Security Vulnerability of FDD Massive MIMO Systems in Downlink Training Phase
We consider downlink channel training of a frequency division duplex (FDD) massive multiple-input-multiple-output (MIMO) system when a multi-antenna jammer is present in the network. The jammer intends to degrade mean square error (MSE) of the downli…
Authors: Mohammad Amin Sheikhi, S. Mohammad Razavizadeh
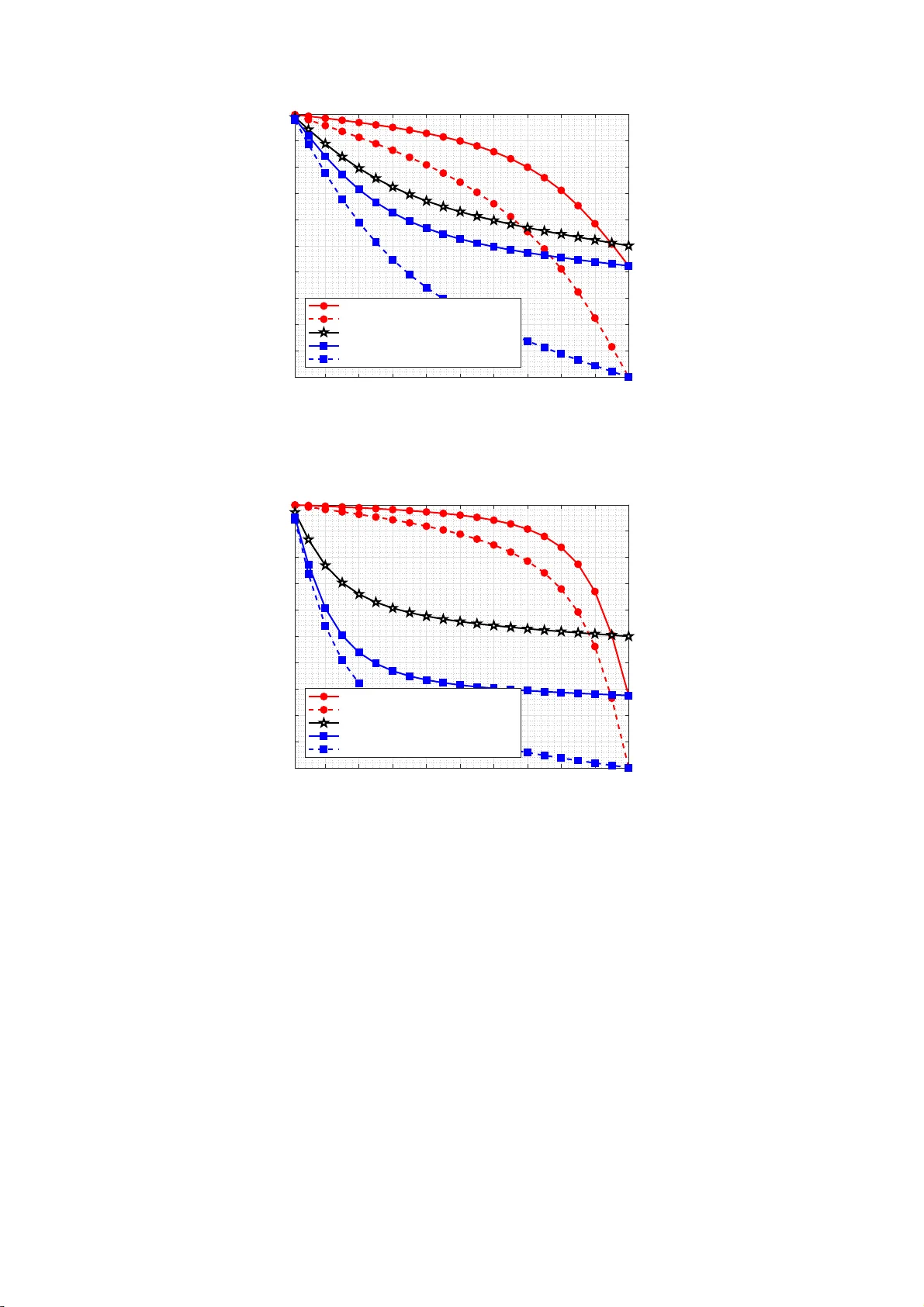
Security V ulnerabilit y of FDD Mass i v e MIMO Systems in Do wnlink T raining Phase Mohammad Amin Sheikhi, and S. Mohammad Razavizadeh School of Electrical Engineering Iran Uni v ersity of Science and T echnology (IUS T) ee.sheikhi@gmail.com, smrazavi@ieee.org Abstract W e consider downlink channel training of a frequency di vision duplex (FDD) massiv e multiple-input- multiple-output (MIMO) system when a multi-ant enna jammer is present in the network. T he jammer intends to degrade mean square error (MSE) of the downlink channel training by designing a n atta ck based o n second-order stat istics of it s channel. The channels are assumed to be spatially co rrelated. First, a closed-f orm expression for the channel estimation MSE is derived and then the jammer determines the conditions under which the MSE is max imized. Numerical results demonstrate that the proposed jamming can sev erely increase the estimation MSE even if t he optimal training signals with a large number o f pilot symbols are used by the legitimate system. Index T erms Massi ve MIMO, FDD, Phy sical La y er Security , Jamm ing, Spatial Corre lation, Channel Estimation I . I N T RO D U C T I O N M ASSIVE MIMO is known as one of the main technologies in n ext generation of wireless networks (5G) in which the base stations (BS) in the cellular networks are s u pplied with a very large number of antennas [1]. This technology brings diff erent adv antages in the performance which spectral ef ficienc y (SE) imp rovement i s the most imp ortant one [2]. Massive MIMO can be deployed in two modes: frequency division duplex (FDD) and time di vision duplex (TDD). In contrast t o the T DD m assive MIMO systems, i n the FDD mode, t h e SE does not always improve with the nu m ber of BS antennas and it may ev en degrade if the number of BS antennas gets too large. The reason is due to lar ge overhead in downlink traini ng of the FDD massiv e MIMO systems [3]. On the other hand, in th e TDD mode, channel reciprocity can be utilized to estimate the downlink channel gain from the uplink trainin g. B ut there are some problems i n the TDD mode, for example, pilot con tamination and calibration errors caused by hardware impairment can degrade the TDD massive MIMO sy stems performance significantly [4], [5]. Besides, the FDD mode has some adva ntages over the TDD mo de, e.g . l ower l atency and better performance in sym metric traffic services. More importantly , most of t he currently deployed systems are working in th e FDD mode and economically it will be m ore ef ficient for the new generation networks to operate in the FDD mo de. Therefore, using the FDD mode in massive MIM O sy stems has b een an important research topic in recent years. One of the important problem s in th i s regard is reducing the downlink training overhea d that h as been in vestigated in some papers, e.g. [6]–[10]. Also, there are some works on improving the efficienc y o f FDD massive MIM O systems with some assum ptions about the channel model. For instance, the authors in [11] hav e considered a single-user FDD mas s iv e MIMO with a correlated channel and prop osed an algorithm to opt i mize the ener gy efficienc y of the sy s tem by adjusting training length and transm it power . Another main issue in 5G networks is the security concerns because of their h uge capacity and wider cove rage. Physical layer security is one of t h e most effecti ve approaches to solve t he security issues of wireless networks against eavesdropping and jamming attacks [12 ]. M assiv e MIMO has an int ri nsic security against passive eavesdropping [13]. But in the case of active eavesdroppers and jam mers, massive MIM O security is not guaranteed and could be vuln erable. This problem has been in v estigated extremely i n many works, e.g. [14]–[18]. In [14], the autho rs have consi dered a multi-user TDD massive MIMO system and demonstrated that how a lim ited-power sm art j ammer can perform an optimal attack in bo t h uplink channel estimation and data transmissio n to m inimize the uplin k spectral ef ficiency of the syst em. In [15], t he authors hav e explored the pilot con tamination attack by an activ e ea vesdropper in a mu lti-cell TDD m assive MIMO network. The secrecy rate is analyzed for m atched filter precoding and an artificial random n oise transmissio n strategy . In additi on, a precoder nu l l space design is proposed to secure the communicatio n against t he ea vesdropper . In [16], th e authors hav e studied an advanced full-dup lex adversary with a m assiv e array who tries to attack a TDD si ngle-user massive MIMO network. The adversary simul taneously performs ea vesdropping and jam ming. It i s shown t hat eve n with imperfect jammi ng channel estim ation and self- interference, the jammer can still disable con vention al physical layer protecting schemes. In [17], the authors hav e proposed an app roach to detect jammers in the TDD massive MIMO system s by e xploiting som e unu s ed pilots in the system and showed that by increasing the number of base s tation antennas and unused pil ots, the prop osed s cheme can detect the jammin g more ef ficiently . In [18], a robust j am ming-resistant receiver in the uplink o f a TDD mass ive MIMO network is designed which utilizes som e purposely u n used pil ot symbols in the training phase. All of the aforementi oned papers and other related references therein h ave assumed th e TDD mode for massive M IMO networks and as far as we know , no work in th e literature has considered the security is sues of FDD m assiv e MIM O systems. In this paper , we s tudy the security of m ass iv e MIMO sys tems in FDD mode. In parti cul ar , we consider downlink channel t rain i ng of an FDD m assiv e MIM O system when there is a multi-antenna jamm er i n the en vironm ent who tries to attack t he training phase and degrade the channel esti m ation performance. In contrast to many other papers in this field, we have taken into account the spatial correlation of the channels which makes the channel mo del more realistic. The jammer designs its att ack b ased on the second-order statistics of its channel. W e show that how a smart jam mer can efficiently attack the t raining phase and increase th e esti m ation error significantly . The mean square error (MSE) m aximization i s selected as the attack criterion and the o ptimal design of the jammer s ignal is analytically deriv ed. Numerical results illustrate that how much the proposed att ack can jeopardize the downlink training phase in this sys tem even if the BS us es optimal pilots for channel est i mation. This security vulnerabil i ty is shown to be more sev ere at st ronger correlated channels . The remainder of this paper is or gani zed as follows. In Section II, the system model is i ntroduced. Downlink channel training procedure i s presented i n Section III. In Section IV , t h e jamming s ignal desig n problem is formulated and solved. Numerical resul t s are giv en in Section V and in the end, Section VI p rovides the conclusion o f this paper . A. Nota tion Throughout the paper , we use bol dface uppercase to denote matrices, boldface lowerc ase for vectors and italic letters to denote scalars. ( . ) H represents conjugate transpos e and A ( i : j ) denotes a matrix contain ing columns i to j of a matrix A . E { . } is the expectation operator and v ∼ C N (0 , R ) represents circularly- symmetric complex Gaussian random vectors wi th zero mean and cov ariance matrix R . The L × L identity matrix is denot ed by I L . For two random matri ces x and y , the covariance matrix is represented by C x , y . I I . S Y S T E M M O D E L W e consider a single-cell network with a large-scale BS supplied with M >> 1 antennas and a single- antenna user-equipment (UE) in the p resence of a jammer who has N antennas. The network operates in the FDD mode. Therefore, for downlink channel estim ation, t he BS transmits a training sequence to the UE, then the UE est imates the channel gain and feedbacks its esti m ation to the BS. The BS transmits a pi lot signal, ϕ m with the length of L symbols from each of its transmit antennas. These pilots can be stacked into an M × L matrix called Φ . Unitary traini ng sequence w i th the same power at each of the pi lot symbol s is adopted in thi s paper , i.e. Φ H Φ = I L . W e assume that the jamm er has a prior kno w l edge of L and transmits a j amming sign al cont aining at least L s y mbols from each of its antennas. Th e signal transmi tted by the jammer can be collected i nto an N × L matrix called Z . The recei ved signal by the UE will be y = p LP b Φ H h + p LP j Z H g + w , (1) where P b is the BS t ransm it power in the t rain i ng phase, h ∈ C M × 1 is the channel gain from the BS to the UE, P j is t h e jamm er transmit power , g ∈ C N × 1 is t h e channel gain from the jam mer to the UE and w ∼ C N ( 0 , σ 2 I L ) m odels the thermal noise at th e UE. The channel gain from t h e BS to the UE i s assumed to be s p atially correlated. It is modeled as h ∼ C N (0 , R h ) where R h = E ( hh H ) i s the cova riance matrix of th e channel vector h . The same m odel is used for the channel gain from the jammer t o the UE, i .e. g ∼ C N (0 , R g ) . I I I . D O W N L I N K C H A N N E L E S T I M A T I O N The UE us es the receiv ed signal in (1) to est i mate h by mini mum m ean square error (MMSE) meth o d [19] th at yields ˆ h = C h , y C − 1 y , y y , (2) where the cov ariance matrices are computed as C h , y = p LP b R h Φ (3) C y , y = LP b Φ H R h Φ + LP j Z H R g Z + σ 2 I L . (4) The est imated channel gain di stribution is ˆ h ∼ C N (0 , ψ ) where the cov ariance matrix ψ is computed as ψ = R h Φ ( Φ H R h Φ + P j P b Z H R g Z + σ 2 LP b I L ) − 1 Φ H R h . (5) W e define the estimatio n error vector as ǫ = h − ˆ h that ǫ ∼ C N (0 , R h − ψ ) and t he av erage MSE per antenna (hereafter MSE) is compu t ed as M S E = 1 M E [ k ǫ k 2 2 ] . (6) By exploiting W ishart matrix properties in [20], t he MSE will be M S E = 1 M tr ( R h − ψ ) . (7) The eigen value decom position (EVD) of R h is R h = U h D h U H h where D h = diag ( λ h 1 , λ h 2 , ..., λ h M ) is a diagonal matrix containi ng the eigen values of R h in descending order and U h contains the correspond i ng eigen vectors. The BS do es not know about the jam mer presence and designs the pil o t matrix Φ t o minimi ze the MSE w i thout taki n g into account the effect of the jammer . In [9], it is shown that the optimal design of pi l ots to minimi ze the MSE is as follows Φ opt = arg min Φ 1 M tr ( R h − ψ ) = U h (1 : L ) . (8) In the next section, we will analyze t he estim ation performance with the above op t imal pilot desig n in the presence of our prop o sed jammer s ignal desig n . I V . J A M M E R A T TAC K S I G N A L D E S I G N In th i s section, we look at t he channel estim ation procedure from the j am mer’ s point o f view and show that how a sm art jammer wi t h a limited power can ef ficientl y design i ts attack signal, Z , to maximize the estimation error even if the BS us es t h e opt imal pilots as in (8). The jammer knows its channel cova riance matrix R g since it i s the second-order st at i stics of the channel and changes slowly over many coherence intervals. The eigen value decompo s ition (EVD) o f R g is R g = U g D g U H g where D g = diag ( λ g 1 , λ g 2 , ..., λ g N ) is a diagonal matrix contai n i ng the eigen values of R g in d ecreasing order and U g is corresponding eigen- vector matrix. The jam m er can desi gn the signal Z in different ways. Howe ver , in all designs, th e unitary signal structure with equal power at each of the sy mbols i s used, i.e. Z H Z = I L . The jam mer solves t he following opti mization problem to design its att ack signal Z opt = arg max Z 1 M tr ( R h − ψ ) . (9) s . t . Z H Z = I L The matrix Z opt that maxim izes the objective functi on in (9) mini mizes tr ( ψ ) . The following lemma giv es a sim ple equiv alent prob lem for (9) and and p resent s a s o lution for it. Lemma 1. An equivalent problem for (9) is Z opt = arg max Z tr ( Z H R g Z ) . (10) s . t . Z H Z = I L The Z opt in (1 0) sho uld satisfy these two conditions Z H opt R g Z opt = diag ( λ g 1 , λ g 2 , ..., λ g L ) (11) Z H opt Z opt = I L (12) which im plies that Z opt = U g (1 : L ) . pr oof: See Appendix. Based on t his lemm a, we conclude t h at if the BS uses L sym bols for d ownlink training, a jammer with N ≥ L antennas can design an opt imal attack s ignal and m aximize the MSE. In the next section, we will e va luate the performance of the prop o sed jammi ng attack by num erical simulatio n s. V . N U M E R I C A L R E S U L T S In this section, the performance of the proposed jamming is explored by means of numerical sim ulations and we inspect the est i mation MSE in dif ferent channel condit i ons and pilot s i gnal desi gns at the BS. W e consider a BS with a uniform l inear array (ULA) consi sting of M = 1 00 antennas. Th e exponential correlation m odel is used for the cov ariance m atrix R h with elements R h i,j = r | i − j | , where th e coefficient r ∈ (0 , 1] d etermines the strength of the correlation in the channel [5]. The same m odel is us ed for the jammer’ s channel covariance matrix. Pa th-loss and s h adow-f ading are assumed t o be t h e same for both channels and are normalized to unit y . Furthermore, the variance of thermal noi s e is assumed to be σ 2 = 1 and th e transmit power of the BS and the jam mer are m easured in dB relativ e to σ 2 . T o show t he vulnerability of the estimation procedure in the presence of the proposed jamming, we consider fi ve different scenarios and compare them in terms of t he channel estimatio n MSE. T h e BS can desig n the pilot signal m atrix in different ways but two extreme cases are important here. In the first case, the BS u s es the opt i mal pilot s in (8). In th e second case which is the worst case scenario, the BS uses the complement ary of th ese pilots. W e call it the worst-case p ilots wh i ch are obtained by the following problem, Φ c = arg max Φ 1 M tr ( R h − ψ ) = U h ( M − L + 1 : M ) . (13) This can be d erived b y fol lowing an approach s imilar to the proof of (8) i n [9]. In th e jamm er side, we consi d er our proposed jamm ing design and two oth er scenarios for benchmarking. First, t h e jammer is silent and does not attack the syst em. In the second scenario, the jamm er designs it s attack si g nal withou t considering the second-order statisti cs of its channel and the objective in (9) and only satisfies constraint 10 20 30 40 50 60 70 80 90 100 Number of Training Symbols (L) 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Mean Square Error (MSE) single-shot jamming - worst case pilots no jamming - worst case pilots proposed jamming - optimal pilots single-shot jamming - optimal pilots no jamming - optimal pilots Fig. 1. MSE of the system versus the number of training symbols L . (The channel correlation coef fi cient is r = 0 . 4 , the number of BS antennas is M = 100 and the transmit po wer of the BS and the jammer are P b = P j = 5 dB .) 10 20 30 40 50 60 70 80 90 100 Number of Training Symbols (L) 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Mean Square Error (MSE) single-shot jamming - worst case pilots no jamming - worst case pilots proposed jamming - optimal pilots single-shot jamming - optimal pilots no jamming - optimal pilots Fig. 2. MSE of the system versus the number of training symbols L . (The channel correlation coef fi cient is r = 0 . 7 , the number of BS antennas is M = 100 and the transmit po wer of the BS and the jammer are P b = P j = 5 dB .) Z H Z = I L . One way to do this which we call single-shot jammin g is when ev ery column of Z has only one ’1’ entry , and no ne of the rows has mo re than o n e ’1’ entry . Fig. 1 illustrates the MSE of the estimator versus the number of pil ot symbols th e aforementioned pilot and jamming signal designs . W e can see that in a realistic case t hat the BS uses the opt imal pilots Φ opt , our p rop osed jamm ing has a severe effect on the MSE and m akes it close to the case that the BS uses the worst-case pil ots. When the number o f symb ols, L gets clos e to the number o f BS ant enn as, the MSE under the proposed jammin g gets ev en larger than the worst-case pilots scenario. W e also see that when there is no jam ming i n the system, the M SE will tend to zero b y increasing L , but in the presence of the proposed jammer , it wil l satu rate t o a value around 0.5. This imp l ies t hat t he estimation procedure in this system is seve rely vulnerable to the jamm ing attack. The other poi nt t h at can be seen from this figure is 20 40 60 80 100 120 140 160 180 200 Number of BS Antennas (M) 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 Mean Square Error (MSE) proposed jamming - optimal pilots single-shot jamming - optimal pilots no jamming - optimal pilots Fig. 3. MSE of the downlink channe l estimation versu s the number of BS antennas M . (The channel correlation coef ficient is r = 0 . 7 , the number of training symbols is L = 20 and the number of jammer antennas is N = 25 .) the m erit of our proposed jamming in compared to si ngle-shot jammi ng design. Fig. 2 is i n t h e same scenario as in Fig. 1 but with a larger correlatio n coefficient i.e. a stron g er correlated channel. W e can see that when the channel is m ore correlated, the optimal pilot design makes the MSE very small in the case of no jammer or wi th single-shot jamming in t h e system. But with our proposed jammer signal desig n, the MSE gets signi ficantly large. Also it should be no t ed that in all the scenarios, when the number of pilot s ymbols L is equal to the nu m ber of BS antennas, the MSE will be relatively s mall, but if the j am mer us es our proposed design, th e MSE will still be around 0.5 and can be very destructive in th e downlink data phase precoder design . Fig. 3 shows the channel estimatio n MSE versus the numb er of BS ant ennas. The number of p ilot symbols in the syst em is fixed at L = 20 and th e jammer is assumed to have N = 2 5 antennas. As we see, in the presence of our proposed smart jammer , the m o re antennas at the BS can blow down th e MSE. Howev er , after a mi nimum point, the MSE starts to grow up by increasing the nu m ber of BS antenn as. That is because a large number of antennas leads t o a high di mensional channel vector and L = 20 pilot length is not sufficient to esti mate thi s channel even i f it is strongly correlated. Note that at any number of BS antennas, the MSE in the presence of our proposed jammer is still larger than all ot h er scenarios that adopt optimal pilo t designs at the BS. V I . C O N C L U S I O N In this work, we cons idered the security of an FDD mas s iv e M IMO sys tem agains t a jammer who intends t o attack the downlink t raining phase and degrade the estimation p erformance. T he jammer tries to maximize the estimati on MSE by opti m al design ing of its attack sig nal e ven if t he BS uses th e op timal training signals with a large num ber of p i lot symbols. Numerical results showed the severe impact of this attack. In particular , when the BS uses optimal pilo t s with enough length of symbols, th e estimation M SE could tend to zero in the absence of jammer or in the presence of oth er jam ming schemes. But i f the jammer attacks the syst em using our proposed desig n, the estim ation MSE will be stil l large even at a lar ge number of pil o t symbol s. This shows the security vulnerability in the downlink t rain i ng phase of FDD massive MIMO syst ems against the proposed smart jamm er . A P P E N D I X A. proof of Lemma 1 First, we show that solv i ng the problem in (10 ) is equiv alent to the solu tion of (9). As M is a constant and R h is independent of Z , we have arg max Z 1 M tr ( R h − ψ ) = a rg min Z tr ( ψ ) (14) Using the fact that tr ( AB C ) = tr ( B C A ) , we can rewr ite equation (5) as follows tr ( ψ ) = tr (( P j P b Z H R g Z + Q 1 ) − 1 Q 2 ) (15) Q 1 = Φ H R h Φ + σ 2 LP b I L (16) Q 2 = Φ H R 2 h Φ (17) Q 1 and Q 2 are i ndependent of Z . Also not e that Z H R g Z i s in th e in verted part of ψ , th erefore arg min Z tr ( ψ ) = arg max Z tr ( Z H R g Z ) . (18) T o solve t h e equiv alent problem in (10), we us e the fact that for a matrix R g and any matrix Z satisfying the con s traint (11), the t race of matrix A = Z H R g Z is maximized when A is diagonal and also the main diagonal entries of A are maximized. By exploiti n g the EVD of R g and no ting th at the eigen values of R g are in decreasing order in D g , we conclude that the matrix Z opt which maximizes tr ( A ) and satisfies (11), must m eet the following equation Z H opt R g Z opt = diag ( λ g 1 , λ g 2 , ..., λ g L ) (19) which impl ies that Z opt = U g (1 : L ) . R E F E R E N C E S [1] E. G. Larsson, O. Edfors, F . T ufvesson, and T . L. Marzetta, “Massiv e mimo for next generation wireless systems, ” IEEE Communications Maga zine , vo l. 52, pp. 186–195, F ebruary 2014. [2] H. Q. Ngo, E. G. L arsson, and T . L. Marzetta, “Energy and spectral efficienc y of very large multiuser mimo systems, ” IEEE T ransa ctions on Communications , v ol. 61, pp. 1436–144 9, April 2013. [3] Z. Ji ang, A. F . Molisch, G. Caire, and Z. Niu, “ Achiev able rates of fdd massive mimo systems with spatial chann el correlation, ” IEEE T ransactions on W i r eless Communications , vol. 14, pp. 2868–28 82, May 2015. [4] O. Elijah, C. Y . Leo w , T . A. Rahman, S. Nunoo , and S. Z. Iliya, “ A comprehens iv e surve y of pilot contamination in massi ve mimo 5g system, ” IEEE Communications Surv e ys T utorials , vol. 18, pp. 905–9 23, Secondquarter 2016. [5] E. Bj ¨ ornson, J. Hoydis, M. K ountouris, and M. Debbah, “Massi ve mimo systems with non-ideal hardware: Energy efficiency , estimation, and capacity limits, ” IEEE T ransactions on Information Theory , vol. 60, pp. 7112–713 9, Nov 2014. [6] W . Shen, L. Dai, Y . Shi, B. Shim, and Z. W ang, “Joint channel training and feedback f or fdd massi ve mi mo systems, ” IEEE Tr ansactions on V ehicular T echnolog y , v ol. 65, pp. 8762 –8767, Oct 2016. [7] Z. Gao, L. Dai, W . Dai, B. S him, and Z. W ang, “Str uctured compressi ve sensing-base d spatio-temporal joint channe l estimation for fdd massi ve mimo, ” IEEE T ransactions on Communications , vol. 64, pp. 601–617, F eb 2016. [8] J. Fang, X. Li , H. Li, and F . Gao, “Low-rank cov ariance-assisted downlink training and channel estimation for fdd massiv e mimo systems, ” IEEE T ransa ctions on W i r eless Communications , vol. 16, pp. 1935–19 47, March 2017. [9] J. Choi, D. J. Love, and P . Bidigare, “Do wnlink training t echniques for fdd massiv e mimo systems: Open-loop and closed-loop training with memory , ” IEEE Journal of Selected T opics in Signal Pro cessing , vol. 8, pp. 802 –814, Oct 2014. [10] B. Dutta, R. Budhiraja, and D. R. Ko ilpillai, “Limited-feedback low-encoding comp lexity precoder design for do wnlink of fdd multi-user massi ve mimo systems, ” IEE E T ransactions on Communica tions , vol. 65, pp. 1956–1971, May 2017. [11] Y . W ang, C. Li, Y . Huang, D. W ang, T . Ban, and L. Y ang, “Energ y-efficient optimization for do wnli nk massiv e mimo fdd systems with transmit-side channel correlation, ” IEEE T ransactions on V ehicular T echnolo gy , vol. 65, pp. 7228–724 3, Sept 2016. [12] Y . W u, A. Khisti, C. Xiao, G. Caire, K. W ong, and X. Gao, “ A survey of physical l ayer security techniques for 5g wireless netwo r ks and challenges ahead, ” IEEE Jo urnal on Selected Areas in Communications , v ol. 36, pp. 679–695 , April 2018. [13] D. Kapetano vic, G. Zheng, and F . Rusek, “Physical l ayer security for massi ve mimo: An ov erview on passiv e eav esdropping and active attacks, ” IEEE Communications Ma gazine , vol. 53, pp. 21–27, June 2015. [14] H. Pirzadeh, S. M. Razavizadeh, and E . Bj ¨ ornson, “Subv erting massive mimo by smart jamming, ” IEEE W i r eless Communications Letters , vol. 5, pp. 20–23 , Feb 2016. [15] Y . Wu, R. Schober , D. W . K. Ng, C. Xiao, and G. Caire, “Secure massive mimo transmission with an active eavesdropp er, ” I EEE T ransactions on Information Theory , vol. 62, pp. 3880–390 0, July 2016 . [16] N. Nguyen, H. Q. Ngo, T . Q. Duong, H . D. Tuan , and D. B. da Costa, “Full-duplex cyb er-weapon with massive arrays, ” IEEE Tr ansactions on Communications , v ol. 65, pp. 5544–555 8, Dec 2017. [17] H. Akhlaghpasand, S . M. Razavizadeh, E. Bj ¨ ornson, and T . T . Do, “Jamming detection in massiv e mimo systems, ” I EEE W ir eless Communications L etters , vol. 7, pp. 242 –245, A pril 2018. [18] T . T . Do, E. Bj ¨ ornson, E. G. Larsson, and S. M. Razavizadeh, “Jamming-resistant receivers for the massiv e mimo uplink, ” IEEE T ransactions on Information F orens ics and Security , vol. 13, pp. 210–223, Jan 2018. [19] S. M. Kay , Fundamentals of Statistical Signal Pr ocessing: Estim ation Theory . Upper Saddle Riv er, NJ, US A: P r entice-Hall , Inc., 1993. [20] A. M. Tulino and S. V erd ´ u , Random Matrix Theory and W ireless Communications , vol. 1. Hanover , MA, USA: Now Publishers Inc., June 2004.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment