Color Image Encryption Based on Chaotic Block Permutation and XOR Operation
In this paper, chaotic block image permutation and XOR operation are performed to achieve image encryption. The studied method of encryption makes use of chaotic systems properties for secure and speed image encryption. Firstly, the original image is…
Authors: Raneem A. Aboughalia, Osama A. S. Alkishriwo
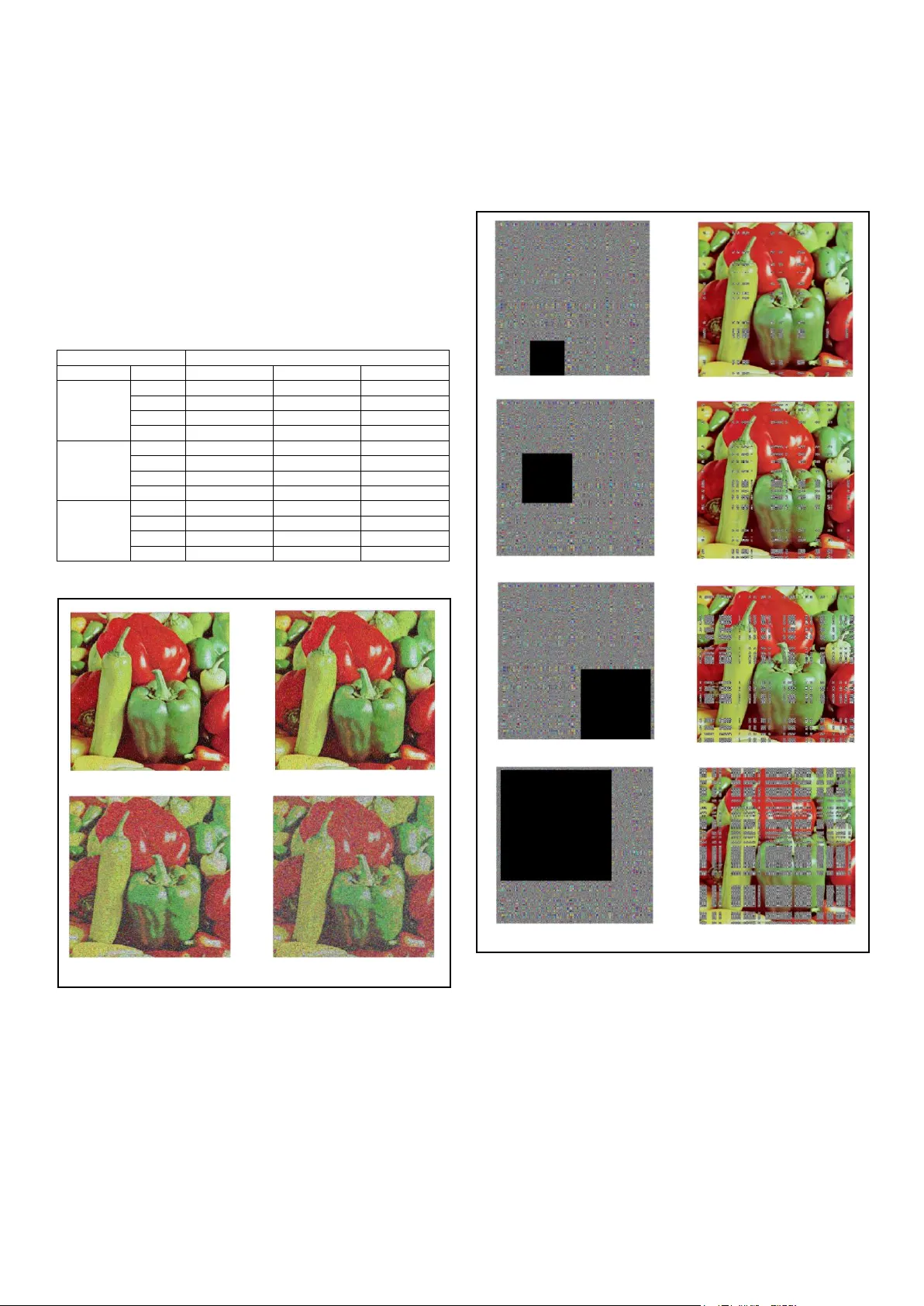
Liby an International Conference on Electrical E ngineering and T echnologies (LICEET 2018) 3 – 7 march 2018, Tripoli - Libya 492 LICEET137320 18 Color Image Encryption Based on Chaotic Block Permutation and XOR Operation Ranee m A. Aboughalia Depart ment of Electrical and Electro nic Engineering University of Trip oli Tripoli , Libya Raneem.abg@gmail.co m Osama A. S . Alkishriwo Department of Electrical and Electronic En gineering University of Trip oli Tripoli , Lib ya Alkishriewo@yahoo.co m Abstract — In this paper, chaotic block image per mutation and XOR operation are perform ed to achieve image encryption. Th e studied method of encryption m akes use of chaotic systems properties f or secure and speed im age encryption. Firstly, the original im age is divided into blocks o f equal size. Then, two chaotic maps are used to generate two key streams which are permuted among themselves to produce one key steam . The image blocks are then shuffled using par t of key stream. Finally, scrambled image is diffused by XOR operation with the k ey stream to get the encry pted imag e . The experimental results of se veral performance analyses abo ut the pix el correlation, various statistical analysis, informa tion entropy analysis, differential analysis, th e key spa ce and key s ensitivity analysis, show that t he alg orithm can resist se veral know attack s e ffectively and has the advantages of large key space, high security, and high spe ed, assuring safety performa nce and secure image encryption . Keywords — Color image encry ption ; chaotic; l ogistic map; duffing map ; I. I NTRODUCTI ON Image in formation tra nsmission has increased rapidly with the incredible development of internet technologies and wireless communication networks. All kinds of multimedia data like d igital image, a udio, text and video can be accessed easily on internet. As a result, cr yptographic techniques ar e required to accomplish a certain level of confide ntiality a nd information security, duri ng data storage and trans mission. There are a number of d ata p rotection approaches including a wide variet y of algorithms used for d ata encryption. Ho wever, traditional encr yption algorithms which are proposed for text infor mation such as DES, IDES, RSA are not suitable f or im age e ncryption because o f the larger scale of data, hi gher redundanc y and stronger co rrelation o f pixels in images [ 1] . In literat ure, various techniques have been de veloped to design secure image encryption algorithms. Among these approaches is the c ha os image encryption sche mes which have many excel lent properties, such as ergodicity, rando m-like behavior, and sensiti vity to initial values, etc, whic h can be used as an ideal image encryption method. Chao tic characteristics attracted the attention of cr yptographers. They applied chaos theory to cryptograp hy and have d eveloped many ima ge encr yption based on chaos. Compared with traditional encr yption algori thm, image encryption cha os- based has large ke y space, which is i mplemented si mply and is robust. As early i n [2], Matthew p ropo sed a logistic map based encryption algorithm. I n [3], Fridrich f irstly introduced permutation-diffusion architecture for chaotic image encryption. Later, many researchers paid a great attention to chaotic image encryptio n technology and pr oposed a variet y of algorithms [4 - 7] . Here in this paper the em phasis is on chaoti c based color image encryption algorith m, e mploy ing t wo different chaoticm aps to generate two key streams X and Y that areused to sc ramble image b locks and to perf orm the bitw ise XOR operation to achiev e image encry ption. The rem ainder of th is pape r is o rganized as foll ows. In Section II, chaotic maps are briefly addressed. I n Section III , the algorithm will be described in details. In Secti on IV ,sim ulation results and security analysis are presented.In Section V, com parison between the pr oposed algorithm test results w ith other algorithms is giv en . T he conclusions are given in S ection V I. II. C HAOTIC MAPS A. Log istic map Logistic Map is a po lynomial equiv alence of de gree 2.The map was popularized in a seminal 19 76 pap er by the biologist Robert May, in part as a discrete-time demographic model analogous to the logistic e quation first created b y P ierre François Verhulst. Mathematically, the logistic map is w ritten as : . (1) where, µ and x 0 are the control parameter and initial state value, respectively. If one c hoose µ [3.5 7, 4], the system is chaotic. (4.1) Liby an International Conference on Electrical E ngineering and T echnologies (LICEET 2018) 3 – 7 march 2018, Tripoli - Libya 493 LICEET137320 18 (a) (b) (c) (d) Fig. 2. Encryption results: (a) plain text Lena image, (b) encrypted Lena image , (c) plain text Mandrillimage, (d) encry pted Mandril image . B. Du ffing map The Duffin g map (also cal led as 'Holmes map ') is a discrete-time dynamical syste m. It is an example of a dynamical system that exhibits chaotic behavior. T he Duffing map take s a point ( , ) in the p lane and maps it to a ne w point given by (2): (2) The map depends on t he two constants a and b . These are usually set to a = 2 .75 and b = 0. 2 to p roduce chaotic behavio r . It is a discrete version o f the Duffing equation. III. E NCRYPTI ON AND DECRYPTI ON ALGO RITHM The studied image e ncryption algorithm uses bloc k permutation and XOR operat ion. Initially the ori ginal col o r image is divided into blocks o f . Chaotic maps are being used to generate key st ream, with ini tial condition . The generated key stre am i s used to permute the d ivided image blocks. The shuffled image blocks of images are merged to form a single image. Fig.1sho ws the block diagram of the encr yption method. A. En cryption A lgorithm The following are the seque nce of steps used to encrypt images. Input s to the algorithm are the original images, desired blocks size, initial condition generated u sing ra ndom function, chaotic map key strea m, while t he Output is t he encrypted image. . Step1: Input t he original i mage of size and the block size. Step2: Gen erate random initial conditions , taking into account the original i mage p ixel values. Step3: Usi ng the initial conditions generate chaotic map s k ey streams and . Step4: Original image is di vided into blo cks of size ). Step5: Shuffle the block of images u sing p art of the key stream of length . Step6 : Combine t he scr ambled image b locks i nto a single image. Step7: P erform XOR operat ion bet ween p ixel data of the scrambled i mage and the key strea m generated by chaotic maps . IV. SIMULA TION RESULT S AND PREFORMA NCE ANALYSIS In thi s sectio n, experimental r esults and p erformance analysis of t he studied image e ncrypting algorithm is presented. T est i mages were chosen to be standard 8-bit colo r images. . Figure 2 shows the encr yption results of different test i mages using different chaotic maps, while Fig. 3 shows the encryption and d ecr yption proce ss steps of t he propo sed encryption algorithm . Chaotic map Generator Original ima ge y Divide it into blocks and shuffle them Scrambled image XOR operation Encrypted i m a g e w v x Fig. 1. Block diagram of encry ption algorithm. Liby an International Conference on Electrical E ngineering and T echnologies (LICEET 2018) 3 – 7 march 2018, Tripoli - Libya 494 LICEET137320 18 (a) (b) (c) (d) A. Differen tial Attack In ge neral the two m ost common measures used to quantify this requirement are the Number of Pixel Change Rate (NPCR) and the Unified Averaged Changed Intensity (UACI), which are used to evaluate the stren gth of image encryption algorithms with respect to d ifferential attac ks. If and are tw o different encr ypted i mages whose corresponding plaintext i mages dif fer by o nly o ne pixel , then the NPCR and U ACI can be mathematically d efined as NPCR (3) UACI (4 ) where, (5) From the NP CR and UACI results illustrated in Tables 1 and 2, we ca n find that o ur p roposed algorithm is v ery sensitive to small chan ges in plain text images B. Histog ram Analysis An i mage histogra m s hows the frequency of the pixel intensity values within the image. Unifor m histograms do not provide any use ful information, thus to resist statistic al attacks, the encrypted image should have unifor m histogram as shown in Fig. 4(d ) and (h) . Image Red Green Blue Peppers 33.4947 33.4997 33.4933 Lena 33.4945 33.4815 33.4178 Sailboat 33.4420 33.4801 33.4559 Mandrill 33.5002 33.5688 33.5514 Airplane 33.4530 33.4835 33.4333 Image Red Green Blue Peppers 99.5953 99.6044 99.6201 Lena 99.6071 99.6246 99.6208 Sailboat 99.6258 99.6197 99.6174 Mandrill 99.6193 99.6082 99.6227 Airplane 99.6048 99.5953 99.5968 (a) (b) (c) (d) (e) (f) (g) (h) Fig. 3. Image e ncryption and d ecry ption proce ss: (a) plainte xt image , (b) permutated image , (c) encrypted imag e, (d) reconstructe d image. F i g . 4 . Table 1: NPCR te st results. F i g . 5 . Table 2 : UACI test results. F i g . 6 . Fig. 4 . Histogram analysis: (a) plain te xt Le na image, (b) histogram of th e plain text Lena image, (c) encrypted Lena image, (d) histogram of encrypted L ena image, (e) plain text Sailboat image , (f) h i stogr am of t he plain text S ailboat image, (g ) encrypted Sailboat i mage, an d (h) histogram of encry pted Sailboat image. Liby an International Conference on Electrical E ngineering and T echnologies (LICEET 2018) 3 – 7 march 2018, Tripoli - Libya 495 LICEET137320 18 C. Addjacent Pixel Correlation The original image p ixel correlation is usuall y v er y high; a secure image encr yption algorithm mus t prod uce an encrypted image ha ving low corr elation b etween ad jacent pixels to prevent statistical attack. Theresults in Fig. 5 and Table 3 emphasizes that there i s no correlationof adjacentpixelsinencr yptionimages, indicating that the tested encryption alg orithm effectively des tr o yed the correlation of pixels. Image Direction Red Green Blue Lena original Horizontal 0.9798 0.9691 0.9327 Vertical 0.9893 0.9825 0.9576 Diagonal 0.9697 0.9555 0.9183 encrypted Horizontal -0.0470 -0.0377 -0.0473 Vertical -0.0475 -0.0501 -0.0477 Diagonal 0.0015 0.0050 0.0035 Mandrill original Horizontal 0.9231 0.8655 0.9073 Vertical 0.8660 0.7650 0.8809 Diagonal 0.8543 0.7348 0.8399 encrypted Horizontal -0.0728 -0.0727 -0.0691 Vertical 0.0383 0.0265 0.0359 Diagonal -0.0051 -0.0017 -0.0015 D. Informtion Entropy Analysis The inf ormation entropy gives a measure of stati stical randomness and unpredictabilit y of in formation, taken place in encrypted images. The info rmation e ntropy of a message source can be described as (6 ) where is the number of bits that is required to represent the symbol , and is th e probability of sym bol .It is desired from sec urity point o f view that encrypted images should have t heir e ntropy measure close to the ideal value 8 . The entropy measures of the R,B ,G components of the o riginal and the encr ypted images are shown in Table 4, im plies that information lea kage in t he encr ypted ima ges is low and the encrypted image is secure a gainst entrop y-base attack. Image Red Green Blue Peppers original 7.3388 7.4963 7.0583 encrypted 7.9992 7.9993 7.9993 Lena original 7.2531 7.5940 6.9684 encrypted 7.9992 7.9993 7.9993 Sailboat original 7.3124 7.6429 7.2136 encrypted 7.9993 7.9993 7.9993 Mandrill original 7.7067 7.4744 7.7522 encrypted 7.9993 7.9993 7.9993 Airplane original 6.7178 6.7990 6.2138 encrypted 7.9993 7.9994 7.9993 E. Noise a nd Data Lo ss Analysis The strength of the studied encryption algorithm agai nst attacks that may lead to data loss, can be examined by subjecting the encr ypted i mage to noise or p ixel cr opping attack o f so me le vel a nd then visuall y ob serving the quali ty of the reconstructed i mages with respec t to the original image. To evaluate the resistance of the encryption algorithm peak signal to noise ratio (P SNR), can be employed. PSNR (7) MSE (8) where MSE is the m ean square error between the recovered image a nd the ori ginal image , and and are the ro ws and columns w hich re present the w idth and height of the image . Test PSNR Image Red Green Blue Peppers 0.05 11.6135 7.5505 11.7968 0.1 11.2445 7.5345 11.4232 0.3 10.4170 7.5283 10.2242 0.5 10.0416 7.5367 9.6083 Lena 0.05 10.8025 10.2446 13.6931 0.1 10.4866 10.0331 13.1787 0.3 9.5731 9.5299 11.8703 0.5 9.1468 9.2888 11.1701 Mandrill 0.05 10.0970 11.2275 9.3268 0.1 9.9166 10.9530 9.2152 0.3 9.5018 10.2608 8.9420 0.5 9.2917 9.9344 8.8066 Fig. 5. Adjacent pixel correlation of Le na i mage: (a) vertical pixel correl ation, (b) horizontal pixel correlation, and (c) di agonal pixel correl ation of plain text image, (d) vertical pixel correl ation, (e) h orizontal pixel corre lation, and (f) diagonal pixe l correlation of encry pted image. Table 3 : Correlation coefficients i n three directions: horizon tal vertical and diagonal. F i g . 7 . Table 4 : Info rmation entropy fo r plaintext and encry pted images. F i g . 9 . Table 5 : PSNR resul ts for speckle noi se attack. F i g . 8 . Liby an International Conference on Electrical E ngineering and T echnologies (LICEET 2018) 3 – 7 march 2018, Tripoli - Libya 496 LICEET137320 18 (a) (b) (c) (d) (e) (f) (g) (h) Fig. 7.Data loss attack: (a) encrypted with 5% lo ss, (b) decrypted with 5% loss, (c) encrypted with 10% loss, (d) d ecry pted w ith 10 % loss, (e) encrypted with 20% loss, (f) d ecrypted with 20% loss, (g) encrypted with 50% loss, and (h) decrypted w ith 50% loss. Applying speckle noise with densities and to the encr ypted i mage, it ca n b e observed in Fig. 6 that the rec onstructed image can still be readable with PSNR results lis ted in Table 5. Moreover, if the encrypted image i s attac ked by a data c ut of sizes sho wn in T able 6, then t he decr yption proce ss is applies to these cropped images. The decr ypted images contain m ost o f the vis ual infor mation as shown in Fig . 7. Thus, the p roposed encryption algorithm has excellent performance in noise and d ata loss attacks. F. Key S pace and Key S ensitivity The studied image encryption method has two initial parameters (x,y) and iteration N, ta king the computatio nal precision to be 10 -10, the ke y space was found to be = , which is a lmost eq uivalent to and that shows that the algorithm is of sufficient key sp ace to resist t he exhaustive searchin g and brute -force attack. G. Speed Test For the proposed algorithm time consumptio n include ke y stream g eneration, blocks permutation, and diffusion is Test PSNR Image Per. Red Green Blue Peppers 5% 11.9657 7.7292 11.8259 10% 11.7077 7.7454 11.5457 20% 11.5124 7.7774 10.7218 50% 10.2513 7.6863 9.3865 Lena 5% 11.2526 10.3184 13.9350 10% 11.0161 10.2432 13.6034 20% 10.1572 10.2377 13.0271 50% 9.0974 9.5211 11.4750 Mandrill 5% 10.1306 11.3380 9.1982 10% 10.0704 11.2090 9.1950 20% 9.8815 10.9865 9.1244 50% 9.5040 10.2031 8.8019 (a) (b) (c) (d) Table 6 : PSNR results fo r data loss attack. F i g . 1 0 . Fig. 6. Speckle noise attack: (a) , (b) , (c) , and (d) . Liby an International Conference on Electrical E ngineering and T echnologies (LICEET 2018) 3 – 7 march 2018, Tripoli - Libya 497 LICEET137320 18 measured . The speed analysis test has bee n ca rried out on an Intel(R) Core(T M)i7-26 70QM 2.2 GHz, and 8 GB RAM running on Windo ws 7 and MATL AB R2015a.T hecomputational ti me for encr ypting color image with different cha otic maps is 0.4253 second. V. COMPARSI ON WIT H OTHER SCHEMES In this section, we compare our algorithm with o ther recentl y proposed algorithms. We see from T able 7 that our sc heme is the fastest b esides that it exhibits a very large key space , a very good infor mation e ntropy, and an acceptab le UACI and NPCR values as co mpared with other works. Metrix Our [4] [5] [6] [7] Key space Encrypti on time (s) 0.425 1.853 1.82 3.76 4.9 Entropy 7.99 7.99 7.99 7.99 7.99 NPCR 99.62 99.6 - 99.71 99.61 UACI 33.46 33.4 - 33.45 33.46 VI. CONCLUTION S In this paper, an image encryption method based on block permutation and XOR operation is in troduced . The pr ocess involves dividing the image into blocks and then shuffling them. P ixels of the blocks ar e XORed with the chaotic key stream to get the e ncrypted image. Simulatio n r esults and performance analysis show that the p resented algorith m can resist several known attacks effectively, assuring safety performance and secure image encryptio n. Adjacent p ixel correlation of encrypted i mage is found to b e less than that of the original image. Also the results o f NPCR and UACI val ues are very clo se to the ideal values, which clearl y show that the proposed encryption method prod uces good results. R EFERENCES [1] N. K. Pareek, V . P atidar, and K. K. Sud, “Image encryption using chaotic logistic map,” Image and Vision Computing, Vo l. 24, pp. 926-934, Feb. 2006. [2] R. Matthews, “On the derivation of a chaotic encryption algorithm,” Cryptologia, Vol. 13, no. 1, pp. 29 -41, Jan. 1989. [3] J. Fridrich , “Symmetric cip hers based on two dimensiona l chaotic maps,” International Journal of Bifurcation an d Chaos, Vol 8, no. 6, pp. 1259 – 1284, Jun. 1998. [4] X. Tong and M. Cui, “Im age encr yption scheme based on 3D baker with dynamical compound chaotic sequence cipher generator,” Signal Processing, Vol. 89, no. 4, pp. 480 -491, Apr. 2009. [5] C. L i, G. L uo, K. Qin , and Ch. L i, “An i mage encryption scheme based on chaotic tent map,” Nonlinear Dynam ics, Vol. 87, no. 1, pp. 127-133, Jan. 2017. [6] X. W u, B. Zh u, Y. Hu, and Y. Ran, “A novel c olou r im age encryption scheme using rectangular transform-enhanced chaotic tent map,” IEEE Access, Vol. 4, pp. 6429 -6436, Apr. 2017. [7] H-M Yuan, Y. Liu, T. Lin, T. Hu, and L- H Gong, “A new parallel image cry ptos ystem based on 5D hy per- ch aotic system,” Image Communication, Vol. 52, pp. 87-96, Mar. 2017. Table 7 : Comparison o f someencry ption schemes using L ena as test image. F i g . 1 1 .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment