Social Learning Against Data Falsification in Sensor Networks
Although surveillance and sensor networks play a key role in Internet of Things, sensor nodes are usually vulnerable to tampering due to their widespread locations. In this letter we consider data falsification attacks where an smart attacker takes c…
Authors: Fern, o Rosas, Kwang-Cheng Chen
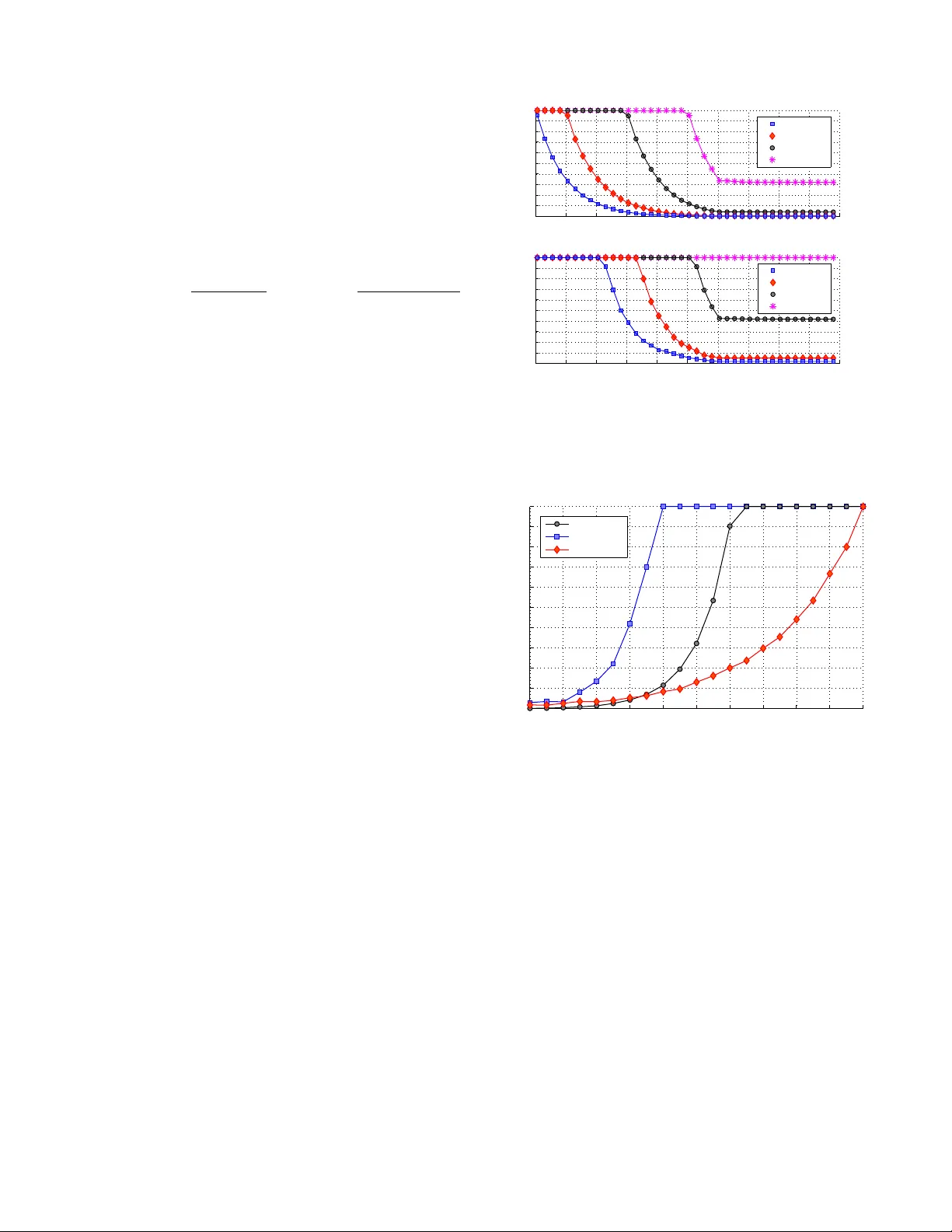
1 Social Learning Against Data F alsification in Sensor Networks Fernando Rosas and Kwang-Cheng Chen, F ellow , IEEE Abstract —Although surveillance and sensor networks play a key r ole in Inter net of Things, sensor nodes ar e usually vulnerable to tampering due to their widespread locations. In this letter we consider data falsification attacks where an smart attacker takes control of critical nodes within the network, including nodes serving as fusion centers. In order to face this critical security thread, we propose a data aggregation scheme based on social learning, resembling the way in which agents make decisions in social networks. Our results suggest that social learning enables network resilience, e ven when a significant portion of the nodes hav e been compromised by the attacker . Finally , we show the suitability of our scheme to sensor networks by developing a low-complexity algorithm to facilitate the social learning data fusion rule in devices with r estricted computational power . Index T erms —Data fusion, sensor networks, surveillance net- works, bizantine generals problem, social learning, network security , r esilient networks. I . I N T RO D U C T I O N Large distributed sensor networks typically provide surveil- lance services ov er extensiv e areas, such as activity monitoring in military or secure zones, protection of drinkable water tanks from chemical attacks, or intrusion detection [1], [2]. Howe ver , the reliability of these netw orks is in many cases limited due to the high vulnerability of the sensor nodes [3]. In reality , nodes are frequently located in unprotected locations and are susceptible to physical or cyber captures. Moreov er , nodes are generally not tamper-proof due to cost concerns, and their limited computing power , memory , and energy capabilities do not allo w sophisticated cryptographic techniques. One serious threat to the reliability of distributed surveil- lance is the data falsification or “Byzantine” attack, where an adversary takes control over a number of authenticated nodes [4]. Follo wing the classic Byzantine Generals Pr oblem [5], Byzantine nodes can generate false sensing data, exhibit arbitrary behaviour or collude in order to create a networked malfunction. The ef fect of data falsification attacks over dis- tributed detection has been intensely studied, characterizing the impact over the detection performance and also proposing various defense mechanisms (c.f. [6] for an overvie w , and also [7]–[9]). These w orks focus in networks with star or tree topology , where the data is gathered in a special node called “fusion center” (FC) that is responsable for the final decision. A key assumption in the literature is that the adversary can compromise regular sensor nodes but not the FC itself. The authors are with the Graduate Institute of Communication Engi- neering, National T aiwan University , T aipei 10617, T aiwan (email { nrosas, ckc } @ntu.edu.tw). K.C. Chen is also with the Department of Electrical Engineering, University of South Florida, T ampa, FL 33620, USA (email kwangcheng@usf.edu). Howe ver , in many scenarios the short range of the nodes’ transmissions force the FC to be installed in unsafe loca- tions, being vulnerable to tampering as well. A tampered FC completely disables the detecting capabilities of the network, generating a single point of failure and hence becoming the weakest point of the system [10]. T o address this serious security thread, this letter is novel in considering powerful topology-aware data falsification attacks, where the adversary knows the network topology and lev erage this knowledge to take control of the most critical nodes of the network —either regular nodes or FCs. This represents a worst-case scenario, where the network structure has been disclosed e.g. from network tomography via traffic analysis [11]. The design of reliable distributed detection schemes is a challenging task. In effect, even though the distributed sensing literature is vast (see e.g. [1], [2] and references therein), the construction of optimal schemes is in general NP-hard [12]. Moreov er, although in many cases the optimal schemes can be characterized as a set of thresholds for likelihood functions, the determination of these thresholds is usually an intractable problem [13]. For example, symmetric thresholds can be suboptimal e ven for networks with similar sensors arranged in star topology [14], being only asymptotically optimal when the network size increases [13], [15]. Moreover , symmetric strategies are not suitable for more elaborate netw ork topolo- gies, and hence heuristic methods are usually necessary . T o deal with this dilemma, in this letter we propose a low- complexity data aggregation scheme based on social learn- ing principles, which resembles social decisions-making pro- cesses while av oiding fusion center functions [16]–[18]. The scheme is a threshold-based data fusion strategy related to the ones considered in [13]. Howe ver , its connection with social decision-making enables an intuitive understanding of its inner mechanisms, and also allows an ef ficient implementation that is suitable for the limited computational capabilities of a sensor node. For avoiding the security threads introduced by fusion centers, our scheme uses a tandem or serial topology [19]– [23]. Contrasting with the literature, our analysis does not focus on optimality issues of the data fusion but aims to illus- trate how this scheme can enable network resilience against a powerful topology-aw are data falsification attacker , ev en when a significant number of nodes have been compromised. I I . S Y S T E M M O D E L A N D P RO B L E M S TA T E M E N T A. System model W e consider a network of N sensor nodes that are deployed ov er an area where surveillance is needed. The output of the 2 sensor of the n -th node is denoted by S n , taking values over a set S that can be discrete or continuous. Based on these sig- nals, the network needs to infer the v alue of the binary variable W , with events { W = 1 } and { W = 0 } corresponding to the presence or absence of an attack, respectiv ely . No knowledge about of the prior distribution of W is assumed, as attacks are rare and might follo w unpredictable patters. W e consider nodes with equal sensing capabilities, and hence assume that the signals S n are identically distributed. For the sake of tractability , it is assumed that the variables S 1 , . . . , S N are conditionally independent ∗ giv en the ev ent { W = w } , follo wing a probability distribution denoted by µ w . It is assumed that both µ 0 and µ 1 are absolutely continuous with respect to each other [25], i.e. no particular signal determines W unequiv ocally . The log-likelihood ratio of these two distrib utions is therefore giv en by the logarithm of the cor- responding Radon-Nikodym deriv ative Λ S ( s ) = log dµ 1 dµ 0 ( s ) † . In addition to sensing hardware, each node is equipped with computing capability and a low-po wer transcei ver to transit and receiv e data. Howe ver , battery limitations impose sev ere restrictions ov er the communication bandwidth, and thus it is assumed that each node forward its data to others by broadcasting a binary variable X n . Note that these signals could be appended to wireless control packages and viceversa. The nodes transmit their signals sequentially according to their indices. Due to the nature of wireless broadcasting, which might be ov erlooked in some security literatures, nearby transmissions can be ov erheard. Therefore, it is assumed that the n -th node can generate X n based on information provided by S n and X n − 1 = ( X 1 , . . . , X n − 1 ) . A strate gy is a collection of functions π n : S × { 0 , 1 } n − 1 → { 0 , 1 } such that X n = π ( S n , X n − 1 ) . Although the burden of ov erhearing all the pre viously broadcasted signals can be reduced by designing smart network topologies and routing strategies, these networking functions are left for future studies. The network operator collects the transmitted packages from a specific node labeled as n c ∈ { 1 , . . . , N } , possibly employing unmanned ground or aerial vehicles that access a shared signal at a specific network location, or by using a shared communication channel. The network performance is quantified by the corresponding miss-detection and false alarm rates, gi ven by P { MD } = P { X n c = 0 | W = 1 } and P { F A } = P { X n c = 1 | W = 0 } , respecti vely . Finally , it is assumed that N ∗ Byzantine nodes are con- trolled by an adversary without being noticed by the network operator . The adversary can freely define the values of the binary signals transmitted by byzantine nodes in order to degrade the network performance. It is further assumed that the adversary is “topology-a ware”, knowing the node sequence and the strategy that is in use. Therefore, the adv ersary could well control the N ∗ most critical nodes in terms of network ∗ The conditional independency of sensor signals is satisfied when the sensor noise is due to local causes (e.g. thermal noise), but do not hold when there exist common noise sources (e.g. in the case of distributed acoustic sensors [24]). † When S n takes a finite number of values then dµ 1 dµ 0 ( s ) = P { S n = s | W =1 } P { S n = s | W =0 } , while if S n is a continuous random v ariable with conditional p.d.f. p ( S n | w ) then dµ 1 dµ 0 ( s ) = p ( s | w =1) p ( s | w =0) . performance. Howe ver , the adversary has no knowledge about n c , as it can be chosen at run-time and changed regularly . B. Problem statement Our goal is to dev elop a network-resilient strategy to mitigate the effect from a powerful topology-aware adversary when the network operator (i.e. defender) has no knowledge of the number of Byzantine nodes or other attack’ s statistics. Note that in most surveillance applications miss-detections are more important than false alarms, being difficult to estimate the cost of the worst-case scenario. Therefore, the system performance is ev aluated follo wing the Neyman-Pearson criteria by setting an allowable false alarm rate and focusing on the achiev able miss-detection rate. Most signal processing techniques for distrib uted detection rely on a FC(s) that gather data and generate estimators, and sensor nodes that provide informati ve signals to them [26]. Intuitiv ely , if X n is influenced by X m with m < n , this would “double-count” the information provided by S m . Therefore, in order to guarantee diversity , traditional distributed detection schemes choose to ignore pre viously broadcasted signals. Howe ver , as nodes don’t perform any data aggregation, each of their shared signals are not, by themselves, good estimations of the target v ariable. This generates a single point of failure in the network, as if the adversary compromises the FC(s) then the only accurate estimator that exist within the network is lost and hence the inference process fails. I I I . S O C I A L L E A R N I N G A S A D A T A A G G R EG AT I O N S C H E M E A. Data fusion rule Social learning models supply new directions to analyze the sequential decision processes where agents combine personal information and peers’ opinions [18]. Applied to a sensor network, each node can be considered as an agent that decides the presence of attacks based on measurements and ov erheard signals from other nodes. In this letter we consider rational agents that follo w a Bayesian strate gy , denoted as π b n ( S n , X n − 1 ) , which can be described by P W = 1 | S n , X n − 1 P W = 0 | S n , X n − 1 π b n =0 ≶ π b n =1 u (0 , 0) − u (1 , 0) u (1 , 1) − u (0 , 1) . (1) Abov e, u ( x, w ) is a cost assigned to the decision X n = x when W = w , which can be engineered in order to match the relev ance of miss-detections and false alarms [27]. Moreover , by noting that X n − 1 = π b n − 1 ( S n − 1 , X n − 2 ) is influenced only by S 1 , . . . , S n − 1 , the conditional independency of the signals imply that S n and X n − 1 are also conditionally independent giv en W = w . Therefore, using the Bayes rule, a direct calculation sho ws that (1) can be re-written as Λ S ( S n ) + Λ X n − 1 ( X n − 1 ) π b n =0 ≶ π b n =1 τ , (2) where τ = log P { W =0 } P { W =1 } + log u (0 , 0) − u (1 , 0) u (1 , 1) − u (0 , 1) and Λ X n − 1 ( X n − 1 ) is the log-likelihood ratio of X n − 1 . As the prior distribution of W is usually unknown, the network operator needs to select 3 the lowest value of τ that satisfies the required false alarm rate giv en by the Neyman-Pearson criteria (c.f. Section II-B). As in a realistic scenario the statistical properties of the potential topology-aware data falsification attacks are not av ailable to the defender , our approach is to make each node to follow a bayesian strategy ignoring the potential attack. Such an approach has three attractive features: 1. Provides a computation rule that does not need to adapt to dif ferent attacker’ s profiles. 2. Minimizes the average cost E u ( π n ( S n , X n − 1 ) , W ) when no attacks tak e place [27]. 3. Enables network resilience (c.f. Section III-C and IV). Clearly Byzantine nodes do not follow (2), as their interest is to degrade the network performance. Let us denote as B the set of indices of the Byzantine nodes and N ∗ the cardinality of B . As events { W = 0 } are much more frequent than { W = 1 } , any abnormal increase of the false alarm rate would be easily noted and hence provides no benefit to the adversary . Therefore, a rational strategy for the adversary is to increase the miss-detection rate by forcing X n = 0 for all n ∈ B . B. An algorithm for computing the social log-lik elihood The only challenge for implementing (2) in a sensor node as a data fusion rule is to have an efficient algorithm for computing Λ X n − 1 ( x n − 1 ) . For finding such an algorithm, a direct application of the chain rule of probabilities shows that Λ X n ( x n ) = log n Y k =1 P n X k = x k | X k − 1 = x k − 1 , W = 1 o P n X k = x k | X k − 1 = x k − 1 , W = 0 o , with the understanding that X 0 = x 0 is null. Then, follo w- ing the discussion presented in Section III-A, we compute P { X k = x k | X k − 1 = x k − 1 , W = w } ignoring potential attacks. Assuming that the k -th node is not a Byzantine node, one obtains P { X k = 0 | X k − 1 = x k − 1 , W = w } = Z S P n X k = 0 | X k − 1 = x k − 1 , W = w , S k = s o d µ w ( s ) = Z S 1 π b k ( s, x k − 1 ) = 0 d µ w ( s ) = P w Λ S ( S k ) + Λ X k − 1 ( x k − 1 ) < τ = F Λ w ( τ − Λ X k − 1 ( x k − 1 )) , (3) where F Λ w ( · ) is the c.d.f. of the variable Λ s ( S n ) conditioned to W = w . Using the above results, it can be sho wn that Λ X n +1 ( x n +1 ) − Λ X n ( x n ) = λ ( x k , τ − Λ X n ( x n )) , where λ ( · , · ) is defined as λ ( x, a ) = x log F Λ 1 ( a ) F Λ 0 ( a ) + (1 − x ) log 1 − F Λ 1 ( a ) 1 − F Λ 0 ( a ) . Lev eraging above deriv ations, we de velop Algorithm 1 as a simple iterative procedure for computing Λ X n ( x n ) . Note that the algorithm’ s complexity scales gracefully , as it grows linearly with the length of x n . Moreover , the algorithm does not need any information about potential attack, only requiring knowledge of the signals statistics as gi ven by F Λ w . Algorithm 1 Computation of Λ X n ( x n ) 1: function L O G L I K E L I H O O D ( x n , τ ) 2: L 1 = λ ( x 1 , τ ) . 3: for k = 2 , . . . , n do 4: L k = L k − 1 + λ ( x k +1 , τ − L k − 1 ) . 5: end f or 6: retur n L n 7: end function C. Information cascades as str ength or weakness The term “social learning” refers to the fact that the ac- curacy of X n as a predictor of W grows with n , and hence n c is usually chosen as one of the last nodes in the decision sequence. Howe ver , as the number of shared signals grows the increasing “social pressure” can make the nodes to ignore their individual measurements and blindly follo w the dominant choice [16]. This phenomenon, known as information cascade , introduces sev ere limitations in the achiev able asymptotic performance of social learning [17]. A positiv e effect of information cascades, which has been ov erlooked before, is to make a large number of agents/nodes to hold equally qualified estimator(s), generating many loca- tions where the network operator can collect and aggregate the data. This property avoids the existence of a single point of failure to rob ustly face topology-aware attacks. An attempt to blindly guess n c in order to tamper the n c -node would be inefficient due to the large number of potential candidates. Howe ver , an attacker can also lev erage the information cascade phenomenon. A rational attacking strategy is to tamper the first N ∗ nodes of the decision sequence, setting their signals in order to push the networked decisions towards a misleading cascade ‡ . If N ∗ is large enough an information cascade can be triggered almost surely , making the learning process to fail. Howe ver , if N ∗ is not large enough then the network may undo the initial pool of wrong opinions and end up triggering a correct cascade anyway . This capability of “resilience” is e xplored in the next section. I V . P R O O F O F C O N C E P T T o illustrate the application of social learning against topology-aware data falsification attacks, we consider a net- work of randomly distributed sensors ov er a sensitive area following a Poisson Point process (PPP). The ratio of the area that is within the range of each sensor is denoted by r . If attacks occur uniformly over the surveilled area, then r is also the probability of an attack taking place under the cov erage area of a particular sensor is. It is further assumed that each node is equipped with a binary sensor (i.e. S n ∈ { 0 , 1 } ), whose probability of generating a wrong measurement due to electronic and other imperfections is denoted by q . ‡ Intuitiv ely , it is more likely for a node to follow a misleading cascade if all the pre vious N ∗ nodes hav e been tampered and act homogeneously , than for a node of higher index if the previous decisions are non-homogeneous. 4 For finding the posterior distrib utions of S n , first note that P 0 { S n = 1 } = q , as a sensor false-alarm can only be due to noise. The probability of detecting an ev ent is giv en by P { S n = 1 | W = 1 } = P { attack in range, good measurement | W = 1 } + P { attack out of range, bad measurement | W = 1 } = r + q − 2 r q . Therefore, the sensor miss-detection rate is P 1 { S n = 0 } = 1 − r − q + 2 r q . The signal log-likehood is hence given by Λ S ( S n ) = S n log r + q − 2 r q q +(1 − S n ) log 1 − r − q + 2 r p 1 − q . Note that Λ S (1) > Λ S (0) , which is consequence of r + q − 2 r q > q and q < 1 / 2 . Correspondingly , the c.d.f. of Λ S is F Λ w ( l ) = 0 if l < Λ(0) , P { S n = 0 | W = w } if Λ(0) ≤ l < Λ(1) , 1 if Λ(1) ≥ l . W e studied a network composed by N = 200 sensor nodes, generating X n sequentially following (3) and using Algorithm 1 to compute Λ X n ( X n ) . F ollowing Section III-C, it is assumed that a topology-aware attacker tampered the first N ∗ nodes of the decision sequence and uses them to increase the miss-detection rate by setting X n = 0 for n = 1 , . . . , N ∗ . Finally , in order to fav our the reduction of miss-detections ov er false alarms, τ = 0 is chosen as is the lowest value that still allows a non-trivial inference process.F or each set of parameter v alues, 10 4 simulation runs are performed. Simulations demonstrate that the proposed scheme enables strong network resilience in this scenario, allo wing the sensor network to maintain a low miss-detection rate e ven in the presence of an important number of Byzantine nodes (see Figure 1). In contrast, f a traditional distributed detection scheme is used, a topology-aware attacker can cause a miss- detection rate of 100% by just compromising the few nodes that perform data aggregation, i.e. the FC(s). Figure 1 sho ws that nodes aggregating data by social learning can achie ve an av erage asymptotic miss-detection rate of less than 5% ev en when 30% of the most critical nodes are under the control of the attacker , having some resemblance with the well-known 1/3 threshold of the Byzantine generals problem [5]. Moreov er , Figure 1 also suggest that our scheme can still provide network resilience within the 10% most unfav orable cases. Interestingly , the data aggregation is performed node by node independently of the network size. Hence, in a v ery large network the first 200 nodes would exhibit the same performance as the one shown in Figure 1. Adding more nodes may not introduce significant improv ements to the asymptotic performance, as the asymptotic estimator is copied by later nodes following an information cascade. Nevertheless, in a large network information cascades provide the fundamental benefit of creating a large number of nodes from where the network operator can access aggregated data. The netw ork resilience pro vided by our scheme is influenced by the sensor statistics, which are determined by q and r (see Figure 2). Intuiti vely , the achiev able miss-detection rate under a low number of Byzantine nodes is reduced by a smaller q 1 21 41 61 81 101 121 141 161 181 201 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Sensor node Miss−detection rate N * /N = 0% N * /N = 10% N * /N = 30% N * /N = 50% 1 21 41 61 81 101 121 141 161 181 201 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Sensor node Miss−detection rate N * /N = 0% N * /N = 10% N * /N = 30% N * /N = 50% Fig. 1: Above: Performance of a surveillance netw ork based on social learning, with binary signals of range r = 5% and error rate q = 10 − 4 , when N ∗ out of N nodes are compromised by an attacker . Bellow: Performance considering the 10% most unfavorable cases. 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Attack intensity (N * /N) Miss−detection rate r=5%, q=10 −4 r=5%, q=10 −3 r=2%, q=10 −4 Fig. 2: Asymptotic average performance of a surveillance system. A smaller sensor error rate ( q ) or large sensing range ( r ) impro ves the performance under a low N ∗ , but the latter also makes the performance degradation less graceful when N ∗ grows. or larger r . Furthermore, our numerical results suggest that the number of Byzantine nodes affects the miss-detection rate exponentially with a rate of growth inv ersely proportional to r , as nodes with smaller r trust each others decisions less and hence are less affected by “social pressure”. Consequently , it is desirable to deploy sensors with smaller probability of malfunction ( q ) than lar ger cov erage ( r ), as a larger coverage makes the network more vulnerable to Byzantine nodes and subsequent misleading information cascades. Our scheme does not require knowledge about attack statis- tics, being well-suited for practical scenarios as operation in large scale or mobile scenarios suggest dynamically changing topology . Moreover , simulations sho w that if the adversary tamper not the initial nodes but a dif ferent set of the same cardinality , then the attack has less impact ov er the system performance. This suggests that our scheme can provide fur- ther resilience against attackers who are not topology-aw are. 5 R E F E R E N C E S [1] V . V . V eerav alli and P . K. V arshney , “Distributed inference in wireless sensor networks, ” Philosophical T ransactions of the Royal Society of London A: Mathematical, Physical and Engineering Sciences , vol. 370, no. 1958, pp. 100–117, 2012. [2] S. Barbarossa, S. Sardellitti, and P . D. Lorenzo, Distributed Detection and Estimation in W ireless Sensor Networks . Academic Press Library in Signal Processing, V ol. 2, Communications and Radar Signal Processing, Oct. 2013, vol. 2, pp. 329–408. [3] E. Shi and A. Perrig, “Designing secure sensor networks, ” IEEE W ireless Communications , vol. 11, no. 6, pp. 38–43, 2004. [4] S. Marano, V . Matta, and L. T ong, “Distributed detection in the presence of byzantine attacks, ” IEEE T ransactions on Signal Pr ocessing , vol. 57, no. 1, pp. 16–29, 2009. [5] L. Lamport, R. Shostak, and M. Pease, “The byzantine generals prob- lem, ” ACM T ransactions on Pr ogramming Languages and Systems (TOPLAS) , vol. 4, no. 3, pp. 382–401, 1982. [6] A. V empaty , L. T ong, and P . K. V arshne y , “Distributed inference with byzantine data: State-of-the-art re view on data falsification attacks, ” IEEE Signal Processing Ma gazine , v ol. 30, no. 5, pp. 65–75, 2013. [7] V . S. S. Nadendla, Y . S. Han, and P . K. V arshney , “Distributed inference with m-ary quantized data in the presence of byzantine attacks, ” IEEE T ransactions on Signal Pr ocessing , vol. 62, no. 10, pp. 2681–2695, May 2014. [8] J. Zhang, R. S. Blum, X. Lu, and D. Conus, “ Asymptotically optimum distributed estimation in the presence of attacks, ” IEEE T ransactions on Signal Pr ocessing , vol. 63, no. 5, pp. 1086–1101, March 2015. [9] B. Kailkhura, Y . S. Han, S. Brahma, and P . K. V arshney , “Distributed bayesian detection in the presence of byzantine data, ” IEEE T ransactions on Signal Processing , v ol. 63, no. 19, pp. 5250–5263, Oct 2015. [10] B. Parno, A. Perrig, and V . Gligor, “Distributed detection of node replication attacks in sensor networks, ” in 2005 IEEE Symposium on Security and Privacy (S&P’05) . IEEE, 2005, pp. 49–63. [11] R. Castro, M. Coates, G. Liang, R. Nowak, and B. Y u, “Network tomography: recent developments, ” Statistical science , pp. 499–517, 2004. [12] J. Tsitsiklis and M. Athans, “On the comple xity of decentralized decision making and detection problems, ” IEEE Tr ansactions on Automatic Contr ol , vol. 30, no. 5, pp. 440–446, 1985. [13] J. N. Tsitsiklis et al. , “Decentralized detection, ” Advances in Statistical Signal Pr ocessing , vol. 2, no. 2, pp. 297–344, 1993. [14] D. W arren and P . W illett, “Optimum quantization for detector fusion: some proofs, examples, and pathology , ” Journal of the F ranklin Institute , vol. 336, no. 2, pp. 323–359, 1999. [15] J.-F . Chamberland and V . V . V eerav alli, “ Asymptotic results for decen- tralized detection in power constrained wireless sensor networks, ” IEEE Journal on selected ar eas in communications , v ol. 22, no. 6, pp. 1007– 1015, 2004. [16] S. Bikhchandani, D. Hirshleifer, and I. W elch, “ A theory of f ads, fashion, custom, and cultural change as informational cascades, ” Journal of political Economy , pp. 992–1026, 1992. [17] D. Acemoglu, M. A. Dahleh, I. Lobel, and A. Ozdaglar, “Bayesian learning in social networks, ” The Review of Economic Studies , vol. 78, no. 4, pp. 1201–1236, 2011. [18] V . Krishnamurthy and H. V . Poor , “Social learning and bayesian games in multiagent signal processing: How do local and global decision makers interact?” IEEE Signal Pr ocessing Magazine , vol. 30, no. 3, pp. 43–57, 2013. [19] R. V iswanathan, S. C. Thomopoulos, and R. T umuluri, “Optimal se- rial distributed decision fusion, ” IEEE T ransactions on Aerospace and Electr onic Systems , vol. 24, no. 4, pp. 366–376, 1988. [20] J. D. Papasta vrou and M. Athans, “Distributed detection by a lar ge team of sensors in tandem, ” IEEE T ransactions on Aerospace and Electr onic Systems , vol. 28, no. 3, pp. 639–653, 1992. [21] P . F . Swaszek, “On the performance of serial networks in distributed detection, ” IEEE transactions on aer ospace and electr onic systems , vol. 29, no. 1, pp. 254–260, 1993. [22] R. V iswanathan and P . K. V arshney , “Distributed detection with multiple sensors i. fundamentals, ” Proceedings of the IEEE , v ol. 85, no. 1, pp. 54–63, 1997. [23] I. Bahceci, G. Al-Regib, and Y . Altunbasak, “Serial distributed detection for wireless sensor networks, ” in Information Theory , 2005. ISIT 2005. Pr oceedings. International Symposium on . IEEE, 2005, pp. 830–834. [24] A. Bertrand, “ Applications and trends in wireless acoustic sensor net- works: A signal processing perspectiv e, ” in 2011 18th IEEE Symposium on Communications and V ehicular T echnology in the Benelux (SCVT) , Nov 2011, pp. 1–6. [25] M. Loe ve, Probability Theory I . Springer, 1978. [26] R. Rajagopalan and P . K. V arshney , “Data-aggregation techniques in sensor networks: A survey , ” IEEE Communications Surveys T utorials , vol. 8, no. 4, pp. 48–63, Fourth 2006. [27] H. V . Poor , An introduction to signal detection and estimation . Springer Science & Business Media, 2013.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment