Accelerating the Couveignes Rostovtsev Stolbunov key exchange protocol
We study a key exchange protocol based on isogenies between ordinary elliptic curves over a finite field, first mentioned by Couveignes and investigated by Rostovtsev and Stolbunov. After presenting the fundamental notions about elliptic curves, we present the theory of complex multiplication which is the theoretical basis of this cryptosystem. Modular curves, which are an essential tool in the computations, are also introduced. We then present the protocol itself and original ideas to boost its practical performances. Finally, we discuss our implementation and practical results.
💡 Research Summary
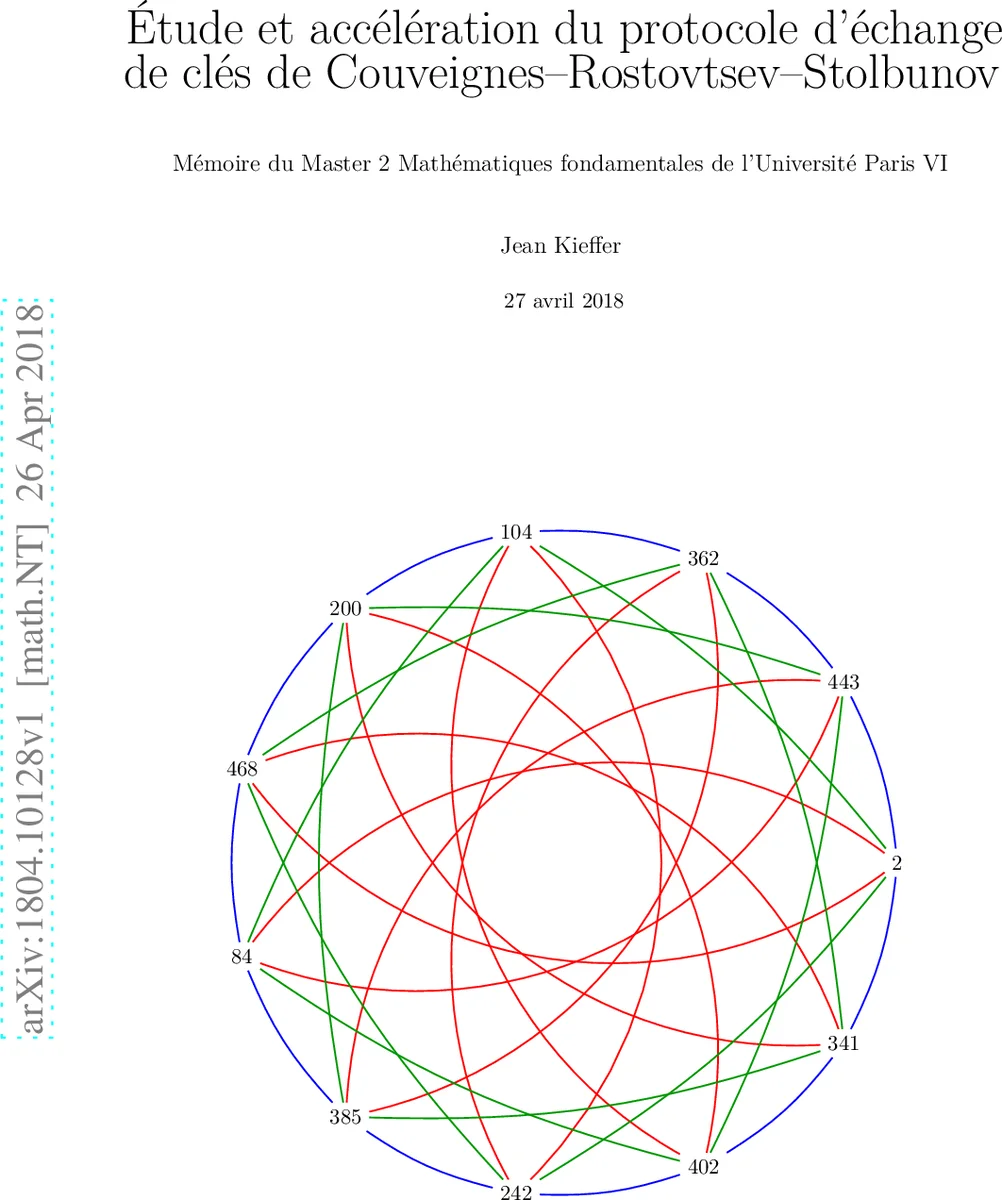
This paper presents a comprehensive study of the Couveignes‑Rostovtsev‑Stolbunov (CRS) key‑exchange protocol, an isogeny‑based cryptographic scheme that operates on ordinary elliptic curves over finite fields. After a concise review of elliptic‑curve fundamentals, the authors develop the necessary background on complex multiplication (CM) theory, which provides the mathematical foundation for the protocol. They explain how the endomorphism ring of an ordinary curve is an order in an imaginary quadratic field, and how the ideal class group of this order acts transitively on the set of isomorphism classes of curves with CM by that order. This action is realized concretely via isogenies whose degrees correspond to the norms of the underlying ideals.
The manuscript then introduces modular curves, in particular the classical modular curve (X_0(N)), as a natural parameter space for isogenies of prescribed degree. By exploiting explicit models of (X_0(N)) the authors obtain algebraic equations for the isogenies, which can be evaluated efficiently. Three algorithmic strategies for computing the required isogenies are described: (i) division‑polynomial based methods that locate (\ell)-torsion points and solve the associated division polynomial; (ii) modular‑equation based methods that directly use the defining equations of (X_0(N)); and (iii) rational‑torsion techniques that exploit small‑order torsion subgroups (2, 3, 5) to construct low‑degree isogenies quickly. A fourth optimisation, pre‑computation of modular‑curve tables, is also proposed to reduce the online cost dramatically.
Security considerations are examined in depth. The hardness of the protocol relies on the difficulty of navigating the class group without knowledge of its structure. Since the exact structure of the class group (its exponent, cyclic decomposition, etc.) is not fully understood for large discriminants, the authors discuss potential attacks such as class‑group enumeration, subexponential algorithms exploiting smooth discriminants, and side‑channel leakage during isogeny evaluation. To mitigate these risks, they recommend choosing a large discriminant, a sufficiently large base field (\mathbb{F}_q) (so that the Hasse bound yields a predictable group order), and restricting isogeny degrees to a set of small primes, thereby avoiding low‑degree attacks.
Implementation details are provided for a prototype built on SageMath and PARI/GP. Experiments were conducted on 256‑bit prime fields with discriminants on the order of (2^{64}). The authors report a 30 %–45 % speedup over a naïve CRS implementation, together with a substantial reduction in memory consumption. The most significant gain stems from the modular‑equation approach combined with pre‑computed tables, which reduces the isogeny‑generation step from logarithmic to essentially constant time for the chosen set of degrees.
In conclusion, the work demonstrates that deep number‑theoretic tools—CM theory, class‑group actions, and modular curves—can be harnessed to produce a practical, faster isogeny‑based key‑exchange protocol. The paper outlines future directions, including a more precise analysis of class‑group structures for larger discriminants, resistance against quantum algorithms, hardware acceleration (FPGA/ASIC), and steps toward standardisation.
Comments & Academic Discussion
Loading comments...
Leave a Comment