Cybercrime Investigators are Users Too! Understanding the Socio-Technical Challenges Faced by Law Enforcement
Cybercrime investigators face numerous challenges when policing online crimes. Firstly, the methods and processes they use when dealing with traditional crimes do not necessarily apply in the cyber-world. Additionally, cyber criminals are usually technologically-aware and constantly adapting and developing new tools that allow them to stay ahead of law enforcement investigations. In order to provide adequate support for cybercrime investigators, there needs to be a better understanding of the challenges they face at both technical and socio-technical levels. In this paper, we investigate this problem through an analysis of current practices and workflows of investigators. We use interviews with experts from government and private sectors who investigate cybercrimes as our main data gathering process. From an analysis of the collected data, we identify several outstanding challenges faced by investigators. These pertain to practical, technical, and social issues such as systems availability, usability, and in computer-supported collaborative work. Importantly, we use our findings to highlight research areas where user-centric workflows and tools are desirable. We also define a set of recommendations that can aid in providing a better foundation for future research in the field and allow more effective combating of cybercrimes.
💡 Research Summary
The paper “Cybercrime Investigators are Users Too! Understanding the Socio‑Technical Challenges Faced by Law Enforcement” investigates the practical, technical, and social obstacles that cybercrime investigators encounter in the United Kingdom. The authors adopt a qualitative, user‑centred approach, combining a short pre‑interview questionnaire with semi‑structured, face‑to‑face interviews of ten experts drawn from both government (six participants from UK law‑enforcement agencies) and the private sector (four participants from security‑intelligence firms). Participants hold a range of roles, from operational analysts to senior managers, providing a broad perspective on the end‑to‑end investigative workflow.
The study begins by reviewing the literature on cybercrime definitions, intelligence‑gathering cycles, and prior work on digital forensics and police perceptions of cybercrime. It highlights a gap: most existing research focuses on technical tool development or on the attitudes of patrol officers, while the holistic processes used by specialised cyber investigators remain under‑explored, especially outside the United States.
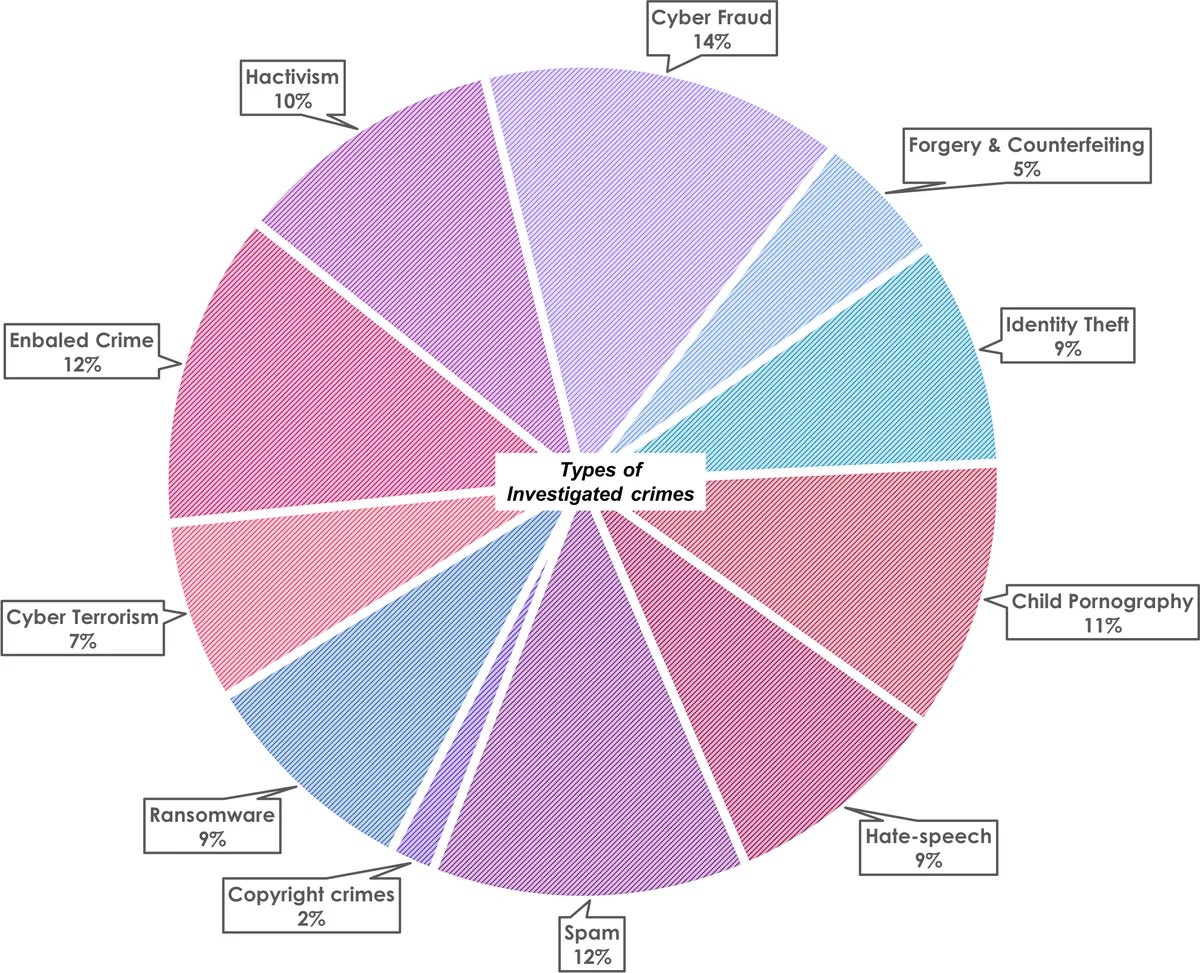
Methodologically, the authors use snowball sampling to recruit participants, ensuring diversity of expertise. The questionnaire collects demographic and role‑related data, while the interview guide explores four thematic areas: (1) types and volume of cyber incidents handled, reporting mechanisms, and triage criteria; (2) detailed investigative processes, including iterative and proactive elements; (3) team composition, geographic distribution, and collaborative needs; and (4) tool support, covering usability, availability, and perceived limitations. Interviews lasted between 45 minutes and 1.5 hours, were audio‑recorded, transcribed, and analysed using thematic analysis.
Key findings are organised into five inter‑related challenge domains:
-
Process Mis‑alignment – Traditional crime‑investigation models (e.g., the classic intelligence cycle) do not map cleanly onto cyber investigations. Data collection, processing, and analysis are hampered by massive, heterogeneous data sources (network logs, cloud artefacts, mobile devices). Manual preprocessing creates bottlenecks, and investigators lack automated pipelines to normalise and enrich data.
-
System Availability and Reliability – Many agencies rely on legacy forensic platforms that are difficult to update and prone to downtime. System outages interrupt evidence preservation, jeopardising the chain‑of‑custody and potentially undermining admissibility in court.
-
Collaboration Deficits – Investigation teams are often geographically dispersed, yet current Computer‑Supported Collaborative Work (CSCW) tools are limited to email and basic chat. Real‑time shared dashboards, role‑based task allocation, and secure cross‑organisation information exchange are missing. Legal and procedural barriers further restrict data sharing between public and private entities, leading to information silos.
-
Skill Gaps and Training – Rapid evolution of cyber threats outpaces formal training programmes. Participants report ad‑hoc learning, insufficient exposure to emerging attack techniques, and a lack of structured, continuous professional development. This skill deficit reduces the effectiveness of newly introduced tools.
-
Usability of Existing Tools – Forensic and analytical tools are described as complex, with non‑intuitive interfaces and opaque evidence‑tracking mechanisms. Junior investigators struggle to navigate these systems, and the difficulty in documenting a clear evidence trail hampers courtroom presentation.
Based on these insights, the authors propose a research agenda centred on user‑centric design and process automation:
- Automated Data Normalisation Pipelines – Build modular, scalable preprocessing services that ingest raw artefacts, apply standard schemas, and feed downstream analytics.
- High‑Availability Cloud‑Based Evidence Repositories – Migrate storage to resilient cloud platforms with robust access‑control, audit logging, and redundancy to protect the chain‑of‑custody.
- Real‑Time Collaborative Dashboards – Develop secure, role‑aware workspaces that visualise case status, share artefacts, and enable synchronous analyst interaction across agencies.
- Sustainable Training Frameworks – Implement continuous learning programmes, including threat‑intel briefings, tool‑specific workshops, and certification pathways aligned with investigative duties.
- Usable, Transparent Forensic Interfaces – Redesign tool front‑ends using human‑centred design principles, emphasizing clear workflow guidance, drag‑and‑drop evidence handling, and built‑in provenance tracking.
The paper concludes that addressing cybercrime effectively requires more than new technical solutions; it demands an integrated socio‑technical strategy that aligns processes, tools, organisational culture, and legal frameworks. While the empirical data are UK‑specific, the identified challenges and recommendations are broadly applicable to other jurisdictions grappling with the same shift from traditional to digital investigations. Future work should prototype the suggested systems, conduct field trials, and measure impact on investigation speed, evidence quality, and investigator satisfaction.
Comments & Academic Discussion
Loading comments...
Leave a Comment