ECG encryption and identification based security solution on the Zynq SoC for connected health systems
Connected health is a technology that associates medical devices, security devices and communication technologies. It enables patients to be monitored and treated remotely from their home. Patients' data and medical records within a connected health …
Authors: Xiaojun Zhai, Amine Ait Si Ali, Abbes Amira
1 Corresponding author: Xiaojun Zhai, Departm ent of Electronics, Co m puting and Mathematics, Kedleston Road , Derby, DE22 1GB, Tel: 01332593892, Em ail: x.zhai@derby.ac.uk ECG Encryption and Id entification based Security Solution on the Zynq SoC for Connected Health Systems Xiaojun Zhai, Department of Electronics, Computing and Mathematics, Un iversity of Derby, UK Amine Ait Si Ali, KINDI Center for Computing Research, Qatar University, Qatar Abbes Amira, KINDI Center for Computing Rese arch, Qatar University, Qatar Faycal Bensaali, KINDI Center for Computing Research, Qatar Univ ersity, Qatar 2 Abstract — Con nected health is a technology that associates medical device s, security devices and communication technologies. It enables patients to b e monitored an d treated remo tely from their ho me. Patients’ data and medical records within a connected health system shou ld be securely stored and transmitted for further analysis and diagnosis. This paper presents a set of security solutions that can be deployed in a conn ected health environ ment, which includes the advanced encry ption standard (AES) algorithm and electroc ardiogram (ECG) identification sy stem. Efficient Sy stem-on-Chip (SoC) imple mentation s for the proposed algor ithms have been carried out on the Xilinx ZC702 prototyping board. The Achieved hardware implem entation results have shown that the proposed AES and ECG identification based system met the real-time requirements and outperformed existing field programmab le gate array (FPGA)-based systems in different key performance metrics such as processing time, hardware resources and power consumption. The pro posed systems can process an ECG samp le in 10.71 ms and uses only 30% of the available hardware resources with a power consumption of 107 mW. Keywords — Advanced encryption standard (AES), electrocardio gram (ECG) encryption and identificatio n, field programmable gate array (FPGA), Zy nq7 system on chip (SoC). 3 I. INTRODUCTI ON Population of middle aged and old people is the most dominated in the highest developed countries and regions, which requires govern ments to deal with the problems in the health-care sector [1]. This results on lim ited number of working adults to take care of the growing dependent elder ly population, which may cause potential financial problems, but also increasing the time for a patient to rece ive treatment [2]. Therefore, new solutions are necessary to increase the level of automation from the existing systems and be able to safely and efficiently handle the enormous amounts of data generated, stored and transmitted between them [3]. One of the most promising technologies to achieve this is to apply the Internet of T hings (IoT) paradigm, in wh ich information and communicatio n systems are embedded in a health care environment [4]. In this paper, the field of wireless monitorin g of vital signs using IoT is proposed, in which it embraces the measuring and digitisa tion of vital sign s such as the blood pressure or electrocardiograms (ECGs), transmittin g packets over a wireless network and delivering this medical information to health-care professionals. It allows the use of what is defined as pervasive health-care: “health-care to anyone, anytime and anywhere” [5]. It can be used in clinics and hospitals to ease the monitoring of patients, but also outside of medical facilities, giving elderly or sick people th e oppo rtunity to be part of their soc ial communities by b eing simultaneously monitored and/or even in contact w ith their health-care provid er. Such systems can, if they are designed appropriately , deal with a high amount of patients, by consuming fewer resources in terms of care attendants and capacities of medical facilities and help to make health-care more efficient and econ omical. Since the health-care d ata contains h ighly sen sitive and personal data, stro ng security issues should be add ressed to avoid serious consequences, causing damage, disruption to operations or, in some scenarios, even loss of life, one of the solution to that is to apply p rotection and encryptio n on the healthcare data [6 ]. There is a h igh interest in using the health-care monitored biometric signals to identify the individual patien ts. The main benefits of this approach are that there is no need for supplying extra bio metric sensors and the biometric signals are continuou sly monitored together with other medical signals. An ECG signal is l e ss prone to fraud and it has been widely used in the field of health monitoring where it can provide an automatic living identification system. This sy stem helps monitoring the life of the patient since the ECG sign als are a sign that the perso n is still alive and provide vital information about th e health conditions. The drawback o f using ECG signals for hu man identification is that there is a large nu mber of sign als comi ng from the se nsor t hat need to be p roces sed i n real-ti me. 4 In addition to patient identi fication, priv acy and security o f transmitting and storing patien t’s medical d ata is also a major issue in co nnected health. Data and various information are shared b etween different org anizations, platforms and people in the health industry . Therefore, data encryp tion is vital to protect and secure infor mation. Advanced encryption standard (AES) algorithm is considered as the state o f the art encryption system that is widely used in many applications including con nected health systems [7 ]. Programmable system-on-Chip (SoC) based implementations are being used by researchers to accelerate digital signal processing (DS P) algorith ms to meet the real-ti me requirements by explo iting the paralle lism, pipelin ing and the hardware/software co-design offere d by such platforms. For the encryptio n and ECG identification systems, th e SoC-based solution can be used to collect data from ECG sensors and process it in real-time. Compactness and cost effectiveness are so me of the advantage s when using su ch solutions. Further more, reconfigu rability of progr ammable devices provides the user with a p ossibility to easily upgrade and calibrate their sy stems depending on the needs. Heterogeneous platforms, such as the Zy nq SoC, based hardw are, p rovide not only similar adv antages but they also provide the user with h igher flexibility where v arious interfaces, processing system (PS) and p rogrammable logic (PL) can be used. This paper presents a set of security solutions that can be deployed in a connected he alth environment with applic ation to ECG. Thi s incl udes ECG encr yption using the AES algorithm and ECG identification using multi resol ution and p rincip le c omponent analysi s (PCA) . Effi cient SoC implem entati ons fo r the propose d alg orithms have been carried out on the Xilinx ZC702 prototyping board equipped with the Z ynq SoC device. The implementation is verified using the d ata obtained from two p ersonal data sets measure d from the VS100 ECG sensor [8] and the S himmer3 ECG se nsor [9] as w ell as the public ECG MIT-BIH database [10]. Achieved results have shown that the proposed sy stem only requires 3 0% of the available hardware re sources and 107 mW to process an ECG sample in 10.71 ms, which outperforms the ex isting field programmable gate array (FPGA )-based implementations in different key performance metrics. This paper starts by reviewing the state of the art AES algorithms and ECG identification systems in se ction II. The simulation o f the proposed appro ach for AES algorithms and ECG identification are p resented subsequently in sectio n III. This is followed by the descr iption of the proposed system architecture and its hard ware implementation in Sec tion IV. Experimental setup and resu lts analysis are then given in section V. Finally conclusions are drawn . 5 II. R ELATED W ORK Connected health sy stems have been increasingly attracting ma ny researchers. In this se ction, the most recen t and related work to connected health is summarised. In [11], a system is pro posed to monitor the heart of cardiac patients using ECG measurements. The heart electrical impulses are collected using an ECG sensor and a personal digital assistant (PDA) is used to p rocess the ECG signals and perform the diagnosis. The PDA is capable of calling the medical staff in the cas e of an emergency o r critical situation. The u ser can also visualize his /her own medical da ta using a graphical in terface on the PDA. Ano ther connected hea lth system is presented in [12] where a sensorized glove for measuring hand finger flexion for rehabilitation purposes is developed. The sy stem consists of a glove and a set of configured sensors placed in specific places and connected to the acquisition unit. The aim is to give feedback to the rehabilitation sy stem using fingers’ positions. In both [1 1] and [12] the security and privacy is to be improved. AES/Rijndael is a block cipher that c an encrypts blocks with a fixed length of 128 b its and a corresponding decipher that is basically a simple i nversion of the ci pher [13]. A high throughput pipelined approach was presented in [14], however, this was achieved with the sacrifice of hi gh design effort and resource consumption. A similar low area and memory free solution for the implementation of the AES algorith m on FPGA was presented in [15], the proposed design that uses an 8 -bit data path, supports 128-bit keys and requires 1 60 clock cycles for one encryption was implemented on both Spartan 3 (X C3S50) and Spartan 6 (X C6SLX4) FPGA s requiring 184 and 80 slices respectively. The cla imed throughpu t is 36.5 Mbps for the Sparta n 3 while it r eaches 58.13 Mbps for the Spartan 6. The implemented design consists of five blocks: ShiftRow , Sbox, MixColumn, KeySchedule and Delay, the key point of this solution is that it uses the Xilinx SRL 16/32 to implement key Schedule block to reduce the number of slice s. Anot her hig h throug hput an d pipe lined im plem entat ion of AES algorithm on FPGA was presented in [16], the implementation was performed on both Virtex-5 and Virtex-6 and the best c laimed throughput of 260 Gbit/s was achieved for the implemen tation using the counter mode on the Virtex-6. The key point is that the Sbox implementation here combines betwee n both memory and non-memory based approaches. A high throughput solution was also presen ted in [17] for an implementation on Virtex 5 using VHD L, the claimed throughpu t is 222 Gbit/s. Other solution was presented in [18] for the implementation of the AES encryption algorithm on an ASIC 65- nm CMOS, 22-nm CMOS and NVidia GeForce 8800 G TX. A hardware implementation on FPGA of an improved version of the unsecure data encryption standard (DES) is presented in [19]. It has been presented in the contex t of 6 threats to cryptographic chips. The literature review has also shown that the use of high level synthesis (HLS) tools such as Vivado for the implementation of the AES algorithm in contrast with the use of HDL codes can help resolving various issue s such as complex ity and the time require d for design verification and evalua tion, this has been discussed in [2 0] and [21]. It has been sh own that HDL based d esign offers more flexibility and control while using HLS based design save a considerable amount of time while having the same frequency, throughput and area. Various techniques have been used in the past along with different i mplementations for the use o f ECG signals for human identification. Two main app roaches are being used to extract the most useful features from signals generated by an ECG sensor [22]. The first one is the fiducial approach that consists in the search for specific points of interest to extrapolate timing and magnitud e measurements. In th is approach the ty pical features are link ed to peaks and timing duration of the P, QRS and T waves which are the representation of the hea rt activity in terms of depolarization and repolarization of the atria and ventricles. Features related to the physical functionality of the heart are not considered in the fiducial approach, only statistica l and analytical features fro m the morphology of the signal waveforms are considered. In [23], a fiducial approach based on the multi resolution D aubechies D4 and D6 wavelet transforms is proposed to detect the QRS complex and the onsets and offsets of the P and T waves on the MIT-BI H database [10]. A positive recognition rate of 98% was achieved . In [24], researchers hav e developed a quadratic Spline wavelet based framework that aims at the automatic analysis of single lead ECGs for human identifica tion, the maxima, minima and zero crossing values in the w avelet co efficient reconstruction o f the ECG signals at various scales are found prior to the detection of the QRS, P and T fiducial points. The fiducial approach in this con tribution has shown a positive reco gnition o f 99.61% when applied to the MIT-BIH d atabase. The second main approach to extract features from ECG signals for human identification is called the fiducial independent approach. The fiducial independent approach was used by [25] achi eving a positive recognition rate of 99.6%. The wavel e t coefficients have been extracted by using the Daubechies wavelet of order eight, the independent component analy sis (ICA) is used to find the independent components from the statistical independ ent rando m variables; finally the PCA is used to reduce the dimensionality of the extracted feature. Various SoC based human identification syste ms using ECG signals have been found in the literature [26-29]. An ECG-QRS complex detection has been imple mented on the Xilinx Virtex-II pro FPGA in [26], an identification rate of 99.681 % wa s achieved testing on the MIT-BIH database. Another SoC implementation using FPGA was presented in [27], it consists in the detection of arrhythmia patterns using ECG 7 signals. In [28] and [29], two other embedded sy stem based implementations were presented for the ECG sign als denoising, filtering and compression. The work presented in this pap er aims at providing an efficient architecture and implementation of the AES-128 encryption and ECG-based identification system for protecting perso nal medical data privacy . The achieved results show that the speed, resources and power consu mption of the proposed imple mentation are sufficien t for the use of the proposed architectures in the connected health sy stem. The main contribu tions of this paper can be su mmarised as foll ows : A novel SoC so lution i s introd uced. I t unifi es wire less he alth-c are monit oring s ystem with th e identif ication of individuals using ECG . The proposed approach introduces a way to integ rate the acquisition and processing unit into reconfigurab le hardware. This allows the implementation of a h igh-perform ance state-of-the-art data processing sy stem which is also highly adaptive. The communicatio n, visualization, security and identification can be realized on one piece o f hardware without making the compro mise of resource sharing and time-consu ming sequential execution of tasks. III. P ROPOSED S YSTEM A. System Overview An overview of the proposed system can be seen in Fig. 1. The aim is to collect ECG signals in a saf e and secure envi ronment such a s a hos pit al, hom e or am bulanc e. The co lle cted da ta ca n then be sent wirel essl y to the l ocal processing unit based on the Zynq SoC w here all informatio n will be processed in real-time. Identification of the patient is performed based on the ECG signals collected locally, other ECG based examinations can be performed in the hospital or in the ambulance In the case where the data need to be sent to a different location for furthe r examination or for exchan ge of information, the data will be encryp ted first using the AES algorithm and then decrypted when received in the final destination. Three types of ECG signals data sets have been used to evaluate and validate the system. Two are private data sets co llected in the lab and one is a public data set. The two personal da ta sets are obta ined using the V S100 ECG sensor [8] and the Sh immer3 ECG sensor [9] wh ile the public o ne is the MIT-BIH database [10]. B. Software Simulation Simulation of the proposed algorithms is carried out using both MATLAB and C/C++ environment, where MATLAB is used to generate an ECG database that contains the required files for testing the AES c ipher-decipher 8 block and ECG identification b lock. Fig. 2 shows an overall system block diagram. 1) ECG Database In Fig. 2, the ECG database block consists of four diffe rent data, includ ing original ECG signal, Eigen ECG vector, projected training vector and mean vector. The original ECG signal is divided into two sub-sets, one set is used for training, and the other set is used for testing. The testing se t is stored into text files, to be used in cipher block. However, the training file is used for enrolment and gener ating the relevant featur e data sets. The Eigen ECG matrix E , proje cted trai ning p and mean vectors m are the correspo nding ECG fe atures . It first establis hes one sing le mean signal and then it calculates the variation of each ECG from the mean ECG signal and stores them again in a matrix A . This matrix is used to calculate the covariance matrix to reduce the computa tion time and resources. A surro gate L of the covariance matrix C is used to calculate the eigenvectors V and eigenvalues D . The advantage of doing this is that L has much lower dimension than C , which could significantly redu ce the computation time. The eigenvectors are sorted and eliminated by the size of the e igenvalues. If the eigenvalue is lower than on e, the correspondin g eigenvector is eliminated. However, these eigenvalues do not represent the eigenvectors of the covariance matrix C , which are recovered by multiplying the sorted eigenvectors of L with the d eviation matrix A . Fig. 1. System Overview. 9 Fig. 2. Overall block diagram [30]. The deviated ECG signals are projected from matrix A onto the ECG space, which represents the unique features of the training ECG signals. In order to calculate the feat ure s of the ECG signals u sed for testing, the mean of the training database must first b e subtracted fro m the test signal. Subsequently, the p rojected vector is then calculated via a multiplication of the Eigen ECG matrix by the mean subtract ed signal. This process is repre sented by the following equ ation: T pE I (1) where E is the Eigen ECG matrix, I is th e mean subtracted signa l, and p is proj ecte d test vect or. 2) AES Cipher-decip her The text files that contain the origi nal ECG signals are firs tly used in the cipher block. The encrypted text files are then used in decipher block. Finally, the decrypted text files are used in the identification block . The algorithms of the c ipher-decipher block is revised and implemen ted in C++ based on the wo rk presented in [31]. The algorithm supports AES-128 standard, 3) ECG Identification In the ECG identification block , the same process of gene rating the database is repeated, where the testing ECG signal is projected to the ECG space usin g equation (1). The next step is to calculate the Eu clidian distance between each projected tra ining vector and the pro jected test vector using equation 2. The index of the mi nimum error between the feature vectors represents the ID of the 10 identified EC G. 2 1 (' ) n ii i dp p (2) where d i is the Euclidian distance between the i th training vector and the projected test vector. p and p’ are the projected test vector and th e i th proje cted tr aining ve ctor re specti vely. This process could be called just once fo r a single identifica tion o r for all t est sam ples f or eval uating the al gorit hm. The single identification process is justified as it allows grea te r scrutiny o f a test signal that was falsely recognized, because a plot shows three sign als: the test ECG; the exp ected training ECG; and the identified ECG for further analysis, such as the difference between the signals. Furthermore, the single identification process can be used for security identification, as the display ed ID can be used for verification. IV. H ARDWARE A RCHITECTURE AND I MPLEMENTATION In order to ac celerate the co mputational in tensive part of the p roposed algorith ms a hardware architec ture has been designed. The propo sed architecture consists of three par ts: cipher, decipher and ECG identification blocks. Vivado HLS [32] is used to design the three blocks, where C/C ++ codes of the b locks are synthesised an d translated to a hardware description languag e (HDL). In order to transfer data and control between each block, the interface of eac h block is designed to use AXI-lite Slave Periphera l interface, which means that each block can be accessed b y a microprocessor through its peripheral bus. The main idea of this work is to design an architecture that could select different hardware acceleration blocks and per form comput ationally intensive algorithmic calculation, e .g. cipher- decipher and ECG identification block. A block diagram of the proposed system is shown in Fig. 3. Micr o pr oc essor AXI - l it e I nte rc onne ct A X I- li te M a ste r AXI -l ite Sl ave AXI- l ite Sl ave AXI- l ite Sl ave Ci phe r ECG Ide ntif ic a tio n Dec ip her Fig. 3. A block diagram of the proposed system on the Zynq SoC. 11 A. Cipher and Deci pher Bl ocks There are two data interfaces in the c ipher block, which include an input and output data array. Both in put and output data arrays are designed as 1 6×8-bit arrays, th us the block size for each ca lculation is 128 bits. The deciphe r block is an inverse ca lculation of the cipher block, which has the same input and output array s as the cipher block. The algorithm of the cipher an d decipher blocks have b een implemented using C++. Direc tives in Vivado H LS to optimise the codes for hardware implementation have been used. The used directives are summarised in the following Table I. TABLE I U SED D IRECTIVES IN C IPHER B LOCK Instance Directives Function Interface s_axilite Create AXI-Lite slave interface Array Array_Reshape Reshape the targeted array to a specific dimension Loop unroll Transforms loop by creating multiple copies of the loop body Basically, by applying different directives from Table I, the arch itecture is sy nthesised under the user control. For example, the “set_directiv e_loop_unroll” comman d allows t he loop to be fully unrolled or partially un rolled by a factor, creating as many copies of the lo op-body in the regi ster transfer level (RTL) as there are loop iterations. As a result of this, different iterations of the original loop can be run at the same time, thus the processing time of the block is significantly reduced. B. ECG Identification Block Fig. 4 shows an overall d iagram of th e proposed ECG identific ation arch itecture. The proposed ECG identification archite cture con sists of two part s: the enrolme nt and har dware acc elerat ion part. The enr olment part is com pleted on softwa re; howev er, the hardware acceler ation pa rt is perform ed on t he Zynq PL, which mainly cons ists of PCA val ues and Euclidian D istance calculators. Th e PCA values ca lculator is mainly used to perform the PCA projection (i.e. equati on 1). The E uclidea n Distance calcul ator is used to calc ulate Eu clidea n distanc e (i.e. equation 2 ). 1) PCA Projection Block In the PCA project ion block , the test input si gnal is fir st subtra cted from the mean si gnal of the complete training matr ix T . Subsequentl y, the projected vector is the n calculate d via a multipli cation of the Eige n ECG ma trix by th e 12 mean su btracted signal. This proces s is shown in Fig. 5. In Fig. 5, the si ze of test and m ean sig nal vect ors is n , which is the le ngth of t he traini ng vect or. In thi s work, the lengt h of the trai ning vecto r is set to 300. The size of Eigen ECG m atrix is m × n , where m i s the numbe r of P CA features, and n is t he size of test vect or. The test signal i s su btracted from the mean sign al, and then the resultin g vector is multiplied by eac h row of the Eige n ECG matrix one by one. Aft er that, th e results are ac cumulated and formed a project PCA vector with size of m . 2) Euclidean D istance Calculator Bloc k In the Eucli dian distance calculator bl ock, Euclidi an distance of the projected trai ning vec tor and the projec ted test vect or is calcu lated a s stated i n equati on 2. Since the calc ulation of the squ are root would not affect t he searc h of the minim um value of the Euclidian dista nce, this cal culation ha s been el iminate d to reduce the hardwar e usage. Fi g. 6 demonstrates the architecture of the Euclidian distance calculator block. In Fi g. 6, the pr ojecte d test ve ctor is the output of t he PC A proje ction bl ock, which has a size of m. The size of the projected training matrix is m × i , where i is t he numb er of t he traini ng vect ors in the trai ning databas e. Eac h row of the projecte d traini ng matrix is s ubtract ed from the projecte d test ve ctor, and t hen the r esulting differenc e is multipl ied by itself. Subsequen tly, an accu mulator is used to su m all elements and form a Euclidian distance v ector with size of i . Once the calculated Euclidean distance vector is available, the next step is to search for the minimal Euclidian distance that represents the ID of the identified ECG. 3) Directives Used in ECG Identifi cation Bloc k Similar to other two blocks, the interface directives used in the ECG i dentification block is still “AXI-lite slave bus”. There are four input arra ys, which are correspo nding to the four parameters in the datab ase block, shown in Fig. 2, respectively. However, the output o f this block is on ly a variable that conta ins the iden tified ID. Unlike the used optimization in most loops used in the other two blocks, th e di rectives “pipelined” is u sed in the ECG identification block, which could increase the throu ghput of the PCA projection and Euclidian distance calc ulator blocks. 13 Bui l d up Tr ai ni ng Dat aba se Sel ec t Tr ai ni ng and Tes t ECG Sampl es DWT fo r De n o is in g Complete PCA Compl et e PCA Value s Dat aba se of Tr ai ni ng Dat aba se Compa re C o m p ut e E uc li di an Dist anc e ID H a rd w a re Ac c e l er a ti on Pa rt Enr ol ment Par t Fig. 4. An overall diagram of the proposed ECG identification system. Fig. 5. Block diagram of the PCA projection block. Fig. 6. Block diagram of Euclidean Distance Calculator. C. Implement ation of t he Prop osed Arc hitect ures Xilinx Zynq progra mmable SoC is used for the implementation of th e proposed architectu res. Since th is type of platform tightl y integrates dual-core ARM Cortex-A9 proce ssors with Xilinx 7-series FPGA logic [33], which makes it a perfect implementation platform of the proposed architecture. The proposed architectures were firs tly generated as a set of individual IP cata logs using Vivado HLS, they were then integrate d together using Vivado Design Suite [32]. Fig. 7 shows a block diagram of the proposed system with all building blocks and their interconnections 14 generated by Vivado Design Suite as w ell as the chip layout high lighting the amount of resou rces used by each block. Fig. 7. Block diagram of the proposed implementation in Vivado Design Suite. In Fig. 7, in addition to the three user IP Catalogs, t here are four other Xilinx build-in IP Catalogs. They are “Xilinx Zynq7 Processing System”, “Processor System Reset”, “A XI Interconn ect” and “Concat”. The Xilinx processing system has direct physical connection s to DDR memory, which is used for the runn ing of the software in the Zynq7 processing system. A set of blocks of cust om logic in the PL can be controlled and m onitored by using memory mapped registers which can be accessed by processors via the AXI4 interconnect. The “Processor System Reset” is used to supp ort asynchronous external reset input which is sy nchronized with the clock. The “Concat” IP is used to concatenate the interrupt signals generated from the different blocks of custom logic. The software runs on the Zynq7 processing sy stem that controls and drives the custo m logic through AXI4 bus interface. The control process is summarized in the “Con trolling the custom logic” pseud o code. Controlling the custom logic: 1. Input: D in is the input data array of the the custom logic block. 2. Output: D out is the output data array of the custom logic block. 3. Initial p rocessor and the custom logic; 4. if Initialization is successful then 5. setup the interrupt; 6. if setup the interrupt i s successful then 7. for all data in D in do 8. write data into th e custom logic; 15 9. if the custom logic is ready then 10. start the custom logic; 11. whil e result of the custom is not ready then None ; end 12. read data f rom the custom logic to D out . 13. end 14. end 15. end 16. end V. E XPERI MENTA L S ETUP AN D R ESULT A NALYSIS In order to achieve real-time perfor mance, the signal processing algorithms are imple mented on PL as an ad-h oc digital circuit, which could b e one of the valuable soluti ons for acc elerating computationally intensive algorithms. In addition, the PL could also balance the gap between software and hard ware design to allow maximu m performance and flexibility to be delivered during development. Xilinx Vivado HLS tool [32] has been used for the design and development of the proposed hardware architecture. The desi gn was fir st im plement ed usi ng C++, and then a C ++ level sim ulation was performed. The pu rpose of this is to eval uate the results of the algor ithm whi ch shoul d be the s ame res ults obt ained fr om MATLAB imple mentati on. After that, a C/C++ synthesis was perform ed to translate the codes to a HDL. VHDL was selecte d as the target HDL. Thereafter, a RTL simulation was employed where the same C++ testbench used in C++ level simulation has been used again to evaluate the final RTL implementation, whi ch simplifies the design process for evaluating the signa l proce ssing a lgori thm. A. Vivado HLS Simulation 1) C/C++ Simu lation Prior to the hardware implementation, the proposed cipher-decipher and ECG identification system was validated using Vivado HLS C simulator. ECG signals obtained from VS100 ECG sensor [8], Shimmer3 ECG sensor [9] and MIT-BIH database [10] were used for the evaluation. A total of 60 , 2261 and 20 ECG signal samples fro m the VS, Shimmer3 and MIT-BIH databases have been used for testing resp ectively. The arch ieved recognition rate for each database is 99.5%, 95% and 100% respectively. Fig. 8 shows so me samples from the used ECG databases. Once the codes passed Vivado C simulation, the C++ codes were translated to HDL, and then RTL level simula tion is performed in order to validate the generated HDL architecture. 16 0 50 10 0 15 0 20 0 25 0 300 20 00 21 00 22 00 23 00 0 50 10 0 15 0 20 0 25 0 300 20 00 22 00 24 00 26 00 (a) (b) Sam pl e s of ECG Sam p l e s o f ECG EC G Am pli tu de EC G Am pli tu de 02 0 4 0 6 0 8 0 1 0 0 1 2 0 - 20 0 0 20 0 40 0 60 0 Sample s o f ECG (c) EC G Am pli tu de Fig 8. Samples from used ECG database. (a) Sample data collected from VS100 ECG sensor; (b) Sample collected f rom Shimmer ECG sensor. (c) Sample collected from MIT-BIH database. 2) C/RTL Co-simulation The same C++ testbench used in the C/C++ simulation was used for the C/RTL co-simulation; ho wever, instead o f using the C++ fun ction, the sy nthesized RTL architecture s ar e used to perform the calculation. Th e simulator used in the C/RTL co-simulation was XSIM where VH DL was selected as the generated HDL. The clock period for the simulation was set to 10 ns. The achieved results from the C/RTL co-simulation are the same as the C/C++ simulation. Table II summaries the processing time and hardware utilization estimate of each block. TABLE II P ROCESSING TIME AND H ARDW ARE U TILISATION E STIMATE OF E ACH B LOCK (C/RTL C O - SIMULATION ) Block Processing time (ms) LUT (%) FF (%) DSP48E (%) BRAM_18K (%) Cipher 0.022 5 0.8 0 3 Decipher 0.050 6 0.8 0 3 ECG Identification 0.404 63 9 5 5 The processing time for th e Cipher and D ecipher blocks is obta ined for processing 128 -bit input data. However, the input data size of the ECG identifica tion block is 300×3 2 bits. Based on the estimated utilization of each block, it is possible to implemen t all three block s in the sa me Zynq7 SoC, to b e a complete security solu tion for conn ected health systems. 17 B. Hardware Implementation The proposed system h as been successfully implemented on the PL of the Xilinx ZC702 evaluation board. In addition, the corresponding software (i.e. Drivers and con tr ol codes) is also implemented using the Xilinx Software Development Kit running on the ARM cortex-A9 core of Zynq7 SoC. 1) Pro grammable Logi c Utiliza tion The proposed architecture consumes about 30 % of the available LUTs and 11% flip-flops. Most of LUTs, flip - flops and DSP48E are used for creating the instances of the proposed architecture, for examp le, AXI interfaces, multipliers, etc. Other LUTs and flip-flops are used as mul tiplexe rs or registers and for creating a memory to store the resulting matrix. It is worth noting that the targ et Zynq SoC has the smallest chip capacity in its family, which means that the proposed arc hitecture has very efficient size, and can be easily deploy ed on a low-cost FPGA or integrated with other b iometric identification sy stems on a large chip. Table III shows the PL hardware usage of the proposed architecture. Tab le IV su mmarizes the hard ware resources usage o f individual b locks. 2) Power Consumpti on The on-chip power consumption consists mainly of two parts, which are static and dyn amic power consumption. The static power is consumed due to transistor leakage. The dynamic power is consumed by fluctuatin g power as the design runs, i.e. Zynq7 Processing System (PS7), clock, pow er, logic power, signal power, BRAMs pow er, etc., which are directly affected by the chip clock frequency and the usage of chip area. The details of estimated power consumption of the implementation are su mmarised in Table V. The PS7 consumes much more power than the PL; this is due to the fact that the ARM dual core Cortex-A9 based processing sy stem has much higher running frequency than the PL and it runs drivers and con trol programmes. Co mpare to the PS7, the custom logic blocks consumes on ly a small portion of the total on-chip power consumption. TABLE III O VERALL H ARDW ARE R ESOURCES U SAGE Name Usage Total Available Resources on Chip Utilisation (%) LUT 16,133 53,200 30.3 FF 11,797 106,400 11.1 BRAM_18K 17 140 12.1 DSP48E 12 220 5.5 18 TABLE IV H ARDWARE R ESOURCES U SAGE FOR I NDIVID UAL C USTOM L OG IC Name LUT FF BRAM_18K DSP Cipher 1,126 841 4.5 0 Decipher 1,212 829 5 0 ECG Identification 13,189 9,368 7.5 12 TABLE V E STIMATION OF P OWER C ONSUM PTIO N Utilization Details Power (W) Utili zati on (%) Dynamic Power Consumption Cloc k 0.02 4 1 Signals 0.028 2 Logic 0.022 1 DSP 0.004 < 1 BRAM 0.028 2 PS7 1.564 93 Static Power Consumption Device Static 0.158 9 3) Timing Analysis The ARM processor runs at 650 MHz and the PL clocked at 50 MHz. The processing time o f the proposed system is measured by coun ting the number of ARM processor’s clock c ycles spent for obtaining the calculated results of one ECG signal (i.e. 300×32 bits) from individual custom logic. Table VI shows the comparison between the software and hardware implementations of each block in terms of the processing time. As it can be seen in Table VI, the overall processing time using the hardware implementa tion has improved by a factor of 44 compared to the software imple mentation. In ad dition, the proposed i mplementation has also outperfor med the existin g ECG identification i mplementations [31] on a HS/SW hybrid pla tform by a factor o f 305. As a resu lt of this i mprovement, the processing speed meets the minimum time constraint of a real-time data processing system. TABLE VI P ROCES SI NG T IME OF EACH I NDIVIDUAL B LOCK Cipher Decipher ECG Identification Total Hardware Implementation (m s) 3.21 7.41 0.09 10. 71 Software Implementation (m s) 108.31 361.09 0.32 46 9.72 C. Comp arison with Existin g Work This section co mpares the data pro cessing throug hput of the pro posed cipher and deciph er with the w ork presented in [31 ] and [34], as well as other existing AES-128 encryption FPGA implementation. The comparison is 19 made based on the following three metrics: processing speed, area analy sis, power consumption and overall evaluation. 1) Com parison of the AES processing speed The throughput of the AES cipher and decipher is calculated using the runnin g frequency and the execu tion time. The execution ti me is measured by the clock counter in the Zynq7 PS. Th e running frequency f and the throughpu t T are then calculated according to equation s 3 and 4 respectively. t f 1 (3) f B T ( 4 ) where t is the execution time and B is block size which is equal to 128 bits for our case. Table VII presents t he results of the proposed and exiting work. As it can be seen from Table VII, the throughputs of the proposed AES cipher and decipher imple mentations have outperformed the existing work in [31] and [34] by a factor of 1.6 and 3.7 respectively. This is d ue to the fact that the proposed implementation has used appropriate direc tives in Vivado HLS in order to reduce the latency of the proposed architectures. TABLE VII C OMPARISON OF AES P RO CE SSIN G S PEED Cipher Decipher [31] [34] P roposed work [31] [34] Proposed work Execution time (µs) 41.0 40.8 25.1 213 211 57.9 Execution frequency (kHz ) 24.4 24.5 39.9 4.7 4.7 17.3 Throughput (Gbit/s) 3.1 3.1 5.1 0.6 0.6 2.2 2) Com parison of Hardware Resources Usage for AES imp lementation The occupied area after placement and routing in terms of slice s, LUTs and BRAMs is shown in Table VIII. The proposed work has significantly less hardware resource requ irement to implement AES cipher and decipher block. 20 TABLE VIII C OMPARISON OF H ARDWARE R ESOURCES FOR AES I MPL EM ENTA TIO N Cipher Decipher [31] [34] Proposed work [31] [34] Prop osed work Slice 3443 3430 372 5723 5536 431 LUTs 5513 8589 1126 5514 8262 1 212 BRAM 2 2 4.5 2 1 5 3) Com parison of Power Consumption for AES implementation Table IX shows the comparison of power consu mption for AES implementation . According to the results show n in Table IX, the proposed implementation consumes less power than the existing work. This improvement has not only benefited from the new technologies introduced in t he la test SoC, but also is optimized using Vivad o HLS. TABLE IX C OMPARISON OF P OWER C ONSUMPTION F OR AES I MPL EMENTATION Cipher Decipher [31] [34] Proposed work [31] [34] Proposed work Clock (m W) 45 45 2 95 92 2 Logic (m W) 10 10 2 48 35 3 Signals (m W) 25 25 2 252 192 2 Total (m W) 132 13 2 6 447 3 71 7 4) Com parison of Overall AES-128 encryption implementation Table X shows the comparison of o verall AES-128 encryp tion implementations of the proposed wo rk with other existing works. As it can be seen from Tab le X, the proposed work outperforms other existing work in ter ms of Throughput/Slice, which achieves 13.73 Mbps/Slice. Although the propo sed work does not have the highest throughput in the comparison, but it uses the lowest number of slices of the available ch ip area. In addition, the proposed implementation has significantly low er the clock speed compared to other work, which means that it would 21 have better power efficiency. TABLE X C OMPARISON OF AES-128 E NCRYPTI ON FPGA I MPLEMENTATION Work Dev ice Clock (MHz) Throughput (Mbps) Area (Slices) Throughput /Area (Mbps/Slice) Proposed work Zynq XC7Z020 50 5107 3 72 13.73 [14] Virtex-V XC5LVX85 576.07 73737 22994 3.21 [35] Spartan-III XC3S4000 206.28 2640 405 6. 520 [36] Virt ex-IV XC4VLX100 645.70 82650 12256 6.744 [37] Virtex-IV XC4VLX25 166.7 2134 626 4.41 [38] APEX20KC N/A 1188 895 1.33 5) Com parison of Overall ECG Identification implementation Table XI shows the comparison of the proposed FPGA-based ECG identification implemen tation with other existing work. The proposed implementation pro cesses a sample in 0.09 ms which outperforms other existing work. Although the propo sed work uses more LUTs for the implem entation a s maxim ized p ipeline and par alleli sm were set to achieve a high processing speed that meet the real-time requiremen ts. TABLE XI C OMPARISON OF FPGA BASED ECG I DENTI FICATION I MPLEMENTATION Work Device Cl ock (MHz) Proce ssing Speed (ms) LUTs Proposed work Zynq XC7Z020 50 0.09 13,189 [39] Virtex-II 20 1.87 2170 [40] Spartan 3 36 N/A 9,136 VI. C ONCLUSION In this paper a set of securit y solutions have been presented that ensure patients’ data and medica l records within a connected health sy stem can be securely transmitted and saved for further ana lysis and diagnosis. The proposed ECG identification system consists of a SoC implementation of the AES and ECG identification algo rithms, which can be used to collect data from ECG sensors, process it and meet the real-time response constraint. The proposed Zynq SoC implementation provides not only high data pro cessing performance but they also prov ide the user with higher fle xibilit y in term s of va rious i nterfa ces, har d proce ssors a nd PL. Re sults pr esent ed have shown t hat the pr oposed 22 implementation only needs 30% of hardware resources and 10 7 mW to process an ECG sample in 10 .71 ms, which outperforms the existing FPGA-based syste m in different key performance metrics. R EFER ENCE S [1] E. Gonzales, C. Matz-Costa, N. Morrow -Howell, Increasing opportunities for the produ ctive engag ement of older adults: A res ponse to population aging , The Gerontologist, 55 (2015) 252-261. [2] K. Barnett, S.W. Mercer, M. Norbury, G. Watt, S. Wyke, B. Guthrie, Epidemiology of multimorbidity and implications for heal th care, research, an d medical education: a cross-sec tional study, The Lancet, 380 37-43. [3] J. Gubbi, R. Buyya, S. Marusic, M. Palanisw ami, Internet of Things (IoT): A vision, architectural elem ents, and future dire ctions, Future Generation Computer Systems, 29 (2013) 1645-1660. [4] J.A. Sta nkovic, Research Directions f or the Internet of T hings, IEEE Internet of Things J ournal, 1 (2014) 3-9. [5] U. Varshney, Pervas ive healthcare and wireless health monitoring, Mob. Netw. Appl., 12 (2007) 113-127. [6] C. Tankard, The security issues of the Internet of Things, C omputer Fraud & Security, 2015 (2015) 11-14. [7] K. Hyejung, K. Yongsang, Y. Hoi-Jun, A low energy bio s ensor node processor for continuous healthcare monitoring system , S olid-State Circuits Conference, 2008. A-SSCC '08. IEEE Asian, 2008, pp. 317-320. [8] Intelesens Ltd, VS100 patch-based vital si gns monitor, 2015. [9] Shimmer, Shimmer 3 ECG s esnor, 2015. [Accessed on June 2015] [10] The MIT-BIH Normal Sinus Rhythm Databas e, 2015. [Accessed on June 2015] [11] C.D. C apua, A. Meduri, R. Morello, A Sm art EC G Measurement Sys tem Based on W eb-Service-Oriented A rchitecture f or Telemedic ine Applications, IEEE Transactions on Instrumentation and Me asurement, 59 (2010) 2530-2538. [12] M. Borghetti, E. Sardini, M. Serpel loni, Sensorized Glove for Measuring Hand Finger Flexion for Rehabilitation Purposes, I E EE Transactions on Instrumentation and Measurement, 62 (2013) 3308-3314. [13] J. Daeme n, V. Rijmen, The design of Rijndael: AES-the advanced encryption s tandard, Springer Scienc e & Business Media2002. [14] T. Good, M. Benaissa, Pipelined AES on FPGA with support for feedback m odes (in a multi-channel environment), IET I nformat ion Security, 1 (2007) 1- 10. [15] C. Junfeng , M. Benai ssa, Low area memory-free FPGA imple men tation of the AES algorithm, 2012 22nd International Conferenc e on Field Programmable Logic and Applications (FPL), 2012, pp. 623-626. [16] A. Soltani, S. Shar ifian, An ultra-high throughput and fu lly pipelined im plementation of AES algorithm on FPGA, Microproce ssors and Mic rosystems, 39 (2015) 480-493. [17] M.I. Soliman, G.Y. Abozaid, FPGA im plementation and performance evaluation of a high throughput crypto coprocessor, Journa l of Parallel and Distributed Computing, 71 (2011) 1075-1084. [18] M. Mozaffari-Ke rmani, A. Reyhani-Ma soleh, Effi cient and Hig h-Performance Pa rallel Hardwar e Architectures for the AES-G CM, IEEE Transac tions on Computers, 61 (2012) 1165-1178. [19] W. Shan, X. Chen, B. Li, P. Cao , J. Li, G. Gao, L. Shi, Evaluation of Correlatio n Power Analysis Resistance and Its Applic ation on Asymmetric Mask Protected Data Encryption Standard Hardware, IEEE Transactions on Instrumentation and Meas urement, 62 (2013) 2716-2724. [20] E. Homsirikam ol, K. Gaj, Hardware Benchmarking of C ryptographic Algorithms Using High-Level Synthe sis Tools: The SHA-3 Con test C ase Study, in: K. Sano, D. Soudris, M. Hübner, C.P. Diniz ( Eds.) Applied Reconfigurable Computing: 11th International Sym posium, ARC 2015, Bochum , Germany, A pril 13-17, 2015, Proceedings, Springer International Publishing, Cham , 2015, pp. 217-228. [21] E. Homsirikamol, K. Gaj, Can high-level synthesis compete against a hand-written cod e in the cryptographic domain? A case study, 2014 International Conference on ReConFigurable Computing and FPGAs (ReConFig14), 2014, pp. 1-8. [22] S. Karpagach elvi, M. Arthan ari, M. Sivaku mar, ECG feature ex traction tech niques-a surve y approach, International Journ al o f Computer Scienc e and Information Security, 8 (2010) 76-80. [23] S. Mahmoodabadi, A. Ahm adian, M. Abolhasani, M. Eslami, J. Bidgoli, ECG f eature extraction based on multiresolution wavele t transform, 27th Annual International Conference of the Engineering in Medicine and Biology Society , IEEE, 2006, pp. 3902-3905. [24] S.Z. Fatemian, D. Hatzinakos, A new ECG feature extractor for biometric recog nitio n, 16th International Conference on Dig ital Signal Processing, IEEE, 2009, pp. 1-6. [25] C. Ye, M.T. Coim bra, B.V. Kumar, Investigation of human identification us ing two-lead electrocardiogram (ECG) signals, 20 10 Fourth IEEE International Conference on Biometrics : Theory Applications and Systems (BTAS), IEEE, 2010, pp. 1-8. [26] Y. Li, H. Yu, L. Jiang, L. Ma, Z. Ji, Adaptive lif ting sc heme for ECG QR S complexes detec tion and its FPGA implementation, 2010 3rd In ternational Conference on Biomedical Engineering and Informatics (BMEI), IEEE, 2010, pp. 721-724. [27] Y. Jewajinda, P. C hongstitvatana, FPGA-based online-learni ng using parallel gene tic algorithm and neural network for ECG s ignal class ification, 2010 International Conference on Electrical Engineering/Electronics Co mputer Telecommunications and Inf ormation Technology (EC TI-CON ), IEE E, 20 10, pp. 1050-1054. [28] M. Bahoura, H . Ezzaidi, FPGA-implemen tation of wave let-based denoising technique to rem ove power-line interference from EC G signal, 2010 10th IEEE International Conference on Information Technology a nd App lications in Biomedicine (ITAB), IEEE, 2010, pp. 1-4. [29] Y. Yang, X. Huang, X. Yu, Real-ti me ECG monitoring system ba sed on FPGA, 33rd Annual Conferen ce of the IEEE Industrial El ectronics Society, 2007, IEEE, 2007, pp. 2136-2140. [30] X. Zhai, A. Amira, F. Bensaali, ECG Security Identificatio n System on the Zynq SoC Platform, Computer and Information Tec hnology; Ubiquitous Computing and Communications; Depe ndable, Autonom ic and Secure Computing; Pervas ive Intelligence and Computing (CIT/IUCC/DASC/P ICOM), 2015 IEEE International Conference on, 2015, pp. 1164-1169. [31] A. Amira, M.A. Saghir, N. Ramzan, C. Grecos, F. Sc herb, A Reconfigurable Wireless Environm ent for ECG Monitoring and Encry ption, International Journal of Embedded and Real-Time Communication Systems (IJERTCS), 4 (2013) 72-87. [32] Xilinx Inc., Vivado HLS User Guide, 2015. [Ac cessed on June 2015] [33] Xilinx Inc., Zynq-7000 All Programmable SoC, 2012. [Accessed on June 2015] [34] H. Tana, A.N. Sazish, A. A hmad, M.S. Sharif, A. Amira, Effic ient FPGA implementa tion of a wireless comm unication system us ing Bluetooth connectivity, Proceedings of 2010 IEEE International Symposium on Circuits and Systems (ISCAS), 2010, pp. 1767-1770. [35] D.e.S. Kundi, S. Zaka, A. Qurat Ul, A. Aziz, A co mpact AES encryption core on X ilinx FPGA, 2nd International Con ference o n Comput er, C ontr ol and Communication, 2009, 2009, pp. 1-4. [36] C. Dong, S. Guochu, H. Yihong, G. Zhigang, Efficient architecture and implementations of AES, 2010 3rd International Conf erence on Adv anced Computer Theory and Engineering (ICACTE), 2010, pp. V6-295-V296-298. 23 [37] H.N. U padhyay, J.B.B. Rayappan, Surve y and analysis of hardwa re cryptographic and ste ganographic systems on FPG A, Journal of Applied Sciences, 12 (2012) 201-210. [38] T. Hoang, An efficient FPGA implementation of the Advanced Encry ption Standard algorithm, 2012 IEEE RIVF International Co nfe renc e on Com put ing and Communication Technologies, Rese arch, Innovation, and Vision for the Future (RIVF), IEEE, 2012, pp. 1-4. [39] Y. Li, H. Yu, L. Ji ang, L. Ma, Z. Ji, Adaptive lifting sc h eme for ECG QRS co mplexes de te ction and its FPGA i mplementation, Biome dical Engineering and Informatics (BMEI), 2010 3rd International Conference on, IEEE, 2010, pp. 721-724. [40] P. Zicari, A. Amira, G. Fischer, J. Mclaughlin, An embedded sys tem for on field testing of human identification using ECG biometr ic, 11th International Conference on Information Science, Sign al Processi ng and their Applications (ISSPA), 2012, pp. 65-70.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
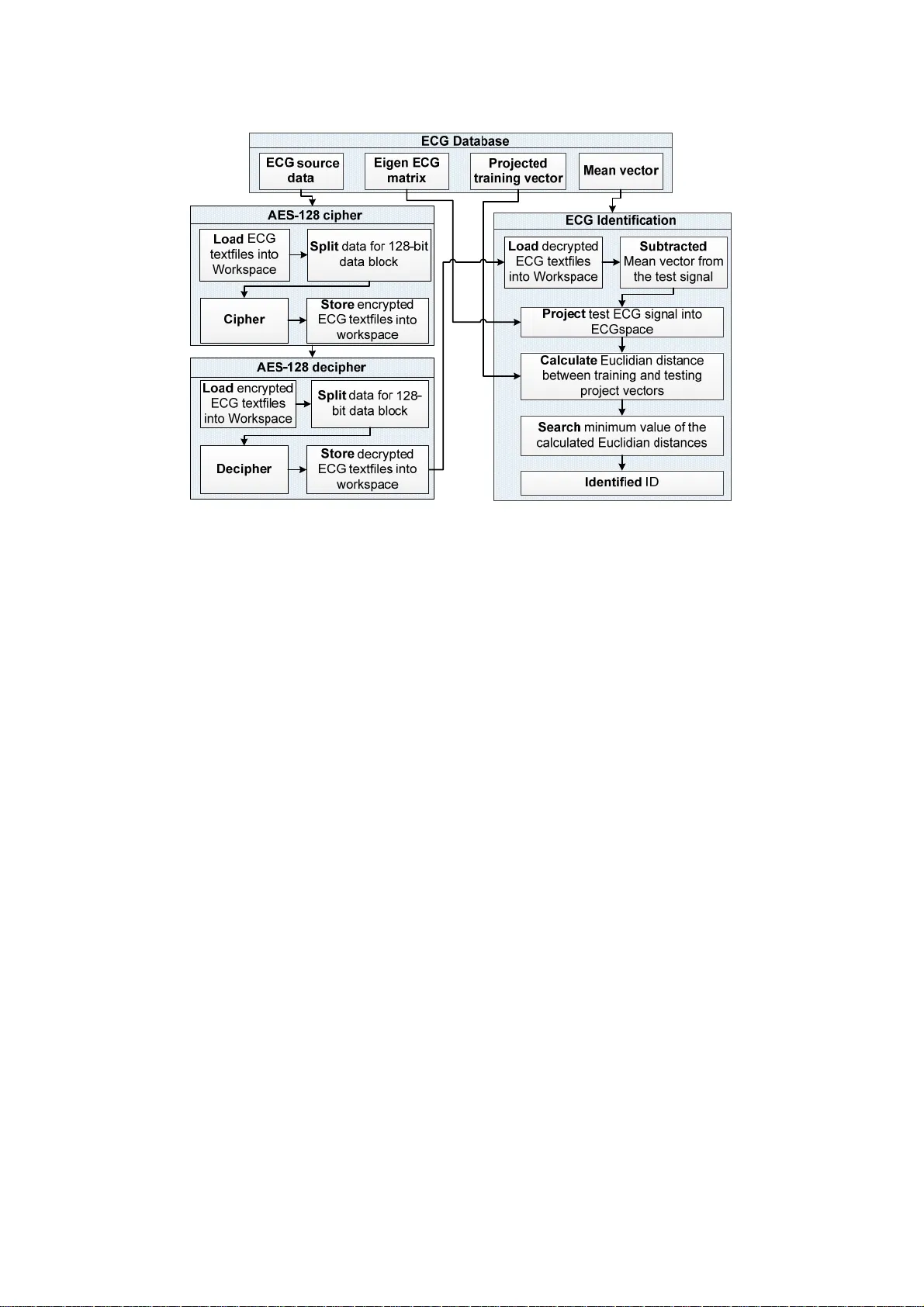
Leave a Comment