Secure Hop-by-Hop Aggregation of End-to-End Concealed Data in Wireless Sensor Networks
In-network data aggregation is an essential technique in mission critical wireless sensor networks (WSNs) for achieving effective transmission and hence better power conservation. Common security protocols for aggregated WSNs are either hop-by-hop or…
Authors: Esam Mlaih, Salah A. Aly
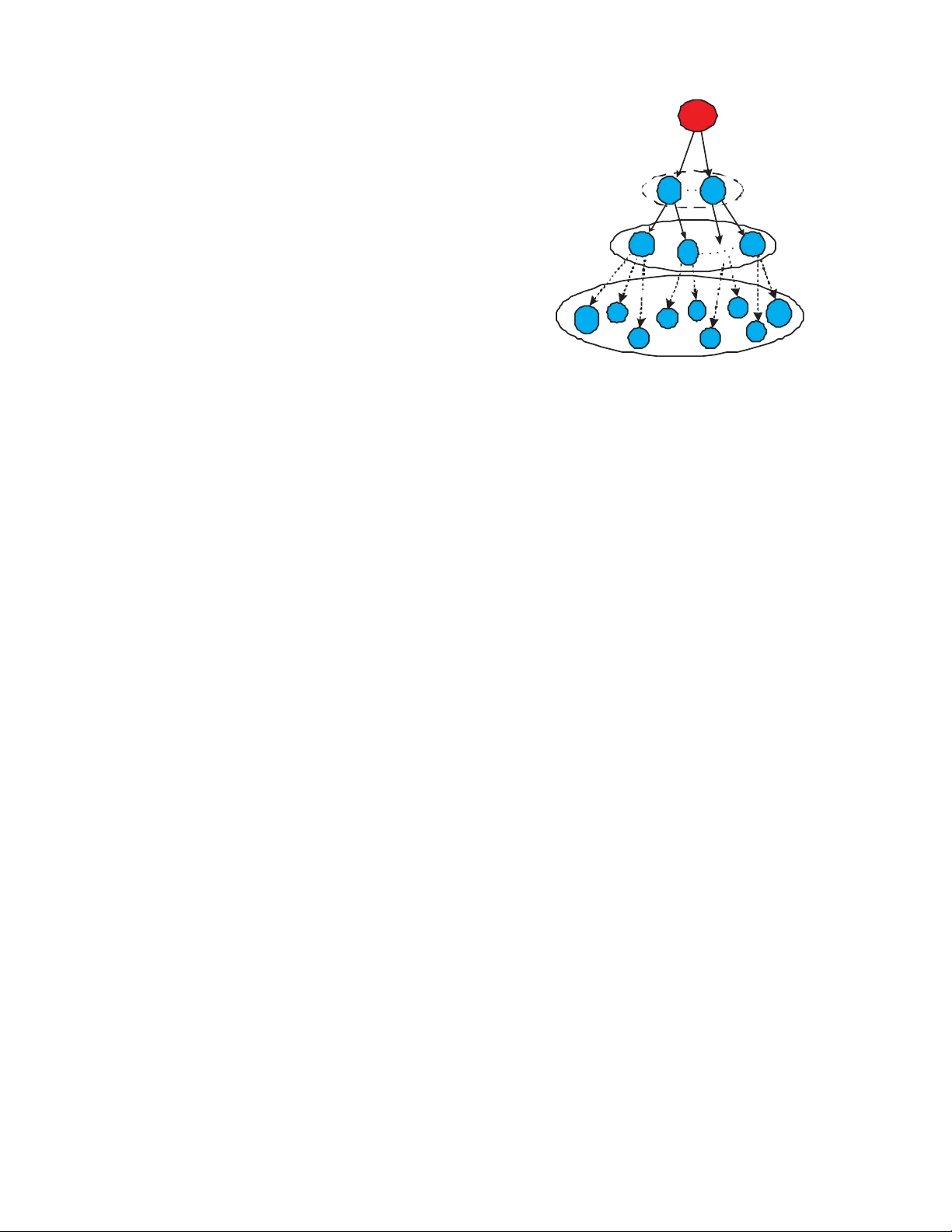
Secure Hop-by-Hop Aggre gation of End-to-End Concealed Data in W ireless Sensor Netw orks Esam Mlaih Departmen t of Com puter Scien ce T exas A&M University , TX 7 7843 , USA Email: mlaih@tamu.e du Salah A. Aly Departmen t of Com puter Scien ce T exas A&M University , TX 7 7843 , USA Email: salah@cs.tamu.ed u Abstract —In-network data aggregation is an essential tech- nique in mission critical wireless sensor networks (WSNs) for achieving effectiv e transmission and hence better po wer conser va- tion. Common security protoco ls fo r aggrega ted WSNs are eith er hop-by-hop or end-to-end, each of which h as its own encryption schemes considering different security primitives . En d-to-end encrypted data aggregation protocols introduce maximum data secrecy with in-effi cient data aggreg ation an d more vul nerability to activ e attacks, while hop -by-hop data aggregation protocols introduce maximum data integrity with efficient data aggrega tion and more vulnerabilit y to passive attacks. In this paper , we propose a secure aggrega tion protocol fo r aggr egated WSNs deployed in hostile en vironments in which dual attack modes are present. Our proposed protoco l is a blend of fl exible data agg regation as in hop-by-hop pro tocols and optimal d ata confidentiality as in end-to-end protocols. Our protocol introduces an efficient O (1) heuristic f or checking data integrity along with cost-effective heuristic-based divide and conquer attestation p rocess which is O (ln n ) in av erage - O ( n ) in the worst scenario- for fu rther verification of aggr egated results. I . I N T R O D U C T I O N A wireless senso r network is usually a collectio n of hun- dreds or thousands of resource-con strained devices with small memories, low ban dwidth an d limited power resources. They are d eployed in fields w here per sistent h uman mon itoring and surveillance are either imp ossible or infeasible . These small detectors can be used to sense e vents r anging from simple readings (e.g. sensing roo m temp erature) to m ore im portant and sensitiv e measures (e .g. intr uder d etection in militar y applications, detecting wildfire or signs of any catastrophic pheno mena). Raw data co llected u sing these limited sensor s are usually queried b y a m ore powerful device called base station (BS) -which may be far away from sensing fields- for further analysis and event-based reaction s [16]. Since wireless sensor n etworks are energy con strained and bandwidth limited , reduc ing com munication s betwee n sensors and base s tations has a significant ef fect on po wer conserv ation and b andwidth u tilization [7 ]. Agg regated sensor networks serve this purpose by introd ucing designated nodes called aggregators that provide efficient data collectio n an d tr ansmis- sion. An ag gregator can sense its own data while agg regating received results from childre n nodes, which in turn may be leaf sensors o r ag gregators as well. Aggregated wireless sensor n etworks pr ovide better power conservation and efficient use of communicatio n c hannels but introdu ce ad ditional security concerns. A passive adversary may capture sensitive results of aggregated data that represents a large partition of th e aggregated WSN if the ke y of the r oot aggregator o f that partition is comprom ised. On the other hand, an ac ti ve ad versary can forge a ggregated data of a partitio n b y compro mising the pare nt n ode of that p artition. M any secur ity protoco ls for ag gregated WSNs we re in troduced to solve these security problem s. These secu rity protocols can be classified accordin g to their under lying encryp tion schemes into e nd-to- end and hop-b y-hop secure data ag gregation protoco ls. The pap er is organized as follows. In Section II, we presen t previous work on secure ag gregation on WSNs and we define our pro blem. In Section I II, we pr esent our network model and its design g oals, along with attacker mo del. In Section s IV and V, we demon strate our security pr otocol and provid e anal- ysis o f its complexity . The paper is conclu ded in Section VIII. I I . R E L AT E D W O R K In this section, we g iv e a short backgroun d on previous work of secu re agg regation pro tocols in WSNs, which are classified as en d-to-e nd and hop-b y-hop . In end-to -end enc ryption schemes [1] , [4], [10 ], [1 5], in- termediate agg regators apply some ag gregation fu nctions on encryp ted data wh ich th ey can’t decr ypt. Th is is becau se these intermediate aggregators d on’t have access to th e keys that are on ly shar ed between data orig inators (usu ally leaf sensor nodes) an d the BS. In CD A [4] sensor no des share a comm on symmetric key with the BS that is kept h idden fro m middle- way aggr egators. I n [1 ] ea ch leaf sensor share a distinct long- term key with the BS. T his key is or iginally deriv ed from the master secret only kn own to the BS. These p rotocols show t hat aggregation of end-to -end encry pted data is possible through using add itiv e Pr i vacy Homomorp hism (PH) a s th e un derlyin g encryp tion sch eme. Althou gh these proto cols are supp osed to provide maximu m data secrecy acro ss the path s between leaf sensor nodes and their sink, overall secrecy resilience of a WSN becom es in dang er if an adversary g ains a ccess to the master key in [1], or comp romises only a sin gle leaf sen sor node in CDA to acquir e the com mon symmetric key shared between all leaf nod es. In [10], [15] pub lic key encryption based on elliptic curves is used to conceal transient data from leaf sensor s to the BS. These schem es e nhance secre cy resilience of WSNs against 2 individual sensor attacks, since compromising a sing le or a set o f senso r no des won’t reveal the decr yption key that only the BS k nows. An attracting featu re o f [1 0] is the introd uc- tion o f data integrity in end-to -end encry pted WSNs thro ugh Merkle hash trees of Message Authenticatio n Cod es ( MA Cs). Howe ver , both scheme s raise power consum ption c oncern s, since compu tation requirem ents for public key encry ption is still considered h igh f or WSNs [12]. Many hop- by-ho p a ggregation protoco ls in WSNs like [3], [6], [9] , [13], [ 17], provide more e fficient aggr egation oper a- tions and high ly consider data in tegrity . Howe ver , since sensed data being pa ssed to non -leaf aggregators are r ev ealed for the sake o f midd le-way agg regation, hop-b y-ho p aggr egation protoco ls repr esent weaker mo del of data confidentiality per- spectiv e than end- to-end aggregation p rotocols. Data secrecy can be r ev oked o f a par tition if a passiv e adversary has obtained the key o f the r oot a ggregator of th at partition. A. Pr oblem Statemen t The ch allenge is to find a gen eral security p rotoco l fo r aggregated WSNs that is not lim ited to certain to pology and provid es strong data confid entiality comparab le to those in secu re end-to-end comm unication pro tocols. Also, it can provide efficient d ata aggregation and integrity c omparab le to those in hop- by-ho p aggregatio n, tak ing in to account the presence of active and passive ad versaries. So , when some nodes o f the aggregated WSN are ph ysically co mpro mised, compro miser must not gain more inf ormation or ha ve influence on aggr egated results beyond the effects of its com promised nodes. For these purp oses, we pr opose our secur ity proto col that provid es end- to-end data c oncealmen t using d ata d iffu- sion, and in th e same time, it provid es secure an d flexible hop - by-ho p aggregation with efficient data integrity test f ollowed by attestation pr ocess when forged data ar e detected in or der to e liminate and exclude con tributions o f any comp romised nodes that mig ht b e the sou rce o f th e forged data. I I I . S Y S T E M M O D E L A. Nota tions W e use the following nota tions to describe our protoco l: • BS ref ers to the Base Station. • S = { S 1 , S 2 , . . . , S n } represents the set of sen- sor/aggregato r no des in the WSN. Since in our mo del sensors have the ag gregation c apabilities, the term senso r will b e used to refer to a sensor that ag gregates as well. • I D S i refers to the n ode ID of sen sor n ode S i . • K S i ,S j denotes a pairwise sym metric key b etween node S i and node S j . K S i and K ′ S i are two pairwise symmetric keys o f nod e S i shared with the BS, and K is a set of all keys. • m S i denotes a sensed data rea d by sensor S i . m S i is a bound ed real value, i.e. m S i ∈ D = [ u, v ] fo r m aximum and minimum sen sible values v and u , re spectiv ely . • E nc K ( m ) de notes an en cryptio n o f a message m using a key K . n' nodes n" nodes Level i Level j Level k n nodes S in S i S j2 S j1 S jn' S kn" S k1 BS Fig. 1. Network Model (Aggregated WSN). • M AC ( K S i , m S i ) deno tes a me ssage authentica tion c ode of m S i that is sensed by sensor S i , this co de is g enerated using th e symmetric key K S i that is sha red b etween S i and the BS. • F K ( m ) ref ers to a diffusion algo rithm that is a p ublic knowledge in the WSN. It takes as input a key K and a data m , th e resu lt is a diffused value D ∈ [ u , v ] . • S i − → S j represents a o ne (or m ore) hop com municatio n from senso r no de S i to S j . B. Network Mode l W e assume a g eneral ag gregated multi-hop WSN consisting of a large co llection of resource-con strained sensor/aggregato r nodes (MICA motes [5] for example) c onnected in a tree topolog y rooted at a po werfu l n ode called the Base Station (BS). An illustration of this model is depicted in Fig. 1. W e don’t imp ose any r estrictions on the topo logy as lon g as it is a conn ected tree rooted at the BS. W e do n’t requir e a specific agg regation tree co nstruction a lgorithm, any efficient tree constructio n alg orithm like T aG [8] can be used in our model. Th e BS may initially issue a ggregation q ueries or it may be con nected to an off-network distant querier which is in this case considered data consumer, and the BS is con sidered its query server . Aggregation qu eries r epresents the union of all sensor readings a long the paths of th e WSN to its root, i.e. the BS. W e assume that every sensor node S i is deployed with two unique symmetric keys K S i and K ′ S i shared with th e BS, using a secu re key de ployment protoco l, like MI B [1 1]. A secure broadc ast au thentication protocol is assumed for authenticating messages, an example of such p rotocol is µ TESLA [12]. Se- cure ke y distribution between adjacen t no des is also assum ed, some ca n be f ound in [2]. C. Attacker Model W e assum e a d ual o peration al mode adversar y (both p assi ve and active) who is interested in rev ealing in-network data 3 secrecy and injecting f orged data. In our mode l, we consid er effecti ve attack s, wher e an adversary physically compro mises k ≪ n no des to gain the advantage that would result of attacking m nodes where k < m ≤ n without the need of attempting such attack on these m no des directly . That is, with few comprom ised nodes, an adversar y can en dange r the security of an aggregated WSN as if it ha d physically compro mised mu ch larger collection of no des. When we denote a no de as b eing p hysically compr omised, we mean that an adversary gain ed co ntrol over the node’ s op eration, ha ving access to all its memor y , keys, and r esources, and is ca pable to reprogra m such a compromised node with attacking code. Attacker is no t limited to a sing le place, it ca n compr omise scattered par titions of nodes in wh ich ev ery partition m ay have nodes in pa rent/childr en relationship. In this work , we don’t consider preventing attacks that disrupt the regular ope ration of a WSN such as denial- of-service (DoS) a ttack [14] or underlying r outing protocol attacks. W e are interested in prev enting attacks that aim to acquire ag gregation results or tampe r them rather than attacks that aim to p revent a quer ier f rom bein g served . D. Design Goa ls W e d esigned our protocol to protec t ag ainst spy-out a nd false d ata injectio n attacks, fo r that, we con sidered th e fol- lowing security perspectives: • Resilience: An adversary wh o co mprom ises few nod es of an ag gregated WSN must n ot spy-out o r gain any im pact on the fin al agg regation ou tcome beyond the in fluence of the reading s and results of its com promised no des. • Efficient Data Integrity , Comm itment an d Attestation : Aggregation r esult must be verified to be th e authentic union o f sensor read ings and inte rmediate resu lts. Such verification and attestation pr ocesses shou ld not impose significant overhead over the WSN that is over aggr ega- tion co mmun ication overhead. • Gener ality: The proto col should apply to any aggregated WSN with arbitrar y tree to polog y , moreover , the proto - col should support expandable WSNs without any extra reconfigu ration. • Status M onitoring : BS must determ ine when a sensor node b ecomes dead or unrea chable, by kn owing and maintaining a list o f all nod es con tributed in every aggregation query . I V . E FFI C I E N T A N D S E C U R E D AT A A G G R E G AT I O N P R OT O C O L In th is section, we pr esent our p roposed pr otocol that resolves th e c ompro mise between data secrecy and efficient aggregation. An overview o f the protocol will be presented first, then it will be followed by discussing the protoco l details. A. Ove rview Our pro tocol is desig ned over the approac h of data diffusion that preserves the mathematical relationships between different values which are all bo unded by a d efined range. By p reserving mathematical relationship s we can pe rform efficient hop -by- hop aggregation of collecte d diffused data. The in formatio n of th ese ma thematical relatio nships are kept concealed end -to- end to maintain complete commu nication path secr ecy . Beside maintaining the math ematical relationship s, the diffusion algo- rithm must no t in crease the size of encry pted data. Based on this, we can a chieve efficient secu re hop-by -hop ag gregation of en d-to-e nd concealed data in ag gregated WSNs. B. Network Setu p a nd Query Disseminatio n After field dep loyment, communica tion paths should be established. An efficient algorithm like T aG [ 8] can be used for tr ee topolog y co nstruction. Commu nication ch annels ar e secured using pairwise e ncryptio n keys between ev ery par- ent/children nodes, this is the same techniqu e used in many hop-b y-hop pr otocols (e.g. [1 7]) fo r securin g commu nication channels. After tree co nstruction , e very sensor no de S i sends its I D S i and an initial rand om reading m 0 i ∈ [ u, v ] to the BS in a message encr ypted u sing pairw ise symmetric key K S i . The initial rando m reading m 0 i serves in d ata d iffusion algor ithm as we will see later . When t he BS recei ves a query from a querier, it disseminates this q uery throug h th e WSN p aths. This query contains the desired aggregation function to b e perfor med. C. Data Diffusion The p urpo se of the data diffusion proc ess is to con solidate transient data from intermediate aggregators while gi ving them flexibility and efficiency while applying agg regation fu nctions on these con cealed d ata. Data d iffusion serves also in d ata integrity check as we w ill see later . Every senso r n ode diffuses its sensed d ata befor e transmission. Middle-way aggregation of diffused data occur s before the fina l result rea ches the BS, which is the o nly one who can rev ert diffused result to its actual value. Assume S = { S 1 , S 2 , . . . , S n } be the set o f sensor nodes and every no de S i reads a value m S i . E very sensor node S i uses a d iffusion f unction F K ( m S i ) , using th e keys K S i and K ′ S i to generate a p air of diffused d ata, wh ere K S i , K ′ S i are two share d keys between S i and the b ase station (BS). W e define the diffusion f unction F K S i ( m S i ) as fo llows: Definition 1 : Assum e P S : D × K → D be a pub lic generato r map (i. e., o ne way fun ction) to pro duce D j = P S ( K S i , D j − 1 ) (1) where D j ∈ D , D 0 = m 0 S i , and K S i ∈ K for j ≥ 1 and 1 ≤ i ≤ n . Let F : D × D − → D be a diffusion functio n defined as F K S i ( m j S i ) = P S ( K S i , D j − 1 ) ⊙ m j S i , (2) The value o f the generato r sequence P S is taken as an input alon g with the sensed readin g m j S i to the m athematical operan d ⊙ which genera tes a diffused v alue F K S i ( m j S i ) ∈ D . There is no strict definition of operand ⊙ , it refers to any reversible operation that takes two inputs and produ ces an 4 ….. ….. ….. ….. ….. BS H G Q W R X Y Z Fig. 2. An exampl e of an aggregate d WSN tree. output that belo ngs to D . Examp les o f ⊙ cou ld vary between trivial o perator s su ch as simple addition ”+” to mo re comp lex bijection functio ns. D ′ j is gener ated symmetrically to D j , but using key K ′ S i instead o f K S i . Since the BS shares the private key K S i and initial ran dom reading m 0 S i of every sensor node S i , th e BS is able to generate the diffusion value D j of every transmission p hase. This means that the BS can revert every diffused reading D j S i sent by a sen sor S i in the WSN to its actual value. V . T H E S U M A G G R E G AT I O N In this section, we pr opose the S U M aggregation func- tion in o ur secu re aggregation p rotocol. The alg orithm that perfor ms the S U M aggregation SumAgg is illustrated in algorithm 1. When the BS receives a qu ery o f S U M aggre- gation functio n, it br oadcasts this r equest throu gh the WSN. Whenever a sensor no de gets this requ est, it passes such a request to its childre n nodes, this goes on until reachin g leaf lev el. A leaf sensor nod e receiving this r equest will sen d its diffused reading to its par ent. For illustration pu rposes, let us consider the network in Fig. 2. Le af sensor X sends the following packet to its immed iate paren t W : X − → W : I D X , I V X,W , E nc K X,W F K X ( m X ) , F K ′ X ( m X ) , M AC X (3) where M AC X = M AC K X , F K X ( m X ) || F K ′ X ( m X ) (4) As we can see, node X sends its I D X and an encryp ted pair of its diffused sensed data m X to its parent W . X also sends a pairwise cou nter I V X,W to pro tect again st rep lay attack s. Finally , X sends a MA C of its reading using its p riv ate key an d attach it at the en d of the p acket for authen tication pur poses as we sh all see later . The sen sor n ode W receiv es similar packets fro m its other children, i.e. Y and Z . Now W needs to aggregate data received from its childre n along with its own sensed d ata m W . This is done th roug h ap plying the S U M aggregation fu nction Input : A WSN with set S of n nod es and BS. Output : S U M ag gregation result. BS br oadcasts S U M a ggregation query in the WSN for ∀ S i ∈ S do l ist S i = { I D S i } Sense m S i D S U M S i = F K S i ( m S i ) D S U M ′ S i = F K ′ S i ( m S i ) for ∀ S j that is a n imm ediate c hild o f S i do D S U M S i = D S U M S i + D S U M S j D S U M ′ S i = D S U M ′ S i + D S U M ′ S j l ist S i = l i st S i ∪ l ist S j end for end for BS sum s ag gregation of its im mediate children nodes. if IPET ch eck for final agg regation result in the BS passes then return S U M else Call Com Att /* Commitmen t and Attestation Algo .*/ end if Algorithm 1 : SumAgg: S U M Ag gregation Algorith m as we can see in the fo llowing packet that W sends to its parent G : W − → G : li st W , I V W ,G , E nc K W,G X S i ∈ list W F K S i ( m S i ) , X S i ∈ list W F K ′ S i ( m S i ) , M AC W (5) where M AC W = M AC K W , X S i ∈ list W F K S i ( m S i ) || X S i ∈ list W F K ′ S i ( m S i ) ⊕ M AC X ⊕ M AC Y ⊕ M AC Z (6) Here li st W represents the list o f all I D s of the children of W w ho contributed in the agg regation, inclu ding I D W . As we c an see, W sends its I D W and I D s o f all its ch ildren who con tributed in the agg regation, an d the agg regated S U M of their d ata. As shown above, W s ums a ll pa irs of data in ord er , i.e. all first elem ents of every pa ir are sum med together, the same thing happen s to second elements of all pairs. This scen ario con tinues until th e BS receives from every immediate child a packet that co ntains the I Ds of all no des participated in the S U M agg regation on the partition rooted by that child, along with its diffused ag gregation p air . T he BS then computes th e final aggregation pair ( DS U M , DS U M ′ ) of d iffused summation: ( D S U M , DS U M ′ ) = X i ∈ list ∗ F K i ( m S i ) , X i ∈ list ∗ F K ′ i ( m S i ) (7) where l ist ∗ = l ist H ∪ . . . ∪ li st G ∪ . . . ∪ li st Q (8) 5 The actual values o f this diffused pair ( D S U M , DS U M ′ ) should ref er to the same outp ut, but since they are diffused differently , they look d ifferent. Because th e BS knows K S i and K ′ S i for every no de S i , the BS is able to generate the diffusion values that every no de contributed in the aggre- gation has used to diffuse its read ing, the BS can r ev ert the pair ( D S U M , DS U M ′ ) to th eir actual values. This is done by fin ding the sum mations of all diffusion values that were ap plied a long the p ath of agg regation, and using these summations when applying the reverse d iffusion fun ction o n counter parts resu lts D S U M an d D S U M ′ : ( S U M , S U M ′ ) = D S U M ¯ ⊙ X i ∈ list ∗ D i , D S U M ′ ¯ ⊙ X i ∈ list ∗ D ′ i (9) Here, the operan d ¯ ⊙ ref ers to the reverse o f the diffusion operation . Now the BS revealed the actual result of S U M and S U M ′ aggregation, it needs to check the in tegrity of this result. The BS che cks the equ ality o f reverted pair S U M and S U M ′ , if th ey ar e equal t hen the aggregation result is accepted (unless th e BS doub ts it), otherwise the re sult is re jected an d attestation p rocess will start to detect the p ath and the sour ce of th e outliers as explain ed in Section VI. The test th at uses eq uation 9 the n chec ks the equ ality of resulted pair is called Identical Pair Equality T est (IPET) . IPET is an O (1 ) heu ristic tha t gives u s a quick initial indication about the in tegrity of the aggregation result. Lemma 2 : Th e complexity of Su mAgg algor ithm with data diffusion is O ( n ln( n )) on average, an d the BS need s O (1 ) to verify the integrity o f the final agg regation result. Other ag gregation f unctions like M E AN and M AX can be derived from above de scription of S U M ag gregation with slight modification s. V I . C O M M I T M E N T A N D A T T E S TA T I O N In this section we tu rn our atten tion to verifying sensor’ s commitmen ts of aggregation, and attestation for find ing outlier or compro mised nod es. Note that we don ’t conside r dete cting the case where a comprom ised node tries to forge its own data, this is becau se such a situation is hard to detect if forged data belon gs to norm al data ran ge an d this resem bles node malf unction . In co ntrast, we are inter ested in d etecting compro mised nod es that are trying to forge aggregation data of the ir no n-comp romised childre n. The divide and conque r algorithm for co mmitment and attestation ComAtt is p resented in algorithm 2, this algo rithm uses IPET check as a heur istic to reco nstruct on ly those branche s of the n etwork MAC tree which are necessary for the attestation pro cess, av oiding unnecessary r econstructio n of the wh ole MAC tree of the WSN. When the BS d iscovers that the fina l aggregation result fails the IPET check , it starts the attestation pro cess by add ing its immediate ch ildren who contributed in the aggregation to the set Q -which is the set contain ing nodes to be tested- for verification. For every node S i ∈ Q , the BS che cks S i as f ollows. Th e BS asks fr om every no de S i ∈ Q to r esend Input : l i s t ∗ (list of I Ds of all nod es contr ibuted in an aggregation) , M AC Agg (MA C of fin al aggregation result) Output : l i st L (list o f I D s of ou tliers) list L = ∅ , l ist C = ∅ Q = { S i : ∀ S i ∈ list ∗ ∧ S i is immediate children of BS } while Q 6 = ∅ do Pick a node S i from Q S i − → B S : l ist S i , I V S i , ( D S U M S i , D S U M ′ S i ) , M AC S i M AC C alc S i = Reconstructed M AC S i in B S using collected data and M A C Agg if M AC C alc S i 6 = M AC S i OR IPET check of S i packe t fails then if S i is not committed to its pre vious aggre gation packet then list C = list C ∪ S i end i f list L = list L ∪ S i Q = Q ∪ { S j : ∀ S j ∈ list ∗ ∧ S j is immediate children of S i } end if Q = Q − S i end wh ile fo r ∀ S i ∈ list L − l ist C do list ′ S i = ( list S i − l ist L ) ∪ S i S i − → B S : list ′ S i , I V S i , ( P j ∈ list ′ S i F K j ( m j ) , P j ∈ list ′ S i F K ′ j ( m j )) , M AC S i if IPET check of aggregation pair of S i passes then list L = list L − S i end if end for RETURN list L Algorithm 2 : ComAtt: Commitment an d Attestation Algo . its aggregation packet. The BS then c hecks the commitmen t of S i by constru cting its au thentication code M AC C alc S i with the help of the final aggregation result au thentication code M AC Agg and co llected data. I f M AC C alc S i is identical to M AC S i , th en the BS knows that S i is com mitted to its previously sent ag gregation packet. If S i is committed and its aggr egation p air passes the IPET ch eck then it is assumed honest - unless the BS doubts its result as we shall see later- and its descendan ts will be excluded from further verifications. On the other hand, if S i appeared not to be committed to its pre viou sly sent aggregation, or its aggregation p air fails the IPET test, then S i is added to the list of o utliers l i st L , and ev ery children S j of S i is added to the set Q for furthe r in vestigation. For the case when com mitment test o f S i fails, S i is also added to the list o f n ot co mmitted no des l i st C . After pro cessing all no des in Q , li st L will be h aving suspected nodes that either no t c ommitted or failed the IPET check. No n-comm itted nod es in l ist L are d irectly c onsidered dishonest or comp romised without any further inv estigation. Howe ver , it m ight be the case that an ho nest comm itted node in l ist L failed the IPET check because one or mo re of its children were compro mised. W e need to elimin ate such ho nest nodes f rom l i st L , this is do ne by fur ther investigation o f committed nod es that fail IPET check, i.e . S i ∈ l i st L − l i s t C . 6 For every such nod e S i , the BS requ ests a new a ggregation of S i that excludes data fr om any node S j ∈ l ist L , th at is, the BS is giving S i a ch ance to prove its hon esty by finding the aggregation of its only hone st childr en. I f the ne w aggregation of S i passes th e IPET check, th en S i is re moved from l ist L , o therwise, it is kept the re. Finally , the ComAtt algorithm returns l i st L that contains the set of outliers or compro mised nodes. Lemma 3 : Th e commitmen t process in ComAtt algorith m is O ( c ln n ) in average for so me con stant c , and O ( n ) in the worst case. Pr o of: Th e p roof is a direct consequence fr om the bi- nary tree search algor ithm, co nsidering the heigh t ( depth) of aggregation equals ln n in av erage V I I . S E C U R I T Y A N A LY S I S In th is section, we show how o ur security proto col could be compare d to hop-b y-ho p an d end- to-end pr otocols in terms of security lev el an d efficiency of data integrity chec k. A. Nod e Attacks W e consid er the logical hypoth esis tha t a node S i is attacked by an intrud er ( attacker) I . This attacker I can gain access to all inform ation of this no de includ ing K S i , l ist S i and m S i . In this case, it ca n alter the message m S i to m I and encryp t it using th e key K S i . W e show that the o nly influen ce such an attacker can ha ve on fina l agg regation result is sending forged aggregation of attacked node s. If the attacker attempts to change the aggr egation values o f its children with out knowing their dual diffusion seeds, then this attemp t will be qu ickly caught by the I PET test. So, an a ttacker in this case won’t be able to forge its agg regation excep t b y ch anging its own reading m I and ag gregations of its c hildren wh ich their dual diffusion seeds are known to the attacker . That is , if an attacker wants to forge the aggregation of n no des and not g et cau ght by IPET , then this attacker must compromise or acquire pri vate data o f n no des. Lemma 4 : Ou r a ggregation proto col represents a security model against spy-out attack s th at is better or at least as good as h op-b y-hop aggregation proto cols. Pr o of: Ou r pro tocol has an ad vantage over hop -by-h op protoco ls because of transient d ata diffusion. Only when a passiv e ad versary succeed s in b reaking the d iffused data o f all children of a ho p, our protocol becom es vu lnerable to spy-out attacks as any othe r hop- by-ho p p rotoco l. Lemma 5 : Ou r p rotocol p erform s either mo re efficient or at least as g ood as end-to-en d aggregation pro tocols in checkin g data in tegrity . Pr o of: In our pro tocol, we u se IPET heuristic to recon- struct the only necessary bra nches of the M A C tr ee for testing data integrity . In the w orst case, we will need to reconstruct the whole MAC tree, which is th e case in en d-to-en d pr otocols. V I I I . C O N C L U S I O N S In this paper, we demon strated a mode l for secure d ata aggregation in WSNs, which is a b lend of hop-b y-ho p o pera- tional efficiency an d end-to- end data secrecy . W e showed that this model has low co mputatio nal co mplexity and the BS u ses O (1) heuristic to verify final a ggregation result o f sensed data and it needs O (ln n ) in av erage to detect an attacked n ode. W e plan to perfor m simulation an d furthe r secur ity analysis of th is m odel in ou r f uture work. R E F E R E N C E S [1] C. Castelluc cia, E. Mykletun, and G. Tsudik. Efficient aggregati on of encrypt ed data in w ireless sensor networks. In Mobile and Ubiquitous Systems: Networking and Servi ces, 2005. MobiQuit ous 2005. The Sec- ond Annual Internationa l Confer ence on , pages 109–117, 2005. [2] H. Chan, V . Gligor , A. Perrig, and G. Muralidha ran. On the distri bution and re vocat ion of cryptographic keys in sensor netwo rks. IEEE T rans. Dependabl e Sec ur . Comput . , 2(3):233–247, 2005. [3] H. Chan, A. Perrig, and D. Song. Secure hierarchi cal in-network aggre gation in sensor networks. In Proc . 13 ACM conf . on computer and communications security , Nove mber 2006. [4] J. Girao, D. W esthoff, and M. Schneider . CD A: Concealed Data Aggreg ation in W irele ss Sensor Networks. In Pr oc. 40th International Confer ence on Communiacations, IEEE ICC ’05 , Kore a, May 2005. [5] M. Horton, D. C uller , K. Pister , J. Hill, R. Sze wczyk, and A. W oo. MICA the commercializ ation of microsensor m otes. In Sensors , 19(4):40–4 8, April 2002. [6] L . Hu and D. Evans. Secu re aggre gation for wireless netw orks. In Symposium on Applications and the Internet W orkshops (SAINT’03) , number 384, 2003. [7] C. Intanagonwiw at, D. Estrin, R. Govinda n, and J. Heidemann. Impact of network density on data aggregat ion in wireless sensor netwo rks. In Pr oc. of International Confer ence on Distrib uted Computin g Systems (ICDCS ’02) , V ienna, Austria, July 2002. [8] S. Madden, M. Franklinm, J . Hellerstein, and W . Hong. T A G: a tiny aggre gation servic e for ad-hoc sensor networks. SIGOPS Oper . Syst. Rev . , (36(SI):):131–146 , May 2002. [9] A. Mahimkar and T . S. Rappaport. Secureda v: a secure data aggrega tion and veri fication protocol for sensor networks. In Pr oc. IE EE Global T elecommunicat ions Confer ence , 2004. GLOBECOM ’04. , volume 4, pages 2175–2179, 2004. [10] E. Mykletun, J. Girao, and D. W esthof f. Public ke y based cryptoschemes for data concealment in wireless sensor netwo rks. In Proc . IE EE Internati onal Confe renc e on Communicat ions (ICC ’06) , 2006. [11] A. Perrig, M. Luk, and C. Kuo. Message-in -a-bottle : User-friendl y and secure k ey depl oyment for sensor no des. In Proc. of the A CM Co nfer ence on E mbedded Network ed Sensor System (SenSys ’07) , October 2007. [12] A. Perrig, R. Szeczyk , W en V ., D. Cull er , and J . T ygar . SPINS: security protocol s for s ensor network s. Mobil Computing and Networkings , page 189199, 2001. [13] B. Przydatek , D. Song, and A. Perrig. SIA: Secure information aggre gation in sensor networks. In Proc. of SenSys 2003 , page 255265, Ne w Y ork, Nove mber 2003. [14] D. Raymond and S. Midkif f. Denial-of-servi ce in wireless sensor netw orks: Attacks and defenses. IEE E P ervasive Computing , 7(1):74– 81, 2008. [15] Y . Sang, H. Shen, Y . Inoguchi, Y . T an, and N. Xiong. Secure data aggre gation in wireless sensor networks: A survey . In Proc . of the Sev enth International Conferen ce on P arallel and Distrib uted Com- puting , Applicatio ns and T echnolo gies (PDCAT ’06) , pages 315–320, W ashington, DC, USA, 2006. IEEE Computer Society . [16] I. Stojme novic. Han dbook of sensor net works, algo rithms and ar- chite chtrues. W ile y series on parall el and distrib uted computing , 2005. [17] Y . Y ang, X. W ang, and S. Z hu. SD AP: a secure hop-by-hop data aggre gation protocol for sensor networks. In Proc. 7th ACM Intera tional Symposium on Mobile Ad Hoc Networking and Computing , May 2006.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment