CLIMEX: A Wireless Physical Layer Security Protocol Based on Clocked Impulse Exchanges
A novel method and protocol establishing common secrecy based on physical parameters between two users is proposed. The four physical parameters of users are their clock frequencies, their relative clock phases and the distance between them. The protocol proposed between two users is backed by theoretical model for the measurements. Further, estimators are proposed to estimate secret physical parameters. Physically exchanged parameters are shown to be secure by virtue of their non-observability to adversaries. Under a simplified analysis based on a testbed settings, it is shown that 38 bits of common secrecy can be derived for one run of the proposed protocol among users. The method proposed is also robust against various kinds of active timing attacks and active impersonating adversaries.
💡 Research Summary
The paper introduces CLIMEX (Clocked Impulse EXchange), a wireless physical‑layer protocol that enables two devices to share secret information derived from their intrinsic physical parameters: the individual clock frequencies, the relative clock phase, and the inter‑node distance. Unlike conventional physical‑layer key generation schemes that rely on the randomness of the wireless channel (e.g., RSS, channel state information), CLIMEX exploits the deterministic yet device‑specific characteristics of crystal oscillators and propagation delay, making it robust even in static or low‑entropy channel conditions.
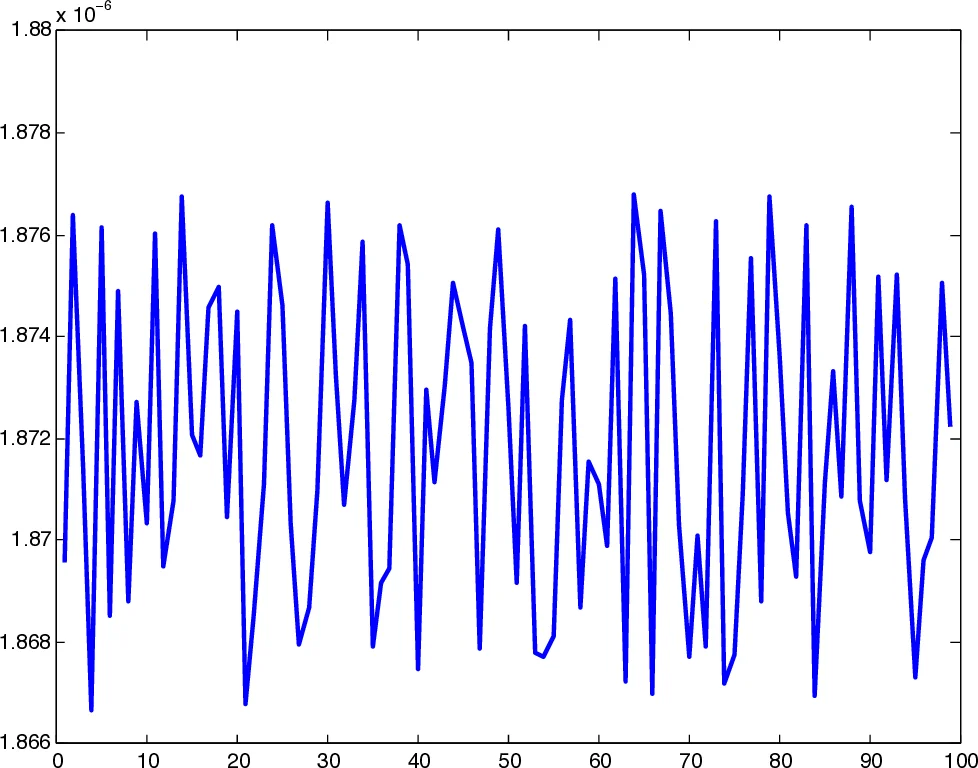
The protocol builds on a classic round‑trip‑time (RTT) measurement. In a standard RTT exchange, Alice sends a PING at regular intervals defined by her clock, Bob replies after a fixed delay, and Alice records the round‑trip time. CLIMEX modifies this exchange in two crucial ways. First, Alice adds a secret random offset Δ₁ to each PING transmission relative to her clock edge; only Alice knows these offsets. Second, Bob does not use a constant reply delay; instead he applies a scaled delay (\bar{\delta}_B) that depends on his own clock period and the frequency difference (f_d = f_A - f_B). These modifications introduce non‑linear, piecewise‑linear (sawtooth) behavior into the measured RTT series.
Mathematically, the measurement vector observed by Alice can be expressed as
\
Comments & Academic Discussion
Loading comments...
Leave a Comment