SD-CPS: Taming the Challenges of Cyber-Physical Systems with a Software-Defined Approach
Cyber-Physical Systems (CPS) revolutionize various application domains with integration and interoperability of networking, computing systems, and mechanical devices. Due to its scale and variety, CPS faces a number of challenges and opens up a few research questions in terms of management, fault-tolerance, and scalability. We propose a software-defined approach inspired by Software-Defined Networking (SDN), to address the challenges for a wider CPS adoption. We thus design a middleware architecture for the correct and resilient operation of CPS, to manage and coordinate the interacting devices centrally in the cyberspace whilst not sacrificing the functionality and performance benefits inherent to a distributed execution.
💡 Research Summary
The paper addresses the growing complexity of Cyber‑Physical Systems (CPS) by introducing a software‑defined approach called SD‑CPS, which adapts concepts from Software‑Defined Networking (SDN) to the CPS domain. The authors first clarify the distinction between the Internet of Things (IoT) and CPS, emphasizing that CPS requires tighter integration of physical devices and cyber control while demanding higher security, privacy, and management guarantees. They argue that SDN’s separation of the control plane from the data plane, together with its global network view, offers a promising foundation for tackling CPS challenges such as unpredictable execution environments, coordination overhead, security, fault tolerance, large‑scale decision making, and orchestration of intelligent agents.
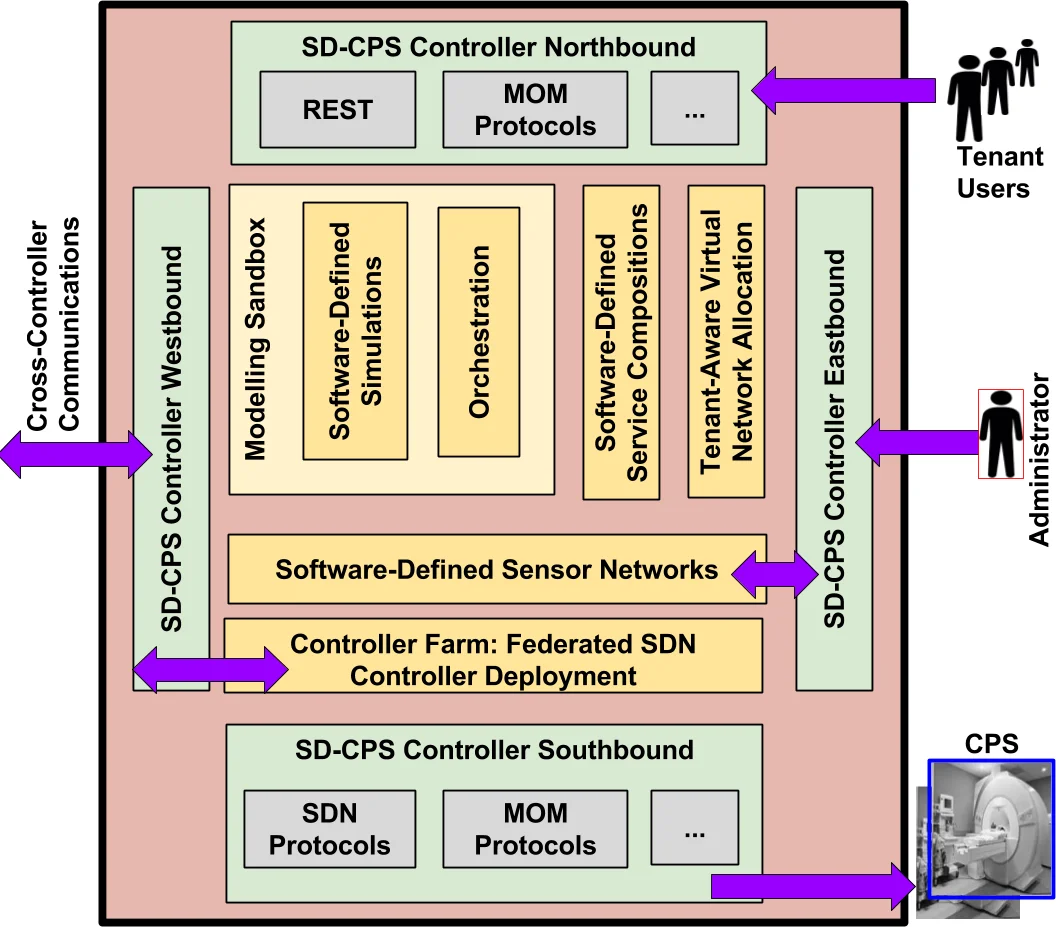
SD‑CPS is built around a centrally deployed “cyber” controller that is, in fact, a federated farm of multiple SDN controllers. This controller farm provides multi‑tenant isolation, protected access to internal data stores, and a unified view of the entire CPS network. Four families of APIs are defined:
- Northbound API – uses REST and message‑oriented middleware (AMQP, MQTT) to expose high‑level intents from tenant applications, allowing policy‑driven management of devices.
- Southbound API – combines OpenFlow with lightweight MOM protocols to communicate with both SDN‑compatible switches and legacy or non‑OpenFlow physical devices (sensors, actuators).
- Westbound API – enables inter‑controller communication across domains, supporting federated control without sacrificing tenant isolation.
- Eastbound API – provides administrators with the ability to configure and manage the controller farm itself, effectively turning the controller into a “software‑defined sensor network.”
Two architectural pillars are introduced: Software‑Defined Service Composition and Modeling Sandbox. Service composition breaks CPS workloads into micro‑services that can be executed in parallel on the controller farm or on device firmware, leveraging real‑time network telemetry to select optimal execution paths. When congestion or failures are detected, the controller creates sub‑flows, clones traffic, and recomposes it at intermediate or final nodes, thereby providing path redundancy and load balancing. The Modeling Sandbox implements a cyber‑twin concept: physical devices are represented virtually, allowing simulations, emulations, and eventual physical deployment to share the same control logic. This reduces design‑validation cycles and mitigates the unpredictability of real‑world execution.
Security is treated as a first‑class concern. By centralizing control, SD‑CPS reduces the attack surface and can enforce policy‑based QoS and isolation across tenants. Existing SDN security mechanisms are reused, while additional authentication and authorization extensions are added to the southbound interface to protect interactions with heterogeneous CPS devices.
A prototype implementation uses OpenDaylight Beryllium as the core SDN controller, Java 1.8 for the middleware logic, and ActiveMQ for MOM communication. Experiments demonstrate that the controller farm scales horizontally, that service composition reduces end‑to‑end latency, and that flow cloning maintains data delivery under simulated link failures.
In summary, SD‑CPS offers a unified, software‑defined middleware that addresses CPS’s core challenges—management, scalability, resilience, and security—while preserving compatibility with existing CPS deployments. The authors suggest future work on richer policy engines, AI‑driven automatic optimization, and real‑time threat detection to further broaden the applicability of the SD‑CPS paradigm.
Comments & Academic Discussion
Loading comments...
Leave a Comment