Contagion dynamics of extremist propaganda in social networks
Recent terrorist attacks carried out on behalf of ISIS on American and European soil by lone wolf attackers or sleeper cells remind us of the importance of understanding the dynamics of radicalization mediated by social media communication channels. In this paper, we shed light on the social media activity of a group of twenty-five thousand users whose association with ISIS online radical propaganda has been manually verified. By using a computational tool known as dynamical activity-connectivity maps, based on network and temporal activity patterns, we investigate the dynamics of social influence within ISIS supporters. We finally quantify the effectiveness of ISIS propaganda by determining the adoption of extremist content in the general population and draw a parallel between radical propaganda and epidemics spreading, highlighting that information broadcasters and influential ISIS supporters generate highly-infectious cascades of information contagion. Our findings will help generate effective countermeasures to combat the group and other forms of online extremism.
💡 Research Summary
The paper investigates how extremist propaganda, specifically that of the Islamic State (ISIS), spreads on the social media platform Twitter. Unlike many prior studies that rely on keyword‑based data collection, the authors start from a manually verified list of 25,538 ISIS‑supporting accounts compiled by the “Lucky Troll Club” crowdsourcing effort. These accounts were confirmed by Twitter’s anti‑abuse team and subsequently suspended between March and June 2015. Using the Observatory on Social Media (OSoMe) data stream—approximately a 10 % random sample of the full Twitter firehose—the researchers retrieved every tweet, retweet, and mention involving these accounts from January 2014 through June 2015, yielding a corpus of 3,395,901 tweets. About 1.2 million tweets originated directly from the ISIS accounts, while the remaining 2.2 million were generated by 54,358 distinct external users who retweeted or mentioned the extremist accounts.
Because more than 92 % of the content is in Arabic, the authors deliberately avoid language‑dependent analyses (e.g., sentiment or topic modeling) and instead focus on language‑agnostic network and temporal metrics. They first characterize basic account statistics at the moment of suspension: the follower distribution follows a classic long‑tail (mean ≈ 516, median = 130), indicating that most accounts have modest reach, yet a non‑trivial minority possess several hundred or even thousands of followers. The follow‑ee (friends) distribution, however, shows an unexpected upward trend between 100 and 1,000 connections, suggesting coordinated “follow‑back” schemes designed to artificially inflate visibility.
Activity distributions for tweets and retweets also exhibit power‑law behavior, confirming that a small core of highly active users generates a disproportionate share of the content. Approximately 1 % of the ISIS accounts posted at least 30 tweets during the observation window, and a handful posted thousands, hinting at the possible use of automated bots to amplify output. Weekly time‑series analysis reveals a gradual buildup of activity from early 2014 until March 2015, after which tweet volume spikes dramatically—reaching over 100,000 tweets per week—coinciding with the period of massive account suspensions (notably a surge of >10,000 suspensions on April 2, 2015). Following the suspensions, activity declines sharply, confirming the impact of platform‑level enforcement.
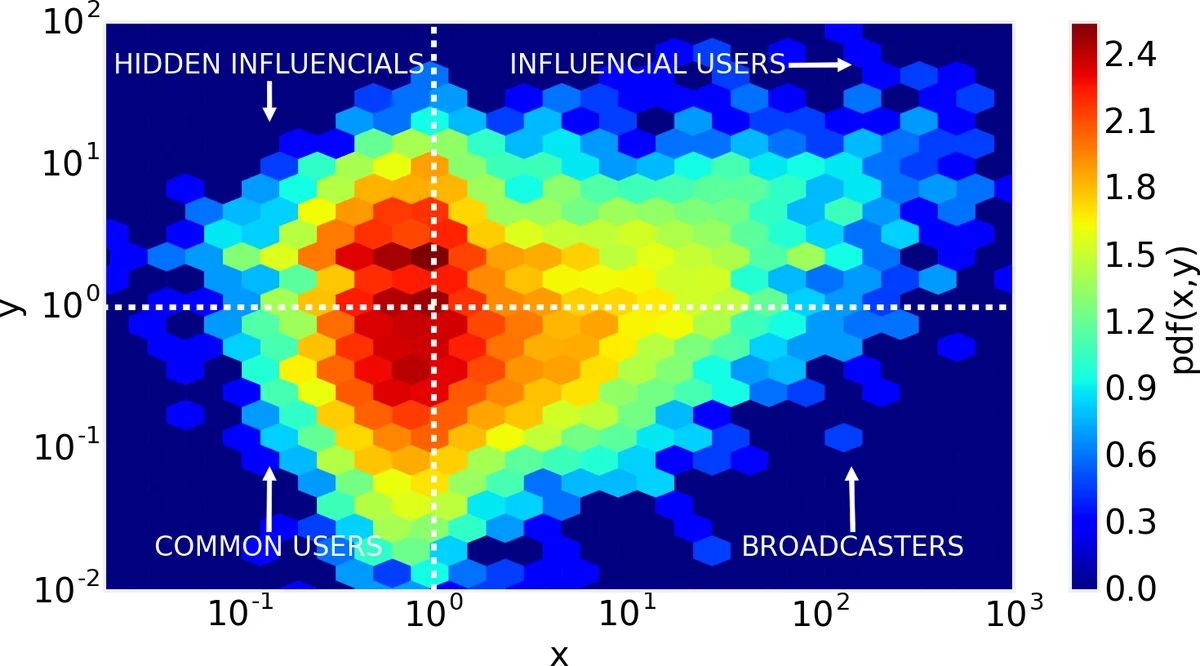
To uncover the dynamics of influence within the extremist network, the authors employ Dynamic Activity‑Connectivity Maps (DACM). Each account is plotted on a two‑dimensional plane defined by “activity” (tweets/retweets per unit time) and “connectivity” (followers, follow‑ees, and interaction frequency). The DACM reveals a distinct cluster of high‑activity, high‑connectivity nodes that act as “super‑spreaders.” These nodes are responsible for generating highly infectious cascades: when they post, the content rapidly propagates through retweets and mentions, forming infection chains analogous to epidemiological models. The authors quantify these cascades by treating each tweet as an infection event and measuring the size and depth of the resulting retweet trees. The resulting diffusion curves follow an S‑shaped trajectory typical of epidemic spread, with a rapid acceleration phase aligning with the March‑May 2015 activity surge.
Methodologically, the study contributes two best‑practice recommendations: (1) begin data collection from a manually verified list of extremist actors rather than relying solely on keyword filters, thereby reducing sampling bias; and (2) leverage large‑scale streaming data sources (e.g., OSoMe) when available, as they provide a more representative snapshot of platform activity than the limited public API.
The findings have clear policy implications. First, the identification of a small set of high‑influence accounts suggests that early detection and targeted suspension of these “super‑spreaders” could dramatically curtail the reach of extremist propaganda. Second, the observed pattern of reciprocal following indicates coordinated network manipulation; monitoring such anomalous follow‑back behavior could serve as an early warning signal for organized propaganda campaigns. Finally, the epidemic‑style diffusion analysis demonstrates that extremist content behaves similarly to contagious diseases, implying that public‑health‑style intervention frameworks (e.g., “vaccination” through counter‑narratives, “contact tracing” of retweet cascades) may be effective when adapted to the online information environment.
Overall, the paper provides a rigorous, data‑driven portrait of ISIS’s online propaganda machinery, highlights the pivotal role of a few highly active and well‑connected accounts, and offers actionable insights for researchers, platform operators, and policymakers seeking to mitigate the spread of extremist content on social media.
Comments & Academic Discussion
Loading comments...
Leave a Comment