A Tensor Completion Approach for Efficient and Robust Fingerprint-based Indoor Localization
The localization technology is important for the development of indoor location-based services (LBS). The radio frequency (RF) fingerprint-based localization is one of the most promising approaches. However, it is challenging to apply this localizati…
Authors: Yu Zhang, Xiao-Yang Liu
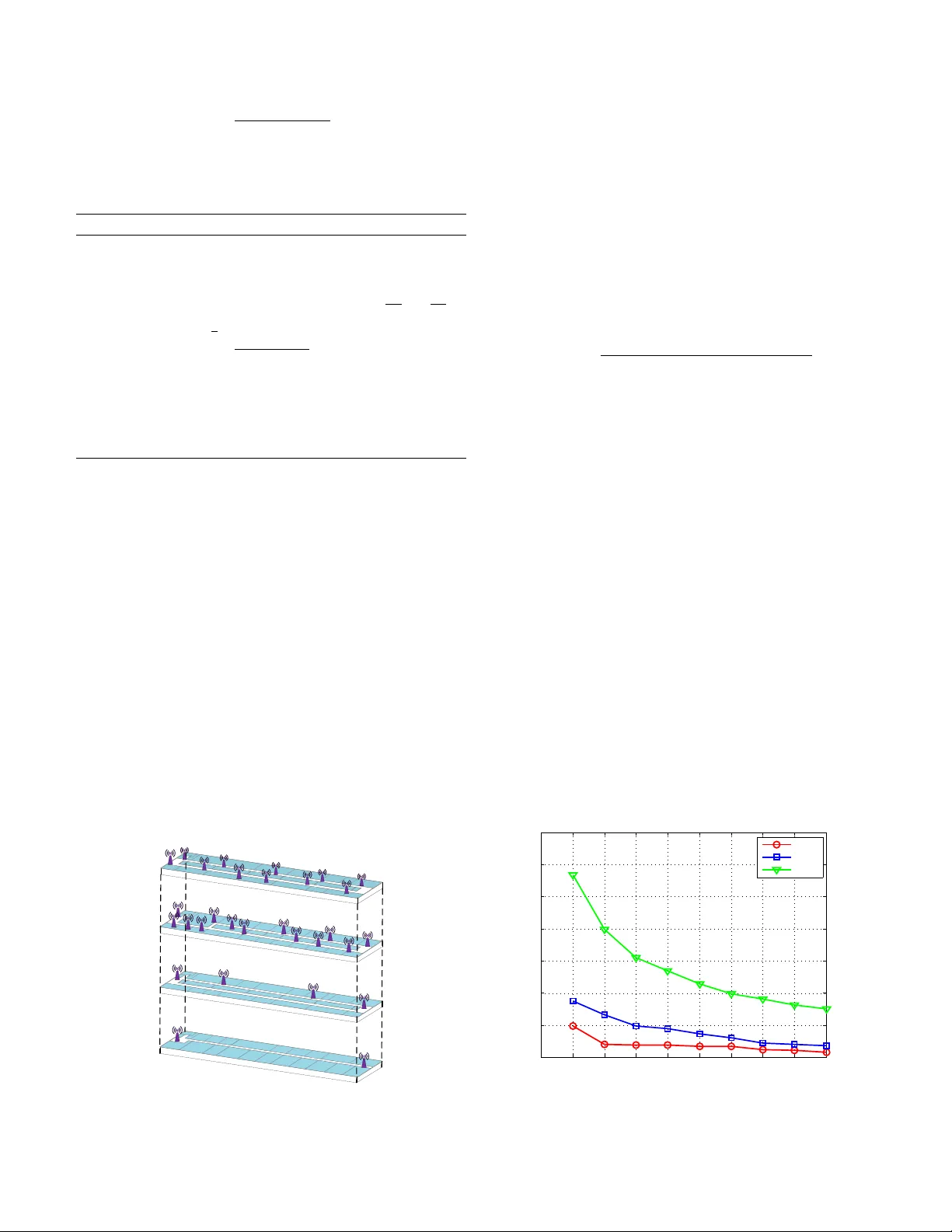
A T ensor Completion Approach for Ef ficient and Rob ust Fingerprint-based Indoor Localization Y u Zhang ∗ , Xiao-Y ang Liu † ∗ Shanghai Institute of Measurement and T esting T echnology , China † Shanghai Jiao T ong Uni versity , China ∗ zhang yu@simt.com.cn, † yanglet@sjtu.edu.cn Abstract —The localization technology is important f or the development of indoor location-based services (LBS). The radio frequency (RF) fingerprint-based localization is one of the most promising approaches. However , it is challenging to apply this localization to real-world en vironments since it is time-consuming and labor -intensive to construct a fingerprint database as a prior f or localization. Another challenge is that the pr esence of anomaly readings in the fingerprints reduces the localization accuracy . T o address these two challenges, we propose an efficient and r obust indoor localization approach. First, we model the fingerprint database as a 3-D tensor , which represents the relationships between fingerprints, locations and indices of access points. Second, we introduce a tensor decomposition model for rob ust fingerprint data recovery , which decomposes a partial observation tensor as the superposition of a low-rank tensor and a spare anomaly tensor . Third, we exploit the alternating direction method of multipliers (ADMM) to solve the con vex optimization pr oblem of tensor -nuclear-norm completion for the anomaly case. Finally , we verify the pr oposed approach on a ground truth data set collected in an office building with size 80 m × 20 m. Experiment results show that to achieve a same error rate 4 % , the sampling rate of our approach is only 10 % , while it is 60 % for the state-of-the-art approach. Moreov er , the proposed approach leads to a more accurate localization (nearly 20 % , 0.6 m improv ement) over the compared approach. I . I N T R O D U C T I O N Indoor location-based services (LBS) have received more and more attention with applications to many fields, such as navigation, health care and location-based security . The indoor localization is a supporting technology for LBS. The RF fingerprint-based approach is re garded as a promising solution, which can exploit ubiquitous infrastructure of W iFi access points and achiev e higher localization accuracy [1] [2] [3]. It consists of two phases: a training phase (site surve y) and an operating phase (online location). In the first phase, RSS fingerprints are collected from different access points (APs) at reference points (RPs) and constructs a fingerprint database (radio map), in which fingerprints are related with the corresponding RPs. In the second phase, the real-time RSS samples measured by user’ s mobile device are compared with the stored fingerprint database to estimate the user’ s current location. Howe ver , the major challenge for the RF fingerprint-based approach comes from the time-consuming and labor-intensi ve site surve y process, which collects RSS samples at dense RPs for constructing the fingerprint database. It will be a very exhausti ve process and lead to a significant workload. Further- more, the RSS fingerprints are usually corrupted by ubiquitous anomaly readings, which may come from the people moving, measuring de vice itself or the dynamic surroundings. As a result, it reduces the accuracy of the fingerprint data and then increase the localization error . Therefore, it is necessary to distinguish fingerprints from anomaly readings in a robust and accurate way . Some research w orks ha ve been dedicated to relie ve the site survey burden. The radio propagation model can be exploited to construct the fingerprint database from a small number of measurements [4]. Howe ver , it needs to ov ercome the influence produced by multipath fading and unpredictable nature of radio channel. The interpolation approaches are used to construct a complete fingerprint database, which usually estimate the missing RSS data by the interpolation of the measurements at local adjacent RPs [5]. They still demand collecting a lot of fingerprint data for obtaining better localization accuracy . Recent approaches include the matrix completion [6] and tensor completion [7], which recover the fingerprint data by exploiting the inherent spatial correlation of RSS measurements. Howe ver , the recovery accuracy may be reduced because of the presence of anomaly readings, which decrease the localization performance. T o explain the impact of the anomaly readings to data recov ery accuracy in tensor completion, we first verify that the tensor completion experiences performance degradation with the presence of a small portion of anomalies. Fig. 1 is a simple example, a 100 × 100 × 30 low-rank tensor taking values in [0,100], can be exactly recov ered using 40 % uniformly random selected samples. If we add anomalies with two different ratios 1 % and 5 % into the constructed tensor , the recov ery errors increase significantly . The essential reason is that a portion of anomaly readings break down the low-rank structure of tensor . Therefore, in this paper, we aim to reduce the ef forts during the site surve y , and at the same time, improv e the recovery accuracy of fingerprint data. Firstly , we exploit the notion of tensor rank proposed in [8] to model the RF fingerprint data as a 3-D tensor . Secondly , we propose a tensor decomposition model in the anomaly case for rob ust fingerprint data recov ery . The model decomposes a corrupted observ ation tensor as the superposition of a low-rank tensor and a spare anomaly tensor . Thirdly , we formulate the robust fingerprint data recovery problem as an optimization problem and exploit the ADMM algorithm for fingerprints completion. Finally , ev aluations on 0 10 20 30 40 50 60 70 80 90 0 5 10 15 20 25 30 35 Sampling Rate * 100 (%) Error * 100 (%) Without Anomaly Readings 1% Anomaly Readings 5% Anomaly Readings Fig. 1. T ensor completion with anomaly readings. a real fingerprint data set sho w that our scheme outperforms existing approach. Our contributions are as follows: • T o the best of our knowledge, this is the first work to study the anomaly tensor completion approach for fingerprint database construction. • W e exploit the ADMM algorithm to solve the proposed tensor completion problem. • The performance of the proposed tensor completion ap- proach is ev aluated based on the ground truth collected in real experiment field. Under the sampling rate 20 % , our approach achiev es less than 5 % recovery error . The localization accurac y has the improv ement of 20 % compared with the existing approach. The remainder of this paper is organized as follows. In Section II, we present the related works. Section III shows the problem formulation. Robust tensor completion is giv en in Section IV . The performance is ev aluated through imple- mentations in Section V . Finally , Section VI concludes the paper . I I . R E L AT E D W O R K Constructing fingerprint database is an important step for fingerprint-based localization, which has a great impact on the accuracy of localization. In order to ensure accuracy , a complete database is needed for localization. Some approaches are proposed for achieving complete fingerprint data while reducing the site surve y efforts. These approaches f all into two categories: correlation-aware approach and sparsity-aware approach. The correlation-a ware approach exploits the fact that the fingerprints at nearby RPs are spatially correlated. For ex- ample, the radio propagation model can construct the finger- print database by inserting some virtual data from the real measurements [4], which is not accurate in complex indoor en vironment because of signal reflection and dif fraction. So the interpolation approaches are used to construct a complete fingerprint database [5] [9], which usually estimate the missing RSS data by the interpolation of the measurements at local adjacent RPs. [10] presented a krigging interpolation method that can achieve more accurate estimation and reduce the workload. Such schemes outperform the radio propagation model approach, b ut they demand collecting a lot of fingerprint data for obtaining better localization accuracy . Sparsity-aware approach considers the inherent spatial cor- relation of RSS measurements. It exploits the compressive sensing (CS) to construct complete fingerprint database from partial observ ation fingerprints [11]. [12] assumed that RSS matrix for each AP was low-rank. [6] further assumed that the lo w-rank matrix w as smooth and exploits this property to construct fingerprint database. [13] exploited the spatial correlation structure of the fingerprints and use the frame work of matrix completion to build complete training maps from a small number of random sample fingerprints. Recently , as extension of matrix completion and a strong tool, tensor completion is applied to many domains for data completion from limited measurements. [7] proposed an adapti ve sampling method of tensor fibers based on which, the fingerprint data is constructed using tensor completion. It is the most related work to our approach. Through proper sampling, these ap- proaches can exactly recover the data from a small number of entries via low-rank optimization. Howe ver , fingerprints usually suffer from anomaly readings, the influence of the anomaly readings to data recovery accuracy is not considered in it. All abov e approaches mainly aim at reducing the site surve y efforts. Howe ver , the anomaly readings are common and ubiquitous and effect the recov ery accuracy of data. Our work is to further improv e the recovery accuracy by distin- guish fingerprint data from anomaly readings while reducing calibration efforts. Further more, the localization accuracy can be improv ed using the constructed fingerprint database. I I I . P R O B L E M F O R M U L A T I O N In this section, we first briefly describe our localization sys- tem architecture. Then we present the notations used through- out the paper , the algebraic frame work and preliminary results for third-order tensors as proposed in [7] [8] [14]. Finally , according to the fundamental theorems of tensor completion, we formulate the system model and state the problem for efficient and robust fingerprint-based indoor localization. T r a i n i n g O p e r a t i n g L o c a t i o n Q u e r y F i n g e r p r i n t D a t a b a s e L o c a t i o n E s t i m a t i o n R S S S a m p l i n g R S S M a p R e c o v e r y Fig. 2. Architecture of localization system. A. Indoor Localization System W e present our indoor localization system architecture, as shown in Fig. 2. The fingerprint-based localization procedure can be divided into two phases: training and operating. The main task of training phase is constructing the fingerprint database. W e first collect the fingerprint data at partial RPs, then recov er the the fingerprints of other RPs based on the sampled data and construct a radio map, in which the mapping between RSS fingerprint and its corresponding location is stored. In the operating stage, a user sends a location query with current fingerprint, then the serv er matches the query fingerprint with constructed radio map to estimate his location and returns the result to the user . B. Overview of 3-D T ensors A third-order tensor is denoted by T ∈ R N 1 × N 2 × N 3 , and its ( i, j, k ) -th entry is T ( i, j , k ) . A tube (or fiber) of a tensor is a 1-D section defined by fixing all indices b ut one, which is a vector . A sl ice of a tensor is a 2-D section defined by fix all b ut tw o indices. W e will use T (: , : , k ) , T (: , j, :) , and T ( i, : , :) to denote the f r ontal , l ateral and hor iz ontal slices , respectiv ely . In this paper, a vector T ( i, j, :) denotes a fingerprint at reference point ( i, j ) . Define ˘ T ( i, j, :) = fft( T ( i, j, :)) , which denotes the Fourier transform along the third mode of T . Similarly , one can obtain T from ˘ T via in verse Fourier transform, i.e., T = ifft( ˘ T , [ ] , 3) . The blkdiag( ˘ T ) is a block diagonal matrix, which places the frontal slices in the diagonal, i.e., diag( ˘ T (1) , ˘ T (2) , ..., ˘ T ( N 3 ) ) , where ˘ T ( i ) is the i th frontal slice of ˘ T , i =1, 2, ..., N 3 . The operation of a tensor-tensor product between two 3-D tensors is the foundation of algebraic development in [], which is defined as follows: Definition 1. t-product . The t-pr oduct K = A ∗ B of A ∈ R N 1 × N 2 × N 3 and B ∈ R N 2 × N 4 × N 3 is a tensor of size N 1 × N 4 × N 3 whose ( i, j ) th tube K ( i, j, :) is given by K ( i, j, :) = P N 2 k =1 A ( i, k , :) ∗ B ( k , j, :) , for i = 1, 2, ..., N 1 and j = 1, 2 , ..., N 4 . One can view a third-order tensor of size N 1 × N 2 × N 3 as an N 1 × N 2 matrix of tubes. So the t-product means the multiplication of two matrices, and the circular con volution of two tubes replaces the multiplication of two elements. Definition 2. T ensor transpose . Let T be a tensor of size N 1 × N 2 × N 3 , then T > is the N 2 × N 1 × N 3 tensor obtained by transposing each of the fr ontal slices and then r eversing the or der of transposed fr ontal slices 2 through N 3 . Definition 3. Identity tensor . The identity tensor I ∈ R N 1 × N 1 × N 3 is a tensor whose first fr ontal slice I (: , : , 1) is the N 1 × N 1 identity matrix and all other fr ontal slices ar e zer o . Definition 4. Orthogonal tensor . A tensor Q ∈ R N 1 × N 1 × N 3 is orthogonal if it satisfies Q > ∗ Q = Q ∗ Q > = I . Definition 5. The in verse of a tensor V ∈ R N 1 × N 1 × N 3 is written as V − 1 ∈ R N 1 × N 1 × N 3 and satisfies V − 1 ∗ V = V ∗ V − 1 = I . Definition 6. f-diagonal tensor . A tensor is called f-diagonal if each fr ontal slice of the tensor is a diagonal matirx . Definition 7. t-SVD . F or T ∈ R N 1 × N 2 × N 3 , the t-SVD of T is given by T = U ∗ Θ ∗ V > , (1) wher e U and V are orthogonal tensors of size N 1 × N 1 × N 3 and N 2 × N 2 × N 3 r espectively . Θ is a r ectangular f-diagonal tensor of size N 1 × N 2 × N 3 . Definition 8. T ensor tubal-rank . The tensor tubal-rank of a thir d-order tensor is the number of non-zer o tubes of Θ in the t-SVD . Definition 9. The tensor-nuclear -norm (TNN) denoted by kT k T N N and defined as the sum of the singular values of all the fr ontal slices ˘ T is a norm and is the tightest con vex r elaxation to the l 1 -norm of the tensor multi-rank. In fact, the tensor-nuclear -norm kT k T N N is equivalent to the matrix nuclear-norm k blkdiag( ˘ T ) k ∗ , i.e. , kT k T N N = k blkdiag( ˘ T ) k ∗ . C. System Model Suppose that the localization area is a rectangle R ∈ R 2 . W e divide the R into grids of same size. The grid map includes N 1 × N 2 grid points, which are called reference points (RPs). The grid map and the number of RP are denoted by C and N = N 1 × N 2 , respectively . There are N 3 av ailable access points (APs) in R , which are randomly deployed and the locations are unkno wn. W e use a third-order tensor T ∈ R N 1 × N 2 × N 3 to denote the RSS map. For each RP ( i, j ) , the RSS fingerprint at the RP can be denoted as a vector T ( i, j, :) , where T ( i, j, k ) is the RSS value of the k th AP . Note that if the k th AP cannot be detected, we assume the noise level is equal to − 110 dBm, namely , T ( i, j, k ) = − 110 dBm. The radio map stores the RSS fingerprint at each RP and its corresponding coordinates. W e use T ( i, j, :) to denote the RSS map of C , and the t-SVD is T = U ∗ Θ ∗ V > . The RSS value has high spatial correlation (columns and rows of C ) for each AP and also across these N 3 APs. Therefore we model this correlation by assuming that T has a low-rank tensor component X ∈ R N 1 × N 2 × N 3 , with tubal-rank r . Namely , there are only r non-zero tubes in Θ . On the other hand, the observed RSS values may be corrupted by anomaly readings. The anomalies are unknown a priori and sparsity . W e assume that T has another sparse tensor component Y ∈ R N 1 × N 2 × N 3 . Therefore, we suppose the T is the superposition of the X and Y . The model is defined as: T = X + Y . (2) D. Pr oblem Statement It will be a time-consuming and labor-intensi ve work if we collect fingerprint data at all RPs. T o reduce the workload in the site survey process, we sample fingerprints on a subset of RPs. Therefore, the site survey process is represented by using the following partial observation model under tubal-sampling: M = P Ω ( X ) + P Ω ( Y ) , (3) where M = P Ω ( T ) is an observ ation tensor , Ω being a subset of the grid map C , the ( i, j, k ) th entry of P Ω ( S ) is equal to S ( i, j, k ) if ( i, j ) ∈ Ω and zero otherwise. Note that the subset Ω can be obtained by non-adaptiv e or adaptiv e tubal-sampling approaches as proposed in [7]. W e focus on recov ering a tensor X from a partial observ a- tion tensor M . There are two properties about X : the tensor X is lo w-tubal-rank, and the estimated ˆ X should equal to M on the set Ω . W e can exploit the two properties to estimate X giv en the observ ation M by solving the follo wing optimization problem: Obj: h ˆ X , ˆ Y i = arg min hX , Y i r ank ( X ) + λ kY k 1 , 1 , 2 s.t. M = P Ω ( X ) + P Ω ( Y ) . (4) where X is the decision variable, rank( · ) denotes the tensor tubal-rank, and λ > 0 is a regularization parameter and the kY k 1 , 1 , 2 for 3D-tensor is defined as P i,j kY ( i, j, :) k F [14]. The goal of the problem (4) is to estimate a tensor X with the least tubal-rank in giv en set Ω and observation M case. Note that we must set a sufficient condition to guarantee unique solution for problem (4), which is defined as: kP Ω c ( Y ) k F = 0 . (5) It is quite reasonable that our aim is to recover the low-rank tensor X and we do not want to recover the anomaly tensor [15]. I V . R O B U S T T E N S O R C O M P L E T I O N W e adopt uniform random tubal-sampling approach from the grid map C to produce observation. Gi ven Ω , the tensor tubal-rank function in (4) is combinatorial. Similar to the low- rank matrix completion case, the optimization problem (4) is NP-hard. In this case, the tubal-rank measure can be relaxed to a tensor nuclear norm (TNN) measure as studied in [14], which is applied in the problem of tensor completion and tensor principal component analysis. Inspired by using the tensor-nuclear -norm for tensor com- pletion in no anomaly case, we propose the following problem for the anomaly case, which is equiv alent with (4) : Obj: h ˆ X , ˆ Y i = arg min hX , Y i kX k T N N + λ kY k 1 , 1 , 2 s.t. M = P Ω ( X ) + P Ω ( Y ) . (6) In order to solve the proposed conv ex optimization problem, we use the general ADMM. Based on the frame of ADMM, we introduce an intermediate variable Z and X = Z . Specifically , the augmented Lagrangian function of (6) is L ( X , Z , Y , A , B ) = kZ k T N N + λ kY k 1 , 1 , 2 +( M (:) − P Ω ( X (:) + Y (:))) T A (:) + µ 2 kM − P Ω ( X + Y ) k 2 F +( X (:) − Z (:)) T B (:) + ρ 2 kX − Z k 2 F . (7) The ADMM generates the new iterate ( X k +1 , Z k +1 , Y k +1 , A k +1 , B k +1 ) via the follo wing specific form: X k +1 = arg min X ( M (:) − P Ω ( X (:) + Y (:))) T A (:) + µ 2 kM − P Ω ( X + Y ) k 2 F +( X (:) − Z (:)) T B (:) + ρ 2 kX − Z k 2 F , (8) Z k +1 = arg min Z kZ k T N N + ( X k +1 (:) − Z (:)) T B (:) + ρ 2 kX k +1 − Z k 2 F , (9) Y k +1 = arg min Y λ kY k 1 , 1 , 2 +( M (:) − P Ω ( X k +1 (:) + Y (:))) T A k (:) + µ 2 kM − P Ω ( X k +1 + Y ) k 2 F , (10) A k +1 = A k + µ ( M − P Ω ( X k +1 + Y k +1 )) , (11) B k +1 = B k + ρ ( X k +1 − Z k +1 )) , (12) where µ , ρ , A and B are multipliers, K (:) denotes vectorizing the tensor K . The solution for X k +1 is gi ven by X k +1 = ( I + P Ω ) − 1 ( Z k + M − P Ω ( Y k + A k µ ) − B k ρ ) , where I is the identity tensor . The solution for Z k +1 is giv en by: Z k +1 = arg min Z kZ k T N N + ρ 2 kZ − ( X k +1 + B k ρ ) k 2 F . (13) Let J = X k +1 + B k ρ . By the definition, kZ k T N N = k blkdiag( ˘ Z ) k ∗ , therefore, (13) is a standard nuclear norm minimization problem and can be solved by applying soft thresholding on the singular values of J . Let A = U Σ V T be the singular v alue decomposition of A . W e define the singular value soft-thresholding (shrinkage) operator as D ε ( A ) = U S ε [Σ] V T , where S ε [ · ] is an element-wise soft-thresholding operator defined as: S ε [ x ] = x − ε, if x > ε, x + ε, if x < − ε, 0 , otherwise, (14) where ε > 0 . Therefore, the optimal solution to (13) is: blkdiag( ˘ Z ) = D 1 µ (blkdiag(fft( J ) , [ ] , 3)) , (15) we can obtain ˘ Z from blkdiag ( ˘ Z ) . The solution for Y k +1 is giv en by: Y k +1 = arg min Y λ kY k 1 , 1 , 2 + µ 2 kM − P Ω ( X k +1 + Y ) + A k µ k 2 F , (16) so Y is given by: Y k +1 ( i, j, :) = (1 − λ µ kY k ( i, j, :) k F ) + Y k ( i, j, :) . (17) For algorithm implementation, one can initialize A 0 and B 0 as zero tensors. Ω is an indicator matrix of size N 1 × N 2 . The iterativ e algorithm for (6) is proposed in Algorithm 1. Algorithm 1 Robust T ensor Completion Input: parameters Ω , M , N 1 , N 2 , N 3 , λ , µ , ρ , A 0 , B 0 . 1: Initialize: A 0 ← 0 ; B 0 ← 0 ; k ← 0 2: while not con verged do 3: X k +1 = ( I + P Ω ) − 1 ( Z k + M − P Ω ( Y k + A k µ ) − B k ρ ) 4: blkdiag( ˘ Z ) = D 1 µ (blkdiag(fft( J ) , [ ] , 3)) 5: Y k +1 ( i, j, :) = (1 − λ µ kY k ( i,j, :) k F ) + Y k ( i, j, :) 6: A k +1 = A k + µ ( M − P Ω ( X k +1 + Y k +1 )) 7: B k +1 = B k + ρ ( X k +1 − Z k +1 )) 8: k ← k + 1 9: end while Output: X , Y V . P E R F O R M A N C E E V A L U A T I O N In this section, we present the ev aluation methodology , which includes these aspects: ground truth, compared ap- proaches and metric. Then the experiment results sho w the fingerprint database recovery performance and localization performance of the proposed and compared approaches. A. Methodology The indoor localization system is named as SIMT -Net, as shown in Fig. 3. Our experiment field of 80 m × 20 m is on the fourth floor of a real office building. It is divided into 268 × 63 grid map. There are 30 APs deployed in the whole building, which can be detected in the e xperiment field of the fourth floor . W e collect the fingerprints at each RP in the grid map and use them to build a full third-order tensor as the ground truth. T o be specific, for each RP , we set the av erage of RSS time samples as its RSS vector . The ground truth tensor has dimension 268 × 63 × 30. Note that the RSS v alues are measured in dBm. Fig. 3. SIMT -Net. T o verify the effecti veness of the proposed approach, namely , tensor completion with anomaly readings (TCwA), two approaches for data recov ery are chosen for comparison. One of them is the standard tensor completion (STC) approach with not considering anomaly readings. Another is the oracle solution (OS) served as the optimal solution [16]. W e focus on two kinds of performance: recovery error and localization error . T o recov er the complete measurements in the test area, we randomly sample a subset of all RPs as the known measurements. V arying of the sampling rate is from 10 % to 90 % . W e quantify the recov ery error in terms of normalized square of error (NSE) for entries which are not included in the samples. The NSE is defined as: N S E = Σ ( i,j ) ∈ Ω c k ˆ T ( i, j, :) − T ( i, j, :) k 2 F Σ ( i,j ) ∈ Ω c kT ( i, j, :) k 2 F , (18) where ˆ T is the estimated tensor, Ω c is the completion of set Ω . T o further ev aluate the ef ficiency and robust of the con- structed radio map, the estimated tensor ˆ T is used for lo- calization. Here, we adopt classical localization technique, K-nearest neighbor (KNN), in the operating phase. In our experiments, we uniformly select 200 testing points within localization area and then exploit KNN algorithm to perform location estimation. The localization error is defined as the Euclidean distance between the estimated location and the real location of the testing point. B. F ingerprint Database Recovery P erformance Figure. 4 shows the RSS tensor recovery performance for varying sampling rate. Experimental results show the recov ery errors for these three algorithms decrease with the sampling rate increases. It can be found that TCwA yields better performance than STC which do not take anomaly into consideration. Concretely , our TCwA approach achie ves recov ery error ≤ 4 % for sampling rate ≥ 10 % , while STC approach has error 4 % at the sampling rate 60 % . The result indicates that TCwA has robust behavior . 0 10 20 30 40 50 60 70 80 90 0 2 4 6 8 10 12 14 Sampling Rate * 100 (%) NSE * 100 (%) OS TCwA STC Fig. 4. Comparison of different approaches. 0 0.5 1 1.5 2 2.5 3 3.5 4 4.5 5 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Location error (Meter) CDF OS STC TCwA Fig. 5. The CDFs of localization error of KNN with 20% sampling rate. C. Localization P erformance The anomaly readings have lar ge influences on the radio map construction and localization error . T o further e valuate the efficiency and robustness of the constructed radio map, the constructed results are used for location estimation. In our experiment, parts of RSS fingerprints of the RPs are used to construct fingerprint database while the rest are served as test. W e select randomly fingerprints of 200 RPs as the test data from the rest. Fig. 5 shows the empirical CDFs of localization error of KNN with 20 % sampling rate. Our approach TCwA yields better performance compared with the STC approach. F or example, the TCwA achie ves 2.5 m (80 % ) localization error , while STC has about 3.1 m (80 % ) localization error . The dif ference of localization accuracy be- tween TCwA and OS is small. It is shown that the localization results are consistent with the fingerprint database construction results. V I . C O N C L U S I O N S In this paper , we study the problem of constructing finger- print database in the site surve y process for indoor localization. W e propose a tensor decomposition model in the anomaly case for fingerprint data recovery . According to the low-tubal- rank feature of tensor and relationship between tensor-nuclear - norm and matrix nuclear-norm, we exploit ADMM algorithm to perform tensor completion and reconstruct the fingerprint database. Experiment results show that the proposed approach significantly reduces the number of measurements for fin- gerprint database construction while guaranteeing a higher recov ery accuracy of fingerprint data. It behaves robustly to anomaly readings interference. Furthermore, the localization accuracy is also enhanced compared to the existing approach. R E F E R E N C E S [1] M. Ficco, C. Esposito, and A. Napolitano, “Calibrating indoor position- ing systems with low efforts, ” IEEE T ransactions on Mobile Computing , vol. 13, no. 4, pp. 737–751, 2014. [2] S. Sorour , Y . Lostanlen, S. V alaee, and K. Majeed, “Joint indoor localization and radio map construction with limited deployment load, ” IEEE T ransactions on Mobile Computing , vol. 14, no. 5, pp. 1031–1043, 2015. [3] M. D. Redzic, C. Brennan, and N. E. O’Connor, “Seamloc: seamless indoor localization based on reduced number of calibration points, ” IEEE T ransactions on Mobile Computing , vol. 13, no. 6, pp. 1326–1337, 2014. [4] Z. Xiang, H. Zhang, J. Huang, S. Song, and K. C. Almeroth, “ A hidden environment model for constructing indoor radio maps, ” IEEE International Symposium on W orld of W ireless Mobile and Multimedia Networks (W oWMoM) , pp. 395–400, 2005. [5] S.-P . K uo and Y .-C. Tseng, “Discriminant minimization search for large-scale rf-based localization systems, ” IEEE T ransactions on Mobile Computing , vol. 10, no. 2, pp. 291–304, 2011. [6] Y . Hu, W . Zhou, Z. W en, Y . Sun, and B. Y in, “Efficient radio map construction based on low-rank approximation for indoor positioning, ” Mathematical Pr oblems in Engineering , vol. 2013, 2013. [7] X.-Y . Liu, S. Aeron, V . Aggarwal, X. W ang, and M.-Y . W u, “ Adapti ve sampling RF fingerprints for fine-grained indoor localization, ” IEEE T ransactions on Mobile Computing , 2016. [8] M. E. Kilmer , K. Braman, N. Hao, and R. C. Hoover , “Third-order tensors as operators on matrices: A theoretical and computational framew ork with applications in imaging, ” SIAM Journal on Matrix Analysis and Applications , vol. 34, no. 1, pp. 148–172, 2013. [9] J. Krumm and J. Platt, “Minimizing calibration efforts for an indoor 802.11 device location measurement system, ” Microsoft Researc h, T ech. Rep. MSRTR-2003-82 , 2003. [10] B. Li, Y . W ang, H. K. Lee, A. Dempster , and C. Rizos, “Method for yielding a database of location fingerprints in wlan, ” IEE Proceedings- Communications , vol. 152, no. 5, pp. 580–586, 2005. [11] C. Feng, W . S. A. Au, S. V alaee, and Z. T an, “Receiv ed-signal-strength- based indoor positioning using compressiv e sensing, ” IEEE T ransactions on Mobile Computing , vol. 11, no. 12, pp. 1983–1993, 2012. [12] Y . Zhang, Y . Zhu, M. Lu, and A. Chen, “Using compressive sensing to reduce fingerprint collection for indoor localization, ” IEEE Wir eless Communications and Networking Conference (WCNC) , pp. 4540–4545, 2013. [13] D. Milioris, M. Bradonjic, and P . Muhlethaler , “Building complete training maps for indoor location estimation, ” IEEE INFOCOM , pp. 75–76, 2015. [14] Z. Zhang, G. Ely , S. Aeron, N. Hao, and M. Kilmer, “Novel methods for multilinear data completion and de-noising based on tensor-svd, ” IEEE Confer ence on Computer V ision and P attern Recognition , pp. 3842– 3849, 2014. [15] X.-Y . Liu, X. W ang, L. Kong, M. Qiu, and M.-Y . W u, “ An LS- decomposition approach for robust data recovery in wireless sensor networks, ” arXiv preprint , 2015. [16] Z. Zhou, X. Li, J. Wright, E. Cands, and Y . Ma, “Stable principal component pursuit, ” IEEE International Symposium on Information Theory Pr oceedings (ISIT) , pp. 1518–1522, 2010.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment