Reversible Privacy Preservation using Multi-level Encryption and Compressive Sensing
Security monitoring via ubiquitous cameras and their more extended in intelligent buildings stand to gain from advances in signal processing and machine learning. While these innovative and ground-breaking applications can be considered as a boon, at the same time they raise significant privacy concerns. In fact, recent GDPR (General Data Protection Regulation) legislation has highlighted and become an incentive for privacy-preserving solutions. Typical privacy-preserving video monitoring schemes address these concerns by either anonymizing the sensitive data. However, these approaches suffer from some limitations, since they are usually non-reversible, do not provide multiple levels of decryption and computationally costly. In this paper, we provide a novel privacy-preserving method, which is reversible, supports de-identification at multiple privacy levels, and can efficiently perform data acquisition, encryption and data hiding by combining multi-level encryption with compressive sensing. The effectiveness of the proposed approach in protecting the identity of the users has been validated using the goodness of reconstruction quality and strong anonymization of the faces.
💡 Research Summary
The paper addresses the growing tension between ubiquitous video surveillance in intelligent buildings and the privacy requirements imposed by regulations such as the GDPR. Existing privacy‑preserving approaches either permanently anonymize data (making it irreversible) or rely on computationally heavy techniques such as differential privacy or homomorphic encryption, which are unsuitable for real‑time monitoring. To overcome these drawbacks, the authors propose a novel, reversible, multi‑level privacy‑preserving framework that simultaneously performs data acquisition, compression, encryption, and embedding of de‑identification information using compressive sensing (CS).
The core idea is to treat each video frame as a vector s ∈ ℝᴺ, identify privacy‑sensitive pixel indices (e.g., face regions) forming a set C, and then perturb the standard CS measurement matrix A with a ternary mask M. For indices in C, each entry of M is set to 0 with probability p or to −2·Aᵢⱼ with probability 1 − p; all other entries remain zero. The perturbed matrix  = A + M is used to acquire compressed measurements ỹ =  s. The mask M is encoded as a ternary vector w, which is linearly embedded into the measurements using an embedding matrix B (derived from DCT rows) with a controlled power constraint ‖Bw‖₂ ≤ P_E. The transmitted signal therefore becomes
y_w = (A + M) s + B w = H x + B w + n,
where x are the sparse coefficients of s in a wavelet basis Φ, H = AΦ, and n = M s acts as structured noise.
Three user classes are considered:
- Eavesdropper – knows neither A nor B; cannot recover any information.
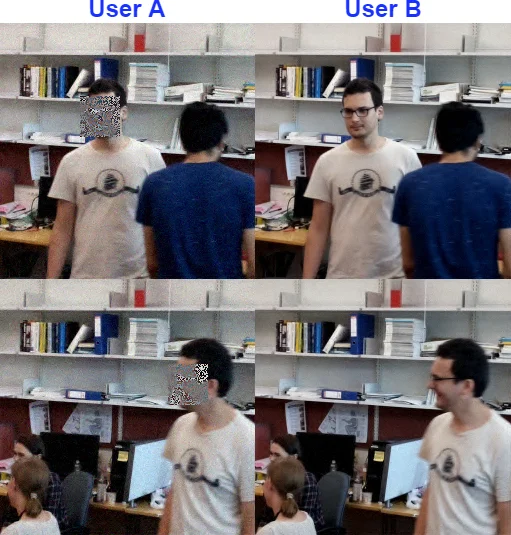
- Semi‑authorized user (User A) – possesses A but not the mask w. This user applies a standard ℓ₁‑minimization CS decoder to recover a version of the frame where non‑sensitive regions are reconstructed with high fidelity, while the masked regions (faces) remain heavily degraded and unrecognizable.
- Fully authorized user (User B) – holds an additional key k_b that allows extraction of w. By applying a null‑space matrix F (so FB = 0) to y_w, the embedded component B w is eliminated, yielding a cleaned measurement ỹ = F H x + z. A first ℓ₁‑reconstruction provides an estimate x̃, from which w is estimated via least‑squares, thresholded to recover the ternary mask, and finally used to reconstruct M. With the recovered M, a second CS reconstruction restores the original frame with near‑original quality, including the previously masked faces.
Algorithms for both user types are explicitly described (Algorithm 1 for semi‑authorized, Algorithm 2 for fully authorized). The reconstruction for the fully authorized user involves: (i) annihilator filtering, (ii) preliminary ℓ₁ recovery, (iii) least‑squares estimation of w, (iv) hard‑thresholding to retrieve the ternary mask, (v) reconstruction of M, and (vi) a final ℓ₁ optimization that incorporates the corrected measurement matrix A + M.
Implementation details focus on practical memory constraints. Instead of storing full random Gaussian matrices, the authors construct A by selecting rows from a Noiselet transform and permuting them, while B is built from DCT rows. The sparsifying basis Φ is a 2‑D wavelet transform, chosen for its incoherence with Noiselet and DCT bases, ensuring good CS performance and inherent security.
Experimental validation uses two 10‑minute video sequences (3,219 frames total) captured in an office environment. Measurement rates (MR) ranging from 0.3 to 0.8 are tested. Results (Table I) show that for semi‑authorized users the PSNR of masked (face) regions stays around 9–10 dB across all MRs, rendering faces unrecognizable, while the rest of the scene achieves 21–43 dB, only 3–5 dB lower than the fully authorized user. Fully authorized users obtain PSNRs of 30–42 dB for the whole frame, indicating high‑quality reconstruction of both sensitive and non‑sensitive content.
To assess resistance against automated identification, a pre‑trained CNN from the dlib library (99 % accuracy on standard datasets) is applied to the reconstructed frames. The semi‑authorized reconstructions dramatically reduce recognition rates, confirming strong anonymization, whereas the fully authorized reconstructions retain recognizability.
Key contributions of the work are:
- Unified acquisition‑encryption‑embedding: CS measurement, encryption (via random matrix A), and steganographic embedding of the de‑identification mask are performed in a single linear operation, drastically reducing computational load.
- Multi‑level reversible de‑identification: By embedding the perturbation mask, the system supports three distinct access levels without requiring a separate secure side‑channel.
- Resource‑efficient implementation: Use of structured transforms (Noiselet, DCT, Wavelet) avoids the prohibitive memory footprint of full random matrices, making the approach viable for real‑time video streaming.
Limitations include the need to tune the perturbation probability p and embedding power a to balance privacy strength against reconstruction quality, and reliance on accurate detection of sensitive regions (face detection) for mask placement. The current scheme assumes static keys; dynamic key management and periodic re‑keying would be necessary for long‑term deployments.
Future research directions suggested are: (i) integrating secure key‑exchange protocols for dynamic mask updates, (ii) exploring non‑linear or adaptive perturbation strategies to further harden the system against sophisticated attacks, (iii) extending the framework to non‑visual data such as biomedical signals, and (iv) hardware acceleration (FPGA/ASIC) to achieve true real‑time performance in edge devices.
In summary, the paper presents a compelling, mathematically grounded solution that reconciles the need for high‑quality video analytics with stringent privacy requirements. By leveraging the intrinsic randomness of compressive sensing and embedding de‑identification information directly into the compressed stream, it delivers a reversible, multi‑level privacy mechanism that is both computationally lightweight and robust against modern recognition attacks, paving the way for privacy‑aware surveillance in smart environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment