Optimal State Estimation Synthesis over Unreliable Network in Presence of Denial-of-Service Attack: an Operator Framework Approach
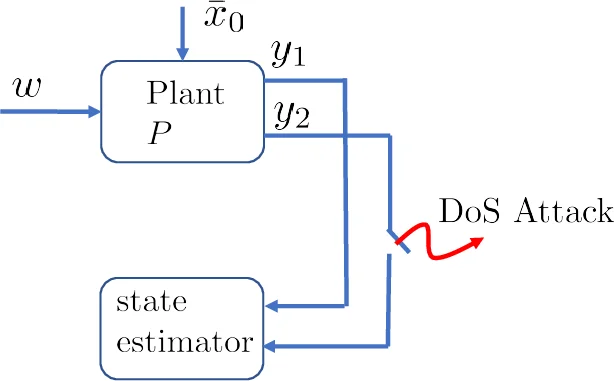
In this paper, we consider the problem of state-estimation in the presence of Denial-of-Service (DoS) attack. We formulate this problem as an state estimation problem for a plant with switching measured outputs. In the absence of attack, the state-estimator has access to all measured outputs, however, in the presence of attack, only a subset of all measurements are made available to the state-estimator. We seek to find an state-estimator that results in the minimum estimation error for the worst-case attack strategy. First, we parameterize the set of all state-estimators that result in stable estimation error for the worst-case attack scenario. Then, we will show that any state-estimator in this set can be written as a generalized Luenberger observer with an appropriately defined observer-gain. This observer-gain, in general, can be an operator and possibly unbounded as opposed to the classical static observer-gain. Furthermore, we will show that finding the optimal state-estimator that results in the minimum estimation error can be cast as a convex program over the set of stable factors of the observer operator-gain. This optimization in, in fact, linear programming and tractable.
💡 Research Summary
This paper addresses the problem of remote state estimation for linear plants when a Denial‑of‑Service (DoS) attack intermittently blocks a subset of sensor measurements. The authors model the attack as a switching signal σ(t) that selects which measurement channels are available at each time step, thereby turning the plant into a Linear Switching System (LSS). Unlike most existing works that rely on stochastic models and finite‑horizon cost functions, this study adopts a deterministic, infinite‑horizon framework and assumes the attacker has full knowledge of the plant dynamics and the past switching actions. The estimator, however, only knows the attacker’s actions causally (i.e., up to the current time).
The first major contribution is a complete parametrization of all stable state‑estimators. Lemma 9 shows that any estimator Tσ mapping the available measurements yσ to an estimate x̂ can be expressed together with an auxiliary operator Xσ such that
Comments & Academic Discussion
Loading comments...
Leave a Comment