An Analysis on Caching Placement for Millimeter/Micro Wave Hybrid Networks
In this paper, we consider a hybrid millimeter wave (mmWave) and micro wave ($\mu$Wave) network from the perspective of \emph{wireless caching} and study the optimal probabilistic content/file caching placement at desirable base stations (BSs) using …
Authors: Sudip Biswas, Tong Zhang, Keshav Singh
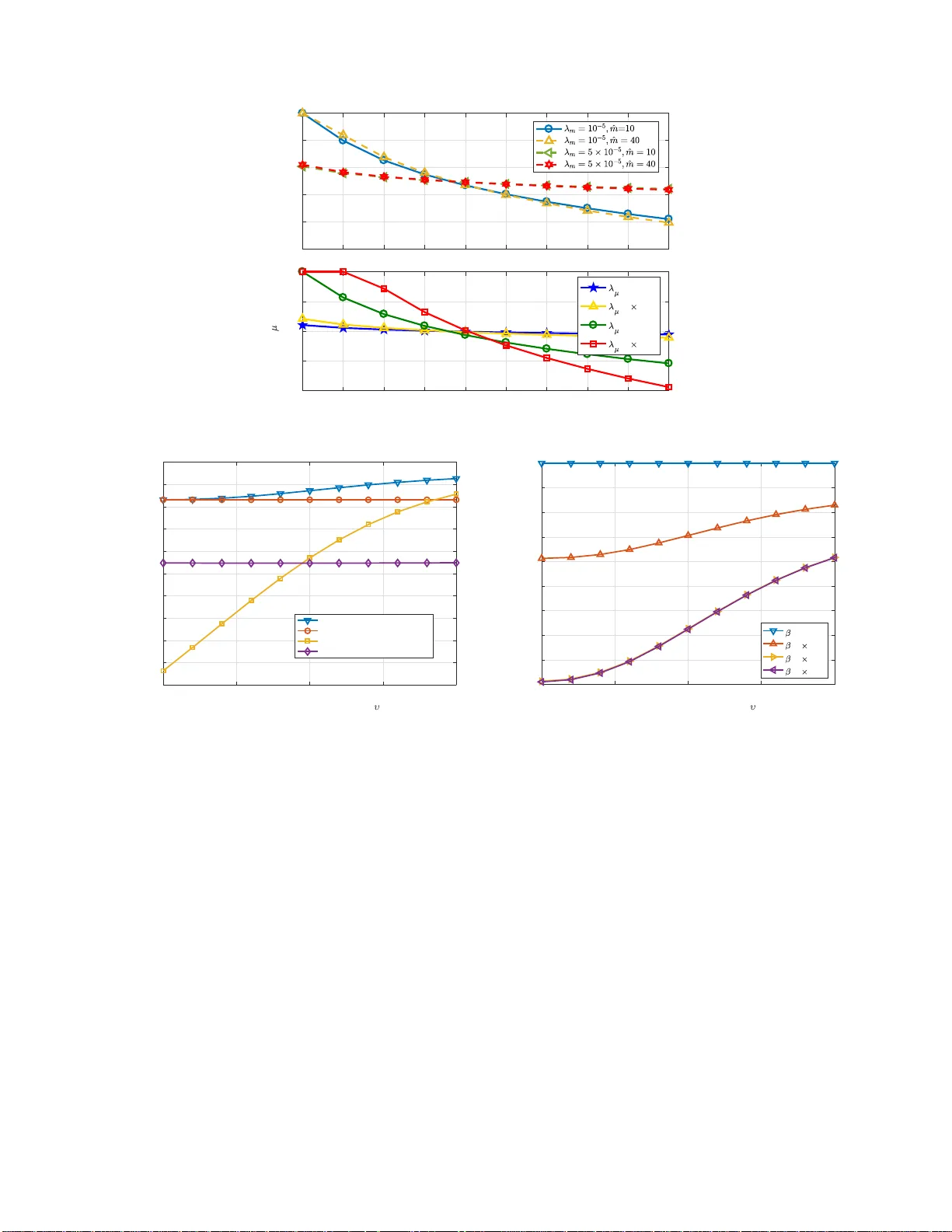
1 An Analysis on Caching Placement for Millime ter/Mi cro W a v e Hy brid Netw orks Sudip Biswas, T ong Zhang, K e shav Singh, Satyanarayana V uppala, and Tharmalingam Ratnara jah Abstract In this pap er , we co nsider a hybr id millimeter w av e (mmW a ve) and micro wav e ( µ W av e) net- work from the per spectiv e of wir eless caching and study the op timal probab ilistic content/file caching placement at desirable base statio n s (BSs) using a stochastic geometric fr amew ork. Considering th e av erage success pro bability (ASP) of file d eliv er y as the perfo rmance metric, we derive expr essions for the association pr o bability of the typical user to the mmW ave and µ W av e networks. Accordin g ly , we p rovide an upp e r bound f or the ASP o f file delivery and form ulate the con tent caching plac e ment scheme as an o ptimization pro blem with r espect to cach in g probab ilities, that jointly o ptimizes the ASP of file deli very considerin g both co ntent p lac ement an d delivery phases. I n p articular, we consider the caching placement strategy un der b oth noise-limited and interferen c e-limited en vironm e nts. W e numerically ev alu ate th e pe r forman ce of the p r oposed cach ing schemes under essential factors, such as blockag e s in the m mW a ve network, cluster radius, BS density , and path loss and compare it with u niform caching placemen t, cach ing M mo st p opular contents, and rando m cachin g placem ent. Numerical results demonstra te the sup eriority o f the pr oposed cachin g sch e me over oth ers, albeit certain trade-o ffs. Index T erms W ireless caching , millimeter-wa ve ne twork s, micro wa ve networks, Poison p o int p rocesses. I . I N T R O D U C T I O N Demand for higher capacity and lower latency in wireless networks is i ncreasing exponentially , which has resulted in the dev elopment of the fifth generation (5G) wireless communi cati o n systems, w i th key goals of data rates in the range of Gb p s, bi l lions of connected de vi ces, Sudip Biswas, T ong Zhan g, K eshav Singh, and Tharmalingam Ratnarajah are with Institute for Digital C ommunications, School of Engineering, Univ ersity of Edinburg h, Edinbur gh, UK. Email: { sudip.biswas, k.singh, t.zhang, t. ratnarajah } @ed.ac.uk. Satyanarayana V uppala is with Univ ersity of Luxembour g, L uxembourg . Email: satyanarayana.vu ppala@uni.lu. Corresponden t author: T ong Zhang. 2 lower latency , im proved coverage and reliabi l ity , and en vironment-friendly operation. A large portion of the data traf fic is due to the sur ge in int ernet usage, m obile applicati ons usage, social media and online video streaming through m obile de vices (e.g. mobile phones, tablets, laptops, etc.). Accordingly in [1], Ericsson has predicted that global mob ile data traf fic will surpass 100 E x aBytes by 20 2 3 . Noneth eless, i t is interesti ng t o note t hat a sub stantial amou nt of the data traffi c are redundantly generated over networks [2], as several popular contents are asynchronously and repeatedly requested by many users. M otiv ated by this, pre-fetching some popular video contents in the local cac hes of base stations (BSs), also termed as wireless edg e caching, has b een considered as a promi sing technique to alleviate network t raffic l oads. In particular , wireless edge caching has the advantages of 1) alleviating the burden of the b ackhaul by av o i ding repeated transmissi o n of the same contents from the core network t o end-users, 2) reducin g latency by shortening t h e comm u nication distance, 3) imp roving network capacity and th rou ghput, and 4) re ducing the operational cost due to lower cost of storage memory than bandwidth. Further to alleviate the spectrum crunch and meet the data rate d emands, while on one hand, techniques like heterogeneous networks (HetNets ) and n etwork densification through sm all cell networks (SCNs) [3] hav e b ecom e commonplace i n current wi reless communicati o ns researc h, on th e o ther hand, millim eter wav e (mmW a ve) frequencies are being cons i dered as an alternative solution to t he currently operatio nal micro wav e ( µ W a ve) networks. Also, mm W a ve transmission by nature is mo re suitable for o p eration in sm all cells due to it s limited range of propagation. Hence, it is realisti c to say that in future 5 G networks, mmW a ve and traditional µ W a ve networks wi ll exist in conju nction wi th each other , which will allow for a seaml ess coverage and transmissi o n. Consequently , with regards to th e aforementi oned technologies, researchers are looking into ho w to maximize the a verage success probability (ASP) of content deli very in cellular networks to increase the users’ quality of experience (QoE) [4] [5]. In t h is paper , we will consi d er a hybrid mm/ µ W a ve network and demonst rate the feasibi lity of caching i n such a network. 1) Related work o n wir eless caching: Whil e caching has been used to m aintain internet traf fic over the last two decades, but mainly related to computer-based technolog ies [6], [7], recently wireless caching has triggered cons iderable interest from both academia and indus t ry due to 3 its potenti al of reducing backhaul l o ads, latency and cost. In this regard, [8], [9] showed the ef fectiveness of proactive caching on the network edge to help reducing traffi c congestion in backhaul links . While a simi lar system, but in volving stochastic geometry based framework was studied i n [10] for t h e scenario of BSs located in the Euclidian plane, caching in device-to-de vice (D2D) communi cations was consi dered i n [11] and [12]. Further , the authors in [13] proved that popularity-based optimal caching placement in t erms of outage probability gi ves better results than uniform caching where all BS s uniformly fetch all contents in their l ocal caches irrespective of the popul arity . Hence, caching placement scheme is a ke y f actor that determines the success and performance of a caching system, and it is an endeav ou r for researchers to find optimal ways to perform content caching placement in various networks. In this regard, whil e the authors in [14] explore the optimal m et h ods for caching in a multiple-inpu t multiple-output (MIMO) network, [15] studies optimal cac hing strategies for D2D commun i cations. 2) Related work on mmW ave and hybrid networks: Due to the vast am ount of u nused spectrum in mmW a ve frequency range, considerable efforts have been made to analyze mm W a ve systems recently . Ho we ver , s ignals transmitted at mm W a ve frequencies are easily attenuated b y blockages, such as concrete buildings, trees, etc. Hence, t o quantify t h e performance of mmW a ve cellular systems, [16] performed real tim e propagation channel measurements. Th en, while in [17] a blockage model for m mW a ve prop agati on was introduced to analyze the rate and cover age area of mm W a ve systems, a distance dependent pat h loss mod el along wi th antenna gain parameters were introduced in [18] to characterize the prop agati on en vironment in such systems. Further , while the above works focussed on urban en vironment s , [19] proposed a path loss model for rural mmW a ve networks and [20] showed the feasibilit y and application of mmW a ve in out door cellular networks. On a similar vein, hybrid wireless networks, which comb i ne two diffe rent tiers of base stations can also increase the capacity of wireless networks and spectrum effi ciency . Accordingly , research w orks in [21]–[25] ha ve focussed on the s tudy of capacity for su ch netw orks. Further , with regards to future 5G networks, the auth ors in [26] were among the first t o consider a mm W a ve overlaid µ W a ve network. Subsequently , th e authors in [27] provided up l ink and downlink covera ge analysis of such hybri d networks and [20] provided a coverage analysis in a densified heterogenous mmW a ve SCN. 4 Based on the aforesaid, in this paper we s tudy the optimal content caching placement strategy in a mm/ µ W av e hybri d network by maxim i zing t he ASP of file deliv ery . In particul ar , considering a stochastic geometric framew ork, we model a hy b rid cellul ar network in volving both mmW a ve and µ W a ve BSs, which are randomly located within a bound ed region. The BSs have finite cache memory and store files in them in a probabili stic and ind epend ent way . W e consider a typical user , which receives the content of interest from the serving BSs offer ing the best receiv ed si gnal power among its neighbou ri ng BSs. The m ain d i stinctions of this work can be summ arized as in the follo wing points: • W e calculate t h e associati o n probability of the user to a mmW a ve or µ W a ve network based on the simplified long-term average bi ased (L T AB) recei ved signal power ( i.e., least path loss). Usin g the associati o n prob abi lity , we provide the expression for the ASP of file deliv ery . While, a closed-form e xp ression is provided for t he ASP of file deliv ery under a noise-limit ed scenario, an upper bound is provided for the interference-limited case. • T o opt imally place th e con t ents in the h ybrid network, w e p ropose two algorithms , one each for noise-limi ted and interference-limited scenarios to acquire o p timal caching probabil ities by maximizing the ASP o f fi le delivery . • Be sides characterizing the ef fects of b lockages o n th e ASP for the typical user over a bounded region, we also e valuate the ef fects of channel fading in conjuncti on with other essential fac tors, such as mm/ µ W a ve BS densit y , cluster ra dius, and content popularity . • Finally , throu g h numerical si mulations we compare the performance of the proposed caching placement s cheme with other caching strategies su ch as, 1) uniform caching placement, 2) caching M m o st po p u lar contents, and 3) random caching placement. Numerical result s demonstrate th e superiority of the proposed caching scheme over others, alt h ough with certain performance trade-of fs. I I . S Y S T E M M O D E L W e consider the downlink transm ission in a cache-enabled hybrid cellular network com p rising of bot h mmW a ve and µ W ave networks as sho wn in Fig. 1. Wh i le mm W a ve BSs and associated users form the SCNs, µ W ave BSs and their associated u s ers form the macro cell networks (MCNs). Further , mmW a ve BSs and µ W a ve BSs are i ndependently m o deled by two homogeneous Poisson point processes (PPPs) Φ m with density λ m and Φ µ with density λ µ , respecti vely. T h e 5 µ Wave BS Blockages Typical User mmWave BS Origin/server content Storage unit Storage unit Backhaul link Backhaul links Fig. 1: An illustration of a cache enabled hybrid mmW ave - µ W ave network. users in the network follo w another independent homogenous PPP Φ u with density λ u . All the processes are independent of each other . Further , bot h mmW a ve and µ W a ve BSs are equipped with mu l tiple antennas n m t and n µ t , respectively . The users are assum ed to be equipp ed wit h two sets of antennas n m r and n µ r , to recei ve both mmW av e and µ W a ve transmi ssions, respectiv ely 1 . Hereinafter , throughou t t he paper subscript/superscript / notation of m and µ will be used to refer to mmW a ve BSs and µ W av e BSs, respectively . In a typical cellu l ar network, BSs retrie ve requested files using capacity-lim ited b ackhaul links. During p eak h ours, this results in an informati on- congestion bottleneck both at th e BSs as well as in the backhaul li n ks. T o alleviate this bottleneck, caching popular contents at the mmW a ve a nd µ W a ve BSs are proposed. The requested content will be served d irectly to th e users by one of the neighbouring BSs dependi n g on the a vailability of the file in its local cache and t he ass ociation criteria of the users to the BSs. The performance of caching howev er , depends on the density of BS n o des, cache size, users’ request rate, the caching strategy , content popularity , cluster radius and blockages in the network. A. Caching policy W ithout loss of generality , a typical user is assumed to be located at the orig i n that is the centre of a two dimensi onal (2-D) disk wit h a radius R . This circle signifies a finit e network region, i n whi ch all BSs from both mmW av e SCN and µ W a ve M CN can communi cate with the typical user. The typical user will be associated to eit h er mmW a ve network or µ W a ve netw o rk depending on the L T AB received s i gnal power and the a va ilability of requested files at t h e serving 1 While to recei ve mmW ave signals, the users utilize multiple antennas, µ W ave signals are captured by a single antenna only . This is due to the fact that the wa velength of mmW av e si gnals is very small and hence more antennas can be accommodated within a small physical space. Ho weve r , for µ W ave receiv ers, it may not be feasible to equip small de vices with more than one antenna owing to larger wave lengths of µ W ave signals. Henceforth, we use n µ r = 1 . 6 BSs. In particular , the typical user is associated to the mm W a ve network if and only if 1) the strongest L T AB received signal power achiev ed at the asso ciated mmW av e BS is greater t h an the maximum value of the same at the µ W a ve BS, 2) the requested file is prefetched i n the associated m mW a ve BS, selected according to the best receive d sig n al power , and 3) th e rate supported by the serving mmW a ve BS is greater th an the guaranteed t arget rate. If eit her of th e aforementioned conditions cannot be s atisfied by the mmW ave network, the t ypical user wil l be offl oaded to the µ W av e network 2 , where a potent ial µ W a ve serving BS will be chosen from a subset that has the request ed file sto red in its cache. Now , if t he serving µ W av e BS can achie ve the guaranteed target rate, the request ed file can b e successfully delivered to the typi cal user . As for the case that the requested file is delivered from t he local caches, it will be t ermed as “cache hit”. Otherwise, it is a “cache miss”, where BSs will t hen utilize backhaul links to retrie ve the requested file in real time 3 . This scenario is not ideal for caching and shoul d be av oided. Our aim is to develop an effe ctiv e cache pl acement strategy to maximize “cache hit”. M ore details on the communication policy wi ll be discussed in later sections. 1) Cac hi ng model: T o cache pop ular files requested by a user , each BS contain s st orage units, referred to as l ocal cac hes. The cache size of the µ W a ve BSs is assumed to be lar ger than that of mm W av e BSs. Additionaly , a central source/server containing a global cache 4 is accessible to all the BSs in t h e hybrid network via wired backhaul links. For s implicity , we represent the size of the cache by the number of files. It is assum ed that each mmW av e and µ W a ve BS can cache up to C m and C µ files of length B bits each, respectiv ely , such that C m < C µ . Further , we assume that the distribution of us ers’ requests follows th e independent reference model (IRM), in which t he content popularity is stationary and each user in dependently requests a data-file of size B bits 5 from the file set S , { s 1 , s 2 , . . . , s i , . . . s L } , where L is the total number of files cached in the n etwork. The popularity of t he request ed files is assumed t o be ind epend ent of each other and is m o delled by th e Zipf distrib u tion [29]. In particular , the popularity of the i th file in the l ibrary is gi ven as 2 Similar offload ing strategies with respect to a threshold capacity were analyzed in [ 18 ], [28] and stated t o be reasonable for mmW ave based networks. 3 The cache miss scenario is mentioned here f or the sake of completeness, but is beyond the scope of discussion in this work. 4 In the e vent t hat the fi le requested by t he t ypical user is not in the local cache, then the file i s retrieved from global cache that contains all the files a user may request. 5 For analytical simplici t y , we assume that all files hav e the same size. 7 f i = 1 /i υ P L j =1 1 /j υ , 1 ≤ i ≤ L , (1) where υ is the Zipf exponent, that controls the ske wness of t h e content popularity . 2) Cac hi ng placement strate gy: A p robabilistic caching placement s trategy i s assumed, where each BS (mm or µ W a ve) caches its file in an independ ent ly and identically distributed (i.i .d) manner by producing M indices generated according to Π , { π i : s i ∈ S , i = 1 , 2 , ..., L } , where 0 ≤ π i ≤ 1 and P L i =1 π i ≤ M . The files are cached in advance during of f-peak hours through prior request s or overhearing. The caching BSs sto ri n g file i can be m odelled as an independent PPP with intensity λ j i , p j i λ j , where p j i is t he probabi l ity of caching the i th file for all s i ∈ S and j ∈ { m, µ } . Now , from all L files, the typical user requests on e file depending on the file popularity f i , such that a file with higher po pularity is request ed with hi gher likelihood . For analytical tractabilit y , hereinafter we assum e that the popularit y of t he files is perfectly known and that the files in the set S are o f the sam e size and n ormalized t o one 6 , i.e., S , { 1 , 2 , . . . , L } . B. MmW ave network model 1) Bloc kage model: Mm W av e s ignals are sus ceptible t o blockages, making it imperative to model blockages for true representatio n of practical mmW a ve syst em s. Blockages in the network are usu all y concrete buildings. W e consider the bl ockages to be stationary blocks whi ch are in variant wi th respect to direction. W e adopt the modeling of b l ockages in [30], and accordingly , consider a two st at e statisti cal model for each lin k. The link can be either li n e-of-sight (LOS) or non-line-of-sight (NLOS). LOS ( L ) link occurs when there is a direct propagati on path between the transmi t ter and t h e recei ver , while NLOS ( N ) occurs when th e link is blocked and the recei ver receiv es the signal through refl ection from a blockage. Let th e LOS link be of length r and β be the b l ockage density , then th e probabilities of occurrence p L ( . ) and p N ( . ) of LOS and NLOS states, respecti vely , can be given as a function of r as p L ( r ) = e − β r , p N ( r ) = 1 − e − β r . (2) 2) Beamforming mo del: Due to the sm all wave lengths of mmW av es, directional beamformin g at both transmi tters and recei vers can be exploited for compensating the path loss and additional noise. The beam patterns are approximated as sectorized gain pat t erns [31]. Let θ be the 6 In the case of unequal fi le size, each file can be div i ded into small partitions of the same size, with each partiti on being treated as an indi vidual file. 8 beamwidth of the m ain lobe. Th en the antenna gain pattern for a t ransmit or receiv e node about an angle φ is given as [31] G q ( θ ) = G M q if | φ | ≤ θ G m q if | φ | > θ , (3) where q ∈ { T , R } , with T denoti n g the transmitt er , and R the receiv er , φ ∈ [0 , 2 π ) is the angl e of boresight direction and G M q and G m q are t h e ar ray gains of main and side lobes, respectively . The effe ctiv e antenna gain/int erference 7 seen by the typical user wil l depend on the directivity of the gains of main ( i.e., G M ) and side ( i.e ., G m ) lobes of the ant enna beam p attern, giv en as G i = G M G M , p MM = ( θ 2 π ) 2 G M G m , p Mm = θ (2 π − θ ) (2 π ) 2 G m G M , p mM = θ (2 π − θ ) (2 π ) 2 G m G m , p mm = ( 2 π − θ 2 π ) 2 , (4) where p lk , with l , k ∈ { M , m } , denotes the probabi lity that the antenna gain G l G k is seen by th e typical u ser . Thu s, the ef fectiv e gain can be considered as a rando m variable, which can take any of the mentioned values in (4). F or simplicity and tractability , we assu m e that the beamforming gain b et ween the mmW ave s erving BS and the typical user i s al ways G M G M since the alig n ed beamforming gain between the typi cal user and the mmW ave serving BS is maximum [32]. 3) Channel model: T o capture a generalized propagation en vironment and for analytical tractability , in this work we consider the Nakagami fading m odel 8 . Let ˆ m be the Nakagami fading p arameter and Γ( ˆ m ) the gamma fun ct i on. Then, the channel power i s distributed as X ˆ m ∼ f X ˆ m ( x ; ˆ m ) , ˆ m ˆ m x ˆ m − 1 e − ˆ mx Γ( ˆ m ) . (5) C. µ W ave network model The µ W a ve channels are modeled in a simi lar way as that of its mmW a ve counterparts with the on ly exceptions that the antennas are n ow omni d irectional with transm itted sig n al power P µ and path loss exponent α µ . It is to be noted t hat the blockage ef fects are no t consi d ered for µ W a ve systems due to low penetration lo ss of µ W av e signals . 7 In order to av oid ambiguity of notation, hereinafter G always denotes the ef fectiv e antenna gain/interference. 8 The choice of Nakagami- ˆ m fading to simulate the small scale fading is commonly used in lit erature [30], [31], [33]. 9 Under the consideration of separate encodi ng scheme at each BS, BS l sends an information symbol s l through a linear beamforming vector 9 v l = [ v 1 l , . . . , v l n µ t ] T with uni t norm, i.e., || v l || 2 = 1 , i ∈ Φ µ . Therefore, by a sli ght ab use of not at i on, the receiv ed signal at the t ypical user from the µ W ave BS l can be giv en as y = p P µ h H 1 ,l v l r − α µ / 2 l s l + X i ∈ Φ µ ,i 6 = l p P µ h H 1 ,i v i r − α µ / 2 i s i + n 1 , (6) where h 1 ,i = [ h 1 1 ,i , . . . , h n µ t 1 ,i ] T is th e downlink channel between the µ W av e BS i to the typical user 10 and n 1 denotes the additiv e Gaussian noise at the typical user . I I I . R A T E C H A R AC T E R I Z A T I O N F O R T H E T Y P I C A L U S E R The ty p ical user may be connected to either a mmW a ve BS or a µ W a ve BS depending o n th e communication policy , which will be d i scussed in the next section. In t his section we characterize the rate of the typical user when it is connected to ei t her a mmW a ve or a µ W ave BS. Let Φ m i be the set of mm W a ve BSs, which ha ve file i in t heir local caches. Given that a t ypical user is served by a mmW a ve BS (from Φ m i ) that contains the request ed file and with t he stron g est recei ved signal po wer at the user is gi ven as ζ m 1 ,i = max k ∈ Φ m i ( P m G 1 ,k X 1 ,k r α j 1 ,k ) , (7) where P m , G 1 ,k and X 1 ,k are the t ransmit power , directional antenna g ai n , and channel power coef ficient at the typical user from the associated mmW a ve BS, respecti vely . Further , r 1 ,k is t he distance between th e typical user and the serving mmW av e BS and α j is the p ath lo ss exponent with j ∈ {L , N } . Now , let Φ c m i (or Φ m i ) be the set of interfering BSs, i . e., in t erference from all other mmW a ve BSs w i thout file i in their cache memory . Then, Φ c m i is written as Φ c m i = Φ m \ Φ m i . (8) Therefore, the SINR at the ty p ical user , receiving file i from t h e serving mmW a ve BS l , where l ∈ Φ m i , can no w be defined as γ m 1 ,l i , P m G 1 ,l X 1 ,l r − α j 1 ,l ( σ 2 m 1 ,l | {z } A + X t ∈ Φ c m i P m G 1 ,t X 1 ,t r − α j 1 ,t | {z } B ) . (9) 9 A maximal ratio t ransmit (MR T) precoding scheme is considered, i. e., v l = h 1 ,l || h 1 ,l || 2 . 10 The subscript 1 in h 1 ,l corresponds to the typical user . 10 In the denominator above, A represents the noi se power at the ty pical user , B is the interference 11 seen at the typical user from the mmW a ve BSs which do not contain t h e file i . Accordingly , the downlink rate 12 at the typical user requesting t h e i th file is e xp ressed as R m l i = (1 /N l i ) × lo g 2 1 + γ m l i , (10) where N l i is the total load of th e serving mmW ave BS. Sim ilarly , by a slight abuse of notation, we use the s am e symbols to denote the total load of the associated µ W ave BS and the distance between the typical u s er and its associated µ W a ve BS. Accordingly , the downlink rate at the typical user , receiving file i from the serving µ W ave BS l , with l ∈ Φ µ i , is gi ven as R µ l i = (1 /N l i ) × lo g 2 1 + γ µ l i , (11) where γ µ l i , P µ H l r − α µ l n σ 2 µ l |{z} A + X t ∈ Φ c µ i P µ H t r − α µ t | {z } B o . (12) Here, H l = || h H l v l || 2 = || h l || 2 denotes t h e power gain of the fading channel 13 Like before, A and B denote noi se and interfere nce from t he set of µ W a ve BSs not ha ving file i , respectively . I V . A S S O C I A T I O N P RO BA B I L I T Y In this section, we present the com munication po l icy , where we determi n e the association probability of t h e typi cal user p mw and p µw connected to eit h er a mm W a ve network or a µ W a ve network, respective ly . T o calculate p mw and p µw , we form u late a problem by comparing the maximum L T AB receive d signal power s between mmW a ve and µ W a ve BSs. Accordi n gly , we introduce bias factors B µ and B m [28], [34], which are always posi tiv e. When B = 1 , n o biasing i s cons i dered and t he associati on g o es back t o a t raditional cell associati o n po l icy based on maximum received power or nearest node. Lev eraging the anal y s is from [28], we cons ider that the typical user is connected to the best network with respect to L T AB receiv ed power ( i.e., B m P m G l r − α j l , j ∈ { m, µ } for mmW a ve network and B µ P µ r − α µ l for µ W av e n etwork). Howe ver , unlike µ W a ve network, it is import ant to characterize the least path loss distri bution in m mW a ve 11 W e assume that each user is served by only one BS and BSs storing the same file cooperate among each other so that interference to wards t he typical user is mitigated. Round-robin scheduling is used to select users to be served in each time slot. Accordingly , the typical user suffers fr om interference in the network only fr om the BSs t hat do not cache t he requested file. 12 Hereinafter , for notational simplicity , we omit the subscript 1 that is used to represent the typical user . 13 Ignoring the independ ence among n µ t channels and sacrificing t he channel diversity gain, while assuming that each entity of h l is an i.i.d. complex Gaussian random variable with zero mean and variance 1 /n µ t , H l can be considered to be Nakagami- ˆ m distributed with ˆ m = 1 . Henceforth, this simplification helps us to obtain tractable mathematical deriv ations. 11 network by incorporating the effect of b l ockages. As mentioned before, the possi bility of t he channel lin k being LOS or NL O S follows from t he exponential blockage probabil ity model. Accordingly , t h e least path loss distribution for a typ i cal user in a m mW a ve network i s give n in Lemm a 1, foll owed by t he association probability of the typical user to µ W a ve network in Theorem 1. A pictorial representati o n of the above communication pol i cy is presented i n Fig. 2. Lemma 1. The least path loss distr ibution for a typical user in a mmW ave network is given as F mm ξ l ( r ) = 1 − exp − π λ m ( r P m G l B m ) 2 α N − 2 π λ m β 2 (1 − e − β ( r P m G l B m ) 1 α L (1 + β ( r P m G l B m ) 1 α L )) + 2 π λ m β 2 (1 − e − β ( r P m G l B m ) 1 α N (1 + β ( r P m G l B m ) 1 α N )) ! . (13) Pr oof. The proof of this lemma follows from the proof of Theorem 1 of [35]. Howe ver , for con venience, we present a sketch of the p roof here. Consid er a point p rocess , where the points represent the p at h loss between th e typi cal user and rando m ly placed BSs in a m m W a ve network. Let φ mm = n ξ l , x α m l P m G l B m o be a homog eneous PPP of intensity λ m . Here, the dist ance is a random variable, and its LOS state occurs with the p rob ability of e − β x . By u sing Mappi ng theorem [36, Th eorem 2.34], the densit y function of this one dimensional PP P under the ef fect of blockages can b e given as Λ([0 , r ]) = ( r P m G l B m ) 1 α L Z 0 2 π λ m xe − β x d x + ( r P m G l B m ) 1 α N Z 0 2 π λ m x (1 − e − β x )d x. (14) Using the v o i d probabilit y of a PPP and with the help of (14), t h e least path loss distribution in a mmW ave network can be g iven as (13), where B m = 1 / P m and B µ = 1 / P µ . Theor em 1. In a hybrid network consisti ng of mmW ave and µ W ave BSs as described, considering the least pas s loss distri bution, t he pr obabil ity tha t a typical u ser is connected to the µ W ave network is given by p µw = 2 π λ µ ∞ Z 0 r exp − Λ m ¯ P mm ¯ P µ 1 α m r α µ α m ! ! e − π λ µ r 2 d r , (15) wher e ¯ P mm = P m G l B m , with G l = G M G M and ¯ P µ = P µ B µ , with B m = 1 P m , B µ = 1 P µ . Then, 12 User requests i th file mmW ave or µ -W ave network? Select the associated mmW ave BS Is requested file av ailable? R m i ≥ ν i ? Successfully served by the mmW ave BS Select the associated µ W ave BS Is requested file av ailable? R µ i ≥ ν i ? Successfully served by the µ W ave BS Retrieve through backhaul l ink Failure in serving the user ( p mw ) ( p µw ) (Y) (N) (Y) (N) (Y) (Y) (N) (N) Fig. 2: An illustration of the communication policy for the typical user with either mmW ave or µ W ave network. Λ m ¯ P mm ¯ P µ 1 α m r α µ α m = π λ m ¯ P mm ¯ P µ 1 α N r α µ α N − 2 π λ m β 2 1 − e − β ¯ P mm ¯ P µ 1 α N r α µ α N 1 + β ¯ P mm ¯ P µ 1 α N r α µ α N ! + 2 π λ m β 2 1 − e − β ¯ P mm ¯ P µ 1 α L r α µ α L 1 + β ¯ P mm ¯ P µ 1 α L r α µ α L ! . (16) Pr oof. The p roo f ca n be obtained by le veraging resul ts of Lemma 1. V . P E R F O R M A N C E M E T R I C W e use t h e av erage success probability (ASP) of file deliv ery as the performance metri c to design the caching placement st rategy . In particular , A SP is defined as t he successful respons e to the user’ s request, which occurs when the downlink rate is more than the target bit rate of the file. Thus, when the typi cal user request s the i th file, the ASP of file d eliv ery ca n be expressed as P s ( { ν i } ) = X L i =1 f i P [ R x i ≥ ν i ] , (17) where x i ∈ Φ m i /µ i is the s erving BS 14 selected according to (7), f i is the probabili ty of requesting the i th file, ν i is the tar get bit rate of file i and R x i is the rate at th e typical user . Now , as the m mW a ve and µ W a ve networks follow two independent PPPs, it is poss i ble to perform the analysis on both the processes independently with an association probabili t y . 14 For notational simplicity , x i denotes either µ W ave serving BS or mmW ave serving BS for file i depending on the context. 13 Accordingly , giv en that p mw is the associat i on probabili t y that the typical user is connected to the mmW av e n etwork, t h e file i is serv ed by the associated mm W a ve BS that is abl e to support the downlink rate greater than the tar get bit rate. Otherwise, the typical user will be associated to the µ W a ve network with the probabi lity p µw = 1 − p mw . In this regard, we assum e that the typical user can communicate wi th all BSs t hat cache the requested file 15 . According l y , the total ASP of file delivery can be give n as P s ( { ν i } ) = P mm s ( { ν i } ) p mw + P µ s ( { ν i } ) p µw , (18) where P mm s ( ν i ) and P µ s ( ν i ) denote the conditional ASP of file delivery by the mmW a ve and µ W a ve networks, respectively . Theor em 2. The ASP of fi le delivery by th e mmW ave BSs is tightl y upper bounded by P mm s ( { ν i } ) ≤ X L i =1 ( f i ( X ˆ m l =1 ˆ m l ( − 1) l +1 X j ∈{ L,N } ( p j exp − AlQ i σ 2 m x i P m G x i r − α j x i (19) × 3 Y ˆ q =1 Y ˆ j ∈{L , N } exp h − λ m i Z ∞ 0 1 − 1 1 + AlQ i ˆ G ˆ q r − α ˆ j t G x i r − α j x i ˆ m ˆ m p ˆ j 2 π p ˆ q r t dr t i , wher e G x i = G M G M , ˆ G ˆ q ∈ { ˆ G 1 = G M G M , ˆ G 2 = G M G m , ˆ G 3 = G m G m } , p ˆ q ∈ { p 1 = p MM , p 2 = 2 p Mm , p 3 = p mm } with ˆ q ∈ { 1 , 2 , 3 } . P articularly , p j , p ˆ j ∈ { p N = 1 − e − β r x i , p L = e − β r x i } with j, ˆ j ∈ {L , N } , A = ˆ m ( ˆ m !) − 1 ˆ m , wher e for mmW a ve network, ˆ m > 1 is the Nakagami parameter . Q i = 2 N x i ν i − 1 , and λ m i = (1 − p m i ) λ m . Pr oof. This proo f is given in App endix A. Theor em 3. The ASP of fi le delivery by th e µ W ave BSs is tightl y upper boun d ed by P µ s ( { ν i } ) ≤ X L i =1 f i ( X ˆ m l =1 ( ˆ m l ( − 1) l +1 exp ( − lAQ i σ 2 µ x i P µ r − α µ x i ) exp [ − 2 π λ µ i Z ∞ 0 r t (1 − (1 + AlQ i r − α µ t r − α µ x i ˆ m ) − ˆ m ) dr t ] )) , (20) wher e ˆ m = 1 , Q i 16 = 2 N x i ν i − 1 and λ µ i = λ µ (1 − p µ i ) . All p a rameters ar e either defined befor e or are generally the s ame as those defined for the mmW ave network but with notati onal changes. 15 If the user cannot be served from the local caches due to low deli very rate, other BSs meeting t he target rate requirement, but without file i in their local caches should retriev e the r equested file via backhaul links or coordinated transmission between BSs. This howe ver is out of scope of the current work and is left for f uture work. 16 N x i denotes the total load of either the associated mmW ave or µ W ave BS depending on the context. Q i for mmW av e and µ W ave are usually different as the total load of the serving BS s for file i may be dif ferent. Howe ver , for simplicit y we assume that the total loads are equal in this work. 14 Pr oof. Due to page lim itations, the proof of this theorem is omitted but can be obtained in a similar w ay as the proof of Theorem 2. V I . P RO P O S E D C A C H I N G P L AC E M E N T I N T H E H Y B R I D N E T W O R K T o place the contents in t he hybrid network, we aim to op timize t he ASP of file delivery by considering a finite memory size and content po p u larity . This can be achie ved by optimally determining caching probabi l ities in the file caching placement phase. Accordingl y , we formulate an optimization problem as below . P1 : max { p m i } , { p µ i } P s ( { ν i } ) , (21) s.t. X L i =1 p m i ≤ C m , (22) X L i =1 p µ i ≤ C µ , (23) 0 ≤ p m i ≤ 1 & 0 ≤ p µ i ≤ 1 , ∀ i ∈ S , (24) The const raints in (22) and (23) ensure that the size of the total cached files shoul d be less than or equal to C m for mmW av e and C µ for µ W a ve networks. In the above , the ASP is giv en as in (25), s hown on the t o p of the this page. The functions cons i sting of variables p m i and p µ i are exponential functions, which are con vex. Hence, their summation is also conv ex. Ho wever , due to the binomi al term ( − 1) l +1 , th e objectiv e function is no longer con ve x. In particular , i t is a difference of con vex (DC) functions and hence a DC (DCP), which m akes it qui te rigorous to cop e with the opt imization problem. In this regard, we consider t h e noise-limited (NL) and interference-limited (IL) scenarios separately to try to si mplify the probl em and ref ormulate the optimizatio n problem under t wo di fferent scenarios. A. Opt imal caching pr obabiliti es und er NL scenario Recent studies on mmW a ve networks [32], state that mmW av e networks in urban sett i ngs are more NL than IL. This i s due to the fact that in the presence of blockages, the signals recei ved from unintentional sources are close to negligible. In such densely blocked scenarios (typical for urban settings), signal to noise ratio (SNR) provides a good enough approximation to SINR for d irectional mmW a ve networks. Furthermore, for the µ W a ve case, when t he num ber of users is much smaller than the number of serving BSs, the impact o f int erference is negligible when compared to the nois e power . Accordingl y , the typical user ca n be serv ed without sharing 15 P s ( { ν i } ) = P mm s ( { ν i } ) p mw + P µ s ( { ν i } ) p µw ≤ X L i =1 ( f i ( X ˆ m l =1 ˆ m l ( − 1) l +1 X j ∈{L , N } ( p j exp − AlQ i σ 2 m x i P m G x i r − α j x i × exp h − λ m i X 3 ˆ q =1 X ˆ j ∈{L , N } Z ∞ 0 1 − 1 1 + AlQ i ˆ G ˆ q r − α ˆ j t G x i r − α j x i m ˆ m p ˆ j 2 π p ˆ q r t dr t i | {z } Z ( i,l ) p mw + X L i =1 f i ( X ˆ m l =1 ( ˆ m l ( − 1) l +1 exp ( − lAQ i σ 2 µ x i P µ r − α µ x i ) exp [ − λ µ i Z ∞ 0 2 π r t (1 − (1 + AlQ i r − α µ t r − α µ x i ˆ m ) − ˆ m ) dr t ] | {z } W ( i,l ) p µw = X L i =1 f i X ˆ m l =1 ˆ m l ( − 1) l +1 X j ∈{L , N } ( p j exp − AlQ i σ 2 m x i P m G x i r − α j x i exp h − λ m i Z ( i, l ) i ) p mw + X L i =1 f i ( X ˆ m l =1 ( ˆ m l ( − 1) l +1 exp ( − lAQ i σ 2 µ x i P µ r − α µ x i ) exp [ − λ µ i W ( i, l )] )) p µw . (25) resources with other users. Hence, i n this section we ignore the interference part B in (9) and (12), and consider th e NL case only to analyze t he effects of channel selection div ersity o n optimal caching strategy . Additio n ally , such an assumption also aids us in deri ving closed form expressions for the ASP of file deli very . Theor em 4. The ASP of fi le delivery by th e mmW ave network i n a N L scenario is given by P mm s ( { ν i } ) = X L i =1 f i " 1 − exp − X j ∈{L , N } k j p m i Z j η i G x i Q i − ˆ k p m i η i G x i Q i δ m N # (26) where k j = c j π λ m ˆ m ˆ m δ m j Γ( ˆ m ) , c j ∈ {− 1 , 1 } 17 , with j ∈ {L , N } , ˆ k = π λ m Γ( δ m N + ˆ m ) m δ m N Γ( m ) , δ m j = 2 α j , η i = P m σ 2 m x i , Q i = 2 ρ i − 1 , ρ i = N x i ν i . Z j ( ˜ ω ) = R ∞ 0 R ˜ ω 0 exp ( − ˆ m ω ψ ) ω ( ˆ m +1) d ω ψ ( δ m j + ˆ m − 1) exp ( − β ψ δ m j 2 ) d ψ with ˜ ω = η i G x i Q i . All other parameters ar e as defined b efore. Pr oof. The p roo f is gi ven i n Appendix C . 17 c L = 1 , c N = − 1 . 16 Similarly , the ASP of file d el ivery in the µ W a ve network can be derived wi th the channel power gain now being exponential l y distributed, where blockage ef fects and beamforming g ain s are ignored. Theor em 5. The ASP of fi le delivery in a µ W ave network in a NL scenario is given by P µ s ( { ν i } ) = X L i =1 f i 1 − exp ( − ˜ k p µ i ( ˜ η i Q i ) δ µ ) , (27) wher e ˜ k = π λ µ Γ( δ µ + 1) , ˜ η i = P µ σ 2 µ x i , δ µ = 2 α µ , Q i = 2 ρ i − 1 , ρ i 18 = N x i ν i . The optimization problem P1 i s now con vex and the objectiv e function can be rewritten as P s ( { ν i } ) = X L i =1 f i " 1 − exp − X j ∈{L , N } k j p m i Z j η i G x i Q i − ˆ k p m i η i G x i Q i δ m N # p mw + X L i =1 f i 1 − exp ( − ˜ k p µ i ( ˜ η i Q i ) δ µ ) p µw . (28) The Lagrangian function of the opti mization problem (21 ) -(23) is L ( { p m i } , { p µ i } , ˜ ω , ˆ ω , { ˜ µ i } , { ˆ µ i } ) = X L i =1 f i " 1 − exp − X j ∈{L , N } k j p m i Z j η i G x i Q i − ˆ k p m i η i G x i Q i δ m N # p mw + X L i =1 f i 1 − exp ( − ˜ k p µ i ( ˜ η i Q i ) δ µ ) p µw − ˜ ω X L i =1 p m i − C m − ˆ ω X L i =1 p µ i − C µ − X L i =1 ˜ µ i ( p m i − 1) − X L i =1 ˆ µ i ( p µ i − 1) , (29) where ˜ ω , ˆ ω , ˜ µ i and ˆ µ i are the Lagrangian multipliers associated with th e cons traints (22)-(23), respectiv ely . Since Slater’ s condition satisfies the opti m ization problem, the optimal solution of the problem ca n be achie ved by solving its dual , which can be written as min ˜ ω , ˆ ω, { ˜ µ i } , { ˆ µ i }≥ 0 max { p m i } , { p µ i } L ( { p m i } , { p µ i } , ˜ ω , ˆ ω , { ˜ µ i } , { ˆ µ i } ) . (30) The dual problem in (30) is then solved in an iterati ve fashion which alternates between a sub- pr oblem , u pdating the caching probabili t y variables { p m i } and { p µ i } by fixing the Lagrangian multipli ers ( ˜ ω , ˆ ω , { ˜ µ i } , { ˆ µ i } ) , and a master problem , compu t ing new Lagrangian multipli ers based on the obtained caching probabili t ies. Further , in the sub-probl em, b y taking the partial deriv ative of (29) with respect to p m i , we can find the op timal caching prob abi lities for mmW a ve BSs. Accordingly , ∂ L ( { p m i } , ˜ ω , { ˜ µ i } ) ∂ p m i = f i exp [ p m i ( − A i − B i )] + ˜ ω + ˜ µ i (31) 18 By normalizing the whole bandwidth, ρ max = 1 bits/s/Hz and N x i ∈ [0 , 1] expresses the portion of the whole bandwidth. Hence, ρ i ≤ 1 . 17 Algorithm 1 : Computation of { p ∗ m i } and { p ∗ µ i } 1: Initialize : ˜ ω , ˆ ω , { ˜ µ i } , { ˆ µ i } 2: Comp u te p m i using (32). 3: Comp u te p µ i using (33). 4: Upd ate the Langr angian multiplier s ˜ ω , ˆ ω , { ˜ µ i } , and { ˆ µ i } . 5: Repeat steps 2 − 4 until conv ergence. 6: p ∗ m i ← p m i ( ˜ ω ∗ , ˜ µ ∗ i ) , p ∗ µ i ← p µ i ( ˆ ω ∗ , ˆ µ ∗ i ) . where A i = P j ∈{L , N } k j Z j ( η i G x i Q i ) and B i = ˆ k ( η i G x i Q i ) δ m N . The opt imal caching probabilit y is now given by p m i = 1 A i + B i log f i p mw ˜ ω + ˜ µ i + , (32) where [ x ] + = max { 0 , x } . Like wise, the optimal caching probabi lity for µ W a ve BS i s given by p µ i = 1 ˆ T i ˜ k log p µw f i ˆ ω + ˆ µ i + , (33) where ˆ T i = ( ˜ η i Q i δ µ . Th e Lagrange m u l tipliers are updated using subgradient method . The algorithm to find th e opti mal caching prob abi lities { p ∗ m i } and { p ∗ µ i } is gi ven in Algo rithm 1. B. Opt imal caching pr obabiliti es und er IL scenario Compared to t he NL case, the in terference part in (9) and (12) will be domi nant when the number of mm/ µ W a ve BSs ( i.e., density) increases and b l ockage densit y in t h e network decreases. In this subsection, the ASP of file deliv ery under a IL case is given. Theor em 6. The IL ASP o f file delivery in a mmW ave n etwork is given by P mm s ( ν i ) ≤ X L i =1 f i X ˆ m l =1 ˆ m l ( − 1) l +1 X j ∈{L , N } p j 3 Y ˆ q =1 Y ˆ j ∈{L , N } exp h − λ m i Z ∞ 0 1 − 1 1 + AlQ i ˆ G ˆ q r − α ˆ j t G x i r − α j x i ˆ m ˆ m p ˆ j 2 π p ˆ q r t dr t i . (34) Pr oof. This proo f can be obtained similar to Theorem 2 with interference part only . 18 Theor em 7. The IL ASP o f file delivery in a µ W ave n etwork is given simil arly as P µ s ( ν i ) ≤ X L i =1 f i X ˆ m l =1 ˆ m l ( − 1) l +1 exp h − 2 π λ µ i Z ∞ 0 r t 1 − 1 + lAQ i r − α µ t r − α µ x i ˆ m − ˆ m dr t i )) , (35) wher e all the parameter s are as defined befor e. Pr oof. This proo f can be obtained by le veraging on t he deri vation of Theorem 3. After establishing t he ASP of file delivery for t he hyb rid network in an IL scenario, the objective function of the optimi zati on problem P1 for this IL case can now be rewritten as in (36), shown on the top of the next page. In the above, h ( { p m i } ) , g ( { p m i } ) , hh ( { p µ i } ) , g g ( { p µ i } ) are con vex. The opti m ization problem to find the op timal file placement scheme can now be formulated as a standard DCP pr obl em and gi ven as P2 : min { p m i } , { p µ i } [ − h ( { p m i } ) + g ( { p m i } ) − hh ( { p µ i } ) + g g ( { p µ i } )] (37) s.t. X L i =1 p m i ≤ C m , (38) X L i =1 p µ i ≤ C µ , (39) 0 ≤ p m i ≤ 1 , & 0 ≤ p µ i ≤ 1 , ∀ i ∈ S . (40) Now , it can be n oted that si nce mmW av e and µ W a ve networks can be independently represented through th ei r respecti ve association probabilities, we can separately calculate the opt imal caching probabilities for mm W a ve BSs and µ W a ve BSs by rewriting th e above op t imization problem into two sub-DCP problems. Based on [37], we propose an it erati ve algorithm as giv en in Algorithm 2 to ob t ain the optimal caching probabil ities for bot h mmW av e and µ W a ve networks by separately con verting the sub-DC obj ectiv e functi ons to con vex funct i ons. Below , we give the proof of con ver gence of Algorithm 2. Theor em 8. The original objective function in (37) of the DCP pr o blem P2 can be con ve xi fi ed by r eplacing it with its upper bound. The p r oposed algori thm i s t h en con ver gent w ith r esp ect to an incr eas e in the i teration n u mber . Pr oof. Let p k m and p k µ be the feasible point s for probl em P2 . Applying T aylor series approx- imation on h ( { p k +1 m i } ) and hh ( { p k +1 µ i } ) at feasible points p k m and p k µ , the objective function is re w ri t ten as 19 P s ( { µ i } ) ≤ X L i =1 f i X ˆ m l =1 ˆ m l ( − 1) l +1 X j ∈{L , N } p j 3 Y ˆ q =1 Y ˆ j ∈{L , N } exp h − λ m i Z ∞ 0 1 − 1 1 + AlQ i ˆ G ˆ q r − α ˆ j t G x i r − α j x i ˆ m ˆ m p ˆ j 2 π p ˆ q r t dr t i p mw + X L i =1 f i ( ˆ m X l =1 ( ˆ m l ( − 1) l +1 exp h − 2 π λ µ i Z ∞ 0 r t 1 − 1 + lAQ i r − α µ t r − α µ x i ˆ m − ˆ m dr t i )) p µw = X L i =1 f i X ˆ m l =1 ˆ m l ( − 1) ( l +1) X j ∈{L , N } p j × exp " − (1 − p m i ) λ m 3 X ˆ q =1 X ˆ j ∈{L , N } Z ∞ 0 1 − 1 1 + AlQ i ˆ G ˆ q r − α ˆ j t G x i r − α j x i ˆ m ˆ m p ˆ j 2 π p ˆ q r t dr t | {z } ˆ Z ( i,l ) # p mw + L X i =1 f i ˆ m X l =1 ˆ m l ( − 1) ( l +1) × exp h − (1 − p µ i ) λ µ Z ∞ 0 r t 1 − 1 + lAQ i r − α µ t r − α µ x i ˆ m − ˆ m 2 π dr t | {z } ˆ W ( i,l ) i p µw = X L i =1 f i X l = odd number ˆ m l X j ∈{L , N } p j exp [ − λ m ˆ Z ( i, l )] exp [ p m i ( λ m ˆ Z ( i, l )] p mw | {z } h ( { p m i } ) − X L i =1 f i X l = ev en number ˆ m l X j ∈{L , N } p j exp [ − λ m ˆ Z ( i, l )] exp [ p m i ( λ m ˆ Z ( i, l )] p mw | {z } g ( { p m } ) + X L i =1 f i X l = odd number ˆ m l exp ( − λ µ ˆ W ( i, l )) exp [ p µ i ( λ µ ˆ W ( i, l ))] p µw | {z } hh ( { p µ i } ) − X L i =1 f i X l = ev en number ˆ m l exp ( − λ µ ˆ W ( i, l )) exp [ p µ i ( λ µ ˆ W ( i, l ))] p µw | {z } g g ( { p µ i } ) (36) v k +1 = g ( p k +1 m ) − h ( p k +1 m ) + g g ( p k +1 µ ) − hh ( p k +1 µ ) , (41) such th at (41) i s now con vex. Since the region o f feasible solution remains the sam e, the feasib l e points p k m and p k µ are als o feasible for the con vexifie d problem and ot h er feasible points p k +1 m and p k +1 µ that exist for t h e con vexified problem are also th e feasible points of the problem P2 . Furthermore, for all p m and p µ using T aylor s eries app roximation, the con ve xity of h and hh giv es us ˆ h ( p k +1 m ; p k m ) ≤ h ( p k +1 m ) , (42) and ˆ hh ( p k +1 µ ; p k µ ) ≤ hh ( p k +1 µ ) . (43) 20 Algorithm 2 : Computation of { p ∗ m i } and { p ∗ µ i } 1: Initialize : co unter k = 0 , { p 0 m i } , { p 0 µ i } , step size ∆ = 10 − 4 and threshold ˆ δ = 10 − 5 2: Repeat 3: Compute: ˆ h ( p k +1 m ; p k m ) = h ( p k m ) + ∇ h T ( p k m )( p k +1 m − p k m ) ˆ hh ( p k +1 µ ; p k µ ) = hh ( p k µ ) + ∇ hh T ( p k µ ) ( p k +1 µ − p k µ ) 4: Solve 1: Set the value o f { p k +1 m i } to be a solution of minimize g ( { p k +1 m i } ) − ˆ h ( { p k +1 m i } ; { p k m i } ) subject to P L i =1 p k +1 m i ≤ M , 0 ≤ p k +1 m i ≤ 1 , ∀ i ∈ S 5: Solve 2: Set the value o f { p k +1 µ i } to be a solution of minimize g g ( { p k +1 µ i } ) − ˆ hh ( { p k +1 µ i } ; { p k µ i } ) subject to P L i =1 p k +1 µ i ≤ N , 0 ≤ p k +1 µ i ≤ 1 , ∀ i ∈ S 6: Update: k = k + 1 . 7: p k m = p k − 1 m + sig n ( p k m − p k − 1 m ) × ∇ h T ( p k − 1 m ) × ∆ , p k µ = p k − 1 µ + sig n ( p k µ − p k − 1 µ ) × ∇ h T ( p k − 1 µ ) × ∆ , where sig n ( x ) = 1 , x > 0 0 , x = 0 − 1 , x < 0 8: Until conv ergence or maximum iteration number is rea ched. Hence, if p 0 m and p 0 µ are chosen to be feasible, all corresponding iterates wil l be feasible. Now , we show that the objecti ve v alu e con ver ges o ver the iterations . According to the inequalities g ( p m ) < h ( p m ) , (44) g g ( p µ ) < hh ( p µ ) , (45) and v k +1 ≤ g ( p k +1 m ) − ˆ h ( p k +1 m ; p k m ) + g g ( p k +1 µ ) − ˆ hh ( p k +1 µ ; p k µ ) | {z } ˆ v k +1 , (46) we minimize the value o f ˆ v k +1 at each iteration k , and obtain v k by using pre vious p k m and p k µ such that v k ≥ ˆ v k +1 ≥ v k +1 . (47) The value of the above objectiv e function is now non -i n creasing and will always con verge, possibly to ne gat ive infinity , wh ich concludes th e proof. V I I . N U M E R I C A L R E S U L T S After de veloping the analyti cal framework in the previous sections, we no w ev aluate the performance (ASP of file deliv ery) of th e proposed caching placement s t rategy with respect to 21 T ABLE I: Parameter values Parameter notation Physical meaning V alues η i = P m σ 2 m x i , ∀ i ∈ S SNR of the typical user for file i from the mmW av e serving BS 54 (dB) ˜ η i = P µ σ 2 µ x i , ∀ i ∈ S SNR of the typical user for file i from the µ W av e serving BS 104 (dB) θ Mainlobe beamwidth π / 6 G M / G m Mainlobe antenna gain / sidelobe antenna gain 15 (dB) / -15 (dB) G x i Effecti ve antenna gain between the serving mmW ave BS and typical user 225 (dB) α L / α N Path loss exp onent of LoS and NLoS 2 / 4 α µ µ W ave path loss expone nt 3.5 λ m mmW ave BS density 5 × 10 − 5 (nodes/m 2 ) λ µ µ W ave BS density 10 − 6 (nodes/m 2 ) β Blockage density 0.008 υ S ke wness of the content popularity 0.8 L The number of files 10 R The radius of the bounded cov erage region 500 (m) C m / C µ Cache size of mmW ave/ µ W av e BS 5 / 6 ˆ m Nakagami fading parameter for mmW ave ( µ W ave) channel 10 (1) ρ max The maximum fil e deliv ery rate 1 (bit/sec/Hz) ρ i , ∀ i ∈ S The rate for i -th file delivery ( i.e., ρ i ∈ [0 , ρ max ] ) 0.8 (bits/sec/Hz) Algorithm 1 and 2 . Unless otherwise st ated, most of t he parameters used and their correspondi n g values are inspired from lit erature and giv en in T able I. A uniform target rate for each file is considered for simplicity throughout the analysis. W e b egin by ev aluatin g th e opti m al caching probabilities in a NL hybrid network for varying densities of mmW av e and µ W a ve networks and different Nakagam i parameters i n Fig. 3. It is worth not ing that according to the CDF of t he pro cess { r α X } in (70), when λ m p m i becomes higher , the mi n imum of the CDF of { r α X } increases. Accordingly , the ASP of file deliv ery will be higher due to the increase in intensity m easure. In fact, the reciprocal of { r α X } represents the ef fective channel gain and hence, with the increase in density , the probability to obtain higher channel gain also increases. Howe ver , it can also be seen that wh en the density in creases, t he caching probabil ities for t he most popular files decrease and tend t o be uniformly dis t ributed. This means that by sacrificing higher channel gain for a fe w specific contents, we ca n increase the hitting probability of all contents ( content diversity gain ) such that the optimal ASP of file deliv ery can be achieved. Therefore, there is a tradeoff between channel gain and cache h i t. Besides, in t h e same figure, we also ev aluate the effect of Nakagami fading parameter ˆ m , wh ich relates to the channel power gain. The figure shows t h at the proposed algori t hm is not aff ected by ˆ m , which shows that BS dens i ty is a m ore significant parameter than the fading parameter ˆ m . The above explanation holds true for µ W av e systems as well as can be seen from the tradeoff in performance for µ W ave optim al caching probabilities in t erms of BS density. 22 1 2 3 4 5 6 7 8 9 10 0 0.2 0.4 0.6 0.8 1 {p * m } 1 2 3 4 5 6 7 8 9 10 File index 0.2 0.4 0.6 0.8 1 {p * } =10 -5 =5 10 -6 =10 -6 =5 10 -7 Fig. 3: Optimal caching probability v .s. v arying λ and ˆ m v alues under NL scenario. 0 0.5 1 1.5 2 Content popularity exponent ( ) 0.5 0.55 0.6 0.65 0.7 0.75 0.8 0.85 0.9 0.95 1 ASP of file delivery (P s ) Proposed caching placement UC placement MC placement RC placement Fig. 4: ASP of fi le delivery for various caching placement strategies under NL scenario. 0 0.5 1 1.5 2 Content popularity exponent ( ) 0.91 0.92 0.93 0.94 0.95 0.96 0.97 0.98 0.99 1 ASP of file delivery (p s ) =10 -4 =2 10 -3 =3 10 -2 =4 10 -1 Fig. 5: ASP of fi le delivery for various blockage densities under NL scenario. W e now comp are the ASP of file delivery of t he proposed content placement st rategy as shown in Alg o rithm 1 in a NL hybrid network with three differe nt con tent p lacement strategies: 1) caching the M most popular contents (MC), 2) cac hing the contents uniformly (UC), and 3) caching content s randomly (RC) in Fig. 4. It is evident from the figure that t he proposed caching placement scheme is superior t o the M C, UC and RC in terms o f ASP of file delivery for varying content popularities. When the ske wness υ of the content p o pularity distribution is close to zero, meaning of whi ch is that the content popularity is uni formly d i stributed and uni formly requested by users, the propo sed caching placement strategy is significantly better than the o thers. On the other hand, while MC is bet t er than RC for higher va lues of υ and vice versa for low υ , both perform comparativ ely inferior to UC th roughout almost the entire range of υ . Next, in Fig. 5, 23 0 500 1000 1500 Iteration number 0.982 0.984 0.986 0.988 0.99 0.992 0.994 0.996 0.998 ASP of file delivery (p s ) = 0.6 = 2 Fig. 6: Con ver gence of Algorithm 2 under IL scenario for content popularity exponents υ = 0 . 6 and 2 . 0 0.5 1 1.5 2 Content popularity exponent ( ) 0.92 0.93 0.94 0.95 0.96 0.97 0.98 0.99 1 ASP of file delivery (P s ) Proposed caching placement MC placement UC placement RC placement Fig. 7: ASP of fi le delivery for various caching placement strategies under IL scenario. 0 0.5 1 1.5 2 Contennt popularity exponent ( ) 0.97 0.975 0.98 0.985 0.99 0.995 1 ASP of file delivery (p s ) = 10 -4 = 5 10 -3 = 5 10 -2 Fig. 8: ASP of fi le delivery for various blockage densities under IL scenario. we ev aluate th e ef fect of bl ockages on ou r proposed algorith m for the NL scenario. It can be seen that when blo ckage density i ncreases, the A SP of file deliver y decreases. Th is is due to t he fact that increasing blockages in the mmW ave network results in the attenuat i on o f the receiv ed signal. Ho wever , the decrease in opt imal ASP is not v ery significant. This can be explained as: 1) for a substanti al blockage density , wit h the in crease in ske wness , the num ber of files with higher probability requests decre ases up to e ven less than the cache size of µ W ave BSs, 2) the proposed algorithm makes sure that the hi gher caching probabili ty of th e mos t requested files is stored in the l imited number of µ W av e BSs, which are not aff ected by blockages, and 3) for the mmW a ve network, the algorithm also m akes s ure that the most requested files are stored onl y i n the m mW a ve BSs with less aver age probability of NLOS than LOS. Hence, it can be concluded that the proposed algorithm is a blockag e-awar e opti mal caching st rategy . After validating the results for the NL scenario, we now do the s am e for t he IL case with 24 similar parameter settings as in T able I, except for µ W a ve BS density λ µ = 10 − 5 , blockage density β = 0 . 0 0 5 , and tar get rate ρ i = 0 . 08 . W e begin by showing th e ev olutio n of Algori t hm 2 in Fig. 6 for υ = { 0 . 6 , 2 } . The mon o tonic increase of t he cost functi o n (ASP of file delivery) verifies the con ver gence of t he proposed algorithm, which w as also verified in Theorem 8. Similar to the NL case, i n Fig. 7, we show the superiority of t he proposed caching placement scheme in IL scenar io over three d i f ferent content placement strategies: MC, UC, and RC. Lik e before, the proposed caching placement scheme is mostly sup erior to the MC, UC and RC in terms of ASP of file delivery for varying cont ent popularities. When the skewness ( υ ) of the content popu l arity distribution is cl o se t o zero, the proposed caching placement strategy is disti n ctiv ely better than th e others. Howe ver , at higher values of υ , performance of M C is comparable to or slightly better than the proposed algori thm. This is du e to the fact that high er values of υ means that the content popularity is not un iform and the contents are no t uniformly requested by the us ers. Instead, only the mo s t popular files are requested by the u s ers which giv es a performance edge to MC. Furthermore, while M C is better t han RC and UC for higher values of υ and close to UC for low υ , UC performs better t han RC throug h o ut the ent i re range of υ . Finally , in Fig. 8 , we ev aluate the ef fect of b lockages on our propo sed algo ri t hm for the IL scenario. Unl ike the NL case, when blockage densi t y increases, the ASP of file delivery in creases in the IL case. The i ncrease i n opt imal ASP is due to the eff ect of interference mitigatio n t h rough blockages. More blockages in the network help in att enu ating the interfering sign al s , which enhances the rate of file deli very . Thi s can be consi d ered as one of the very few inst ances when blockages are beneficial. V I I I . C O N C L U S I O N The coexistence of a hybrid mmW a ve and µ W av e networks from the perspectiv e of wir eless caching w as shown. Usi ng stochastic geometric framework, that accounts for not only interfer - ence am ong the op eratin g base stations (BSs), uncertainties both i n nod e locations and channel fading, path loss and loads at cache-enabled BSs, but also blockages in the m mW a ve network, we studi ed the op t imal probabilisti c file caching placement at desirable mmW a ve/ µ W a ve BSs. In this regar d, expressions for the association probability of a user t o the m mW a ve or µ W a ve 25 network was calculated, which was then used t o derive closed form expression for av erage success probabil ity (ASP) o f file delivery in a noise-lim ited s cenario and a upper boun d for the same in a int erference-limited scenario. Usi ng the ASP of file delivery , we formulated the probabilisti c content caching placement scheme as an optimi zation problem with respect to caching probabilit ies and accordingly propo sed two algorithms, one each for n o ise-limited and interference-limited scenarios t o acquire op t imal caching probabilit ies by maximizi n g the ASP o f file deli very . Numerical e valuations were done wit h regards to the performance of the proposed content placement scheme under seve ral essential factors, which demo nstrated the s uperiority of the proposed caching schem e ov er others, e ven though certain trade-of fs were observed. A P P E N D I X A P RO O F O F T H E O R E M 2 T o proof this theorem, we subs titute (9) and (10) int o (17). Accordingly , the condi t ional ASP of file deli very by the mmW av e BSs can be reduced to P mm s ( ν i ) = X L i =1 f i P [ γ m x i ≥ 2 N x i ν i − 1 | {z } Q i ] (48) = X L i =1 f i P " P m G x i X x i r − α j x i σ 2 m x i + X t ∈ Φ c m i P m G t X t r − α ˆ j t | {z } I ˆ G, ˆ j Φ c m i ! ≥ Q i # (49) ( a ) ≤ X L i =1 f i E α j , I ˆ G, ˆ j Φ c m i ( 1 − " 1 − exp − AQ i ( σ 2 m x i + I ˆ G, ˆ j Φ c m i ) P m G x i r − α j x i !# ˆ m ) (50) ( b ) = X L i =1 f i E α j , I ˆ G, ˆ j Φ c m i ( 1 − X ˆ m l =0 ˆ m l ( − 1) l exp − AlQ i ( σ 2 m x i + I ˆ G, ˆ j Φ c m i ) P m G x i r − α j x i !) ( c ) = X L i =1 f i X ˆ m l =1 ˆ m l ( − 1) l +1 E I ˆ G, ˆ j Φ c m i X j ∈{L , N } p j exp − AlQ i ( σ 2 m x i + I ˆ G, ˆ j Φ c m i ) P m G x i r − α j x i ! (51) ( d ) = X L i =1 f i X ˆ m l =1 ˆ m l ( − 1) l +1 X j ∈{L , N } p j E I ˆ G, ˆ j Φ c m i exp − AlQ i ( σ 2 m x i + I ˆ G, ˆ j Φ c m i ) P m G x i r − α j x i ! (52) = L X i =1 f i ˆ m X l =1 ˆ m l ( − 1) l +1 X j ∈{L , N } p j exp − AlQ i σ 2 m x i P m G x i r − α j x i ! E I ˆ G, ˆ j Φ c m i exp − AlQ i I ˆ G, ˆ j Φ c m i P m G x i r − α j x i ! . ( 53) Here, x i refers to the ass o ciated mmW a ve BS that has t he requested file i in its local cache. Particularly , (a) follows from t he tight lower bound of a Gamma random variable [31], and by 26 taking uncondition al expectation with respect to path loss exponent α j and interference I ˆ G, ˆ j Φ c m i . Further , (b) follo ws from the Bino mial theorem, (c) is obtained by taking aver age ov er α j , and (d) i s obtain ed by exploiting the independence of P j over I ˆ G, ˆ j Φ c m i . Now , applyi ng the thinnin g theorem o f a PPP by considering blo ckages and ef fective antenn a gains, the point p rocess I ˆ G, ˆ j Φ c m i can be di vi ded int o 6 independent s ub-PPPs as sho wn in the fol lowing. I ˆ G, ˆ j Φ c m i = I G M G M , L Φ c m i + I G M G m , L Φ c m i + I G m G m , L Φ c m i + I G M G M , N Φ c mi + I G M G m , N Φ c m i + I G m G m , N Φ c m i (54) Accordingly , the e xpectation part in (53 ) can be reduced to E I ˆ G ˆ q , ˆ j Φ c m i exp − AlQ i ( I G M G M , L Φ c m i + I G M G m , L Φ c m i + I G m G m , L Φ c m i + I G M G M , N Φ c mi + I G M G m , N Φ c m i + I G m G m , N Φ c m i ) P m G x i r − α L x i = 3 Y ˆ q =1 Y ˆ j ∈{L , N } E I ˆ G ˆ q , ˆ j Φ c m i exp − AlQ i I ˆ G ˆ q , ˆ j Φ m i P m G x i r − α j x i , (55) where (55) follows from the fact that sub-PPPs i n (54) are ind ependent. Below we comp ute the expectation of I G M G M , L Φ m i only . Al l other t erms in (55) can be derived in a s imilar way . By utilizing Laplace transform, t he abov e e xpectatio n can be gi ven as E h exp − s ( i,l,j ) I ˆ G, ˆ j Φ c m i ˆ G = G M G M , ˆ j = L i ( f ) = E Φ ˆ G 1 , L m i n Y t ∈ Φ ˆ G 1 , L m i E X t h exp ( − s ( i,l,j ) P m G M G M X t r − α L t ) io ( g ) = E Φ ˆ G 1 , L m i n Y t ∈ Φ ˆ G 1 , L m i 1 1 + s ( i,l,j ) P m G M G M r − α L t ˆ m ˆ m o (56) ( h ) = exp h − λ m i Z ∞ 0 1 − 1 1 + s ( i,l,j ) P m G M G M r − α L t ˆ m ˆ m e − β r t 2 π p MM r t dr t i , (57) where Φ c m i and Φ m i hav e the sam e meaning b ut t he use of the later is for notational sim plicity . Further , Φ ˆ G 1 , ˆ j m i is the po int process marked by the una vailability of file i , G M G M and LoS state. s ( i,l,j ) = AlQ i P m G x i r − α j x i G x i = G M G M = AlQ i P m ( G M G M ) r − α j x i and p MM is t h e p rob ability when t h e ant enn a gain takes value G M G M and e − β r k is the p robability of th e o ccurrence of Lo S transmissi on. In the above, (f) follows from independent channel fading gains , (g) follows from the moment generating functi o n of a Nakagami - ˆ m random variable, and (h) follows from the probabili ty generating functional of a PPP [36]. 27 Now , taki n g into account all the sub-PPPs giv en by (54), we have E [ exp ( − s ( i,l,j ) I ˆ G, ˆ j Φ c m i )] = E [ exp ( X 3 ˆ q =1 X ˆ j ∈{ L,N } ( − s ( i,l,j ) I ˆ G ˆ q , ˆ j Φ c m i ))] (58) ( i ) = 3 Y ˆ q =1 Y ˆ j ∈{L , N } E [ exp ( − s ( i,l,j ) I ˆ G ˆ q , ˆ j Φ c m i )] (59) = 3 Y ˆ q =1 Y ˆ j ∈{L , N } exp h − λ m i Z ∞ 0 1 − 1 1 + s ( i,l,j ) P m ˆ G ˆ q r − α ˆ j t ˆ m ˆ m p ˆ j 2 π p ˆ q r t dr t i , (60) where (i) follows from the fact that all su b -PPPs are independent. Finall y , substit u ting the above results into (53), th e desired proof is obtained. A P P E N D I X B P RO O F O F T H E O R E M 4 Considering the NL scenario, the recei ved SNR at the typical u s er in the mmW a ve network served by BS x i can be reduced t o a form given as γ SNR m x i ≈ P m G x i X x i r − α j x i / σ 2 m x i . (61) Accordingly , the rate supported by the serving BS deliv ering file i t o the typical us er is R SNR m x i ≈ log (1 + γ SNR m x i ) / N x i . (62) Now , the conditional probability of file delivery in the mmW a ve network is gi ven by P mm s ( { ν i } ) = X L i =1 f i P [ log (1 + γ SNR m x i ) ≥ N x i ν i | {z } ρ i ] = X L i =1 f i P [ P m G x i X x i r − α j x i σ 2 m x i ≥ 2 ρ i − 1 | {z } Q i ] = X L i =1 f i P [ r α j x i X x i ≤ P m G x i Q i σ 2 m x i ] , (63) where α j = { α L , α N } . According t o thinni n g theorem, the PPP Φ m i is thin n ed from t he process Φ m with densit y λ m p m i , where p m i is t h e p rob ability that the i th file is stored in the cache. Further , t h e process Φ m consists of two sub-PPPs ( i.e., Φ L m i and Φ N m i ). Init i ally , it i s necessary to calculate the density o f Ψ i = { r α j x i ( , || ψ q || ) } = {| | y i,q || α j } , where i ∈ S , q ∈ N , j ∈ {L , N } . By using the m apping theorem, the intensity measure of the process Ψ i is gi ven by Ψ i ([0 , ψ ]) = X j ∈{L , N } Z ψ 1 α j 0 λ m p j p m i 2 π r d r , (64) = X j ∈{ L,N } c j 2 π λ m p m i ( − 1 β ) ψ 1 α j exp ( − β ψ 1 α j ) + 1 β ( exp − β ψ 1 α j ) − 1 + λ m p m i π ψ 2 α N , 28 where c j ∈ {− 1 , 1 } , c L = 1 , c N = − 1 . Then the density is gi ven b y λ Ψ i ( ψ ) = d Ψ i ([0 , ψ ]) d ψ ( a ) = X j ∈{L , N } c j λ m p m i 2 π ( − 1 β ) n ( 1 α j ) ψ ( 1 α j − 1) exp ( − β ψ 1 α j ) + ψ 1 α j exp ( − β ψ 1 α j )( − β 1 α j ) ψ ( 1 α j − 1) o + λ m p m i 2 π ( − 1 β 2 ) exp ( − β ψ 1 α j ) − β 1 α j ψ ( 1 α j − 1) + λ m p m i π 2 α N ψ 2 α N − 1 = X j ∈{L , N } c j λ m p m i 2 π ( 1 α j ) exp ( − β ψ 1 α j ) ψ ( 2 α j − 1) + λ m p m i π 2 α N ψ 2 α N − 1 ( b ) = X j ∈{L , N } c j λ m p m i π δ m j exp ( − β ψ δ m j 2 ) ψ ( δ m j − 1) + λ m p m i π δ m N ψ δ m N − 1 . (65) Here, (a) follows from substi tuting p L = exp ( − β r x i ) , p N = 1 − exp ( − β r x i ) and (b) follows from the fact that δ m j = 2 α j . No w , the density of the process Ω i = { r α j X x i ( , || y i,q || α j X x i ) } = {|| ω q ||} is acquired according to the displacement theorem. Below we show its deri vation. But, first we giv e the joint probability of ψ q and X x i as P [ ψ X x i ≤ ω ] = P [ X x i ≥ ψ ω ] = 1 − F X ( ψ ω ) . (66) Due to the f act that the integral of pdf is its cdf, the joint p robability is g iv en by f ( ψ , ω ) = d 1 − F X ( ψ ω ) d ω = ψ ω 2 f X ( ψ ω ) = ψ ω 2 ˆ m ˆ m ( ψ ω ) ˆ m − 1 exp ( − ˆ m ( ψ ω )) Γ( ˆ m ) . (67) According to the di s placement theorem, we use t h e above joi n t prob ability t o calculate the density of the p rocess Ω i , which is gi ven by λ Ω i ( ω ) = Z ∞ 0 λ ( ψ ) f ( ψ , ω ) d ψ = Z ∞ 0 X j ∈{L , N } c j π λ m exp ( − β ψ δ m j 2 ) p m i δ m j ψ ( δ m j − 1) + λ m p m i π δ m N ψ δ m N − 1 ! × ψ ˆ m ˆ m ( ψ ω ) ˆ m − 1 exp − ˆ m ( ψ ω ) ω 2 Γ( ˆ m ) d ψ = X j ∈{L , N } c j p m i λ m δ m j ˆ m ˆ m π ω ( ˆ m +1) Γ( ˆ m ) Z ∞ 0 ψ ( δ m j + ˆ m − 1) exp ( − ˆ m ω ψ − β ψ δ m j 2 ) d ψ + p m i λ m π δ m N ω δ m N − 1 Γ( δ m N + ˆ m ) ˆ m δ m N Γ( ˆ m ) . (68) Now , according to the complementary v oid function, the CDF of ω q can be gi ven as F Ω i ( ˜ ω ) = P [ ω q < ˜ ω ] = 1 − P Ω i [0 , ˜ ω ) = 0 . (69) 29 Since the displ acement theorem and mappi ng theorem o f a PPP is stil l a PPP , P [Ω i [0 , ˜ ω ) = 0] = exp [ − R ˜ ω 0 λ Ω i ( ω ) d ω ] . Acc ordingly , the CDF of ω q can be giv en as F Ω i ( ˜ ω ) = 1 − e xp − X j ∈{L , N } k j p m i Z j ( ˜ ω ) − ˆ k p m i ˜ ω δ m N , ( 70) where Z j ( ˜ ω ) = R ∞ 0 R ˜ ω 0 exp ( − ˆ m ω ψ ) ω ( ˆ m +1) d ω ψ ( δ m j + ˆ m − 1) exp ( − β ψ δ m j 2 ) d ψ and shoul d be a pos itive va lue due to the form of the integrand, ˆ k = π λ m Γ( δ m N + ˆ m ) Γ( ˆ m ) ˆ m δ m N , and k j = c j π λ m ˆ m ˆ m δ m j Γ( ˆ m ) . No w , according to (63) and (70), t he ASP of file delivery in mmW a ve network can be written as P [ γ SNR m x i ≥ Q i ] = F Ω i ( P m G x i Q i σ 2 m x i ) = 1 − exp − X j ∈{L , N } k j p m i Z j P m G x i Q i σ 2 m x i − ˆ k p m j ( P m G x i Q i σ 2 m x i ) δ m N (71) Finally , we ca n generate the ove rall prob abi lity from (63) as P mm s ( ν i ) = X L i =1 f i h 1 − exp − X j ∈{L , N } k j p m i Z j η i G x i Q i − ˆ k p m i η i G x i Q i δ m N i , (72) where k j = c j π λ m ˆ m ˆ m δ m j Γ( ˆ m ) , η i = P m σ 2 m x i , p j ∈ { p L , p N } , δ m j = 2 α j , ∀ j ∈ { L , N } . R E F E R E N C E S [1] Erricson, “Mobile data traffic growth outlook, ” htt ps:// www .eri csson.com/en/mo bility-report/reports/nov ember-2017/mob ile- data-traffic-gro wth-outlook, Nov . 2017. [2] N. Golrezaei et al. , “Femtocaching and de vice-to-device collaboration: A ne w architecture for wireless video distribution, ” IEEE Commun. Mag. , vol. 51, no. 4, pp. 142–149, Apr . 2013. [3] N. Bhushan et al. , “Network densification: the dominant theme for wireless ev olution into 5G, ” IEEE Commun. Mag. , vol. 52, no. 2, pp. 82–89, F eb . 2014. [4] J. Song, H. S ong, and W . Choi, “Optimal caching placement of caching system wit h helpers, ” in Pr oc. IEEE Int. Conf. Commun. (ICC) , Jun. 2015, pp. 1825–1830. [5] S. H. Chae and W . Choi, “Caching placement in stochastic wireless caching helper networks: Channel selection div ersity via caching, ” IEEE T rans. W ireless Commun. , vol. 15, no. 10, pp. 6626–6 637, Oct. 2016. [6] T . Koh onen, Content-addr essable memories . S pringer Science & Business Media, 2012. [7] G. Ananthanarayanan et al. , “Pacman: coordinated memory caching for parallel jobs, ” in Pr oc. 9th USENIX Conf. Netw . Syst. Des. Implementation (NSDI) , Apr . 2012, pp. 20–20. [8] G. Paschos et al. , “Wireless caching: T echnical misconceptions and business barriers, ” IEEE Commun. Mag. , vol. 54, no. 8, pp. 16–22, Aug. 2016. [9] E. Bastug et al. , “Living on the edg e: The role of proactiv e cach ing in 5G wireless networks, ” IE E E C ommun. Mag. , vol. 52, no. 8, pp. 82–89, Aug. 2014. [10] M. Mitici et al. , “Optimal deployment of caches in the plane, ” in Proc. IE E E Global Signal Inf. Process. (GlobalSIP) , Dec. 2013, pp. 863–866. [11] A. Altieri et al. , “On fundamental trade-of fs of de vice-to-device communication s in large wireless networks, ” IEEE T rans. W ir eless Commun. , vol. 14, no. 9, pp. 4958–4971, Sep. 2015. 30 [12] M. Ji, G. Caire, and A. F . Molisch, “Fundamental limits of caching in wireless D2D networks, ” IE EE T rans. Inf. Theory , vol. 62, no. 2, pp. 849–869, F eb . 2016. [13] S . T . ul Hassan et al. , “Caching in wireless small cell networks: A storage-bandwidth tradeoff, ” IEEE Commun. Lett. , vol. 20, no. 6, pp. 1175–117 8, Jun. 2016. [14] S . P . Shariatpanahi, H. Shah-Mansouri, and B. H. Khalaj, “Caching gain in wireless networks with fading: A multi-user di versity perspectiv e, ” in Pr oc. IEE E W ire less Commun. Netw . Conf. (WCNC) , Apr . 2014, pp. 930–935. [15] N. Golrezaei et al. , “Base-station assisted device-to-de vice communications for high-throughput wireless video networks, ” IEEE Tr ans. W ir eless Commun. , vol. 13, no. 7, pp. 3665–3676, Jul. 2014. [16] M. Akdeniz et al. , “Millimeter wav e picocellular system e v aluation for urban deployme nts, ” in Proc. IEEE Global Commun. Conf. (Globecom) W orkshop s , Dec. 2013, pp. 105–110. [17] T . Bai, R. V aze, and R. W . Heath, “ Analysis of blockage ef fects on urban cellular netwo rks, ” I E EE T rans. W ir eless Comm. , vol. 13, no. 9, pp. 5070–508 3, Jun. 2014. [18] S . Singh et al. , “Trac table model for rate in self-backhauled mil limeter wav e cellular networks, ” I E EE J. Select. Areas Commun. , vol. 33, no. 1, pp. 2196–2211, Jan. 2015. [19] G. R. MacCartney and T . S. Rappapo rt, “Rural macrocell path loss models for millimeter wav e wireless communications, ” IEEE J. Sel. Are as Commun. , vol. 35, no. 7, pp. 1663–1677, Jul. 2017. [20] E . T urgut and M. C. Gursoy , “Cov erage in heterogeneous downlink millimeter wave cellular networks, ” IEEE T rans. Commun. , vol. 65, no. 10, pp. 4463–4477, Oct . 2017. [21] B . Liu, Z. Liu, and D. T owsle y , “On the capacity of hybrid wireless netwo rks, ” i n Pr oc. IEEE Int. Conf. Comput. Commun. (INFOCOM) , Mar . 2003, pp. 1543–15 52. [22] A. Zemli anov and G. de V eciana, “Capacity of ad hoc wireless networks with i nfrastructure support, ” IEEE J. Sel. Ar eas Commun. , vol. 23, no. 3, pp. 657–667, Mar . 2005. [23] Y . Pei , J. W . Modestino, and X. W ang, “On the throughput capacity of hybrid wireless networks using an l-maximum-hop routing strategy , ” in Pro c. IEEE V eh. T echnol. Conf. (V TC) , Oct. 2003, pp. 2173–2176. [24] P . L i, C. Zhang, and Y . Fang, “Capacity and delay of hybrid wireless broadband access networks, ” IEE E J. Sel. Areas Commun. , vol. 27, no. 2, pp. 117–125, Feb. 2009. [25] G. Zhang et al. , “Capacity of content-centric hybrid wireless networks, ” IEEE Access , vol. 5, pp. 1449–1459, Feb . 2017. [26] S . V uppala, S. Biswas, and T . Ratnarajah, “ An analysis on secure communication in millimeter/micro-wav e hybrid networks, ” IEEE Tr ans. Commun. , vol. 64, no. 8, pp. 3507–35 19, Aug. 2016. [27] H. E lshaer et al. , “Do wnlink and uplink cell association with traditional macrocells and millimeter wav e small cells, ” IEEE T rans. W ireless Commun. , vol. 15, no. 9, pp. 6244–62 58, S ep. 2016. [28] H. S. Jo et al. , “Heterogeneous cellular networks with flexible cell association: A comprehensi ve downlink sinr analysis, ” IEEE Tr ans. W ir eless Commun. , vol. 11, no. 10, pp. 3484–3495, Oct. 2012. [29] M. Penrose, Random geometric graphs . Oxford Uni versity Press, 2003. [30] T . Bai and R. W . Heath, “Cov erage and rate analysis for milli meter-wa ve cellular networks, ” IEE E T rans. W ireless Commun. , vol. 14, no. 2, pp. 1100–111 4, Feb . 2015. [31] A. Thornbur g, T . Bai, and R. W . Heath, “Performance analysis of outdoor mmwave ad hoc networks, ” IEEE T rans. Signal Pr ocess. , vol. 64, no. 15, pp. 4065–4079 , Aug. 2016. [32] S . B iswas et al. , “On the performance of relay aided millimeter wav e networks, ” IEEE J. Sel. T op ics Signal Pro cess. , vol. 10, no. 3, pp. 576–588, Apr . 2016. 31 [33] M. R. Akdeniz et al. , “Millimeter-wa ve channel modeling and cellular capacity ev aluation, ” IEEE J. Select. Ar eas Commun. , vol. 32, no. 6, pp. 1164–117 9, Jun. 2014. [34] S . Singh, H. S. Dhillon, and J. G. Andre ws, “Of floading in heterogeneou s netwo rks: Modeling, analysis, and design insights, ” IEEE T rans. W ireless Commun. , vol. 12, no. 5, pp. 2484–24 97, May . 2013. [35] D. Maamari, N. Devro ye, and D. T uninetti, “Coverage in mmwav e cellular networks with base stati on co-operation, ” IEEE T rans. W ireless Commun. , vol. 15, no. 4, pp. 2981–29 94, Apr . 2016. [36] M. Haenggi, Stochastic Geometry for W ireless Networks . Cambridge Unive rsity Press, 2012. [37] X. S hen et al. , “Disciplined con vex -conca ve programming, ” i n Pro c. IE EE 55th Conf. Decis. Control (CDC) , Dec. 2016, pp. 1009–1 014.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment