Abstract Interpretation of Stateful Networks
Modern networks achieve robustness and scalability by maintaining states on their nodes. These nodes are referred to as middleboxes and are essential for network functionality. However, the presence of middleboxes drastically complicates the task of network verification. Previous work showed that the problem is undecidable in general and EXPSPACE-complete when abstracting away the order of packet arrival. We describe a new algorithm for conservatively checking isolation properties of stateful networks. The asymptotic complexity of the algorithm is polynomial in the size of the network, albeit being exponential in the maximal number of queries of the local state that a middlebox can do, which is often small. Our algorithm is sound, i.e., it can never miss a violation of safety but may fail to verify some properties. The algorithm performs on-the fly abstract interpretation by (1) abstracting away the order of packet processing and the number of times each packet arrives, (2) abstracting away correlations between states of different middleboxes and channel contents, and (3) representing middlebox states by their effect on each packet separately, rather than taking into account the entire state space. We show that the abstractions do not lose precision when middleboxes may reset in any state. This is encouraging since many real middleboxes reset, e.g., after some session timeout is reached or due to hardware failure.
💡 Research Summary
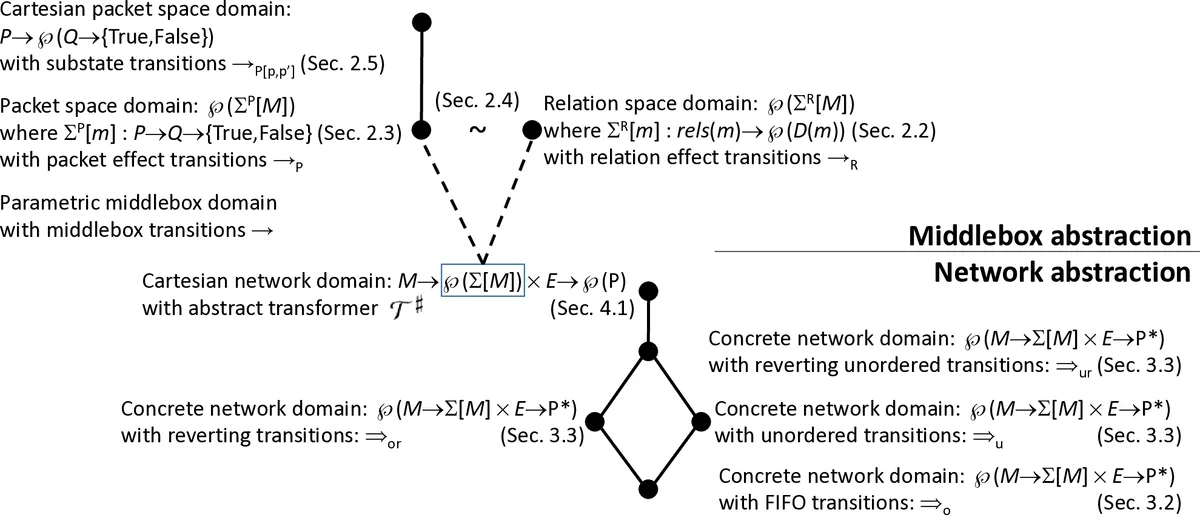
The paper tackles the verification of safety properties—specifically isolation—in modern networks that contain stateful middleboxes such as firewalls, caches, and load balancers. While previous work modeled middleboxes as finite‑state programs and abstracted away packet ordering, the resulting verification problem remained EXPSPACE‑complete, making it impractical for realistic networks. The authors propose a novel abstract‑interpretation framework that combines several layers of abstraction to achieve polynomial‑time analysis in the size of the network, with an exponential factor only in the maximal number of state queries a middlebox can perform (denoted k), which is typically small (often ≤5).
The approach consists of two orthogonal abstraction dimensions:
-
Network‑level abstractions:
- Order abstraction: The algorithm ignores the exact order in which packets arrive at each middlebox and the number of times a particular packet may be processed.
- Counter abstraction: It abstracts away the exact cardinality of packets pending on each channel.
- Cartesian abstraction: Correlations between the states of different middleboxes and between different channel contents are removed, treating each component independently.
These three abstractions together produce a chaotic‑iteration fixed‑point algorithm whose state space is polynomial in the number of middleboxes, hosts, and packet types.
-
Middlebox‑level abstraction – Packet Effect Semantics:
- Traditional semantics store the full content of each relation maintained by a middlebox. The authors observe that, because the language (AMDL) restricts relation updates to insertions or deletions of tuples built solely from packet fields and constants, the effect of a middlebox on any particular packet can be captured by the truth values of all membership queries that the packet would trigger.
- They define a packet‑effect state as a function mapping each possible packet to a map from each query to a Boolean value. This representation decomposes a monolithic middlebox state into loosely coupled per‑packet effects.
- A transition in this semantics updates the Boolean outcomes for all packets whose queries are affected by a relation insertion or deletion. The authors prove that this semantics is bisimilar to the original relation‑effect semantics, guaranteeing no loss of precision.
The key insight is that, under the packet‑effect representation, a Cartesian abstraction that discards correlations between different packets incurs no additional precision loss for a large class of networks: those that are safe even when packet processing order is arbitrary and when middleboxes may revert to their initial state at any moment. The latter “revert” capability models realistic phenomena such as session time‑outs or hardware failures. Remarkably, the presence of arbitrary resets simplifies verification: the analysis becomes exact (no false alarms) under these conditions, whereas without resets the problem remains EXPSPACE‑complete.
Complexity analysis shows:
- The algorithm runs in O(poly(N)·2^k) time, where N is the size of the network (number of hosts, middleboxes, and packet types) and k is the maximal number of state queries per middlebox.
- When k is a fixed constant, the overall verification is polynomial in N, essentially optimal given the lower bound proved by the authors.
The authors implemented the technique and evaluated it on synthetic and real‑world topologies, including a buggy cache‑firewall chain (Fig. 1) and larger data‑center‑style networks with dozens of hosts and middleboxes. The tool detected the known safety violation in the buggy configuration and verified the correct one, scaling to networks with hundreds of hosts in a few minutes. The experiments confirm that the exponential factor is indeed limited by the small k observed in practice.
In summary, the paper introduces the first abstract‑interpretation algorithm for stateful network safety that:
- Leverages a novel packet‑effect semantics to enable a powerful Cartesian abstraction.
- Provides soundness (no missed violations) and, under realistic reset assumptions, precision (no false positives).
- Achieves polynomial‑time performance in network size, with only a modest exponential dependence on a parameter that is small in real deployments.
Future directions suggested include automated minimisation of k, handling dynamic policy updates, and extending the model to richer packet payload abstractions.
Comments & Academic Discussion
Loading comments...
Leave a Comment