Breaking the Target: An Analysis of Target Data Breach and Lessons Learned
This paper investigates and examines the events leading up to the second most devastating data breach in history: the attack on the Target Corporation. It includes a thorough step-by-step analysis of this attack and a comprehensive anatomy of the malware named BlackPOS. Also, this paper provides insight into the legal aspect of cybercrimes, along with a prosecution and sentence example of the well-known TJX case. Furthermore, we point out an urgent need for improving security mechanisms in existing systems of merchants and propose three security guidelines and defenses. Credit card security is discussed at the end of the paper with several best practices given to customers to hide their card information in purchase transactions.
💡 Research Summary
The paper provides a comprehensive examination of the 2013 Target Corporation data breach, which resulted in the theft of approximately 40 million credit and debit card numbers and 70 million personal records. It begins by situating the incident within the broader context of retail data breaches, noting that it was the second‑largest breach after the 2007 TJ X incident and that a wave of similar attacks (Home Depot, Sally Beauty, Neiman Marcus, Michaels, P.F. Chang’s) followed in the subsequent years.
The authors reconstruct the attack timeline in five phases. Phase I starts with a third‑party HVAC vendor, Fazio Mechanical Services, being compromised via a phishing email that delivered the Citadel Trojan. Because Fazio had privileged access to Target’s Ariba billing system, the attackers harvested the vendor’s credentials and used them to gain an initial foothold inside Target’s corporate network. Phase II exploits weak network segmentation; despite Target’s use of VLANs, the attackers moved laterally from the business network into the point‑of‑sale (POS) environment.
In Phase III the attackers deployed BlackPOS, a Windows‑based memory‑scraping malware. BlackPOS registers as a service called “POSWDS,” starts automatically, scans for processes that interact with card readers, and reads large memory chunks (≈10 MB) to locate track‑data patterns using a custom string‑matching algorithm that is more efficient than regular expressions. Extracted card data are encrypted and written to a disguised file (C:\WINDOWS\system32\winxml.dll).
Phase IV concerns data exfiltration. Rather than sending data directly to external servers, BlackPOS aggregates encrypted payloads on compromised internal FTP servers (hard‑coded credentials “Best1 user” / “BackupU$r”). Transfers occur during business hours over NetBIOS/SMB, blending with normal traffic. From the internal repository the data are relayed to external drop sites in Miami and Brazil, where they are sold on underground forums.
Phase V describes monetization: the stolen data, estimated at 11 GB, were advertised on black‑market sites such as Rescator and linked to a Russian aggregation server.
The paper then dissects BlackPOS’s design features that enable it to evade detection. These include multi‑stage exfiltration (internal staging before external upload), string obfuscation to defeat signature‑based AV, self‑destruct code that removes the malware if environmental checks fail, encryption of payloads to bypass DLP, time‑based communication to hide in peak traffic, and hard‑coded internal IPs and credentials that indicate a tailored build for the victim network. The authors trace the malware’s evolution from early McAfee‑detected variants (PWS‑FBOI, BackDoor‑FBPP) to the sophisticated 2013 version used against Target, Neiman Marcus, and Home Depot.
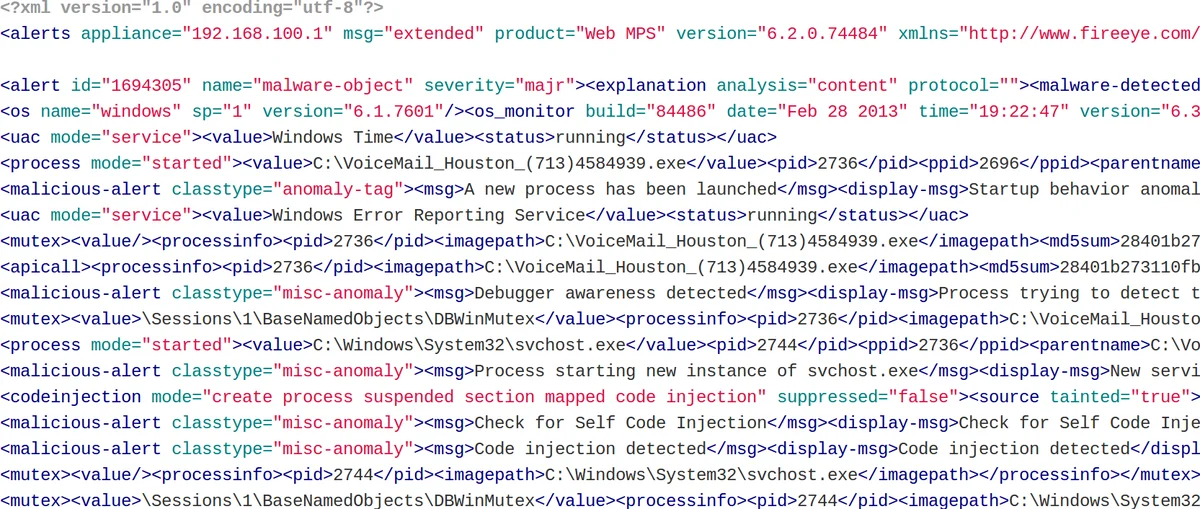
A parallel discussion of the security controls that Target had in place reveals critical operational failures. Although Target deployed the FireEye intrusion detection platform six months before the breach, alerts from FireEye, Symantec, and other tools were ignored, and automatic malware removal functions were disabled by administrators unfamiliar with the system. VLAN‑based segmentation was poorly designed and easily bypassed, POS terminals ran with excessive privileges, and third‑party account controls were lax, enabling the initial vendor compromise.
From a legal perspective, the authors outline the challenges of prosecuting large‑scale data breaches that span multiple jurisdictions. They compare the Target case—still without public arrests—to the TJ X case, where the perpetrators were convicted, sentenced to 20 months in prison, and fined over $10 million. The TJ X precedent demonstrates that successful prosecution requires coordinated international law‑enforcement efforts, robust digital forensics, and clear statutory frameworks.
To address the identified gaps, the paper proposes three practical security guidelines for merchants: (1) enforce payment‑system integrity through code signing, immutable firmware, and least‑privilege configurations on POS devices; (2) design an effective alert system that prioritizes, escalates, and automatically responds to security events, eliminating manual dismissal of critical warnings; and (3) implement rigorous network segmentation using both physical and logical controls, with dedicated firewalls and IDS/IPS for the card‑holder data environment.
Finally, the authors discuss the current state of credit‑card security, highlighting weaknesses in the legacy magnetic‑stripe ecosystem and advocating for EMV chip‑and‑PIN adoption, tokenization, and one‑time virtual card numbers. They provide best‑practice recommendations for consumers: enable transaction alerts, use chip‑enabled cards, prefer tokenized payments (e.g., Apple Pay, Google Pay), and avoid storing card numbers or CVV on merchant websites.
In conclusion, the Target breach illustrates how a combination of third‑party vendor compromise, inadequate network segmentation, mismanaged security tooling, and sophisticated POS malware can lead to massive data loss. The paper emphasizes that technical defenses must be complemented by strong governance, continuous monitoring, and international legal cooperation to mitigate future retail data breaches.
Comments & Academic Discussion
Loading comments...
Leave a Comment