Analyzing Power Beacon Assisted Multi-Source Transmission Using Markov Chain
Wireless power transmission (WPT) is envisioned to be a promising technology for prolonging the lifetime of wireless devices in energy-constrained networks. This paper presents a general power beacon (PB) assisted multi-source transmission, where a p…
Authors: Xuanxuan Tang, Yansha Deng, Yueming Cai
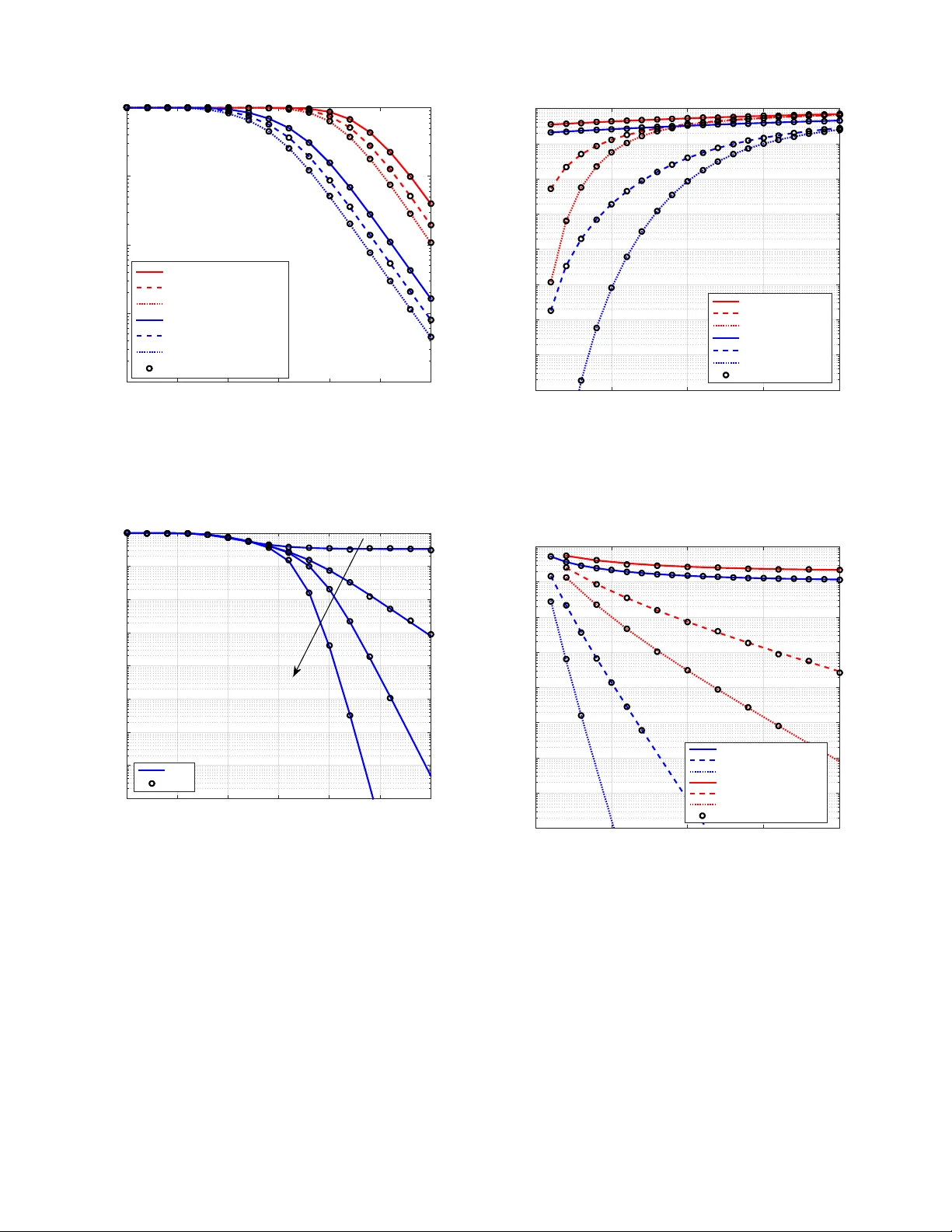
1 Analyzing Po wer Beacon Assisted Multi-Source T ransmission Using Mark ov Chain Xuanxuan T ang, Y ansha Deng, Member , IEEE , Y ueming Cai, Senior Member , IEEE , W endong Y ang, and Arumugam Nallanathan, F ellow , IEEE Abstract —Wir eless power transmission (WPT) is en visioned to be a promising technology f or prolonging the lifetime of wireless devices in energy-constrained networks. This paper presents a general power beacon (PB) assisted multi-source transmission, where a practical source selection scheme with information transmission (IT) mode or non-IT mode is developed to maximize the transmission reliability . In the IT mode, a zero- for cing (ZF) beamf ormed signal with no interference to the destination is transmitted at the multi-antenna PB to supply wireless energy for the sources, and bring non-negative effect to the destination. Among multiple sources, the energy-sufficient source with the best channel quality is selected for wireless information transmission (WIT), while the other sources remain for energy harvesting. In the non-IT mode, the equal power transmission is adopted at PB to focus on energy delivery . Using Marko v chain theory , the energy arri val and departur e of each finite-capacity storage at the source is characterized mathematically , and the comprehensiv e analytical expressions of the energy outage pr obability (EOP), the connection outage probability (COP), and the average transmission delay (A TD) are formulated and deriv ed. Our results re veal that the EOP , COP , and A TD can be significantly improv ed via increasing the number of sources deployed in the proposed network with finite transmit power of PB. W e also prove that the multi-source network will never experience energy outage with infinite transmit power of PB. Index T erms —Wir eless power transfer , Markov chain, energy storage, energy outage probability , av erage transmission delay . I . I N T RO D U C T I O N The lifetime of current wireless de vices is significantly limited by the energy capacity of their batteries, especially in some energy-constrained scenarios, such as wireless sensor networks (WSNs) [1], wireless body area networks (WBANs) [2], and low-po wer wide-area networks (LPW ANs) [3]. T o cope with this limitation, the energy harvesting (EH) has emerged as a promising technology to enable the sustainable energy for the devices without replacing their battery [4, 5]. Harvesting energy from the ambient en vironment sources like solar, wind, thermoelectric, electromechanical, etc, has This work was supported by the National Natural Science Foundation of China under Grant No. 61771487, and the China Scholarship Council. This work was done while X. T ang was a visiting student with the Department of Informatics, King’s College London. The corresponding author is Y ansha Deng. X. T ang, Y . Cai, and W . Y ang are with the College of Communications Engineering, Army Engineering University of PLA, Nanjing 210007, China (email: tang xx@126.com, caiym@vip.sina.com, ywd1110@163.com). Y . Deng is with the Department of Informatics, King’ s College London, London WC2R 2LS, U.K. (email: yansha.deng@kcl.ac.uk). A. Nallanathan is with the School of Electronic Engineering and Com- puter Science, Queen Mary University of London, London, UK (email: arumugam.nallanathan@qmul.ac.uk). been extensiv ely researched and applied in industry . Howe ver , this approach does not suitable for wireless communication devices, as it could not guarantee controllable and continuous energy supply due to the randomness and instability of the en vironment, which may degrade the user experience. Recently , the wireless power transmission (WPT) via radio- frequency (RF) radiation has drawn much attention among the wireless communities due to the great advancements of microw ave technologies over the past decades [6, 7]. Com- pared to collecting energy via natural sources, WPT is capable of deli vering a controllable amount of energy as well as information. In order to realize WPT in practice, the simulta- neous wireless information and power transmission (SWIPT) via the same modulated micro wave has been proposed and discussed extensi vely in existing literature. Specifically , two classic practical architectures have been presented, namely the “time-switching” architecture [8, 9] and the “power -splitting” architecture [10–12], where the receiving signal can be splitted either ov er time or power domain for independent WPT and wireless information transmission (WIT), respecti vely . Note that the efficiency of WPT relies on the received signal power while the reliability of WIT hinges on the receiv ed signal-to- noise ratio (SNR) [13], as the noise power is relati vely low , the distance for WPT is drastically shorter than that for WIT . Under this circumstance, the short range limitation of WPT and the same propagation link between WPT and WIT largely limit the information transmission range. T o face the challenge of aforementioned SWIPT design, some works have proposed the po wer beacon (PB) assisted WPT systems [13, 14]. In such systems, WPT and WIT processes are decoupled and the PB can be deployed much closer to the wireless-powered equipments, which boosts the efficienc y of WPT significantly . In 2017, the PB-based product “Cota Tile” has been designed by Ossia Inc. to charge wireless devices at home, which has receiv ed the “Innov ation A wards” at the 2017 Consumer Electronics Show (CES) [15]. In [16], a no vel PB assisted wiretap channel was studied to exploit secure communication between the energy constrained source and a legitimate user under eavesdropping. In [17], the authors studied a PB assisted wireless-powered system, where each user first harvested ener gy from RF signals broadcast by its associated AP and/or the PB in the downlink and then used the harvested energy for information transmission in the uplink. The faction of the time duration for downlink WPT was then optimized for each user . In [18], the users clustering around the PB for WPT , and deliv er information to the APs. In [19], the device-to-de vice (D2D) communication sharing the resources 2 of downlink cellular network was powered by the energy from PBs. The aforementioned works hav e assumed no energy storage across different time slots, and the wireless-po wered devices consume all the harvested energy in the current time slot to perform its o wn information transmission (IT). This type of operating mode, named as “harvest-use” [20], may not practical due to the following two-fold reasons: 1) the wireless devices are usually equipped with battery , which can storage energy ov er different time slots; and 2) the “harvest-use” approach results in the random fluctuation of the instant transmit power of a wireless-powered device, which may not only affect the performance of the device itself, but also create chaos to the whole system. Recent research hav e shifted to the so-called “harvest-store- use” operating mode [21], where the de vices are capable of storing the harvested energy in a rechargeable battery . In [22], an accumulate-and-jam protocol was presented to enhance the physical layer security in wireless transmission. The full- duplex (FD) relaying scheme w as studied in the WPT netw orks in [23, 24]. Unlike the single energy storage scenario in [22– 24], the multiple energy storages were considered in [25] and [26] with energy harvested from natural sources and wireless signals, respecti vely . In [26], a wireless-powered uplink and downlink network was studied, where the WPT occurs in the downlink performing by time division AP , and the IT occurs in both uplink and downlink, where the AP transmits the downlink information, and the users use the harvested energy storing for uplink information. Both the energy at the AP and the users are modelled using Marko v chain, and the time- frequency resource allocation and user scheduling problem was studied to minimize ov erall energy consumption. In this paper , we study the energy storage and data transmis- sion of PB assisted wireless-powered multi-source networks, where the network can operates in the non-IT mode or the IT mode. In the non-IT without any energy sufficient sources, the whole network experiences energy outage e vent with no IT in the network, thus the PB uses the equal po wer allocation among all antennas for directing its energy . In the IT mode, the source with the best channel quality among all the energy-suf ficient sources is selected for IT , to av oid the interference from the PB to the destination, a zero-forcing (ZF) beamformed signal is designed during the WPT , with no inteference to the data transmission between the source and the destination. • W e formulate a Markov-based analytical framework for the energy storage and energy usage of the proposed multi-source wireless-po wered networks to characterize its dynamic behaviors of the energy arriv al and departure. T o f acilitate the network performance analysis, we also deriv e the state transition probabilities of the proposed network, and the stationary probabilities of all the states. • W e propose a operating mode selection procedure for the proposed network to select the non-IT mode and the IT mode based on the ener gy states of all the sources. A flexible beamforming transmission scheme is proposed at the PB, which can adapt to the network operating mode. In the non-IT mode, the beamformer is designed with equal po wer among antennas. In the IT mode, the beamformer is designed to bring no interference to the data transmission between the selected source and the destination. • Based on our deriv ed stationary probabilities of all the states, we deriv e the energe outage probability and the connection outage probability of proposed network in the non-IT mode and the IT mode, respectively . T o quantify the delay performance, we also define and deriv e anlaytical expression for the average transmission delay of proposed networks. Our deriv ed analytical results are all validated via simulation, which show the correctness of our deriv ations, and demonstrate design insights. The remainder of the work is organized as follo ws: Section II describes the system model and presents the details of the operating mode selection as well as the source selection procedure. In III, the energy state transitions among all the states are carried out. In IV, the energy outage probability , the connection outage probability , and the average transmission delay of the network are respectiv ely inv estigated. Simulation results are giv en in Section V, and Section VI summarizes the contributions of this paper . Notation: Throughout this paper , the boldface uppercase letters are used to denote matrices or vectors. ( · ) T , ( · ) H , and ( · ) † are denoted as the transpose operation, the conjugate transpose operation, and the orthogonal operation, respecti vely . F γ ( · ) and f γ ( · ) represent the cumulative distribution function (CDF) and the probability density function (PDF) of random variable γ , respectiv ely . E [ · ] denotes the e xpectation operation. I I . S Y S T E M M O D E L W e consider a multi-source wireless-powered transmission network as sho wn in Fig. 1, which consists of single power beacon node B , K number of wireless-powered source nodes { S k } K k =1 , and a destination node D . It is assumed that B is equipped with N B antennas, and all the other nodes are equipped with a single antenna, where all nodes are working in half-duplex (HD) mode. Each source (IoT/ mobile de vice) is equipped with an energy storage with a finite energy capacity of ε T . W e assume that all the channels experience quasi-static Rayleigh fading and the channel coefficients keep constant during a block time T 0 but change independently from one packet time to another 1 . A standard path-loss model [8, 29] is adopted, namely the average channel power gain ¯ γ ab = E h | h ab | 2 i = d − α ab , where α is the path-loss factor , h ab and d ab denote the channel coefficient and the distance between a and b , respectiv ely . A. Energy Discr etization and State Modeling T o quantify the ener gy storage at the sources, we define a discrete-le vel model [22, 24], namely , each storage is dis- cretized into 1 + L lev els, where L is the discretizing lev el of the network, and the l -th energy lev el is defined as ε l = l · ε ∆ , l ∈ { 0 , 1 , · · · , L } , (1) 1 This assumption has been extensi vely adopted in the WPT researches [22, 27, 28]. 3 B a s e s t a t i o n S o u r c e w i t h e n e r g y s t o r a g e … 1 S k S K S B D … … P o w e r b e a c o n Fig. 1. System model where ε ∆ = ε T L is the single unit of energy . For instance, if the ne w ener gy arri val from the harvested ener gy at the k th source node is ε k , the amount of energy that can be saved in the energy storage after discretization can be expressed as [22, 24] ˜ ε k = ε l ∗ , with l ∗ = arg max l ∈{ 0 , 1 , ··· ,L } { ε l : ε l ≤ ε k } . (2) Recall that there are K storages and each storage has (1+ L ) lev els, thus we ha ve N states in total with N = (1 + L ) K . The ener gy lev el index es in all the storages form an energy state set Θ = { ~ s 1 , · · · , ~ s n , · · · , ~ s N } , where the n th state is giv en by ~ s n = [ l n 1 , · · · , l n k , · · · , l n K ] , (3) with n ∈ { 1 , · · · , N } and l n k ∈ { 0 , 1 , · · · , L } representing the energy le vel index of k th storage at state ~ s n . B. Network Operating Modes At any giv en time, the network is under one specific energy state, and different operating modes are adopted in dif ferent states. When the source does not hav e enough energy to support the IT operation, we define this source as energy outage. When all the sources experience the energy outage at the same time, we define the multi-source network as energy outage. As a result, we assume tw o operating modes: 1) the network operates in IT mode when there is as least one source can perform IT operation; and 2) the network operates in non- IT mode when all the sources are in energy outage. Next, we describe the operating mode selection procedure, and the transmission formulation for each operating mode. 1) Operating Mode Selection: W e select the operating mode based on the distributed selection method [30, 31]. At the start of each time slot, a pilot signal is broadcasted by D . Using this pilot signal, all the sources that are not in energy outage as well as the PB can indi vidually estimate the channel po wer gains between themselves and D . For each source that is not in energy outage, its timer with a parameter in versely proportional to its o wn channel power gain is switched on, namely , the timer of source S k has the parameter of C 0 . | h S k D | 2 , where h S k D denotes the channel coefficient between S k and D , and C 0 is a constant and is properly set to ensure that the shortest duration among all the timers always finishes within the given duration [30, 31]. Once the shortest timer e xpires, the corresponding source sends a short flag signal to declare its existence, and all the other sources who are waiting for their timer expiring will back off when the y hear this flag signal from another source and start to harvest energy . At the same time, D will get ready for receiving useful information upon hearing this flag signal. For the source that is in energy outage, it will neither estimate its channel nor set a timer . Hence, if the whole network undergoes energy outage, no flag signal would be produced during this flag signal duration. As a result, the operating mode of the network can be easily determined and known by all the nodes within the network. For the notation con venience, the set of indexes of source nodes that are in IT mode at state ~ s n are defined as ϑ T H n = k : l n k ≥ l th S , (4) where l th S denotes the transmit energy lev el threshold, which is expressed as l th S = arg min l ∈{ 1 , ··· ,L } ε l : ε l ≥ ε th S , (5) where ε th S denotes the transmit energy threshold of sources. 2) Non-IT Operating Mode: When the network remains at the Non-IT operating mode, we have ϑ T H n = Φ 0 , where Φ 0 is the empty set. As described above, no information could be transmitted and all of the sources will harvest energy from the wireless signal transmitted by B . Specifically , the harvested energy at the k -th source is expressed as ε n k = η T 0 P B h T B S k w 1 2 , (6) where h B S k = h h B 1 S k , · · · , h B b S k , · · · , h B N B S k i T repre- sents the channel coefficient v ector between B and S k , k ∈ { 1 , · · · , K } , b ∈ { 1 , · · · , N B } . w 1 ∈ C N B × 1 is the normalized weight vector applied at B with its b th element satisfying w 1 ,b = 1 / √ N B . The amount of harvested energy that can be saved in the k th energy storage after discretization, ˜ ε n k , can be obtained according to (2) by making an appropriate replacement, namely ε k → ε n k , ˜ ε k → ˜ ε n k . 3) IT Operating Mode: When the network remains at the IT operating mode, we have ϑ T H n 6 = Φ 0 . As such, a source that has the largest channel power gain is selected for IT operation among all the satisfied sources. Mathematically , the index of the selected source can be giv en by i ∗ = arg max k ∈ ϑ T H n n | h S k D | 2 o . (7) Enjoying the energy harv ested from B , the source to destination transmission may also suffer from interference brought by the wireless signals deli vered by B . Note that B has also estimated the channel between itself and D with the pilot signal. T o exploit the adv antages of multiple antennas, the ZF beamforming scheme can be used at b to fully av oid the interference from B to D . T o be spe- cific, a normalized weight vector w 2 ∈ C N B × 1 satisfying w 2 = h † B D is applied at B so as to keep h T B D w 2 = 0 , 4 where h B D = h h B 1 D , · · · , h B b D , · · · , h B N B D i T represents the channel coef ficient vector between B and D , and ( · ) † denotes the orthogonal operation. Hence, the receiv ed signal- to-noise ratio (SNR) at D is given by γ n,i ∗ D = P S N 0 | h S i ∗ D | 2 , (8) where N 0 is the power density of the additive white Gaussian noise (A WGN), and P S represents the transmit po wer of sources with P S = l S ε ∆ T 0 , (9) where l S is the actual transmit energy lev el satisfying l th S ≤ l S ≤ L . At the same time, all the other sources except S i ∗ harvest energy from wireless signals, and the harvested energy at the k th source on condition that S i ∗ is selected for IT could be expressed as ε n,i ∗ k = η T 0 P S | h S i ∗ S k | 2 + P B h T B S k w 2 2 , (10) where k ∈ { 1 , · · · , K } \ { i ∗ } , and the amount of harvested energy that can be sav ed in the k th energy storage after discretization, ˜ ε n,i ∗ k , can be deri ved according to (2) by making an appropriate replacement, namely ε k → ε n,i ∗ k , ˜ ε k → ˜ ε n,i ∗ k . I I I . E N E R G Y S TA T E T R A N S I T I O N S In this section, we present a thorough study on the tran- sitions of the energy states. Let us denote ~ s n and ~ s n 0 as the states at the current and the next time slots, respectiv ely , n, n 0 ∈ { 1 , · · · , N } . W e then denote the transition probability to transfer from ~ s n to ~ s n 0 within one step as p ~ s n → ~ s n 0 . For the notation con venience, the non-IT set of states Θ 1 and the IT set of states Θ 2 are defined as Θ 1 = ~ s n : ∀ n, s.t.ϑ T H n = Φ 0 , (11) and Θ 2 = ~ s n : ∀ n, s.t.ϑ T H n 6 = Φ 0 , (12) respectiv ely . Note that Θ 1 represents the set of states that all the sources hav e to conduct EH operation. In other words, we ha ve Θ 1 = { [0 , · · · , 0 , 0] , · · · , [( l S − 1) , · · · , ( l S − 1) , ( l S − 1)] } . Besides, Θ 2 is the set of states that at least one source can perform IT operation. It is obvious that Θ 1 is the complement set of Θ 2 , so the numbers of states in Θ 1 and Θ 2 are N 1 = ( l S ) K and N 2 = N − ( l S ) K , respectively . The energy lev el increment between two states is defined as ∆ ~ s n = ~ s n 0 − ~ s n = [∆ l n 1 , · · · , ∆ l n k , · · · , ∆ l n K ] , (13) where ∆ l n k = l n 0 k − l n k , and l n 0 k , l n k ∈ { 0 , 1 , · · · , L } . Note that when the network operates in the non-IT mode, the energy lev el in any of the sources will not decline. Hence, it is not possible to transfer from ~ s n to ~ s n 0 within one step if ~ s n 0 / ∈ Θ n,n 0 1 , where Θ n,n 0 1 is a subset of Θ which satisfies Θ n,n 0 1 = { ~ s n 0 : ∀ k , s.t. ∆ l n k ≥ 0 } . It is noted that the construction of Θ n,n 0 1 relies on a specific ~ s n . Similarly , when n k l n k l 1 n k lL n k l 1 nn kk n k ll 1 n k l n k l n k lL n k l n k l n k n k l n k l ( a ) ( b ) Fig. 2. State transition when (a) l n 0 k 6 = L and (b) l n 0 k = L . the network operates in the IT mode, the energy lev el in any of the sources except for the selected one S i ∗ will not decline, and the energy lev el of S i ∗ will decline l th S due to the IT operation. Hence, it is not possible to transfer from ~ s n to ~ s n 0 within one step if ~ s n 0 / ∈ Θ n,n 0 ,i ∗ 2 , where Θ n,n 0 ,i ∗ 2 is a subset of Θ which satisfies Θ n,n 0 ,i ∗ 2 = ~ s n 0 : ∆ l n i ∗ = − l th S ; ∀ k 6 = i ∗ , ∆ l n k ≥ 0 . A. State T ransition When Operating in Non-IT Mode If the network works in the non-IT mode, namely ~ s n ∈ Θ 1 . Then the probability of the k th source S k to transfer from l n k to l n 0 k within one step can be expressed as p n → n 0 k = Pr ~ s n 0 ( k ) = l n 0 k | ~ s n ( k ) = l n k . (14) As mentioned before, p n → n 0 k = 0 is always true when ∆ l n k < 0 in non-IT mode. For the case with ∆ l n k ≥ 0 , we will show that p n → n 0 k differs when l n 0 k = L and l n 0 k 6 = L , which imply the state after transition for S k is full and not full, respectively . On one hand, if l n 0 k 6 = L , as sho wn in Fig. 2 (a), l n k can transfer to l n 0 k within one step only when the harvested energy , ε n k , satisfying ε ∆ l n k ≤ ε n k < ε ∆ l n k +1 . On the other hand, if l n 0 k = L , as shown in Fig. 2 (b), it will transfer from l n k to l n 0 k within one step only when the harvested energy ε n k satisfying ε n k ≥ ε ∆ l n k . Hence, we formulate the transition probability of the k th source as p n → n 0 k = ( F ε n k ε ∆ l n k +1 − F ε n k ε ∆ l n k , l n 0 k 6 = L, 1 − F ε n k ε ∆ l n k , l n 0 k = L. (15) When ~ s n ∈ Θ 1 , as each source harvests ener gy indepen- dently , the transition probability of all the sources p 1 ~ s n → ~ s n 0 can be expressed as p 1 ~ s n → ~ s n 0 = K Y k =1 p n → n 0 k . (16) T o derive p 1 ~ s n → ~ s n 0 , we present the following Lemma. Lemma 1. The CDF of ener gy harvested at the k th sour ce with the n th state ε n k is derived as F ε n k ( x ) = 1 − exp − x η T 0 P B ¯ γ B S k . (17) 5 Pr oof: W e first present the CDF as F ε n k ( x ) =Pr( η T 0 P B h T B S k w 1 2 ≤ x ) =Pr( η T 0 P B X N B b =1 h B b S k w 1 ,b 2 ≤ x ) =Pr( η T 0 X 1 ≤ x ) = Pr X 1 ≤ x η T 0 (18) where X 1 = P B P N B b =1 h B b S k w 1 ,b 2 . W ith Rayleigh fad- ing h B b S k ∼ C N (0 , ¯ γ B S k ) and w 1 ,b = 1 / √ N B with b ∈ { 1 , · · · , N B } , we hav e P N B b =1 h B b S k w 1 ,b = 1 √ N B P N B b =1 h B b S k . It is noted that the sum of finite Gaussian random v ariables is still a Gaussian random v ariable [32], hence P N B b =1 h B b S k ∼ C N (0 , N B ¯ γ B S k ) , which results in 1 √ N B P N B b =1 h B b S k ∼ C N (0 , ¯ γ B S k ) . Therefore, X 1 is an exponentially distrib uted random variable with the mean of P B ¯ γ B S k with f X 1 ( y ) = 1 P B ¯ γ B S k exp − y P B ¯ γ B S k . (19) Substituting (19) into (18), we prov e (17). By substituting (15) and (17) into (16), the transition probability of all sources from ~ s n to ~ s n 0 in non-IT mode for ~ s n 0 ∈ Θ n,n 0 1 can be deriv ed as p 1 ~ s n → ~ s n 0 = e − ε ∆ l n k ηT 0 P B ¯ γ BS k Y k / ∈ ϑ L n 0 K k =1 1 − e − ε 1 ηT 0 P B ¯ γ BS k . (20) B. State T ransition When Operating in IT Mode If the network works in IT -mode, namely ~ s n ∈ Θ 2 . W e further assume the condition that i ∗ = i , namely the transfer from ~ s n to ~ s n 0 results from the IT selection of S i . Correspondingly , we ha ve Θ n,n 0 ,i ∗ 2 = Θ n,n 0 ,i 2 = ~ s n 0 : ∆ l n i = − l th S ; ∀ k 6 = i, ∆ l n k ≥ 0 on this condition. Then the transition probability of the k th source to transfer from ~ s n to ~ s n 0 within one step is deriv ed as p n → n 0 ,i k = ( F ε n,i k ε ∆ l n k +1 − F ε n k ε ∆ l n k , l n 0 k 6 = L, 1 − F ε n,i k ε ∆ l n k , l n 0 k = L. (21) As such, the transition probability of all sources from ~ s n to ~ s n 0 in the IT mode can be written as p 2 ~ s n → ~ s n 0 = p n i Y k 6 = i K k =1 p n → n 0 ,i k . (22) T o derive the source selection probability p n i , we present the following Lemma. Lemma 2. F or the IT mode ~ s n ∈ Θ 2 , the pr obability that the sour ce S i satisfying l n i ≥ l th S to be selected for information transmission p n i = Pr ( S i ∗ = S i ) is derived as p n i = X n 1 ∈ τ i 1 ,K ( − 1) P K k =1 n 1 ,k ¯ γ S i D P K k =1 n 1 ,k ¯ γ S k D + 1 , (23) wher e τ i 1 ,K is the set of K − length vectors with all its elements as binary numbers, n 1 is a qualified vector in τ i 1 ,K with its k th element satisfying n 1 ,k ∈ { 0 , 1 } for k ∈ ϑ T H n \ { i } , and n 2 ,k = 0 for k / ∈ ϑ T H n and k = i . Pr oof: When l n i ≥ l th S , we denote Z i = | h S i D | 2 , and Z 0 i = max k ∈ ϑ T H n \{ i } { Z k } K k =1 with i ∈ ϑ T H n , then p n i is giv en as p n i = Pr ( Z i > Z 0 i ) , which can be calculated as p n i = Z ∞ 0 F Z 0 i ( z ) f Z i ( z ) dz . (24) W e first deriv e F Z 0 i ( z ) = Y k ∈ ϑ T H n \{ i } K k =1 1 − e − z ¯ γ S k D . (25) Referring to [33], F Z 0 i ( z ) can be rewritten as F Z 0 i ( z ) = X n 1 ∈ τ i 1 ,K K Y k =1 ( − 1) n 1 ,k e − n 1 ,k ¯ γ S k D z = X n 1 ∈ τ i 1 ,K ( − 1) P K k =1 n 1 ,k e − z P K k =1 n 1 ,k ¯ γ S k D . (26) In addition, we know that f Z i ( z ) = 1 ¯ γ S i D e − z ¯ γ S i D . (27) Substituting (26) and (27) into (24), and after some simple manipulations, (23) can be readily deriv ed. T o derive the transition probability of the k th source from ~ s n to ~ s n 0 in the IT mode, we present the following lemma. Lemma 3. The CDF of the energy harvested at the k th sour ce with the n th state ε n,i ∗ k is derived as F ε n,i ∗ k ( x ) = 1 − e − x ηT 0 P B ¯ γ BS k − P S ¯ γ S i ∗ S k P B ¯ γ B S k − P S ¯ γ S i ∗ S k × e µ 1 x ηT 0 − 1 e − x ηT 0 P S ¯ γ S i ∗ S k , (28) wher e µ 1 = P B ¯ γ BS k − P S ¯ γ S i ∗ S k P S ¯ γ S i ∗ S k P B ¯ γ BS k . Pr oof: W e first present the CDF of ε n,i ∗ k as F ε n,i ∗ k ( x ) = Pr η T 0 P S | h S i ∗ S k | 2 + P B h T B S k w 2 2 ≤ x = Pr( X 2 + X 3 ≤ x η T 0 ) = Z x ηT 0 0 F X 2 x η T 0 − y f X 3 ( y ) dy , (29) where X 2 = P S | h S i ∗ S k | 2 and X 3 = P B P N B b =1 h B b S k w 2 ,b 2 . W ith w 2 = h † B D , the construction of w 2 is inde- pendent with h B S k , so we have P N B b =1 h B b S k w 2 ,b ∼ C N 0 , ¯ γ B S k P N B b =1 | w 2 ,b | 2 with P N B b =1 | w 2 ,b | 2 = 1 [32]. As a result, the PDF of X 3 is derived as f X 3 ( y ) = 1 P B ¯ γ B S k exp − y P B ¯ γ B S k . (30) Besides, we know that X 2 ∼ exp ( P S ¯ γ S i ∗ S k ) , and its CDF is written as F X 2 ( x ) = 1 − exp − x P S ¯ γ S i ∗ S k . (31) 6 Substituting (30) and (31) into (29), we prove (28) in Lemma 3. By utilizing the results in Lemmas 2 and 3, the transition probability from ~ s n to ~ s n 0 in IT mode when ~ s n 0 ∈ Θ n,n 0 ,i 2 can be derived as p 2 ~ s n → ~ s n 0 = X n 1 ∈ τ i 1 ,K ( − 1) P K k =1 n 1 ,k ¯ γ S i D P K k =1 n 1 ,k ¯ γ S k D + 1 × Y k 6 = i, k ∈ ϑ L n 0 K k =1 Λ 1 ( i, k ) × Y k 6 = i, k / ∈ ϑ L n 0 K k =1 Λ 2 ( i, k ) , (32) with Λ 1 ( i, k ) = e − ε ∆ l n k ηT 0 P B ¯ γ BS k + P S ¯ γ S i S k P B ¯ γ B S k − P S ¯ γ S i S k × e − ε ∆ l n k ηT 0 P S ¯ γ S i S k e µ 1 ε ∆ l n k ηT 0 − 1 , (33) Λ 2 ( i, k ) = Λ 1 ( i, k ) − P S ¯ γ S i S k e − ε ∆ l n k +1 ηT 0 P S ¯ γ S i S k P B ¯ γ B S k − P S ¯ γ S i S k × e µ 1 ε ∆ l n k +1 ηT 0 − 1 − e − ε ∆ l n k +1 ηT 0 P B ¯ γ BS k , (34) where ϑ L n 0 = n k : l n 0 k = L o represents the set of sources whose energy lev el is L at state ~ s n 0 . T o conclude, the transition probability from ~ s n to ~ s n 0 is summarized as p ~ s n → ~ s n 0 = p 1 ~ s n → ~ s n 0 , ~ s n ∈ Θ 1 , ~ s n 0 ∈ Θ n,n 0 1 , p 2 ~ s n → ~ s n 0 , ~ s n ∈ Θ 2 , ~ s n 0 ∈ Θ n,n 0 ,i 2 , 0 , other s. (35) Let us denote A ∈ R N × N as the state transition matrix of the proposed network, where the ( n, n 0 ) -th element a n,n 0 represents the probability to transfer from ~ s n to ~ s n 0 , and is giv en by a n,n 0 = p ~ s n → ~ s n 0 . (36) W e then formulate the stationary distribution π ∈ R N × 1 for the ener gy states, where its n th element, π n , stands for the stationary probability of state ~ s n for the network. It is easily to know that A is irreducible and row stochastic. As a consequence, a unique stationary distribution must e xist that satisfies [22, 34] π = A T π . (37) According to [34, Eq. (12)], the solve of (37) could be deriv ed as π = A T − E + Q − 1 b , (38) where b = (1 , 1 , · · · 1) T , E is the identity matrix, and Q is an all-ones matrix. ! , . ., , . ., 0 nS n i s t s i l k i s t s k , . ., 0 n k s t s k 1 nN 1 nN 1 n n n nn s s s 1 n s 1 nN 1 0 nn n Y E S Y E S Y E S N O Y E S Y E S N O N O 1 , nn n n s s ap 2 , nn n n s s ap N O Y E S N O N O E N D ,, S K L l 1 K NL NN A0 0 n 12 ,, 1 n n n nn s s s Fig. 3. Flow diagram for the generation of the state transition matrix A. For a better comprehension, Fig. 3 depicts the block diagram for the construction of the state transition matrix A based on the system parameters K , L and l S . Fig. 4 illustrates the transitions of the states for a simple e xample with K = 2 and L = 2 . The corresponding state transition matrix A could be derived as (39). By applying the described approach, the stationary state probabilities of all the states, as well as the EOP , COP and A TD for S 1 and S 2 are obtained as sho wn in T able I. The related parameters are set as P B = 30 dBm, ε T = 20 mJ, ε th S = 10 mJ, l S = l th S , η = 0 . 8 , R t = 3 bits/s/Hz, x B = − 3 m, x D = 200 m, r S = 1 m, N B = 5 , N 0 = − 80 dBm, and α = 3 . The coordinates of B and D as well as S 1 and S 2 are B = ( − 3 , 0) , D = (200 , 0) , S 1 = ( − 1 , 0) and S 2 = (0 , 1) , respectiv ely . The unit of distance is the meter . I V . O U TAG E A N D D E L AY In this section, we characterize the performance in terms of outage and delay . Specifically , we focus on the deriv ations for the EOP in the non-IT mode, the COP , and the a verage transmission delay (A TD) in the IT model. T o re veal key insights of the proposed network, we derive exact expressions for the EOP , COP , and A TD of proposed networks. 7 2 s 1 s 5 s 3 s 6 s 4 s 8 s 7 s 9 s 2 s 1 s 5 s 3 s 6 s 4 s 8 s 7 s 9 s 00 S t a t e 12 nn ll 01 02 10 11 12 20 21 22 U n i d i r e c t i o n B i d i r e c t i o n Fig. 4. State diagram of the Markov chain representing the states of the storages and the transitions between them for a case with K = 2 and L = 2 . T ABLE I I L LU S T R A T I ON O F E X A MP L E W H E N K = 2 , L = 2 . State s n [ l n 1 , l n 2 ] π n [ p n 1 , P n 2 ] State COP s 1 [0,0] 0.0220 [0,0] 0 s 2 [0,1] 0.0434 [0,1] 0.0545 s 3 [0,2] 0.1587 [0,1] 0.0545 s 4 [1,0] 0.0640 [1,0] 0.0553 s 5 [1,1] 0.1022 [0.4963,0.5037] 0.0030 s 6 [1,2] 0.1811 [0.4963,0.5037] 0.0030 s 7 [2,0] 0.1998 [1,0] 0.0553 s 8 [2,1] 0.2210 [0.4963,0.5037] 0.0030 s 9 [2,2] 0.0078 [0.4963,0.5037] 0.0030 Deriv ed results EOP [ p T , 1 , p T , 2 ] Overall COP 0.0220 [0.5179,0.4601] 0.0271 [ ¯ T 1 , ¯ T 2 ] [1.9309,2.1734] A. Energy Outage Pr obability In the proposed network, the EOP is defined as the network energy outage in the non-IT mode when all the sources experience energy outage. The EOP is deriv ed as in the following theorem. Theorem 1. The EOP for the multi-sour ce WPT network is derived as P E O = X ~ s n ∈ Θ 1 π n , (39) wher e π n has been derived as in (38) . Pr oof: According to the definition of the network energy outage giv en in II-B, the EOP of the proposed network is readily derived. Corollary 1. The EOP for the multi-source WPT network when the transmit power of the PB goes to infinity ( P B → ∞ ) is given by P E O = ( P ~ s n ∈ Θ 1 π n , K = 1 , 0 , K ≥ 2 , (40) wher e π n has been derived as in (38) . Pr oof: W e fisrt denote A = A 1 , 1 A 1 , 2 A 2 , 1 A 2 , 2 , where A i,j represents the transition matrix from Θ i to Θ j , i, j ∈ { 1 , 2 } . W e also denote the stationary distributions of states in Θ 1 and Θ 2 as π Θ 1 ∈ R N 1 × 1 and π Θ 2 ∈ R N 2 × 1 , respectively . When P B → ∞ , we hav e ε n k → ∞ , ε n,i ∗ k → ∞ . Therefore, if ~ s n ∈ Θ 1 , it will always transfer to the all- full state [ L, · · · , L ] , because the harvested energy at each source will always exceed the energy capacity . Similarly , if ~ s n ∈ Θ 2 , it will always transfer to an almost-all-full state [ L, · · · , l i ∗ , · · · , L ] , where 0 ≤ l i ∗ ≤ L − l S and i ∗ ∈ { 1 , · · · , K } is the index of the selected IT source. Note that both [ L, · · · , L ] and [ L, · · · , l i ∗ , · · · , L ] are an element of Θ 2 . As a result, for K ≥ 2 , regardless of any current state the network remains, it will ne ver transfer to Θ 1 , which results to A 1 , 1 = 0 N 1 × N 1 and A 2 , 1 = 0 N 2 × N 1 . Substituting the deriv ed results into (37), we deriv e the matrix-form equation as 0 N 1 × N 1 A 1 , 2 0 N 2 × N 1 A 2 , 2 T π Θ 1 π Θ 2 = π Θ 1 π Θ 2 , (41) which yields to π Θ 1 = 0 . Referring to (39), we derive the EOP of the network as P E O = X ~ s n ∈ Θ 1 π n = N 1 X k =1 π Θ 1 ,k = 0 , (42) where π Θ 1 ,k denotes the k th element of π Θ 1 . Whereas, for K = 1 , due to the half-duplex nature, the single source can not harvest ener gy when it transmits information. Hence, if the network remains in Θ 2 , the source will always consumed energy until an energy outage e vent occurs. As such, the EOP when K = 1 is derived using (39). B. Connection Outage Pr obability The COP quantifies the probability that the information can not be correctly decoded at the legitimate receiv er when the IT operation actually takes place. According to the total probability theorem, and considering the fact that no data is transmitted when energy outage occurs. Theorem 2. The overall COP for the multi-source WPT network is derived as P C O = X ~ s n ∈ Θ 2 π n Y k ∈ ϑ T H n K k =1 1 − exp − σ 2 D γ t th ¯ γ S k D P S , (43) wher e π n has been derived as in (38) . Pr oof: According to the total probability theorem, the ov erall COP of the multi-source WPT network can be calcu- lated as P C O = X ~ s n ∈ Θ π n P C O,n ( a ) = X ~ s n ∈ Θ 2 π n P C O,n . (44) where the result after ( a ) = is deri ved according to the fact that no information would be transmitted when energy outage occurs, 8 A = 0 . 0356 0 . 0237 0 . 0471 0 . 0318 0 . 0212 0 . 0421 0 . 2674 0 . 1779 0 . 3533 0 . 0851 0 0 0 . 0972 0 0 0 . 8177 0 0 0 0 . 0851 0 0 0 . 0972 0 0 0 . 8177 0 0 . 2737 0 . 2427 0 . 4836 0 0 0 0 0 0 0 0 . 1358 0 . 3604 0 . 0429 0 0 0 . 4609 0 0 0 0 0 . 4963 0 0 . 0429 0 0 0 . 4609 0 0 0 0 0 . 2737 0 . 2427 0 . 4836 0 0 0 0 0 0 0 0 . 1358 0 . 3604 0 . 5037 0 0 0 0 0 0 0 0 . 4963 0 0 . 5037 0 . (39) and P C O,n represents the COP when the network remains at state ~ s n , which is derived as P C O,n = X i ∈ ϑ T H n Pr ( i ∗ = i ) Pr γ n,i ∗ D < γ t th . = X i ∈ ϑ T H n p n i F γ n,i ∗ D γ t th (45) where γ t th = 2 R t − 1 , R t (bits/s/Hz) denotes the transmission rate of the network. According to the selection policy described in (7), we can present the CDF of γ n,i ∗ D as F γ n,i ∗ D ( x ) = F Y S D σ 2 D x , (46) where Y S D = P S max k ∈ ϑ T H n n | h S k D | 2 o . After some manipula- tions, the CDF of Y S D is derived as F Y S D ( y ) = Y k ∈ ϑ T H n K k =1 1 − exp − y ¯ γ S k D P S . (47) It is easy to find from (46) and (47) that the CDF of γ n,i ∗ D has no relationship with the selection probabilities of every source S i , i ∈ ϑ T H n . Besides, according to the total probability theorem, we derive P i ∈ ϑ T H n p n i = 1 . Hence, P C O,n can be calculated as P C O,n = F γ n,i ∗ D γ t th = Y k ∈ ϑ T H n K k =1 1 − exp − σ 2 D γ t th ¯ γ S k D P S . (48) By substituting π n in (38) and P C O,n in (48) into (44), the COP of the proposed network is deriv ed. C. A vera ge T ransmission Delay IN the IT mode, there would be at most one source to send messages at each time slot, a transmission delay is caused at each source. In practical, we may concern that how many time slots on av erage a specific source need to wait for to be selected for IT operation, which can be quantified by the av erage transmission delay (A TD). Before delving into the in vestigation, we will clarify the fundamental conception of A TD by giving out a simple example. Let us start by looking into the netw ork of K energy- sufficient sources, where all the sources can be selected for IT operation equally . It is readily known that at each time slot, each source has the transmision probability of 1 /K . In other words, for each source, a time slot is allocated once on av erage within K slots. As a consequence, the A TD would be ¯ T = K T 0 for ev ery source in this network 2 . Howe ver , in our proposed energy storage networks, whether a specific source can be selected for IT operation differs for dif ferent storage states. In other words, the transmission probability of a certain source is not fixed, and all the sources do not have the equal transmission probability as well. In order to solve this problem, we denote p n T ,i as the transmission probability for source S i at state s n . According to the previous description, p n T ,i can be deriv ed as p n T ,i = 0 , l n i < l S , p n i , l n i ≥ l S . (49) Theorem 3. The average transmission pr obability for sour ce S i and its A TD are derived as p T ,i = X ~ s n ∈ Θ π n p n T ,i = X ~ s n ∈ Θ 2 π n p n T ,i , (50) and ¯ T i = T 0 p T ,i = T 0 P ~ s n ∈ Θ 2 π n p n t,i , (51) r espectively , where π n has been derived as in (38) . Pr oof: The proof is omitted. V . N U M E R I C A L R E S U LT S In this section, we present the numerical results to illustrate the impacts of various system parameters on the performance of the proposed network. As shown in the below figures, the theoretical results are in exact agreement with the numeri- cal simulations, which show the correctness of the analysis. W ithout any loss of generality , all the nodes are set in a two-dimensional plane in all simulations, and the coordinates of B and D are set as B = ( x B , 0) and D = ( x D , 0) , and the coordinates of the source nodes are assumed to be S 1 = ( − r S , 0) , S 2 = (0 , r S ) , S 3 = ( r S , 0) , S 4 = (0 , − r S ) , S 5 = ( √ 2 2 r S , √ 2 2 r S ) and S 6 = ( − √ 2 2 r S , − √ 2 2 r S ) , respec- tiv ely . With K sources, we take sources from S 1 to S K in order automatically , and we set α = 3 , R t = 3 bits/s/Hz, N B = 5 , N 0 = − 80 dBm, and ε th S = 10 mJ. 2 For the extreme case of K = 1 , we can find that the source can always transmit successively . W e say that the A TD of this network is ¯ T = T 0 , even though no time slot is needed to wait for IT operation. 9 P B (dBm) 10 15 20 25 30 35 40 EOP 10 -4 10 -3 10 -2 10 -1 10 0 Theo., x B = ! 5 m, 2 = 0 : 6 Theo., x B = ! 5 m, 2 = 0 : 8 Theo., x B = ! 5 m, 2 = 1 Theo., x B = ! 3 m, 2 = 0 : 6 Theo., x B = ! 3 m, 2 = 0 : 8 Theo., x B = ! 3 m, 2 = 1 Simu. Fig. 5. EOP of the multi-source WPT network versus the transmit power of power beacon P B with different x B and η . P B = 30 dBm, l S = l th S , ε T = 40 mJ, x D = 200 m, and r S = 1 m. P B (dBm) 10 15 20 25 30 35 40 EOP 10 -8 10 -7 10 -6 10 -5 10 -4 10 -3 10 -2 10 -1 10 0 Theo. Simu. K = 1 ; 2 ; 3 ; 4 Fig. 6. EOP of the multi-source WPT network versus the transmit power of power beacon P B with different K . l S = l th S , η = 0 . 8 , ε T = 40 mJ, L = 2 , x B = − 3 m, x D = 200 m, and r S = 1 m. Fig. 5 plots the EOP of the multi-source WPT network versus the transmit power of the po wer beacon P B with different x B and η . As can be seen from this figures, the EOP declines rapidly when P B increases. Besides, it shows that the EOP will gro w sev erely when x B increases. Moreov er , the EOP also raises when η becomes smaller . This can be well understood because a greater x B implies a farther distance of energy transmission, which results in the decline of accessible energy that can be harvested by sources due to a much sev erer path poss. Like wise, a smaller η means a lower energy efficienc y , which indicates that less ener gy can be con verted by sources and saved in their storages. " T (mJ) 0 500 1000 1500 2000 EOP 10 -8 10 -7 10 -6 10 -5 10 -4 10 -3 10 -2 10 -1 10 0 Theo., L = 2, K = 1 Theo., L = 2, K = 2 Theo., L = 2, K = 3 Theo., L = 4, K = 1 Theo., L = 4, K = 2 Theo., L = 4, K = 3 Simu. Fig. 7. EOP of the multi-source WPT network versus the energy capacity ε T with different K and L . P B = 30 dBm, l S = l th S , η = 0 . 8 , x B = − 3 m, x D = 200 m, and r S = 1 m. " T (mJ) 0 50 100 150 200 EOP 10 -8 10 -7 10 -6 10 -5 10 -4 10 -3 10 -2 10 -1 10 0 The o., " " = 10 m J, K = 1 The o., " " = 10 m J, K = 2 The o., " " = 10 m J, K = 3 The o., " " = 20 m J, K = 1 The o., " " = 20 m J, K = 2 The o., " " = 20 m J, K = 3 Simu. Fig. 8. EOP of the multi-source WPT network versus the energy capacity ε T with different K and ε ∆ . P B = 30 dBm, l S = l th S , η = 0 . 8 , x B = − 3 m, x D = 200 m, and r S = 1 m. Figs. 6 plots the EOP of the multi-source WPT network versus the transmit power of the po wer beacon P B with different K . It is depicted that, the EOP performance is rather poor when K = 1 , which howe ver can be greatly impro ved when multiple sources are deployed, especially when a larger P B can be provided. This finding is of significant importance because it indicates the effecti veness to greatly decrease the EOP of network by increasing the number of the sources. Figs. 7-8 e xamine the EOP of the multi-source WPT net- work versus the energy capacity ε T . W e note that in Fig. 7, the 10 " T (mJ) 20 40 60 80 100 120 140 160 180 200 COP 10 -4 10 -3 10 -2 10 -1 Theo.,ov erall CO P Theo.,state COP (worst) Theo.,state COP (b est) Theo.,state COP Simu. P B = 25 ; 30 ; 35 dBm Fig. 9. COP of the multi-source WPT network versus the energy capacity ε T with different P B . K = 2 , ε ∆ = 20 mJ, l S = l th S , η = 0 . 8 , x B = − 3 m, x D = 200 m, and r S = 1 m. discretization level of the network L is fixed so that the single unit of energy ε ∆ grows proportionally with the growth of ε T . Howe ver , in Fig. 8, L and ε T are proportionally increased while k eeping ε ∆ unchanged. From Fig. 7, we find that for a specific ε T , the EOP reduces when a larger L is applied. By contrast, for a giv en L , the EOP grows rapidly with the increase of ε T . Specifically , when ε T is large enough, the EOP approaches close to 1, even when multiple sources are applied. On the contrary , it is demonstrated in Fig. 8 that, the EOP declines significantly with the increase of ε T , which differs from the behavior shown in Fig. 7. W e note that the harvested energy at each time slot is limited. Therefore, less ener gy could be harvested for the network when the single unit of energy ε ∆ grows, as a larger ε ∆ is more difficult to be satisfied. Figs. 9-10 compare the COP of the multi-source WPT network versus the energy capacity ε T with different P B . It is noted that the red square symbols represent the COPs when the network remains at a certain state, and the blue lines are the network overall COPs. As depicted in these figures, the COPs under different states vary greatly , and the overall COP firstly approaches to the worst state performance and then goes do wn to get close to the best state performance if an appropriate P B could be provided. Besides, this trend could be accelerated by increasing P B . All these observations indicate that a greater energy capacity and P B are both benefit to decrease the o verall COP of the network. Fig. 11 plots the COP of the multi-source WPT network versus the transmit power of the po wer beacon P B with different K and x D . As can be predicted, the COP of the network grows rapidly when x D increases, which again is resulted from the path loss effect of the wireless channel. In addition, we observe that the COP performance could also be significantly enhanced by adding the number of the sources. It is noted that for a specific line with fixed K and x D , the " T (mJ) 20 40 60 80 100 120 140 160 180 200 COP 10 -5 10 -4 10 -3 10 -2 10 -1 Theo.,ov erall CO P Theo.,state COP (worst) Theo.,state COP (b est) Theo.,state COP Simu. P B = 25 ; 30 ; 35 dBm Fig. 10. COP of the multi-source WPT network versus the energy capacity ε T with different P B . K = 3 , ε ∆ = 20 mJ, l S = l th S , η = 0 . 8 , x B = − 3 m, x D = 200 m, and r S = 1 m. P B (dBm) 10 15 20 25 30 35 40 45 50 COP 10 -8 10 -7 10 -6 10 -5 10 -4 10 -3 10 -2 10 -1 Theo., ov erall COP , x D = 400 m Theo., ov erall COP , x D = 200 m Simu. K = 1 ; 2 ; 3 ; 4 Fig. 11. COP of the multi-source WPT network versus the transmit power of power beacon P B with different K and x D . L = 2 , ε T = 20 mJ, l S = l th S , η = 0 . 8 , x B = − 3 m, x D = 200 m, and r S = 1 m. COP goes up with the increase of P B at first and then turns down quickly at about 20 to 25 dBm, which reaches a floor ev entually . W e highlight that, as has clarified pre viously , it is rather dif ficult for the sources to collect sufficient energy from the wireless signals if P B remains at a very low level. Hence, the EOP of network would be rather large in this case, so IT operation can only occur with a very little probability . Recalling that the overall COP is the weighted average of all the states, hence, it would be rather low because the network will stay in energy outage state with a very high probability . It should be pointed out that the lo w le vel of COP under 11 P B (dBm) 20 25 30 35 40 A TD (slots) 10 0 10 1 10 2 10 3 10 4 10 5 10 6 Theo., A TD of S 1 , r S = 0 : 5 m Theo., A TD of S 2 , r S = 0 : 5 m Theo., A TD of S 1 , r S = 1 m Theo., A TD of S 2 , r S = 1 m Simu. x B = ! 4 m x B = ! 5 m x B = ! 3 m Fig. 12. A TD of the multi-source WPT network versus the transmit power of power beacon P B with different r S and x B . K = 2 , L = 2 , ε T = 20 mJ, l S = l th S , η = 0 . 8 , and x D = 200 m. P B (dBm) 20 25 30 35 40 A TD (slots) 10 0 10 1 10 2 Theo., A TD of S 1 Theo., A TD of S 2 Simu. P S = 10 ; 30 ; 50 mW Fig. 13. A TD of the multi-source WPT network versus the transmit power of power beacon P B with different P S . K = 2 , L = 5 , ε T = 50 mJ, η = 0 . 8 , r S = 0 . 3 m, x B = − 3 m and x D = 200 m. this condition does not mean a good performance. Instead, it indicates a very poor performance because it will result in a huge transmission delay to the sources. Figs. 12-13 present the A TD of the multi-source WPT network versus the transmit power of the po wer beacon P B with different r S , x B and P S . It is easy to find from these two figures that the A TD performance is not symmetric to all the sources, and this asymmetry would be enlarged when r S increases. This is comprehensible because in the proposed network, each source undergoes independent but not identically distributed channels. Generally speaking, the sources that are more close to the power beacon will hav e P B (dBm) 20 25 30 35 40 A TD (slots) 10 0 10 1 10 2 10 3 10 4 Theo., K = 1 Theo., K = 2 Theo., K = 3 Theo., K = 4 Theo., K = 5 Theo., K = 6 Simu. Fig. 14. A TD of the multi-source WPT network versus the transmit power of power beacon P B with different K . L = 2 , ε T = 20 mJ, η = 0 . 8 , r S = 0 m, x B = − 4 m and x D = 200 m. lower A TD. Furthermore, we observe in both two figures that the A TD becomes about 2 time slots when P B becomes large, which is equal to the number of the sources. Moreo ver , we see that the A TD rises sharply when the po wer beacon gets far from the sources. Furthermore, Fig. 13 depicts that the A TD for all the sources would increase when the transmit power of sources is promoted. W e note that, under the giv en conditions, P S = 10 , 30 , 50 mJ actually corresponds to l S = 1 , 3 , 5 , respectiv ely . As a result, by promoting P S , on the one hand, it needs to spend much more time slots for the sources to accumulate suf ficient energy , and on the other hand, the ener gy consumption of the IT operation would also increase. Figs. 14 plots the A TD of the multi-source WPT network versus the transmit power of the po wer beacon P B with different K . Similar with Figs. 12-13, we find that the A TD could be rather huge in the lo w regime of P B . Howe ver , when the number of the sources increase gradually , the A TD performance could be improved drastically . For example, when P B = 20 dBm, the A TD will decline from about 3000 time slots when K = 1 to just about 6 time slots when K = 6 . Furthermore, when P B gets high, the A TD reduces quickly and ev entually reaches a constant, which is about K . W e note that the best A TD performance is also K in a network where all the sources are energy-suf ficient, which is resulted from the source selection approach. All above results imply the validity to impro ve A TD performance by deploying more sources in the network, especially when the wireless energy is not so sufficient. V I . C O N C L U S I O N S In this paper, we presented a general Markov-based model for the PB assisted multi-source wireless-po wered network with our proposed source selection transmission scheme, which captures the dynamic energy behaviors of the state tran- sitions of the whole network. T wo network operating modes, 12 the IT mode with ZF beamforming and the non-IT mode with equal po wer transmision, were proposed for sustainable ener gy utilization and reliable data transmission. T o characterize the reliability of proposed netw ork, the energy outage probabily was deriv ed for non-IT mode, and the connection outage probability was deriv ed for IT mode. T o quantify the delay brought by the source selection transmission, the A TD was also defined and deri ved. All the analytical results are validated by simualtion, and the results shown that the EOP , COP , and A TD can be significantly improved via increasing the number of sources deployed in the proposed network. R E F E R E N C E S [1] S. T ang and L. T an, “Reward rate maximization and optimal transmission policy of EH device with temporal death in EH- WSNs, ” IEEE T rans. W ir eless Commun. , vol. 16, no. 2, pp. 1157–1167, Feb ., 2017. [2] D. Sui, F . Hu, W . Zhou, M. Shao, and M. Chen, “Relay selection for radio frequency energy-harvesting wireless body area network with buf fer, ” IEEE Internet Things J. , to appear , 2017. [3] U. Raza, P . K ulkarni, and M. Sooriyabandara, “Low power wide area networks: An overvie w , ” IEEE Commun. Surve ys T uts. , vol. 19, no. 2, pp. 855–873, 2nd quart., 2017. [4] D. W u, Y . Cai, and M. Guizani, “ Asynchronous flow schedul- ing for green ambient assisted living communications, ” IEEE Commun. Mag. , vol. 53, no. 1, pp. 64–70, Jan., 2015. [5] L. P . Qian, G. Feng, and V . C. M. Leung, “Optimal transmission policies for relay communication networks with ambient energy harvesting relays, ” IEEE J. Sel. Ar eas Commun. , vol. 34, no. 12, pp. 3754–3768, Dec., 2016. [6] G. Pan, H. Lei, Y . Deng, L. Fan, J. Y ang, Y . Chen, and Z. Ding, “On secrecy performance of MISO SWIPT systems with T AS and imperfect CSI, ” IEEE T rans. Commun. , vol. 64, no. 9, pp. 3831–3843, Sep., 2016. [7] Z. Y ang, Z. Ding, P . Fan, and N. Al-Dhahir , “The impact of po wer allocation on cooperati ve non-orthogonal multiple access networks with SWIPT, ” IEEE T rans. W ireless Commun. , vol. 16, no. 7, pp. 4332–4343, Jul., 2017. [8] C. Zhong, H. A. Suraweera, G. Zheng, I. Krikidis, and Z. Zhang, “W ireless information and power transfer with full duplex relaying, ” IEEE T rans. Commun. , v ol. 62, no. 10, pp. 3447– 3461, Oct., 2014. [9] Y . Zeng and R. Zhang, “Full-duple x wireless-po wered relay with self-energy recycling, ” IEEE W ireless Commun. Lett. , vol. 4, no. 2, pp. 201–204, Apr ., 2015. [10] X. Zhou, R. Zhang, and C. K. Ho, “W ireless information and power transfer: Architecture design and rate-energy tradeoff, ” IEEE T rans. Commun. , vol. 61, no. 11, pp. 4754–4767, Nov ., 2013. [11] D. W ang, R. Zhang, X. Cheng, and L. Y ang, “Capacity- enhancing full-duplex relay networks based on power splitting (PS-)SWIPT, ” IEEE T rans. V eh. T echno. , v ol. 66, no. 6, pp. 5445–5450, Jun., 2017. [12] X. Zhou, “Training-based SWIPT: Optimal power splitting at the recei ver , ” IEEE T rans. V eh. T echno. , v ol. 64, no. 9, pp. 4377– 4382, Sep., 2015. [13] K. Huang and X. Zhou, “Cutting the last wires for mobile communications by microwa ve power transfer, ” IEEE Commun. Mag. , vol. 53, no. 6, pp. 86–93, Jun., 2015. [14] X. Zhou, J. Guo, S. Durrani, and M. D. Renzo, “Power beacon- assisted millimeter wa ve Ad Hoc networks, ” IEEE T rans. Com- mun. , vol. 66, no. 2, pp. 830–844, Feb., 2018. [15] “Cota: Real wireless po wer , ” CES 2017 Inno vation A wards , [Online]. A vailable: http://www .ces.tech/Events- Experiences/Innov ation-A wards-Program/Honorees.aspx. and http://www .ossia.com/cota/. [16] X. Jiang, C. Zhong, Z. Zhang, and G. Karagiannidis, “Power beacon assisted wiretap channels with jamming, ” IEEE T rans. W ireless Commun. , vol. 15, no. 12, pp. 8353–8367, Dec., 2016. [17] Y . Ma, H. Chen, Z. Lin, Y . Li, and B. V ucetic, “Distributed and optimal resource allocation for power beacon-assisted wireless- powered communications, ” IEEE T rans. Commun. , vol. 63, no. 10, pp. 3569–3583, Oct., 2015. [18] L. Chen, W . W ang, and C. Zhang, “Stochastic wireless powered communication networks with truncated cluster point process, ” IEEE T rans. V eh. T echno. , vol. 66, no. 12, pp. 11 286–11 294, Dec., 2017. [19] L. Shi, L. Zhao, K. Liang, and H. H. Chen, “W ireless energy transfer enabled D2D in underlaying cellular networks, ” IEEE T rans. V eh. T echno. , vol. 67, no. 2, pp. 1845–1849, Feb ., 2018. [20] A. Salem, K. A. Hamdi, and K. M. Rabie, “Physical layer security with RF ener gy harvesting in AF multi-antenna relaying networks, ” IEEE T rans. Commun. , vol. 64, no. 7, pp. 3025– 3038, Jul., 2016. [21] C. Pielli, C. Stefano vic, P . Popo vski, and M. Zorzi, “Joint compression, channel coding and retransmission for data fidelity with energy harvesting, ” IEEE T rans. Commun. , to appear, 2017. [22] Y . Bi and H. Chen, “ Accumulate and jam: T owards secure communication via a wireless-powered full-duplex jammer, ” IEEE J. Sel. T opics Signal Pr ocess. , vol. 10, no. 8, pp. 1538– 1550, Dec., 2016. [23] H. Liu, K. J. Kim, K. S. Kwak, and H. V . Poor , “Power splitting- based SWIPT with decode-and-forward full-duplex relaying, ” IEEE T rans. W ir eless Commun. , vol. 15, no. 11, pp. 7561–7577, Nov ., 2016. [24] ——, “QoS-constrained relay control for full-duplex relaying with SWIPT, ” IEEE T rans. W ir eless Commun. , vol. 16, no. 5, pp. 2936–2949, May , 2017. [25] I. Ahmed, K. T . Phan, and T . Le-Ngoc, “Stochastic user scheduling and power control for energy harvesting networks with statistical delay provisioning, ” in 2015 IEEE 26th Annual International Symposium on P ersonal, Indoor , and Mobile Ra- dio Communications (PIMRC) , Hong Kong, China, 2015. [26] Q. Y ao, T . Q. S. Quek, A. Huang, and H. Shan, “Joint downlink and uplink energy minimization in WET-enabled networks, ” IEEE T rans. W ir eless Commun. , vol. 16, no. 10, pp. 6751–6765, Oct., 2017. [27] I. Krikidis, S. Timotheou, S. Nikolaou, G. Zheng, D. W . K. Ng, and R. Schober, “Simultaneous wireless information and power transfer in modern communication systems, ” IEEE Commun. Mag. , vol. 52, no. 11, pp. 104–110, Nov ., 2014. [28] J. Zhang, C. Y uen, C. K. W en, S. Jin, K. K. W ong, and H. Zhu, “Large system secrecy rate analysis for SWIPT MIMO wiretap channels, ” IEEE T rans. Inf. F or ensics Security , vol. 11, no. 1, Jan., 2016. [29] K. Hosseini, W . Y u, and R. S. Adve, “Large-scale MIMO versus network MIMO for multicell interference mitigation, ” IEEE J. Sel. T opics Signal Pr ocess. , v ol. 8, no. 5, pp. 930–941, Oct., 2014. [30] A. Bletsas, A. Khisti, D. P . Reed, and A. Lippman, “ A simple cooperativ e div ersity method based on network path selection, ” IEEE J. Sel. Ar eas Commun. , vol. 24, no. 3, pp. 659–672, Mar ., 2006. [31] X. T ang, Y . Cai, Y . Huang, T . Q. Duong, W . Y ang, and W . Y ang, “Secrecy outage analysis of buf fer-aided cooperativ e MIMO relaying systems, ” IEEE T rans. V eh. T echno. , to appear, 2017. [32] Z. Ding, Z. Zhao, M. Peng, and H. V . Poor , “On the spec- tral ef ficiency and security enhancements of NOMA assisted multicast-unicast streaming, ” IEEE T rans. Commun. , vol. 65, no. 7, pp. 3151–3163, Jul., 2017. [33] A. Y ilmaz, F . Y ilmaz, M. S. Alouini, and O. Kucur , “On the performance of transmit antenna selection based on shadowing side information, ” IEEE T rans. V eh. T echno. , vol. 62, no. 1, pp. 454–460, Jan., 2013. 13 [34] I. Krikidis, T . Charalambous, and J. S. Thompson, “Buffer -aided relay selection for cooperative diversity systems without delay constraints, ” IEEE T rans. W ireless Commun. , vol. 11, no. 5, pp. 1957–1967, May , 2012.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment