Most Websites Dont Need to Vibrate: A Cost-Benefit Approach to Improving Browser Security
Modern web browsers have accrued an incredibly broad set of features since being invented for hypermedia dissemination in 1990. Many of these features benefit users by enabling new types of web applications. However, some features also bring risk to users’ privacy and security, whether through implementation error, unexpected composition, or unintended use. Currently there is no general methodology for weighing these costs and benefits. Restricting access to only the features which are necessary for delivering desired functionality on a given website would allow users to enforce the principle of lease privilege on use of the myriad APIs present in the modern web browser. However, security benefits gained by increasing restrictions must be balanced against the risk of breaking existing websites. This work addresses this problem with a methodology for weighing the costs and benefits of giving websites default access to each browser feature. We model the benefit as the number of websites that require the feature for some user-visible benefit, and the cost as the number of CVEs, lines of code, and academic attacks related to the functionality. We then apply this methodology to 74 Web API standards implemented in modern browsers. We find that allowing websites default access to large parts of the Web API poses significant security and privacy risks, with little corresponding benefit. We also introduce a configurable browser extension that allows users to selectively restrict access to low-benefit, high-risk features on a per site basis. We evaluated our extension with two hardened browser configurations, and found that blocking 15 of the 74 standards avoids 52.0% of code paths related to previous CVEs, and 50.0% of implementation code identified by our metric, without affecting the functionality of 94.7% of measured websites.
💡 Research Summary
The paper presents a systematic cost‑benefit methodology for evaluating the security impact of individual Web API standards in modern browsers and proposes a practical mechanism for selectively disabling high‑risk, low‑benefit features. The authors begin by observing that contemporary browsers expose a large and ever‑growing set of JavaScript APIs—ranging from media synthesis to hardware sensors—yet the security model has not kept pace, leaving every site with near‑universal access to potentially dangerous functionality. To address the lack of a quantitative framework, the authors define “benefit” as the number of websites that require a given feature to deliver a user‑visible function, and “cost” as a composite metric comprising (1) the count of CVEs historically associated with the feature, (2) the number of academic attacks that rely on the feature, and (3) the amount of browser source code (measured in lines of C++ code) dedicated exclusively to implementing the feature.
Using this three‑dimensional cost model, the authors analyze 74 Web API standards implemented in Firefox and Chrome. Benefit is measured through a large‑scale human study: two independent evaluators performed 1,684 paired tests across a diverse set of sites, determining whether disabling a particular feature broke the site’s core functionality. The evaluators achieved 97 % agreement, providing a reliable estimate of each feature’s necessity in everyday browsing.
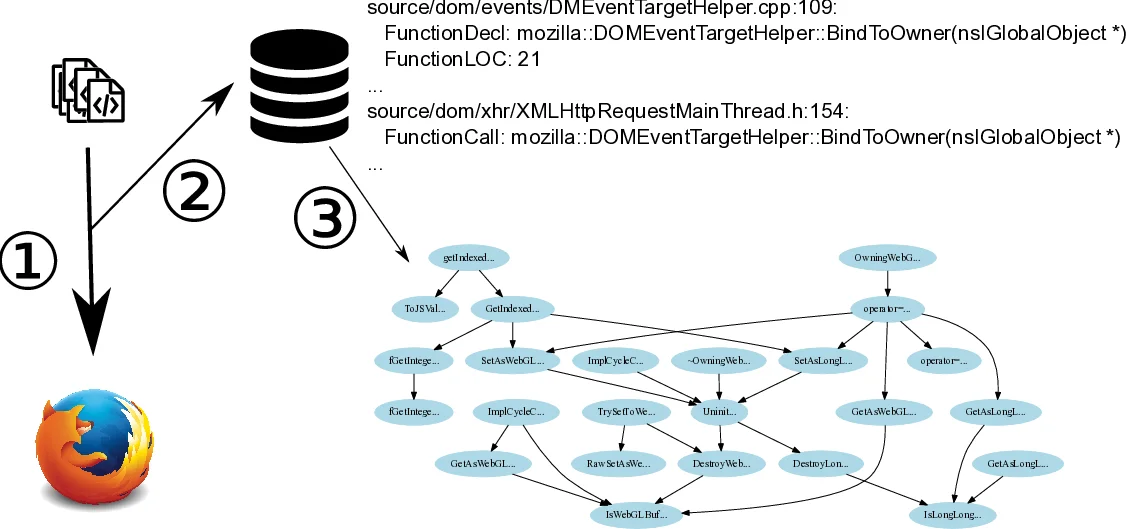
Cost is quantified by mining the National Vulnerability Database for CVE entries per feature, cataloguing attacks described in peer‑reviewed papers, and performing static analysis on the Firefox codebase to count lines of code that are exclusively used for each standard. The authors find a statistically significant correlation between code size and historical vulnerability count, supporting the premise that larger, more complex implementations are more error‑prone.
Armed with these measurements, the authors identify 15 standards that exhibit high cost and low benefit (e.g., Vibration API, Ambient Light Sensor, Battery API, WebGL, certain cryptographic primitives). To enforce selective blocking, they develop a browser extension that leverages the ES6 Proxy object. The proxy intercepts all property accesses, method calls, and other operations on the global window object. For blocked features, the proxy returns safe “no‑op” values (empty functions, zero, empty strings, or undefined) that satisfy the expectations of most JavaScript code without invoking the underlying browser capability. This approach avoids the “all‑or‑nothing” behavior of tools like NoScript and prevents runtime errors that would otherwise arise from simply deleting properties.
The extension ships with two pre‑defined policies—conservative and aggressive—corresponding to different subsets of blocked standards. The authors evaluate the extension on the Alexa top‑200 sites and a random sample of the remaining Alexa‑10k sites. Blocking the 15 high‑cost standards eliminates 52 % of code paths associated with previously reported CVEs and reduces the amount of implementation code by 50 %, while preserving functional correctness on 94.7 % of the tested sites. Compared against NoScript and the Tor Browser Bundle (which also disables certain APIs), the proposed solution offers comparable or greater security gains with far fewer site breakages.
Key contributions include: (1) a novel cost‑benefit framework that combines vulnerability history, academic attack mapping, and implementation complexity; (2) a human‑driven methodology for measuring feature necessity; (3) an ES6 Proxy‑based “feature firewall” that can disable APIs without breaking typical JavaScript code; (4) an open‑source, highly configurable extension that allows users to tailor policies per site and adapt to future API changes.
The paper concludes by emphasizing that applying the principle of least privilege at the API level is both feasible and effective. It suggests future work on extending the methodology to mobile browsers, integrating dynamic, machine‑learning‑based policy generation, and continuously updating cost metrics as new standards emerge. Overall, the study demonstrates that a disciplined, data‑driven approach to browser feature management can substantially reduce the attack surface while maintaining a smooth user experience.
Comments & Academic Discussion
Loading comments...
Leave a Comment