An optimization technique on pseudorandom generators based on chaotic iterations
Internet communication systems involving cryptography and data hiding often require billions of random numbers. In addition to the speed of the algorithm, the quality of the pseudo-random number generator and the ease of its implementation are common practical aspects. In this work we will discuss how to improve the quality of random numbers independently from their generation algorithm. We propose an additional implementation technique in order to take advantage of some chaotic properties. The statistical quality of our solution stems from some well-defined discrete chaotic iterations that satisfy the reputed Devaney’s definition of chaos, namely the chaotic iterations technique. Pursuing recent researches published in the previous International Conference on Evolving Internet (Internet 09, 10, and 11), three methods to build pseudorandom generators by using chaotic iterations are recalled. Using standard criteria named NIST and DieHARD (some famous batteries of tests), we will show that the proposed technique can improve the statistical properties of a large variety of defective pseudorandom generators, and that the issues raised by statistical tests decrease when the power of chaotic iterations increase.
💡 Research Summary
The paper addresses the pressing need for high‑quality, high‑throughput pseudo‑random number generators (PRNGs) in Internet security and data‑hiding applications. Recognizing that existing generators are either fast but insecure or secure but slow, the authors propose a generic post‑processing technique based on chaotic iterations (CI) that can be applied to any underlying PRNG to improve its statistical properties without sacrificing speed.
Chaotic iterations are defined on the binary vector space B^N. A deterministic iteration function f (typically the vectorial Boolean negation) is applied only to a single component selected by a “strategy” sequence S. The strategy itself is derived from the outputs of two auxiliary PRNGs (denoted PRNG1 and PRNG2). This selective, non‑linear updating satisfies Devaney’s definition of topological chaos, guaranteeing sensitive dependence on initial conditions and dense periodic points, which in turn injects strong non‑linearity into the output stream.
Three concrete CI‑based PRNG families are described:
-
Old CIPRNG – Uses a 4‑bit internal state. PRNG2 supplies the component index (S_n = PRNG2() mod 4) while PRNG1 determines how many iterations are performed before an output is taken (m = PRNG1() mod 2 + 13). Only the selected bit is negated each iteration; after m iterations the entire 4‑bit state is emitted. This design is simple, requires minimal overhead, and already yields substantial statistical improvement.
-
New CIPRNG – Extends the state to 32 bits and introduces an irregular decimation of the strategy sequence. PRNG2’s output is reduced modulo N to obtain S_n, and a flag array d_i prevents reuse of the same index within a round. PRNG1 computes a variable iteration count m = f(PRNG1()) that controls the number of updates per output. The richer state space and more diverse strategy dramatically enhance randomness, at the cost of modestly increased computation.
-
Xor CIPRNG – Updates a whole subset of bits simultaneously by XOR‑ing the current state with a mask S_n generated by PRNG2 (x_n = x_{n‑1} ⊕ S_n). This parallelizable scheme is especially suited for GPU implementation, achieving about 20 GSamples/s. While its raw statistical quality is slightly lower than the other two families, applying multiple functional powers (repeating the iteration function) restores full compliance with stringent test suites.
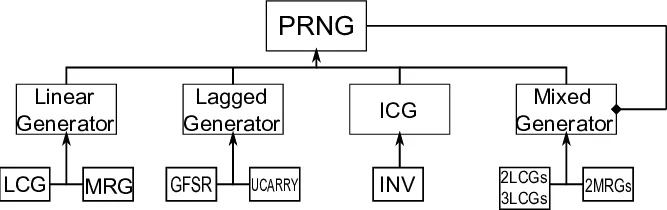
The authors evaluate the three CI families on a broad spectrum of well‑known PRNGs, grouped into four classes: linear generators (LCG, MLCG), lagged generators, invertible (carry‑based) generators, and mixed generators (GFSR, etc.). For each base generator they construct three CI configurations: single (both PRNG1 and PRNG2 belong to the same class), mixed (different classes combined), and multiple (repeated functional composition).
Statistical assessment employs the NIST SP 800‑22 suite (15 tests) and the DieHARD battery (18 tests). Each experiment generates 100 sequences of 1 M‑bit length, computes p‑values, and checks uniformity (p‑value_T > 0.0001) and extreme tails (p > 0.9999). Results, summarized in tables, show that:
- Almost all defective base generators fail several NIST/DieHARD tests when used alone.
- Applying the Old or New CIPRNG transforms the same generators into fully compliant ones; the New variant consistently yields the highest pass rates.
- Xor CIPRNG, even in its basic form, improves the statistical profile of every base generator; with multiple functional powers it also passes the entire NIST suite.
- Mixed and multiple CI configurations further reinforce robustness, indicating that the chaotic iteration layer effectively masks structural weaknesses of the underlying PRNGs.
The paper concludes that chaotic iterations provide a powerful, algorithm‑agnostic “chaos‑filter” that injects non‑linearity and diffusion into PRNG outputs. By tuning the strategy generation, iteration count, and functional power, designers can balance throughput and randomness quality to meet application‑specific requirements. Future work is outlined: hardware implementation (FPGA/ASIC), deeper cryptographic security analysis (predictability, state recovery), and exploration of more sophisticated strategy sources (e.g., cryptographic hash‑based). Overall, the study demonstrates that a mathematically grounded chaotic post‑processing step can elevate a wide range of existing PRNGs to meet modern security standards while preserving high generation speeds.
Comments & Academic Discussion
Loading comments...
Leave a Comment