (t) Energy transfer circuit Edge computing circuit (a) System scenario . . . AP ė WDs WPT WD 1 ė AP Offload WD 2 ė AP Offload WD N ė AP Offload 0 ( ) t T m 1 ( ) t T m 2 ( ) t T m ( ) N t T m . . . T (b) T ime frame structure Fig. 1. Considere d system model o f wireless powered ME C for warehouse en vironmental monitoring in IIoT I I . S Y S T E M M O D E L A N D P RO B L E M F O R M U L AT I O N A. System Overview W e consider a n IIoT system con sisting of an AP end owed with M EC and WPT function alities, and N heterogen eous WDs indexed by N = { 1 , 2 , · · · , N } . As sho wn in Fig. 1( a ), WDs in the system are divided into sets of T yp e-I and T ype- II devices, denoted by N 1 and N 2 , respectively . Similar to WPCN, we assume the system operates in a fr ame-based time-division-multiplexing man ner [15]– [ 17], [19]. Fig. 1(b ) illustrates the system ’ time frame structu re with dur ation T , which co nsists of two pha ses. In the first p hase, the first µ 0 ( t ) T amou nt of time is assigned for d ownlink WPT , where µ 0 ( t ) ∈ [0 , 1) denotes its allocated time portion at slot t . In the second phase, the rest (1 − µ 0 ( t )) T amo unt o f time is used for the co mputation offl oading in th e up lin k. T he time allocated for WD i to offload is d e noted by µ i ( t ) T , wher e µ i ( t ) ∈ [0 , 1) . Consider am bient d ata ana lysis fo r II oT , the computatio n results at the AP is no t required to be returned to WDs. Hence, the time portions ˜ µ ( t ) = ( µ i ( t ) , i ∈ ˜ N ) satisfies X i ∈ ˜ N µ i ( t ) ≤ 1 , µ i ( t ) ≥ 0 , ∀ i ∈ ˜ N , (1) where ˜ N , { 0 } ∪ N represents the set of the AP and all WDs. W e con sider that the AP has a reliable power supply and a constant tran smit power P 0 by con necting with the power grid . It is assumed that the AP and all WDs have one single antenna each. Compar ed to P 0 , the energy harvested f rom noises a n d received u plink signals from o ther WDs is much smaller , thus is assumed to be negligible [15]–[ 17], [1 9]. W ithin time slot t , the amount o f energy harvested b y the i - th WD can be expressed as [15], [2 1] e H i ( t ) = ξ i P 0 h i ( t ) µ 0 ( t ) T , i ∈ N , (2) where ξ i ∈ (0 , 1) is the e n ergy harvesting efficiency , and h i ( t ) is the c h annel power gain between th e AP an d the i -th WD. T ABLE I S U M M A RY O F N OTATI O N S Notation Description N ( N 1 , N 2 ) Set of all (T ype-I, T ype-II) wireless devices ξ i Energy harvesting efficienc y of device i P 0 Transmit power of AP P i ( t ) Offloading transmit power of device i at slot t h i ( t ) Channel power gain between AP and device i at slot t T Interval of a time block W System bandwidth µ 0 ( t ) Time portion for wireless power transfer at s lot t µ i ( t ) Time portion for device i to offload at slot t c i ( t ) Achievable offloading data size of device i at slot t E i ( t ) A vailable energy of device i at slot t e i ( t ) Of floading transmit energy of device i at s lot t e H i ( t ) Energy harvested by device i at slot t A i ( t ) Data that can be collected by device i within s lot t a i ( t ) Data collected a t device i within slot t Q i ( t ) Data queue ba c klog of device i at slot t S i ( t ) Da ta queue backlog of AP at s lot t r i ( t ) A vailable data processing speed of AP at slot t X Time-a verage of any stochastic process X U i ( · ) Utili ty of device i W ith out loss o f g e nerality , we assume e H i ( t ) ≤ e H i, max , wher e e H i, max is the maxim um harvested energy in on e slot reco rded from a lo ng time. It is further assumed that all channels ar e indepen d ent and id entically distributed ( i.i.d.) flat blo ck fadin g , i.e., chann els remain static within each time slot b ut may vary across different slots [13], [14], [2 8]. By exploiting the channe l reciprocity in time- division mode system [15] [21], the AP can acquir e b oth the u p link and downlink channel states at th e beginnin g o f each time slot with little signa lin g cost. This c a n be achieved by e a c h WD sending its pilot for channe l measuremen t a t the AP [19], [28]. Hence, the achievable offloading data size of WD i (in bits) within time slot t can be given by [21], [22] c i ( t ) = µ i ( t ) T W log 2 (1 + P i ( t ) h i ( t ) N 0 ) , i ∈ N , (3) where W den otes the communication bandw id th, P i ( t ) repre- sents the transmit power of WD i , and N 0 denotes th e n oise power at th e re ceiv er of the AP . G iven the limited u plink transmission power , c i ( t ) in (3) is upp er boun ded by c max i . The notations used in this p aper are summarized in T able I. B. Energy Models for Heter ogeneous Devices Energy mod els fo r T y pe-I and T ype-II de vices are entirely different due to their battery management capab ilities, wh ic h are further discussed in the following. 1) T ype-I devices: Th is type of WDs is eq u ipped with batteries that hav e lo w energy s torage capacity and high self- discharge rate. In this case, the harvested but unused energy within the cu rrent slot will be depleted and c annot be kept for future use. As a result, if µ i ( t ) 6 = 0 , i -th WD will manag e its energy in a myopic mann er , i.e., exhausting all the harvested energy f o r of floading. Th us, we h av e P i ( t ) = 0 if WD i stay 4 silent in the offloading p h ase, otherwise, WD i will offload with transmit power P i ( t ) = η i e H i ( t ) µ i ( t ) T , i ∈ N 1 , (4) where η i represents the fixed portion of the h arvested energy that is u sed f or data of floading . As the device exhausts all the harvested energy fo r uplink transmission, η i = 1 in the sequel. The ma x imum transmit power constraint for T ype-I d evices is neglected here since the h arvested energy from WPT at ea c h slot is small in practice [21]. 2) T ype-II d evices: Different from T y pe-I d evices, each device i ∈ N 2 is eq uipped with a rechargeable battery that has a high energy storage capa c ity and low discharge r ate. As long as the maximum battery capacity θ i is not exceeded, a T yp e-II d evice can save the har vested en e rgy in its batter y for offloading in the following slots when the channel fading condition is u nfav o rable. Denote E ( t ) = ( E i ( t ) , i ∈ N 2 ) as the vector o f T ype-I I de vices’ energy queu e sizes at slot t , and e ( t ) = ( e i ( t ) , i ∈ N 2 ) as the vector o f their co r respond ing uplink transmit energy . The a v ailable energy in WD i ev o lves accordin g to the dynamic equation E i ( t + 1) = min { E i ( t ) + e H i ( t ) , θ i } − e i ( t ) , i ∈ N 2 . (5) At any time slot t , the tra n smit energy e i ( t ) must f ollow the ener gy-availa ble condition e i ( t ) ≤ E i ( t ) + e H i ( t ) , i ∈ N 2 , (6) such th a t the energy used would no t exceed wha t has been cumulatively harvested so far . Meanwh ile, since a T ype - II device can accum ulate m uch energy befor e its tra n smission, when offloading, it shou ld also satisfy the maximum transmit power constraint e i ( t ) ≤ P max i µ i ( t ) T , i ∈ N 2 , (7) where P max i is i -th WD’ s maximum transmit power . C. Data Co llection and Queuein g Models At any slot t , the v olume of data that can be c o llected by WD i is de noted by A i ( t ) . Due to th e dynamic changes of en vironm ent in IIoT , we assume A i ( t ) to be i.i.d. over slo ts with a m aximum A max i [10], [13]. Giv en the data fresh n ess and the limited da ta buffer of WD, only part of the data, denoted by a i ( t ) , would be collected in to the data buffer . Hence, we have 0 ≤ a i ( t ) ≤ A i ( t ) ≤ A max i , ∀ i ∈ N . (8) Let Q ( t ) = ( Q i ( t ) , i ∈ N ) d enote the back log of data que u e of WDs at slot t , i.e., any c ollected but hav e not been offloaded data that are qu eued in the data buf fer . At e very slot, th e network decides h ow much data sho u ld be collected (i.e., a i ( t ) ) and h ow mu ch existing data in the buffer to offload (i.e., c i ( t ) ) accor d ing to th e network state. Follo w the basic operation s of c a scaded q ueueing system s [10], [1 3] (e. g., the edge computin g network wh e re the d ata arriv al and offloading operate on a first-in- fir st-out basis), the amoun t of data to be collected (i.e., a i ( t ) ) is determ ined at slot t and queued into the data b uffer at the beginning of slot t + 1 . Ther efore, th e data backlog Q i ( t ) ev olves as follows: Q i ( t + 1) = [ Q i ( t ) − c i ( t )] + + a i ( t ) , i ∈ N , (9) where [ x ] + = max { x, 0 } . In some special cases, for examp le, at th e early stage of the n etwork, Q i ( t ) may be smaller than c i ( t ) as the collection o f d ata takes time. Here, th e first term in the right-h and-side ( RHS) of equation (9) is used to guara ntee that the device cannot offload mo re than what remains in its data buf fer when Q i ( t ) < c i ( t ) happen s [10], [29]. The AP maintains N data buffers S ( t ) = ( S i ( t ) , i ∈ N ) to sto re th e d ata th at o ffloaded from WDs but ha ve not been processed. Con strained by the limited compu ting capab ility of the AP , at mo st r i ( t ) amoun t of data from i - th WD can b e processed at slot t , where r i ( t ) is a stochastic numb er with the maximu m r max i [13]. Natura lly , the da ta queue dyn amics at the AP are gi ven by S i ( t + 1) = [ S i ( t ) − r i ( t )] + + min { c i ( t ) , Q i ( t ) } , (10) where the second ter m in th e RHS of (1 0) repr esents the d ata- available constra in t of WD i , which means the WD ca nnot offload more da ta than what it has sto r ed. In the case when c i ( t ) > Q i ( t ) , the excessive offloading rate will be used for transmitting dum my data [10], [29]. W e will later show that the optimization is still asymptotically optimal by do in g this. D. Pr oblem F ormulation Consider warehouse en vironm ental mon ito ring serv ices in an IIoT system, un fair data collection and offloading would reduce the overall system pe rforman ce. This is bec ause we may waste to o many resour ces fo r of floading redundant data from one place wh ile lacking enou gh data fro m o th er ar eas for analysis. Therefo r e, in th is paper, we aim at max imizing the system thro ughpu t while gua r anteeing fairness among WDs. Howe ver, fairness in the conside red scenario is not easy to ach iev e due to the d oubly near-far phenom enon [15] and heteroge n eity of the WDs, which is fu r ther discussed in section V. T o add ress th is issue, instead of dir ectly ma ximizing the thro ughp u t, we formula te th e problem as a sum-utility maximization problem as fo llows P: max ˜ µ ( t ) , e ( t ) , a ( t ) X i ∈N U i ( a i ( t )) s.t. (1) , (6) , (7) , (8) , C1: Q i < ∞ , ∀ i ∈ N , C2: S i < ∞ , ∀ i ∈ N , where a ( t ) = ( a i ( t ) , i ∈ N ) , X = lim t →∞ 1 t P t − 1 τ =0 E { X ( τ ) } defines the time average expecta tio n o f any stochastic pro cess X ( t ) , constraints C1 and C2 ensure the stability o f all the data queues, an d the utility f unction based on prop ortional fairness [1 3], [30] is defined as U i ( x ) = log(1 + x ) . Here, log( · ) denotes the natural logar ithm. As c a n be seen fr om the u tility functio n , the margin a l utility decreases as th e amou nt of d ata collected b y a WD increase. As a result, the system would be in clined to c o llect equal amounts of da ta from different WDs rathe r th an show an 5 apparen t p referenc e for some d evices. This thereb y en sures system fairness. The p roblem P is a typ ical stocha stic optimiza tio n prob lem. An of fline op timization of P would require comple te non- causal NSI, which is imp o ssible in practice due to the high ly stochastic an d unpredictab le cha r acteristics of I IoT systems. Even if such NSI is a vailable, the problem is still challenging due to its high computation al complexity . Therefo re, we are motiv ated to p ropose online algorithm to jointly schedu le ˜ µ ( t ) , e ( t ) and a ( t ) without future NSI. I I I . O N L I N E S C H E D U L E O F H E T E RO G E N E O U S D E V I C E S In this section, we develop a n online decision -making algorithm by emp loying L y a p unov optimization. The original problem P is decoup led in to a series of deterministic per -time slot problems at indepe n dent time slots, whic h are then solved by con vex optim ization techniq u e. W e later prove that the propo sed alg orithm pr eserves a symptotic optimality co mpared with the op timum of the or iginal problem. A. Pr oblem T ransformation Define Θ ( t ) = [ Q ( t ) , E ( t ) , S ( t )] as the con c a tenated vector of the queu e s at WDs an d the AP . T o hand le the time- coupling in p roblem P , we first define a n on-negative perturb ed L yapu n ov f unction as L Θ ( t ) = 1 2 ( X i ∈N S i ( t ) 2 + X i ∈N Q i ( t ) 2 + X i ∈N B ( E i ( t ) − θ i ) 2 ) , (11) where θ i is a weight perturbation, also the b attery ca p acity of T ype - II devices mentioned in Section II. W e will later show that (6) can be satisfied with a pro per choice o f θ i . Mean while, when min imizing L Θ ( t ) , we push th e data b acklogs at both the AP and WDs towards zero, which is equivalent to satisfying stability constraints C1 and C2 in P . Then the one- slot cond itional L yapunov drift can be expressed as ∆( Θ ( t )) = E L Θ ( t + 1) − L Θ ( t ) | Θ ( t ) . (12) where the expectation is taken with r e spect to the random NSI and the contro l actions. Based o n L yapu nov op timiza- tion tech n ique, we con sider minimizing the drif t-plus-pen alty expression ∆ V Θ ( t ) = ∆ Θ ( t ) − V E ( X i ∈N U i a i ( t ) | Θ ( t ) ) , (1 3) instead of d irectly le veraging the objection in P . Lemma 1 : For any op timization decisions m ade o n slot t , and all possible v alues o f Θ ( t ) , the drift-plus-pena lty e xpres- sion for all slot t satisfies ∆ V Θ ( t ) ≤ B 1 − V E ( X i ∈N U i a i ( t ) | Θ ( t ) ) + X i ∈N Q i ( t ) E { a i ( t ) − c i ( t ) | Θ ( t ) } + X i ∈N S i ( t ) E { c i ( t ) − r i ( t ) | Θ ( t ) } + X i ∈N 2 [ E i ( t ) − θ i ] E { e H i ( t ) − e i ( t ) | Θ ( t ) } , (14) where V > 0 is a control parameter that affects an explicit tradeoff between system utility an d data backlo gs, B 1 denotes a finite constan t tha t satisfies B 1 = 1 2 ( X i ∈N ( A max i ) 2 + ( r max i ) 2 + 2 X i ∈N ( c max i ) 2 ) + 1 2 ( X i ∈N 2 [( e H i, max ) 2 + ( P max i T ) 2 ] ) (15) Pr oo f: Please refer to App endix A Minimizing ∆ V Θ ( t ) is still dif ficult d ue to its dynamics. Instead, w e are motiv ated to minimize the RHS of (14) accordin g to the prin ciple of opportun istically minimizing an expectation [31] in a per-slot manner, subject to the con stra ints (1), (7), and ( 8). B. Optimal S cheduling Decisions In this sub section, we present an E ne rgy -aware R esource S cheduling algo rithm with R eal-time N SI (ERS-RN al- gorithm) to add ress the above problem. Since a ( t ) and ( e ( t ) , ˜ µ ( t )) can be decoupled with each oth er and ar e in - depend ent o f the current backlog Θ ( t ) , the minimiza tio n problem c a n be separ ated into tw o optimization sub-pr oblems as follows. 1) Distributed Data Collection : For each time slot t , the data co llection sub- p roblem can be decompo sed f or individual WD. The op tim al data collection strategy can be obtain ed by solving P1: m in a i ( t ) Q i ( t ) a i ( t ) − V U i a i ( t ) s.t. (8) . The pro blem P1 is a conve x optimization pro blem since th e objective function is co n vex and its co nstraint is linear . Hence, the o ptimum is either at the stationa r y poin t of a i ( t ) = V / Q i ( t ) − 1 or on one of the bound aries. For any WD i ∈ N , the optimal data co llec tio n strategy is thus chosen b y a i ( t ) = ( A i ( t ) , V ≥ ( A i ( t ) + 1) Q i ( t ) [ V Q i ( t ) − 1] + , other wise (16) The g iv en policy ind ic a te s that the amount o f data collected by each WD depends on the length o f its backlog. A de vice is inclined to co llec t more data when its ba c klog is small. 6 2) Joint Energy and T im e Alloca tion : Accor ding to (14), the o ptimal transmit powers e ( t ) and the optimal time po r tions ˜ µ ( t ) can b e derived b y solving P2: min e ( t ) , ˜ µ ( t ) X i ∈N [ S i ( t ) − Q i ( t )] c i ( t ) + X i ∈N 2 [ E i ( t ) − θ i ][ e H i ( t ) − e i ( t )] s.t. (1) , (7) . Due to the constraint (1), e ( t ) an d ˜ µ ( t ) in pr oblem P2 cannot b e co mpletely d ecoupled . Ge nerally , P2 is a non- conv ex optimization problem. T o solve this pro blem, we first define a set N t , { i | i ∈ N , S i ( t ) ≥ Q i ( t ) } , and then find an interesting prop e rty of its optimization as shown in the following theorem. Theor em 1: For any device i ∈ N t ∩ N 2 , the term [ S i ( t ) − Q i ( t )] c i ( t ) + [ E i ( t ) − θ i ][ e H i ( t ) − e i ( t )] in the objective function of P2 gets its min imum when µ i ( t ) = 0 , e i ( t ) = 0 . Besides, for arbitrary WD i ∈ N t ∩ N 1 , its optimal time portion is giv en by µ i ( t ) = 0 . Pr oo f: Please refer to Appendix B Remark 1: Theorem 1 s uggests th at the AP prefer s to serve WDs who have a larger data ba c klog than that queuein g at the AP . This result is in a ccordan c e with o ur intu ition that when the waiting queue at the AP is large, offloading data from a WD whose qu e ue length is small only brings transmission energy loss and mor e e xecution delay . By excludin g the devices in N t , we denote the remaining T ype - I WDs to be sched uled as N t 1 . Similarly , let N t 2 collect the T ype-II devices tha t are not in N t . For the sake of bre vity , we define D i ( t ) = [ S i ( t ) − Q i ( t )] T W , β i ( t ) = h i ( t ) / ( N 0 T ) , δ i ( t ) = ξ i P 0 h 2 i ( t ) / N 0 in the sequel. Then the problem P2 can be simplified an d rewritten as follows P3: min v ( t ) X i ∈N t 2 D i ( t ) φ i ( t ) − X i ∈N t 2 [ E i ( t ) − θ i ] e i ( t ) + X i ∈N t 1 D i ( t ) ψ i ( t ) + µ 0 ( t ) T P 0 X i ∈N 2 [ E i ( t ) − θ i ] ξ i h i ( t ) s.t. C3: X i ∈ ˜ N \N t µ i ( t ) ≤ 1 , µ i ( t ) > 0 , ∀ i ∈ ˜ N \N t , C4: e i ( t ) ≤ P max i µ i ( t ) T , i ∈ N t 2 , where v ( t ) = { e i ( t ) | i ∈ N t 2 } ∪ { µ i ( t ) | i ∈ ˜ N \N t } collects all variables that is to be o p timized, and φ i ( t ) = µ i ( t ) log 2 (1 + β i ( t ) e i ( t ) µ i ( t ) ) , i ∈ N t 2 , (17) ψ i ( t ) = µ i ( t ) log 2 (1 + δ i ( t ) µ 0 ( t ) µ i ( t ) ) , i ∈ N t 1 . (18) Note from (17) that φ i ( t ) is a persp ectiv e fu nction o f f ( x ) = log 2 (1 + β i ( t ) x ) . Since f ( x ) is a concave function of x ≥ 0 , φ i ( t ) is jointly concave with respect to e i ( t ) > 0 and µ i ( t ) > 0 for arbitrary i ∈ N t 2 [32]. Similar ly , we can prove that ψ i ( t ) is concave in { µ 0 ( t ) , µ i ( t ) : ∀ i ∈ N t 1 } when µ 0 ( t ) > 0 an d µ i ( t ) > 0 . Since the obje c tive fun ction in P3 is a negative weighted sum o f φ i ( t ) , ψ i ( t ) and several Algorithm 1: ERS-RN Algor ithm At the AP : 1: Observe Q ( t ) , S ( t ) , E ( t ) , r ( t ) and ch a nnel gains; 2: Choose v ( t ) by solvin g P3 ; 3: Infor m v ( t ) to WDs and execute WPT ; 4: Update E i ( t ) at each T yp e-II de vice i by v ( t ) and (5). At any WD i : 5: Observe Q i ( t ) , A i ( t ) and c i ( t ) ; 6: Decide a i ( t ) based o n (16); 7: Offload data and give f eedback Q i ( t ) to the AP in the arrange d seque n ce; 8: Update Q i ( t ) accordin g to (9). At the AP : 9: Update S ( t ) according to (10). linear fun ctions, the objective functio n o f P3 is c o n vex in v ( t) . Meanwhile, the con stra in ts C3 and C4 are line ar , a n d thus conv ex. Therefore, the problem P 3 is a conve x optimization problem , which can be effecti vely solved by off-the-shelf tool- box CVX [33] at a maximal co mputation al complexity ord er of O (max { (2 |N t 2 | + |N t 1 | + 1) 3 , C } ) [31]. Here , (2 |N t 2 | + |N t 1 | + 1) represents the number of v ariables to b e op timized, C is th e cost to e valuate the objec tive func tio n to g ether with its first and second derivati ves. Based on the above analy sis, th e who le process of the ERS- RN algo rithm is sum m arized in Algo r ithm 1 . W e call the algorithm energy -aware because the AP c onducts the energy allocation by itself and ob tains the real- time kn owledge of all de vices’ energy stor ages without any feedb ack f r om WDs. Note that the jo int energy an d time allocation de p ends on real- time data qu eue lengths fed back by all WDs. He nce, the optimization of time por tions can o nly be coordin ated at the AP in a centralized manner . C. P erforman ce Analysis In this subsection, we start by showing that the p ropo sed ERS-RN algorithm is asym ptotically optimal. De note U ⋆ as the offline o ptimum of pro blem P , which can only b e obtained by using full non-c ausal knowledge of the IIoT network. Let U ∗ denote the long-term time-a verage utility ach iev ed by the ERS-RN alg o rithm. Then, we can establish the following theorem. Theor em 2: Suppose the pr oblem P is feasible, the gap between U ∗ and U ⋆ satisfies U ⋆ − U ∗ ≤ B 1 /V . (19) Pr oo f: Please refer to App endix C Theorem 2 suggests that the achiev able time-average utility of the p roposed method can b e arbitrarily close to the offl ine optimum b y setting a sufficiently large V . In other words, the prop osed appro ach is asympto tically optimal in terms of solving the origina l pro blem P . Ho wev er , it is not the larger the value o f V , the b etter . The inc rease of V would also cau se a negati ve impact on system data backlo gs, as revealed in the following theorem. 7 Theor em 3: At any time slot, the data backlo g s at WD i ∈ N and the AP are all upp e r bounded , with upper bounds given by Q max i = V + A max i , (20) S max i = V + A max i + c max i . (21) Pr oo f: Please refer to Appendix D W ith The orem 3, we then provide the value of the weigh t perturb ation p arameter θ i and p rove the ene r g y-availab ility constraint (6) is al ways satisfies in the following the o rem. Theor em 4: W ith the pro p osed a lgorithm, the energy storage capacity ( or the p erturbatio n p a rameter) θ i is given as follows θ i = ( V + A max i ) c max i e min i + P max i T , (22) where e min i is th e minim um transm it energy other tha n zer o. The equation (2 2) en sures there is e n ough energy in the battery for op timal schedule. In o ther words, E i ( t ) + e H i ( t ) > P i ( t ) T . Pr oo f: Please refer to Appendix E Theorem 3 and 4 show that Q max i , S max i and θ i increase monoto nically with the contro l parameter V . A larger V leads to a high er system utility at the expe nse of larger queu e leng ths at all WDs and the AP . On the other han d , a tiny V impairs the asymp totic o ptimality of achievable utility but reduces the d emands for large storag e spaces of the system. This reveals a [ O (1 /V ) , O ( V )] tradeoff between the system utility and the required storage spaces. Therefor e , instead of giving each WD a substantial data an d e nergy storage space, we can reduce th e man ufacturing c o sts of IIoT systems by embedd ing approp riate data buffers and batteries for WDs based on the expected system utility . I V . R E S O U R C E S C H E D U L I N G I N I I O T W I T H I M P L E M E N TA T I O N C O N S I D E R AT I O N S In this section, we co nsider a more general setting in which th e overhead and d elay for transmitting NSI canno t be overlooked. W e dev elop a mod ified version of th e ERS- RN algorithm, called ERS-ON, to address the issues b roug h t by practical application , and further analyze its p erform a n ce theoretically . A. Practicability Considerations As discussed, real-time N SI feedback ( i.e., Q ( t ) ) is nee d ed at the AP for the joint optimization of energy allocations and time portio ns. Howe ver, the transmission of NSI would occu py the time for d ata offloading, which may jeopard ize network perfor mance, or ev en pro h ibit the system from working. T o av o id e xplosive feedback costs, system s may send back only partial NSI, as th e majo rity of feed b acks have less contr ibution for optimization. Moreover , even if all WDs giv e co ntinuou s feedback s at every slot, the AP can only get outdated NSI (e.g., Q ( t − 1) at slot t ) since it has to make the scheduling decision b efore obtaining Q i ( t ) in the uplink phase at slot t . As a result, the propo sed ERS-RN algorithm m a y be hard to be directly ap plied to real systems. Some modifications are needed in the p resence of ou tdated NSI. Therefo re, in this section , we procee d to consider a mor e practical scenario of the co nsidered IIoT system, where any device i that has b een assign ed time for offloading at slot t should spare at least ǫ i T tim e to give feed back of its data backlog . Here, th e time portion ǫ i is a constant obtained by historical experience such th a t ther e is always enoug h energy for transmitting an L bits feed b ack. WDs that h av e no t gotten any up link ch ances (i.e., silent) at slot t are generally not required for feedback s in order to reduc e system NSI overheads. The only exception is for those WDs that r emain silent in th e past m slots, in case the shortage of NSI update at the AP permanen tly prevents some WDs from offloading. For notation simplicity , we denote those WDs that reach their compulso r y feedbac k interval mT at time slot t as M t in the sequel. B. Energy-A war e Resour ce Schedulin g Algorithm with Out- dated NSI The ou tdated NSI (i.e., data backlo gs at WDs) ac quired throug h th e above f eedback m echanism h a s a direct imp act on the optimization o f problem P 3 . T o overcome the limitation of the ERS-RN algorithm, we develop a modified version of the ERS alg o rithm with Outda te d NSI (ERS-ON) by appr ox- imating the latest feedback of WDs’ data b acklog values as the cur rent values. Le t b Q i ( t ) den ote the ap proxim a tion o f i -th WD’ s data b acklog th a t the AP holds at time slot t . Hence, we have b Q i ( t ) = Q i ( t − τ i ) , where τ i ∈ { 1 , · · · , m } . T hen, the problem P3 can be transformed into P4: min v ( t ) X i ∈N t 2 b D i ( t ) φ i ( t ) − X i ∈N t 2 [ E i ( t ) − θ i ] e i ( t ) + X i ∈N t 1 b D i ( t ) ψ i ( t ) + µ 0 ( t ) T P 0 X i ∈N 2 [ E i ( t ) − θ i ] ξ i h i ( t ) s.t. C4 , C5: X i ∈ ˜ N \N t µ i ( t ) ≤ 1 − X i ∈M t ǫ i , µ i ( t ) > ǫ i , ∀ i ∈ N \N t . where b D i ( t ) = [ S i ( t ) − b Q i ( t )] T W , and C5 ensures there is enoug h time fo r offloading and feedback in each time slot. Similar to P3 , problem P4 can b e solved by CVX or o ther conv ex optim iza tion tech niques as the constrain t C5 pr e ser ves conv exity . Let { e ∗ i ( t ) | i ∈ N t 2 } collect the o ptimal en ergy solution s and { µ ∗ i ( t ) | i ∈ ˜ N \N t } denote the optimal time portions o f problem P4 . The time portion s fo r WDs and the AP at time slot t can th us be given by µ i ( t ) = 0 , i ∈ N t \M t ǫ i , i ∈ M t µ ∗ i ( t ) , otherwise , (23) where µ i ( t ) = 0 mea ns WD i keeps silent at slot t . Different from the time por tions allocation, the energy policies for WDs vary with their types. For T ype-I devices, same like the statemen t in section II, all the harvested energy would be consu m ed for offloading/feedba ck o r be depleted . On the con trary , T ype-I I devices in N 2 ∩ M t can dy namically 8 T ABLE II S Y S T E M S I M U L AT I O N P A R A M E T E R S Basic Radio Configuration Parameters Spectrum Bandwidth W (MHz) 0.2 [34] Pass Loss Exponent α 2 [22] P 0 / P max i / N 0 (W) 2/1/ 10 − 9 [22], [34] e min i / e H i, max (mJ) 0 . 005 / 0 . 16 c max i / L (Kbits) 100/0.016 [35] Channel Power Gain h i ( t ) = 10 − 3 d − α i e h ( t ) [22] Other Simulation Paramete rs Energy Harvest ing Efficie ncy ξ i 0.8 [22] Slot Duration (m s) 100 [35] Simulati on Run-Time (slots) 1000 adjust their transmit energy to ensure the chan nel capacity equals the data size of feedback, i.e., L = T W φ i ( t ) , thu s sa ving excessi ve energy for future use. Mor e specifically , th e energy allocation policy for device i ∈ N 2 satisfies e i ( t ) = ǫ i β i ( t ) 2 l i − 1 , i ∈ N 2 ∩ M t e ∗ i ( t ) , i ∈ N t 2 0 , otherwise , (24) where l i = L/ ( ǫ i TW ) . The allocated transmit en ergy of T ype- II de vices would not violate the constraints (6) and ( 7) since we have a large β i ( t ) and small l i when WD i ∈ N 2 ∩ M t . C. Asymp totic Optimality Analysis und er Outdated NSI The use of outdated NSI will ine vitably impair the p e rfor- mance of systems. In th e worst case, a WD would lose m chances to offload durin g the past mT time duration du e to a la c k of in formatio n update a t the AP . For any slot t , th e difference between th e approximate v alues maintained at the AP and the actual data backlogs at WDs a r e bou nded by Q i ( t ) − b Q i ( t ) = t X τ = t − τ i + 1 Q i ( τ ) − Q i ( τ − 1 ) ≤ τ i A max i ≤ mA max i , (25) where the fir st inequality is derived from (8) an d (9). F or analytical tractab ility , we d enote b U ∗ as th e utility obtained by u sin g b Q i ( t ) for optimization . Based on (25), we can prove that the op tim ality loss due to the outdated knowledge of Q ( t ) is strictly up per bound e d as shown in the following theorem. Theor em 5 : Supp ose the problem P is feasible, the ga p between b U ∗ and U ⋆ is boun ded: U ⋆ − b U ∗ ≤ ( B 2 + B 3 X i ∈N ǫ i ) /V , (26) where B 2 = B 1 + m P i ∈N ( A max i ) 2 and B 3 = 2 P i ∈N ( c max i ) 2 . Pr oo f: Please refer to Appendix F Theorem 5 proves that th e asymp totic o ptimality of the pr o- posed ERS-ON alg orithm is n o t comprom ised with outd ated NSI. Compared with Th eorem 2, the optim a lity loss caused by outdated NSI is n o greater than a co n stant divided by V . Moreover , the optimality lo ss is linear to m and increases with the g rowth of feedba c k overheads, which coincid es with the intuition that a long compu lsory f eedback in terval a n d a large overhead result in weak system perf ormanc es. 1 0 0 2 0 0 3 0 0 4 0 0 5 0 0 6 0 0 1 4 0 1 6 0 1 8 0 2 0 0 2 2 0 2 4 0 2 6 0 2 8 0 A v e r a g e t h r o u g h p u t ( k b p s ) C o n t r o l p a r a m e t e r V E R S - O N ( p r o p o s e d ) E O T - O N G A N H D O - O N P F N Fig. 2. A vera ge system throughput versus the control parameter V V . S I M U L AT I O N S In this s ection, we verify the analysis and e valuate the per - forman ce of th e proposed algo rithm via MA TLAB simulation s. The pa r ameters used in our simu lation are taken from the existing synthetic da ta set [22] and 3GPP specificatio ns [34], [35], to cap ture the featu res of practical wireless chann els. Detailed infor mation is listed in T able II. The initial values of Q ( t ) , S ( t ) an d E ( t ) are set to be zero for the fair compariso n with [13]. I n o ur simulations, we set T = 100 ms and consider fi ve T ype-I devices and five T y pe-II de vices. Specifically , we set the distan ce between the AP and T ype- I devices as d 1 = ( d i , i ∈ N 1 ) = [3 , 5 , 7 , 9 , 11] m . W ithou t loss of g enerality , we consider d 2 = ( d i , i ∈ N 2 ) = d 1 . The channel is m odeled after th e Rayleigh fading mo d el and is s et as h i ( t ) = 10 − 3 d − α i e h ( t ) [15], where α den otes the pass-loss exponent, e h ( t ) is an exp o nentially distributed ra n dom variable with unit mean which repr esents th e short-term fading. W e assume that α = 2 an d the chann e l rec ip rocity holds for the uplink and do wnlink. The sp e c trum band width for offloading and the receiver n oise power are set as W = 0 . 2 MHz and N 0 = 10 − 9 W , respectiv ely . For any de vice i ∈ N , the energy harvesting efficiency ξ i = 0 . 8 , and A max i = 1 Mbps. At the AP , the transmission power P 0 = 2 W , r max i = 50 kbps, and m = 4 . For analysis simplicity , we assume ǫ i = ǫ = 0 . 0 05 s f o r any i ∈ N in the sequ el unless other wise stated. W e intro duce four benchm ark algor ithms to evaluate the perfor mance of the pro posed ERS-ON a lg orithm, which w ork as follows: 1) Hom ogeneo us device optimization with outdated NSI (HDO-ON): all WDs are seen as T ype-I devices and optimized without co n sidering their heterogen eity . 2) Eq u al offloading time with outdate d NSI (E OT -ON): all WDs are given equal offloading time at each slot. The optimization o f e ( t ) and µ 0 ( t ) in this scheme is similar to the ERS-ON algorithm. 3) Prop ortiona l fairness w ith out NSI (PFN): the allocation of o ffloading tim e por tions are b ased on pro portion al fairness meth od with no knowledge of Q ( t ) . In the scheme, overheads for feedback can be saved. 9 1 0 0 2 0 0 3 0 0 4 0 0 5 0 0 6 0 0 0 . 5 0 0 . 5 5 0 . 6 0 0 . 6 5 0 . 7 0 0 . 7 5 0 . 8 0 0 . 8 5 0 . 9 0 0 . 9 5 1 . 0 0 J a i n ' s f a i r n e s s i n d e x C o n t r o l p a r a m e t e r V E R S - O N H D O - O N E O T - O N P F N G A N (a) Fa irness performance versus control paramete r V E R S - O N H D O - O N E O T - O N P F N G A N 0 . 5 0 0 . 5 5 0 . 6 0 0 . 6 5 0 . 7 0 0 . 7 5 0 . 8 0 0 . 8 5 0 . 9 0 0 . 9 5 1 . 0 0 J a i n ' s f a i r n e s s i n d e x T y p e - I T y p e - I I (b) Fa irness among dif ferent de vice types, where V = 300 Fig. 3. Impact of control parameter V and schemes on fairness 4) Gree d y alg orithm with out NSI (GAN): the scheme maximizes th e system thro ughp u t b a sed on c hannel condition s without considering fairness. Fig. 2 illustrates the average throug hput of the prop osed and b enchmar k mechanisms as V increases. Faster growth is seen in the pr oposed alg orithm whe n V is smaller than 200. W ith a further increase of V , the gr owth rate gradually slows down, which co incides with what revealed in Th e orem 5. As expec ted, th e prop osed a lg orithm significantly outperf orms HDO-ON, since T ype- II devices in E RS-ON ca n sa ve th eir energy f o r future use wh en channel conditions are not go o d. This proves the necessity to con sider the heterogeneity of WDs in system optimization. Besides, we c a n also observe that the ERS-ON algo rithm achie ves high e r throu ghput than GAN. This is b ecause GAN wastes mu c h offloading time for WDs that own good channe l condition s but with little or ev en no d ata ba c klogs. The po or per f ormanc es of GAN and PFN com bined suggest th at it is desirab le to acq uire NSI f o r system optimization even if the f eedback would occupy som e transmission resour ce. Fig. 3 shows the fairness against the control p a r ameter V . 1 0 0 2 0 0 3 0 0 4 0 0 5 0 0 6 0 0 2 5 5 0 7 5 1 0 0 1 2 5 1 5 0 1 7 5 2 0 0 2 2 5 2 5 0 2 7 5 A v e r a g e d a t a b a c k l o g a t t h e W D ( k b i t ) C o n t r o l p a r a m e t e r V E R S - O N H D O - O N E O T - O N P F N G A N (a) Data backlog at the wireless devi ce versus V 1 0 0 2 0 0 3 0 0 4 0 0 5 0 0 6 0 0 0 5 0 1 0 0 1 5 0 2 0 0 2 5 0 3 0 0 3 5 0 4 0 0 4 5 0 5 0 0 w i t h o u t f e e d b a c k A v e r a g e d a t a b a c k l o g a t t h e A P ( k b i t ) C o n t r o l p a r a m e t e r V E R S - O N H D O - O N E O T - O N P F N w i t h f e e d b a c k (b) Data backlog at the access point versus V Fig. 4. Impact of control parameter V on av erage data backlog in steady state Jain’ s index is u sed to measure fairness amon g WDs [ 13], [30]. W e observe fr om Fig. 3 (a) that HDO- ON has almost the same high fairness with ERS-ON alg orithm, which is bar e ly affected by the choice of V . Howe ver, with less con cern on the heterogeneity , HDO-ON achieves the high fairness at the cost of trem endous throu g hput. Furthermor e, Fig. 3(b) shows the fairness o f T ype-I a n d T yp e-II devices, where V is set as 300. On one han d, w e ca n s ee fro m EOT -ON, PFN, and GAN that heter ogeneo u s battery capacities would lea d to an uneven offloading opp ortunity . Different from the ab ove schemes, our propo sed ERS-ON algorithm strikes a good bala n ce between T ype - I and T ype - II devices, showing its su periority in hand ling systems with heterog eneous WDs. On the o ther han d , th e near to one Jain’ s in dex also indicates that ERS-ON can also well tackle the do ubly near-far pr oblem caused b y different d i . Although higher thro ughpu t can b e achieved by cho osing a larger V , it is n ot always better f o r the ERS-ON algor ithm to do so. As shown in Fig. 4, the increase of V would also result in linear growth o f data backlogs at both the WD and the AP . By jointly con sidering Figs. 2, 3 a n d 4, we can obser ve 10 0 . 0 0 5 0 . 0 1 0 0 . 0 1 5 0 . 0 2 0 0 . 0 2 5 2 5 4 2 5 5 2 5 6 2 5 7 2 5 8 2 5 9 2 6 0 2 6 1 2 6 2 A v e r a g e t h r o u g h p u t ( k b p s ) F e e d b a c k o v e r h e a d ( s ) E R S - O N w i t h c o m p l e t e N S I E R S - O N , m = 4 E R S - O N , m = 8 E R S - O N , m = 1 2 Fig. 5. Impact of ǫ and m on system avera ge throughput that the utility-backlog perform ance follows the [O(1/V) ,O(V)] tradeoff, which verifies Theo rem 3 and 5. B esides, the results also pr ovide guide lines for the design of data buf fer lengths of WDs in I IoT , since an app ropriate V can min imize the cost of embed ding lengthy sto r age spaces given a fixed throug hput expectation. B y using ERS-ON algorithm, as depicted in Fig . 4(a), we can keep the d a ta buffer len gth at the WD to a small lev el co mpared with b enchmar ks, especially when V is large. In Fig. 4(b), the curve for GAN is drop ped since its qu e u e length at the AP increases as time go es by and never reaches a steady state. It can be ob served that EOT -ON maintains sho r ter data backlogs at the AP side. Th is is because its volume of offloading data is much less than ERS-ON. Furth e r more, we also ob serve that sche m e with NSI feedb ack has a sho rter data backlog at the AP than one withou t. For implem entation consideratio ns, the impact of ǫ and m o n average thro ughp ut is fu rther ev aluated. W e set ǫ to vary from 0.005s to 0.0 25s, and carry out simu lations under different compulsor y fe e d back intervals. Fig. 5 shows that the av erage thro ughpu t linear ly reduces as ǫ increases. This is be- cause the NSI f e edback proce ss tak es up more time originally assigned fo r offloading when ǫ becom es larger . Compared with m = 8 and m = 12 , ERS-ON with m = 4 achieves a hig her throug hput, which correspo nds to the con c lusion in Theorem 5. Besides, in Fig. 5, ERS-ON with complete NSI feedback represents that WD has to uplink their NSI in e very slot. Its throughpu t perfo rmance ou tperfor ms the others when ǫ = 0 . 00 5 s . Ho wev er , the a c hiev able thr ough p ut decreases rapidly as ǫ grows, and gets w orse than ERS-ON with m = 12 when ǫ = 0 . 02 5 s. This reveals th at more NSI co ntributes to the optim ization of resource allocatio n when the overhead of f e edback is small. Meanwhile, many re so urces would be wasted by co mplete NSI fe e dback when the signaling cost is relativ ely large. I n this case, it is even better to ch oose an approp riately large m . Although the above sections on ly c o nsider the scenario of a single AP , the proposed algorithm can be readily extended to the scen ario of mu ltiple cellular base stations by applying frequen cy reuse techniqu e [36]. As th e n ame suggests, the technique utilizes a fractio n of the total frequ ency band in each cell, such that no two neighbo r cells use the same f r equency . As a result, inter-cell interfe rence can be re d uced, an d each cell can run the prop osed Algorithm 1 independently with its allocated band width. V I . C O N C L U S I O N Giv en th e data collection a nd offloading in WPT - MEC based heterogeneo us IIoT systems, we h av e p roposed an energy-aware resource scheduling algorithm for thro ughp ut maximization and offloading fairness. The perform a n ce of such an algorithm was analyzed un der a typical scen ario, where overhead and delay of feedbac k s were non- negligible. Simulations show that the propo sed algo r ithm can ach iev e asymptotic optimality , and effecti vely tackle the doubly near - far pr oblem as well as the unfairness caused by hetero geneou s battery cap a bilities. As a result, the use of th e algor ithm is fully justified by its merits on high th rough put, fairness and perpetua l oper a tion in implementation . The in tegration o f th e m achine-to- machine (M2M) commu - nications to the wireless powered MEC ne twork is prom is- ing to tac kle the scalab ility pro blem in large-scale app lica- tions [37]. In such a scenario , the prop osed algor ith m is still valuable. W e can first divide I IoT d evices into different clu sters accordin g to their proximity and choose th e de vice with the best ch annel con d ition in each cell to ser ve as the cluster head. Th e AP only n eed to schedule th ose clu ster heads for data offloading with the pro posed algorithm, while the oth er devices m igrate their d ata to nearb y cluster heads throug h M2M interaction s. By this way , th e computatio nal co mplexity at th e A P can b e broug ht down, and th e f eedback of NSI can also b e reduced . Ho wever , M 2M commu nication b rings interferen ce fo r the data offloaded to the AP . How to le vera ge spatial r euse to coord inate the schedulin g leaves for futur e work. A P P E N D I X A Note that for any x ≥ 0 , y ≥ 0 , z ≥ 0 , the following inequality ([ x − y ] + + z ) 2 ≤ x 2 + y 2 + z 2 + 2 x ( z − y ) . (27) always holds. Squar ing both sides of (9), summing over i ∈ N , dividing both sides by 2 and c o mbining (27), we ob tain 1 2 X i ∈N [ Q 2 i ( t + 1) − Q 2 i ( t )] ≤ 1 2 X i ∈N [ c 2 i ( t ) + a 2 i ( t )] + X i ∈N Q i ( t )[ a i ( t ) − c i ( t )] ≤ 1 2 X i ∈N [( c max i ) 2 + ( A max i ) 2 ] + X i ∈N Q i ( t )[ a i ( t ) − c i ( t )] . (28) Similarly , using (5) an d (10), we have 11 1 2 X i ∈N 2 [( E i ( t + 1) − θ i ) 2 − ( E i ( t ) − θ i ) 2 ] ≤ 1 2 X i ∈N 2 [( e H i ( t )) 2 + e 2 i ( t )] + X i ∈N 2 [ E i ( t ) − θ i ][ e H i ( t ) − e i ( t )] ≤ 1 2 X i ∈N 2 [( e H i, max ) 2 + ( P max i T ) 2 ] + X i ∈N 2 [ E i ( t ) − θ i ][ e H i ( t ) − e i ( t )] , (29) and 1 2 X i ∈N [ S 2 i ( t + 1) − S 2 i ( t )] ≤ 1 2 X i ∈N [ r 2 i ( t ) + (min { c i ( t ) , Q i ( t ) } ) 2 ] + X i ∈N S i ( t )[min { c i ( t ) , Q i ( t ) } − r i ( t )] ≤ 1 2 X i ∈N [ r 2 i ( t ) + c 2 i ( t )] + X i ∈N S i ( t )[ c i ( t ) − r i ( t )] ≤ 1 2 X i ∈N [( r max i ) 2 + ( c max i ) 2 ] + X i ∈N S i ( t )[ c i ( t ) − r i ( t )] (30) Substituting (28)-(3 0) into ( 12) yield (15). T aking expecta- tion of the L yap unov drif t condition ed o n Θ ( t ) and sub tracting V E { P i ∈N U i ( a i ( t )) | Θ ( t ) } to b oth sides proves the result. A P P E N D I X B By substituting (2) into the objectiv e function of pr oblem P2 , the p roblem can be refo rmulated into minimizing X i ∈N 2 [ S i ( t ) − Q i ( t )] c i ( t ) − X i ∈N 2 [ E i ( t ) − θ i ] e i ( t ) + X i ∈N 1 [ S i ( t ) − Q i ( t )] c i ( t ) + µ 0 ( t ) X i ∈N 2 [ E i ( t ) − θ i ] ξ i P 0 h i ( t ) T . (31) The last te r m in (3 1) a dec r easing fun ction of µ 0 ( t ) since P i ∈N 2 [ E i ( t ) − θ i ] ξ i P 0 h i ( t ) T is a non-positive constan t. For any WD i ∈ N t ∩ N 1 , we can choose µ i ( t ) = 0 to min imize th e term [ S i ( t ) − Q i ( t )] c i ( t ) and re-allo c ate the orig inally allocated time p ortion o f WD i for µ 0 ( t ) . F or arb itrary i ∈ N t ∩ N 2 , as c i ( t ) is a no n-decre asing fun c tio n of e i ( t ) and E i ( t ) < θ i , the term [ S i ( t ) − Q i ( t )] c i ( t ) − [ E i ( t ) − θ i ] e i ( t ) is non- decreasing with e i ( t ) . Hence, the m inimal value o f the first and second terms in (31) is 0 when e i ( t ) = 0 . In such co ndition, µ i ( t ) has no contribution to the value o f the objection fu nction. It is better to make µ i ( t ) = 0 and add the value of µ 0 ( t ) so as to minim ize the objective fu n ction. A P P E N D I X C Based on [31], for all σ > 0 , there exists a feasible stationary policy Π † that cho oses a † ( t ) , e † ( t ) and ˜ µ † ( t ) such that a † ( t ) , c † ( t ) and e H † satisfy: U ⋆ − E { X i ∈N U i ( a † i ( t )) } ≤ σ , E { a † i ( t ) − c † i ( t ) } ≤ σ , i ∈ N , E { c † i ( t ) − r i ( t ) } ≤ σ , i ∈ N E { e H † i ( t ) − e † i ( t ) } ≤ σ , i ∈ N 2 (32) The 0-additive appr oximation ensures b y (14) is as follows ∆ V ( Θ ( t )) ≤ B 1 − V E ( X i ∈N U i a † i ( t ) | Θ ( t ) ) + X i ∈N Q i ( t ) E n a † i ( t ) − c † i ( t ) | Θ ( t ) o + X i ∈N S i ( t ) E n c † i ( t ) − r i ( t ) | Θ ( t ) o + X i ∈N 2 [ E i ( t ) − θ i ] E { e H † i ( t ) − e i ( t ) † | Θ ( t ) } , (33) By substituting (32) into (33) and taking σ → 0 , we h av e ∆( Θ ( t )) − V E ( X i ∈N U i a i ( t ) | Θ ( t ) ) ≤ B 1 − V U ⋆ (34) Using iterated expectation s and telescop ing sums over t , dividing both sides by V t and rearrangin g terms yields 1 t t − 1 X τ =0 E ( X i ∈N U i a i ( t ) ) ≥ U ⋆ − B 1 V − E { L ( Θ (0)) } V t (35) Since E { L ( Θ (0)) } < ∞ holds, taking limits on both sides of (35) as t → ∞ proves the result. A P P E N D I X D The proof ca n be obtained by math ematical ind uction. W e first show that Q i ( t ) is deterministic b ound ed by V + A max i for all t . Th is clearly h olds for t = 0 as Q i (0) = 0 . Supp ose it holds for time slot t , then we sho w it als o holds for time slo t t + 1 . Consider the case when Q i ( t ) ≤ V . Since the buffer can in crease b y at most A max i at any slot, we hav e Q i ( t + 1) ≤ V + A max i . Then consider the other case when V < Q i ( t ) ≤ V + A max i . In this ca se, the d ata adm ission a i ( t ) sho uld choose to be zero according to (16). Hence, we ha ve Q i ( t + 1) = [ Q i ( t ) − c i ( t )] + ≤ Q i ( t ) ≤ V + A max i . In oth er words, Q i ( t + 1) ≤ V + A max i holds at t + 1 , which completes the pro of of the up per bound of Q i ( t ) . Similarly , we proceed to prove S i ( t ) ≤ V + A max i + c max i by mathematical ind uction. Again , it holds for t = 0 as S ( t ) = 0 at the beginn ing and we suppose it also hold s in time slot t . When S ( t ) ≤ V + A max i , fro m (10), we obtain S i ( t + 1) = [ S i ( t ) − r i ( t )] + + min { c i ( t ) , Q i ( t ) } ≤ S i ( t ) + c max i ≤ V + A max i + c max i . (36) Otherwise, in the case when S i ( t ) ≥ V + A max i , using the previously proven con clusion (20) yields S i ( t ) ≥ Q i ( t ) . Th is 12 means the correspon ding back log at the AP is larger than the queue length a t i -th WD, i.e . , i ∈ N t . In su c h a con dition, the AP will allocate no offl oading time for WD i according to Theo rem 1. Therefore, no da ta from WD i arriv e at the AP at time slot t , i.e., c i ( t ) = 0 . W e have S i ( t + 1) = [ S i ( t ) − r i ( t )] + ≤ S i ( t ) ≤ V + A max i + c max i . (3 7) From ( 3 6) an d (3 7), we can prove th at S i ( t + 1 ) ≤ V + A max i + c max i holds at time slot t + 1 . This th us conclude s the proof. A P P E N D I X E If θ i is set according to (22) and E i ( t ) ≤ P max i T at slot t , we obtain E i ( t ) − θ i ≤ − ( V + A max i ) c max i e min i (38) Considering arbitrar y WD i ∈ N 2 , we have [ S i ( t ) − Q i ( t )] c i ( t ) − [ E i ( t ) − θ i ] e i ( t ) ≥ − Q i ( t ) c i ( t ) + ( V + A max i ) c max i ≥ 0 (39) where th e second inequality h olds becau se (20) is always satisfied. According to the proof in Theorem 1, WD i will not be allocated time f or of floading if (39) ho lds. This proves that E i ( t ) > P max i T is guar a nteed under the gi ven θ i , thus we have E i ( t ) + e H i ( t ) > P i ( t ) T . A P P E N D I X F Before the pr oof of Theorem 5, we fir st pr ove the f ollowing theorem throu gh mathematical induction . Theor em 6: At each time slot, the dif ference b etween the backlog s at each WD i ∈ N and the AP is strictly bounded , which is given by S i ( t ) − Q i ( t ) ≤ 2 c max i . (40) Pr oo f: The upp er boun d holds at slot t = 0 giv en th at S i ( t ) = Q i ( t ) = 0 , ∀ i ∈ N . Suppose it hold s at time slot t . Then, if S i ( t ) − Q i ( t ) < 0 , we h ave Q i ( t + 1) = [ Q i ( t ) − c i ( t )] + + a i ( t ) ≥ Q i ( t ) − c i ( t ) + a i ( t ) . (41 ) Combining (36) and ( 41), we see th at S i ( t + 1) − Q i ( t + 1) ≤ S i ( t ) − Q i ( t ) + 2 c i ( t ) − a i ( t ) < 2 c i ( t ) − a i ( t ) ≤ 2 c max i On the o ther hand, if 0 ≤ S i ( t ) − Q i ( t ) ≤ 2 c max i , c i ( t ) = 0 accordin g to The orem 1. Hence, we h av e S i ( t + 1) − Q i ( t + 1) = [ S i ( t ) − r i ( t )] + − Q i ( t ) − a i ( t ) ≤ S ( t ) − Q i ( t ) ≤ 2 c max i As a r esult, the up per bound also hold s at time slot t + 1 , which conclud e s the proof. Owing to the feedb ack m echanism of queue lengths, part of the offloading oppor tunity will be occup ie d . Hen ce, only (1 − P i ∈M t ǫ i ) T can be used fo r WPT an d offloading in each time du ration. This will h av e a d irect influence on c i ( t ) and e H i as can be seen from (2) and (3). Let F ( t ) de n ote the function in side th e expectation on the RHS of the drift bound in (14). Similar to F ( t ) , we are motiv a ted to minimize th e expectation of b F ( t ) under the feed back mechanism, where b F ( t ) = − V X i ∈N U i a i ( t ) + X i ∈N b Q i ( t )[ a i ( t ) − (1 − X i ∈M t ǫ i ) c i ( t )] + X i ∈N S i ( t )[(1 − X i ∈M t ǫ i ) c i ( t ) − r i ( t )] + X i ∈N 2 [ E i ( t ) − θ i ] [(1 − X i ∈M t ǫ i ) e H i ( t ) − e i ( t )] . (42) Since the real-time queue leng th is always larger than th e approx imate queue backlog, combined with (25), we ha ve b Q i ( t ) ≤ Q i ( t ) ≤ b Q i ( t ) + mA max i (43) Therefo re, we can derive that F ( t ) − b F ( t ) = X i ∈N [ Q i ( t ) − b Q i ( t )] a i ( t ) + X i ∈M t ǫ i X i ∈N S i ( t ) c i ( t ) + X i ∈N [ b Q i ( t )(1 − X i ∈M t ǫ i ) − Q i ( t )] c i ( t ) + X i ∈M t ǫ i X i ∈N 2 [ E i ( t ) − θ i ] e H i ( t ) ≤ m X i ∈N ( A max i ) 2 + X i ∈M t ǫ i X i ∈N [ S i ( t ) − Q i ( t )] c i ( t ) ≤ m X i ∈N ( A max i ) 2 + 2 X i ∈N ǫ i X i ∈N ( c max i ) 2 (44) where the first inequa lity holds since E i ( t ) ≤ θ i and (43) are satisfied, and the second inequ ality is de riv ed from Th eorem 6. Submitting (44) into (14), we have ∆ V ( Θ ( t )) =∆( Θ ( t )) − V E ( X i ∈N U i a i ( t ) | Θ ( t ) ) ≤ B 2 + B 3 X i ∈N ǫ i + E { b F ( t ) | Θ ( t ) } , (45) where B 2 = B 1 + m P i ∈N ( A max i ) 2 and B 3 = 2 P i ∈N ( c max i ) 2 . W e can then prove this theo rem by using the similar a rgu ment in the pr o of of theorem 2. R E F E R E N C E S [1] E. Sisinni, A. Sai fullah, S. Han et al. , “Industri al internet of thing s: Challe nges, opportuni ties, and directi ons, ” IEEE T rans. Ind. Inf. , vol. 14, no. 11, pp. 4724–4734, Nov . 2018. [2] K. W ang, Y . W ang, Y . Sun et al. , “Green i ndustrial inte rnet of things archit ecture : An energy-e ffic ient perspecti ve, ” IEEE Commun. Mag . , vol. 54, no. 12, pp. 48–54, Dec. 2016. [3] J. W an, S. T ang, Z. Shu et al. , “Software-de fined industria l i nternet of things in the context of industry 4.0, ” IEEE Sensors J. , vol. 16, no. 20, pp. 7373–7380, Oct. 2016. [4] I. Bi sio, C. Garib otto, A. Gratta rola et al. , “Exploiti ng conte xt-a war e capabi litie s over the internet of thi ngs for industry 4.0 applicatio ns, ” IEEE Netw . , vol. 32, no. 3, pp. 101–107, May 2018. [5] Y . Fu, S. W ang, C. W ang et al. , “ Artificia l intell igence to manage netw ork traffic of 5G wireless networ ks, ” IE EE Ne tw . , vol. 32, no. 6, pp. 58–64, Nov . 2018. [6] H. Y e, L. Liang, G. Y . Li et al. , “Machine lea rning for vehicu lar net- works: Recent adv ance s and applica tion exampl es, ” IEEE V eh. T echnol. Mag . , vol. 13, no. 2, pp. 94–101, June 2018. 13 [7] M. Tseng, T . Edmunds, and L. Canaran, “Introduction to Edge Com- puting in IIoT, ” Industrial Internet Consortium (IIC) White Paper , T ech. Rep., June 2018. [8] M. Aazam, S. Zeadally , and K. A. Harras, “Deployi ng F og Computing in Industrial Internet of Things and Industry 4.0, ” IEEE T rans. Ind. Inf. , vol. 14, no. 10, pp. 4674–4682, Oct. 2018. [9] K. Kaur, S. Garg, G. S. Aujla et al. , “Edge computing in the industrial interne t of things en vironmen t: Softwa re-defined- networ ks-based edge - cloud interpl ay , ” IEEE Commun. Mag. , vol. 56, no. 2, pp. 44–51, Feb . 2018. [10] Y . Mao, J. Zhang, S. H. Song et al. , “St ochasti c joint ra dio and com- putati onal re source management for multi-user mobile-edge computing systems, ” IEEE T rans. W ir eless Commun. , vol . 16, no. 9, pp. 5994–600 9, Sept. 2017. [11] X. L yu, H. Tian, W . Ni et al. , “Energy-ef ficient admissio n of delay- sensiti ve tasks for mobile edge computing, ” IEEE T rans. Commun. , vol. 66, no. 6, pp. 2603–2616, June 2018. [12] J. Zhang, X. Hu, Z. Ning et al. , “Energy- latenc y tradeof f for energy- aw are offloadi ng in mobile edge computing net works, ” IEEE Internet Things J. , vol. 5, no. 4, pp. 2633–2645, Aug 2018. [13] X. L yu, W . Ni, H. T ian et al. , “Optimal schedule of mobile edge computing for internet of things using partial information, ” IEEE J. Sel. Area s Commun. , vol. 35, no. 11, pp. 2606–2615, Nov . 2017. [14] Y . Mao, J. Zhang, and K. B. Letaief, “Dynamic computation offloading for mobil e-edge computing with energy harv esting de vices, ” IEEE J. Sel. Areas Commmun. , vol. 34, no. 12, pp. 3590–3605, Dec. 2016. [15] H. Ju and R. Zhang, “Throughput maximiza tion in wireless po wered communicat ion networks, ” IEEE Tr ans. W irele ss Commun. , vol. 13, no. 1, pp. 418–428, Jan. 2014. [16] Q. W u, M. T ao, D. W . K. Ng et al. , “Energy-ef ficien t resource alloca tion for wi reless po wered communication network s, ” IEEE T rans. W ir eless Commun. , vol. 15, no. 3, pp. 2312–2327, Mar . 2016. [17] J. Y ang, Q. Y ang, K. S. Kwak et al. , “Power-de lay tradeof f in wireless po wered communication networks, ” IEEE T rans. V eh. T ech nol. , vol. 66, no. 4, pp. 3280–3292, Apr . 2017. [18] S. Mao, S. Leng, K. Y ang et al. , “Energy ef ficienc y and delay tradeof f in multi-user wireless po wered mobile-edge computing systems, ” in Pr oc. IEEE GLOBE COM , Dec. 2017, pp. 1–6. [19] Z. Hadzi-V elk ov , I. Nikoloska, H. Chingoska et al. , “Opport unistic scheduli ng in wireless powe red communicat ion networks, ” IEEE T rans. W irel ess Commun. , vol. 16, no. 6, pp. 4106–4119, June 2017. [20] Y . L. C he, L. Dua n, and R. Zhang, “Spati al throughput maximiza tion of wireless po wered communicati on netwo rks, ” IEEE J. Sel. Areas Commmun. , vol. 33, no. 8, pp. 1534–1548, Aug. 2015. [21] S. Bi and Y . J. Zhang, “Computat ion rate maximiza tion for wireless po wered mobile-edg e computing with binary co mputation of floading , ” IEEE T rans. W irel ess Commun. , vol. 17, no. 6, pp. 4177–4190 , June 2018. [22] X. Hu, K. W ong, and K. Y ang, “Wir eless powere d cooperation-a ssisted mobile edge computing, ” IEEE T rans. W ir eless Commun. , vol. 17, no. 4, pp. 2375–2388, Apr . 2018. [23] F . W ang, J. Xu, X. W ang et al. , “Joint offloadin g and computing optimiza tion in wireless po wered mobile-edge computing systems, ” IEEE T rans. W ireless Commun. , vol. 17, no. 3, pp. 1784–1797, March 2018. [24] Z. Hou, H. Chen, Y . Li et al. , “Incenti ve mechanism design for wireless ener gy harvesti ng-based inte rnet of things, ” IEE E Internet Things J . , vol. 5, no. 4, pp. 2620–2632, Aug. 2018. [25] X. Lyu, W . Ni, H. Tian et al . , “Di stribu ted online optimizatio n of fog computing for selfish devic es with out-of-dat e informati on, ” IEEE T rans. W irel ess Commun. , vol. 17, no. 11, pp. 7704–7717, Nov . 2018. [26] C. Ren, X. L yu, W . N i et al. , “Distribut ed online learni ng of fog computing under non-uniform devic e cardinality , ” IE EE Internet Things J . , vol. 6, no. 1, pp. 1147–1159 , Feb . 2019. [27] X. Ly u, C. Ren, W . Ni et al. , “Mult i-timesca le decentraliz ed onli ne orchestra tion of softwar e-defined networks, ” IEEE J. Sel. Areas Comm- mun. , vol. 36, no. 12, pp. 2716–2730, Dec. 2018. [28] Z. Y ang, W . Xu, Y . Pan et al. , “Optimal fairness-a ware time and power alloc ation in wireless po wered communication n etwork s, ” IEEE T rans. Commun. , vol. 66, no. 7, pp. 3122–3135, July 2018. [29] L. Huang and M. J. Neely , “Utili ty optimal scheduling in ener gy- harve sting netw orks, ” IEEE/ACM T rans. Netw . , vol. 21, no. 4, pp. 1117– 1130, Aug. 2013. [30] H. SH I, R. V . Prasad, E. Onur et al. , “Fairness in wirel ess net- works:i ssues, measures and chall enges, ” IEEE Commun. Survey s & T utorials , vol. 16, no. 1, pp. 5–24, First 2014. [31] M. J. Neely , “Stochasti c network optimizati on with applic ation to communicat ion and queueing systems, ” Synthesis Lectur es on Commun. Netw . , vol. 3, no. 1, pp. 1–211, 2010. [32] S. Boyd and L. V andenber ghe, Con vex Optimization . UK: Cambridge Uni v . Press, 2004. [33] M. Grant and S. Boyd. (2010, Apr .) Cvx: Matla b software for discipl ined con ve x programming (web page and s oftware). [Online ]. A va ilabl e: http://cvxr . com/cvx [34] 3GPP , “Cel lular system support for ultra-lo w comple xity and lo w throughput Internet of Things, ” Rep. TR 45.820 v13.1.0, T ech. Rep., Nov . 2015. [35] ——, “Study on NR Indust rial Internet of Things, ” Rep. TR 38.825 v16.0.0, T ech. Rep., Mar . 2019. [36] G. Nie, H. Tia n, C. Sengul et al. , “Forwa rd and bac khaul link opti- mizatio n for energy effic ient ofdma small cell net works, ” IEEE T rans. W irel ess Commun. , vol. 16, no. 2, pp. 1080–1093, Feb 2017. [37] A. V irdis, C. V allati , G. Nardini et al. , “D2D communica tions for lar ge- scale fog platforms: Enabli ng direct M2M interact ions, ” IEEE V eh. T echnol. Mag . , vol. 13, no. 2, pp. 24–33, June 2018.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment