Secrecy Outage of Proactive Relay Selection by Eavesdropper
In this paper, we consider an active eavesdropping scenario in a cooperative system consisting of a source, a destination, and an active eavesdropper with multiple decode-and-forward relays. Considering an existing assumption in which an eavesdropper…
Authors: Sarbani Ghose, Chinmoy Kundu, Octavia A. Dobre
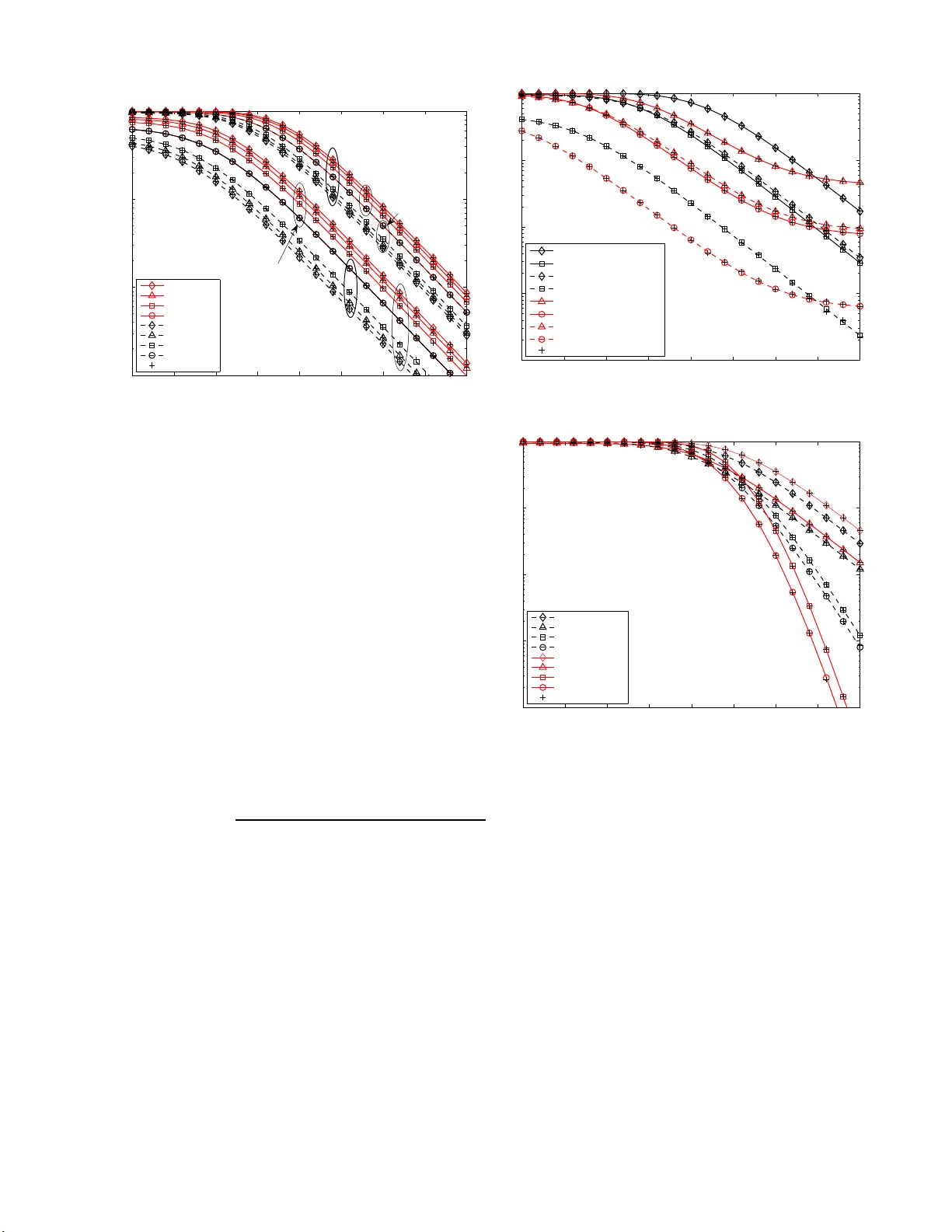
Secrec y Outage of Proacti v e Relay S election by Ea ve sdropper Sarbani Ghose ∗ , Chinmoy Kundu † , and Octa via A. Dobre ‡ ∗ Cryptolog y and Security Research Unit, I ndian Statistical Institute, K o lkata 700108 , India † School o f E lectronics, Electrical Engineer ing and Computer Science, Queen’ s University Belfast, U.K. ‡ Faculty of Eng ineering an d Ap plied Scien ce, M emorial University , St. John ’ s, NL A1B 3X5 , Can ada ∗ sarbani_v @isical.ac.in, † c.kund u@qub.ac.uk, ‡ odobr e@mun.ca Abstract —In this p aper , we consid er an active ea vesdr opping scenario in a cooperative system consistin g of a source, a des- tination, and an active eav esdropper with multip le decode-and- fo rward relays. Considering an existing assumption in which an ea vesdr opper is also a p art of network, a proactiv e relay selection by the eav esd ropper is proposed. The best relay which maximizes the eav esdropping rate is selected by th e eav esd ropper . A relay selection scheme is also proposed to imp ro ve the secrecy of the system by minimizing the eav esdropping rate. Performances of these schemes are compared with two passiv e ea vesdr opping sce- narios in which the ea vesdropper perfo rms selection and maxima l ratio combining on th e relay ed links. A realistic channel model with in dependent non-identi cal links between nodes and direct links from the source to both the destination and ea vesdr opper are assumed. C losed-fo rm expressions f or t he secrecy outage probability (S OP) of these schemes in Rayleigh fadin g channel are obtained. It is shown that the relay selection by the proactiv e ea vesdr opper is most detrimental to the system as not only the SOP increases with the increase i n the number of relay s, but its divers ity also remains un changed. Index T erms —Activ e ea vesdr opping, cooperativ e system, Decode-and-forwa rd relay , relay selection, secrecy outage p rob- ability . I . I N T RO D U C T I O N Due to the inh erent open ness of wireless med ium, wireless networks are vulnerab le to illegitimate eav esdropp ing. Over recent y ears, phy sical layer secur ity has become a promising technique to secure wireless com munication s by utilizing the physical ch a nnel pro perties of both legitimate and illegitimate users [1]–[3]. Based on th e classical wiretap ch a nnel framework, various cooper a tive transmission techniques using r elays ha ve been developed against eav esdroppin g. Relays can cooperate mainly in three schemes or a mixture of these schemes: i) cooperative beamfor ming [4], ii) coo p erative jamm in g [5], and iii) relay selection [6]–[16]. In cooperative b eamform ing, all relays perfor m distributed b eamform ing towards the legitimate user to transmit their r eceiv ed signal. In coo perative jamming, they transmit interferen ce or jamm in g signal to c o nfuse the illegitimate user . These techn iques re quire com plex signal processing to find beamf orming o r jam ming signal vectors at the transmitters or receivers. Deviating from the former two cases, relay selection schemes select simply th e best relay (ba sed on different definitions of being the best r elay) among se veral r elays to forward the receiv ed sign al tow ards the legitimate user [6]– [16]. Based on global instantaneous channel state informatio n (ICSI) o r statistical channel state info rmation (SCSI) o f the links, optimal and suboptimal relay selection schemes are developed. It is also shown that some o f these r e la y selection schemes can ach ieve full secrecy d iv ersity . A major assum p- tion wh ile a c hieving glob al ICSI in these works is that the eav esdropp er is another active user in the wireless network [3], [1 7], and h ence, logic a lly there is no difference between a legitimate or illegitimate user cap ability . It is also to be noted that in all p reviously mention ed literature , relay selection schemes are developed against eav esdroppin g to safeguard the legitimate com municatio n . The literature ab ove assumes that ea vesdropper s only listen to a transmission intend ed for th e legitimate user . Recen tly , a ne w kind of adversary is introd u ced in secrecy , which proactively attacks th e sy stem to en hance its eav esdropp in g perfor mance [18]–[26]. I n [18]–[20], a jamming signal is transmitted to degrade the received sign al qu ality o f the legitimate user when simultan eously eav esdropp ing. While [18], [19] stud y m ethods to counter activ e eavesdropping , [20] utilizes pro activ e eaves dropp ing for surveillance. In pilot contamina tio n attack [2 1], the ea vesdropper sends identical deterministic pilots as the legitimate rece i ver in the channel training phase of a multi-an tenna time- division du plexing sys- tems, as opposed to random jammin g signal. T he beamf ormer designed by the transmitter o n this basis will significan tly compro mise infor mation to the ea vesdropper . In the spoofing relay attack proposed in [22], [23], the eavesdropper acts as a relay to spoo f the source to change its rate in fa vour o f eav esdropp ing. Detection of such spoofing attack is stud ied in [24]. Activ e eav esdropp ing is also studied in massive mu ltiple- input multiple-o utput system in [25], [26]. In the above pro activ e eav esdropp ing literature, the eaves- dropp er jams, co ntaminates the pilot, or spoofs the desired informa tio n sign a l f rom the source ; howe ver, it doe s n ot ac- ti vely select the inf ormation source . I n a coope rativ e network where multiple relays are used to co n vey th e message from an info rmation source, an eavesdropper can proactively select the best r e lay to its benefit. Being a part of the network, an eav esdropp er either can p retend to b e a legitimate destina tio n and there by compro mise the secrecy of the system, or can be a legitimate user with a surveillance ob jectiv e. An eavesdropper proactively selecting a relay and its consequen c es on the secrecy of the system has n ot b een studied so far in th e literature. Motiv a te d b y the above discussion, we have considered a cooper ativ e network where m ultiple decode- and-fo rward (DF) relays can b e used by a so urce to conve y its message to a destination . An eavesdropper p roactively selects the best relay to incr ease its e avesdroppin g inf ormation rate. A realistic scenario is considered where both th e destination and eav esdropp er receive the direc t co mmunica tio n from the source; howe ver, the links between nod e s ar e independen t non- identically distributed. The main contribution of this pape r in three fold: 1) W e propose a pro activ e relay selection by the ea ves- dropp er to en hance its eavesdropping capab ility . Su ch a scenario is is not considered y et in the literature; 2) W e also stud y two passi ve ea vesdropping schem es, where th e ea vesdropper selects the best relayed lin k in one sch e me and m aximally com bines all the relay e d links in the anoth e r sche m e for comparison with the propo sed active eavesdroppin g . In addition , a passi ve relay selection schem e based on the eaves dropp er’ s channel quality is studied to improve secrecy from the system’ s point of view for the comp arison purp ose; 3) W e consider a mor e general chan nel mod el where links between nodes are independe nt non-id entically distributed, as well as with direct links from the source to the destination and eaves dropp er . 1 The remain der of the pap er is organiz e d as follows. Sec- tion I I describes the sy stem mod el. Section II I ev a lu ates the secrecy outage prob ability for different proactive and pa ssive eav esdropp ing schemes. The nume r ical results are p resented in Section IV, and conclusions are drawn in Section V. Notation: P [ · ] is the p robability of o ccurren c e of an e vent, E X [ · ] defines the expectation o f its argument over th e ran dom variable (r .v .) X , [ x ] + , max(0 , x ) and max ( · ) den otes the maximum of its argu ment, F X ( · ) repr esents th e cumu lati ve distribution fun ction ( CDF) of the r .v . X , and f X ( · ) is th e correspo n ding proba b ility density function (PDF). I I . S Y S T E M M O D E L W e con sider a c ooperative system with a sour c e ( S ), a destination ( D ), N DF relays ( R k , k ∈ { 1 , · · · , N } ) and an ea vesdropper ( E ), as shown in Fig. 1. There exists dir e ct commun ication links from S to D and E . All the links between nod es are modeled as indep endent non-iden tically distributed Rayleigh fading cha nnel af fec te d by cir cularly sym- metric in depend ent ad d itiv e white Gaussian noise (A WGN). The signal-to -noise ratio ( SNR) of the links be tween S - R k , R k - D , S - D , R k - E , an d S - E are denoted as γ sk , γ kd , γ sd , γ ke , and γ se . As th e links are Ray leig h faded, correspo nding 1 Most of the literature in relay selection to improv e security assumes indepen dent identic al links, wit hout dir ect links from the source to the destina tion and eave sdropper [6]–[12], [14 ]. Some exce ptions can be found in [13], [15], [16], which conside r either direct links or non-identic al links or both. Fig. 1. System model. SNRs ar e exponen tially d istributed with par a meters β sk , β kd , β sd , α ke , and α se , respec tively , wh ere E { γ } = 1 /β . 2 In the first time slot when S br oadcasts its message, it is r e ceiv ed b y R k , ∀ k , D an d E . In proactive relay selection by eavesdropper, E selects the b est relay which ma ximizes its info rmation rate or equiv alently its link SNR and dir ects it to retransmit in the second tim e slot. The achiev able secr ecy rate o f the system is defin ed as [1], [2], C s , 1 2 log 2 1 + γ M 1 + γ E + , (1) where γ M and γ E are the SNRs at D and E , re spectiv ely , after maximal-ra tio-comb in ing (MRC) the dire ct an d relayed transmission in the second time slot. Th e multiplier 1 / 2 is for the required two tim e slots to com plete th e co mmunicatio n process. For the DF relay system , the rate of a dual-ho p link is lim ited by the minimum o f the individual ho p rates. This is equiv alent to the minim um of th e in dividual hop SNRs. The secrecy rate of a single DF relay , i.e., o n ly fo r the k th relay , following [8], [13] is C k s = 1 2 log 2 1 + γ kD + γ sd 1 + γ ke + γ se + , (2) where γ kD = min ( γ sk , γ kd ) . T he distribution of γ kD is also exponential with par ameter β kD = β sk + β kd . I I I . S E C R E C Y O U TAG E P RO B A B I L I T Y The secrecy ou ta g e prob ability (SOP) is define d as the probab ility that achiev ab le secrecy ca p acity is below a certain threshold secrecy rate P o ( R s ) = P [ C s < R s ] = P 1 + γ M 1 + γ E ≤ ρ , (3) where R s is the threshold secrecy rate and ρ = 2 2 R s . A. Pr oa ctive Re lay S election b y E ( MAX-E) In this scheme, E selects the k th relay for which the R k - E link SNR is maximum. Once the relay is selected by E , R k decodes th e signa l rece i ved from S an d b roadcasts it. The SOP of the system ca n b e derived from (3) by find ing th e probab ility of the selection of the b est relay and then finding 2 The subscript denoting a particular path is omitted to show the genera l case. the SOP if the p articular relay is selected. By summ ing up all, SOP is obtained following the law o f to tal probab ility as P o ( R s ) = N X k =1 P γ ke > γ − ke P 1 + γ sd + γ kD 1 + γ se + γ ke < ρ , (4) where γ − ke = max i =1 ,...,N i 6 = k { γ ie } denote s the max imum SNR among the rest of the ch annels receiv ed by E except th e k th one. The PDF of γ − ke can be ob tained from the CDF of γ e = max k =1 ,...,N { γ ke } f ollowing [13] as F γ e ( x ) = 1 + N X m =1 ( − 1) m X m e − xα ′ m , (5) where X m = N − ( m − 1) X i 1 =1 N − ( m − 2) X i 2 = i 1 +1 · · · N − 1 X i m − 1 = i m − 2 +1 N X i m = i m − 1 +1 , (6) and α ′ m = P m l =1 α i l e . The PDF o f the r .v . γ − ke can be expressed in the easily realizab le sum mation f orm as f γ − ke ( x ) = − N − 1 X m =1 ( − 1) m X ′ m α ′ m e − xα ′ m , (7) where X ′ m = N − ( m − 1) X i 1 =1 i 1 6 = k N − ( m − 2) X i 2 = i 1 +1 i 2 6 = k · · · N − 1 X i m − 1 = i m − 2 +1 i m − 1 6 = k N X i m = i m − 1 +1 i m 6 = k . (8) Then, we can ev alu ate (4) as follows P o ( R s ) = N X k =1 P γ ke > γ − ke P γ ke > γ sd + γ kD − ργ se − ( ρ − 1) ρ = N X k =1 [ I 1 + I 2 + I 3 ] . (9) Assuming X = γ kD + γ sd , Z = γ se and λ = x − z ρ − ( ρ − 1) ρ , finally I 1 , I 2 and I 3 are expressed in the integral forms in (17), (19), and (21), respectively . For the distribution of the r .v . X , which is the sum o f two indep endent n o n-iden tica lly exponentially distributed r .v . s, we fo llow [27], wher e B 1 = β kD β sd β kD − β sd and B 2 = β kD β sd β sd − β kD . B. Relay Selection by the System to Minimize Ea vesdr op ping Rate (MIN-E) The eavesdropper in this section is assumed to b e passive. The system selects the relay to en hance its secrecy by ch o osing the lowest q uality link to E only . This mea ns that the relay having minimum instantan eous SNR am ong all the link s tapped b y E is selected. Following the law of to tal pro bability , the SOP can b e o btained as P o ( R s ) = N X k =1 P γ ke < γ − ke P 1 + γ sd + γ kD 1 + γ se + γ ke < ρ = N X k =1 P γ ke < γ − ke P γ ke > γ sd + γ kD − ργ se − ( ρ − 1) ρ , (10) where γ − ke = min i =1 ,...,N i 6 = k { γ ie } . The PDF of the r . v . γ − ke can b e easily obtain e d from the definition of CDF and d ifferentiating it as f γ − ke ( y ) = α exp ( − αy ) , (11) where α = P N i =1 i 6 = k α ie . Then ( 10), can be e valuated as P o ( R s ) = N X k =1 P γ kD + γ sd − ργ se − ( ρ − 1) ρ ≤ γ ke ≤ γ ke − = N X k =1 [ I 4 + I 5 ] . (12) For the d eriv atio n above, we assume X = γ kD + γ sd and λ = x − ρz − ( ρ − 1) ρ . I 4 and I 5 can b e expressed in the integral form in (23) and (25), respectively . Th eir so lu tions c a n b e stated in (24) and (2 6), where B 1 = β kD β sd β kD − β sd and B 2 = β kD β sd β sd − β kD are due to th e PDF of X . C. Best Relay ed Link Selection a t E while MR C at D (MAX- MRC) In this section E is a ssumed to be a passi ve listener . In the first time slot, E simply cho oses the best r elayed lin k amo ng all, and performs MRC with the direct transmission. No relay selection is in volved. D perfor m s MRC with all the relaye d and direct links re ceiv ed by it in the first and second time slots. From (3), we o btain the SOP of th e system as P o ( R s ) = P " 1 + γ sd + P N k =1 γ kD 1 + γ se + γ e < ρ # = 1 − P " γ e ≤ P N k =0 γ kD − ργ se − ( ρ − 1) ρ # = 1 − Z ∞ 0 Z ∞ ρz + ρ − 1 F Y ( λ ) f X ( x ) dxf Z ( z ) dz . (13) For th e derivation above, we assume γ e = max ∀ k γ ke , γ 0 D = γ sd , Y = γ e , X = P N k =0 γ kD , Z = γ se , and λ = x − z ρ − ( ρ − 1) ρ . For the PDF of X , we follow th e PDF o f the sum of N + 1 indepen d ent no n-identically d istributed exp o nential r .v .s from [27] as, f ( t ) = N X i =1 Q N j =1 λ j Q N j =1 j 6 = i ( λ j − λ i ) e − tλ i , (14) where λ i , ∀ i , ar e the param eters of th e exponential distribu- tion. W e su bstitute the CDF of γ e and PDF o f X fro m (5) 0 5 10 15 20 25 30 35 40 10 −3 10 −2 10 −1 10 0 SNR P o ( R s ) N = 4, MAX−E N = 3, MAX−E N = 2, MAX−E N = 1, MAX−E N = 4, MIN−E N = 3, MIN−E N = 2, MIN−E N = 1, MIN−E Simulation R s = 1 MAX−E MIN−E R s = 0 MAX−E MIN−E Fig. 2. SOP ver sus SNR of MAX-E and MIN-E for dif ferent N and R s v alues, with 1 /α ke = 3 d B, ∀ k , 1 /β sd = 3 dB, 1 /α se = 0 d B, and 1 /β sk = 1 / β kd . and (1 4), respec ti vely , in (13) to obtain th e SOP expression in (27). D. MRC of All Relayed Links with the Dir ect Links at E and D (MRC-MRC) This section discusses the SOP when E and D b oth combine signals re c e i ved in the first and second time slots using MRC. The SNRs at D a n d E are γ M = γ sd + P N k =1 γ kD and γ E = γ se + P N k =1 γ ke , respecti vely . The SOP of the MRC-MRC technique can be obtained from (3) as P o ( R s ) = Z ∞ 0 F γ M ( ρx + ρ − 1) f γ E ( x ) dx. (15) For the distribution of γ M and γ E , we u se the PDF of the sum of N + 1 independent non-id entically d istributed r .v .s [2 7]. Substituting the CDF and PDF , SOP can be ev alu ated as P o ( R s ) = Z ∞ 0 N +1 X i =1 N +1 X p =1 Q N +1 j =1 j 6 = i β j D Q N +1 q =1 α qe Q N +1 j =1 j 6 = i ( β j D − β iD ) Q N +1 q =1 , q 6 = p ( α qe − α pe ) × (1 − exp [ − β iD ( ρ − 1 + ρx )]) e − α pe x dx, (16) whose solution is shown in (28). I V . N U M E R I C A L R E S U LT S In th is section, numerical r esults are plotted alon g with sim- ulation results to verify the an alytical fin d ings. It is assum ed that the A WGN affects all recei ving nodes equally . Unless otherwise specified, P o ( R s ) is plotted against SNR with SNR divided eq ually between S − R k and R k − D , ∀ k . Th e direct link a vera g e SNRs are con sidered as 1 /β sd = 3 dB and 1 / α se = 0 dB. Th e requir ed thr eshold R s is assumed either 0 or 1 bits p er channel use ( bpcu). Sec r ecy outag e probab ility with R s = 0 provide s the intercept probability by E , a s an interc e p t event occurs when the secrecy cap a city 0 5 10 15 20 25 30 35 40 10 −4 10 −3 10 −2 10 −1 10 0 SNR P o ( R s ) MAX−E, R s = 1, BALANCED MIN−E, R s = 1, BALANCED MAX−E, R s = 0, BALANCED MIN−E, R s = 0, BALANCED MAX−E, R s = 1, UNBALANCED MIN−E, R s = 1, UNBALANCED MAX−E, R s = 0, UNBALANCED MIN−E, R s = 0, UNBALANCED Simulation Fig. 3. SOP versus SNR of MAX-E and MIN-E in balance d ( 1 /β sk = 1 /β kd ) and unbalan ced case ( 1 /β sk = 30 dB) with 1 /α ke = { 0 , 3 , 6 , 9 } dB, k = 1 , · · · , 4 , 1 /β sd = 3 dB, 1 /α se = 0 dB. 0 5 10 15 20 25 30 35 40 10 −4 10 −3 10 −2 10 −1 10 0 SNR P o ( R s ) N = 2, MAX−E N = 2, MIN−E N = 2, MRC−MRC N = 2, MAX−MRC N = 4, MAX−E N = 4, MIN−E N = 4, MRC−MRC N = 4, MAX−MRC Simulation Fig. 4. SOP versus SNR of all schemes for N = 2 , 4 with R s = 1 bpcu, 1 /β sd = 3 dB, 1 /α se = − 3 dB, and having all other channe l parameters non-iden tical . becomes negative [8] . These particular param eter values are only for th e illustration p u rpose. Other values provide the same trend in the figu re; results are not included here d ue to space limitations. Fig. 2 compar es th e pr o posed relay selection schemes, MAX-E a n d MIN-E, by in c reasing N from 1 to 4 . Ea vesdrop- ping link average SNRs are consider ed equa l w ith 1 /α ke = 3 dB, ∀ k . It can be obser ved th a t not only P o ( R s ) is worse for MAX-E, but it also increases with the increase in N , while it decreases f or M IN-E. MAX-E is exactly the requiremen t from the E ’ s perspective; howe ver , it is d etrimental to th e system which tries to a void eavesdropping . Moreover , it can be seen that p erform ances do not change equally with the increase in N . The ch ange is more when N is in creased f rom 1 to 2 ; thereafter, th e changes diminish with subsequent increase in N . In addition, it is noticed that though N increases, the slopes of the curves do not ch ange. Fu rthermo re, it is also observed that SOP incr eases with the increase in R s . Ho wev er , N affects less at highe r R s as curves for R s = 1 are more closely spaced than R s = 0 . Fig. 3 com pares MAX-E and MIN-E for N = 4 when the eavesdroppin g link average SNRs are all different, i.e. , 1 /α ke = 0 , 3 , 6 , and 9 dB, respectively , for k = 1 , · · · 4 . T wo cases are d epicted: balanced and unbalan c e d. In the b alanced case, 1 /β sk = 1 /β kd , ∀ k , whereas, in the unb alanced case 1 /β sk = 30 dB, ∀ k , 1 /β kd , ∀ k , increases as SNR in the x -a x is. It can be observed that in the balanced case, the performa n ces improve with SNR; on the co ntrary , in the unb alanced case, the perform ances satur ate depending on the SNR of the S − R k links. In the DF relay systems, the dual hop SNR is constra in ed by the minimum of th e ind ividual ho p SNRs, an d hence, th e observation. The o bservation would have been similar if 1 /β kd had been fixed to a particu lar SNR as well. Fig. 4 compares the p erform a nces of all schem es when each of the S − R k − D bran ch effecti ve SNRs, a s well as all the eav esdropp ing lin k average SNRs are dif ferent fo r N = 2 and N = 4 , r espectively . When N = 2 , 1 / α ke = 6 , 9 dB for k = 1 , 2 , whereas when N = 4 , 1 /α ke = 0 , 3 , 6 , 9 dB, for k = 1 , · · · , 4 . 1 /α se = − 3 dB is con sidered to make it d ifferent from other eavesdropping link s. A balanced case, i.e., 1 /β sk = 1 / β kd is co nsidered. When N = 2 , 1 /β sk is assumed to be 20 % and 3 0% fo r k = 1 , 2 , r espectively , of the SNR represen ting x -axis. When N = 4 , 1 /β sk is assumed to be 5 , 10, 15 , an d 20% for k = 1 , · · · , 4 , respectively , to make the total S − R k − D , ∀ k , lin k SNRs 100%. It is observed that for a given N , the proactive relay selection by E , MAX-E, is the worst for the system, although the b est for E . Though , both MAX-E and MAX- M RC select the max imum eavesdropping channel quality for them, the proactive eavesdropping is better than the p assi ve eavesdrop- ping fro m E ’ s p erspective. The b est scheme fo r the sy stem secrecy is MAX-MRC as D perf orms MRC c o mbining . Fro m E ’ s perspective, MRC-MRC is better th an MAX-MRC as E is able to p erform MRC on the relayed signals. Although the systems with N = 2 and N = 4 are not compara b le as parameters are dif ferent, it can be no ticed that th e secrecy diversity o rder-the slope of the curves at high SNR-remains the same for both MAX-E and MIN-E . P o ( R s ) rema ins p arallel as N incr eases, as seen in Fig. 2. On the contr ary , bo th p assi ve eavesdropping scheme MRC- MRC a n d MAX-MRC benefit from the in crease in N , as the secrecy diversity o rder improves to aid the system secrecy . This conclud es that pr oactive eavesdropping o n the basis of the relay selection is the b est for E . Moreover , the relay selection schem e, MIN-E, to aid the system secrecy based o n the minimum among th e eav esdroppin g link q uality , per forms worse than bo th MAX-M RC an d M RC-MRC. Simulation resu lts exactly m atch the theore tica l o nes, which confirms the validity of the analytical findings. V . C O N C L U S I O N Relay selection is thus far co nsidered to imp rove the se- crecy of the system. Being part of a wireless network, an eav esdropp er migh t p retend to b e a legitimate d estination, and activ ely select a relay to maximize its eavesdropping capability . W e study such an active ea vesdropping scenario, where the eav esdropp er selects the best relay to maxim ize the eavesdropping r ate. Three o ther passi ve ea vesdroppin g scenarios a re also considered f ocusing o n the eav esdropp ing link and ea vesdropping cap ability f or th e comparison purpose. Closed-form expressions for the secr ecy outage prob ability are obtained co nsidering a more realistic scenario of indep endent no-iden tically distributed ch annels and the direct links b etween the source an d both d estination and ea vesdropper . It is con - cluded that the active eavesdropping is the worst for the system secrecy , and the secr ecy outage proba bility decreases with the increase in the num ber o f relays, while the secrecy diversity remains unchan ged. A C K N O W L E D G M E N T This w ork w as supported in part by th e R oyal Society-SERB Newton In ternational Fellowship under Gran t NF151345 , an d by th e Natur a l Science an d Eng ineering Council o f Canad a (NSERC), th rough its Discovery progr a m. R E F E R E N C E S [1] A. D. W yner , “The W ire-T ap Channel, ” Bell Syste m T echnical J ournal , vol. 54, no. 8, pp. 1355–1387, Oct. 1975. [2] S. Leung-Y a n-Cheong and M. Hellman, “The Gaussia n W ire-T ap Chan- nel, ” IEEE T rans. Inf. Theory , vol . 24, no. 4, pp. 451–456, Jul. 1978. [3] M. Bl och, J. Barros, M. R. D. Rodrigues, and S. McLaughl in, “W ireless Information -Theoreti c Security, ” IEE E T rans. Inf . Theory , v ol. 54, no. 6, pp. 2515–2534, Jun. 2008. [4] L. Dong, Z . Han, A. Petropulu, and H. Poor , “Improvin g Wirel ess Physical Layer Security via Cooperating Relays, ” IEEE Tr ans. Signal Pr ocess. , vol. 58, no. 3, pp. 1875–1888, Mar . 2010. [5] S. Goel and R. Negi, “Guaran teeing Secrecy using Artificial Noise, ” IEEE T rans. W irel ess Commun. , v ol. 7, no. 6, pp. 218 0–2189, Jun. 2008. [6] I. Krikidis, “Opportuni stic Relay Selection for Cooperati ve Netw orks with Secrecy C onstraint s, ” IET Commun. , v ol. 4, n o. 15, pp. 1787–1791 , Oct. 2010. [7] I. Krikidis, J. Thompson, and S. McLaughlin, “Relay Selec tion for Secure Coope rati ve Networks with Jamming, ” IEEE T rans. W ir eless Commun. , vol. 8, no. 10, pp. 5003–5011, Oct. 2009. [8] Y . Zou, X. W ang, and W . Shen, “Opt imal Relay Selec tion for Physica l- Layer Security in Cooperat i ve W ireless Networks, ” IEEE J . Sel. A re as Commun. , vol. 31, no. 10, pp. 2099–2111, Oct. 2013. [9] E. R. Alotaibi and K. A. Hamdi, “Rela y Selecti on for Multi-Desti nation in Coopera ti ve Networ ks with Secrecy Constrai nts, ” in Proc. IEEE V ehicular T echnol ogy Confer ence , V ancouve r , Canada, Sep. 2014, pp. 1–5. [10] V . N. Q. Bao, N . Linh-Trung, and M. Debbah, “Rela y Selection Schemes for Dual-Hop Networks under Security C onstraint s with Multiple Eav es- droppers, ” IEEE Tr ans. W ir eless Commun. , vol. 12, no. 12, pp. 6076– 6085, Dec. 2013. [11] L. W ang, K. J. Kim, T . Q. Duong, M. Elka shlan, and H. Poor , “Security Enhancement of Cooperati ve Single Carrier Systems, ” IEEE T rans. Inf. F orensi cs and Securi ty , vol. 10, no. 1, pp. 90–103, Jan. 2015. [12] L. Fan , X. Lei, T . Q. Duong, M. Elkashla n, and G. K. Karagiannidi s, “Secure Multiuser Communications in Multip le Am plify-an d-Forw ard Relay Ne tworks, ” IEEE Tr ans. Commun. , vol. 62, no. 9, pp . 3299–3310, Sep. 2014. [13] C. K undu, S. Ghose, and R. Bose, “Sec recy Outage of Dual-hop Rege nerati ve Multi-R elay System with Relay Select ion, ” IEE E T rans. W ire less Commun. , vol. 14, no. 8, pp. 4614–4625, Aug. 2015. [14] F . S. AL-Qahtani, C. Zhong, and H. Alnuweiri, “Opportuni stic Relay Select ion for Secrec y Enhanceme nt in Coopera ti ve Networks, ” IEEE T rans. Commun. , vol. 63, no. 5, pp. 1756–1770, May 2015. [15] C. Kundu, T . Ngatc hed, and O. Dobre, “Relay Selection to Improv e Secrec y in Cooperat i ve Threshold Decode-and -Forw ard Relayi ng, ” in Pr oc. IE EE G lobal Communication Confer ence , W ashington, DC, USA, Dec. 2016, pp. 1–6. I 1 = Z ∞ 0 Z ∞ ρz + ρ − 1 Z λ 0 Z ∞ λ f γ ke ( t ) f γ − ke ( y ) f X ( x ) f γ se ( z ) dtdy dxdz (17) = − N − 1 X m =1 ( − 1) m X ′ m ρα se B 1 e − β sd ( ρ − 1) ( α ke + ρβ sd ) ( α se + ρβ sd ) + B 2 e − β kD ( ρ − 1) ( α ke + ρβ kD ) ( α se + ρβ kD ) − B 1 e − β sd ( ρ − 1) ( α ke + α ′ m + ρβ sd ) ( α se + ρβ sd ) − B 2 e − β kD ( ρ − 1) ( α ke + α ′ m + ρβ kD ) ( α se + ρβ kD ) . (18) I 2 = Z ∞ 0 Z ∞ ρz + ρ − 1 Z ∞ λ Z ∞ y f γ ke ( t ) f γ − ke ( y ) f X ( x ) f γ se ( z ) dtdy dxdz (19) = − N − 1 X m =1 ( − 1) m X ′ m ρα ′ m α se α ke + α ′ m B 1 e − β sd ( ρ − 1) ( α ke + α ′ m + ρβ sd ) ( α se + ρβ sd ) + B 2 e − β kD ( ρ − 1) ( α ke + α ′ m + ρβ kD ) ( α se + ρβ kD ) . (20) I 3 = Z ∞ 0 Z ρz + ρ − 1 0 Z ∞ 0 Z ∞ y f γ ke ( t ) f γ − ke ( y ) f X ( x ) f γ se ( z ) dtdy dxdz (21) = − N − 1 X m =1 ( − 1) m X ′ m α ′ m α se α ke + α ′ m B 1 α se β sd + B 2 α se β kD − B 1 e − β sd ( ρ − 1) β sd ( α se + ρβ sd ) − B 2 e − β kD ( ρ − 1) β kD ( α se + ρβ kD ) . (22) I 4 = Z ∞ 0 Z ∞ ρz + ρ − 1 Z ∞ λ Z y λ f γ ke ( t ) f γ − ke ( y ) f X ( x ) f γ sd ( z ) dtdy dxdz (23) = α se α ke α + α ke B 1 exp ( − β sd ( ρ − 1)) ( ρβ sd + α se ) ( ( α ke + α ) /ρ + β sd ) + B 2 exp ( − β kd ( ρ − 1)) ( ρβ kd + α se ) ( ( α ke + α ) /ρ + β kd ) . (24) I 5 = Z ∞ 0 Z ρz + ρ − 1 0 Z ∞ 0 Z y 0 f γ ke ( t ) f γ − ke ( y ) f X ( x ) f γ sd ( z ) dtdy dxdz (25) = α ke α + α ke B 1 β sd + B 2 β kD − B 1 α se exp ( − β sd ( ρ − 1)) ( ρβ sd + α se ) β sd − B 2 α se exp ( − β kD ( ρ − 1)) ( ρβ kD + α se ) β kD . (26) P o ( R s ) = 1 − α se N +1 X i =1 Q N +1 j =1 β j D Q N +1 j =1 j 6 = i ( β j D − β iD ) " e − β iD ( ρ − 1) β iD ( α se + ρβ iD ) − N X m =1 ( − 1) m X m ρe − β iD ( ρ − 1) ( α ′ m + ρβ iD ) ( α se + ρβ iD ) # . (27) P o ( R s ) = N +1 X i =1 N +1 X p =1 Q N +1 j =1 j 6 = i β j D Q N +1 q =1 α qE Q N +1 j =1 j 6 = i ( β j D − β iD ) Q N +1 q =1 , q 6 = p ( α qe − α pe ) 1 α pe − e − ( ρ − 1) β iD α pe + ρβ iD . (28) [16] L. F an, N. Y ang, T . Duong, M. Elkashla n, and G. Karagianni dis, “Exploit ing Direct Links for Physical Layer Securi ty in Multi-User Multi-Re lay Netwo rks, ” IEEE T rans. W ir eless Commun. , vol. 15, no. 6, pp. 3856–3867, Jun. 2016. [17] M. R. A. Khandak er, K. K. W ong, and G. Z heng, “Truth-T elling Mechani sm for T wo-W ay Relay Selection for Secrec y Communications with Ener gy-Harv esting Re venue , ” IEE E T rans. W ir eless Commun. , vol. PP , no. 99, pp. 1–1, 2017. [18] G. T . Amariucai and S. W ei, “Half-Duple x Acti ve Eav esdroppi ng in Fast- Fadi ng Channels: A Block-Ma rko v W yner Secrecy Encoding Scheme, ” IEEE T rans. Inf. Theory , vol. 58, no. 7, pp. 4660–4677, Jul. 2012. [19] A. Mukherjee and A. L. Swindlehurst, “Jamming Games in the MIMO W ireta p Channel W ith an Acti ve Eavesdro pper, ” IEEE T rans. Signal Pr ocess. , vol. 61, no. 1, pp. 82–91, Jan. 2013. [20] J. Xu, L. Duan, and R. Zhang, “Proacti ve Eav esdroppi ng V ia Jamming for Ra te Maximiza tion Over Rayl eigh Fadi ng Channels, ” IEE E W irele ss Commun. Lett. , vol . 5, no. 1, pp. 80–83, Feb . 2016. [21] X. Zhou, B. Maham, and A. Hjorungnes, “Pilot Contamina tion for Acti ve Eavesdrop ping, ” IEEE Tr ans. W ir eless Commun. , vol. 11, no. 3, pp. 903–907, Mar . 2012. [22] Y . Zeng and R. Zhang, “ Acti ve Eav esdropping V ia Spoofing Relay Attack, ” in Pro c. IEEE Internationa l Confe re nce on Acoustic s, Speech and Sig nal Proc essing (ICASSP) , Shanghai, China , Mar . 2016, pp. 2159– 2163. [23] ——, “W ireless Information Surveillanc e via Proact i ve E av esdroppi ng with Spoofing Relay, ” IEEE J . Se l. T opics Signal Pr ocess. , vol. 10, no. 8, pp. 1449–1461, Dec. 2016. [24] J. K. Tu gnait, “Detec tion of Acti ve E av esdroppin g Attack by Spoofing Relay in Multiple Antenna Systems, ” IEEE W ireless Commun. Lett. , vol. 5, no. 5, pp. 460–463, Oct. 2016. [25] D. Kapeta novi c, G. Zheng, and F . Rusek, “Physical Layer Security for Massi ve MIMO: An Overvie w on Passi ve Eavesdropp ing and Acti ve Attacks, ” IEEE Commun. Mag. , vol. 53, no. 6, pp. 21–27, Jun. 2015. [26] Y . W u, R. Schober , D. W . K. Ng, C. Xiao, and G. Caire, “Secure Massi ve MIMO Transmission with an Acti ve Eav esdropper, ” IEEE T rans. Inf. Theory , vol . 62, no. 7, pp. 3880–3900, Jul. 2016. [27] M. Akkouchi , “On the Con volution of E xponenti al Distribution s, ” J . Chungc heong Math. Soc. , vol. 21, no. 4, pp. 501–510, Dec. 2008.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment