Design an Advance computer-aided tool for Image Authentication and Classification
Over the years, advancements in the fields of digital image processing and artificial intelligence have been applied in solving many real-life problems. This could be seen in facial image recognition for security systems, identity registrations. Henc…
Authors: Rozita Teymourzadeh, Amirize Alpha Laadi, Yazan Samir
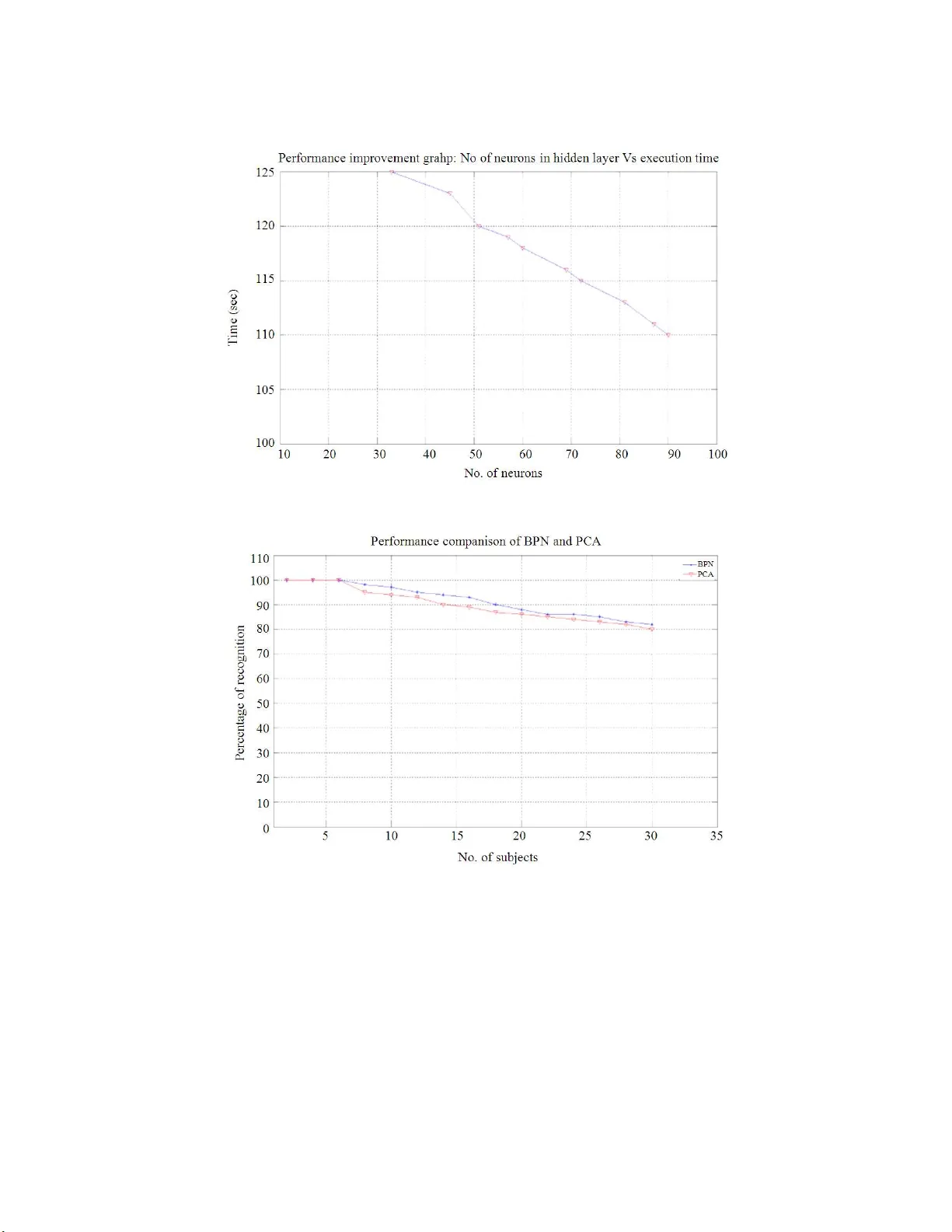
In/SN Date: 30 -05-2012 Time: 1: 3 0 Corresponding Author: Rozita Teymourzadeh, Departme nt of Electrical a nd Electronic, Faculty of Engineering, Technology and Built Environment, UCSI University, 56000, Cher as Kuala Lumpur M alaysia 1 Design an Advance Computer-Aided Tool for Image Authentication and Classification 1.2 Rozita Teymourzadeh, 1 Amirize Alpha Laadi, 2 Yazan Samir Algnabi, 2 MD Shabul Islam and 2 Masuri Othman 1 Department of Electrical and Electronic, Faculty of Engineering, Technology and Built Environm ent UCSI University, Jalan Choo Lip Kung, Taman Taynton View, 56000 Cheras, Kuala Lumpur, Malaysia 2 Department of VLSI Desig n, Institute of Micro Engineering and Nano electronics I MEN, Universiti Kebangsaan Malay sia, 43600 Bangi, Selangor, Malaysia Abstract: Proble m state ment: Over the years, advanceme nts in the fields of digita l image proc essing and artificial i ntelligence hav e been applied in solvi ng many real -life proble ms. T his c ould be seen i n facial image r ecognitio n for securit y systems, id entity r egistrations. He nce a bott leneck of i dentity registratio n is image pr ocessing. Ap proac h: These are carried out in form of image prepro cessing, image region extra ction by crop ping, feature extractio n using Principal Co mponent Anal ysis (PCA) and image co mpression usin g Discrete Cosine Tr ansform (DCT ). Other pro cessing include filtering and his togram eq ualizatio n u sing co ntrast stretchin g is p erfor med while enha ncing the ima ge as part of the analytical t ool. He nce, thi s researc h work pr esents a un iversal inte gration i mage for gery d etectio n analysis to ol with ima ge fac ial r ecognition using Bl ack Propagation Neural Ne twork (BPNN) proce ssor. The proposed de sig ned too l is a multi-function smart too l with the nove l architect ure of programmab le error goal and light inte nsity. F urther more, its advanc e d ual databa se increa ses the efficiency for high per formance application. Results: With t he f act that, th e facial image recognition will al ways, gi ve a matchin g o utput or closest possible outpu t i mage for ever y input image irr espective of the authenticity, the univer sal smart GUI tool is proposed and designed to pe rform image forgery detection wit h t he high acc urac y of ±2% e rror ra te. Concl usion: Mea nwhile, a novel structure t hat provide s efficient auto matic image forger y detection for all input te st image s for the B PNN re cognition is presented. H ence, a n input image will be a uthenticated befor e being fed into the recognit ion too l. Key w ords: Pr incipal Component Analysis (PC A), Discrete Cosine Tra nsform (DCT), Blac k Propagatio n Neural Net work (B PNN), Local Binary Patter n (LBP) INTRODUCTIO N Facial image recognition is a bottleneck of ima ge proce ssing that s hows a lot of interrest in p ast few year s (Kumar et al ., 20 07). Move towardes to 2 -D face recognitio n leads to have template-based approac h and geometric -based ap proac h (Bolm e et al . , 2003 ). f urth er com plex f eat ure s are c omp osed of sev eral o f the f eatu re exam pl es. This typ e of repre sen ta tion leads to an abs tr acti on f rom th e imag e p ixel s . Siro vich an d Kirby (1987 ) pro pos ed Ei gen pictu re as econ omi cally repres ent ation of image in a best coord in at e s ys tem. It w as ob se rved that an accept abl e pict u re of a fac e c ould be r econs tru ct ed f rom th e spe cif icat ion of gray levels at 214 pixel locat ion s. Howev er, they show ed that in actua l constru ct ion , only 40 num be rs with admixtu res of Eigen pictur es can be cha ract eri zed a f ace. Wu and Haung (1 990) to ok advantage of 24 measurement s i n fid ucially signs of profile double facial ima ge. The pro posed system has bee n reduced b y recognizi ng performance when more image in t he database because t here are not e nough to differentiate features tha t identif y a user. Then , Tur k and Pen lan d (1991) introduced the Eigen faces method that achieved a remarkable acknowled gement speed, but the spee d drastica lly reduced, when against resizing . W isk ott et al. (1997 ) use d magni tude inf orm ation and phase info rma tion t hat is rece iv ed f rom Ga bor w avel et tran sf orm ati on of th e fac e image. F or ident ifyin g a pers on, t his inf orm at ion is com par ed with all of the inf orma ti on in datab ase End time 2 sea rch ing f or th e one who h as th e same tran sf ormat ion as tes t im age. Gallagher (2005) analyzed a set of images and proposed that image for gery most often i ncludes so me form of geometric tra nsformation. These processes were based on a re-samp ling and inter polation step . Lat er on , Ahone n and H adi d (2006) i n trod uced th e Loc al Binary Patt ern (LB P). T hi s operat or w as used to measu re th e textur e informa tion of l oca l a rea of g ray im age. The various re search work had been completed (Ming et a l ., 200 8; Me hry ar e t a l. , 2010; J aeyoung and Jun, 2011 ; Han et al., 2011; Lu et al., 2003) to reduce the efficie ncy with variatio ns in illumi nation, i mage size, size o f database, percentage error. In addition, inability to d etect altere d images for m ore realistic recognitio n still is challe nging task. Hence, this stud y pro poses an ef ficient passive evaluation tool for authenticity of input i mages before recognitio n pr ocess stage, further more, the adj ustment of illumination of images usi ng contrast stretching and image histogra m eq ualization techniques will be performed. I n this pro posed research work, the q uality perce ntage is adj ustable in order to achieve hi gh performance (as low a s 2% error ra te) with a dual database approach. The test image i s red uced to a lower 1-D dimensio nal vector , which represents distinguishi ng features of t he te st image. The 1-D image vecto rs a re fed into the neural network, the E uclidean dist ance of the 1-D i mage vector is co mpared to each te st datab ase and the closest match is found and o utputted. Syste m design fundame ntal: The focus of the imag e authenticatio n stage (Fig. 1) is the presence o f the image re-sa mpling trace a nd/or interpola tion signal. A derivative ope rator on the variance of the image w ill detect these tra ces. Later, the signal is pro cessed through r adon transfor mation that re sults in a per iodic signal embedded or complete ly i mposed on the image spectrum graph (Gallagher , 2 005 ). Hence, interpo lated signal and r e-sampled signal will b e read y to function. Interpolate d signal: T here are two mai n sta ges in geometric transfor m (P opescu and Farid, 2005; P rasad & Ra makrishnan, 2006 ). In the first st age, a spa tial transfor mation o f the phy sical re -arrangement of pixels in t he image is performed a nd can be r epresented b y a transfor mation function T as shown in E qu.1. X Y X ΄ T X, Y Y΄ T X, Y (1) As earlier stated, t he geometric opera tions th at are common with most forger ies a re re-scali ng, rotation a nd skewing. Hence, the impor tance of detection will be traced wit utilization o f affine tr ansformatio ns. The general e quation s for affine transfor mation s are given b y: 0 1 2 0 1 2 X ΄ a a x a y Y ΄ b b x b y (2) The second sta ge is the inte rpola tion. H ere pixel intensity values of t he transfor med image are assigned using lo w pas s inter polation filter. According to the sampling theor y, if t he N yquist c riterion is satisfied, the spectrum F ( w ) d oes not overlap in the Fourier do main. The original signal f ( x ) can b e reco nstructed pe rfectly from its samples f k u sing the op timal sine interpolation (Hou and Andr ews, 19 87). Combining the derivative theore m with the convolution theorem lea ds t o the conclusion t hat by convolution of f k with derivative ker nel D n ( w ), it is possible to r econstruct the nth derivative of the image f ( x ). T he r esult o f interpola ted o peration of f w ( x ) is denoted by Equ. 3; 𝑓 ( 𝑥 ) = f w − k D { f } ( 𝑥 ) = D f w − k = f D {w} − k (3) By ass uming t he c onstant variance rando m pr ocess, then the variance of D n {f w } which is var { D n { f w }( x )} as a functio n of x is give n by: 𝑣𝑎𝑟 { 𝐷 { 𝑓 } ( 𝑥 ) } = 𝑅 {𝑓 }(𝑥 , 𝑥 ) = 𝜎 D {𝑤 } − k (4) Similarl y, the covariance i s rep resented as Eq u. 5: 𝑅 {𝑓 } ( 𝑥 , 𝑥 + 𝜉 ) = 𝜎 D { 𝑤 } − k xD { 𝑤 } − k ( 5) End time 3 Fig. 1: Pro posed process structure Now, b y a ssuming that 𝜗 is an i nteger, it can b e noticed that: 𝑣𝑎𝑟 { 𝐷 { 𝑓 } ( 𝑥 ) } = 𝑣𝑎𝑟 { 𝐷 { 𝑓 } ( 𝑥 + 𝜗𝛥 ) } (6) Thus, v ar { D n { f w }( x )} is periodic over x with per iod ∆x that ∆ x is the sa mpling step . It is verified the perio dicity by t he followin g: 𝑣𝑎𝑟 { 𝐷 { 𝑓 }( 𝑥 + 𝜗𝛥 )} = 𝜎 D {𝑤 } − k = 𝜎 D {𝑤} − (k − 𝜗 = 𝑣𝑎𝑟 { 𝐷 { 𝑓 } ( 𝑥 ) } (7) Re-s am pled sign al : From Eq. 4, it is clear that diff eren t in terpo la tors w ill change the st ru ctu re of the ori gin al sign al in d iffe ren t w ays . The resu lti ng p eriod ic vari ance fun cti on com puted usin g Eq. 4 for the near est-n eigh bor in t erp ola tion. Hence , sig nals inte rpolated by this in t erp ola tor are eas ily recogn ized by applying a deri vativ e opera tor to them (Hou and Andr e ws , 1987 ). It is continu ous but its first deriv ative is discon tinuou s. Cub ic inte rpolati on is a very frequ ently use d in t erp ola tion techniq ue and has been widely stud ied. It use s a thi rd orde r int erpol ation polyn omial as th e kern el. Rad on trans forma tion: Rad on transf ormati o n is appl ied to f ind tra ces of aff ine tr ansforma tion. T he Rad on trans format io n compu tes project ions o f magn itude of D n {b(x , y )} along specifi ed direc tion det ermin ation by an a ngl e θ. The pr ojectio n is a line i ntegral in a certain directio n. This line i ntegral is expr essed as: 𝜌𝐷 { 𝑏 } ( 𝑥 , 𝑦 ) = ∫ |𝐷 { 𝑏 ( 𝑥 , 𝑦 ) } | 𝑑𝑙 (8) By assumin y that: 𝑥 , 𝑦 , = 𝑐𝑜𝑠Ɵ 𝑠𝑖𝑛Ɵ −𝑠𝑖𝑛Ɵ 𝑐𝑜𝑠Ɵ 𝑥 𝑦 (9) It is po ssible to represent the Radon tr ansform i n the followin g way: 𝜌Ɵ ( 𝑥 , ) = ∫ 𝐷 { 𝑏 ( 𝑥 , 𝑦 ) } . ( 𝑥 , 𝑐𝑜𝑠Ɵ − 𝑦 , 𝑠𝑖𝑛Ɵ , 𝑥 , 𝑠𝑖𝑛Ɵ + 𝑦 , 𝑐𝑜𝑠Ɵ ) 𝑑 𝑦 , (10) The Radon tran sformat ion is com puted at ang les θ from 0-17 9 degree s, in 1 degree increm e nts . Henc e, the out put o f this is 180 1-D vect ors, δθ (θ is the orien tation of the X ’ axis countercl ockwis e f rom the x -axi s). The cor resp onding auto cov arian ce seq uences of δθ contain a spe cific s trong p eriodici ty, if th e invest igated signal h as been re-sam p led . The auto covariance seque nces of θ is computed a s Eq.11: 𝑅 Ɵ ( 𝑘 ) = ∑ ( ρθ ( i + k ) − ρθ ) ( ρθ ( i ) − ρθ ) (11) The proj ect target is to determine the image bein g investigated has undergone affine transfor mation. Hence, we foc us onl y on the s trongest p eriod ic p atterns present in the a uto covar iance Rδθ. End time 4 Fig. 2: Pro posed sys tem p erfor mance flowchart Image recog nition: T he d ifficulty o f r ecognizing faces is a cla ss if ica ti o n p ro bl em. T he pr op o sed te c hniq ue use s a r ti fic ia l neu ro ns in or de r to tra in th e c la ss ifi er . It al so invo l ve s a dime ns io na li ty r ed uc ti on pr ep roc e ssi ng o f the fa c ia l i mage s. In rec e nt t ime s, BP N N s yste m (V in a y e t a l . , 2 0 07 ) i mpl e ment at io n mak e us e o f fr a cta l enc od i ng me tho d , t he fr ac ta l co de s wer e pre se nt ed a s inp u t t o th e BP N N f or id e nti fic a ti on pu rp os es . Howe ve r, i n ord er to c o mpl et e ima ge au the nti c ati on a nd rec o gnit io n i n the r e se ar ch work , fo ur st age s ar e i ntr od uce d . Proposed syste m struct ure: T he proposed resear ch work dea ls with an integration of four phases. The initial phase de als with imag e verification (o riginality authenticatio n) w ith neural network pr e-processi ng training and testing phases . Figure 2 sho ws t he flowchart per formance of this re search work that will be discussed i n four stage s. Image ve rificati on (Phase 1): The image verification phase is per formed using d etecting trace s o f image tampering s uch as re-sampling o r interpo lation or both. In this phase, a test/input process involves de rivative operat ors and radon tra nsformation. T his proc ess prod uces a periodic p attern in the image spectr um i f t he test image is forged or i t p roduce s simple i mpulse signals if the te st ima ge is still o riginal. Meanw hile , It is observe d that both image spectra form s coul d be ov erlapped that prod uces a f orm of im age tam pering . Howev er, the pro posed system spec ificat ion all ows s electi ng only orig inal tes t or input images . End time 5 Fig. 3: I mage vectorizatio n Fig. 4: Neural network tra inin g curve Image-pre processing (Phase 2 ): The i mage preproce ssing as second phase is r eady to fu nction. I n the p re-processi ng p hase, ti me effective prepro cessing is pe rformed in ord er to mak e image data be st fit for neural networ k input. Average filtering is applied a nd contrast of the image is enh anced through histogram equalization pr ocess. Then th e im a ge siz e i s reduced i n ord er to make i t light but e fficient and best fit for neural proce ssing phase. B efore moving i mages into the neural proc essing phase, all ima ges data (te st im age and trai ning da tabase images) under go a process of vector ization that is conversion of 2-D images into 1 -D vecto rs. T his conversion is due to neural network requires 1-D vectors for proce ssing and co nversion is perfor med using PCA (Esbe nsen and G eladi, 1987) and 2-D discrete cosine transfor m. Figure 3 sho ws the vectorization o f one ori ginal image. Neural netw ork training (P hase 3): T he third phase is the neural net work training. The structure of the proposed neural networ k is ba sed upo n multi-la yers that are inp ut, hidden and outpu t layer. T he number of neurons in the hidd en l ayer is d etermined by experiences and guesswork considering opti mal performance . As a final point, productio n level contai ns nerve cells that are the number of obj ects is b eing considere d. The alg o rithm for effective use of a neural networks and reduces the slope of error s through chan ging weight and offset c ontinued with i mpe tus. T he neural n e twork is trained upon some set of images and tested upon different set of i mages. In the proposed m et hod, neural network uses B PNN algorithm for e rror computation and new weight ca lculation for each neuron link. It returns the ou tput o f ea ch le vel, extract the mea n sq uare error ( MSE) and spread it b ack if it is not close to the target. The response of the neural network is reliant upon weights, biases and transfer functions. The transfer function s make use o f in the feed forward BPNN in inter mediate, input and output layer. Fig. 4 shows the trainin g graph of neural network while the system will find the or iginal image. Testing st age (Phase 4): T he four th phase is t he testi ng of the neura l network. I mages for testing are a pplied to the tra ined neural net work along with the a lread y trained database images for calc ulating the pe rcentage accurac y and error . In testi ng pha se, just like in the training p hase, incoming images unde rgo all the pre -processing sta ge and are made available to the network for e valuation. This test images (extra cted face image) is then proce ssed us i ng th e neural network a nalytic tool. After a number o f iterations b y the net work thro ugh each image in the data base, the err or reduces ba sed on the gradient de scent-lear ning rule, the se t error goal is reached and a match ing ima ge to test image is fo und as shown in the r esults sessio n. RESULTS AND D ISCUSS ION The t wo data base containin g t raining image s is made up of ten i mages n umber ed (1 -10) each, with t he same size, for mat and dimension. T he test images are sampled a nd crop ped with t he different po sition. Fig ure 5 and 6 show the image spectru m respectivel y. End time 6 Fig. 5: Origina l image spe ctrum Fig. 6: Forged image spec trum Fig. 7: I mage recognitio n End time 7 Fig. 8: Neuro ns in hidden la yer vs. execution ti me Fig. 9: Recog nition p ercentage vs. n umber of subj ects These spe ctra ar e resulted from ori ginal and forged images respec tively. The diffe rence in spectrum is seen as a kind of sinusoidal p eriodic pattern, w hic h re places or overlaps the original impul se signal s o r sp ikes of an original image. These are the result of obtaining the first a nd seco nd der ivative o f the a uto covar iance of the images. T he auto c ovariance is ob tained usi ng the ra don transfor mation through 0-179 degree s. Hence, it is a proved for efficienc y of proposed system to detec t the authenticit y of image s. Th e m ajo r int eg ral part of the pro pos ed a nal yti cal to ol i s the ca pa bili ty to ex tra ct a fa ce f rom a ful l im age and ru n i t thr ough any giv en dat ab a s e fo r a ma tch ing or equ iv al ent f ace ima ge. Fig ur e 7 ill ust rat es the rec ogn iti on of inpu t im ag e wh il e di ff eren t p osi ti on is app lie d. The high-spee d perfor mance is deter mined by the prop er selection o f th e number of hidden neurons. T he larger amount of hid den neuro ns results the faster network converge s. Figure 8 s hows the time consuming End time 8 required wh en the hidd en la yers i n neural net work proce ssor are incr eased. Figure 9 sho ws the error pe rcentages of pr oposed analytical tools when the numbe r o f i maged are increased. As shown in Fig. 9, it is found that with increasing the n umber of su bjects, performance error that i s per centage of rec ognitio n with utilizi ng PC A and BPNN a pproach will decrease slightly. M ATERIALS AND M ETHO DS The analytical image a uthentication tool designed based on graphica l interfaci ng co mputer-aided syste m. The design process was to create software m o del of efficient to ol usi ng MAT LAB-GUI so ftwar. T he syste m was designed simula ted f o r image authent ication and classificatio n. The d esign was e mulated the follo wing characteristic s; neureal network pro cessing, loca l binar y pattern and fina ly analytica l too ls smart s ystem. CONCLU SION In this research w o rk, an integrat ion o f i mage forgery d etectio n with a n i mage facial r ecognitio n analytical tool using bac k pr opagation neural net work was propo sed. In this proj ect the te st image is authenticate d be fore b eing fed into the reco gnition tool . Therefor e, the result of the first image veri fication of this pro ject confirms the or iginality or a lteration of an image before it is feed into the r est of the algorith m for recognitio n purpose . I t also introduce s co ntrast stretching of hi stograms, dual data base a nd a djustable perce ntage err or as a functio nality of t he p rop osed research work. T he BPNN for face image recognitio n is only hi ghly a ccurate with sma ll number of subj ects and requires a lo wering of the im age r esolution for a whole recognitio n task as a way o f r educing t he co mputationa l complexity. T he pro jec t was designed and in vestigated and it w a s found that t he resolution improved b y ±2% error r ate when number of database images app lied is less than 20 i mages. REFERENC ES Ahonen, T. and A. Hadid, 2006. Face reco gnition wi th local binary patterns: Application on Face Recognition, Pro c. IEEE T ransactions on Pattern Analysis a nd Mac hine I ntellig ence IE EE P ress, 28: 2037 -2041. DOI: 10. 1109/TPAMI.200 6.244 Bolme, D ., R. Be veridge, M. Teixeira and B. Draper, 2003 . T he CSU Face Identificat ion Evaluatio n System: Its Purpo se, Features and Struct ure. Internatio nal Conference on Visio n Systems, pp: 304-31 1. Graz, Austria, April 1 -3. Published b y Springer-Verla g. DOI: 1 0.1.1.89.1 918 Esbense n K, Geladi P. 19 87. Che mometrics and Intelligen t Labor ator y System s. Pr oceedi ngs of t he Multivariate Statistic al Workshop for Geo logists and Geoche mists, Volume 2 , Issues 1 – 3, pp. 37 – 52. DOI : 10.1016/016 9-7439(87)800 84-9 Gallagher, A.C., 2005. Detection of linear and cubic interpolatio n i n JP EG c ompressed images. I n Proc eeding of the IEEE Co mputer. Soc 2 nd Canadian Conf. Compute r Robot Vision, Washington, DC, pp: 65-72 . DOI: 10.1109 /CRV.2005 .33 Han, H., J. Jeong and E. Arai, 2011. Virtual out of focus wit h single i mage to e nhance 3 D per ception. IEEE Conference o n 3 DT V T he True Vision- Capture, T ra nsmission and Disp lay of 3D Video, pp: 1-4 D OI: 10.11 09/3DTV.2011 .587718 8 Hou, H. and H . Andre ws, 1978. C ubic splines for i mage interpolatio n and d igital fil tering. IEE E Tr ans. Acoust., Speech Signal Process., 26: 508-517. DOI: 10 .1109/TASSP.1 978.1163 154 Jaeyoung, K. and H. J un, 2011. Implementation of image pr ocessing and au gmented re ality p rograms for s mart m o bile d evice . I EEE Conference o n Strategic T echnolog y (IFOST). 2 : 1070-10 73. DOI : 10.1109 /IFOST.2 011.6021205 Kumar, V.B., B.S. Shreyas a nd G.C.N.S. Murthy, 2 007. A Ba ck Propa gation Based Face Re cognition Model, Using 2D Symmetric Gabo r Fe atures. I EEE Proc eeding of The Signal Processing, Communica tions And Net working, pp : 433-43 7. DOI: 10 .1109/ICSCN.20 07.3507 76 Lu, J., K .N. Plataniotis and A.N. V enetsanopo ulos, 2003 . Regulariz ed Discriminate Analysis F o r the Small Sample Size Problem in Face recognition, Science Direct P attern Recognition Letters. Sci. Direct 24: 3079 -3087. DOI: 10.1016/S016 7- 8655(0 3)00167 -3 Mehryar, S., K. Martin, K.N. P lataniotis and S. Stergiopoulos, 20 10. Auto matic land mark detection for 3D f a ce image pro cessing. IE EE Conference o n E volutio nary Co mputation ( CEC), pp: 1-7. DOI: 10.1109 /CEC.2010 .558652 0 Ming, H., Q. Zhang a nd Z. W a ng, 2008. Application of Rough Sets to Image P re-Proce ssing for Face Detection. IEEE P roc. Of the infor mation a nd automation , pp: 545-548. DOI: 10.1109 /ICINFA.200 8.4608060 Pope scu A.C. and H. Far id, 2005. E xposing digital forgeries b y detecting tra ces of re -sampling. IE EE Tr ans. Signal Process. , 53: 758-767. DOI: 10.1109 /ICOSP.200 6.345714 End time 9 Prasad , S. and K.R. Ra makrishna n, 200 6. O n re- sampling detection and its application to image tampering. in cedin ging of the IEEE Interenationa l Conference Multimedia Expo ., Tor onto, ON, Canada, pp: 1 325-1328 . DO I: 10 .1109/ICI EA.2009 513840 6 Sirovich, L. and M. Kir by, 198 7. A lo w dimensiona l proce dure for the c haracterizat ion o f human face s. J. Optical Society Am., 4:519-524. DOI: 10.1364 /JOSAA.4.0005 19 Turk, M. A. and A.P. Pe ntland, 19 91. Face recognition using ei genfaces. IEEE Conf erence o n Co mputer Vision and Pa ttern Recognitio n, pp : 586-591 . DOI: 10.1109 /CVPR.19 91.139758 Wiskott, L., J.M. Fellous, N . Kuiger and C. von de r Malsburg, 1 997. Face r ecognition by e lastic b unch graph matchi ng. IE EE Trans. On pattern Analysis and machine i ntellige nce, 19: 775-77 9. DOI: 10.1109 /34.598235 Wu, C.J . and J.S. Huan g, 19 90. Human face pro file recognitio n by co mputer. J . Sc i. Direc t Patter n Recognition, 23: 2 55-259 . DOI: 10.1016/0 031- 3203(9 0)90013 -B
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment