Two High-performance Schemes of Transmit Antenna Selection for Secure Spatial Modulation
In this paper, a secure spatial modulation (SM) system with artificial noise (AN)-aided is investigated. To achieve higher secrecy rate (SR) in such a system, two high-performance schemes of transmit antenna selection (TAS), leakage-based and maximum…
Authors: Feng Shu, Zhengwang Wang, Riqing Chen
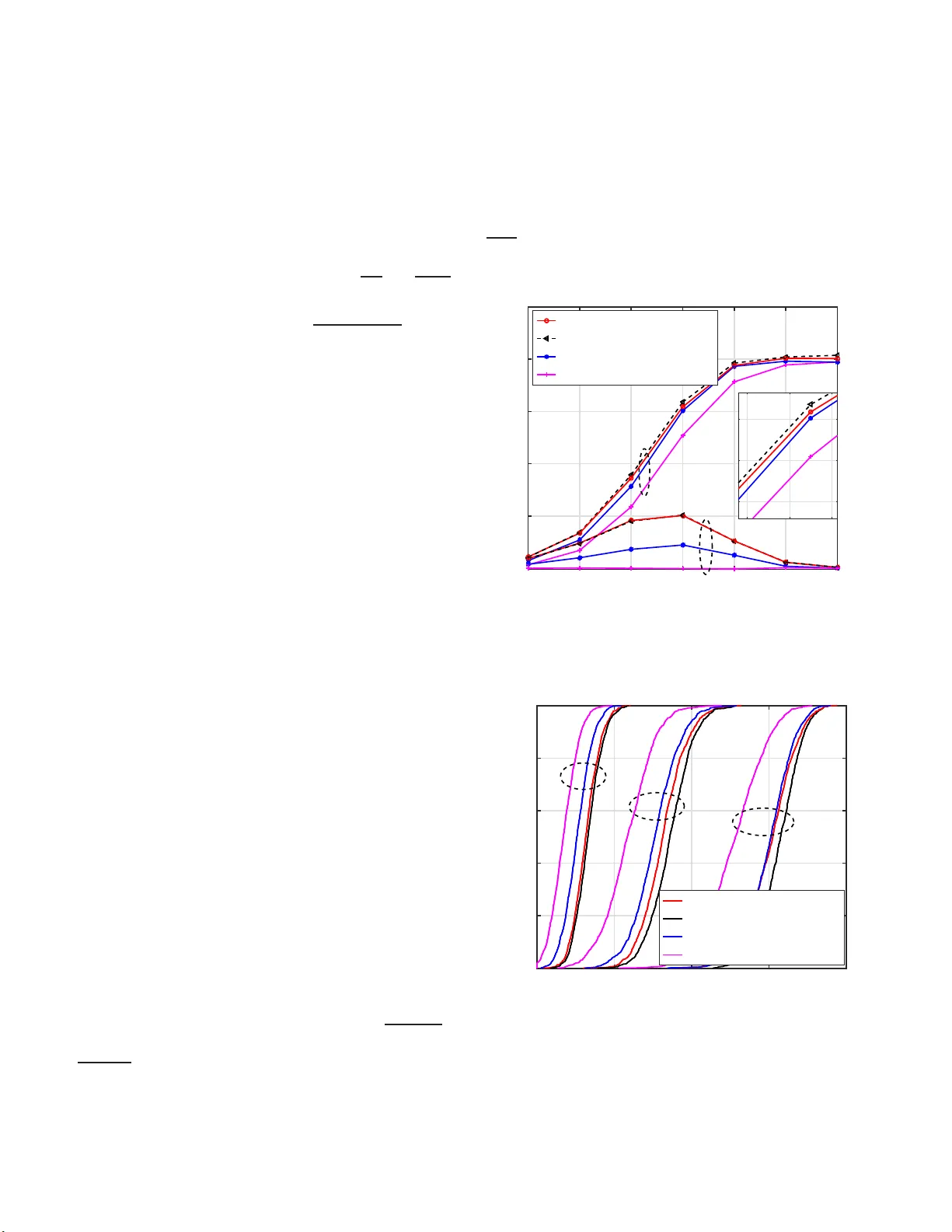
1 T wo High-performance Schemes of T ransmit Antenna Sel ection for Secure Spatial Mo dulation Feng Shu, Zheng wang W ang, Riqing Chen, Y ongpeng W u, and J iangzhou W ang, F ellow , IEEE Abstract —In this paper , a secure spatial modulation (SM) system with artificial noise (AN)-aided is in vestigated. T o achieve higher secrecy rate (SR) in such a system, two high-perf ormance schemes of transmit antenna selection (T AS), leakage-based and maximum secrecy rate (Max-SR), ar e proposed and a generalized Euclidean distance-optimized antenna selection (EDAS) method is designed. From simulation r esults and analysis, the four T AS schemes hav e an decreasing order: M ax-SR, leakage-based, generalized EDAS, and random (conv entional), i n terms of SR perfo rmance. Howev er , the proposed Max-SR method requires the exhaustive search to achieve th e optimal SR p erf ormance, thus its complexity is extremely high as the number of antennas tends to medium and large scale. The proposed leakage-based method app roac hes th e Max-SR method with much lower com- plexity . Thus, it achieves a good balance between complexity and SR perf ormance. In terms of bit error rate (BER), th eir perfo rmances are in an increasing o rder: rand om, leakage-based, Max-SR, and generalized EDAS. Index T erms —M IMO, secure spatial modulation, transmit antenna selection, signal-to-leakage noise ratio, artificial noise. I . I N T RO D U C T I O N S P A TIAL MODULA TION (SM) is emerging as a pr omis- ing m ultiple-inpu t-multiple- o utput (MIMO) commun ica- tion tech nology , w h ich exploits bo th the ind ex of activ ated transmit antennas and amplitude ph ase mod ulation (APM) sig- nals to carry bits informa tio n [1], [2]. Du e to low complexity of transmitter an d receiver , SM tech nology is applicab le to energy-efficient scen arios. However , in such a SM system, it is very possible that the con fidential messages are intercepted by unin tend receivers due to the broad cast natu re of wireless channel. How to achie ve a secur e transmission in SM systems is b ecoming a hot research topic in wireless networks. Recently , phy sical lay er security in MIMO systems have been widely inv estigated, which exploit th e uniquen ess a nd This work was in part supported by the National Natural Science Foun- dation of China (Grant Nos. 61771 244, 61702258, 61472190, 61501238 and 61602245), the China Postdoctoral Science Fo undatio n (2016M591852) , the Postdoctor al research funding program of Jiangsu Province (1601257C) , the Natural Science Foundat ion of J iangsu Province (Grants No. BK20150791 ), and the open research fund of National Mobile Communicatio ns Research Laboratory , Southeast Univ ersity , China (No.2013D02). Feng Shu, Zhengwang W ang are with School of Electronic and Optical Engineeri ng, Nanjin g Uni versity o f Science and T echnology , Nanj ing, 210094, China. Riqing Chen, and Feng Shu are with the College of Computer and Information Sciences, Fujian Agriculture and Forestry Unive rsity , Fuzhou 350002, China. Y ongpeng W u is with the Shanghai Ke y Laboratory of Navigat ion and Location -Based Servi ces, Shanghai Jiao T ong Univ ersity , Minhang 200240 Jiangzho u W ang is with the School of Engineering and Digital Arts, Uni ve rsity of Ke nt, Canterb ury CT2 7NT , U.K. E-mail : j.z.wa ng@k ent.ac.uk time-varying ch aracteristics of chann el to obtain secure tran s- mission again st ea vesdropper [3]–[7]. Some liter ature focuses on th e invest igation of SM sy stems f o r secure transmission [8]–[13]. Th e auth ors in [8] derived th e secrecy mutual in- formation of SM with fin ite a lphabet inp ut an d propo sed a precod in g scheme to impr ove security f or SM or space shift keying (SSK) systems in [12]. Both [9] and [1 3] compressed artificial noise (AN) onto the null-space of th e desired channel to interfere un known e avesdropper . V ia transmitting AN at transmitter [9] or fu ll-duplex receiver [13] may achieve a high secrecy r ate (SR) ap proach ing to the sp ectral efficiency (SE). In [10] and [ 1 1], the auth ors genera lized precoding -aided spatial modu lation (PSM) to secrecy PSM with constructin g time-varying precode r [10] or optimizing the precoder b y jointly minimizing the receive p ower at eavesdropper wh ile maximizing the recei ve power a t desired user [11]. PSM systems utilize the indices of receive antenn as to carry b its informa tio n, which reduces the comp lexity of re ceiv er . How- ev er , all tran smit antennas are acti vated in PSM s ystems, which results in the problems of inter-channel in terferenc e (ICI) and inter-antenna synchro nization (IAS) . On the other han d, tran smit an tenna selectio n (T AS) for improving the perfo r mance of SM systems was firstly in- vestigated in [14]. T he authors of [14] pr o posed two T AS methods: capacity-o ptimized antenna selection (COAS ) and Euclidean d istance-optim ized a n tenna selection ( ED AS). The ED AS sche me showed a better b it erro r ra te (BER) per f or- mance and hig her complexity than CO AS scheme. Th erefore, some literatur e was intended to reduce the comp utational and search complexity of the EDAS scheme [15]–[18]. T o the best of our k nowledge, there is no research work concern ing how to de sign T AS methods for secure SM system. In this p aper, we will focu s on the aspect resear c h an d make our effort to address this prob lem, our m ain con tributions are summarized as follows: 1) T o reach th e b o und of SR, a maximu m secrecy rate (Max-SR) m e th od is pro posed with exhaustive sear ch. In accordan ce with simu lation results, it can show the best SR perform ance in a large ran g e of SNR. 2) T o reduce the leakage of th e con fidential messages power for desired u ser to e avesdropper, a leaka g e-based T AS metho d is p roposed for secure SM system. Also, its low complexity version, i.e., sortin g -based solution, is presen ted to achieve th e same SR perform ance. Sim - ulation results show that the prop osed leakage-b ased method provides a SR perfor mance being close to tha t of the Max-SR method with far lower-complexity . 3) Finally , as a pe rforman ce b enchmar k, we also genera l- 2 ize the co n ventional EDAS m ethod in non-secu re SM system and make it become a secur e E DAS for secure SM sy stem. Meanwhile, we an alyze an d co mpare the complexity for the thr ee T AS meth ods. The remain der is o rgan ized as follows. In Section II, we describe secur e SM system model and g i ve a definition fo r its av erage secrecy rate. Subseq uently , we pro pose two T AS methods: leakage-b ased and Max-SR, and gener alize th e con- ventional EDAS scheme to secu r e SM system in Section III. In Section IV , numerical simu lation results ar e p resented. Finally , we make o ur conclusions in Section V . Notation: throug hout the paper , matrices, vectors, an d scalars a re denoted by letter s of bold upp er case, bold lower case, and lower case, respe c tively . Sign ( · ) − 1 , ( · ) H denote in- verse, conjug ate transpose, respectively . No tation E {·} stands for th e expectation operation. Matrices I N denotes the N × N identity matrix, and tr( · ) deno tes matrix trace. I I . S Y S T E M M O D E L A. Secu r e Spa tial Modula tion Consider a typica l secur e SM system as shown in Fig . 1. In the system , there are a tran smitter (Alice) equip p ed with N tr ansmit an tennas, a desired user (Bob ) with N b receive antennas, an d an ea vesdr o pper (Eve) with N e receive an te n nas, respectively . Without loss of generality , it is assumed that N is not a power of two, thus we h av e to select N t = 2 ⌊ log N 2 ⌋ out of N transmit antennas for mapping th e bits to the antenn a index. Notice that there ar e a to tal Q = N N t patterns, represented as Ω = { Ω 1 , · · · , Ω Q } , wh ere Ω k denotes the antennas set of the k th pattern. After Alice chooses o ne patter n from pattern set Ω a nd shares it with Bob thro ugh a lo w speed forward lin k, she acti vates o ne of N t transmit antennas to emit M -ary APM symbol and uses the index o f activ ated antenn a to conv ey partial bits info rmation. As a result, the SE is log 2 M N t bits per channel use (bpcu) . Referring to th e secure SM system mo del in [9], th e tr ansmit baseband signal with the aid of AN can be expressed as x = β 1 p P S e n s m + β 2 p P S P AN n (1) where e n is the n th colum n of I N t for n ∈ { 1 , 2 , · · · , N t } , and s m denotes the in put symbo l eq u iprobab ly drawn f rom discrete M -ary APM constellation for n ∈ { 1 , 2 , · · · , M } . W e normalize the input symbo l power to unit, i.e., E | s m | 2 = 1 . In (1 ), matr ix P AN ∈ C N t × N t is the AN p r ojection matrix , n ∼ C N (0 , I N t ) is the random AN vector, P S is the to tal transmit power , β 1 , and β 2 are the power allocatio n factors with β 2 1 + β 2 2 = 1 . Her e, it is particu la r ly n oted that all selected N t transmit an te n nas are used to emit AN but on ly one o f the m emits APM symbo l. Ther e fore, such secure SM system alleviates the pr oblems of ICI and IAS comp a red to conv entional secure MIMO systems. According ly , the signals ob ser ved at Bob a nd Eve can be respectively formulated as follows y b = β 1 p P S HT k e n s m + β 2 p P S HT k P AN n + n b , (2) RF APM symbol Activated ant enna Bits stream Eve Forward H G Bob Ă Ă Ă Ă 1 N e 1 N b N t N 1 TAS Artificial noi s e Fig. 1. System model of secure SM with T AS scheme and y e = β 1 p P S GT k e n s m + β 2 p P S GT k P AN n + n e , (3) where H ∈ C N b × N and G ∈ C N e × N are th e chann el state informa tio n (CSI) of desire d and eavesdropping ch annels, respectively . Without loss o f generality , we assume H and G are fre q uency-flat Rayleigh fading channels with each element ob eying the distribution C N (0 , 1) and th e CSIs are av ailab le at Alice, which might be tr ue for acti ve eavesdropper . T k ∈ R N × N t , k = 1 , 2 , ..., Q , is the T AS matrix constituted by the specifically selected N t columns deter m ined by Ω k of I N . Mean w h ile n b ∼ C N (0 , σ 2 b I N b ) an d n e ∼ C N (0 , σ 2 e I N e ) denote the comp lex ad ditiv e white gaussian noise (A WGN) vectors at Bob and Eve, r espectiv ely . Here, we project the AN lying in the null- space of desired channel, therefor e the P AN is given by P AN = 1 µ I N t − H k H H k H k H − 1 H k (4) where µ = k I N t − H k H H k H k H − 1 H k k F is the normal- ized factor of making th e id e ntity tr( P H AN P AN ) = 1 hold s, and H k = HT k . It is obvious that H k P AN = 0 , th is means the AN h as no impact on Bob . Assuming Bob has the kn owledge of H and T k , the maximum -likelihood detector ( MLD) is g iv en by [2] [ ˆ n, ˆ m ] = arg min n ∈ [1 ,N t ] ,m ∈ [1 ,M ] k y b − β 1 p P S HT k e n s m k 2 (5) B. A verage Secrecy Rate and Pr ob lem F ormula tion Here, we characteriz e the security by ev aluating average secrecy rate , which is form ulated as ¯ R s = E H , G ( R s ) (6) 3 with R s = [ I ( x ; y b | H , T k ) − I ( x ; y e | G , T k )] + (7) where R s denotes the definition of SR in [3]. I ( x ; y b | H , T k ) and I ( x ; y e | G , T k ) are th e mutual in formation over desired and eavesdropping chann els, respectively . Accor ding to [9], they are for mulated as fo llows I ( x ; y b | H , T k ) = log 2 M N t − 1 M N t N t X n =1 M X m =1 E n b log 2 N t X n ′ =1 M X m ′ =1 exp k n b k 2 − k δ n ′ ,m ′ k,n,m + n b k 2 σ 2 b , (8) and I ( x ; y e | G , T k ) = log 2 M N t − 1 M N t N t X n =1 M X m =1 E n ′ e log 2 N t X n ′ =1 M X m ′ =1 exp k n ′ e k 2 − k W − 1 / 2 α n ′ ,m ′ k,n,m + n ′ e k 2 (9) where δ n ′ ,m ′ n,m , α n ′ ,m ′ n,m and n ′ e are g iv en by δ n ′ ,m ′ k,n,m = β 1 p P S HT k ( e n s m − e n ′ s m ′ ) , (10) α n ′ ,m ′ k,n,m = β 1 p P S GT k ( e n s m − e n ′ s m ′ ) , (11) and n ′ e = W − 1 / 2 ( β 2 p P S GT k P AN n + n e ) (12) where n ′ e ∼ C N (0 , I N e ) is the A WGN vector , and W is the covariance matrix of inter f erence p lus n oise at Eve W = β 2 2 P S GT k P AN P H AN T H k G H + σ 2 e I N e (13) Finally , our objective is to max imize the SR by T AS scheme, which is written as the following optimization prob lem max R s subject to T k ∈ { T 1 , T 2 , ..., T Q } (14) which is an integer or binary optimization pro blem and is NP- hard. In the next section, we will presen t three T AS schemes for secure SM system. I I I . P RO P O S E D T R A N S M I T A N T E N N A S E L E C T I O N M E T H O D S In this section, we prop o se two new T AS schemes: leakage- based an d Max- SR, and generalize the co n ventional EDAS method to the secure SM scena r io. Then , we analyze the complexity for the thr ee T AS meth ods. A. Pr o posed Leakage-Based Anten na Se lection Metho d 1) Pr oblem F ormulation: Similar to multi-user MIMO system in [19], we view the receive power of confiden tial messages at Eve as the so-called leak age. Thus, the sign al- to-leakage -and-n oise r atio ( SLNR) for the n th chan nel of th e k th pattern is written as S LN R n ( T k ) = β 2 1 P S k HT k e n k 2 β 2 1 P S k GT k e n k 2 + N b σ 2 b (15) It is assumed that all N t T As of the selected pa tter n are acti- vated with equip robability to transmit confiden tial m e ssages, then th e op timization pro blem of maxim iz in g SLN R (Max - SLNR) is formulated as max N t X n =1 S LN R n ( T k ) subject to T k ∈ { T 1 , T 2 , ..., T Q } (16) with T k being th e optimization variable. Howe ver, the above optimization pro blem can be solved by exhau sti ve s earch with complexity O ( Q N t ) floating-po int ope r ations (FLOPs). T o lower its com p lexity , the low-complexity implemen tation is necessary . 2) Low-co mplexity sorting-based solution : Consider ing all transmit antenn a s are uncorrelated, that is, each transmit antenna results in different SLNR, the optimization p roblem in (16) is eq uiv alen t to choo se the largest N t values fro m a ll N SL N Rs. Once we calcu late the SLNR values p e r transmit antenna, we simply arrange them in descendin g order by sorting method as follow S LN R π 1 ≥ S LN R π 2 ≥ · · · ≥ S L N R π N t | {z } N t selected antennas ≥ · · · ≥ S LN R π N (17) where { π 1 , π 2 , ..., π N } is an ordered permutation of { 1 , 2 , ..., N } and S LN R π n is written as S LN R π n = β 2 1 P S tr h π n h π n H β 2 1 P S tr ( g π n g π n H ) + N b σ 2 b (18) where h π n and g π n are the π n th column o f H and G , respectively . B. Pr o posed Ma x-SR Antenna Selection Method In the previous sub section, it is hard for the prop osed leakage-b ased meth od to m aximize SR. In what follows, we will pro p ose th e Max-SR m ethod, w h ich aims to maxim ize SR. For a specific chann e l realization and th e k th selected pattern, th e transmission rates of desired and eavesdropping channels a r e respectively bounded a s [1 4] α ≤ R b ≤ α + lo g 2 N t , β ≤ R e ≤ β + log 2 N t (19) where α and β are given by α = 1 N t N t P n =1 log 2 1 + β 2 1 P S k HT k e n s m k 2 N b σ 2 b β = 1 N t N t P n =1 log 2 1 + β 2 1 P S k GT k e n s m k 2 β 2 2 P S k GT k P AN n k 2 + N e σ 2 e (20) Then, th e correspo nding SR is boun ded as α − β − lo g 2 N t ≤ R s ≤ α − β + lo g 2 N t (21) Notice that α and β are the fu nctions o f T k , thus we can carefully select a p attern for maximizing α − β , which can be formu late d a s max N t X n =1 log 2 1 + β 2 1 P S k HT k e n s m k 2 N b σ 2 b 1 + β 2 1 P S k GT k e n s m k 2 β 2 2 P S k GT k P AN n k 2 + N e σ 2 e subject to T k ∈ { T 1 , T 2 , ..., T Q } (22) 4 In g e n eral, the optimal T AS patter n for (22 ) is usually obtained by an exhausti ve search approach due to the fact that the P AN in (22) is a ssociated with the selected pattern. C. Gen eralized Euclidean Distance Antenna Selection Method Now , we d evelop the gene ralized ED AS method. It is well-known that the mutual inform a tion lacks clo sed-form expression for discrete-inpu t continuo us-outp u t m emoryless channels (DCMC). Here, we present a lower boun d for (8) I ( x ; y b | H , T k ) LB = log M N t 2 + N b 1 − 1 ln2 − 1 M N t N t X n =1 M X m =1 log 2 N t X n =1 M X m =1 exp − k δ n ′ ,m ′ n,m k 2 2 σ 2 b ! , (23) which is similar to that in [ 20]. Note that the lower bound is approx imately tig ht validated by Mo nte-Carlo simulation, so we may use it as an effecti ve d esign metric f or T AS sche m e. Notice that th e term δ n ′ ,m ′ k,n,m in (23) has an impo rtant impact on the lower bound and the minimum Euclidean distance, i.e., d min = min ( n,m ) 6 =( n ′ ,m ′ ) k δ n ′ ,m ′ k,n,m k 2 , is the dominant term in h ig h signal- to -noise ratio ( SNR) region [20]. In oth er words, th e bigg er d min is expe cted to yield a higher mutual informa tio n. Theref ore, we aim to select a T AS pattern o f maximizing th e minim um Euclidean distance over de sired channel or min imizing the minimu m E uclidean distance over eav esdropp in g channel [12], which are f o rmulated as follows T k ∗ = arg max T k ∈{ T 1 , T 2 ,..., T Q } min ( n,m ) 6 =( n ′ ,m ′ ) k δ n ′ ,m ′ k,n,m k 2 (24) T k ∗ = arg min T k ∈{ T 1 , T 2 ,..., T Q } min ( n,m ) 6 =( n ′ ,m ′ ) k α n ′ ,m ′ k,n,m k 2 (25) Here, we o btain two T AS pattern s by (24) and ( 2 5), th en we select the on e which results in high er R s . No te that some low com plexity meth ods fo r efficiently solving the problem s in (24) and (25) can be found in [ 15], [16], [18]. D. Complexity Analysis a nd Comparison Here, we make a co mplexity comp a rison concer ning the above thr ee metho ds. It is obvio us that the p r oposed leakage- based method has the lowest complexity of N (2 N b + 2 N e ) + O ( N 2 ) ≈ O ( N 2 ) FLOPs, where the ter m O ( N 2 ) is the search co mplexity of sorting o p eration. For the prop osed Max-SR metho d , th e complexity is about 2 QN t [ N 2 t ( N b + N e ) + N t (2 N 2 b + N e ) + 2 N e + N b ] ≈ O ( QN 3 t ) FLOPs. The complexity of gen eralized ED AS meth o d is made up o f three terms [18]: (a) the computation al com plexity of the upper triangle matrix of minimu m Euc lid ean distance, (b) the search complexity for optimal patter n , and (c) the complexity of com- puting secrecy rate for two patterns. The comp lexities of terms (a) and (b) are given by O a = 16 M ( N 2 − N ) N b + N e − 2 3 + N [2 ( N b + N e ) − 1] a n d O b = N t 2 + 3 N t + 3 2 N − N t − N +5 N +8 2 in [18]. The comp lexity of term (c) is as follows 2 M 2 N t 2 N noise [2( N t + 1)( N b + N e ) + N e 2 ] + 2 Q [ N 2 t ( N e + N b ) + 2 N t ( N 2 b + N 2 e )] , where N noise is th e n umber of noise samples fo r ev a luating th e secrecy rate. I n summary , it is evident that their com plexities are in in creasing order: leak age- based, Max-SR, and generalized ED AS. I V . S I M U L AT I O N A N D N U M E RI C A L R E S U LT S In this section, numerical simulation results are presented to analyze and com pare the perfor mance o f thre e T AS metho ds from different aspects: average secrecy rate, cum ulativ e den- sity function (CDF) of secrecy rate and bit erro r rate (BER) of Bob . Simulation parameters are set as follows: N b = N e = 2 , N = 15 , N t = 8 , and σ 2 b = σ 2 e . T he SNR is de fin ed as β 2 1 P S σ 2 b , and Quadrature Phase Shift Keying ( QPSK) modulation is e mployed. -10 -5 0 5 10 15 20 SNR (dB) 0 1 2 3 4 5 Average Secrecy Rate (bits/s/Hz) 2 4 6 2 2.5 3 Proposed leakage method Proposed Max-SR Generalized EDAS Random method β 2 =0 β 2 =0.25 Fig. 2. A verage secrec y rate of four T AS methods for β 2 = 0 . 25 , β 2 = 0 0 1 2 3 4 Secrecy Rate (bits/s/Hz) 0 0.2 0.4 0.6 0.8 1 CDF Proposed leakage method Proposed Max-SR Generalized EDAS Random method SNR=5dB SNR=0dB SNR=-5dB Fig. 3. CDF curves of secrecy ra te for S N R=-5dB, 0dB, 5dB and β 2 = 0 . 25 Fig. 2 demo n strates th e average SR for th e th ree T AS methods describ ed in Section-III with β 2 2 = 0 . 25 and β 2 2 = 0 , where th e random T AS m ethod is u sed for p erform ance referenc e . For β 2 2 = 0 . 25 , the SR performa n ce of the propo sed leakage-b ased m ethod is very close to the Max -SR metho d and b etter than the g eneralized EDAS m ethod and rand om 5 0 2 4 6 8 10 12 14 16 SNR (dB) 10 -5 10 -4 10 -3 10 -2 10 -1 10 0 Average BER Proposed leakage method Proposed Max-SR Generalized EDAS Random method Fig. 4. A verage BER curves of Bob for four T AS m ethods method. Whe n we a d just the value of β 2 2 to zero , we fin d the SR perfo r mance of th e pro posed leakage-b ased method is a lm ost iden tical to that o f Max-SR and m uch better than that of generalized ED AS method. It is also seen that rand om method fails to ach iev e positive SR. Fig. 3 shows the CDF cur ves of SR fo r f our T AS meth ods with three different values of SNRs: -5dB, 0dB, a n d 5dB. It is seen f rom Fig. 3 that the SR perf ormance of the pro- posed leakage-b ased meth od is between the p r oposed Max-SR method and the g eneralized ED AS metho d . W ith increasing in the value of SNR, the perf ormance o f gener alized EDAS method app roaches the two pro posed metho ds due to the fact that the m in imum Eu c lidean distance domin ates the mutual informa tio n te r m in the h igh SNR region in accor dance with (23). As SNR in creases, the CDF curves o f SR moves to the right-h and side. Tha t is, th e probab ility th at SR falls in the large value interval gr ows gradu a lly . Howe ver , for all three SNR values, the fou r T AS method s show the same SR perfor mance tr e nd: Max-SR ≥ leakage-b ased ≥ generalize d ED AS ≥ ran dom. Fig. 4 illustrates the c urves of average BER versus SNR for th e three T AS metho d s described in Section -III with β 2 2 = 0 . 25 , where th e random method is u sed fo r performanc e referenc e . From Fig. 4, it is seen that the gen eralized ED AS method exceeds the rema in ing three metho d s in terms of BER perfor mance. This is due to the fact the minimum Euclidean distance m akes an impor tant impact on p air-error prob ability (PEP) in high SNR region. T he BER perform ances of the propo sed lea kage-ba sed and Max-SR are worse than th at of generalized ED AS and better than that of ran dom m ethod. V . CO N C L U S I O N In this paper, we ha ve made an extensive inves tigation of T A S methods in secure SM systems. Then, two high- perfor mance T AS schemes: leakage- based and M ax-SR, h av e been pro posed to improve the SR perform ance, an d the EDAS method has been gene r alized to p rovide a secure transmission. From simulation results a nd complexity an alysis, the proposed Max-SR is the optimal T AS scheme a mong the three T AS methods in terms of SR perform ance w h ile th e proposed leakage-b ased method achie ves a SR performan ce near to the propo sed Max-SR metho d with far low complexity . By means of BER p erform ance, the gene r alized EDAS metho d s substantially outpe r forms the remain ing two meth ods du e to its main g oal to m a x imize minimu m Euclidean distance, which makes a dir ect imp rovement on BER p erform a n ce. R E F E R E N C E S [1] R. Y . Mesleh, H. Haas, S. Sinano vic, W . A. Chan g, and S. Y un, “Spatial modulati on, ” IEEE T rans. V eh. T echnol . , vol . 57, no. 4, pp. 2228–2241, 2008. [2] J. Jegan athan, A. Ghrayeb, and L . Szczecinski , “Spatia l modulation: optimal detection and performance analysis, ” IEE E Commun. Lett. , vol. 12 , no. 8, pp. 545–547, 2008. [3] A. D. W yner , “The wire-tap channel, ” B ell System T ech. J. , vol. 54, no. 8, pp. 1355–1387, 1975. [4] J. Hu, F . Shu, and J . Li, “Robust synthesi s method for s ecure direc- tional modulation with imperfect directi on angle , ” IEEE Co mmun. Lett. , vol. 20 , no. 6, pp. 1084–1087, 2016. [5] F . Shu, X. W u, J. Li, R. Chen, and B. V ucet ic, “Rob ust synthe sis scheme for secure mult i-beam directi onal modulation in broadc asting systems, ” IEEE Access , vol. 4, no. 99, pp. 6614–6 623, 2016. [6] N. Zhao, F . R. Y u, M. Li, Q. Y an, and V . C. M. L eung, “Physical layer security issues in interfe rence- alignment-based wireless networks, ” IEEE Commun. Mag . , vol. 54, no. 8, pp. 162–1 68, 2016. [7] H. M. W ang, Q. Y in, and X. G. Xia, “Distrib uted beamforming for physical -layer securit y of two-way re lay ne tworks, ” IE EE T rans. Signal Pr ocess. , vol . 60, no. 7, pp. 3532–3545, 2012. [8] X. Guan, Y . Cai, and W . Y ang, “On the secrec y mutual informati on of spatial modulati on with finite al phabet, ” in Proc. Int ernationa l Con- fer ence on W ir eless Communications and Signal Proc essing , pp. 1–4, 2013. [9] L. W ang, S. Ba shar , Y . W ei, and R. Li, “Se crec y enhancement analysis against unkn o wn ea vesdr opping in spat ial modula tion, ” IEEE Commun. Lett. , vol. 19, no . 8, pp. 1351–1354, 2015. [10] F . Wu, L. L . Y ang, W . W ang, and Z. Kong, “Secret precoding-a ided spatial modulation, ” IEEE Commun. Lett. , vol. 19, no. S cience, pp. 1544–1547, 2015. [11] F . Wu, R. Zhang, L. L. Y ang, and W . W ang, “Tra nsmitter precoding- aided spatial modulati on for secre cy communications, ” IEEE T rans. V eh. T ec hnol. , vo l. 65, no. 1, pp. 467–471, 2016. [12] S. R. A ghdam and T . M. Duman, “Physical layer securit y for space shift k eyi ng transmission with precoding , ” IEEE W ireless Commun. Lett. , vol. 5, no . 2, pp. 180–183, 2016. [13] C. Liu, L. L. Y ang, and W . W ang, “Secure spatial modulation with a full-dupl ex rec ei ver , ” IEEE W irele ss Commun. Lett. , vol. PP , no. 99, pp. 1–1, 2017. [14] R. Raj ashekar , K. V . S. Hari, and L. Hanzo, “ Antenna sele ction in spatial modulati on systems, ” IEEE Commun. Lett. , vo l. 17, no. 3, pp. 521–524, 2013. [15] K. Ntontin, M. D. Renzo, A. I. Per ez-Neir a, and C. V erikoukis, “ A low- comple xity method for antenna selec tion in spatial modulation systems, ” IEEE Commun. Lett. , vol. 17, no. 12, pp. 2312– 2315, 2013. [16] J. Z heng and J. Chen, “Further complex ity reduction for antenna select ion in spatial modulation systems, ” IEEE Commun. Lett . , vol. 19, no. 6, pp. 937–940, 2015. [17] P . Y ang, Y . Xiao, Y . L. Guan, S. Li, and L. Hanzo, “Transmit antenna select ion for multi ple-inp ut multiple-out put spatial modulatio n systems, ” IEEE T rans. Commun. , vol. 64, no. 5, pp. 2035–204 8, 2016. [18] Z. Sun, Y . Xiao, P . Y ang, S. Li, and W . Xiang, “Transmit antenn a select ion schemes for spatial m odulation systems: Search complex ity reducti on and large-sca le mimo application s, ” IEEE T rans. V eh. T echnol. , vol. 66 , no. 9, pp. 8010–8021, 2017. [19] M. Sadek, A. T arighat, and A. H. Sayed, “ A leakage-base d precoding scheme for downlink multi-use r mimo channels, ” IEEE T rans. W ir eless Commun. , vol . 6, no. 5, pp. 1711–1721, 2007. [20] X. Guan, Y . Cai, and W . Y ang, “On the mutual information and precodi ng for spatia l modulatio n with finite alphabet , ” IEEE W irel ess Commun. Lett. , vol . 2, no. 4, pp. 383–386, 2013.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment