Social learning for resilient data fusion against data falsification attacks
Internet of Things (IoT) suffers from vulnerable sensor nodes, which are likely to endure data falsification attacks following physical or cyber capture. Moreover, centralized decision-making and data fusion schemes commonly used by these networks tu…
Authors: Fern, o Rosas, Kwang-Cheng Chen
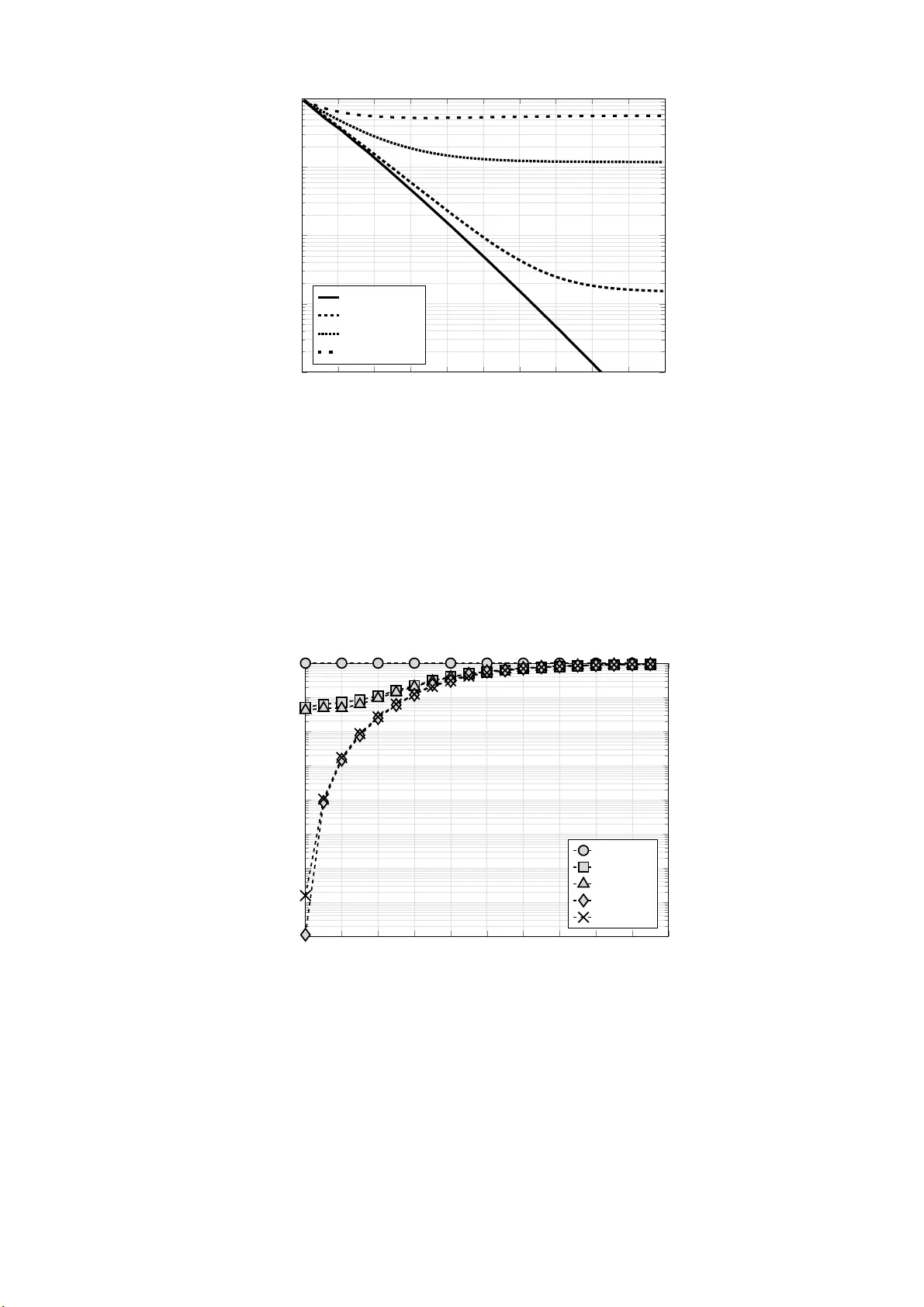
So cial lea rning fo r resilient data fusion against data falsification attacks F ernando Rosas 1 , 2 , Kw ang-Cheng Chen 3 and Deniz G¨ und¨ uz 2 1 Centre of Co mplexity Science and Department of Ma them ati c s, Imp erial College London, UK 2 Depa rtment of Electrical and Electronic Engineering, Imp erial College London, UK 3 Depa rtment of Electrical Engineering, University of South Flo rida, USA Abstract Internet of Things (IoT) suffers f ro m vulnerabl e senso r no des, which are lik ely to endure data falsi fication att acks foll o wing physical or cyb er capture. Mo reover, centralized decision- making and data fusion schemes commo nly used b y t hese net w o rks turn these decision p oints into si ngle p oints of failure, which are li k ely to b e exploited b y smart att ack ers. In o rder to face this serious security thread, w e propose a novel s cheme that enables distributed data aggregation and decision-making b y following so cial lea rning p rinciples. Our proposed scheme mak es senso r no des to act resembling the manners of agents within a so cia l net w o rk. W e analytical ly examine how lo cal actions of ind ividual agents can pro pagate t hrough the whole net w o rk, affecting the collective b ehavi our. Fi nally , we sho w ho w socia l learning can enable net w o rk re sili ence against da ta falsificati on attacks, e ven when a significant p o rtion of the no des have b een comp romised by the adversary . Index terms— Distributed decisi on-making, data fusion, senso r net w o rks, so cial net w o rks, data fal sification a ttacks, Byzantine no des, collective b ehaviour, so cial learning, information cascades. 1 1 In tro ductio n 1.1 Motiv ation Internet of Things (IoT) is exp ected to play a central role in digit al so ciet y . How ever, b efo re adopting this technology it is crucia l to gua rantee its security , sp ecially fo r those publ ic utili- ties whose safety is crucial fo r the well-being of society [1]. Recent cyb er-attacks that created significant damage have b een widely rep o rted, e.g., the s elf-p ropagating malwa re W anna Cry that caused a fa mous wo rldwid e net w o rk hack in May 2017 [2]. Therefo re, developing tech- nologies fo r guaranteeing the safet y of large info rmation net w o rks such as IoT is a challenging but urgent need. A s info rmation net w o rks get mo re closely intert wined with our dail y li fes, ensuring t heir safety in the future wil l b ecome a n even mo re chall enging iss ue. As the level of s ecurit y is determined b y the w eak est element, a majo r dilemma of IoT securit y lies in the low-c omplexity senso r net wo rks th at a re lo cated at the edge of the system. These senso r net w o rks a re usually comp osed b y a larg e numb er of a utonomous electronic devices, which collect info rmation that is critical to the control and op eration of IoT [3, 4]. By monito ring extensive geographical areas, these net w o rks enable a wide range of services to civil so ciety , b eing a k ey element fo r the well-being of sma rt cit ies [5, 6].These net w o rks may also p erfo rm sensitive tas ks, including the surveill ance over military or secure zones, intrusi on detection to p rivate property , monitoring of drink able w ater tanks and pro tection f rom chemical attacks [7, 8]. Although the de sign of secure wireless senso r net w o rks h ave been widely studied (e.g . [9 –11] and references therein), there remain op en pro blems of b oth theo retical and engineering na- ture [12 ]. In p a rticular, as the numb er of senso rs is usually very large, a p recise management of them is therefore challenging, o r even unfeasible. A significant p o rtion of the senso rs mi ght b e deplo yed in unprote cted a reas where it is imp ossible to ensure their physical o r cyber s e- curit y (e.g., wa r zones, o r regions controlled by an adversary). F urthermo re, senso r no des are generally not t amp er-p ro of due to cost restrictions, and ha ve hence l imited computing a nd net- w o rking capabili ties. Therefo re, they ma y not b e capable of emplo ying relia ble cryptographic o r securit y functions of high complexit y . The vulnerability of s enso r no des ma k es it reasonable to exp ect that they might b e victims of cyb er/physical attacks driven b y in telligent adversa ries. A ttacks to inform ati on net w o rks a re usuall y catego rized into outside attacks and insider attacks . Outside attacks include (distributed) denial of services (DoS), which use the b roadcasting nature for wireless com- munications to disru pt the communications capabilities [10]. In contrast, in i nsider atta cks the adversa ry “recruits” senso r no des b y malwa re through cyb er/wireless means, or directly b y physical substituti on [13]. F ollo wing the classic Byzantine Generals Problem [14], these “Byzantine no des” are authenticated, a nd recognized as vali d memb ers of the netw o rk. Byzan- tine no des can hence generate false data, exhibit arbitra ry b ehaviour, and collude with others to create net w o rk malfunctions. In general, inside attacks are considered t o b e more dangerous to in fo rmation net w o rks tha n outside attacks. The effect of Byzanti ne no des and da ta falsifi cation over distribut ed senso r n et w o rks h as b een intensely studied; the impact over the net w ork p erfo rmance ha s b een cha racterized, and va rious defense mechanisms ha s b een p rop osed (c.f. [15] fo r an overview, and also [16–20] fo r some recent contributions). H o we ver, all these wo rks fo cus on netw o rks with star o r tree top ology , and rely on centralising the decision-making in sp ecial nodes, called “fusion centers” (F Cs), whi ch gather all the sensed data. Therefo re, a k ey element in these approache s is a st rong div ision of lab our: o rdina ry senso r no des merely sense and fo rwa rd data, while the p ro cessing is d one exclusively at the FC, co rresp onding to a distrib uted-sensing/centralized- p ro cessing app roach. Thi s literature impli citly a ssume that the FCs are capabl e of executing secure codi ng and protocols, a nd hence are out of the reach of attack ers. Ho w ever, l a rge info r- mation net wo rks might require an other kind of mediato r devi ces, known a s data aggregato rs (D As), which have the cap ability to access the cloud through high-bandwidth com municati on links [21]. DAs a re attra ctive ta rgets t o insider at tacks, as they might als o b e lo cated in 2 unsafe lo cations due to the limited range of senso r nodes’ radi os. Please note that a tamp ered D A can completely disable the sensing capabilit ies of all the no des whose info rmation ha s b een aggregated, generating a single p oint of fail ure that is lik ely to b e exploited b y smart adversa ries [22]. An attractive route to address this i ssue is to consider distributed-sensing/distribu ted- p ro cessing schemes, which a void centralized decisi on making while dis tributing p ro cessing tasks throughout the netw o rk [23]. Ho w ever, the design of practical distributed-sensing / distributed-processing schemes is a challenging task, as collective computati on phenomena usually exhi bit highly non-trivi al features [24 , 25]. In effect, even though the distributed sensing literature is vast (fo r clas sic references c.f. [26–28], and more mo dern su rveys see [3, 4, 29, 30]), the construction of optimal di stributed schemes is in general NP-hard [31]. More over, although in man y scena rios the optimal schemes can be characterized as a set of thresholds f o r li k eliho o d functions, the determinati on of these thresholds is usua lly an intractable p roblem [26]. F o r example, homogeneo us thresholds can b e sub optimal even fo r n et w o rks with similar sensors a rranged in star topology [32], b eing only asymptotically optimal in the netw ork size [33]. Mo reover, symme tric strategies are n ot sui table fo r more complicated net w o rk top ologies, requiring heuristic metho ds. 1.2 Distributed decision-making in so cial learning In pa rallel, si gnificant resea rch effo rts have b een dedicated to analyz ing social learning , which refers to the decision-making processes tha t t ak e place within so cia l net w o rks [34]. In t hese scena rios, agents mak e decisions b ased on tw o elements: p rivate i nfo rmation that represe nts agent’s p ersonal know ledge, and so cial inf o rmation derived from p revious decisions made by the a gent’s p eers [35]. So cial lea rning w as initially investigated b y pioneering w o rks that studied se quentia l decision- making of B a ye sian a gents over simple so cial netw ork structures [36, 37]. These mo dels sho w ed ho w, than ks to so cial interactions, ind ividuals with w eak p rivate si gnals can ha rvest i nfo rma- tion from the decisions of other agents [38]. Interestingly , i t was also found that aggregation of rati onal decisions could generate su b optimal collective resp onses, degrading th e “wisdom of the cro wds” into mere herd b ehaviour. A fter t hese in itial findi ngs, resea rchers have aimed at developing a deeper u nderstanding of information cascades extending th e o riginal mo dels b y considering mo re general cost metrics [39–41], and b y s tudying the effects of the net w o rk top ology on the a ggregated b ehaviour [42–45]. Non-bay esi an lea rning mo dels have also b een explo red, where agents use simple rul e-of-thumb metho ds to exchange in fo rmation [46 – 52]. So cial l ea rning pla ys a crucial role in many imp o rtant so cial phenomena, e.g., in the a dop- tion o r rejection of new technology , o r in the fo rmation of p olit ical opini ons [34]. So cial lea rning mo dels are pa rticularly interestin g fo r studying info rmation cascades and herd dynam- ics, whi ch arises when the s o cial info rmation pu shes a ll the su bsequent a gents to igno re their o wn p ersonal kno wledge and a dopt a homogeneo us b ehaviour [37]. More over, there have b een a renew ed int erest in understanding information cascades i n the context of e-comme rce and digital so ciet y [45]. Fo r exampl e, inf o rmation cascades might ha ve tremendous consequences in online store s where customers can see the opinions of previous customers b efo re d eciding to buy a product, o r in the emergence of viral media contents based on sequentia l actions of like o r dislik e. Therefo re, developing a deep understanding of the mechanics b ehind information cascades are t riggered, and ho w they impact so cial learning, i s fundamental for our mo d ern net w o rk ed so ciety . The main motivation b ehind this a rticle i s to explore the connections that exist b et w een so cial learning and secure senso r netw orks, bu ilding a bridge betw een the resea rch done sepa- rately by economists a nd so ciologist by one side an d electrical engineers a nd computer scien- tists b y other. A k ey insight fo r establ ishing thi s l ink is to realize that each agent’s decision co rresp ond to a comp ressed description of his/her p rivate i nfo rmation. Therefo re, the fact that agents cannot access the p rivat e i nfo rmation of others, but can only observe their de- 3 cisions, can b e understo o d as a constraint in the communication resources. In this w a y , so cial learning can b e rega rded as an inf o rmation netw ork that p erfo rms di stributed inference (see T a ble 1). Mo reover, it w ould b e natura l to use so cial lea rning principles in the design of dist ributed-sensing/distributed-processing schemes, with t he hop e that this might enables additional robustness to decision-making p ro cesses in senso r netw o rks. T able 1 : T able o f corresp ondances Distributed detection So cial learning Sensor no de So cial agen t Comm unication range So cial neighbourho o d En vironmen tal v ariables State of the world Noisy measuremen t Priv ate information Lo cal pro cessing Agen t’s decision Bandwidth constraints Decision sharing 1.3 Con tribution In contrast t o almost all the exis ting resea rch, this wo rk considers p ow erful top ology-a wa re data fals ification attacks, where the adversa ry kno ws the net wo rk top ology and leverages this kno wledge to ta k e control of the most critical no des of t he net w o rk —either regular no des, DAs o r F Cs. This rep resents a wo rst-case scena rio where the net w o rk structure has b een d isclosed, e.g. through net w o rk tomography via traffic analysi s [53]. The reason why this adversa ry mo del has not b een p opular in the literat ure might b e b ecause traditional distri buted sensing schemes do not offer any resistance against this kind of attack. In this w o rk w e explo re the use of a distrib uted-sensing/distributed-p ro cessing scheme based on s o cial lea rning principles in o rder to deal wi th a top ology-a wa re a dversa ry . The scheme is a th reshold-based data f usion s trategy , related to those considered in [26]. Ho w ever, its relationship with social decision-making allo ws an intuitive understanding of its mechanisms. F o r avoiding security threads intro duced b y fusi on centers, our scheme uses tandem or serial decision sequencing [27, 54 –57]. It i s to b e noted th at, contrast ing with some related literature, our a nalysis do es not fo cus on optimality asp ects of data fusi on, but aims to ill ustrate ho w distributed decision making can enable netw o rk resilience against p o w erful top ology-a wa re data fa lsification attacks. W e demonstrate how netw ork resil ience hold even when a significant numb er of no des have b een comp romised. Our w o rk exploits a p ositive effect of i nfo rmation cascades that has b een overlo oke d b efore : info rmation cascades mak e a la rge numb er of agents/nodes to hold equally qualified e stimat o rs, generating many lo cations where a net w o rk op erato r can collect aggregated data. Therefore , info rmation cascades are crucial in our solution f o r a voiding single p oints of failure. F o r enabling a b etter understanding of info rmation cascades, t his wo rk extends results p resented in [58] p roviding a math ematical characterization of info rmation cascades under dat a falsification attacks. In pa rticular, our results clarify the conditions up on whi ch lo cal actions of individua l agents can p ropagate across the net wo rk, comp romising the collective p erfo rmance. These results p rovides a firs t st ep in the clarification of these non-trivial so cial dynamics, enriching our understa nding of decision-making process i n bias ed so cial netw o rks. This pap er expand s the ideas p resented i n [59] b y developing a formalism that allows considering i ncomplete or imp erfect so cial information. This fo rmalism is used to overcome the st rongest limi tation of the s cheme presented in [59], na mely t he fact that each no de w as required to overhear and store all the previous transmissions i n the netw o rk. Cl ea rly thi s cannot tak e pla ce in a la rge senso r netw ork, due b oth to the sto rage constrain ts of the nodes, and to 4 the large energy consumption required to transmit and receive across all pairs of no des [60]. Therefo re, the present wo rk is an imp o rtant step tow ards making th is scheme mo re relevant fo r p ractical appli cations. The rest of this a rticle is structured as follo ws. Section 2 intro duces the system mo del, describing the net w o rk controller and the adversary b ehaviour. Our so cial lea rning data fusion scheme is then describ ed in Section 3, where some basic statistical pro p erties a re explo red and p ractical a lgo rithm fo r implementing the decision rule is derived. Section 4 ana lyses the mathematical p rop erties of the decision p ro cess, p roviding a geometrical description and a cha racterizati on of info rmation cascades. All these ideas a re then i llustrated in a concrete scena rio in Section 5. Fina lly , Section 6 summa riz es our main conclusions. 2 System mo de l and proble m statemen t This section intro duces the basic elements of our framew o rk and settles the basis for our so cial lea rning scheme , which is then intro duced in S ection 3. In the rest of the pap er upp ercase let- ters X a re used to deno te random variables and lo w ercase x realizations of them, while b oldface letters X and x rep resent vecto rs. Also, P w { X = x | Y = y } = P { X = x | Y = y , W = w } is used a s a sho rthand notation. 2.1 System mo d el W e consider a net w o rk of N no des, each co rresp onding to an info rmation-p ro cessing device that has b een deploy ed in a n area of interest. Each node is equipp ed with a sensor tha t enables the net w o rk to track variables of interest. The measurement of the senso r of the n -th node is denoted by S n , taking va lues over a set S ⊂ R that can b e discrete or continuous 1 . B ased on these signals, the netw ork needs to infer the value of an underlying binary va riabl e W . W e consider net wo rks where a ll the no des have equal sensing capabiliti es, that is, the signals S n a re a ssumed to b e identicall y distribu ted. U nfo rtunately , the general dis tributed detection p roblem fo r a rbitrarily co rrelated signals is kno wn to b e NP-ha rd [31 ]. Hence, fo r the sak e of tra ctability , it i s assumed that the variables S 1 , . . . , S N a re conditionally indep endent given the event { W = w } 2 , f ollo wing a pro babil it y dis tribution denoted b y µ w . It is al so assumed that b oth µ 0 and µ 1 a re absolut ely continuous with resp ect to each other [67], i.e., no pa rticular signal determines W unequivo cally . This property , in turn, gua rantees tha t the log-lik eliho o d ratio of these tw o distribut ions is alwa ys w ell-defined, b eing given b y the loga rithm of the co rresp onding Rad on-Nik o dym derivative 3 Λ S ( s ) = log dµ 1 dµ 0 ( s ) . In a ddition to sensing hardw are, each no de i s equipp ed wi th limited computing capab ility and a wireless radio to transit and receive data. Tw o no des in the netw o rk a re assumed to b e connected if t hey can exchange information wirelessly . Note that senso r no des usua lly have a very limited battery budget, which imp ose severe restrictions on their communication capabiliti es [68]. Therefore , it is assumed that each n o de fo rwa rd s i ts data to others only by b roadcasting a bina ry variable X n . These si mple signal s do not imp ose an add itional burden on the communication resources, a s they could b e app ended to existent wireless control pack ages and viceversa, o r could b e shared b y light, ultrasound or other al ternative media. W e fo cus on the case in whi ch the sensing capabi lities of each senso r a re limited; and hence, any inference ab out W ma de based only on the sensed data S n cannot achieve a high accuracy . Interestingly , due to t he nature of wireless broadcasting, nearb y t ransmissions can b e 1 The generalization of our framew or k a nd results to vector-v alued sensor outputs is straig ht for ward. 2 The conditional indep endence of se ns or signals is satisfied when the senso r noise is due to lo cal c a uses (e.g. thermal noise), but do not hold when there exist common noise sources (e.g. in the case of distributed ac o ustic sensors [61]). F or works that consider sensor interdependence see [62 – 66]. 3 When S n takes a finite num b er of v a lues then dµ 1 dµ 0 ( s ) = P { S n = s | W =1 } P { S n = s | W =0 } , while if S n is a contin uous r a ndom v a riable with conditio na l p.d.f. p ( S n | W = w ) then dµ 1 dµ 0 ( s ) = p ( s | W =1) p ( s | W =0) . 5 overhea rd, and therefo re the info rmation that they ca rry can b e fused with what is extracted from the lo cal s enso r. The inf o rmation that a no de can extra ct from overhea ring trans missions of other no des is called “social info rmation”, contrasting with the “senso rial inf o rmation” that is obtain ed from the sensed signal S n . Without loss of generality , no des transmit their signals sequentially acco rding to their indices (i.e., node 1 transmit s first, then no de 2, etc.). It is assumed that this sequence is randomly chosen, and can b e changed b y the net w o rk op erato r at a ny ti me (c.f. Section 2.2). In gene ral t he broadcasted signal s X 1 , . . . , X n − 1 might not b e directly observable b y th e n -th agent b ecause of various observational restrictions. Therefo re, the so cial observations obtai ned b y the n -th no de are represe nted by G n ∈ G n , which can b e a random scalar, vecto r, matrix o r other ma thematical object. S ome cases of int erest are: (i) T he k p revious decisions: G n = ( X n − k +1 , . . . , X n − 1 ) . (ii) The average value of the the previous decisions: G n = 1 n − 1 P n − 1 k =1 X k . (iii) The decisions of a gents connected by an Erdos-Renyi sto chastic netw o rk with pa rameter ξ ∈ [0 , 1] , i .e. G n = ( Z 1 , . . . , Z n − 1 ) ∈ { 0 , 1 , e } n − 1 , where Z k = ( X k with probabilit y ξ , e with probabilit y 1 − ξ . (1) Please note that in the la st example the Erdos-Renyi mo del has only b een used as an illust rative example, and it can b e easily generalized to consider the t op ology of an y s to chastic netw o rk of i nterest. In this w o rk we study t he so cial dynamics based on the p rop erties of the transi tion proba- bility from states g ′ ∈ G n − 1 to g ∈ G n , a s given by the conditional probabilities β n w ( g | x n , g ′ ) := P w G n = g | X n − 1 = x n − 1 , G n − 1 = g ′ , (2) where x n ∈ { 0 , 1 } . W e also assu me t hat the so cial dynamics is causal, meaning tha t G n is conditionally i ndep endent of S m given W for all m ≥ n . 2.2 The net w ork op erator and th e adv ersary The netw ork is managed b y a net w o rk op erator, who is a n external agent tha t uses the netw o rk as a to ol to build an estimate of W . The netw ork operator is opp osed b y a n adversa ry , whose goal is to disrupt the inference capabiliti es of the net w o rk. F o r this aim, the adversa ry controls a group of a uthenticated Byzanti ne no des wi thout b eing noticed b y the netw o rk op erator, which have b een captured b y malw are through cyb er/wireless means , o r by physical subs titution. The overall p erformance of a net w o rk of N no des is defined b y the accuracy of the i nference of the N -th no de, which is the la st one in the decision sequence. As the d ecision sequence is generated randomly b y the net w o rk op erato r, every no de of the net w o rk is equally lik ely to b e at the end of the decision sequence. It is f urther assumed that the a dversa ry has no kno wledge of the decisi on sequence, as it can b e chosen at run-time and changed regularly . As the adversary h as no reason fo r capturing any pa rticular no de in the netw ork , it is hence reasonable to assume that the adversary captures no des randomly . T herefo re, the Byz antine no des a re considered to b e unifo rmly distributed over the net w o rk. F o r simplicity , we mo del the strength of the attack with a single pa rameter p b , which co rresp onds to the p robability of a no de of b eing comp romised 4 . M o reover, we assume that the capture pro babi lity do es not dep end on W 5 . Hence, the numb er of Byz antine no des, denoted b y N ∗ , is a Bi nomial random variable with E { N ∗ } = p b N . Due to the l a w of l a rge 4 This attack mo del as sumes implicitly that the ca pture of each no de is an independent even t. Extensio ns considering cyb e r -infection propagation prop er ties are poss ible (c.f. [69]), being left for future studies. 5 If the capture r atio would b e higher when W = 1, then detecting Byzantine nodes would provide additional evidence to detect attacks. As this w ould go ag ainst the adversary’s interest, we discard this p oss ibilit y . 6 numb ers, N ∗ ≈ p b N fo r la rge net w o rks; and hence, p b is also the ra tio of expected B yzantin e no des i n the net w o rk, which i s the tra ditional metric fo r atta ck strength used in the li terature. F o r enabling th e data processing and fo rwa rding, th e net w ork op erato r defines a strategy , i.e. a data fusi on scheme given b y a collection of (p ossi bly sto chastic) functions { π n } ∞ n =1 such that π n : S × G n → { 0 , 1 } fo r a ll n ∈ N . On the other hand, th e adversa ry can freely set the values of t he binary signals transmi tted b y Byzantine no des. This is modeled b y a random function C : { 0 , 1 } → { 0 , 1 } that co rrupts the no de’s broadcasted s ignal. Therefo re, the broadcasted signal of the n -th n o de is given by X n = ( C ( π n ( S n , G n )) with p robabili t y p b , and π n ( S n , G n ) otherwise. (3) F urthermo re, as b roadcasted signals are binary , the co rruption function C ( · ) can b e charac- terized b y the conditional p robabilit ies c 0 | 0 and c 0 | 1 , where c i | j = P { C ( π ) = i | π = j } . The rest of t his w o rk fo cuses on the cas e in whi ch the net wo rk op erato r can deduce the co rruption function and can estimate the capture risk p b . The average netw ork miss-detection and fa lse alarm rates for an att ack of intensity p b a re defined a s P { MD ; p b } := P 1 { π N ( S N , G N ) = 0 } , and (4) P { F A ; p b } := P 0 { π N ( S N , G N ) = 1 } , (5) resp ectively (note that p b implicitly affects the dis tribution of G N ). The case in which these quantities are unkno wn can b e addressed usin g the current fra mew o rk with a min-max ana lysis, which i s left fo r future studi es. 2.3 Problem statemen t Our goal is to develop a resil ient strategy , in order to p rovide a reliabl e estimation of W even under a significant numb er of un identified Byzantine no des. No te tha t in most surveil lance applications miss-detections are mo re i mp o rtant than false al a rms, b eing di fficult to estimate the cost of the w o rst-case scena rio. Therefo re, the average net w o rk p erfo rmance is evalua ted follo wing the Neyman-Pea rs on criteria, by setting an allo wable false alarm rate α and fo cusing on reducing the miss -detection rate [70]. By denoting b y P the set of all strategies, we l o ok to the follo wing optimiz ation p roblem: minimize { π n } ∞ n =1 ∈P P { MD ; p b } subject to P { FP ; p b } ≤ α. (6) Ho w ever, findi ng an optimal solution is a fo rmidable challenge, even fo r the simple case of net w o rks with sta rt top ology and no Byza ntine atta cks (see [30, 71] and references therein). Therefo re, our aim is to develop a sub-optimal strategy that enables resilience, while b eing suitable fo r implementation in senso r no des with li mited computational p o we r. 3 So cial learning as a data aggre gation scheme This section d escrib es our proposed data fusion scheme, a nd expla ins its functions against top ology-a w are data fa lsification atta cks. In the s equel, Section 3.1 describ es a nd analyses the data fusion rule, then Section 3.2 derives basi c properties of it stati stics, and finall y Section 3.3 p resents a practical al go rithm fo r its implementation. 7 3.1 Data fusion rule Let us assume tha t each senso r no de is a rational agent, who tries t o maximizes the pro fit of an inference within a so cial net wo rk. Ra tional agents follo w Ba yesian strategies 6 , which can b e elegantly describ ed by the f ollo wing decision rul e [70, Ch. 2]: P { W = 1 | S n , G n } P { W = 0 | S n , G n } π n =0 ≶ π n =1 u (0 , 0) − u (1 , 0) u (1 , 1) − u (0 , 1) . (7) Ab ove, u ( x, w ) is a cost assigned to the decision X n = x when W = w , which can b e engineered in o rder to match the relevance of miss-detections and fal se alarms [70]. Let us find a simpler expression fo r th e decision rule (7) . Due to t he causality constrain (c.f. Section 2.1 ), G n can only b e i nfluenced by S 1 , . . . , S n − 1 , and therefo re is conditionall y indep endent of S n given W . U sing t his conditional indep endence condition, one can find that P { W = 1 | S n , G n } P { W = 0 | S n , G n } = e Λ S ( S n )+Λ G n ( G n ) , (8) where Λ G n ( G n ) is the log-like lih o o d ratio of G n . Then, usi ng (8) one can re-write (7) as Λ S ( S n ) + Λ G n ( G n ) π n =0 ≶ π n =1 τ 0 , (9) where τ 0 = log P { W = 0 } P { W = 1 } + log u (0 , 0) − u (1 , 0) u (1 , 1) − u (0 , 1) . In simple wo rds , (10) states how the the n -th no de should fuse the p rivate and social kno wledge: the evidence is p rovided b y the co rresp onding log- lik eliho o d terms, which a re then s imply added and then compa red against a fixed threshold 7 . F urther understand ing of the ab ove decisi on rule can b e at tained by st udying it from the p oint of vi ew of communication theo ry [58]. We first note that the decision is mad e not over the full raw signal S n but over the “decision signal” Λ S ( S n ) , which is a processed version of it. Interestingly , this processing might serve for d imensionality reduction, as even though S n can b e a matrix o r a high-dimensional vecto r Λ S ( S n ) is alw ays a single numb er. D ue to their construction a nd the underlying assumpti ons over S n (c.f. Section 2.1), the variables Λ S ( S n ) a re identically distribut ed and conditionally indep endent given W = w . More over, b y intro ducing the shorthand notation τ n ( G n ) = τ 0 − Λ G n ( G n ) , one can re-write (10) as Λ S ( S n ) π n =0 ≶ π n =1 τ n ( G n ) . (10) Therefo re, the decision is made by compa ring the decision signal with a decision threshold τ n . Note that this rep resents a compa rison b et w een the sensed data , summa rised b y Λ S ( S n ) , and the so cial information ca rried b y τ n ( G n ) . 3.2 Decision statistics Let us find expressions fo r the p robabiliti es of the actions of the n -th a gent, first f o cusing on the case n = 1 . Note t hat P w { π 1 ( S 1 ) = 0 } = P w { Λ S ( S 1 ) < τ 0 } = F Λ w ( τ 0 ) (11) 6 Although B ay esian mo dels are elegant a nd tr actable, they a s sume ag e nts act a lwa ys r ationally [72] and mak e strong assumptions on the knowledge ag e nt s hav e abo ut poster ior probabilities [49]. How ever, Bay esian models provide a n imp ortant b enchmark, not necessa rily due to their accuracy but be cause they give an impor ta nt reference point with which other models can b e compar ed [35]. 7 As the prio r distribution of W is usually unknown, τ 0 is a free parameter of the scheme. F ollowing the discussion in Section 2.3, the net work oper ator shall sele ct the lowest v alue of τ that satisfies the require d false alarm rate given by the Neyman-Pearson criteria. 8 where F Λ w ( · ) is the c.d.f. of Λ S conditioned on W = w . Then, considering the p ossibility that the fi rst no de could b e a Byzanti ne, one can sho w that P w { X 1 = 0 } = p b P w { X 1 = 0 | Byza ntine } + (1 − p b ) P w { X 1 = 0 | not a B yzantin e } = p b ( c 0 | 0 F Λ w ( τ 0 ) + c 0 | 1 [1 − F Λ w ( τ 0 )]) + (1 − p b ) F Λ w ( τ 0 ) (12) = z 0 + z 1 F Λ w ( τ 0 ) , (13) where we a re intro ducing z 0 := p b c 0 | 1 and z 1 := 1 − p b (1 − c 0 | 0 + c 0 | 1 ) as sh o rt-hand notat ion, which a re non-negative constants that summa rize the strength of the adversa ry . In pa rticular, when the adv ersa ry is p o we rless then z 0 = 0 and z 1 = 1 and hence P w { π 1 ( S 1 ) = 0 } = P w { X 1 = 0 } . By considering the n -th no de, one can find that P w { π n ( S n , G n ) = 0 | G n = g n } = Z S P w { π n ( s n , g n ) = 0 | S n = s } µ w ( s ) d s = Z S 1 { π n ( g n , s ) = 0 } µ w ( s ) d s (14) = P w { Λ S ( s ) < τ n ( g n ) } (1 5) = F Λ w ( τ n ( g n )) . (16) The first equality is a consequence of th e fact that S n is conditi onally indep endent of G n given W = w , while the second equality is a consequence that X n can b e expre ssed as a deterministic f unction of G n and S n , and hence b ecomes conditi onally indep endent of W . Note that (16) sho ws that τ n is a sufficient statist ic fo r p redicting X n with resp ect to G n . Note that F Λ w ( x ) can b e directly computed from the st atistics of t he signal dis tribution (its p rop erties a re explo red in Ap p endix A ). Mo reover, using (16) and follo wing a s imilar derivation as in (12) , one can conclude that P w { X n = 0 | G n = g n } = z 0 + z 1 F Λ w ( τ n ( g n )) . (17) Let us now study the statistics of G n . By using the definition of the transition co efficients β n w ( g n +1 | x n , g n ) , one can find that P w G n +1 = g n +1 = X g n ∈G n X x n ∈{ 0 , 1 } β n w ( g n +1 | x n , g n ) P w { X n = x n , G n = g n } . (18) Note that, using the ab ove derivations, th e terms P w { X n = x n , G n = g n } can b e further exp ressed as P w { X n = x n , G n = g n } = P w { X n = x n | G n = g n } P w { G n = g n } (19) = λ ( z 0 + z 1 F Λ w ( τ n ( g n )) , x n ) P w { G n = g n } , (20) where λ ( p, x ) = x (1 − p ) + (1 − x ) p . T herefo re, a closed fo rm exp ression can b e found for (18) recursively over G n . 3.3 An algorithm for computing the so c ial log-lik eliho o d The main challenge fo r implementing (10 ) as a data p ro cessing metho d in a senso r no de is to have an efficient a lgo rithm f o r computing τ n ( g n ) . Leveraging t he ab ove derivati ons, we develop Al go rithm 1 as a it erative procedure fo r computing τ n . In many cases of interest the algo rithm’s complexity scales gracefully . Fo r the particula r case of nodes with memo ry of length k (i.e. G n = ( X n − k − 1 , . . . , X n − 1 ) ), the a lgo rithmic complexit y of Algo rithm 1 is O (2 k N ) , and therefo re gro ws linearly with the siz e of the net w o rk, while b eing l imited in th e values of k that can consider. In general, the algo rithm complexit y 9 Algorithm 1 Computation of the decision threshold 1: function Compute T au ( N , F Λ 0 ( · ) , F Λ 1 ( · ) , β n w ( ·|· , · ) , τ 0 , z 0 , z 1 ) 2: τ 1 = τ 0 3: for x 1 ∈ { 0 , 1 } do 4: P 0 { X 1 = x 1 , G 1 = 0 } = λ ( z 0 + z 1 F Λ 0 ( τ 1 ) , x 1 ) 5: P 1 { X 1 = x 1 , G 1 = 0 } = λ ( z 0 + z 1 F Λ 1 ( τ 1 ) , x 1 ) 6: for n = 1 , . . . , N − 1 do 7: for ∀ g ∈ G n +1 do 8: P 0 { G n +1 = g } = P g n ∈G n P x n = { 0 , 1 } β n w ( g n +1 | x n , g n ) P 0 { X n = x n , G n = g n } 9: P 1 { G n +1 = g } = P g n ∈G n P x n = { 0 , 1 } β n w ( g n +1 | x n , g n ) P 1 { X n = x n , G n = g n } 10: Λ G n ( g ) = log P 1 { G n = g } P 0 { G n = g } 11: τ n ( g ) = ν + η − Λ G n ( g ) 12: for x n +1 ∈ { 0 , 1 } do 13: P 0 { X n +1 = x n +1 , G n +1 = g } = λ ( z 0 + z 1 F Λ 0 ( τ n ( g n )) , x n +1 ) P 0 { G n +1 = g } 14: P 1 { X n +1 = x n +1 , G n +1 = g } = λ ( z 0 + z 1 F Λ 1 ( τ n ( g n )) , x n +1 ) P 1 { G n +1 = g } 15: return τ N ( · ) scales linea rly with N a s long as the cardinalit y of G n a re b ounded, o r if a significant p ortion of the terms β n w ( g n +1 | x n , g n ) are zero. The input s that drive Algo rithm 1 can b e classi fied in t w o groups. First, the terms N , F Λ 0 ( · ) , F Λ 1 ( · ) , β n w ( ·|· , · ) are p rop erties of th e net wo rk (p osi tion of the no de wi thin the deci- sion sequence, senso r statistics and socia l observabi lity , resp ectively) tha t the net w o rk op erato r could measure. On the other hand, τ 0 , z 0 , z 1 a re properties of the ad versa ry profile tha t d e- p end on the p rio r stati stics of W , p b and the co rruption function defined b y c 0 | 0 and c 0 | 1 (c.f. Section 2.2). In most scena rios the kno wledge of the net w o rk controller ab out th ese q uantities is li mited, as attacks are ra re a nd might follow unp redictable pa tters. Limited kno wledge can still b e exploited using e.g. Bay esian estimation techniques [73]. If n o kno wledge is avail able fo r the netw ork controller, then these quantities can b e considered free pa rameters of the strategy tha t span a range of alternative bal ances b etw een miss-detections and f alse p osit ives, i.e. a receiver op erating characteristic (ROC) space. 4 Information cascade The term “so cial lea rning” refers to the fact tha t π n ( S n , G n ) b ecomes a b etter p redicto r of W as n gro ws, a nd hence larg er net w o rks tend to d evelop a mo re accurate inference. Ho w ever, as the numb er of sha red signal s grows, the co rresp onding “so cial p ressure” can make no des to igno re their individua l measurements t o blindl y f ollo w the dominant choice, triggering a cascade of homogeneous b ehaviour. It is our in terest to clarify the role of the so cial p ressure in the decision making of the agents involved in a so cial net w o rk, as info rmation cascades can intro duce severe limi tations in the a symptotic p erformance of so cial l ea rning [44]. Mo reover, an adversary can leverage the i nfo rmation cascade phenomenon. In effect, if the numb er of Byzantine nodes N ∗ is la rge enough then a misleading info rmation cascade can b e triggered almost surely , making the lea rning p ro cess to fail. Ho w ever, if N ∗ is not enough then the netw o rk ma y undo the p o ol of wrong opinions and end up triggering a co rrect cascade. In t he sequel, the effect of inf o rmation cascades is firs t studied in indivi dual no des in Section 4.1. Then, the p ropagation pro p erties of cascades is explore d i n Section 4.2. 10 4.1 Lo c al information cascades In general, the decision π n ( S n , G n ) is made bas ed in the evidence provided by b oth S n and G n . A lo cal cascade tak es pl ace in the n -th agent when t he info rmation convey ed b y S n is igno red in the decision-making p ro cess due to a dominant influence of G n . We use the t erm “lo cal” to emphasize tha t this event is related to the data fusion of an individual agent. This idea is formalized i n t he following defini tion us ing the notion of conditional mutual info rmation [74], denoted as I ( · ; ·|· ) . Definition 1. The so cial information g n ∈ G n gener ates a lo cal information cascade for the n - th agent i f I ( π n ; S n | G n = g n ) = 0 . The ab ove condition summarizes tw o p ossibilit ies: either pi n is a deterministic function of G n and hence there is no va riab ility in π n after G n has b een determined, o r there is stil l va riabi lity (i.e. π n is a sto chastic strategy) b ut it is conditionally indep endent of S n . In b oth cases, the ab ove formulation highli ghts the f act that t he decision π n contains no info rmati on coming f rom S n 8 . Lemma 1. The variables G n → τ n → π n form a Markov Chain (i.e. τ n is a sufficient statistic of G n for pr e dicting the de cision π n ). Pr o of. Using (16) one can fin d that P w { π n | τ n , G n } = λ ( F Λ w ( τ n ) , X n ) = P w { π n | τ n } , and therefore the cond itional ind ep enden cy of π n and G n giv en τ n is clear. Let us now introduce the notation U s = ess sup s ∈S Λ S ( S n = s ) and L s = ess inf s ∈S Λ S ( S n = s ) fo r the essenti al sup ermum an d infimum of Λ S ( S n ) , b eing the si gnals within S that most strongly supp ort the hyp othesis { W = 1 } over { W = 0 } and viceversa 9 . If one of these quantities di verge, this w ould imply tha t there a re si gnals s ∈ S tha t p rovide overwhelming evidence in favour of one of the competing hyp otheses. If b oth a re finite then the agents a re said to have b ounded b eli efs [44]. As senso ry si gnals of electronic devices a re ultimately p ro cessed digitall y , the numb er of different signal s that an agent can obtain are finit e and hence their suprem um is alw ays finite. Therefo re, in the sequel we asume that b oth L s and U s a re finite. Using these notions, the follo wing pro p osition provides a cha racterizati on fo r lo cal info rmation cascades. Prop osition 1. The so cial information g n ∈ G n triggers a lo c al i nf ormation c asc ade if and only if the agents have b ounde d b eliefs and τ n ( g n ) / ∈ [ L s , U s ] . Pr o of. Let us assume that the agen ts ha v e b oun ded b eliefs. F rom the definition of F Λ w , whic h is a cumulat ive densit y fu nction, it is clear that if τ n < L s then F Λ 0 ( τ n ) = F Λ 1 ( τ n ) = 0, while if τ n > U s then F Λ 0 ( τ n ) = F Λ 1 ( τ n ) = 1. Therefore, if τ n ( g n ) / ∈ [ L s , U s ] then, according to (16), it determines π n almost su rely , making π n and S n conditionally ind e- p end en t. T o prov e th e conv erse by contrapositiv e, let us assum e that L s < τ n ( g n ) < U s . Usin g again (16) and the d efi nition of U s and L s , one can conclude that th is implies that 0 < P w { π n = 0 | G n } < 1 for b oth w ∈ { 0 , 1 } . This, in tur n, implies that the sets S 0 ( τ ) = { s ∈ S | Λ S ( s ) < τ n ( G n } and S 1 ( τ ) = S − S 0 b oth h a v e p ositiv e pr ob ab ility under µ 0 and µ 1 , whic h in turn implies the existence of conditional interdep endency b et w een π n and S n in this case. 8 Recall tha t S n and G n are conditionally indep endent given W = w (c.f. Section 3.1), and hence there cannot be redundan t information ab out W that is co nvey ed by S n and also G n . F or a mor e detailed discussion ab out redundant information c.f. [75]. 9 The es sential s upremum is the smallest upp er b o und over Λ S ( S n ) that holds almost s urely , b eing the natural measure-theor etic extension of the notion of s upremum [76]. 11 Intutively , Prop osition 1 sho ws that a lo cal information cascade happ ens when the so cial info rmation goes ab ove the most i nfo rmative signal that could b e sensed. Some consequences of thi s result a re explo red in the next section. 4.2 So c ial information dynamics and global cascades It i s of great interest to pre dict when a lo cal information cascade could p ropagate across the net w o rk, dis rupting the collective b ehaviour and hence affecting t he netw ork p erfo rmance. T he follo wing definition capt ures how, during a “global inform ati on cascade”, the share d signals X n do not convey a nymo re i nfo rmation from t he co rresp onding sensor signals. Definition 2. The so cial informatio n g n ∈ G n triggers a global information cascade if I ( X m : S m | G n = g n ) = 0 holds for al l m ≥ n . A global info rmation cascade is a succession of lo cal info rmation cascades. As Prop osition 1 sho w ed t hat agents are free from lo cal cascades as long as τ n ∈ [ L s , U s ] , one can guess that global cascades are related to the dynamics of τ n . These dynamics are determined b y the transitions of G n , which follows the b ehaviour dictated b y the tra nsition co efficients β n w ( ·|· , · ) . T o further study the so cial info rmation dynamics we intro du ce the follo wing definitions. Definition 3. The c ol le ction { G n } ∞ n =1 is said to have: 1. str ongly consistent tr ansitions if, for any W = w , g ∈ G n and g ′ ∈ G n − 1 , β n w ( g | 1 , g ′ ) > 0 implies τ n ( g ) ≤ τ n − 1 ( g ′ ) , while if β n w ( g | 0 , g ′ ) > 0 implies τ n ( g ) ≥ τ n − 1 ( g ′ ) . 2. weakly consisten t transitions if, f or al l g ∈ G n and g ′ ∈ G n − 1 , τ n − 1 ( g ′ ) ≤ L s and P w { G n = g | G n − 1 = g ′ } > 0 implies τ n ( g ) ≤ L s , while τ n − 1 ( g ′ ) ≥ U s and P w { G n = g | G n − 1 = g ′ } > 0 implies τ n ( g ) ≥ U s 10 . Intuitively , strong consistency mean that the decision threshold evolves monotonically with resp ect to the bro adcast ed signals X n . Corre sp ondingly , weak consistency implies that τ n cannot return into [ L S , U S ] after going b ey ond it . Mo reover, the adjectives “strong” and “w eak” reflect the fact th at w eak consistency only takes place outside the b oundaries of the signal lik eliho o d, while the strong consistency affects all the decision s pace. Mo reover, s trong consistent transitions imply w eak consisten transitions when there a re no Byzanti ne no des, as sho wn in the next Lemma 11 . Lemma 2. Str ong c onsistent tr ansitions satisfy the we ak c onsistency c ondition if p b = 0 . Pr o of. See App end ix B. W e sho w next that if t he evolution of G n b ecomes deterministic and 1-1 after l eaving the interval [ L s , U s ] (hence forth called w eakly invertible transitions ), then it satisfies the w eak consistency condition. Lemma 3. We ekly invertible tr ansitions i mply the we akly c onsistency c ondition. Pr o of. See App end ix C. No w w e present t he main result of this section, which i s t he cha racterization of inf o rmation cascades f o r the case of so cial information that follo ws weakly consistent transitions. Theorem 1. If the so cial information ha ve we akly c onsistent tr ansitions, then a glob al information c asc ade is trigger e d by e ach lo c al information c asc ade. 10 Note that the condition P w { G n = g | G n − 1 = g ′ } > 0 is eq uiv a lent to ask either β n w ( g , | 0 , g ′ ) or β n w ( g , | 1 , g ′ ) to be strictly positive. 11 It is p ossible to build examples where weak co nsistency does not follow stro ng c o nsistency when p b > 0. 12 Pr o of. Let us consider g 0 ∈ G n suc h that it pro duce a local cascade in the n -th no de. T h en, due to Prop osition 1, th is implies that τ n ( g ) / ∈ [ L s , U s ] almost surely . This, com bined with the weakl y consistency assumption, implies that τ n +1 ( G n +1 ) / ∈ [ L s , U s ] almost s urely . A second application of Prop osition 1 mak e us to conclude that P w { π = 0 | G n +1 } is therefore equal to 0 o 1. T his, in turn , guaran tees that I ( π n +1 : S n +1 | G n = g ) = 0) almost sur ely , sho wing that the ( n + 1)-th no de exp er iences a lo cal information cascade b ecause of G n = g 0 . Finally , it is direct to see that a recur siv e application of the ab ov e argumen t allo ws one to pro ve th at I ( π n + m : S n + m | G n = g ) = 0) for all m ≥ 0, confirming the existence of a global cascade. This theo rem has a numb er of imp o rtant conseque nces. Firstly , i t pro vides an intuiti ve geometrical description ab out the nature of global cascades fo r net w o rks wi th w eak consistency . One can imagine the evolution of τ n ( G n ) as function of n as a rand om walk withi n the interval [ L s , U s ] . Because of the w eakly consist ency conditi on, if the random w alk step out of the interval, it will never come back. Mo reover, as consequence of this theo rem, the stepping out of [ L s , U s ] is a necessary and sufficient condition to trigger a global i nfo rmation cascad e over the netw o rk. Also, note that in the case where G n = X n (i.e. each no de see every p revious decision) is direct to pro ve that G n has w eakly invertible transitions. Therefo re, Theo rem 1 i s a gen- eralizati on of Theo rem 1 of [58], now b eing valid fo r the case where there are a f raction of Bizanti ne no des within the net w o rk. 5 Pro of of conc ept This section i llustrates the main results obtain ed in Sections 3 a nd 4 in a simple scena rio. In the sequel, first S ection 5.1 describ es t he scena rio, and th en Section 5.2 discusses numerical simulations. 5.1 Scenario description Let us consider a sensor netw ork that has surveillance dut ies over a sensit ive geographical are a. The sensitive a rea could co rresp ond to a facto ry , a drink abl e w ater container o r a w arzone, whose k ey variables need to b e sup ervised. The tas k of the senso r net w o rk is, through the observation of t hese va riabl es, to detect the events { W = 1 } and { W = 0 } th at co rresp ond to the p resence o r absence of an a ttack to the surveilled a rea, resp ectively . No kno wledge ab out of the p rio r dis tribution of W is a ssumed. W e consider no des that ha ve b een deplo y ed ra ndomly over the sensitive are a, a nd hence their l o cation follo w a P oisson P oint p ro cess (PPP). T he rati o of the area of interest that falls within the range of each sensor is d enoted b y r . If attacks o ccur unifo rmly over the surveilled a rea, then r is also the p robabili t y of an attack ta king place under the coverage a rea of a particula r senso r is. Note that, due to the l imited sensin g range, the miss-detection rate of indi vidual no des i s roughly equal t o 1 − r . As r is usua lly a small numb er ( 5% in our simulations), t his impl ies that without colla b o rati on each no de is extremely unreli able. Each no d e measures its environment using a digital s enso r of m levels dynamical range (i.e. S n ∈ { 0 , 1 , . . . , m − 1 } ). Under the ab sence of a n a ttack, the measured si gnal is assumed to b e no rmally distri buted with a pa rticular mean v alue and va riance. Fo r simplicity of the ana lysis, w e assume that S n conditioned i n { W = 0 } distributes follo wing a binomial distrib ution of pa rameters ( m, q ) , i .e. P 0 { S n = s n } = m s n q s n (1 − q ) m − s n := f ( s n ; m, q ) (21) which b ecause of the central limi t theo rem app ro ximat es a Gaussi an variable when m is relatively la rge. Moreo ver, it is assumed tha t the sensor dynamical range is ad apted to match 13 5 10 15 0 . 05 0 . 1 0 . 15 0 . 2 Digital sensor lev els Probabilit y P 0 { S n = s } P 1 { S n = s } Figure 1: Probabilit y distribution f or a digital sensor o f m = 16 lev els, conditioned on the ev en ts { W = 0 } and { W = 1 } . the mean va lue on the low er third of the senso r dynamical ra nge, i.e. E { S n | W = 0 } = m/ 3 . This na turally imp oses the requirement q = 1 / 3 . F ollo wing standa rd sta tistical app roaches, it is further assumed that the s enso rs control the environment lo oking fo r events where the measured data is significant ly h igh, i.e. when it is la rger than mean value in mo re than t w o standard deviations. This co rresp onds e.g. when a sp ecific chemical compound trespasses safe concentration values o r when to o much movement has b een detected over a given time window (see e.g. [77]). U sing the f act that V ar { S n } = mq (1 − q ) , this gives a threshold T = E { S n } + 2 p V ar { S n } = np + 2 p nq (1 − q ) . Therefo re, it i s as sumed that an attack is related to t he event of S n b eing unifo rmly dist ributed in [ T , m ] . Th erefo re, one fi nds that P 1 { S n = s n } =(1 − r ) P 1 { S n = s n | attack o ut o f range } + r P 1 { S n = s n | attack i n rang e } =(1 − r ) f ( s n ; m, q ) + r H ( s n − T ) m − T , (22) where H ( x ) is the discrete Heavisi de (step) function given b y H ( x ) = ( 1 if x ≥ 0 0 in other case. (23) In summary , S n conditioned on { W = 1 } is mo deled as a mi xture mo del b et we en a Binomial and a tru ncated unifo rm dist ribution, where the relative w eight b et w een t hem is determined b y r (c.f. Figure 1). Fi nally , using (21) and (21) , the l og-lik eliho o d f unction of the signal S n can b e determined as (see Figure 2) Λ S n ( s n ) = log P 1 { S n = s n } P 0 { S n = s n } = log (1 − r ) + r H ( s n − T ) ( m − T ) f ( s n ; m, q ) . (24) W e fo cus on scenarios where a no de can overhea r t he tranmissi ons of a ll the other no des. Ho w ever, we consider the case where the listening p erio d is restri cted 12 . W e th erefo re st udy the case where the so cial i nfo rmation gathered by the n -th no de is G n = ( X n − k − 1 , . . . , X n − 1 ) if n > k . Here k is a design parameter, whose impact in the net w ork p erfo rmance is studied in the next section. 5.2 Discussion W e analysed the p erfo rmance of netw o rks of N = 300 senso r no des whose s enso rs can monitor r = 5% of the ta rget area. Usi ng t he definition given in (4) and (5) , combined wi th (16 ) , 12 It is well-kno wn tha t the wireless radios of small sensor no des consume a similar amount of energy while transmitting or receiving data, and hence r educing ov erhear ing p erio ds is k ey for attaining energy efficiency and hence long netw ork lifetime [6 0]. 14 5 10 15 5 10 Digital sensor level Lik eliho o d Λ S n ( s ) Figure 2: L o g-lik eliho o d of a digital signal of m = 16 lev els with resp ect to the v ariable W . miss-detection and false alarm rates w ere computed as P { MD } = X g ∈G n F Λ 1 ( τ n ( g )) P 1 { G n = g } and (25) P { F A } = X g ∈G n (1 − F Λ 0 ( τ n ( g ))) P 0 { G n = g } , (26) where the t erms P w { G n = g } are computed using A lgo rithm 1 (c.f. Section 3.3. In o rder t o favour the reduction of miss-detections over fa lse ala rms, τ 0 = 0 is chosen as is the low est value tha t still allows a non-trivial inf erence process 13 . We consider an upp er b ound over the tolerable false al a rm ra te of 5% . Simulati ons demonstrate tha t the proposed scheme enables strong net w o rk resilience in this scenario, all o wing the senso r netw ork to maintain a lo w miss-detection rate even in the p resence of an imp o rtant numb er of Byzantine no des (see Figure 3). Please recall that if a traditi onal distributed detection scheme ba sed on centrali sed decision is used, a top ology- a w are attack er can cause a miss-detection rate of 100% by just compro mising the few no des that p erfo rm data aggregation (i.e. th e F C(s)). Fi gure 3 s ho ws that no des tha t indivi dually w ould have a miss-detection rate of 95% can imp rove up t o a round 10% even when 30% of the no des are under t he control of the a ttack er. Therefo re, by making a ll the n o des t o agregate data, the net w o rk can overcome the infl uence of B izanti ne no des and hence even when some no des have b een comp romised the rest of the net wo rk can and generate a co rrect inference. Please note that, fo r the case il lustrated b y F igure 3, when there are Byzanti ne n o des the miss-detection rate imp roves unt il the net w o rk size reaches N = 500 , achieving a p erformance of ≈ 10 − 12 (not sho wn in the Figure). This result has t w o imp o rtant implications. First, this confirms the p rediction of Theo rem 1 that if the signal log-lik eliho o d is b ounded then inf o rma- tion cascades are eventuall y dominant, hence stoping the learning process of the net w o rk (fo r a mo re detailed di scussion ab out t his is sue please c.f. [58]). Secondly , this result stress a k ey difference of our approach with resp ect to the exis tent literat ure ab out i nfo rmation cascad es: even if info rmation cascades become dominant an d hence p erfect so cial l ea rning cannot b e achieved by b ounded signal s, the a chieved p erformance can still b e very high and hence useful in a p ractical inf o rmation-p ro cessing setup . The netw ork resilience provided b y our scheme is influenced by the senso r dynamical ra nge, m , as a higher sensor resolution i s lik ely to p rovide mo re discriminative p o w er. Our results sho w three sharply distinct regimes (see Figure 4). First , if m is to o small ( m ≤ 4 ) the net w o rk p erfo rmance is very p o o r, irresp ective of the numb er of Byza ntine no des. Secondly , if 8 ≤ m ≤ 32 the miss-detection rate without Byz antine no des is app ro x. 10% (cf. Figure 4) and is exp onentially degraded b y the p resence of By zantine no des. Fi nally , if m ≥ 64 then the p erfo rmance under no B yzantine no des is very high, and i s degraded sup er-exp onentially 13 Sim ulations show ed that if τ < 0 then X n = 1 for all n ∈ N independently of the v alue of W , trigger ing a premature information ca scade. 15 0 20 40 60 80 100 120 140 16 0 180 200 10 − 4 10 − 3 10 − 2 10 − 1 10 0 Agen t Rate N ∗ / N = 0 N ∗ / N = 0 . 1 N ∗ / N = 0 . 3 N ∗ / N = 0 . 5 Figure 3: Performance for the inference of eac h no de for v arious attac k in tensities, given b y the a v erage ratio of Byzantine no des N ∗ / N = p b . Agents o v erhear t he previous k = 4 bro adcasted signals, and use sensors with dynamical range of n = 64. b y the p resence of Byzanti ne no des. Interestingly , the p oint at which the miss-detection rate of this regime go es ab ove 10 − 1 is at N ∗ / N = 1 / 3 , having some resemblance with the well- kno wn 1 / 3 threshold of the Byz antine generals p roblem [14]. A lso, it is intriguing the fact that differences b et w een 8 and 32 levels in the dynamical range gives practically no p erfo rmance b enefits. 0 0 . 1 0 . 2 0 . 3 0 . 4 0 . 5 0 . 6 0 . 7 0 . 8 0 . 9 1 10 − 8 10 − 7 10 − 6 10 − 5 10 − 4 10 − 3 10 − 2 10 − 1 10 0 A ttack in tensity ( N ∗ / N ) Miss-detection rate m = 2 m = 16 m = 32 m = 64 m = 256 Figure 4 : Effect of the sensor dynamical range ov er the net w ork resilience. Our results also sho w t he effects of the memo ry size, k , show ing that larg er va lues of k p rovides great b enefits for the net wo rk resilience (see Figure 5). In effect, b y p erfo rming an optimal bay esian inference over 8 b roadcasted signals the net w o rk mis s-detection rate remains b ellow 10% up to an attack intensity of 50% of Byz antine no des. Unfo rtunately , the computation a nd sto rage requirements of Algo rithm 1 gro w exp onential ly with k , and hence usi ng memo ries b eyond k = 10 is not p ractical fo r resource-limited senso r net w o rks. Overcoming thi s li mitation is an relevant future li ne of investigation. 16 0 0 . 1 0 . 2 0 . 3 0 . 4 0 . 5 0 . 6 0 . 7 0 . 8 0 . 9 1 10 − 8 10 − 7 10 − 6 10 − 5 10 − 4 10 − 3 10 − 2 10 − 1 10 0 A ttack in tensity ( N ∗ / N ) Miss-detection rate k = 1 k = 2 k = 4 k = 6 k = 8 Figure 5: A larger no de memory , whic h allows to include more so cial signals into the inference pro cess, greatly improv es the net w ork resilience. 6 Conclus ions T radi tional approaches to data aggregation over i nfo rmation netw o rks are based on a strong division of l ab our, which discrimina tes b et we en sensing no des tha t merely sense and forw ard data, and fusion centers that monopoliz e all the p ro cessing and inference capa bilities. This generates a si ngle p oint of failure, whi ch is li k ely to b e exploited b y smart adversa ries whose interest is the disruption of the netw o rk capabili ties. This serious security thread can b e overcome by distri buting the d ecision making p ro cess across the netw ork using so cial learning principles. This appro ach a voids single p oints of failure b y generating a la rge numb er of no des from where aggregated data can b e a ccessed. In this pap er a s o cial lea rning data fusion scheme ha s b een p roposed, which is s uitable of b eing implemented i n devices with l imited computational capabili ties. W e sho w ed that i f the p rivate signals are b ounded then each lo cal info rmation cascades triggers a global cascade, extending p revious resul ts to t he case where a n adversa ry controles an numb er of B yzantine no des. This result is hi ghly relevant fo r senso r net wo rks, as digital senso rs a re intrinsically b ounded a nd hence satisf y the assumptions of these results. Ho w ever, contrasting with the literature, our appro ach do es not fo cus on the conditions that gua rantee p erfect asymptotical so cial learning (i.e. miss-detec tion and false a larm rates converging to zero), but if their limit i s sma ll enough fo r p ractical appl ications. Our results show that this is the case, even when limiting th e numb er of overheare d transmiss ions. Mo reover, our result s suggest that so cial learning principles can enable signifi cant resil ience of an info rmation net w o rk agai nst t op ology-a w are data f alsificati on atta cks, which can totally disable the detection cap abiliti es of traditional senso r net wo rks. Furthermo re, our result s illustrat e how the net w o rk resilience can p ersists even when the attack er has comp romised an imp o rtant numb er of no des. It is our hop e that these result s can motivate further explo rations on the interface b etw een distributed decision making, statistical inference and signal p ro cessing over technological and so cial net w o rks. 17 A Prop ert ies of F Λ w F o r simplicity let us consider the case of real-value s ignals, i .e. S n ∈ R . In this case, the c.d.f. of the signal l ik eliho o d is given by F Λ w ( y ) = Z S y d µ w (27) where S y = { x ∈ R | Λ s ( x ) ≤ y } . If Λ s is an increasing fun ction, then S y = { x ∈ R | x ≤ Λ − 1 s ( y ) } = ( −∞ , Λ − 1 s ( y )] and hence F Λ w ( y ) = Z Λ − 1 s ( y ) −∞ d µ w = H w (Λ − 1 s ( y )) , (28) where H w ( s ) is the cumulative densit y function (c.d.f.) of S n fo r W = w . Fo r the general case where Λ s is an arbitra ry (piece-wise continuous) functi on, then S y can b e expressed a s the uni on of interval s. Then ∪ ∞ j =1 [ a j ( y ) , b j ( y )] = S y (note that Λ s ( a j ( y )) = Λ s ( b k ( y )) = y ) and hence from (27) is clea r that F Λ w ( y ) = ∞ X j =1 Z b j ( y ) a j ( y ) d µ w = ∞ X j =1 [ H w ( b j ( y )) − H w ( a j ( y ))] . (29) B Pro of of Lemma 2 Pr o of. Lets assume that the pro cess G n has str on g consisten t transitions and consider g ′ ∈ G n − 1 suc h that τ n − 1 ( g ′ ) ≤ L s . Note that, under these cond itions F Λ w ( τ n − 1 ( g ′ )) = 0, and h en ce P w X n − 1 = 1 | G n − 1 = g ′ = 1 − z 0 − z 1 F Λ w ( τ n − 1 ( g ′ )) = 1 − p b c 0 | 1 = 0 (30) holds for an y w ∈ { 0 , 1 } . Moreo v er, this allo ws to fi nd that P w { G n = g | G n − 1 = g ′ } = X x n ∈{ 0 , 1 } β n w ( g | x n , g ′ ) P w X n − 1 = x n | G n − 1 = g ′ = β n w ( g | 1 , g ′ ) . (31) Therefore, d ue to the str on gly consisten t transition prop ert y , if P w { G n = g | G n − 1 = g ′ } = β n w ( g | 1 , g ′ ) > 0 then L s ≥ τ n − 1 ( g ′ ) ≥ τ n ( g ) , (32) pro ving the wea k consistent transition p rop erty . The pro of for the case of τ n − 1 ( g ′ ) ≥ U s is analogous. C Pro of of Lemma 3 Pr o of. Let us consider g 0 ∈ G n suc h that τ n ( g 0 ) / ∈ [ L s , U s ]. Then, due to the w eakly in ve rtible evol ution, f or eac h x ∈ { 0 , 1 } there exists g ( x ) ∈ G n +1 suc h that β n w ( g | x, g 0 ) = ( 1 if g = g ( x ) , 0 in other case. (33) Moreo v er, note that while the deterministic assump tion implies that the ev en t { G n = g 0 } could b e follo wed by either { G n +1 = g (0) } or { G n +1 = g (1) } , the 1-1 assumption requires 18 that g (0) = g (1). With this, note that Λ G n +1 ( g (0)) = log P 1 { G n +1 = g (0) } P 0 { G n +1 = g (0) } = log P g ′ ∈G n x ∈{ 0 , 1 } β n w ( g ( x ) | x, g ′ ) P 1 { X n = x, G n = g ′ } P g ′ ∈G n x ∈{ 0 , 1 } β n w ( g ( x ) | x, g ′ ) P 0 { X n = x, G n = g ′ } (34) = log P x ∈{ 0 , 1 } P 1 { X n = x | G n = g 0 } P 1 { G n = g 0 } P x ∈{ 0 , 1 } P 0 { X n = x | G n = g 0 } P 0 { G n = g 0 } (35) =Λ G n − 1 ( g 0 ) , (36) Ab o ve, (34) is a consequence of g (0) = g (1), wh ile (35) is b ecause of the 1-1 condition o v er the dynamic. Finally , to justify (36) let us first consider P w { X n = x | G n = g 0 } = λ ( z 0 + z 1 F Λ w ( τ n ( g 0 )) , x ) . (37) Because τ n ( g 0 ) / ∈ [ L s , U s ] then F Λ w ( τ n ( g 0 )) is either 0 or 1; in any case it do es not dep end s on W . Th is, in turn means that P 1 { X n = x | G n = g 0 } = P 0 { X n = x | G n = g 0 } , whic h explains ho w (36) is obtained. Please note that (36) shows that, once τ n lea v es [ L s , U s ], it k eeps a constan t v alue. This, in turn, sho ws that w eakly d eterministic transitions s atisfy the w eakly consistency condition. Ac kno wledge men ts F ernando R osas is s upp o rted b y the Europ ean Union’s H2020 resea rch and innovation p ro- gramme, un der the Marie Sk lo do wsk a-Curie grant agreement No. 702981. References [1] Kim, K.-D., Kumar, P .R.: Cyb er–physical systems: A p ersp ective at the centennial . Pro ceedings of the IEEE 100 (Sp ecial Centennial Issue), 1287–130 8 (201 2) [2] Resp onse, S.S .: What Y ou Need to Kno w Ab out t he WannaCry Ransomw are [3] V eeravalli , V.V., Va rshney , P .K.: Distri buted inference in wireless sensor net w o rks. Philo- sophical T ra nsactions of the R o y al So ciety of London A: Mathemati cal, Physical and Engineering Sciences 370 (1958), 100–117 (2012) [4] Ba rbarossa, S., Sa rdellit ti, S., Di Lo renzo, P .: Di stributed detection and estimati on in wireless. A cademic Press Lib rary i n S ignal Pro cessing: Communications a nd Rada r S ignal Pro cessing 2 , 329 (2013) [5] Hanck e, G.P ., Hanck e Jr, G .P ., et al. : The role of advanced sensi ng i n smart cities. Senso rs 13 (1), 393–425 (2012) [6] Difall ah, D.E., Cudre-Ma uroux, P ., McKenna, S .A.: Scalable anomaly detection for sma rt cit y i nfrastructure netw o rks. IEEE Internet Computing 17 (6), 39–47 (2013) [7] Lamb rou, T.P ., P anayiotou, C.G., P olyca rp ou, M.M.: Contamination detection in drink- ing w ater distribution systems usi ng sensor net w o rks. In: Control Conference (ECC), 20 15 Europ ean, pp. 3298–33 03 (2015). IEEE [8] Lamb rou, T.P ., A nastasiou, C.C., Pana yiotou, C.G., P olyca rp ou, M.M.: A low- cost senso r net w o rk for real-time monito ring and contaminati on detection in drinking water distribu - tion systems. IEEE sensors journal 14 (8), 2765–27 72 (2014) 19 [9] P errig, A ., Stank ovic, J., W agner, D .: Securit y in wireless senso r netw ork s. Communica- tions of t he ACM 47 (6), 53–57 (2004) [10] Shi, E., Pe rrig, A.: Desi gning secure senso r net w o rks. IEEE Wireless Communications 11 (6), 38–43 (2004) [11] P atha n, A.-S.K., Lee, H.-W., Hong, C.S.: S ecurit y in wireless senso r net w o rks: issues and challenges. In: Adv anced Communication T echnology , 2006. ICACT 2006. The 8th International Conference, vol. 2, p. 6 (2006). IEEE [12] T ra pp e, W., Ho wa rd, R., Mo ore, R.S.: Lo w-energy security: Limits and opp o r- tunities in the internet of things. IEEE Securit y Privacy 13 (1), 14–21 (2015 ). doi:10.11 09/MSP .2015.7 [13] Marano, S., Matt a, V., T ong, L.: Distri buted detection i n the p resence of byzantine attacks. IEEE T ransa ctions on Signal Pro cessing 57 (1), 16–29 (2009) [14] Lamp ort, L., Shostak, R., Pease, M.: T he byzantine generals problem. ACM T ran sactions on Programming Languages a nd Syst ems (TOPLAS) 4 (3), 382–401 (1982 ) [15] Ve mpaty , A., T ong, L., Va rshney , P .K.: Distributed inference wit h byzantine data: Stat e- of-the-a rt review on da ta fal sification attacks. IEEE S ignal Pro cessing Magazine 30 (5), 65–75 (2013) [16] Nadendla, V.S .S., Han, Y.S ., V arshney , P .K.: Distributed inference with m-a ry quanti zed data in the p resence of b yzantine attacks. IEEE T ransa ctions on Signal Processing 62 (10), 2681– 2695 (2014). doi:10.1109 /TSP .2014.2 314072 [17] Zhang, J., Blum, R.S ., Lu, X., Conus, D.: Asymptotically optimum distribut ed estimation in the p resence of attacks. IEEE T ransactions on Signal Pro cessing 63 (5) , 1086– 1101 (2015 ). doi:10.110 9/TSP .2014 .2386281 [18] Kailkhura, B., Han, Y .S., Bra hma, S., V arshney , P .K.: Dis tributed bay esia n detection in the presenc e of byzantine da ta. IEEE T ransactions on Signal Pro cessing 63 (19), 5250– 5263 (2015). doi:10.110 9/TSP .2015.2450191 [19] Kailkhura, B ., Bra hma, S., Han, Y.S., V arshney , P .K.: Di stributed detection in tree top ologies with b yza ntines. IEEE T ra nsactions on Signal Pro cessing 62 (12), 3208–3219 (2014 ) [20] Kailkhura, B., Bra hma, S ., D ulek, B., Han, Y.S., V a rshney , P .K.: D istributed detection in tree netw orks: Byzantin es and mitigati on techniques. IEEE T ransa ctions on Info rmation F o rensics and S ecurit y 10 (7), 1499–15 12 (2015). d oi:10.11 09/TIFS.2015.241575 7 [21] Chen, K.-C., Lien, S.-Y.: Ma chine-to-machine communications: T echnologies and chal- lenges. Ad Ho c Netw orks 18 , 3–23 (2014) [22] P arno, B., Pe rrig, A ., Gli go r, V .: Distributed detection of no de replication attacks in senso r net wo rks. In: 2005 IEEE Symp osium on Security and Priv acy (S &P’05), pp. 49– 63 (2005). IEEE [23] Lin, S.-C., Chen, K.-C.: Improving sp ectrum efficiency via in-net w o rk computations in cognitive radio senso r netw o rks. IEEE T ransactions on Wireless Communications 13 (3), 1222– 1234 (2014) [24] Daniels, B.C., Ellison, C.J., Krak auer, D.C., Flack, J.C.: Quantifying collectivit y . Current opinion in neurobiology 37 , 106–1 13 (2016) [25] Brush, E.R., Krak auer, D.C., Flack, J.C.: Conflicts of interest imp rove collective compu- tation of adaptive so cia l structures. Science Advances 4 (1), 1603311 (2018) [26] Tsitsikli s, J.N., et al. : Decentralized detection. Advances in St atistical Signal Pro cessin g 2 (2), 297–344 (1993) [27] Viswanathan, R., V arshney , P .K.: D istributed detection with multi ple sensors i . funda- mentals. Pro ceedings of the IEEE 85 (1), 54–6 3 (1997) 20 [28] Blum, R.S., Kassam, S .A., P o o r, H.V.: Distributed detection with multiple senso rs i. advanced topics. Pro ceedings of the IEEE 85 (1), 64–79 (1997) [29] Chen, B ., T ong, L., V arshney , P .K.: Chann el a wa re distributed detection in wireless sensor net w o rks. In: IEEE S ignal Pro cessing Mag (2006). Citeseer [30] Chamb erla nd, J.-F., V eeravall i, V.V.: Wireless senso rs in dis tributed detection applica- tions. IEEE s ignal processing magazine 24 (3), 16–25 (2007) [31] Tsitsikli s, J., Athans, M.: On the complexity of decentraliz ed decision making and de- tection p roblems. IEEE T ra nsactions on Automatic Control 30 (5), 440–4 46 (1985) [32] W arren, D., Willett, P .: Optimum quanti zation fo r detecto r fusion: some proofs, exam- ples, and pathology . Journal of the Franklin Institute 336 (2), 323–3 59 (1999) [33] Chamb erla nd, J.-F., V eeravalli, V .V.: Asymptotic results fo r decentralized d etection in p o we r constrai ned wireless senso r net w o rks. IEEE Journal on selected a reas in communi- cations 22 (6), 1007–1015 (2004) [34] Easley , D., Kleinb erg, J.: Net wo rks, cro wds, and mark ets. Cambridge Universit y Press 1 (2.1), 2–1 (2010) [35] Acemoglu, D ., Ozdaglar, A.: O pinion dynamics a nd lea rning in socia l net wo rks. Dynamic Games and Applicati ons 1 (1), 3–49 (2011) [36] Banerjee, A.V .: A si mple mo del of herd b ehavior. The Quarterly Journal of Economics, 797–8 17 (1992) [37] Bikhchandani , S., Hirs hleifer, D., Welch, I.: A theory of fads, fashion, custom, and cultural change as i nfo rmational cascades. Journal o f p oli tical Ec onomy , 992–10 26 (1992) [38] Bikhchandani , S., Hirshleifer, D., W elch, I.: Learning from the b ehavio r of others: Con- fo rmit y , fads, and inform ati onal cascades. Th e Journal of Economic Perspectives 12 (3), 151–1 70 (1998) [39] Smith, L., Sørensen, P .: Patholog ical outcomes of observational learning. Econometrica 68 (2), 371–398 (2000) [40] Bala , V., Go y al, S.: Conform ism a nd di versit y under so cial lea rning. Eco nomic theo ry 17 (1), 101–120 (2001) [41] Banerjee, A., F udenb erg, D .: W o rd-of-mouth l ea rning. Games and Economic Behavio r 46 (1), 1–22 (2004) [42] Gale, D., Kariv, S .: Ba yesian learning in socia l net w o rks. Games and Economic Behavior 45 (2), 329–346 (2003) [43] Gill, D., Sgroi, D.: Sequential decisions with tests. Games and economic Behavi o r 63 (2), 663–6 78 (2008) [44] Acemoglu, D ., Dahleh, M.A., Lobel, I., Oz daglar, A.: Bay esian lea rning in social net w o rks. The Review of Economic Studies 78 (4), 1201–123 6 (2011) [45] Hsiao, J., Chen, K.C.: Steering inform ati on cascades in a so cial s ystem by selective rewiring and i ncentive seeding. In: to Be Included in 2016 IEEE International Conference on Communications (ICC) (2016 ) [46] DeMarzo, P .M., Zwieb el, J., Va y anos, D.: Pe rsuas ion bias , s o cial influence, and uni- dimensional opinions. So cial Influence, and Uni-D imensional Opini ons (November 2001). MIT Sloan W o rking P ap er (4339 -01) (2001) [47] Golub, B., Jackson, M.O.: Naive lea rning i n so cial net w o rks and the wisdom of cro wds. American Economic Journal: M icro economics 2 (1), 112–14 9 (2010) [48] Acemoglu, D., Ozdaglar, A., Pa randehGheibi, A.: Spread of (mis) i nfo rmation in so cial net w o rks. G ames and Economic B ehavio r 70 (2), 194–227 (2010) 21 [49] Jadbabai e, A., Molavi, P ., Sandroni, A., T ahbaz -Salehi, A.: Non-ba ye sian so cial learning. Games and Economic B ehavio r 76 (1), 210–225 (2012) [50] Lalitha , A., S a rwate, A ., Javidi, T.: So cia l l ea rning and distributed hyp othesis testing. In: 2014 IEEE Int ernational S ymp osium on Info rmation Theo ry , pp. 551–555 (2014). IEEE [51] Rhim, J.B., Goy al, V.K.: Distributed hyp othesis testing with so cial lea rning and symmet- ric fusion. IEEE T ransactions on S ignal Pro cessing 62 (23), 6298–6 308 (2014) [52] Huang, S .L., Chen, K.C.: Information cas cades in so cial netw ork s via dynamic system analyses. In: 2015 IEEE International Conference on Communications (ICC), pp. 1262– 1267 (2015). doi:10.110 9/ICC.2015 .7248496 [53] Castro, R., Coates, M., Liang, G ., No wak, R., Y u, B.: Net w o rk tomography: recent developments. Sta tistical science, 499–51 7 (2004 ) [54] Viswanathan, R., Thomop oulos, S.C., T umuluri , R.: Optimal serial distributed decision fusion. IEEE T ransactions on Aerospace and Electronic Systems 24 (4), 366– 376 (1988) [55] P apas tavrou, J.D., Athans, M .: Distri buted detection by a large team of senso rs in tandem. IEEE T ransactions on Aerospace a nd Electronic S ystems 28 (3), 639–653 (1992) [56] Swaszek, P .F.: On the p erfo rmance of serial net wo rks in distrib uted detection. IEEE transactions on aerospace an d electronic systems 29 (1), 254–260 (1993) [57] Bahceci, I., Al-Regib, G ., Altunba sak, Y.: Serial dis tributed detection f o r wireless senso r net w o rks. In: Info rmation Theory , 2005. ISIT 2005. Pro ceedings. International Symp o- sium On, pp. 830–834 (2005) . IEEE [58] Rosas, F., Hsiao, J.-H., Chen, K.-C.: A technological p ersp ective on inf o rmation cas cades via so cial learning. IEEE Access 5 , 22605–226 33 (2017) [59] Rosas, F., Chen, K.-C.: So cial learning agains t data fals ification i n senso r net wo rks. In: International W o rkshop on Complex Net w o rks and Their Applications, pp. 704–716 (2017 ). Springe r [60] Rosas, F., Ob erli, C.: Mo dulati on and snr optimi zation fo r achieving energy-efficient communications over sho rt-range fading channels. IEEE T ransactions on Wi reless Com- munications 11 (12), 4286–4 295 (2012) [61] Bertrand, A.: Appli cations and trends in wireless acoustic sensor netw ork s: A signal p ro cessing p ersp ective. In: 2011 18th IEEE Symposium on Co mmunications and V ehicular T echnology in the Benelux (SCVT), pp. 1–6 (2011). doi:10.1109 /SCVT.2011.6101302 [62] Kam, M., Zhu, Q., Gray , W.S.: Optimal data fusion of co rrela ted lo cal decisi ons in mul- tiple senso r detection systems. IEEE T ransactions on Aerospace an d El ectronic Systems 28 (3), 916–920 (1992) [63] Chen, J.-G., Ansari, N.: Adaptive fusion of corre la ted l o cal decisions. IEEE T ra nsactions on Syst ems, Man, and Cyb ernetics, Pa rt C (Applications and R eviews) 28 (2), 276–281 (1998 ) [64] Willett, P ., Swaszek, P .F., Blum, R.S.: The go o d, bad and ugly: distributed detection of a kno wn si gnal in dep endent gaussia n noise. IEEE T ra nsactions on Signal Pro cessing 48 (12), 3266–327 9 (2000) [65] Chamb erla nd, J.-F., V eeravalli , V .V.: Ho w dense should a senso r net w o rk b e fo r d etection with co rrelated observations? IEEE T ransa ctions on Information Theory 52 (11), 5099– 5106 (2006) [66] Sundaresan, A., Va rs hney , P .K., Rao, N.S.: Copula-based fusi on of co rrelated decisions. IEEE T ransactions on Aerospace and Electronic Systems 47 (1), 454–471 (2011) [67] Lo eve, M .: Probability Theo ry I. S p ringer, ??? (1978) [68] Ka rl, H., Will ig, A.: Proto cols and Architectures for Wireless Senso r Netw ork s. John Wiley & Sons, ??? (2007) 22 [69] Ka ryotis, V., Khouzani, M .: M alw are Diffusi on Mo dels for M o dern Complex Netw orks: Theo ry a nd Appl ications. Mo rgan Kaufmann, ??? (2016) [70] P o or, H.V.: An Intro duction to Si gnal Detection a nd Estima tion. Springer, ??? (2013) [71] Smith, P ., Hutchison, D., S terb enz, J.P ., Sch¨ oller, M., Fessi, A., Karaliop oulos, M., Lac, C., Pl attner, B.: Netw ork resilience: a systematic appro ach. IEEE Communications Magazine 49 (7), 88–97 (2011) [72] Shill er, R.J.: Conversation, in fo rmation, and herd b ehavior. The American Economic Review 85 (2), 181–185 (1995) [73] Gelman, A., Carlin, J.B., Stern, H.S., Dunson, D .B., Vehta ri, A., Rubin, D.B.: Ba yesian Data Ana lysis vol. 2. CRC press Bo ca Raton, FL, ??? (2014) [74] Cover, T.M., Thomas, J.A .: El ements of Info rmation Theo ry . John Wi ley & Sons, ??? (2012 ) [75] Rosas, F., Ntranos, V., Ell ison, C.J., P ollin, S., Verhelst, M.: Understanding interdep en- dency through complex in fo rmation sharing. Entropy 18 (2), 38 (2016) [76] Dieudonne, J.: T reatise on Analysis vol. I I. Asso ciat ed Press, New Y ork, ??? (1976) [77] McKenna, S.A., Wilson, M., Klise, K.A .: Detecting changes in w ater qua lit y data. Amer- ican Water W o rks Asso ciation. Journal 100 (1), 74 (2008) 23
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment