Recalling a Witness: Foundations and Applications of Monotonic State
We provide a way to ease the verification of programs whose state evolves monotonically. The main idea is that a property witnessed in a prior state can be soundly recalled in the current state, provided (1) state evolves according to a given preorder, and (2) the property is preserved by this preorder. In many scenarios, such monotonic reasoning yields concise modular proofs, saving the need for explicit program invariants. We distill our approach into the monotonic-state monad, a general yet compact interface for Hoare-style reasoning about monotonic state in a dependently typed language. We prove the soundness of the monotonic-state monad and use it as a unified foundation for reasoning about monotonic state in the F* verification system. Based on this foundation, we build libraries for various mutable data structures like monotonic references and apply these libraries at scale to the verification of several distributed applications.
💡 Research Summary
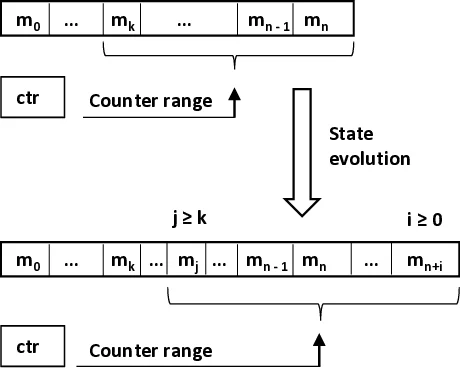
The paper introduces a systematic method for simplifying the verification of programs whose mutable state evolves monotonically, i.e., according to a preorder relation. The central insight is that a property observed in some earlier state can be safely “recalled” later, provided (1) every state transition respects the preorder (s₀ ≤ s₁) and (2) the property is stable under that preorder (p s₀ ∧ s₀ ≤ s₁ ⇒ p s₁). To make this usable in practice the authors define two logical primitives: witness and recall. witness p records that a stable predicate p holds now and will hold in all future states, yielding a state‑independent proposition witnessed p. recall p later re‑establishes p in the current state, assuming witnessed p is available.
These ideas are encapsulated in the Monotonic‑State Monad (MST), a small extension of the standard state monad. MST provides four operations: get, put, witness, and recall. The type of put is constrained by the preorder, ensuring that any state update is monotonic. The witnessed connective turns a state‑dependent predicate into a pure logical assertion, and a lemma witnessed_weaken shows that witnessed is functorial with respect to logical implication.
The authors give a rigorous meta‑theoretic foundation. In §5 they develop a sequent calculus for first‑order logic enriched with the witnessed connective, prove cut‑admissibility, and thereby establish consistency. Using this calculus they prove soundness of a Hoare‑style total‑correctness logic for a core dependently‑typed λ‑calculus extended with the MST interface. In §6 they show how MST computations can be represented as pure state‑passing functions without violating the preorder, enabling relational reasoning (e.g., non‑interference) and safe extension of the interface with new preorder‑respecting actions.
On the implementation side, the paper demonstrates three flavors of references built on MST: (i) untyped references (uref) that allow arbitrary updates, (ii) typed references (ref t) that enforce type‑preserving (weak) updates, and (iii) monotonic typed references (mref t rel) where each reference carries its own preorder, allowing fine‑grained control over monotonicity. This hierarchy lets programmers opt‑in to monotonic reasoning where appropriate while retaining the flexibility of ordinary mutable state elsewhere.
Two substantial case studies illustrate the practical impact. The first is a secure file‑transfer application, which uses monotonic references to guarantee safe memory initialization, model a ghost append‑only log of messages, and combine refinement types with stable predicates to enforce cryptographic security properties. The second is Ariadne, a protocol for ensuring state continuity of hardware‑protected components (TPMs, SGX enclaves) across crashes and restarts. Here a ghost state machine records protocol progress as an append‑only log; monotonicity ensures that once a protocol step is recorded it cannot be undone, simplifying the proof of continuity. Both examples avoid the cumbersome manual framing of invariants that traditional Hoare or separation‑logic approaches would require.
The related‑work discussion positions MST against separation logic, abstract separation logic, and recent effect systems that encode temporal constraints. While separation logic excels at spatial reasoning, MST provides a lightweight, logic‑level mechanism for temporal monotonicity, complementary to spatial invariants. The paper also revisits earlier ad‑hoc uses of monotonicity in the F* verification ecosystem (e.g., cryptographic libraries, TLS implementations) and shows how MST offers a unified, formally justified foundation for all of them.
In conclusion, the authors deliver a compact yet expressive interface for monotonic state, a solid logical foundation, and concrete libraries that scale to real‑world distributed and security‑critical applications. Future work includes extending the approach to concurrent settings, integrating with richer effect systems, and exploring automated synthesis of preorder specifications.
Comments & Academic Discussion
Loading comments...
Leave a Comment