GSM-CommSense-based through-the-wall sensing
We have recently proposed a scheme to use the channel equalization blocks of telecommunication systems to sense changes in an environment. We call this communication-sensing, CommSense for short. After some initial positive results we tried to use ou…
Authors: Abhishek Bhatta, Amit Kumar Mishra
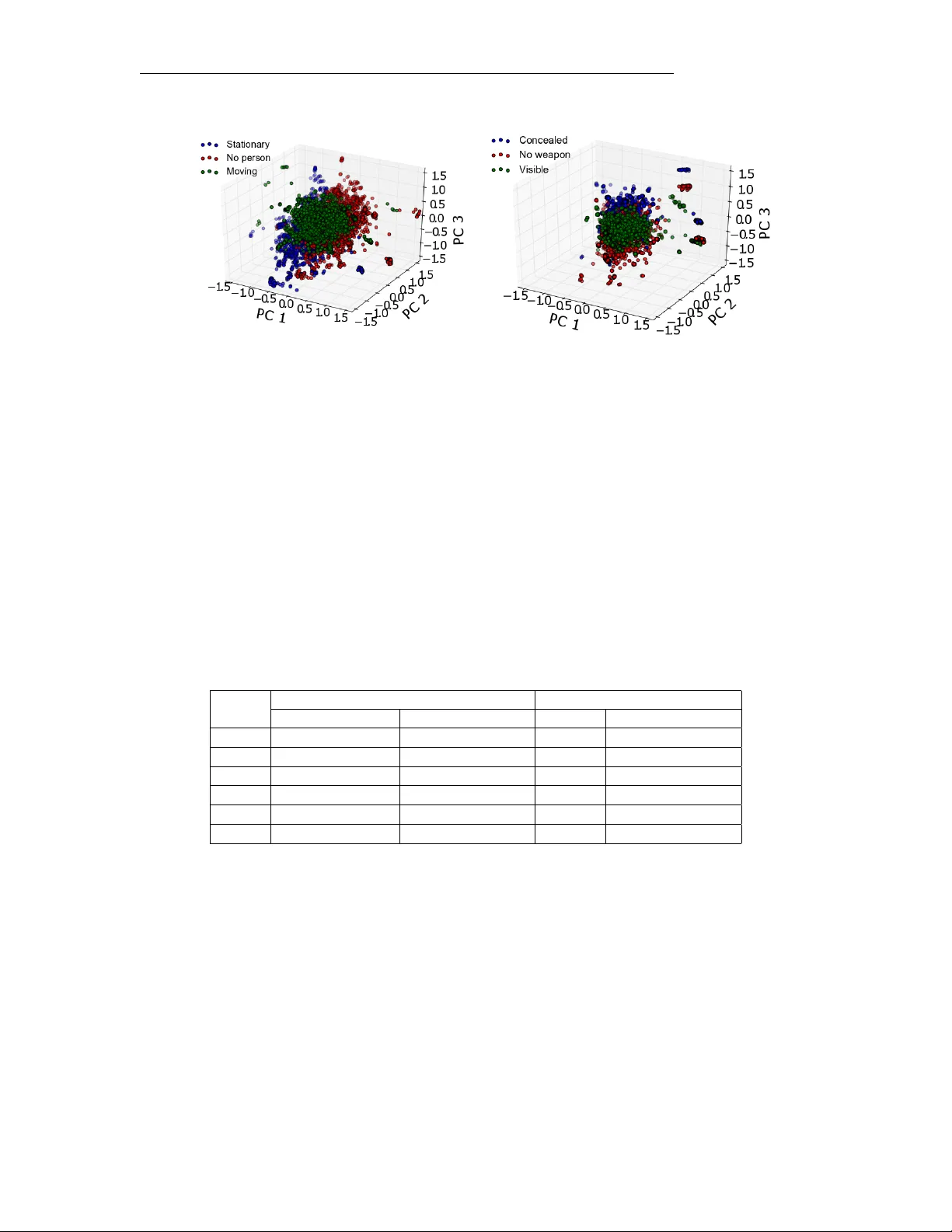
GSM–CommSense-based through-the-wall sensing Abhishek Bhatta Electrical Engineering Department Uni versity of Cape T o wn Email: bhattaomatic@gmail.com Amit Kumar Mishra Electrical Engineering Department Uni versity of Cape T o wn Email: akmishra@ieee.org August 17, 2021 Abstract W e ha ve recently proposed a scheme to use the channel equalization blocks of telecommunication systems to sense changes in an en vironment. W e call this communication-sensing, CommSense for short. After some initial positiv e results we tried to use our global system for mobile communication (GSM) based CommSense system for a through-the-wall sensing application. As the system w as inherently highly under-determined we used statistical machine learning techniques to help us sense environmental changes in the behind-the-w all experiments. W e observ ed that with limited amount of data per GSM frame of 577 µ s a person can be detected across a wall to an accuracy of 77 . 458% and a person carrying a weapon can be detected to an accurac y of 95 . 208% . W e present details of the experiments and the encouraging results that we hav e obtained in this article. 1 Intr oduction Combining radar and telecommunication system capabilities has been a major research focus for a long time [19]. This includes systems like passiv e or commensal radars [10, 17] that use the already available radio-frequency (RF) broadcast transmitters to detect and classify tar get parameters such as location, v elocity , etc.. In our work we started with the initial hypothesis that the channel estimation block of telecommunication systems can be used to gather information about the immediate environment [12], a system which we call communication-sensing (CommSense). The basic concept diagram of the CommSense system is shown in Figure 1. In the previous work [4], we used this system to detect various en vironmental parameters and the results were promising. Thus we decided to explore additional application of this system. In this article we 1 demonstrate the ability of CommSense to use global system for mobile communication (GSM) based signal to achiev e through-the-wall sensing. From here on we will refer to this system as GSM–CommSense. The current literature on using radar systems for through-the-wall sensing relies on either a system that uses a dedicated active transmitter [11], or a passiv e system without a dedicated active transmitter that requires a dedicated recei ver pointed at the reference with another pointed at the scene (surveillance) [9]. The reference and the surveillance channel information is then correlated to extract the target information. The GSM–CommSense system is designed to eliminate the need of the reference antenna and use the channel estimation techniques of GSM systems to extract the channel information. One of the major challenges of the GSM–CommSense system is the lack of sufficient amounts of data. For example in the initial design, GSM–CommSense only outputted 40 samples per data frame receiv ed. This was increased to 48 samples by revising the design and adjusting the buf fer size which is limited by the hardware capabilities. Getting a proper phenomenological sense from this amount of data did not seem possible. Hence, we used the application specific instrumentation framework (ASIN) [13, 16] which uses statistical machine learning to recognize ‘e vents of interest’. The shaded region in Figure 1 is the major focus of the work presented here, which corresponds to the analysis of the data captured by the GSM–CommSense system. W e show some encouraging results obtained from the limited amount of e xperiments we ha ve conducted to sense objects and ev ents behind the wall. 2 GSM–CommSense: A Short Review A channel, also kno wn as a physical transmission medium, introduces interference to the signal being transmitted through it. These interferences are proportional to the properties of the channel itself. In communication systems this type of interference causes degradation of the information and thus v arious channel equalization techniques are used to minimize the channel effects [6, 14, 15]. In case of a GSM system the transmitter transmits a known bit stream referred to as a training sequence which is used at the receiv er to equalize the effects of the channel. The GSM–CommSense system [4, 7] is designed to use the training sequence in order to extract the channel impulse response (CIR) and classify dif ferent en vironmental scenarios. The current work specifically focuses on sensing through-the-w all. The GSM–CommSense system [12], although based on the idea of a radar systems, is not a typical radar system as it does not process the information using correlation between a reference signal and surveillance signal. Instead it uses the training sequence to extract the channel effects. This eliminates the need for a reference channel which aids in reducing the ov erall cost of the design and makes it smaller, more portable system. One of the disadvantages of using the channel equalization to extract the channel parameters is that THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. Dir ect p ath R e fl ected path R e fl ected path BTS Ground surface R e fl ected path R e fl ected pa th Clouds S D R R e c e i v e r C h a n n e l E s t i m a t i o n S t a t i s t i c a l A n a l y s i s S u p e r v i s e d L e a r n i n g C l u s t e r i n g N e u r a l N e t w o r k s CommSense Syst em R eciev e Antenna Sea wa ves Figure 1: Concept diagram showing multipath signals from transmitter to recei ver and the blocks used in the GSM–CommSense system (the shaded region is the focus of the current work). The base transceiv er station (BTS) transmits the signal. it reduces the amount of data av ailable for identifying e vents of interest, as only 10 − 15% of the information transmitted ov er the channel is used for equalization. In [4] the basic implementation of GSM–CommSense is presented and the received data is statistically analysed for different environmental conditions. The system design and hardware considerations are discussed in detail in [7]. The major novelties of the GSM–CommSense system include using the training sequence to estimate the channel, eliminating the need for a reference antenna, all while being implemented on an open source, hardware-software platform, k eeping it open for future modifications. 3 Experimental Setup T erminologies used in the rest of the article. • Event: An event is defined as a general test set-up in which data is captured and analysed. • T est Scenario: A particular set-up under an event is defined here as a test scenario. Each event has multiple test scenarios. • Set: A set represents data captured for 30 s , which is used for analysis. Each test scenario has multiple sets. • Case: A case is used to differentiate between the particular set used for testing. Each case uses one set as test data and others as training data. The objectiv e in the current work is to demonstrate the ability of the GSM–CommSense system to sense ev ents across a brick wall of thickness 222 mm . There are in total two distinct ev ents analysed in this work as described below . THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. (a) Presence (in motion/stationary) and absence of a person in ‘Room 2’ with the receiv er placed in ‘Room 1’ (b) Presence of two persons in ‘Room 2’ one of whom is carrying a weapon with the receiver placed in ‘Room 1’. The test is performed in a house with the layout as shown in Figure 3. The separations show dif ferent rooms in the house and the dotted lines are the location of the doors. The weapons used for the purpose of this test are to y gun and a knife co vered with aluminium foil to increase the radar cross section (RCS) (shown in Figure 2). The aluminium foil is placed as the toy weapons are made of plastic and in reality most of the concealed weapons are made of metal. All the datasets of ev ent (a) were captured within the duration of an hour keeping the external parameters such as location of the objects within the room, temperature of the room, etc., constant for the duration of the test. The experiments for event (b) were conducted on a different day from event (a). This test was also performed within the duration of an hour and the external parameters, as mentioned above, were kept constant for the duration of the test. The receiv er is placed in ‘Room 1’ at a distance of 1 m from the wall and at a height of 1 . 12 m from the floor . The different test scenarios are described below . 3.1 Scenarios f or Event (a) 3.1.1 Person stationary Person standing in ‘Room 2’ at a distance of 3 m from the wall. Three sets of data are captured and analysed for this scenario. Each set contains data received and sampled for a 30 s interval with a break of 20 s in between consecutiv e sets. This time interval was chosen to create statistical rigour to the recei v ed data. Figure 2: Plastic toy weapons co vered with aluminium foil to increase the reflecti vity is used for testing. THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. 3.1.2 No Person In this scenario there is no person in ‘Room 2’ maintaining all the other parameters of the test. This scenario also contains the same amount of datasets with the same duration as the previous case. 3.1.3 Person Mo ving In this scenario the person is walking in a loop in ‘Room 2’ at a distance of approximately 3 m from the w all, as shown in Figure 3 for the entire duration of the test. This scenario also contains same amount of datasets as in the other two test cases. 3.2 Scenarios f or Event (b) 3.2.1 Concealed W eapon There are two persons in ‘Room 2’, one of them concealing a weapon under the jacket and the other is empty handed. Location of the person concealing the weapon is 3 m from the brick wall and the location of the second person is randomized in the room, keeping their random position fixed for each capture. Each set is captured in the same way as the person-stationary scenario defined abov e. 3.2.2 No W eapon In this scenario there are two persons in ‘Room 2’ neither of them carrying a weapon. Location of person- 1 is still at 3 m from the wall and person- 2 is randomly located in the room remaining stationary for the duration of the capture. 3.2.3 V isible W eapon This scenario is similar to the concealed-weapon scenario with the only difference being that the weapons are visible and not concealed under jacket. 4 Data Analysis Real time data is captured using the GSM–CommSense system for each of the scenarios defined in Section 3. The wireless GSM signal is receiv ed and digitally sampled using an analog-to-digital con verter . The channel information is extracted from these samples and saved into a binary file for further analysis. The analysis is performed in two steps, first the data is passed through a clustering algorithm called Principal Component Analysis (PCA) [3] to check if it contains an y visually separable information. The limitations of this method THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. R eceive anten na Brick w all Door Door Door Door Main entra nce Door 1 m 3 m L ocation of stationar y person P ath of moving person R oom 1 R oom 2 Figure 3: Layout of the experimental set-up. is that we can only visually separate the information in three dimensions. This limits the percentage of information av ailable for observation. Therefore, a supervised learning algorithm, Support V ector Machine (SVM) [8, 18] is used to predict each of the cases based on learning from the others. The major limitation of SVM is that it can only predict an outcome for an ev ent it has been trained on, so for each new scenario the algorithm has to be trained separately . Each of these analysis is performed directly on the dataset captured by the GSM–CommSense system. 4.1 Principal Component Analysis (PCA) 4.1.1 Description PCA is a statistical analysis tool which is used to transform an observation of possibly correlated variables into linearly uncorrelated components, called principal components. PCA is designed to provide the largest possible variance in the first principal component and each of the succeeding components has the highest possible variance with the constraint that it is orthogonal to the preceding component. This, when plotted provides the best possible visualization of the captured data. In order to deriv e the principal components from a data first we need to generate the Singular V alue Decomposition (SVD) [1, 2] equi v alent of the dataset. The SVD of the dataset represented by A is given as: A = U∆V T . (1) THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. Here U is a matrix of left singular vectors, V is a matrix of right singular v alues, and ∆ is a diagonal matrix of singular values. The principal component matrix F , as deriv ed from the data representation in Equation (1) is giv en as: F = U∆ . (2) Detailed calculations providing proper explanation of PCA and its implementation on the CommSense system is shown in [4]. 4.1.2 Results and Discussion Figure 4 contains a plot showing the contribution of individual principal components towards the total information present in one of the recorded dataset. It can be observed that the first 12 principal components constitute approximately 98% of the information, based on second order moment, and the contribution of each of the components after that are negligible (less than 0 . 2% per component). The PCA plots for the first three components of each dataset for event (a) are shown in Figure 5a and ev ent (b) are shown in Figure 5b. Although the first three components only contain about 52% of the total information, some differences in the clusters are visible. This is well within the range of expected outcomes because the test is to look for the change in one e vent while keeping ev erything else constant. Each of the colors in the PCA plots show details of a particular test scenario. In Figure 5a the blue color represents the condition when a person is stationary , the green color represents the condition when the person is moving within the room and the red color represents the condition when there is no person in ‘Room 2’ with the receiv er in ‘Room 1’. Similarly Figure 5b the blue color represents the condition when a person is concealing a weapon under a jacket, the green color represents the condition when the weapons are held visibly and the red color represents the condition when the person is not carrying any weapons in ‘Room 2’ with the receiv er 0 5 10 15 Pr incipal Components 0 . 0 0 . 2 0 . 4 0 . 6 0 . 8 1 . 0 Propor tion of v ar iance Cum ulativ e v ar iance V ar iance Figure 4: Scree plot showing the contribution of each principal component towards the total information content in the data. THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. in ‘Room 1’. T o get these plots, only a part of set 1 from each scenario is used which contains 3000 × 40 normalized data points for e vent (a) and 3000 × 48 normalized data points for ev ent (b). This does not result in a clear separation of the data as most of the conditions are constant with the only change being the test scenario itself. Thus another analysis needs to be performed to understand the separation in the datasets from each of the scenarios. 4.2 Support V ector Machines (SVM) 4.2.1 Description SVM is a supervised learning method that takes a labeled dataset, known as training data, and generates a model. This model can be used to categorize the test dataset. The objecti ve of SVM is to design a hyperplane in high dimensional space that classifies training sets into different classes. There may exist multiple such hyperplanes that can achiev e the same task of separating the classes, the best choice is the hyperplane that has maximum separation from nearest element from each class. In order to maximize the geometric margin between two classes and minimize the error , the soft margin SVM can be represented as: min α α α ∈ R F 1 2 || α α α || 2 2 + C n X i =1 l ( y i , f α ( x i )) . (3) Here, α α α is normal vector to the hyperplane that separates two classes of data, l ( . ) is a loss function, C is regularization parameter . f α ( x i ) = < φ ( x i ) , α α α > , where, φ ( x ) : R d > R F is a function that maps the training data points from input space, R d to a F − dimensional feature space, R F . || · || 2 , represents the standard or the Euclidean norm. < · , · > , is the scalar product of two vectors. For large F the inner products of the feature space can be calculated by a kernel function, k ( x, y ) = h φ ( x ) , φ ( y ) i . Detailed explanation regarding implementation of SVM on CommSense system is gi v en in [5]. 4.2.2 Results and Discussion Details of the datasets used in SVM for the purpose of training and testing is given in T able 1. After careful consideration and rigorous testing by varying the SVM parameters the penalty parameter is set to 1 . 0 , a linear kernel is used and, the influence of the training example giv en by , γ , is set to 0 . 025 for event (a) and 0 . 0208 for ev ent (b) to yield the best results. In case of ev ent (a) there are in total 39000 × 40 data points used for training and 12000 × 40 data points used for test. The training dataset is ev enly distributed into the three scenarios defined above with 13000 × 40 points for each scenario. Since two sets are used for training, each THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. (a) (b) Figure 5: PCA plots showing the clustering of through-the-wall data when the receiv er is in ‘Room 1’ and the ev ent occurs in ‘Room 2’. The e vents are: (a) PCA clusters in the presence of a stationary person, a moving person and no person (b) PCA clusters of a person with a concealed weapon, the person without a weapon and the person carrying a visible weapon. set consists of 6500 × 40 points. In the case of e vent (b) the number of sample points from each frame changes from 40 to 48 thus in total 39000 × 48 data points used for training and 12000 × 48 data points used as test dataset. The additional 8 points per dataset creates a noticeable difference in the prediction accuracy . The test dataset is ev enly distributed among the three scenario and there are 4000 × 40 points in ev ent (a) and 4000 × 48 points in e vent (b) per scenario. T able 1: Description of the test set and training set to generate T able 2 and 3 along with the number of data points used for training and testing. Case T raining set T est Set Sets No. of Data Points Sets No. of Data Points Case 1 Set 2( a ) and 3( a ) 39000 × 40 Set 1( a ) 12000 × 40 Case 2 Set 1( a ) and 3( a ) 39000 × 40 Set 2( a ) 12000 × 40 Case 3 Set 1( a ) and 2( a ) 39000 × 40 Set 3( a ) 12000 × 40 Case 4 Set 2( b ) and 3( b ) 39000 × 48 Set 1( b ) 12000 × 48 Case 5 Set 1( b ) and 3( b ) 39000 × 48 Set 2( b ) 12000 × 48 Case 6 Set 1( b ) and 2( b ) 39000 × 48 Set 3( b ) 12000 × 48 T able 2 contains the prediction output for ev ent (a). The datasets captured for this ev ent is represented by set 1( a ) , 2( a ) and 3( a ) in T able 1. The prediction results are shown in terms of percentage of correct classification. In case 1, set 1( a ) is used as test set when the classifier is trained using sets 2( a ) and 3( a ) . Similarly in case 2, set 2( a ) is used as test set when the classifier is trained using sets 1( a ) and 3( a ) . Similarly in case 3, set 3( a ) is used as test set when the classifier is trained using sets 1( a ) and 2( a ) . Since the number of datasets used for training and testing in each of the cases is the same, the average correct classification is calculated by summing the correct classification for each set and dividing by three. The results show that the lowest classification occurs ( 77 . 458% ) in the scenario where no person is present in the room. Although THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. T able 2: Confusion matrix for detection of a person through a brick wall. All the v alues shown here are in percentages. Predicted Label Case 1 Case 2 Case 3 A verage correct classification Person Stationary 86 . 000 4 . 825 9 . 175 85 . 725 3 . 525 10 . 750 86 . 125 4 . 975 8 . 900 85 . 950 No Person 16 . 925 71 . 925 11 . 150 8 . 250 82 . 500 9 . 250 12 . 850 77 . 950 9 . 200 77 . 458 Person Moving 9 . 775 6 . 675 83 . 550 5 . 775 4 . 275 89 . 950 10 . 550 6 . 475 82 . 975 85 . 491 Person Stationary No Person Person Moving Person Stationary No Person Person Moving Person Stationary No Person Person Moving T rue Label T able 3: Confusion matrix for detection of a person carrying weapon through a brick wall. All the values shown here are in percentages. Predicted Label Case 4 Case 5 Case 6 A verage correct classification Concealed W eapon 91 . 675 6 . 750 1 . 575 95 . 850 2 . 525 1 . 625 98 . 100 1 . 500 0 . 400 95 . 208 No W eapon 6 . 550 92 . 475 0 . 975 1 . 350 97 . 875 0 . 775 0 . 925 97 . 675 1 . 400 96 . 008 V isible W eapon 0 . 575 0 . 875 98 . 550 0 . 200 0 . 775 99 . 025 0 . 525 1 . 275 98 . 200 98 . 591 Concealed W eapon No W eapon V isible W eapon Concealed W eapon No W eapon V isible W eapon Concealed W eapon No W eapon V isible W eapon T rue Label the dif ference in prediction is not by a huge amount it can be explained by the fact that the reflections from a person’ s clothing might have similar features as the reflections from the curtains or the bed which the algorithm might be confusing as features of a person. Since there are only 40 feature points per frame, all the details are not captured and some similar features can confuse the algorithm to giv e ambiguous results. T able 3 contains the prediction output for ev ent (b). The datasets captured for this ev ent are represented by set 1( b ) , 2( b ) and 3( b ) in T able 1. The number of correct classifications in percentage for each case is shown in T able 3. In case 4, set 1( b ) is used as test data when the classifier is trained using sets 2( b ) and 3( b ) . Similarly in case 5, set 2( b ) is used as test data when the classifier is trained using sets 1( b ) and 3( b ) . Finally in case 6, set 3( b ) is used as test data when the classifier is trained using sets 1( b ) and 2( b ) . The number of feature points for this test scenario is 48 per frame and that shows a significant improvement in the prediction percentage. The scenario with the minimum av erage correct prediction percentage is the scenario with a concealed weapon ( 95 . 208% ). THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. 5 Conclusion In this article we presented an application of GSM–CommSense tow ards detection of two different through-the-wall ev ents. W e hav e captured multiple sets of data for each event and presented a detailed analysis of each set using different machine learning algorithms. W e show how data from different scenarios is clustered in a three dimensional PCA space and discuss the results. In addition to PCA clustering, we used a widely accepted supervised learning algorithm called SVM to check ho w accurate the predicted classification results are compared to the true values. The results are encouraging as a minimum average classification result obtained for detection of a person through a brick wall is 77 . 458% with only 40 points obtained from each GSM frame of 577 µ s and 95 . 208% in case of detection of weapon through a brick wall with 48 points. The change in the performance result is dependent on multiple factors including the increase in the number of points per sample and the fact that the weapons (with aluminium foil) hav e significantly high radar cross section compared to a person. The thickness and material of the wall is fixed as all the tests are performed in the same location. Changing the location changes many other en vironmental parameters that will cause in ambiguous categorization. Although if we train the system to detect across a certain wall it will always perform with the same amount of accuracy . The limitations for the current analysis is that the location of the person being detected across a wall is the same for all the cases. PCA used to observe clustering of the captured data shows only 52% of the information which makes it difficult to visualize proper separation of the clusters. Thus SVM is used which takes the entire training dataset and transforms into F − dimensional space to characterize the test data. The limitation of SVM is that it can only be tested for e vents it has been trained to detect. Thus in real-time the outcome of this system will be very application specific. Distance of the objects from the wall was kept standard for this particular testing and more robust measurements needs to be taken v arying more parameters. Refer ences [1] Herv ´ e Abdi. Singular v alue decomposition (SVD) and generalized singular value decomposition. Encyclopedia of measurement and statistics. Thousand Oaks (CA): Sage , pages 907–912, 2007. [2] Herv ´ e Abdi. The eigen-decomposition: Eigen v alues and eigenv ectors. Encyclopedia of measur ement and statistics , pages 304–308, 2007. [3] Herv ´ e Abdi and L ynne J W illiams. Principal component analysis. W iley Inter disciplinary Revie ws: Computational Statistics , 2(4):433–459, 2010. THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. [4] Abhishek Bhatta and Amit K Mishra. GSM-based commsense system to measure and estimate en vironmental changes. IEEE Aer ospace and Electr onic Systems Magazine , 32(2):54–67, 2017. [5] Abhishek Bhatta, Amit K Mishra, and Jan Pidanic. Classification of CommSense data using learning algorithms. In IET Radar Confer ence , 2017. [6] Abhishek Bhatta and Amit Kumar Mishra. Implementation of GSM channel estimation using open-source SDR en vironment. In ICMOCE, 2015 International Conference . IEEE, 2015. [7] Abhishek Bhatta and Amit Kumar Mishra. GSM based hand-held CommSense-sensor for en vironment monitoring. In ICIIS, 2016 International Conference on Industrial and Information Systems . IEEE, 2016. [8] Olivier Chapelle, Vladimir V apnik, Olivier Bousquet, and Sayan Mukherjee. Choosing multiple parameters for support vector machines. Machine learning , 46(1-3):131–159, 2002. [9] Ke vin Chetty , Graeme E Smith, and Karl W oodbridge. Through-the-w all sensing of personnel using passiv e bistatic wifi radar at standof f distances. IEEE T r ansactions on Geoscience and Remote Sensing , 50(4):1218–1226, 2012. [10] Michael Inggs, Cunsheng T ong, Roaldje Nadjiasngar , Graham Lange, Anadi Mishra, and Francois Maasdorp. Planning and design phases of a commensal radar system in the FM broadcast band. Aer ospace and Electr onic Systems Magazine, IEEE , 29(7):50–63, 2014. [11] Jing Li, Zhaofa Zeng, Jiguang Sun, and Fengshan Liu. Through-wall detection of human being’ s mov ement by uwb radar . IEEE Geoscience and Remote Sensing Letters , 9(6):1079–1083, 2012. [12] Amit Kumar Mishra. Monitoring changes in an en vironment by means of communication devices, 03 2017. [13] Amit Kumar Mishra and Santu Sardar . Application specific instrumentation and its feasibility for uwb sensor based breast cancer diagnosis. In P ower , Control and Embedded Systems (ICPCES), 2010 International Confer ence on , pages 1–4. IEEE, 2010. [14] P Newson and B Mulgrew . Adaptive channel identification and equalisation for GSM European digital mobile radio. In Communications, 1991. ICC’91, Confer ence Recor d. IEEE International Confer ence on , pages 23–27. IEEE, 1991. [15] Markku Pukkila. Channel estimation modeling. Nokia Resear ch Center , 2000. THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476. [16] Santu Sardar and Akhilesh Kumar Mishra. ASIN-based UWB radar for sludge monitoring. Access, IEEE , 2:290–300, 2014. [17] JM Thomas, HD Griffiths, and CJ Baker . Ambiguity function analysis of Digital Radio Mondiale signals for HF passiv e bistatic radar. Electr onics Letters , 42(25):1482–1483, 2006. [18] Vladimir V apnik. The natur e of statistical learning theory . Springer science & business media, 2013. [19] A. Wilson-Langman, M.R. Inggs, and A.K. Mishra. Symbiotic radar and communication system, December 31 2015. US Patent App. 14/768,382. THIS IS AN A CCEPTED MANUSCRIPT OF AN AR TICLE PUBLISHED BY T A YLOR & FRANCIS IN REMO TE SENSING LETTERS ON 16 DEC 2017, A V AILABLE ONLINE: http://www .tandfonline.com/10.1080/2150704X.2017.1415476.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment