Artificial Noise Aided Secure Cognitive Beamforming for Cooperative MISO-NOMA Using SWIPT
Cognitive radio (CR) and non-orthogonal multiple access (NOMA) have been deemed two promising technologies due to their potential to achieve high spectral efficiency and massive connectivity. This paper studies a multiple-input single-output NOMA CR …
Authors: Fuhui Zhou, Zheng Chu, Haijian Sun
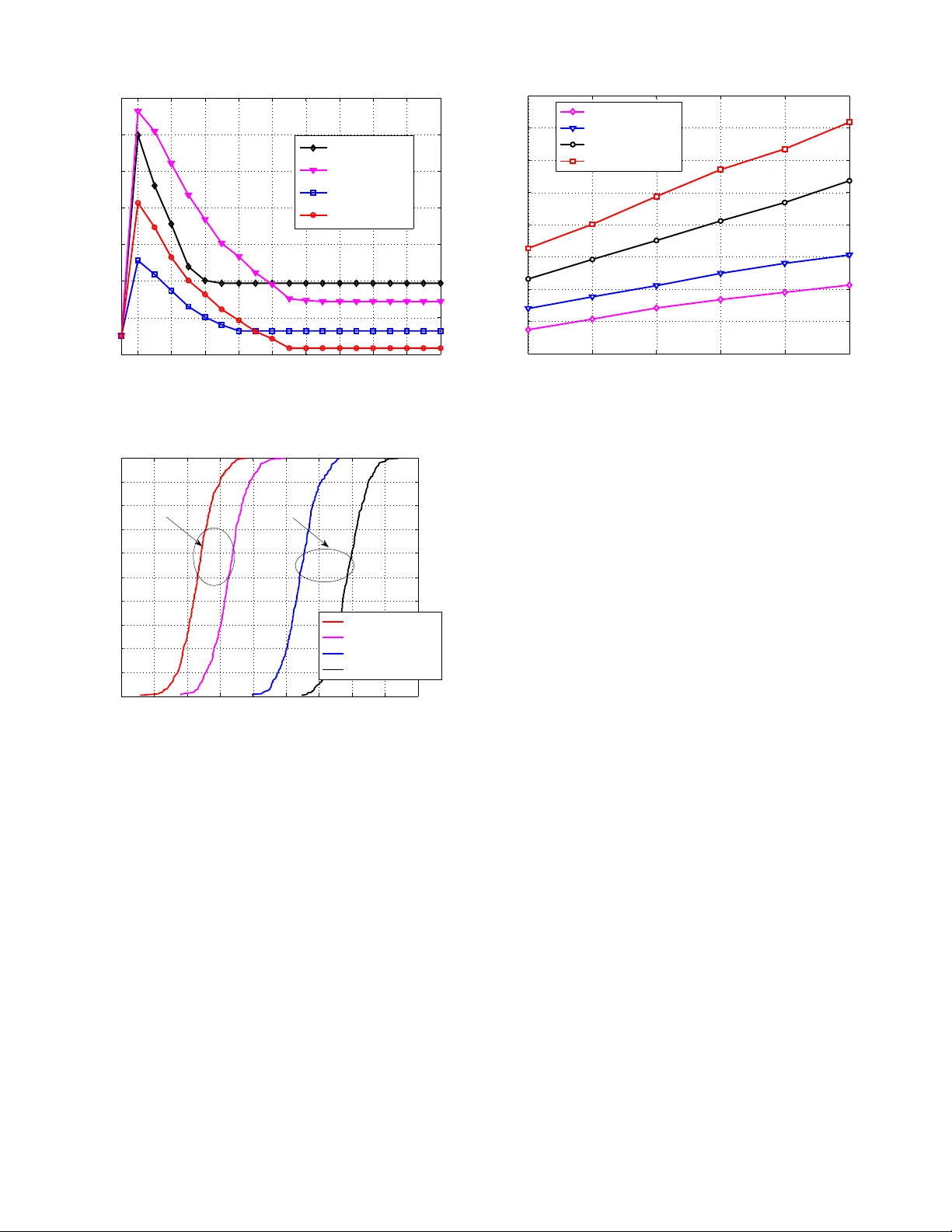
1 Artificial Noise Aided Secure Cogniti v e Beamforming for Cooperati v e MISO-NOMA Using SWIPT Fuhui Zhou, Member , IEEE , Zheng Chu, Member , IEEE , Haijian Sun, Student Member , IEEE , Rose Qingyang Hu, Senior Member , IEEE , and Lajos Hanzo, F ellow , IEEE Abstract —Cognitive radio (CR) and non-orthogonal multiple access (NOMA) hav e been deemed two promising technologies due to their potential to achieve high spectral efficiency and massive connectivity . This paper studies a multiple-input single- output NOMA CR network r elying on simultaneous wir eless information and power transfer (SWIPT) conceived for sup- porting a massive population of power limited battery-driven devices. In contrast to most of the existing works, which use an ideally linear energy harv esting model, this study applies a more practical non-linear energy har vesting model. In order to impr ove the security of the primary netw ork, an artificial-noise-aided cooperative jamming scheme is proposed. The artificial-noise- aided beamforming design problems are in vestigated subject to the practical secrecy rate and energy harvesting constraints. Specifically , the transmission power minimization problems are formulated under both perfect channel state information (CSI) and the bounded CSI error model. The problems f ormulated are non-con vex, hence they are challenging to solve. A pair of algorithms either using semidefinite relaxation (SDR) or a cost function are proposed for solving these problems. Our simulation results show that the proposed cooperativ e jamming scheme succeeds in establishing secure communications and NOMA is capable of outperforming the conv entional orthogonal multiple access in terms of its power efficiency . Finally , we demonstrate that the cost function algorithm outperf orms the SDR-based algorithm. Index T erms —Cognitive radio, non-orthogonal multiple access, non-linear ener gy harv esting, ph ysical-layer secrecy . Manuscript receiv ed September 15, 2017; revised Feb . 1, 2018 and accepted February 15, 2018. Date of publication ****; date of current version ****. The research of F . Zhou was supported in part by the Natural Science Foundation of China under Grant 61701214, in part by the Y oung Natural Science Foundation of Jiangxi Province under Grant 20171B AB212002, in part by The Open Foundation of The State Ke y Laboratory of Integrated Services Networks under Grant ISN19-08, and in part by The Postdoctoral Science Foundation of Jiangxi Province under Grant 2017M610400, Grant 2017KY04 and Grant 2017RC17. The research of Prof. R. Q. Hu was supported in part by the US National Science Foundation grants ECCS-1308006 and EARS- 1547312. The research of Prof. L. Hanzo was supported by the ERC for his Advanced Fellow Grant and the Royal Society for his Research Merit A ward. F . Zhou is with the Department of Electrical and Computer Engineering as a Research Fellow at Utah State University , U.S.A. F . Zhou is also with the School of Information Engineering, Nanchang University , P . R. China, 330031. He is also with State K ey Laboratory of Inte grated Services Netw orks, Xidian University , Xian, 710071, P . R. China (e-mail: zhoufuhui@ieee.org). Z. Chu is with 5G Innovation Center (5GIC), Institute for Communication Systems (ICS), Uni versity of Surre y , Guildford GU2 7XH, U.K (e-mail: z.chu@mdx.ac.uk). H. Sun and R. Q. Hu are with Electrical and Computer Engineer- ing Department, Utah State University , USA (e-mail: h.j.sun@ieee.org, rose.hu@usu.edu). L. Hanzo is with the University of Southampton, Southampton SO17 1BJ, U.K. (e-mail: lh@ecs.soton.ac.uk). I . I N T R O D U C T I O N T HE next generation wireless communication systems call for advanced communication techniques that can achieve high spectral efficienc y (SE) and provide massive connectiv- ity in support of the escalating high data rate requirements imposed by the unprecedented proliferation of mobile devices [1]. Cognitive radio (CR) and non-orthogonal multiple access (NOMA) constitute promising techniques of achie ving high SE [2]-[4]. Specifically , CR enables the secondary users (SUs) to exploit the frequency bands of the primary users (PUs) provided that the interference imposed on the PUs from the SUs is below a certain le vel. NOMA has a higher information- theoretic rate region than orthogonal techniques albeit, which is achiev ed by increasing the receiv er’ s implementation com- plexity [4]. One of the main ideas for realizing NOMA is to exploit the power domain. Specifically , multiple users’ signals are superimposed by using different power lev els and succes- siv e interference cancellation (SIC) is installed at the receiv er for mitigating the mutual interference imposed by using non- orthogonal resources [5]. It is envisioned that applying NOMA in CR networks (CRNs) is capable of significantly improving the SE and the user connectivity [6], [7]. Meanwhile, the next generation wireless communication systems also need energy-ef ficient techniques due to the ever - increasing greenhouse gas emission concerns and explosi ve proliferation of power -limited devices, e.g., sensors and mo- bile phones. Ener gy-efficient techniques can be divided into two broad cate gories. One of the categories focuses on the techniques that can achiev e high energy efficienc y (EE) [8], [9], while the other one aims for recycling energy , where both wireless charging as well as simultaneous wireless information and power transfer (SWIPT) [10] fit. In this paper , we focus on SWIPT since it can simultaneously transmit information and achiev e energy harvesting (EH). In SWIPT , the radio frequency (RF) signals carry not only information to the users, but also transfer energy for the energy harv esting receiv ers (EHRs). Compared to the con ventional EH techniques, such as wind charging, SWIPT has an advantage in providing more stable and controllable amount of power for energy-limited devices. Hence, it is of significant importance to study the application of SWIPT in NOMA CRNs that aim for supporting massiv e population of battery dri ven po wer-limited de vices. Howe ver , due to the broadcast nature of NOMA as well as CR and the dual function of RF signals [11], [12], NOMA 2 CRNs relying on SWIPT are vulnerable to eav esdropping. Malicious EHRs may intercept the confidential information transmitted to the PUs and the SUs [13]. Thus, it is vital to improv e the security of NOMA CRNs using SWIPT . As an alternative to the traditional cryptographic techniques, physical-layer security e xploits the physical characteristics (e.g., multipath fading, propagation delay , etc.) of wireless channels to achieve secure communications [16]-[17]. It was shown [16]-[17] that the secrec y rate of wireless communica- tion systems directly depends on the accuracy of the channel state information (CSI). Moreover , the secrecy rate of SUs in CRNs is more se verely limited [13], [18]-[22] since their transmission po wer should be controlled in order to protect the PUs’ quality of service. In order to improve the secrecy rate of SUs, multiple antennas, cooperativ e relaying, jamming and artificial noise (AN)-aided techniques hav e been applied [18]-[22]. Moreover , the secrec y rate can be further improved by designing an optimal resource allocation scheme [18]-[22]. Furthermore, the secure energy efficiency can be enhanced by using AN-aided techniques and designing the optimal resource allocation schemes [23], [24]. Howe ver , the performance gains achiev ed by using these techniques are significantly influenced by the accuracy of CSI. What’ s worse, it is a challenge to obtain accurate CSI, especially for NOMA [25], [26]. Thus, it is important to design resource allocation schemes under the imperfect CSI. Numerous in vestigations hav e been conducted for improv- ing the security of the conv entional OMA systems and efforts hav e been inv ested into conceiving secure NOMA systems [12], [27]-[30]. Ho wever , no contrib utions ha ve been dev oted to improving the security of NOMA CRNs using SWIPT . In this paper , in order to achiev e secure communications, beamforming design problems are studied in multiple-input single-output (MISO) NOMA CRNs using SWIPT where a practical non-linear EH model is applied as well as different CSI models are considered. An AN-aided cooperativ e scheme is proposed for improving the security of the primary network. By using this scheme, the secondary network imposes artificial noise for jamming the malicious EHRs while aspiring to get a chance to access the frequency bands of the primary network. The related work and the motiv ation of our in vestigation are presented as follo ws. A. Related W ork and Motivation Beamforming design problems have been extensi vely stud- ied both in con ventional CRNs [31]-[36] and in con ventional CRNs using SWIPT [13], [22], [38]-[41]. Recently , some efforts have also been dedicated to designing NOMA resource allocation schemes for impro ving their security [12], [27]-[30]. These contrib utions can be summarized as follows. Due to the broadcast nature of the con ventional CRNs, malicious SUs may intercept the confidential information transmitted to the legitimate SUs. In order to improve the security of CRNs, numerous secure physical-layer techniques hav e been proposed by using dif ferent CSI models [31]-[36]. In [31], a robust beamforming scheme has been proposed for MISO CRNs in the face of a bounded CSI error model. It was shown that as anticipated the secrecy rate of the SUs can be significantly improved by using multiple antennas techniques, by contrast it is reduced when the CSI inaccuracy goes up. By exploiting the relationship between multi-antenna aided secure communications and cognitiv e radio communications, the authors of [32] designed an optimal beamforming scheme for MISO-aided CRNs. In [33], the authors extended the con- tributions of [31] and [32] into a fading channel and the secure throughput was maximized by optimizing both the beam- forming vector and the transmission power . The authors of [34] studied the robust beamforming design problem in MISO CRNs where realistic finite-alphabet inputs are considered. A global optimization approach was proposed for designing an optimal beamforming scheme for maximizing the secrecy rate. Recently , the authors of [35] and [36] studied the beamforming design problems of secure MISO multiuser unicast CRNs and of mutlicast CRNs, respecti vely . Specifically , in [35], an AN- aided beamforming scheme was proposed. It was sho wn that as expected the secrecy rate of SUs can be improv ed by imposing artificial noise on malicious SUs. Cooperation between the primary network and the secondary network w as proposed in [36] where the secrecy rate of SUs was maximized under the max-min fairness criterion. Since energy harv esting has not been considered in [31]- [36], the beamforming schemes proposed in these works are inappropriate in CRNs using SWIPT . Recently , the authors of [13], [22], [38]-[41] studied the resource allocation problems of various CRNs using SWIPT . In [13], a multi-objectiv e optimization framew ork was applied in MISO CRNs with SWIPT . The beamforming scheme, the covariance matrix of AN and energy signals were jointly optimized. It was sho wn that there are several tradeoffs in CRNs using SWIPT , such as the tradeoff between the secrecy rate of SUs and the harvested power of EHRs. The authors of [13] only considered the bounded CSI error model. In [22], the authors studied the robust beamforming design problem both under the bounded CSI error model and the probabilistic CSI error model. It was shown that a performance gain can be obtained under the probabilistic CSI error model compared to the bounded CSI error model. Mohjazi et al. [37] extended the rob ust beam- forming design problem into a multi-user MISO CRNs using SWIPT . The transmission po wer of the cogniti ve base station (CBS) was minimized by jointly optimizing the beamforming of CBS and the power splitting factor of the energy-harv esting SUs. In order to further improv e the secrecy rate and the harvested po wer of EHRs, an optimal precoding scheme was designed for multiple-input multiple-output (MIMO) aided CRNs using SWIPT [38]. In [39], a cooperativ e mechanism and a robust beamforming scheme were proposed for im- proving the security of CRNs, where the energy signals were exploited to jam the malicious EHRs. The authors of [40] have studied rob ust resource allocation problems in MIMO-aided CRNs using SWIPT under the probabilistic CSI error model. The contributions of [13], [22], [38]-[40] assumed an ideal linear EH model. Howe ver , practical po wer conv ersion circuits hav e a non-linear end-to-end wireless po wer transfer function. Hence, the rob ust resource allocation schemes proposed in these treatises would perform difficultly in the face of a 3 realistic non-linear power transfer characteristic. In [41], the robust beamforming design problem was studied in MISO CRNs using SWIPT , where a non-linear EH model was used. The abov e-mentioned contributions were made for CRNs and CRNs with SWIPT where OMA is applied. Ho wever , these resource allocation schemes proposed in the abov e- mentioned works are inappropriate or suboptimal in NOMA systems since NOMA schemes are very different from OMA. The authors of [12], [27]-[30] ha ve studied the optimal re- source allocation problems in NOMA systems in order to achiev e secure communications. In [12], an optimal po wer allocation scheme was proposed for maximizing the secrecy sum rate of a single-input single-output (SISO) NOMA sys- tem, where only an eavesdropper was assumed and a constant decoding order was applied. In [27], the authors considered a more general scenario, where a dynamic decoding order was considered. The sum secrecy rate was maximized by jointly optimizing the decoding order, the transmission rates and the power allocated to users. The secrecy rate maximization problems of MISO NOMA systems [28], [29] and MIMO NOMA systems [30] were in vestigated. It was shown that the secrecy rate achiev ed by using NOMA is higher than that achiev ed by using OMA, and that the secrecy rate of users can be improv ed by using multiple antennas-aided techniques. Although resource allocation problems hav e indeed been conceiv ed for NOMA systems for achieving secure communi- cations [12], [27]-[30], resource allocation schemes proposed in these contributions operated under the assumption that per- fect CSI can be obtained. Moreo ver , these resource allocation schemes cannot work in NOMA CRNs using SWIPT since the interference between the primary network and the secondary network as well as the energy harvesting requirements of the EHRs are required to be considered. Furthermore, the robust resource allocation schemes proposed in conv entional CRNs using SWIPT are inappropriate for NOMA CRNs using SWIPT due to the differences between NOMA and OMA. T o the best of our knowledge, few inv estigations hav e been conduced for improving the security of NOMA CRNs using SWIPT . Thus, in order to achie ve secure communications in NOMA CRNs using SWIPT , beamforming design problems are studied both under the perfect CSI model and the bounded CSI error model. These problems are challenging but mean- ingful. The reasons are from the following two perspecti ves. On the one hand, a practical non-linear EH model is applied, but the EH form is more complex than the linear form. On the other hand, the mutual interference between the primary network and the secondary network as well as the interference among NOMA SUs ha ve to be considered. B. Contributions and Organization In contrast to [12], [27]-[30], this paper studies the beam- forming design problems of MISO-NOMA CRNs using SWIPT , where multiple malicious EHRs exist and a practical non-linear EH model is applied. Both the perfect CSI and the bounded CSI error model are considered. In order to improve the security of the primary network, an AN-aided cooperative scheme is proposed. The main contributions are summarized as follo ws: 1) The AN-aided cooperativ e scheme is proposed for MISO-NOMA CRNs using SWIPT in order to impro ve the security of the primary network. By using this scheme, the CBS transmits a jamming signal to cooper- ate with the primary base station (PBS) for improving the security of the PUs. As a re ward, the secondary network is granted to access the frequency bands of the primary network and provide SWIPT services both for the SUs and for the EHRs in the secondary network. Moreov er , the cov ariance matrix of the jamming signals transmitted at CBS and the beamforming of the CBS and the PBS are jointly optimized. 2) Beamforming design problems are studied under both the perfect CSI model and the bounded CSI error model. In contrast to the works that only an eav esdropper was considered in the NOMA system [12], [27]-[30], we in vestigate a more general scenario, where multiple malicious EHRs exist. The total transmission power is minimized by jointly optimizing the transmission beamforming vectors of both the PBS and the CBS as well as the covariance matrix of the jamming signal transmitted at the CBS, subject to constraints on the secrecy rates of both the PUs and the SUs as well as on the energy harvesting requirements of the EHRs. A pair of algorithms are proposed for solving these challenging non-con ve x problems. One of them relies on semidefinite relaxation (SDR) while the other is based on a carefully concei ved cost function. 3) Our simulation results show that the proposed AN- aided cooperati ve scheme can reduce the transmission power required in MISO-NOMA CRNs using SWIPT . Moreov er , it is shown that the performance achieved by NOMA is proven to be better than that obtained by OMA, ev en when the CSI is imperfect. Furthermore, our simulation results also show that the algorithm based on the cost function outperforms the algorithm based on using SDR. C. Or ganization and Notations The remainder of this paper is organized as follows. The system model is presented in Section II. Our secure beam- forming design problems are examined under the perfect CSI assumption in Section III. Section IV presents our secure beamforming design problems under the bounded CSI error model while our simulation results are presented in Section V . Finally , the paper is concluded in Section VI. Notations: V ectors and matrices are represented by boldface lower case letters and boldf ace capital letters, respectiv ely . The identity matrix is denoted by I ; N P,t and N S,t are the number of antennas of the PBS and the CBS, respectiv ely; vec( A ) denotes the vectorization of matrix A and it is obtained by stacking its column vectors. The Hermitian (conjugate) trans- pose, trace, and rank of a matrix A are denoted respectively by A H , T r ( A ) and Rank ( A ) . x † represents the conjugate trans- pose of a vector x . C M × N stands for an M -by- N dimensional complex matrix set. A 0 ( A 0 ) represents that A is a Hermitian positi ve semidefinite (definite) matrix. H N and 4 E H R s . . . . . . P U s 1 K E H R s . . . . . . P U s M K I n f o r m a t i o n C l u s t e r 1 C l u s t e r M T h e s e c o n d a r y n e t w o r k . . . , pt N T h e p r i m a r y n e t w o r k E H R s . . . . . . S U s ,1 p N , pM N , st N s N P B S CBS s K Fig. 1: The system model. H N + represent a N -by- N dimensional Hermitian matrix set and a Hermitian positiv e semidefinite matrix set, respectively . k·k denotes the Euclidean norm of a vector . |·| represents the absolute value of a complex scalar . x ∼ C N ( u , Σ ) means that x is a random vector , which follo ws a complex Gaussian distribution with mean u and covariance matrix Σ . E [ · ] denotes the e xpectation operator . Re ( a ) extracts the real part of vector a . λ max ( A ) is the maximum eigen value of A . R + represents the set of all nonnegativ e real numbers. [ x ] + denotes the maximum between 0 and x . I I . S Y S T E M M O D E L In this section, we will describe the network model and security metrics in the downlink MISO NOMA CRNs using SWIPT under a practical non-linear energy harvesting model. In [12], [27]-[30], only one eav esdropper has been consid- ered in the designed NOMA systems and resource allocation schemes hav e been proposed. In this paper, the beamforming design problems are studied in a more general scenario, where multiple malicious EHRs exist. The detail description is presented in the following subsections. A. Network Model Our downlink MISO NOMA CR network using SWIPT is shown in Fig. 1. In the primary network, unicast-multicast communications are exploited since the y can provide high SE and massiv e connectivity . This scenario is widely encountered, for example in Internet of Things, wireless sensor networks and the cellular networks [35], [36]. Specifically , the PBS sends different confidential information-bearing signals to the PUs in the different clusters. And the primary users in each individual multicast cluster receiv e the same confidential information-bearing signal from the PBS. In the secondary network, the NOMA is applied since it can achiev e high power transfer efficienc y and SUs can perform SIC [6], [7]. In this case, the PBS broadcasts the information to the PUs in M clusters and simultaneously transfers energy to EHRs. In the secondary network, the CBS provides SWIPT service to K s EHRs and to N s SUs by using NOMA. Due to the constrained size of de vices, the PUs and SUs can only perform information decoding while the EHRs can only harvest energy from the RF signals [22], [35]. The primary netw ork coexists with the secondary network by using the spectrum sharing mode. The PBS is equipped with N p,t antennas and the CBS is equipped with N s,t antennas. All the PUs, SUs and EHRs are equipped with a single antenna. Due to the broadcast natures of NOMA and the dual function of RF signals in SWIPT , the EHR may eavesdrop and intercept the information transmitted by the PBS and the CBS. It is assumed that EHRs in each network can only intercept confidential information from the same network and the PUs in each cluster are respecti vely wiretapped by EHRs in the same cluster [36]. For example, PUs in the m th cluster , where m ∈ M and M ∆ = { 1 , 2 , · · · , M } , are wiretapped by the k th EHR in the m th cluster, where k ∈ M and K m ∆ = { 1 , 2 , · · · , K m } and K m is the number of EHRs while N p,m is the number of PUs in the m th cluster . In order to improve the security of both the primary network and the secondary network, an AN-aided cooperativ e scheme is applied. Using this scheme, the CBS of Fig. 1 transmits a jamming signal to the primary network for improving the security of the PUs. As a rew ard, the primary network allows the secondary network to operate on its frequency bands. All the channels inv olved are assumed to be flat fading channels. In this paper , both the perfect CSI and imperfect CSI cases are studied. The performance achie ved under the perfect CSI can be used as a bound in our analysis and provides meaningful insights into the design of MISO NOMA CRNs using SWIPT . The assumption has also been used in [11], [12], [18], [19]. B. Security Metrics Let y p,m,i denote the signal receiv ed at the i th PU in the m th cluster, y s,j represent the signal receiv ed at the j th SU, y e,m,k denote the EH signal receiv ed at the k th EHR in the m th cluster and y e,l represent the EH signal received at the l th EHR in the secondary network, respectiv ely , where i ∈ N p,m , N p,m = { 1 , 2 , · · · , N p,m } ; j ∈ N s , N s = { 1 , 2 , · · · , N s } and l ∈ K s , K s = { 1 , 2 , · · · , K s } . These signals are respectively expressed as y p,m,i = h † p,m,i " M X m =1 ( w p,m s p,m + v p,m ) # + f † s,m,i N s X j =1 w s,j s s,j + v s + n p,m,i , (1a) y s,j = q † p,j " M X m =1 ( w p,m s p,m + v p,m ) # + h † s,j N s X j =1 w s,j s s,j + v s + n s,j , (1b) 5 y e,m,k = g † e,m,k " M X m =1 ( w p,m s p,m + v p,m ) # + f † e,m,k N s X j =1 w s,j s s,j + v s , (1c) y e,l = q † e,l " M X m =1 ( w p,m s p,m + v p,m ) # + g † e,l N s X j =1 w s,j s s,j + v s , (1d) where h p,m,i ∈ C N p,t × 1 and f s,m,i ∈ C N s,t × 1 are the channel vector between the PBS and the i th PU as well as that between the CBS and the i th PU in the m th cluster , respectiv ely; q p,j ∈ C N p,t × 1 and h s,j ∈ C N s,t × 1 denote the channel vector between the PBS and the j th SU as well as that between the CBS and the j th SU, respectively . Furthermore, g e,m,k ∈ C N p,t × 1 and f e,m,k ∈ C N s,t × 1 are the channel vector between the PBS and the k th EHR and that between the CBS and the j th EHR in the m th cluster , respectiv ely; q e,l ∈ C N p,t × 1 and g e,l ∈ C N s,t × 1 represent the channel vector between the PBS and the l th EHR and that between the CBS and the l th EHR in the secondary network, respectively . Still regarding to (1a) , s p,m ∈ C 1 × 1 and w p,m ∈ C N p,t × 1 are the confidential information-bearing signal for the PUs in the m th cluster and the corresponding beamforming v ector , respectiv ely . Furthermore, s s,j ∈ C 1 × 1 and w s,j ∈ C N s,t × 1 represent the confidential information-bearing signal deliv ered for the j th SU and the corresponding beamforming vector , respectiv ely . Additionally , v p,m and v s denote the noise vector artificially generated by the PBS and the CBS. It is assumed that E [ | s p,m | 2 ] = 1 and E [ | s s,j | 2 ] = 1 . It is also assumed that v p,m ∼ C N (0 , Σ p,m ) and v s ∼ C N (0 , Σ s ) , where Σ p,m and Σ s are the AN co v ariance matrix. In (1) , n p,m,i ∼ C N 0 , σ 2 p,m,i and n s,j ∼ C N 0 , σ 2 s,j respectiv ely denote the complex Gaussian noise at the i th PU in the m th cluster and the l th SU. The secrecy rate of the i th PU in the m th cluster and the secrecy rate of the j th SU, denoted by R p,m,i and R s,j , respectiv ely , can be expressed as R p,m,i = log Γ p,m,i Γ p,m,i − T r ( W p,m H p,m,i ) − max k ∈K m log Γ e,m,k + σ 2 e,m,k Γ e,m,k − T r ( W p,m G e,m,k ) + σ 2 e,m,k !# + , (2a) R s,j = h log 2 Γ s,j Γ s,j − Tr ( W s,j H s,j ) − max l ∈L log 2 Λ e,l,j Λ e,l,j − Tr ( W s,j G e,l ) + , if j = N s , = min z ∈{ j,j +1 ,N s } log 2 Λ s,j,z Λ s,j,z − Tr ( W s,j H s,z ) − max l ∈L log 2 Λ s,l,j Λ s,l,j − Tr ( W s,j G e,l ) + , otherwise . (2b) where W p,m = w p,m w † p,m ; W s,j = w s,j w † s,j ; H p,m,i = h p,m,i h † p,m,i ; F s,m,i = f s,m,i f † s,m,i ; Q p,j = q p,j q † p,j ; H s,j = h s,j h † s,j ; G e,m,k = g e,m,k g † e,m,k ; F e,m,k = f e,m,k f † e,m,k ; Q e,l = q e,l q † e,l and G e,l = g e,l g † e,l . The expressions of Γ p,m,i , Γ e,m,k , Γ s,j , Λ e,l,j , Λ s,j,z and Λ s,l,j are giv en in (3) . W ithout loss of generality , it is assumed that k h 1 k ≤ k h 2 k ≤ · · · ≤ k h N s k . Similar to [12], [27]-[28], it is assumed furthermore that the EHR in the secondary network has decoded SU j ’ s message before it decodes the SU i ’ s message, j < i . This ov er-estimates the interception capability of EHRs and results in the worst-case secrecy rate of the SUs. This conserv ativ e assumption was also used in [12], [27]-[28]. Γ p,m,i = T r (" M X m =1 ( W p,m + Σ p,m ) # H p,m,i + N s X j =1 W s,j + Σ s F s,m,i + σ 2 p,m,i , (3a) Γ e,m,k = T r (" M X m =1 ( W p,m + Σ p,m ) # G e,m,k + N s X j =1 W s,j + Σ s F e,m,k , (3b) Γ s,j = T r (" M X m =1 ( W p,m + Σ p,m ) # Q p,j + ( W s,j + Σ s ) H s,j } + σ 2 s,j , (3c) Λ e,l,j = T r "" M X m =1 ( W p,m + Σ p,m ) # Q e,l + ( W s,j + Σ s ) G e,l ] + σ 2 e,l , (3d) Λ s,j,z = T r (" M X m =1 ( W p,m + Σ p,m ) # H p,z + N s X u = j W s,u + Σ s H s,z + σ 2 s,z , (3e) Λ s,l,j = T r (" M X m =1 ( W p,m + Σ p,m ) # Q e,l + N s X υ = j W s,υ + Σ s G e,l + σ 2 e,l . (3f) C. Non-linear Ener gy Harvesting Model In this paper, a practical non-linear EH model is adopted. According to [41]-[43], the harv esting power of EHRs, de- noted by Φ E , A , can be formulated as: Φ e, A = ψ e, A − P max e, A Ψ e, A 1 − Ψ e, A , (4a) ψ e, A = P max e, A 1 + exp [ − a e, A (Γ e, A − b e, A )] , (4b) Ψ e, A = 1 1 + exp ( a e, A b e, A ) , (4c) 6 where A is the set of EHRs in the primary network and the sec- ondary network, namely , A = A 1 ∪ A 2 , and A 1 = ∪ m ∈M K m , m ∈ M , A 2 = K s ; a e, A and b e, A represent parameters that reflect the circuit specifications, such as the resistance, the capacitance and diode turn-on voltage [42]. Furthermore, P max e, A is the maximum harvested power of EHRs when the EH circuit is saturated. In (4b) , Γ e, A is the RF power received at EHRs. Furthermore, Γ e, A = Γ e,m,k when the EHRs are in the primary network and Γ e, A = Λ s,l, 1 − σ 2 e,l when the EHRs are in the secondary network. Note that the noise po wer is ignored, since it is small compared to the RF signal power [41]-[43]. I I I . A N - A I D E D B E A M F O R M I N G D E S I G N U N D E R P E R F E C T C S I In this section, an AN-aided beamforming design problem is formulated in MISO NOMA CRNs using SWIPT under the perfect CSI. The CSI between the PBS and PUs as well as the CSI between the CBS and the SUs can be obtained through the feedback from the corresponding transmitters and the recei vers [11], [12], [18], [19]. The CSI between the two networks can be obtained with the cooperation between the primary network and the secondary network [18], [33], [34]. The total transmission power is minimized subject to the constraints on both the secrecy rates of PUs and SUs as well as on the harvested power of EHRs in both the primary and the secondary networks. In order to solv e the challenging non- con vex problem, again, a pair of suboptimal algorithms are proposed. One is based on SDR and the other is based on a cost function. A. AN-aided Beamforming Design Pr oblem In order to minimize the sum of the transmission power of the PBS and CBS, the beamforming weights and the AN cov ariance of the PBS and the CBS are jointly optimized under constraints of the secrecy rate of PUs as well as SUs and under the EH requirements of the EHRs. The power minimization problem is formulated as follows: P 1 : min W p,m , Σ p,m W s,j , Σ s T r M X m =1 ( W p,m + Σ p,m ) + N s X j =1 W s,j + Σ s (5a) s.t. C 1 : R p,m,i ≥ γ p,m,i , i ∈ N p,m , m ∈ M , (5b) C 2 : R s,j ≥ γ s,j , j ∈ N s , (5c) C 3 : Φ e,A 1 ≥ ζ e,A 1 , k ∈ K m , m ∈ M , (5d) C 4 : Φ e,A 2 ≥ ζ e,A 2 , l ∈ K s , (5e) C 5 : Rank ( W p,m ) = 1 , Rank ( W s,j ) = 1 (5f) C 6 : W p,m 0 , W s,j 0 . (5g) In (5) , γ p,m,i and γ s,j are the minimum secrecy rate re- quirements of the i th PU in the m th cluster and of the j th SU; ζ e,A 1 and ζ e,A 2 are the minimum EH requirements of EHRs in the primary and the secondary network. The constraints C 1 and C 2 are imposed to guarantee the secrecy rates of the PUs and SUs, respectiv ely; the constraints C 3 and C 4 are the constraints that can satisfy the harvested power requirements of the EHRs in both the primary and secondary networks; and the constraint C 5 is the rank-one constraint required for obtaining rank-one beamforming. Note that the optimization objectiv e of P 1 can be identified as the weight objectiv e of a multiple-objective optimization problem that has two optimization objectives (e.g., the transmission power of the PBS and the CBS) with the same weight. Due to the constraints C 1 , C 2 and C 5 , P 1 is non-con vex and dif ficult to solve. In order to solve this problem, a pair of suboptimal schemes are proposed as follows. B. Suboptimal Solution Based on SDR T o address the constraint C 1 , an auxiliary variable τ m , m ∈ M , is introduced. Then, the constraint C 1 can be equi valently expressed as log Γ p,m,i [Γ p,m,i − Tr ( W p,m H p,m,i )] τ m ≥ γ p,m,i , (6a) log Γ e,m,k + σ 2 E ,m,k h Γ e,m,k − Tr ( W p,m G e,m,k ) + σ 2 e,m,k i τ m ≤ 1 , (6b) where k ∈ K m and m ∈ M . Using successiv e con vex approximation (SCA), the constraints given by (6a) and (6b) can be approximated as (7) and (8) exp ( α p,m,i + β m − λ p,m,i ) ≤ 2 − γ p,m,i , (7a) Γ p,m,i − Tr ( W p,m H p,m,i ) ≤ exp ( e α p,m,i ) ( α p,m,i − e α p,m,i + 1) , (7b) τ m ≤ exp e β m β m − e β m + 1 , (7c) Γ p,m,i ≥ exp ( λ p,m,i ) , (7d) exp ( µ e,m,k − ρ e,m,k − δ m ) ≤ 1 , (8a) Γ e,m,k + σ 2 e,m,k ≤ exp ( e µ e,m,k ) ( µ e,m,k − e µ e,m,k + 1) , (8b) Γ e,m,k − T r ( W p,m G e,m,k ) + σ 2 e,m,k ≥ exp ( ρ e,m,k ) , (8c) τ m ≥ exp ( δ m ) , (8d) where α p,m,i , β m , λ p,m,i , µ e,m,k , ρ e,m,k , and δ m are auxiliary variables. Furthermore, e α p,m,i , e β m and e µ e,m,k are approximate values, and they are equal to α p,m,i , β m and µ e,m,k , respec- tiv ely , when the constraints are tight. Similarly , the constraint C 2 can be approximated as (9) and (10) . When j = N s , the 7 secrecy rate constraint of the N s th SU can be formulated as exp ( α s,N s + β s,N s − λ s,N s ) ≤ 2 − γ s,N s , (9a) Γ s,N s − T r ( W s,N s H S,N s ) ≤ exp ( e α s,N s ) ( α s,N s − e α s,N s + 1) , (9b) τ s,N s ≤ exp e β s,N s β s,N s − e β s,N s + 1 , (9c) Γ s,N s ≥ exp ( λ s,N s ) , (9d) exp ( µ e,l − ρ s,l − ω s,N s ) ≤ 1 , l ∈ K s , (9e) Λ e,l,N s ≤ exp ( e µ e,l ) ( µ E ,l − e µ e,l + 1) , (9f) Λ e,l,N s − Tr ( W s,N s G e,l ) ≥ exp ( ρ s,l ) , (9g) τ s,N s ≥ exp ( ω s,N s ) , (9h) where α s,N s , β s,N s , λ s,N s , µ e,l , ρ s,l , and ω s,N s are auxiliary variables. Furthermore, e α s,N s , e β s,N s and e µ e,l are approximate values, and they are equal to α s,N s , β s,N s and µ e,l , respec- tiv ely , when the constraints are tight. When j = 1 , 2 , · · · , N s − 1 , the secrecy rate constraint of the j th SU can be formulated as κ j − ω j 2 γ s,j ≥ 0 , (10a) exp ( α s,j,z + ξ s,j − λ s,j,z ) ≤ 1 , z ∈ { j, j + 1 , N s } , (10b) Λ s,j,z − Tr ( W s,j H s,z ) ≤ exp ( e α s,j,z ) ( α s,j,z − e α s,j,z + 1) , (10c) κ j ≤ exp e ξ s,j ξ s,j − e ξ s,j + 1 , (10d) Λ s,j,z ≥ exp ( λ s,j,z ) , (10e) exp ( µ e,l,j − ρ s,l,j − τ s,j ) ≤ 1 , (10f) Λ s,l,j ≤ exp ( e µ e,l,j ) ( µ e,l,j − e µ E ,l,j + 1) , (10g) Λ s,l,j − T r ( W s,j G e,l ) ≥ exp ( ρ s,l,j ) , (10h) ω j ≥ exp ( τ s,j ) , (10i) where κ j , ω j , α s,j,z , ξ s,j , λ s,j,z , µ e,l,j , ρ s,l,j and τ s,j de- note auxiliary variables. Furthermore, e α s,j,z , e ξ s,j and e µ e,l,j are approximate values and equal to α s,j,z , ξ s,j and µ e,l,j , respectiv ely , when the constraints are tight. Constraints C 3 and C 4 can be equiv alently expressed as Γ e,A ≥ b e,A − 1 a e,A ln ( P max e,A ζ e,A (1 − Ψ e,A ) + P max e,A Ψ e,A − 1 ) . (11) Based on (7) and (11) , using SDR, P 1 can be solved by iterativ ely solving P 2 , gi ven as P 2 : min Ξ T r M X m =1 ( W p,m + Σ p,m ) + N s X j =1 W s,j + Σ s (12a) s.t. C 6 , (7) − (11) , (12b) where Ξ is the set including all optimization variables and auxiliary variables. P 2 is con ve x and can be ef ficiently solved by using the softw are CVX [22]. Algorithm 1 calculates the solution of P 1 . The details of Algorithm 1 are provided in T able 1, where P n opt denotes the minimum total transmission power at the n th iteration. T ABLE I: The SCA-based algorithm Algorithm 1 : The SCA-based algorithm for P 1 1: Setting: γ p,m,i , γ s,j Υ m,i , ζ e,A 1 , ζ e,A 1 , i ∈ N p,m , k ∈ K m , m ∈ M l ∈ K s and the tolerance error $ ; 2: Initialization: The iterative number n = 1 , e α n p,m,i , e β n m , e µ n e,m,k , e α n s,N s , e β n s,N s , e µ n e,l , e α n s,j,z , e ξ n s,j and e µ n e,l,j and P n opt ; 3: Repeat: solve P 2 by using CVX for the giv en approximate values; obtain e α n +1 p,m,i , e β n +1 m , e µ n +1 e,m,k , e α n +1 s,N s , e β n +1 s,N s , e µ n +1 e,l , e α n +1 s,j,z , e ξ n +1 s,j and e µ n +1 e,l,j and P n +1 opt ; if Rank ( W p,m ) = 1 and Rank ( W s,j ) = 1 Obtain optimal W p,m and W s,j ; else Obtain suboptimal W p,m and W s,j ; end update the iterative number n = n + 1 ; calculate the total transmit power P n opt ; if P n opt − P ( n − 1) opt ≤ $ break; end; 4: Obtain resource allocation: W p,m , W s,j , Σ p,m and Σ s . Algorithm 1 does not guarantee that the optimal beam- forming weights w p,m , w s,j can be obtained. If W p,m and W s,j are of rank-one, the optimal beamforming scheme can be obtained by the eigenv alue decomposition and the obtained eigen vectors are optimal beamforming. If W p,m and W s,j are not of rank-one, the suboptimal beamforming vectors can be obtained by using the Gaussian randomization procedure [22]. C. Suboptimal Solution Based on Cost Function Since W p,m and W s,j are semi-positi ve definite, the ranks of W p,m and W s,j are equal to 1 when their maximum eigenv alues are equal to its trace, namely , when we hav e Rank ( W p,m ) = λ max ( W p,m ) and Rank ( W s,j ) = λ max ( W s,j ) ; Otherwise, we hav e Rank ( W p,m ) > λ max ( W p,m ) and Rank ( W s,j ) > λ max ( W s,j ) . Thus, the rank-one constraint can be equiv alent to M P m =1 [ T r ( W p,m ) − λ max ( W p,m )] + N s P j =1 [ T r ( W s,j ) − λ max ( W s,j )] ≤ 0 . From this insight, we can see that the smaller M P m =1 [ T r ( W p,m ) − λ max ( W p,m )] + N s P j =1 [ T r ( W s,j ) − λ max ( W s,j )] is, the more likely that the rank-one constraints can be satisfied. By exploiting a 8 cost function based approach, P 2 is reformulated into P 3 as P 3 : min Ξ T r M X m =1 ( W p,m + Σ p,m ) + N s X j =1 W s,j + Σ s + ` ( M X m =1 [ T r ( W p,m ) − λ max ( W p,m )] + N s X j =1 [ T r ( W s,j ) − λ max ( W s,j )] (13a) s.t. (12b) , (13b) where ` > 0 is a cost factor . It may be readily sho wn that the minimum v alue M P m =1 [ T r ( W p,m ) − λ max ( W p,m )] + N s P j =1 [ T r ( W s,j ) − λ max ( W s,j )] can be obtained by using a lar ge ` value. Since λ max ( W p,m ) and λ max ( W s,j ) are con vex, P 3 is non-con ve x. The following lemma is applied to solve the non-con ve x problem P 3 . Lemma 1 [45]: Let λ max ( X ) and λ max ( Y ) denote the maximum eigenv alue of X and Y , respectively . If X and Y are semi-positi ve definite, then we hav e λ max ( X ) − λ max ( Y ) ≥ y † max ( X − Y ) y max , where y max is the eigen- vector related to the maximum eigen value of Y . Using Lemma 1, P 3 can be approximated as P 4 . P 4 : min Ξ f W n +1 p,m , W n +1 s,j (14a) s.t. (12b) , (14b) where n is the iteration index and f W n +1 p,m , W n +1 s,j is given by f W n +1 p,m , W n +1 s,j = T r M X m =1 W n +1 p,m + Σ p,m + N s X j =1 W n +1 s,j + Σ s + ` ( M X m =1 T r W n +1 p,m − λ max W n p,m − w n p,m † W n +1 p,m − W n p,m w n p,m i + N s X j =1 T r W n +1 s,j − λ max W n s,j − w n s,j † W n +1 s,j − W n s,j w n s,j io , (15) where w n p,m and w n s,j are the eigen vectors related to the maximum eigenv alue of W n p,m and W n s,j , respectively . It is seen that P 4 is con vex and can be solved by using CVX . By solving P 4 , the iterati ve Algorithm 2 can be designed to solve P 1 . The details of Algorithm 2 are presented in T able 2. I V . A N - A I D E D B E A M F O R M I N G D E S I G N U N D E R I M P E R F E C T C S I In this section, the AN-aided beamforming design problem is studied in a more practical MISO NOMA CRN using SWIPT , where the CSI between the CBS and the EHRs in the T ABLE II: The cost function-based algorithm Algorithm 2 : The cost function-based algorithm for P 1 1: Setting: γ p,m,i , γ s,j Υ m,i , ζ e,A 1 , ζ e,A 1 , i ∈ N p,m , k ∈ K m , m ∈ M l ∈ K s and the tolerance error $ ; 2: Initialization: The iterative number n = 1 , e α n p,m,i , e β n m , e µ n e,m,k , e α n s,N s , e β n s,N s , W n p,m and W n s,j ; 3: Repeat: solve P 4 by using CVX for the giv en approximate values; obtain e α n +1 p,m,i , e β n +1 m , e µ n +1 e,m,k , e α n +1 s,N s , e β n +1 s,N s , e µ n +1 e,l , W ( n +1) p,m and W ( n +1) s,j ; set ` = 2 ` ; end if update the iterative number n = n + 1 ; calculate the total transmit power P n opt ; if Tr W n +1 p,m − λ max W n p,m ≤ $ and Tr W n +1 s,j − λ max W n s,j ≤ $ break; end; 4: Obtain resource allocation: w n p,m , w n s,j , Σ p,m and Σ s . primary network and the CSI between the PBS and the EHRs in the secondary network are imperfect due to the limited cooperation between the primary and the secondary network. Since the bounded CSI error can be readily applied to model the estimating errors [13], [25], [35]-[38], it is opted for this paper . Moreov er , the CSI between the PBS and SUs and the CSI between the CBS and the PBS can be obtained through the cooperation between the primary network and the secondary network, or can be obtained from a third party such as a manager center [8]. Furthermore, the CSI of the secondary link can be obtained by estimating it at the CBS and then sending it back to the CBS through a feedback link, which assumed error- free in this simplified model [22], [44]. Under the bounded error model, a robust AN-aided beamforming design problem is formulated. The non-conv ex problem is solved by using SCA and the S -Procedure [45]. A. Robust AN-aided Beamforming Design Pr oblem F ormula- tion Under the bounded error model, the channel vector q e,l can be formulated as q e,l = q e,l + ∆ q e,l , l ∈ K s , (16a) Ψ e,l ∆ = n ∆ q e,l ∈ C N p,t × 1 : ∆ q † e,l ∆ q e,l ≤ £ 2 e,l o , (16b) while the channel v ector f e,m,k can be e xpressed as f e,m,k = f e,m,k + ∆ f e,m,k , m ∈ M , k ∈ K m , (17a) Ψ e,m,k ∆ = n ∆ f e,m,k ∈ C N s,t × 1 : ∆ f † e,m,k ∆ f e,m,k ≤ £ 2 e,m,k o , (17b) where q e,l and f e,m,k are the estimates of q e,l and f e,m,k , re- spectiv ely; Ψ e,l and Ψ e,m,k represent the uncertainty regions of the channel vectors q e,l and f e,m,k , respectively; ∆ q e,l and ∆ f e,m,k denote the channel estimation errors of q e,l and 9 f e,m,k ; £ e,l and £ e,m,k are the radii of the uncertainty regions Ψ e,l and Ψ e,m,k , respecti vely . Based on the bounded error models for q e,l and f e,m,k , the power minimization problem subject to the constraints on the secrecy rates of the PUs and the SUs as well as on the harvested power requirements of EHRs in both the primary and secondary networks can be formulated as P 5 , gi ven as min W p,m , Σ p,m W s,j , Σ s T r M X m =1 ( W p,m + Σ p,m ) + N s X j =1 W s,j + Σ s (18a) s.t. C 6 : R p,m,i ≥ γ p,m,i , i ∈ N p,m , m ∈ M , ∀ ∆ f e,m,k ∈ Ψ e,m,k , (18b) C 7 : R s,j ≥ γ s,j , j ∈ N s , ∀ ∆ q e,l ∈ Ψ e,l , (18c) C 8 : Φ e,A 1 ≥ ζ e,A 1 , k ∈ K m , m ∈ M , ∀ ∆ f e,m,k ∈ Ψ e,m,k , (18d) C 9 : Φ e,A 2 ≥ ζ e,A 2 , l ∈ K s , ∀ ∆ q e,l ∈ Ψ e,l , (18e) C 10 : Rank ( W p,m ) = 1 , Rank ( W s,j ) = 1 (18f) C 11 : W p,m 0 , W s,j 0 . (18g) The problem P 5 is more challenging to solve due to the infinite inequality constraints imposed by the uncertain regions, Ψ e,l and Ψ e,m,k and owing to the non-con vex constraints C 6 - C 10 . B. Suboptimal Solution Based on Cost Function In order to make P 5 tractable, the S -Procedure of [45] is applied. Lemma 2 ( S -Pr ocedur e ) [45]: Let f i ( z ) = z † A i z + 2Re n b † i z o + c i , i ∈ { 1 , 2 } , where z ∈ C N × 1 , A i ∈ H N , b i ∈ C N × 1 and c i ∈ R . Then, the expression f 1 ( z ) ≤ 0 ⇒ f 2 ( z ) ≤ 0 holds if and only if there exists a ς ≥ 0 such that we ha ve: ς A 1 b 1 b † 1 c 1 − A 2 b 2 b † 2 c 2 0 , (19) provided that there exists a vector b z so that we hav e f i ( b z ) < 0 . Using Lemma 2 and SCA, the constraint C 6 of P 5 can be approximated as (20) at the top of the next page. In (20) , λ e,m,k ≥ 0 and u e,m,k ≥ 0 are slack variables while θ e,m,k and o e,m,k are auxiliary variables. Similarly , the constraint C 7 is approximated as follo ws. When j = N s , one has (21) at the top of the next page. and when j = 1 , 2 , · · · , N s − 1 , the secrecy rate constraint of the j th SU can be approximated as (22) at the top of the next page. where ω e,l ≥ 0 , κ e,l ≥ 0 , τ ≥ 0 and η e,l ≥ 0 are slack v ariables. The constraints C 8 and C 9 can be equi valently expressed as (23) at the top of the next two pages. In (23) , χ e,m,k ≥ 0 and ϕ e,l ≥ 0 are slack variables. By using (20) - (23) , P 5 can be solv ed by iterati vely solving P 6 , gi ven as P 6 : min Ξ 1 f W n +1 p,m , W n +1 s,j (24a) s.t. C 11 , (20) − (23) , (24b) where f W n +1 p,m , W n +1 s,j is given by (15) , and Ξ 1 denotes the set including all optimization variables, auxiliary variables and slack variables. Since P 6 is conv ex, it can be readily solved by using CVX . Similar to P 1 , Algorithm 2 can be used to solve P 5 . The procedure is the same and it is omitted due to space limitation. V . S I M U L A T I O N R E S U LT S In this section, simulation results are pro vided for com- paring the performance obtained by using NOMA to that achiev ed by using OMA. Simulation results are also presented to e valuate the performance of the proposed algorithms. The time division multiple access (TDMA) scheme is selected as the OMA scheme for comparison. The simulation settings are based on those used in [42] and [43]. All the channels in volved are assumed to be Rayleigh flat fading. The number of channel realizations is 10 4 . The variance of noise at all users and EHRs is − 120 dBm. The channel distributions are set as: h p,m,i ∼ C N ( 0 , 2 I ) , f s,m,i ∼ C N ( 0 , 0 . 5 I ) , q p,j ∼ C N ( 0 , 0 . 5 I ) , h s,j ∼ C N ( 0 , 2 I ) , g e,m,k ∼ C N ( 0 , 1 . 5 I ) , f e,m,k ∼ C N ( 0 , 0 . 5 I ) , q e,l ∼ C N ( 0 , 0 . 5 I ) and g e,l ∼ C N ( 0 , 1 . 5 I ) . The detailed simulation settings are gi ven in T able III. T ABLE III: Simulation Parameters Parameters Notation T ypical V alues Numbers of antennas of the PBS N p,t 10 Numbers of antennas of the CBS N s,t 5 Numbers of the clusters M 2 Numbers of PUs N p,m 2 Numbers of SUs N s 3 The maximum harvested power P max e,A 24 mW Circuit parameter a e,A 1500 Circuit parameter b e,A 0 . 0022 The minimum secrecy rate of PUs γ p,m,i 2 bits/s/Hz The minimum secrecy rate of SUs γ s,j 1 bits/s/Hz The minimum EH of EHRs in set A 1 ζ e,A 1 15 mW The minimum EH of EHRs in set A 2 ζ e,A 2 5 mW The tolerance error $ 10 − 4 The radiuses of the uncertainty regions £ e,l 10 − 2 £ e,m,k 10 − 2 Fig. 2 shows the minimum transmission power versus the number of EHRs in the secondary network under the perfect CSI scenario. Since Algorithm 2 is capable of obtaining rank-one solutions, it is used to obtain the results of CRNs using OMA, OMA with cooperation and NOMA without cooperation. Fig. 2 also compares the performance obtained by using Algorithm 1 to that achiev ed by using Algorithm 2. It is seen that the minimum transmission power consumed without the cooperative jamming scheme is higher than that consumed with our proposed cooperative jamming scheme. The reason is that our proposed cooperativ e jamming scheme is beneficial for the PUs to achieve a high secrecy rate and that a low transmission power is required for guaranteeing the secrecy rate of the PUs. This indicates that our proposed cooperativ e jamming scheme is ev entually helpful for secure communications. It is also seen that the transmission po wer consumed by using NOMA is lower than that consumed by using TDMA both with and without cooperation between the primary network and the secondary network. This can be 10 λ e,m,k I − N s P j =1 W s,j + Σ s ! − N s P j =1 W s,j + Σ s ! f e,m,k − f † e,m,k N s P j =1 W s,j + Σ s ! θ e,m,k − f † e,m,k N s P j =1 W s,j + Σ s ! f e,m,k − λ e,m,k £ 2 e,m,k 0 , (20a) u e,m,k I + N s P j =1 W s,j + Σ s ! N s P j =1 W s,j + Σ s ! f e,m,k f † e,m,k N s P j =1 W s,j + Σ s ! f † e,m,k N s P j =1 W s,j + Σ s ! f e,m,k − λ e,m,k £ 2 e,m,k − o E ,m,k 0 , (20b) (7) , (8a) and (8d) . (20c) ω e,l I − M P m =1 ( W p,m + Σ p,m ) − M P m =1 ( W p,m + Σ p,m ) q e,l − q † e,l M P m =1 ( W p,m + Σ p,m ) − Λ e,l − q † e,l M P m =1 ( W p,m + Σ p,m ) q e,l − ω e,l £ 2 e,l 0 , (21a) κ e,l I + M P m =1 ( W p,m + Σ p,m ) M P m =1 ( W p,m + Σ p,m ) q e,l q † e,l M P m =1 ( W p,m + Σ p,m ) e Λ e,l + q † e,l M P m =1 ( W p,m + Σ p,m ) q e,l − κ e,l £ 2 e,l 0 , (21b) Λ e,l = T r [( W s,N s + Σ s ) G e,l ] + σ 2 e,l − exp ( e µ e,l ) ( µ e,l − e µ e,l + 1) , (21c) e Λ e,l = T r ( Σ s G e,l ) + σ 2 e,l − exp ( ρ s,l ) , (21d) (9a) − (9d) , (9e) and (9h) , (21e) τ e,l I − M P m =1 ( W p,m + Σ p,m ) − M P m =1 ( W p,m + Σ p,m ) q e,l − q † e,l M P m =1 ( W p,m + Σ p,m ) − Λ s,l,j − q † e,l M P m =1 ( W p,m + Σ p,m ) q e,l − τ e,l £ 2 e,l 0 , (22a) η e,l I + M P m =1 ( W p,m + Σ p,m ) M P m =1 ( W p,m + Σ p,m ) q e,l q † e,l M P m =1 ( W p,m + Σ p,m ) Λ s,l,j + q † e,l M P m =1 ( W p,m + Σ p,m ) q e,l − η e,l £ 2 e,l 0 , (22b) Λ s,l,j = T r N s X υ = j W s,υ + Σ s G e,l + σ 2 e,l − exp ( e µ e,l,j ) ( µ e,l,j − e µ e,l,j + 1) , (22c) e Λ s,l,j = T r N s X υ = j +1 W s,υ + Σ s G e,l + σ 2 e,l − exp ( ρ s,l,j ) , (22d) (10a) − (10f ) , and (10i) , (22e) explained by the fact that NOMA provides a higher secrecy rate for SUs than TDMA [12], [27]. Thus, the transmission power required for guaranteeing the secrecy rate of SUs can be decreased. Moreover , it is interesting to note that the transmission power achiev ed by using Algorithm 1 is higher than that obtained by using Algorithm 2. It indicates that Algorithm 2 outperforms Algorithm 1 in terms of transmission power minimization. The reason is that Algorithm 2 can obtain rank-one solutions, while Algorithm 1 cannot achie ve rank-one solutions. T able 3 is gi ven to sho w the number of rank-one solutions achiev ed by using Algorithm 1 and Algorithm 2 under perfect CSI. The results are obtained for 1000 channel realizations. It is seen from T able 3 that Algorithm 2 can provide rank- 11 χ e,m,k I + N s P j =1 W s,j + Σ s ! N s P j =1 W s,j + Σ s ! f e,m,k f † e,m,k N s P j =1 W s,j + Σ s ! Γ e,m,k + f † e,m,k N s P j =1 W s,j + Σ s ! f E ,m,k − χ e,m,k £ 2 e,m,k 0 , (23a) ϕ e,l I + M P m =1 ( W p,m + Σ p,m ) M P m =1 ( W p,m + Σ p,m ) q e,l q † e,l M P m =1 ( W p,m + Σ p,m ) Γ e,l + q † e,l M P m =1 ( W p,m + Σ p,m ) q e,l − φ e,l £ 2 E ,l 0 , (23b) Γ e,m,k = T r (" M X m =1 ( W p,m + Σ p,m ) # G e,m,k ) − b e,m,k m + 1 a e,m,k ln ( P max e,m,k ψ e,m,k (1 − Ψ e,m,k ) + P max e,m,k Ψ E ,m,k − 1 ) , (23c) Γ e,l = T r N s X j =1 W s,j + Σ s G E ,l − b e,l + 1 a e,l ln ( P max e,l ψ e,l (1 − Ψ e,l ) + P max e,l Ψ e,l − 1 ) . (23d) 1 2 3 4 5 −5 0 5 10 15 20 25 The number of EHRs in the secondary network The minimum transmission power (dBm) OMA, non−cooperative,Algorithm 2 NOMA, non−cooperative, Algorithm 2 OMA, cooperative,Algorithm 2 NOMA, cooperative, Algorithm 1 NOMA, cooperative, Algorithm 2 Fig. 2: The minimum transmission po wer versus the number of EHRs in the secondary netw ork under the perfect CSI scenario. T ABLE IV : Comparison of the number of rank-one solutions achiev ed by Algorithms 1 and 2 ` ` ` ` ` ` ` ` ` Algorithm ( K s ) (1) (2) (3) (4) (5) Algorithm 1 0 0 0 0 0 Algorithm 2 259 207 248 301 196 one solutions, while Algorithm 1 cannot. The reason is that a cost function related to rank-one solutions is applied in Algorithm 2. When rank-one solutions are achieved, the op- timal beamforming vectors can be obtained for the CBS and PBS; otherwise, the optimal beamforming vectors cannot be obtained. This is the reason why Algorithm 2 performs better than Algorithm 1. Fig. 3 is provided for further verifying the efficiency of 1.5 2 2.5 3 3.5 4 −2 0 2 4 6 8 10 12 14 The minimum secrecy rate of PUs (Bits/s/Hz) The minimum transmission power (dBm) OMA, non−cooperative, Algorithm 2 NOMA, non−cooperative, Algorithm 2 OMA, cooperative, Algorithm 2 NOMA, cooperative, Algorithm 1 NOMA, cooperative, Algorithm 2 Fig. 3: The minimum transmission power versus the secrecy rate of PUs under perfect CSI scenario. the proposed cooperativ e jamming scheme. The number of EHRs in the secondary network is 2. It is observed that the transmission power increases with the secrecy rate of PUs. It can be readily explained by the fact that a high transmission power is required for guaranteeing the increased secrecy rate requirement of PUs. As shown in Fig. 3, the minimum transmission power required when the proposed cooperativ e jamming scheme is applied is lower than that in the absence of cooperation between the primary and the secondary network. This phenomenon further demonstrates the efficiency of our proposed cooperative jamming scheme for achie ving secure communications. It is also seen from Fig. 3 that NOMA outperforms TDMA and that Algorithm 2 performs better than Algorithm 1 in terms of the required transmission po wer . Fig. 4 shows the minimum transmission power versus the 12 2 4 6 8 10 12 14 16 18 20 0 2 4 6 8 10 12 14 The number of iterations The minimum transmission power (dBm) K s =3,Algorithm 1 K s =3,Algorithm 2 K s =2,Algorithm 1 K s =2,Algorithm 2 Fig. 4: The minimum transmission power versus the number of iterations required by using Algorithms 1 and 2. −2 −1 0 1 2 3 4 5 6 7 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 The minimum transmission power (dBm) The empirical cumulative distribution function (CDF) Perfect CSI, Algorithm 2 Perfect CSI, Algorithm 1 Imperfect CSI, Algorithm 2 Imperfect CSI, Algorithm 1 Perfect CSI Imperfect CSI Fig. 5: The empirical CDF of the minimum transmission po wer of the CBS for both perfect and imperfect CSI scenarios. number of iterations required by using Algorithm 1 and Algorithm 2. The number of EHRs in the secondary network is set to 2 or 3 . It is seen from Fig. 4 that both Algorithm 1 and Algorithm 2 require only a fe w iterations to conv erge. This confirms the ef ficiency of our proposed algorithms. It is also seen that the number of iterations required by Algorithm 2 is larger than that required by Algorithm 1. The reason is that the complexity of Algorithm 2 is higher than that of Algorithm 1. From Fig. 3 and Fig. 4, it is seen that there is a tradeoff between the complexity of algorithms and the transmission power obtained by using these algorithms. Fig. 5 sho ws the empirical cumulativ e distribution function (CDF) of the minimum transmission po wer under the perfect CSI and the bounded CSI error model. The number of EHRs in the secondary network is 2. It is seen from Fig. 5 that the transmission po wer consumed under the bounded CSI error model is higher than that consumed under the perfect CSI, for both Algorithm 1 and Algorithm 2. The reason is that a higher transmission po wer is required for guaranteeing the secrecy 1 1.5 2 2.5 3 3.5 −2 0 2 4 6 8 10 12 14 The minimum harvested power of EHRs in the secondary network (mW) The minimum transmission power (dBm) NOMA, perfect CSI OMA, perfect CSI NOMA, imperfect CSI OMA, imperfect CSI Fig. 6: The minimum transmission power versus the minimum harvested power requirement of EHRs in the secondary net- work for both perfect and imperfect CSI scenarios. rates of the PUs and the SUs, when the CSI is imperfect. It is also seen that Algorithm 2 is superior to Algorithm 1 in terms of the transmission po wer minimization, ev en when the CSI is imperfect. Fig. 6 shows the minimum transmission power versus the minimum harvested power requirement of EHRs in the sec- ondary network for both perfect and imperfect CSI scenarios. The number of EHRs in the secondary network is set to 3. The simulation results are obtained by Algorithm 2. It is seen that the transmission po wer consumed by using TDMA is higher than that consumed by using NOMA, for both perfect and imperfect CSI scenarios. The reason is that the secrecy rate of SUs achiev ed by using NOMA can be higher than that obtained by using TDMA [12]. A lower transmission power is required to grantee the secrecy rate of SUs. It is also seen that the imperfect CSI has a significant effect on the minimum transmission power . Moreover , as sho wn in Fig. 6, the minimum transmission power increases with the harvested power of EHRs in the secondary network. It can be readily explained by the fact that a higher transmission power is required to satisfy the increased harvesting power of EHRs in the secondary netw ork. V I . C O N C L U S I O N S Secure communication was studied for MISO NOMA CRNs using SWIPT , where a practical non-linear EH model was applied. T o enhance the security of the primary network, an artificial-noise-aided cooperative jamming scheme was pro- posed. The transmission beamforming vectors and AN-aided cov ariance matrix were jointly optimized to minimize the total transmission power of the network, while the secrecy rates of both PUs and SUs as well as the EH requirement of EHRs were satisfied. The beamforming design problems were inv estigated under both the perfect CSI and the bounded CSI error model. A pair of algorithms were proposed to solve these challenging non-con ve x problems. It was shown that 13 the performance achiev ed by using NOMA is better than that obtained by using OMA. Simulation results also show that the algorithm based on the cost function is superior to the algorithm based on SDR. Moreov er , our proposed cooperativ e jamming scheme is efficient to improve the security of MISO NOMA CRNs using SWIPT . R E F E R E N C E S [1] J. G. Andrews, S. Buzzi, W . Choi, et al. , “What will 5G be?, ” IEEE J. Sel. Areas Commun. , vol. 32, no. 6, pp. 1065-1082, Jun. 2014. [2] Y . C. Liang, K. C. Chen, G. Y . Li, and P . Mahonen, “Cognitiv e radio networking and communications: an overvie w , ” IEEE Tr ans. V eh. T echnol. , vol. 60, no. 7, pp. 3386-3407, Sept. 2011. [3] Z. Zhang, H. Sun, and R. Q. Hu, “Downlink and uplink non-orthogonal multiple access in a dense wireless network, ” IEEE J. Sel. Areas Commun. , to be published, 2017. [4] Z. Ding, X. Lei, G. K. Karagiannidis, R. Schober , J. Y uan, and V . Bhargav a, “ A surv ey on non-orthognonal multiple access for 5G networks: Research chanllenges and future trends, ” IEEE J. Sel. Areas Commun. , to be published, 2017. [5] B. W ang, L. Dai, Z. W ang, N. Ge, and S. Zhou, “Spectrum and energy ef- ficient beamspace MIMO-NOMA for millimeter-w ave communications using lens antenna array , ” IEEE J . Sel. Areas Commun. , to be published, 2017. [6] Y . Liu, Z. Ding, M. Elkashlan, and J. Y uan, “Nonorthogonal multiple access in large-scale underlay cognitiv e radio networks, ” IEEE T rans. V eh. T echnol. , vol. 65, no. 12, pp. 10152-10157, Dec. 2016. [7] L. Lv , J. Chen, Q. Ni, and Z. Ding, “Design of cooperative non- orthogonal multicast cognitiv e multiple access for 5G systems: user scheduling and performance analysis, ” IEEE T rans. Commun. , vol. 65, no. 6, pp. 2641-2656, June 2017. [8] F . Zhou, N. C. Beaulieu, Z. Li, J. Si, and P . Qi, “Ener gy-efficient optimal power allocation for fading cognitiv e radio channels: ergodic capacity , outage capacity and minimum-rate capacity , ” IEEE T rans. W ireless Commun. , vol. 15, no. 4, pp. 2741-2755, Apr . 2016. [9] D. Feng, C. Jiang, G. Lim, L. J. Cimini, G. Feng, and G. Y . Li, “ A survey of energy-eficient wireless communications, ” IEEE Commun. Surveys T uts. , vol. 15, no. 1, pp. 167-178, Feb. 2013. [10] X. Lu, P . W ang, D. Niyato, D. I. Kim, and Z. Han, “Wireless networks with RF energy harvesting: A contemporary surve y , ” IEEE Commun. Surveys T uts. , vol. 17, pp. 757-789, Second Quarter, 2015. [11] Y . Wu, R. Schober , D. W . K. Ng, C. Xiao, and G. Caire, “Secure massiv e MIMO transmission with an activ e eavesdropper , ” IEEE T rans. Inf. Theory , vol. 62, no. 7, pp. 3880-3900, 2016. [12] Y . Zhang, H. W ang, Q. Y ang, and Z. Ding, “Secrecy sum rate maxi- mization in non-orthogonal multiple access, ” IEEE Commun. Lett. , vol. 20, no. 5, pp. 930-933, 2016. [13] D. W . K. Ng, E. S. Lo, and R. Schober, “Multi-objective resource allocation for secure communication in cognitiv e radio networks with wireless information and power transfer , ” IEEE Tr ans. V eh. T echnol. , vol. 20, no. 2, pp. 328-331, Feb. 2016. [14] Y . W u, R. Schober, D. W . K. Ng, C. Xiao, and G. Caire, “Secure massive MIMO transmission in the presence of an active eavesdropper , ” in Pr oc. IEEE ICC 2015 , London, UK, 2015. [15] Y . Zou, B. Champagne, W . Zhu, and L. Hanzo, “Relay-selection improves the security-reliablity trade-off in cognitive radio systems, ” IEEE Tr ans. Commun. , vol. 63, no. 1, pp. 215-228, Jan. 2015. [16] X. Chen, D. W . K. Ng, W . H. Gerstacker , and H. H. Chen, “ A survey on multiple-antenna techniques for physical layer security , ” IEEE Commun. Surveys T uts. , vol. 19, no. 2, pp. 1027-1053, Second Quarter, 2017. [17] Y . W u, J. W ang, J. W ang, R. Schober, and C. Xiao, “Secure transmission with large numbers of antennas and finite alphabet inputs, ” IEEE T rans. Commun. , vol. 65, no. 8, pp. 3614-3628, June 2017. [18] Y . Pei, Y . C. Liang, K. C. T eh, and K. H. Li, “Secure communication over MISO cognitiv e radio channels, ” IEEE T rans. W ireless Commun. , vol. 9, no. 4, pp. 1494-1502, Apr . 2010. [19] Y . W u, R. Schober, D. W . K. Ng, C. Xiao, and G. Caire, “Secure massive MIMO transmission in the presence of an active eavesdropper , ” in Pr oc. IEEE ICC 2015 , London, UK, 2015. [20] Y . Zou, X. Li, and Y . Liang, “Secrecy outage and diversity analysis of cognitiv e radio systems, ” IEEE J. Sel. Ar eas Commun. , vol. 32, no. 11, pp. 2222-2236, Nov . 2014. [21] Y . Zou, J. Zhu, X. Li, and L. Hanzo, “Relay selection for wireless communications against eavesdropping: A security-reliablity trade-off persepectiv e, ” IEEE Network , vol. 30, no. 5, pp. 74-79, May , 2016. [22] F . Zhou, Z. Li, J. Cheng, Q. Li, and J. Si, “Robust AN-Aided Beamform- ing and Power Splitting Design for Secure MISO Cogniti ve Radio W ith SWIPT , ” IEEE Tr ans. W ireless Commun. , vol. 16, no. 4, pp. 2450-2464, April 2017. [23] D. W ang, P . Ren, Q. Du, L. Sun, and Y . W ang, “Security provisioning for vehicular relay networks via cooperative jamming and signal super- position, ” IEEE T rans. V eh. T echnol. , vol. 66, no. 12, pp. 10732-10747, Dec. 2017. [24] D. W ang, P . Ren, Q. Du, J. Chen, and Y . W ang, “ Achieving full secrecy rate with energy-efficient transmission control, ” IEEE T rans. Commun. , vol. 65, no. 12, pp. 5386-5400, Dec. 2017. [25] Q. Zhang, Q. Li, and J. Qin, “Robust beamforming for nonorthongonal muliple-access systems in MISO channels, ” IEEE T rans. V eh. T echnol. , vol. 65, no. 12, pp. 10231-10236, Dec. 2016. [26] F . Alavi, K. Cumanan, Z. Ding, and A. G. Burr , “Robust beaforming techniques for non-orthogonal multiple access systems with bounded channel uncertainties, ” IEEE Commun. Lett. , to be published, 2017. [27] B. He, A. Liu, N. Y ang, V . K. N. Lau, “On the design of secure non- orthogonal multiple access systems, ” IEEE J. Sel. Areas Commun. , to be published, 2017. [28] Y . Li, M. Jiang, Q. Zhang, Q. Li, and J. Qin, “Secure beamforming in downlink MISO nonorthogonal multiple access systems, ” IEEE T rans. V eh. T echnol. , vol. 66, no. 8, pp. 7563-7567, Aug. 2017. [29] J. Lei, J. Zhang, K. H. Park, et al. , “On secure NOMA systems with tranmit antennas selection schemes, ” IEEE Access , to be published, 2017. [30] M. Tian, Q. Zhang, S. Zhao, Q. Li, and J. Qin, “Secrecy sum rate opti- mization for downlink MIMO non-orthogonal multiple access systems, ” IEEE Signal Process. Lett. , vol. 24, no. 8, pp. 1113-1117, Aug. 2017. [31] Y . Pei, Y . C. Liang, K. T eh, and K. H. Li, “Secure communication in multiantenna cogniti ve radio networks with imperfect channel state information, ” IEEE Tr ans. Signal Process. , v ol. 59, no. 4, pp. 1683-1693, Apr . 2011. [32] L. Zhang, R. Zhang, Y . C. Liang, Y . Xin, and S. Cui, “On the relationship between the multi-antenna secrecy communications and cognitive radio communications, ” IEEE T rans. Commun. , vol. 58, no. 6, pp. 1877-1886, June 2010. [33] C. W ang, and H. W ang, “On the secrecy throughput maximization for MISO cognitive radio network in slow fading channels, ” IEEE T rans. Inf. F orensics Security , vol.9, no. 11, pp. 1814-1827, Nov . 2014. [34] W . Zeng, Y . Zheng, and C. Xiao, “Multiantenna secure cognitive radio networks with finite-alphabet inputs: A global optimization approach for precoder desing, ” IEEE T rans. W ireless Commun. , vol. 15, no. 4, pp. 3044-3057, Apr . 2016. [35] D. W . K. Ng, M. Shaqfeh, R. Schober, and H. Alnuweiri, “Robust layered transmission in secure MISO multiuser unicast cognitive radio systems, ” IEEE T rans. V eh. T echnol. , vol. 65, no. 10, pp. 8267-8282, Oct. 2016. [36] V . Nguyen, T . Duong, O. Shin, A. Nallanathan, and G. K. Karagiannidis, “Enhancing PHY security of cooperati ve cognitiv e radio multicast communications, ” IEEE Tr ans. Cogn. Net. , to be published, 2017. [37] L. Mohjazi, I. Ahmed, S. Muhaidat, M. Dianati, M. Al-qutayri, “Down- link Beamforming for SWIPT multi-user MISO underlay cognitive radio networks” IEEE Commun. Lett. , vol. 21, no. 2, pp. 434-437, Feb . 2017. [38] C. Xu, Q. Zhang, Q. Li, Y . T an, and J. Qin, “Robust transcei ver design for wireless information and power transmission in underlay MIMO cognitiv e radio networks, ” IEEE Commun. Lett. , vol. 18, no. 9, pp. 1665- 1668, Sept. 2014. [39] H. Zhang, P . Sun, C. Li, Y . Huang, and L. Y ang, “Cooperative precoding for wireless energy transfer and secure cognitiv e radio coexisence systems, ” IEEE Signal Process. Lett. , vol. 24, no. 5, pp. 540-544, May 2017. [40] Y . Y uan and Z. Ding, “Outage constrained secrecy rate maximization design with SWIPT in MIMO-CR systems, ” IEEE T rans. V eh. T echnol. , to be published, 2017. [41] Y . Huang, Z. Li, F . Zhou, and R. Zhu, “Robust AN-aided beamforming design for secure MISO cognitive radio based on a practical nonlinear EH model, ” IEEE Access , vol. 5, pp. 14011-14019, July 2017. [42] E. Boshkovska, D. Ng, N. Zlatanov , and R. Schober , “Practical non- linear energy harv esting model and resource allocation for SWIPT systems, ” IEEE Commun. Lett. , vol. 19, pp. 2082-2085, Dec. 2015. [43] E. Boshkovska, D. W . K. Ng, N. Zlatanov , A. Koelpin, and R. Schober, “Robust resource allocation for MIMO wireless po wered communication 14 networks based on a non-linear EH model, ” IEEE T rans. Commun. , vol. 65, no. 5, pp. 1984-1999, May 2017. [44] X. Kang, R. Zhang, Y . C. Liang, and H. K. Garg, “Optimal power allocation strategies for fading cognitiv e radio channels with primary user outage constraint, ” IEEE J. Sel. Ar eas Commun. , vol. 29, no. 2, pp. 374-383, Feb. 2011. [45] S. P . Boyd and L. V andenberghe, Conve x Optimization . Cambridge, U.K.: Cambridge Univ . Press, 2004.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment