Graph-Based Resource Allocation with Conflict Avoidance for V2V Broadcast Communications
In this paper we present a graph-based resource allocation scheme for sidelink broadcast vehicle-to-vehicle (V2V) communications. Harnessing available information on the geographical position of vehicles and spectrum resources utilization, eNodeBs ar…
Authors: Luis F. Abanto-Leon, Arie Koppelaar, Sonia Heemstra de Groot
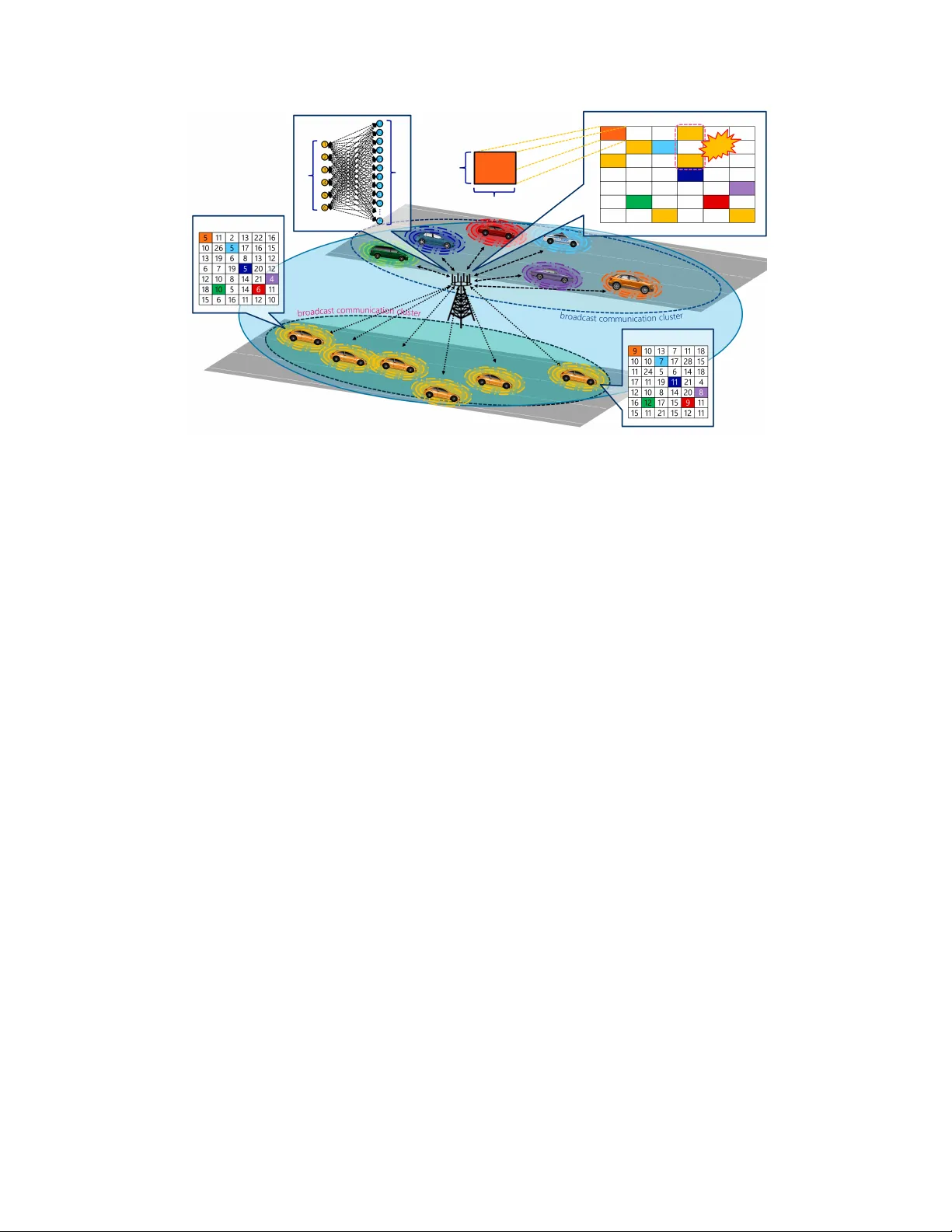
1 Graph-Based Resource Allocation with Conflict A v oidance for V2V Broadcast Communications Luis F . Abanto-Leon Department of Electrical Engineering Eindhov en Uni versity of T echnology Email: l.f.abanto@tue.nl Arie K oppelaar NXP Semiconductors Eindhov en Email: arie.koppelaar@nxp.com Sonia Heemstra de Groot Department of Electrical Engineering Eindhov en Uni versity of T echnology Email: sheemstradegroot@tue.nl Abstract In this paper we present a graph-based resource allocation scheme for sidelink broadcast vehicle- to-vehicle (V2V) communications. Harnessing av ailable information on the geographical position of vehicles and spectrum resources utilization, eNodeBs are capable of allotting the same set of sidelink resources to sev eral different vehicles in order for them to broadcast their signals. Hence, vehicles sharing the same resources would ideally be in different communications clusters for the interference lev el—generated due to resource repurposing—to be maintained under control. W ithin a communications cluster , it is crucial that vehicles transmit in orthogonal time resources to prev ent conflicts as vehicles— with half-duplex radio interfaces—cannot transmit and receive simultaneously . In this research, we hav e en visaged a solution based on a bipartite graph, where vehicles and spectrum resources are represented by vertices whereas the edges represent the achiev able rate in each resource based on the signal–to–interference–plus–noise ratio (SINR) that vehicles perceiv e. The aforementioned constraint on time orthogonality of allocated resources can be approached by aggregating conflicting vertices into macro-vertices which, in addition, narrows the search space yielding a solution with computational complexity equi valent to the con ventional graph matching problem. W e sho w mathematically and through simulations that the proposed approach yields an optimal solution. In addition, we provide simulations 2 showing that the proposed method outperforms other competing approaches, specially in scenarios with high vehicular density . I . I N T RO D U C T I O N V ehicle–to–v ehicle (V2V) communications is one of the nov el use cases under the umbrella of the ne xt generation of wireless systems 5G. Ho w can V2V communications—in its man y facets— be le veraged to comply with the v ery stringent latency and reliability requirements that this type of scenario poses, has attracted much interest. In standardization groups, for instance, support of time-critical communications in safety-related applications has drawn superlativ e attention due to the immediate implications. In this context, sev eral studies have led to the conclusion that connecti vity-enabled vehicles hav e the potential to pre vent accidents [1]. In V2V Mode 3 , v ehicles are assigned sidelink resources—by an eNodeB—to periodically broadcast their signals, namely cooperativ e a wareness messages (CAMs) [2]. CAM messages contain important information about the vehicle, e.g., velocity , direction, position, which can be av ailed by other vehicles (or dri vers) for better decision-making. An important aspect in the resource allocation process is to guarantee that vehicles—within the same communications cluster—will broadcast their signals in orthogonal time resources. This is due to the fact that their half-duplex interface does not allow simultaneous transmission and reception. As a result, vehicles in the same cluster must be allocated resources in different subframes to pre vent conflicts [7]. Nev ertheless, a resource serving a vehicle in certain communications cluster can be repurposed by another provided that the latter vehicle is exclusi vely associated to a different cluster . Thus, eNodeBs will play an important role in ( i ) effecti vely allocating resources to vehicles in cov erage and ( ii ) inferring knowledge about the association of vehicles to in-coverage clusters. It is worth clarifying that although resource allocation is managed by eNodeBs, the fact that vehicles can communicate directly without data ha ving to tra verse eNodeBs is beneficial due to proximity gain [4], lo wer latency and resource reuse gain. On the other hand, matching is a fundamental problem in combinatorial optimization and has found applications in a plethora of areas. Several matching problems can be represented by graphs, which may e xhibit a wide v ariety of morphologies and dif ferent de grees of connectedness. A very specific type of matching problems can be modeled as weighted bipartite graphs, where the objectiv e is to find a verte x–to–vertex matching—between elements of two disjoint sets of vertices—that attains a maximum sum of edge weights. This classical problem is called herein 3 SINR - V ehicle 1 SINR - V ehicle 6 V ehicle v 1 V ehicle v 2 V ehicle v 3 V ehicle v 4 V ehicle v 5 V ehicle v 6 v 3 v 1 v 6 v 5 v 2 v 4 vehicles resources conflict 7 RBs Data & Control 1ms 1.26 MHz 6ms 10 MHz Sidelink Resource Assignment Fig. 1: V ehicular broadcast communications scenario in mode-3 via sidelink unconstrained weighted graph matching [9] [10]. As already mentioned, resource allocation for V2V communications has a primary time orthogonality requirement to prev ent conflicts. A solution based on a bipartite graph would provide sound frame work for approaching a problem of this kind. Ho wev er , due to additional conflict constraints, the unconstr ained weighted graph matching approach cannot be applied straightforw ardly to our problem. W e hav e en visaged a solution where the graph with additional conflict constraints—called herein constrained weighted graph matching —is transformed into a simpler problem that can fundamentally be approached as an unconstrained graph. The objective of this paper is two-fold: ( i ) prov e that an optimal solution for the constrained weighted graph matching problem exists by means of two different approaches and ( ii ) discuss the suitability of such an approach for avoiding resource allocation conflicts in broadcast vehic- ular communications. Our paper is org anized in the following manner . In section II we explain the motiv ation for our work and synthesize our contrib utions. In Section III, we briefly re visit the unconstrained weighted graph matching problem. In Section IV , our proposed approach is described in detail. Section V is dev oted for discussing simulation results. Finally , in Section VI, we summarize our conclusions. 4 I I . M OT I V A T I O N A N D C O N T R I B U T I O N S In our system model, we consider that sidelink spectrum resources for V2V communications are decoupled from uplink/do wnlink bands. Thus, the scenario herein is different from the underlay configuration [5] where idle uplink resources are opportunistically utilized for sidelink vehicular communications. The reason is that for safety-related applications, it will be necessary to count with a frequency band that is always accessible and does not depend on the av ailability of shared resources. As we already mentioned, the allocated resources must be orthogonal in time domain, other - wise conflicts will arise. Our motiv ation is to de velop an approach capable of dealing with such type of constraints in order to provide dependable communications. For instance, in Fig. 1. we observe two clusters, each consisting of 6 vehicles. In one of the clusters, we can observe a resource conflict where v ehicles v 2 and v 5 hav e been allotted resources in the same time subframe. Our goal is to harness the information harvested by vehicles—such as channel conditions— for the eNodeB to perform an ef ficient and ef fectiv e resource allocation task. The contributions of our work are summarized: • Kuhn-Munkres [6] is a computationally efficient method that can be used for solving resource allocation problems formulated as bipartite graphs. Ho we ver , due to additional time orthogonality constraints, the resultant problem is not directly approachable by the aforementioned method. In our solution, vertices conflicting among each other have been aggregated into macro-v ertices yielding a resultant graph which is solv able by Kuhn- Munkres. • V ertex aggreg ation virtually cuts do wn the number of ef fecti ve vertices and therefore narro ws the number of potential solutions without affecting optimality . The en visaged approach can attain an optimal solution at the same computational expense as the unconstrained weighted graph matching problem. • W e sho w through simulations that our approach is capable of providing fairness among all vehicles, especially in scenarios with high vehicle density . I I I . U N C O N S T R A I N E D W E I G H T E D G R A P H M A T C H I N G A weighted complete bipartite graph G = ( V , R , E ) consists of two disjoint sets of vertices V , R and a set E = V × R of edges, as depicted in Fig. 2. An edge x ij connects a v ertex v i ∈ V with a v ertex r j ∈ R and has an associated weight c ij . The objecti ve is to find a matching 5 M ⊆ E that associates ev ery verte x in V with a vertex in R —in a one–to–one manner—and attaining maximum sum of weights. In a bipartite graph, when the cardinality of the vertex sets are equal, i.e., |R| = |V | = N , a perfect matching can be attained. In Fig. 2, the vertices v i represent the vehicles that belong to the same communications cluster V whereas the vertices r j represent the allotable resources, which are denoted by R . In this paper , we consider that the edge weights c ij represent the achiev able rate on each resource based on the SINR that vehicles perceive, i.e., c ij = B log 2 (1 + SINR ij ) , where B is the bandwidth of a sidelink resource. The goal is to assign each vehicle v i —in the sev eral communications clusters that may exist—a resource r j for it to broadcast its signal with the aim of maximizing the sum-rate capacity of the system. A. Summation Repr esentation The bipartite graph matching problem is e xpressed by max N X i =1 N X j =1 c ij x ij (1a) sub ject to N X i =1 x ij = 1 , j = 1 , 2 , . . . , N (1b) N X j =1 x ij = 1 , i = 1 , 2 , . . . , N (1c) x ij = { 0 , 1 } , i, j = 1 , 2 , . . . , N (1d) where constraint (1b) guarantees that each vertex v i ∈ V will be matched to one vertex r j ∈ R only . The constraint (1c) ensures that each verte x r j ∈ R will be associated with a single verte x v i ∈ V . Thus, both constraints enforce a one–to–one matching. The constraint (1c) ensures that x ij is either 1—if verte x v i ∈ V is matched to vertex r j ∈ R —or 0 if they are unmatched. An optimal solution can be ef fectiv ely found by means of Kuhn-Munkres algorithm [6] with O (max( |V | , |R| ) 3 ) = O ( N 3 ) complexity . 6 B. Matrix Repr esentation An alternative representation of (1) is giv en by (2) max c T x c ∈ R M , x ∈ B M , (2a) sub ject to Ax = 1 A ∈ B 2 N × M (2b) where M = N 2 , R denotes the real numbers and B represents the { 0 , 1 } realm. The totally unimodular matrix A encapsulates 2 N constraints— N constraints due to v ertices in V and N additional constraints that arise due to vertices in R . Finally , x = [ x 1 , 1 , . . . , x N ,N ] T , c = [ c 1 , 1 , . . . , c N ,N ] T are the solution vector and weight vector , respectiv ely . I V . P R O P O S E D C O N S T R A I N E D W E I G H T E D G R A P H M A T C H I N G S O L U T I O N Let G = ( V , R , E ) be a bipartite graph such that the cardinality of the sets V and R are related by |R| = K |V | = K N , as depicted in Fig. 3. In this scheme, the K N vertices in R are grouped into N disjoint groups {R α } N α =1 called macro-vertices, such that R = ∪ N α =1 R α , R α ∩ R α 0 = ∅ , ∀ α 6 = α 0 . Each macro-verte x R α is an aggregation of K vertices, i.e., |R α | = K . The target is to find a vertex–to–v ertex matching with maximum sum of weights such that no two vertices in V are matched to an y two vertices that belong to the same macro-vertex R α . This condition must be satisfied as it portrays the time orthogonality requirement that pre vents allocation conflicts. Notice that this type of constraints for conflict av oidance cannot be inherently managed by the approach described in Section III. Thus, this motiv ated us for de veloping an approach capable of v 1 v 2 v N r 1 r 2 r N V V ehicles R Resour ces . . . . . . a. Bipartite graph v i r j c ij = B log 2 (1 + SINR ij ) x ij b . Graph edge Fig. 2: Unconstrained W eighted Bipartite Graph 7 v 1 v 2 . . . v N r 1 r 2 . . . r K r K +1 r K +2 . . . r 2 K . . . r K ( N − 1)+1 r K ( N − 1)+2 . . . r K N macro- macro- macro- verte x R 1 verte x R 2 verte x R N V V ehicles R Resour ces Fig. 3: Constrained W eighted Bipartite Graph handling such constraints. W e will show via two dif ferent approaches in Section IV .A and Section IV .B, that the optimal solution is tantamount to finding the maximum vertex–to–macro-v ertex matching. The problem with additional macro-vertex constraints is formulated in (3) max N X i =1 K N X j =1 c ij x ij (3a) sub ject to K N X j =1 x ij = 1 , i = 1 , 2 , . . . , N (3b) N X i =1 X j ∈R α x ij = 1 , α = 1 , 2 , . . . , N (3c) x ij = { 0 , 1 } , i, j = 1 , 2 , . . . , N (3d) where the constraint (3b) enforces ev ery verte x v i ∈ V to be matched to a single vertex r j ∈ R . The constraint (3c) stipulates that in any macro-vertex R α , only one of its constituting vertices r j ∈ R α can be matched to a single v ertex v i ∈ V . In Fig. 3, K represents the number of resources per subframe, each with duration 1 ms [3]. Thus, a macro-v ertex R α represents the aggre gation of all the resources in subframe α . N denotes 8 the number of av ailable subframes in which the resource allocation task can be accomplished. For example, in Fig. 1, the number of resources per subframe is K = 7 whereas the amount of subframes is N = 6 , which yields a total of 42 resources. Since we consider that the system does not operate at overload, the number of subframes in the system should be at least equal to the cardinality of the maximum-cardinality cluster . Otherwise, there will exist vehicles that will not be served. When the number of v ehicles in a cluster is smaller than the number of subframes, dummy vehicles can be added such that |R| = K |V | = K N . A. Solution Derivation using Summation Repr esentation W e will show that the matching problem with macro-vertex constraints can be recast as an unconstrained graph with smaller cardinality and thus can be solved at the same computational complexity expense as the unconstrained weighted graph matching problem. W e observe that for any two edges x ij and x ik that share the same verte x v i , the fol- lo wing holds true: x ij x ik = 0 , if j 6 = k and r j , r k ∈ R α , ∀ α . The validity of this ex- pression can be readily verified because ev ery vertex v i ∈ V can be matched to one verte x r j ∈ R only . Thus, harnessing the previous relation, the follo wing expression also holds true: P j ∈R α P k ∈R α j 6 = k x ij x ik = 0 for any v i ∈ V , r j , r k ∈ R α , ∀ α . Furthermore, a generalized result is giv en by P N i =1 P N α =1 P j ∈R α P k ∈R α j 6 = k c ij x ij x ik = 0 . Notice that adding c ij to the zero-product x ij x ik does not affect the result. On the other hand, the cost function in (3a) can be expressed as P N i =1 P K N j =1 c ij x ij = P N i =1 P N α =1 P j ∈R α c ij x ij . Moreov er , since x ij = { 0 , 1 } ∀ i, j , the cost function can be further simplified employing the quadratic terms as P N i =1 P N α =1 P j ∈R α c ij x ij = P N i =1 P N α =1 P j ∈R α c ij x 2 ij . In addition, notice that constraint (3a) can be equi valently expressed as P K N j =1 x ij = P N α =1 P j ∈R α x ij = 1 . Thus, collecting the previous outcomes, the problem in (3) can be recast as (4) max N X i =1 N X α =1 X j ∈R α c ij x 2 ij + N X i =1 N X α =1 X j ∈R α X k ∈R α j 6 = k c ij x ij x ik (4a) sub ject to N X α =1 X j ∈R α x ij = 1 , i = 1 , 2 , . . . , N (4b) N X i =1 X j ∈R α x ij = 1 , α = 1 , 2 , . . . , N (4c) x ij = { 0 , 1 } , i, j = 1 , 2 , . . . , N (4d) 9 It was feasible to augment the cost function by adding zero-v alued terms since the solution optimality would not be affected. Thus, the new cost function is N X i =1 N X α =1 X j ∈R α c ij x 2 ij + N X i =1 N X α =1 X j ∈R α X k ∈R α j 6 = k c ij x ij x ik = N X i =1 N X α =1 X j ∈R α c ij x ij ! | {z } d iα X k ∈R α x ik ! | {z } y iα (5) Employing the definition of y iα , the constraint (4b) can be expressed as P N α =1 P j ∈R α x ij = P N α =1 y iα = 1 whereas the constraint (4c) is reduced to P N i =1 P j ∈R α x ij = P N i =1 y iα = 1 . Finally , stemming from the fact that y iα is the outcome of a sum on binary variables x ij , it yields that y iα is also binary . Upon collecting the pre vious results, the original problem in (3) can be expressed as (6) max N X i =1 N X α =1 d iα y iα (6a) sub ject to N X i =1 y iα = 1 , α = 1 , 2 , . . . , N (6b) N X α =1 y iα = 1 , i = 1 , 2 , . . . , N (6c) y iα = { 0 , 1 } , i, α = 1 , 2 , . . . , N (6d) Note that (6) mak es evident that a matching will be between vertices v i ∈ V and macro- vertices R α , which is equi valent to solving the unconstrained matching problem in (1). Howe ver , d iα = P j ∈R α c ij x ij are unkno wn as they depend on x ij . IT o remove the dependency of d iα on x ij , and be able to solve (6), in the follo wing we e xplain our reasoning. W e will show that we can obtain a solution y iα for (6) without first solving for x ij . Analysis: If there exists an optimal solution { x ? ij } i = N ,j = N i =1 ,j =1 to (3), then the following holds true • There must also exist a solution { y ? iα } i = N ,α = N i =1 ,α =1 that satisfies ( ?? ) optimally . This is because, x ij can be linearly mapped to y iα = P j ∈R α x ij . • Thus, giv en an optimal solution { y ? iα } i = N ,α = N i =1 ,α =1 , for some verte x v i 0 and macro-vertex R α 0 , the following is prov able. 10 1) If some y ? i 0 α 0 = 0 , this implies that the edge y ? i 0 α 0 is unmatched with vertex v i 0 ∈ V with macro-verte x R α 0 . This is equi valent to asserting that vertex v i 0 ∈ V is not matched to any of the vertices r j ∈ R α 0 . 2) If some y ? i 0 α 0 = 1 , there must exist an edge x i 0 j 0 = 1 that matches verte x v i 0 ∈ V with verte x r j 0 ∈ R α 0 . As a consequence, such said edge must be optimal, i.e., x ? i 0 j 0 = x i 0 j 0 = 1 , because y ? i 0 α 0 = x ? i 0 j 0 + P j ∈R α 0 j 6 = j 0 x ? i 0 j = 1 . • If some x ? i 0 j 0 = 1 , then its associated weight c i 0 j 0 is also in volv ed in the optimal solution. In other words, d i 0 α 0 = c i 0 j 0 x ? i 0 j 0 + P j ∈R α 0 j 6 = j 0 c i 0 j x ? i 0 j = c i 0 j 0 . T o wit, d i 0 α 0 will be either c i 0 j 0 , ∃ r j 0 ∈ R α 0 when x ? i 0 j 0 = 1 or 0 when x ? i 0 j 0 = 0 . Howe ver , note that if a maximum matching exists, it will then be attained regardless of the other values c ij as long as e very c i 0 j 0 ≥ c ij , ∀ i 6 = i 0 , j 6 = j 0 . Thus, without loss of optimality , d i 0 α 0 = max { c i 0 j | j ∈ R α 0 } . W e hav e shown that it is possible to remove the dependency of d ij on x ij and thus (6) can be solved as an unconstrained weighted gr aph matching problem. B. Solution Derivation using Matrix Repr esentation In this section, we de velop a generalized framew ork by which it is possible to show that (2) is a particular case of the verte x aggregation case, i.e., the unconstrained weighted graph matching problem when K = 1 . Thus, the problem is formulated as max c T x (7a) sub ject to I N × N ⊗ 1 1 × N 1 1 × N ⊗ I N × N ⊗ 1 1 × K x = 1 (7b) where ⊗ represents the tensor product operator , c ∈ R M , x ∈ B M with M = K N 2 . Because the solution x exists on the binary realm, the cost function (7a) can be equiv alently expressed as c T x = x T diag ( c ) x without affecting optimality . On the other hand, in a similar manner as we proceeded in (4) adding zero-valued terms, we employ an equiv alent representation to accomplish the same result. Thus, the sum of weighted pair-wise products c ij x ij x ik with r j , r k ∈ R α , can be expressed as x T I M × M ⊗ [ 1 K × K − I K × K ] diag ( c ) x = 0 . Now , we are able 11 to augment the cost function in (7a) and recast it as follo ws c T x = x T diag ( c ) x = x T diag ( c ) x + x T ( I M × M ⊗ [ 1 − I ] K × K ) diag ( c ) x = x T ( I M × M ⊗ I K × K + I M × M ⊗ [ 1 − I ] K × K ) diag ( c ) x = x T ( I M × M ⊗ 1 K × K ) diag ( c ) x (8) Property 1 (Product of two tensor products) Let X ∈ R m × n , Y ∈ R r × s , W ∈ R n × p , and Z ∈ R s × t , then XY ⊗ WZ = ( X ⊗ W )( Y ⊗ Z ) ∈ R mr × pt Employing Property 1, (8) can be further simplified. Thus, the resultant cost function is sho wn in (9) x T ( I M × M ⊗ 1 K × K ) diag ( c ) x = x T ( I M × M I M × M ⊗ 1 K × 1 1 1 × K ) diag ( c ) x = x T ( I M × M ⊗ 1 K × 1 ) | {z } y T ( I M × M ⊗ 1 1 × K ) diag ( c ) x | {z } d (9) From (9), we obtain that d = ( I M × M ⊗ 1 1 × K ) diag ( c ) x and y = ( I M × M ⊗ 1 1 × K ) x . Hence, we find that x = ( I M × M ⊗ 1 1 × K ) † y . Property 2 (Pseudo-in verse of a tensor product) Let X ∈ R m × n and Y ∈ R r × s , then ( X ⊗ Y ) † = X † ⊗ Y † ∈ R ns × mr Employing Property 2, we obtain that x = I † M × M ⊗ 1 † 1 × K y . In the following, we use the 12 pre vious relation in order to simplify the constraint (7b), I N × N ⊗ 1 1 × N 1 1 × N ⊗ I N × N ⊗ 1 1 × K I M × M ⊗ 1 † 1 × K y = 1 = I N × N ⊗ 1 1 × N 1 1 × N ⊗ I N × N I M × M ⊗ 1 1 × K 1 † 1 × K | {z } 1 y = 1 = I N × N ⊗ 1 1 × N 1 1 × N ⊗ I N × N y = 1 (10) Thus, the problem in (7) can be recast as (11) max d T y sub ject to I N × N ⊗ 1 1 × N 1 1 × N ⊗ I N × N | {z } A y = 1 . (11) Since y is obtained from the product of binary v ariables x ij and a totally unimodular matrix ( I M × M ⊗ 1 1 × K ) , then y ∈ B M . W e can notice that (11) is identical to (2) but in terms of dif ferent v ariables. Fig.4 shows the transformation process from (7) to (11). Ne vertheless, we can notice that d depends on x which is not desirable. In order to eliminate this dependency , we state without a proof—due to space limitations—that d = lim β →∞ 1 β ◦ log n ( I M × M ⊗ 1 1 × K )e ◦ β c o (12) where ◦ log {·} and e ◦{·} are the element-wise natural logarithm and Hadamard exponential [8], respecti vely . V . S I M U L A T I O N S W e consider a 10 MHz channel for conformity with ETSI ITS channelization [2]. The channel is divided into se veral resource chunks, each with an extent of 1 ms in time and 1.26 MHz in frequency . T o wit, 1.26 MHz corresponds to 7 resource blocks (RBs), where one RB consists of I M × M ⊗ 1 1 × K I M × M ⊗ 1 1 × K × diag ( · ) x c y d Fig. 4: T ransformation Process 13 Exhaustiv e Search Graph-based Algorithm Greedy Algorithm Random Algorithm 0 5 10 7 . 18 7 . 18 7 . 48 4 . 82 6 . 88 5 . 99 6 . 88 7 . 18 8 . 07 8 . 07 8 . 07 5 . 11 6 . 88 6 . 88 6 . 88 4 . 53 8 . 37 8 . 37 8 . 37 3 . 67 6 . 29 6 . 29 6 . 29 3 . 11 6 . 59 6 . 59 7 . 18 4 . 82 6 . 59 6 . 59 6 . 59 4 . 82 7 . 48 7 . 48 5 . 7 3 . 39 6 . 88 6 . 88 3 . 95 5 . 11 Rate [Mbits / s / resource] V ehicle v 1 V ehicle v 2 V ehicle v 3 V ehicle v 4 V ehicle v 5 V ehicle v 6 V ehicle v 7 V ehicle v 8 V ehicle v 9 V ehicle v 10 Fig. 5: One-shot simulation for dif ferent approaches 12 subcarriers spaced by 15 kHz [3]. The structure of each resource chunk is sho wn in T able I. Thus, in each subframe, there is a total of 7 resource chunks spanning 49 RBs. T o the best of our understanding, a resource chunk with such proportions is sufficient to con ve y data (5RBs) and control information (2RBs). W ith appropriate modulation and coding schemes, CAM messages with a payload of 200 data bytes can be adequately supported in a resource chunk. The control information is necessary for compatibility with other vehicles that may be out of coverage ( Mode 4 ). Thus, these vehicles can be aware of the resources in use and self-allocate to themselv es an idle resource. T ABLE I: Sidelink Resource Structure Description V alue Number of RBs 7 Number of subcarriers per RB 12 Number of data subcarriers 60 Number of control subcarriers 24 In our model, we consider that clusters are totally independent from each other . This means that a subset of resources used in a certain cluster can be repurposed by vehicles in other clusters. The system parameters that we ha ve employed in our simulations are detailed in T able II. Since we consider a message rate of 10 Hz and N = 100 v ehicles, the resource allocation task is carried out ev ery 0.1 s. Signaling between vehicles and eNode via uplink/downlink resources should also be transmitted at least e very 0.1 s. 14 T ABLE II: System Parameters Description V alue Number of vehicles per cluster 10 - 100 Number of clusters 1 - 7 Message rate (Hz) 10 Number of allottable subframes 100 Number of resources per subframe 3, 7 In Fig. 5 we show a one-shot simulation of the achie v able rates comparing 4 dif ferent algorithms. For this particular simulation, we considered that the number of vehicles is N = 10 and the number of resources per subframe is K = 3 . In the proposed graph-based algorithm we have not enforced any mechanism to incentivize fairness. Howe ver , as can be observed, the approach can provide a fair resource assignment to all the vehicles. Furthermore, it attains the same results as e xhaustive sear ch , which verifies its optimality . The greedy algorithm can provide with good channel quality to some vehicles only b ut there are inevitably others with lo w quality conditions. For the results in Fig. 6, we considered 4 communications clusters with N = 100 vehicles in each and K = 7 . The results hav e been obtained in base of the av erage o ver 1000 simu- lations. W e proved mathematically in Section IV that the proposed approach is optimal. Now , through simulations, we also show that our scheme can attain optimality as it achiev es the same performance as exhaustive sear ch as can be observed in Fig. 6. Notice that gr eedy algorithm performs as equally good as the proposed approach if we examine the highest-rate vehicle only . This is logical as the premise of the gr eedy algorithm is assigning the best resources on first- come first-served basis. Considering the system av erage rate, our proposed approach has a small adv antage. Howe ver , when considering the worst-rate vehicle, our proposal excels as it is capable of providing a higher lev el of fairness. In all cases, the random algorithm is outperformed by the other approaches. Fig. 7 sho ws the achie vable rate for the worst-rate vehicle. The proposed graph-based al- gorithm attains the same performance as exhaustive sear ch . W e observe that when the vehicle density per cluster is low , the gr eedy algorithm attains near optimal solutions as there are far more resources than v ehicles to serv e. Ho wev er , as the density increases, especially near the 15 Highest- Rate V ehicle W orst-Rate V ehicle System A verage Rate System Rate Standard Deviation 0 2 4 6 8 10 8 . 97 7 . 12 8 . 22 1 . 16 8 . 97 7 . 12 8 . 22 1 . 16 8 . 91 5 . 85 8 . 02 1 . 25 7 . 63 1 . 76 4 . 52 1 . 67 Rate [Mbits / s / resource] Exhaustive Search Graph-based Algorithm Greedy Algoritm Random Algorithm Fig. 6: V ehicles Data Rate 20 40 60 80 100 2 3 4 5 6 7 8 Number of V ehicles Rate [Mbits / s / resource] Graph-based Algorithm Exhaustive Search Greedy Algoritm Random Algorithm Fig. 7: W orst-rate vehicle ov erload state, its performance drops. The random algorithm performs worse than the other approaches. Fig. 8 shows the cumulativ e distrib ution function (CDF) of the achiev able rates. W e observe that the proposed approach outperforms the other two approaches. For the sake of comparison, we hav e included the results of the unconstrained system, which does not takes into account conflict a voidance constraints. This is of course not desirable but it serves as a comparison bound. The comple xity of e xhaustive sear ch is O ( |R| ! / ( |R| − |V | )!) whereas the complexity of gr aph- based algorithm is O (max {|V | , |R| /K } 3 ) . The complexity of the gr eedy algorithm and random algorithm are O ( |V ||R| ) and O ( |V | ) , respectiv ely . 16 2 4 6 8 10 0 . 1 0 . 4 0 . 7 1 Rate x [bits / s / Hz] Pr Rate < Rate x Graph-based Algorithm Exhaustive Search Greedy Algoritm Random Algorithm Exhaustive Search w/o constraints Fig. 8: Cumulativ e Distrib ution Function V I . C O N C L U S I O N W e hav e presented a novel resource allocation algorithm for V2V communications considering conflict constraints. W e were able to transform the original problem into a simplified form by means of two approaches. In our future work, we will consider ( i ) power control and ( ii ) the assumption that a subset of vehicles may belong to more than one cluster simultaneously . R E F E R E N C E S [1] ”Crash Data Analyses for V ehicle-to-Infrastructure Communications for Safety Applications, ” FHW A-HR T -11-040, Nov . 2012. [2] ”ETSI TR 102 861; Intelligent T ransport Systems (ITS); STDMA recommended parameters and settings for cooperativ e ITS; Access Layer Part, ” January 2012. [3] ”3GPP TS 36.213; T echnical Specification Group Radio Access Network; Evolved Universal T errestrial Radio Access (E-UTRA); Physical layer procedures; (Release 14) v14.2.0, ” March 2017. [4] G. Y u, L. Xu, D. Feng, R. Y in, G. Y . Li and Y . Jiang, ”Joint Mode Selection and Resource Allocation for Device-to-De vice Communications, ” IEEE Transactions on Communications, V ol. 62, No. 11, pp. 3814-3824, November 2014. [5] W . Sun, E. G. Str ¨ om, F . Br ¨ annstr ¨ om, Y . Sui and K. C. Sou, ”D2D-based V2V communications with latency and reliability constraints, ” IEEE Globecom Wksps, pp. 1414-1419, Dec. 2014. [6] J. Munkres, ”Algorithms for the Assignment and Transportation Problems, ” Journal of the Society for Industrial and Applied Mathematics, V ol. 5, No. 1, pp. 32-38, 1957. [7] ”3GPP TR 36.885; T echnical Specification Group Radio Access Network; Study on L TE-based V2X Services; (Release 14) v14.0.0, ” June 2016. [8] F . Hiai, ”Monotonicity for Entrywise Functions of Matrices, ” Journal of Linear Algebra and its Applications, V ol. 431, No. 8, pp. 1125-1146, September 2009. [9] J. E Hopcroft and R. M. Karp, ”An n 5 / 2 Algorithm for Maximum Matchings in Bipartite Graphs”, SIAM Journal on Computing, V ol. 2, No. 4, pp. 225-231, 1973. [10] R. Duan and S. Pettie, ”Linear-T ime Approximation for Maximum W eight Matching, ” Journal of the ACM, V ol. 61, No. 1, January 2014.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment