Security in Wireless Sensor Networks: Issues and Challenges
Wireless Sensor Network (WSN) is an emerging technology that shows great promise for various futuristic applications both for mass public and military. The sensing technology combined with processing power and wireless communication makes it lucrativ…
Authors: ** 제공되지 않음 (논문 원문에 저자 정보가 포함되어 있지 않음) **
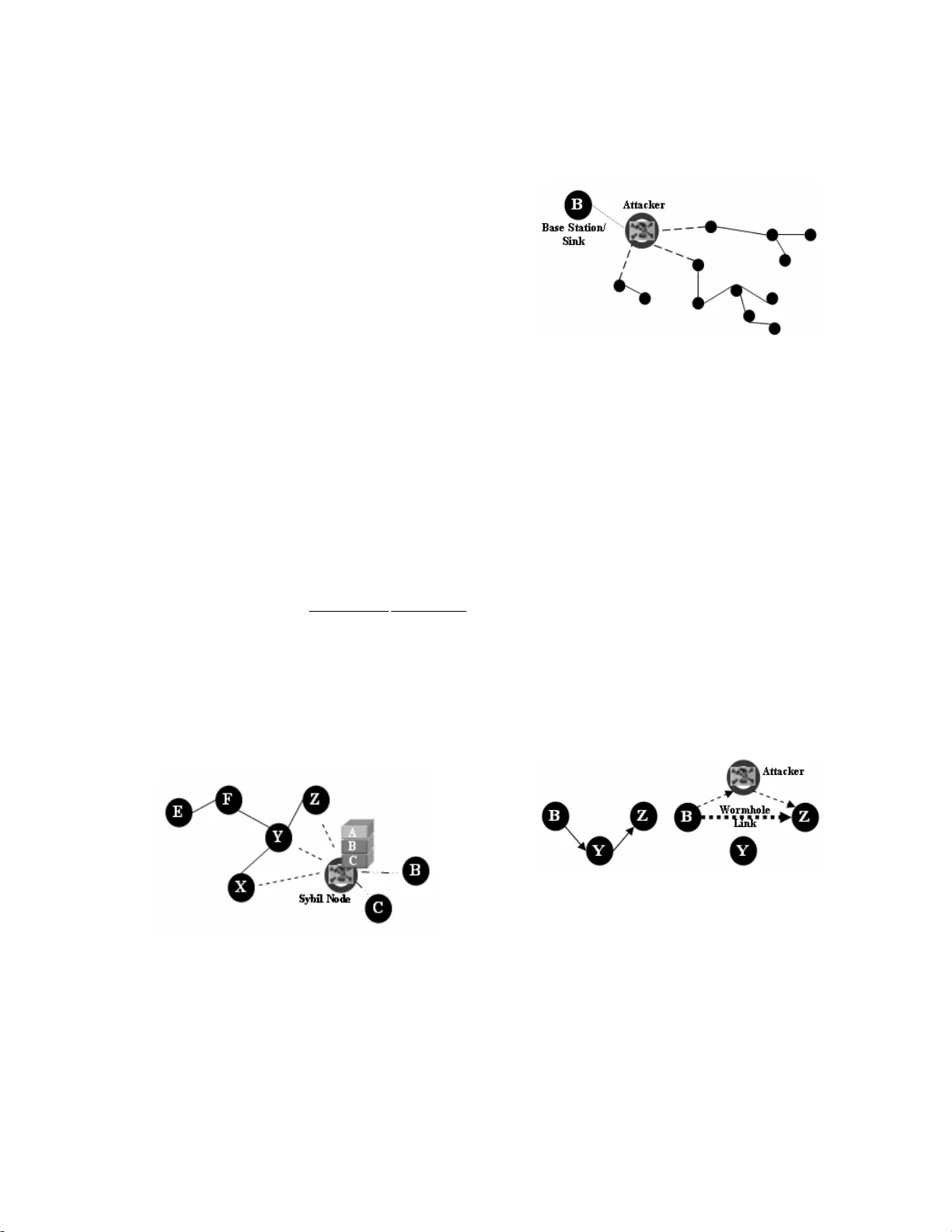
Security in Wireless Sensor Networks: Issues and Challenges Al-Sakib Kh an Pathan Department of Computer Engg. Kyung Hee University, Korea spathan@networking.khu.ac.kr Hyung-Woo Lee Department of Software Hanshin University, Korea hwlee@hs.ac.kr Choo ng Seo n Hong Department of Computer Engg. Kyung Hee University, Korea cshong@khu.ac.kr Abstract Wireless Sensor Net work (WSN) is an em erging technology that shows great promis e for various futuristic applications both for ma ss public a nd milita ry. The sens ing technology combined with processin g power and w ireless commun icat ion ma kes it luc rat ive fo r being exp loite d in abundan ce in future. The inclu sion of wireles s communication technology al so incurs various types o f security threats. The intent of this paper is to investigate the s ecurity related issues and chall enges in wireless senso r networks. We identi fy the security threat s, review proposed securit y mechanisms fo r wireless sens or networks. We also discus s the holistic vi ew of security for en suring layered and robust security in wireless sensor netw orks. Keywords Sensor, Security, Attack, Holistic, Challenge. 1. Introduction Wireless Sensor Networks (WS N) are emerging as bo th an important new tier in the IT ecos ystem and a rich domain of active research in volving hardwar e and system design, networking, dis tributed algorithms, programming mod els, data managem ent, security and socia l factors [1] , [2], [3]. The basic idea o f sensor network is to disper se tiny sens ing devices; w hich are capable of sensing some cha nges of incidents/ parameters and comm unicating with other de vices, over a specific ge ographic area for som e specific purposes like target tracki ng, surveillance, environmenta l monitoring etc. Today’s sensors can mon itor temperature, pressure, humidity, soil makeup, vehicular movement, noise levels, lig hting conditions, the presence or absence of certain kinds of ob jects or substances, m echanical stress levels on attached objec ts, and other properties [4]. I n case of wireless sensor networ k, the communic ation among the sensors is done using w ireless transceivers. The at tractive features of the wireless sensor networks attrac ted many researcher s to work on various issu es related to these types of networ ks. However, while the r outing strategies and w ireless sensor netw ork modeling are gettin g much preference, the security issues are yet to r eceive extensive focu s. In this paper, we explore the security iss ues and challe nges for next gene ration wireless sensor networks and discuss the crucial parameters that requir e extensive investiga tions. Basically the major challe nge for employing any ef ficient security scheme in wireless sensor networks is created by the This work was supported by MIC and ITRC Project size of sensors, consequently the processing p ower, memory and type of tas ks expected fro m the sensors. We di scuss these issues and challe nges in this paper. T o address the critical security issues in w ireless sensor networks we talk abo ut cryptography, ste ganography and ot her basics of networ k security and their applica bility in Section 2. We explore various types of threa ts and attacks against wireless se nsor network in Section 3. Se ction 4 reviews the related works and proposed schem es concerning securi ty in WSN and al so introduces the view of holistic security in WS N. Finally Section 5 concl udes the paper delineating the researc h challenges and fut ure trends toward the research in wireless sensor network security. 2. Feasibility of Basic Security Schemes in Wireless Sensor Networks Security is a broadly used term encompassing the characteris tics of authentica tion, integrity, pr ivacy, nonrepudiatio n, and anti-playbac k [5]. The more the dependenc y on the information provide d by the networks has been in creased, th e more t he risk of secure transmissio n of information ove r the networks has incr eased. For the secure transmission o f various types of information o ver networks, several crypto graphic, steganogr aphic and othe r techniques are used which a re well known. In this section, we discuss the network security funda mentals and how the techniques are meant for wireless sens or networks. 2.1 Cryptograp hy The encryption-decry ption techniques dev ised for the traditional wired netw orks are not feasible to be applie d directly for the wireless networ ks and in particular for wireless sensor networks. WS Ns consist of tiny sensors which reall y suffer from the la ck of proces sing, memory and battery power [6], [7], [8], [9]. Applying any encr yption scheme requ ires transmission o f extra bits, hence extra processing, memor y and battery powe r which are very important resources for the sensors’ longevity. Applyi ng the security mechanisms such as encryption cou ld also increase dela y, jitter and packe t loss in wireless sensor ne tworks [10]. Moreover , some critical questions arise when applyi ng encryption schemes to WS Ns like, how the key s are generated or dissem inated. How the keys are managed, revoked, assigne d to a new sensor added to the network or renewed for ensuring robus t security for the ISBN 89-5519-129-4 - 1043 - Feb. 20-22, 2006 ICACT2006 network. As minimal (or no) human interaction for the sens ors, is a fundamental feature of w ireless sensor networks, it becomes an im portant issue how the keys cou ld be modified time to time for encryp tion. Adoption of pre-loaded keys or embedded ke ys could not be an efficient solution. 2.2. Steganogr aphy While cryptography aim s at hiding the con tent of a message, steganogr aphy [11], [12] aims at hiding the existence of the message. Stegano graphy is the art of covert com munication by embedding a message into the multimed ia data (image, sound, video, e tc.) [13]. The main objective of steganography i s to modify the carrier in a way that is not percepti ble and hence, it looks just like ordinar y. It hides the existence of the covert channel, and fur thermore, in the case t hat we want to send a secret data without sender inform ation or when we want to distribute secret data publicl y, it is very useful. However, securing wirele ss sensor networks is not directly related t o steganogr aphy and processing multimedia data (like audio, video) w ith the inadequate resources [14] of the sensors is difficult and an open researc h issue. 2.3 Physic al Layer Sec ure Access Physical layer secure access in wireless sensor netw orks could be provided by using frequency hoppi ng. A dynamic combination of the para meters like hopping set (availa ble frequencies f or hopping), dwell time (time interval per hop) and hoppi ng patt ern (the sequence in which t he frequ encies from the availa ble hopping se t is used) could be use d with a little expense of me mory, processing and e nergy resources. Important poi nts in physical layer secur e access are the efficient design so that the hopping sequence is modi fied in less time than is required to discove r it and for emplo ying this both the sende r and receiver shoul d maintain a synchro nized clock. A scheme as proposed in [15] could also be util ized which introduc es secure physical la yer access em ploying the singular vector s with the cha nnel synthesized modulation. 3. Security Threats and Is sues in Wireless Sensor Networks M ost of th e threats and att acks against security in wireless networks a re almost si milar to their wire d counterp arts whi le some are exacerbate d with the inclusi on of wireless connectivity. In fact, wireless networks ar e usually more vulnerable to various security threa ts as the unguided transmission medium is m ore susceptible to security at tacks than those of the guide d transmission medium . The broadcast nature of the wireless communicatio n is a simple candidate for eavesdro pping. In most of the ca ses various secu rity issues and threats related to th ose we consider for wireless ad hoc networks a re also applica ble for wireless sensor ne tworks. These issues are well-e numerated in some past r esearches [16], [17], [18] and also a number of security schemes are alread y been propose d to fight against t hem. However, the se curity mechanisms devi sed for wireless ad hoc net works could not be applied directly for w ireless sensor networks because of the architectural dis parity of the two ne tworks. While ad hoc networks are self-or ganizing, dynamic to pology, peer to peer networks formed by a colle ction of mobile nodes and the centralized ent ity is absent [19]; the wireless sensor networks could have a com mand node or a base station (centralize d entit y, so metimes ter med as sin k). The architectural aspect of wireless sensor network co uld make the employm ent of a security schem es little bit easier as the base stations or the centralize d entities could be used extensively in th is case. Nevertheless, the major cha llenge is induced by the constraint of resources of th e tiny sensors. In many cases, sensors are expected to be deployed ar bitrarily in the enemy ter ritory (especia lly in military reconnaissan ce scenario) or over dangerous or hazardo us areas. Ther efore, even if the ba se station (sink) resides in the friendly or safe area, the sensor node s need to be protected from being comp romi sed. 3.1. Attacks in Wir eless Sensor Ne tworks Attacks agains t wireless sensor netw orks could be br oadly considered from two differ ent levels of views. O ne is the attack agains t the security mechanisms and anot her is against the basi c mecha nisms (lik e routing mech anisms). He re we point out the major attacks in wireless sensor networ ks. 3.1.1 Denial of Service Denial of Ser vice (DoS) [20], [21] is produced by the unintentional failure of nodes or malicious ac tion. The simplest DoS attack tries to exhaust the resources avai lable to the victim node, by se nding extra unneces sary packets and thus prevents le gitimate networ k users from accessing servi ces or resources to which the y are entitled. DoS attack is me ant not only for the adversa ry’s attempt to subver t, disrupt, or destroy a network, bu t also for any ev ent that dimini shes a network’s capability to p rovide a service. In wireless sens or networks, several types of DoS attacks in different layers might be performed. A t physical layer the D oS attacks could be jamming and t ampering, at link laye r, collision, exhau stion, unfairness, at network laye r, neglect and greed, homi ng, misdirection, black holes and at tra nsport layer this attack could b e performed by mal icious f looding an d desynchroniz ation. The m echanisms to prevent DoS attacks include payme nt for networ k resources, pushback, str ong authenticati on and identifica tion of traff ic. 3.1.2 Attacks on Information in transit In a sensor network, sensors m onitor the changes of specific parameters or val ues and report to the sink according to the requirement. Whi le sending the report, the information in transit may be altered, spoofe d, replayed again or vanishe d. As wireless communica tion is vulnerable to eav esdropping, any attacker can monit or the traffic flow and get into actio n to interrupt, intercept, m odify or fabricate [22] packets th us, provide wrong informa tion to the base stations or sinks. As sensor nodes typically have short r ange of transmission and scarce resource, a n attacker with high proce ssing power and larger comm unication range could a ttack several sensors at t he ISBN 89-5519-129-4 - 1044 - Feb. 20-22, 2006 ICACT2006 same time to modify the ac tual information during transmission. 3.1.3 Sybil Attac k In many cases, the sensors in a wireless sensor network might need to w ork together to accompl ish a task, hence they can use distrib ution of subtasks a nd redundancy o f information. In such a situation, a node can pretend to be mor e than one node using the identitie s of other legitim ate nodes (Figure 1). This type of attack wher e a node forges the identities of m ore than one node is the Sybil atta ck [23], [24]. Sybil attack tri es to degrade the integrity of data, securit y and resource utiliz ation that the distribute d algorithm attempts to achieve. Sybil at tack c an be pe rformed for attackin g the distributed st orage, routing m echanism, data aggregat ion, voting, fair resource all ocation and misbe havior detection [24]. Basically, any peer-to-peer network (especial ly wireless ad hoc networks) is vulnerable to sybil attack. However, as WSNs can hav e some sort of ba se stations or gate ways, this attack could be prevented using e fficient protoc ols. Douceur [23] showed tha t, without a logica lly centralize d authority, sybil attacks are alwa ys possible except under extreme and unrealistic assumptions of r esource parity and coordina tion among entit ies. However, detect ion of sybil nodes in a network is no t so easy. Newsom e et. al. [24] use d radio resource test ing to detec t th e presence of sybil node(s) in sensor network a nd showed that the proba bility to detect the existence of a syb il node is: Pr(detection) = 1 – ( 1 - ∑ G M allS , , c M m S c n G g M m S s ) ( − − ) r Where, n is the number of nodes in a neighbor set, s is t he number of syb il nodes, m m alicious nodes, g number of good nodes, c is the n umber of nodes that can be tested at a time by a node, of which S are sybi l nodes, M are malicious ( faulty) nodes, G are good (correct) nodes and r is the number of rounds to iterate the te st. Figure 1: Sybil Attack 3.1.4 Blackh ole/Sinkhole Att ack In this attack, a malicious node acts as a blackhole [25] to attract all the traffic in the sensor network. Especially i n a flooding based protocol, the attacker listens to requests for routes then replies to the target nodes tha t it contains the high quality or short est path to the base statio n. Once the malic ious device has been able to in sert itself between the communica ting nodes (for example, sink and sensor node ), it is able to do anything wit h the packets passing betwee n them. In fact, th is att ack can af fect even the nodes th ose are considerably far from the base statio ns. Figure 2 shows the conceptu al view of a b lackho le/sinkhol e attack . Figure 2: Conceptual vie w of Blackhole Attack 3.1.5 Hello Flood Attac k Hello Flood A ttack is introduced in [26]. This attack uses HELLO packets as a weapon to con vince the sensors in WSN. In this sort of a ttack an attacker with a high radio transmission (termed as a laptop-c lass attacker in [26]) range and processing power sends HELLO packets to a number of sens or nodes which are dispersed in a lar ge area within a WS N. The sensors are thus per suaded that the adversary is the ir neighbor. As a conseque nce, while sending the informa tion to the base station, the victim nodes try to go through the attacker as they know that it is their neig hbor and are ultim ately spoofed by the attacker. 3.1.7 Wormho le Attack Wormhole attac k [27] is a critical attack in which the attacker records the packet s (or bits) at one location in the network and tunne ls those to another location. The tunneling or retransmitting of bits could be done selec tively. Wormhole attack is a si gnificant threat t o wireless sensor netw orks, because; this sort of attack does not require compromising a sensor in the netw ork rather, it could be performed eve n at the initial phase when t he sensors start to disco ver the neighboring information. (a) (b) Figure 3: Wormhole Attack Figure 3 (a and b) shows a situation whe re a wormhole attack takes pla ce. When a node B (for e xample, the base station or any other sensor) br oadcasts t he routing request packet, t he attack er receiv es this p acket and re plays it in its neighborho od. Each neighboring node receiving this replaye d packet wi ll consi der itself to be i n the ra nge of No de B, and will mark this node as its parent. H ence, even if the victim nodes are multiho p apart from B, attacker in th is case ISBN 89-5519-129-4 - 1045 - Feb. 20-22, 2006 ICACT2006 convinces t hem that B is onl y a singl e hop away from them, thus creates a worm hole. 4. Proposed Security Schemes and Related Work In the recent years, wireless sensor network security has been abl e to attract th e attentio ns of a number of researchers around the world. I n this section we review and map various security schemes propose d or implemented so far for wireless sensor networks. 4.1. Securit y Schemes for Wireless Sensor Networks [26] gives an analysis of sec ure routing in wireless sensor networks. [34] stud ies how to design se cure distributed sensor networks with multiple supply volta ges to reduce the ener gy consumpt ion on compu tation and t herefore to exte nd the network’s l ife ti me. [7] aims at in creasing energy ef ficienc y for key management i n wireless sensor networks a nd uses Younis et. al. [36] network model for its application. Wood et al. [31] studies D oS attacks against differ ent layers of sensor protocol stac k. JAM [38] presents a mapping protocol w hich detects a jamm ed region in the sensor network and he lps to avoid the fault y region to continue rout ing within the networ k, thus handles D oS attacks cause d by jamming. In [39] the authors show that wormholes those ar e so far considered har mful for WSN cou ld effectively be used as a reactive defen se mechanism for preventing jamm ing DoS attacks. Ye et. al. [33] presents a statistica l en-route filtering (SEF) mec hanism to detec t injected false data in sensor network and f ocus mainly on how to fil ter false data using collective secr et and thus preventing any si ngle compromise d node from breaking the ent ire system. SNEP & µ TES LA [6] are two secure buildin g blocks for provid ing data confidential ity, data freshnes s and broadcast au thentication. TinySec [35] pr oposes a link layer se curity mechanism for sensor networ ks which uses an e fficient symm etric key encryption pro tocol. Newsome et. al. [24] proposes some defense me chanisms against sybil a ttack in sensor networks. Kulkar ni et al. [28] analyzes the prob lem of assigning initial se crets to users in ad-hoc sensor networks to ensur e authenticatio n and privacy during their com munication and po ints out possible wa ys of sharing the secrets. [40] presents a probab ilistic secret shari ng protocol to defend He llo flood attacks. The scheme uses a bidirectio nal verification tec hnique and also in troduces multi-path multi-ba se station routing if bidirecti onal verificati on is not sufficient to defe nd the attack. Security Schemes Attac ks Deterred Netwo rk Archite cture Major F eatures JAM [38] DoS Attack (Jamming) Traditional wirele ss sensor network Avoidance of jammed region by using coa lesced neighbor nodes Wormhole based [39] DoS Attack (Jamming) Hybrid (mainly wirele ss partly wired) sensor network Uses wormholes to avoid jamm ing Statis tical En -Rout e Filtering [33] Information Spoofing Large number of sensors, highly dense wireles s sensor network Detects and drops false reports during forwarding proce ss Radio Resource Testing, Random Key Pre-distribution etc. [24] Sybil Attac k Traditional wirele ss sensor network Uses radio resource, Ra ndom key pre-distribution, Re gistration procedure, Position verification a nd Code attestation for detecting sybil entity Bidirectional Verifica tion, Multi-path multi-ba se station routing [40] Hello Flood Attack Traditional wirele ss sensor network Adopts probabilistic secret sharing, Uses bidirect ional verification a nd multi-path multi-base station routing On Communication Sec urit y [32] Information or Da ta Spoofing Traditional wirele ss sensor network Efficient re source management, Protects the network even if part of the network is com promised TIK [27] Wormhole Attack, Information or Data Spoofing Traditional wirele ss sensor network Based on symm etric cryptography , Requires ac curate time synchronizat ion between all comm unicating partie s, implements temporal leashe s Random Key Predistribution [29], [30], [41] Data and i nformation spoofing, Attac ks in information in Transit Traditional wirele ss sensor network Provide resilience of the network, Protect the network eve n if part of the network is comprom ised, Provide authentication measures for sensor node s [42] Data and Inform ation Spoofing Distributed Sensor Network, Large-scale w ireless sensor network with dynamic nature Suitable for large wire less sensor networks which allows addition and deletion of sensors, R esilient to sensor node capture REWARD [43] Blackhole at tacks Traditional wirele ss sensor network Uses geographic routing, Ta kes advantage of the broadcast inter-radio beha vior to watch neighbor transmissions a nd detect blackhole attac ks TinySec [35] Data and Inform ation spoofing, Message Replay Attac k Traditional wirele ss sensor network Focuses on providing me ssage authenticity, integrity a nd confidentiality, Works in the li nk layer SNEP & µ TESLA [6] Data and Inform ation Spoofing, Messa ge Replay Att acks Traditional wirele ss sensor network Semantic security, Data a uthentication, Replay protec tion, Weak freshness, Low communication overhead Table 1: Summary of various sec urity schemes for wireless sensor networks ISBN 89-5519-129-4 - 1046 - Feb. 20-22, 2006 ICACT2006 REWARD [43] is a rout ing algorithm whic h fights agains t blackholes in the network. [32] proposes separ ate security schemes for data wi th variou s sensitivity levels and a location-base d scheme for wireless sensor networks that protects the re st of the network, even whe n parts of the network ar e compromised. [27] imp lements symmetric key cryptograp hic algorithms w ith delayed key d isclosure on motes to establis h secure communicat ion channels betwee n a base station and sensor s within its range. [41], [42], [29] and [30] propose key pre-distribution sc hemes, which target to improve the resilience of the network. In Table 1 w e summarize va rious securi ty scheme s along with their main properties propose d so far for wireless sensor netw orks. 4.2. Holistic S ecurity in Wireless S ensor Networks A holistic approach [37] aims at improving the perform ance of wireless sensor networks w ith respect to security, longevit y and connect ivity under changi ng environmental c onditions. The holistic approach of secu rity concerns abo ut involving all the layers for ensuring ove rall security in a network. For such a network, a sing le security solutio n for a single layer might n ot be an efficient solu tion rather employ ing a holistic appr oach could be the be st option. Figure 4: Holisti c view of Security in wireless sensor networks The holistic approach has som e basic princ iples like, in a given netw ork; security is to be ensured for all the layers of the protocol stack , the cost for ensuring security should not surpass the assessed security risk at a spec ific time, if there is no physical securi ty ensured for the sensors, the secur ity measures m ust be able to exhibit a gr aceful degrada tion if some of the sensor s in the network are c ompromised, out of order or ca ptured by the ene my and the security m easures should be develo ped to work in a decentralize d fashion. If security is not cons idered for all of the security layers, for example; if a se nsor is somehow captured or jammed in the physical layer, the security f or the overall ne twork breaks despite the fact t hat, there are some efficient security mechanisms worki ng in other layers. By bui lding security layers as in the holistic appr oach, protection coul d be established for the over all network. 5. Conclusion Most of the attacks against security in wireless sensor networks are caused by the insertion of false inform ation by the comprom ised nodes within the network. F or defending the inclusion of fa lse reports by com promised nodes, a means is required for detect ing false reports. However, develop ing such a detection mechan ism and making it efficient represe nts a great research challeng e. Again , ensurin g holi stic security in wireless sensor netw ork is a major research issue. Many of today’s propo sed security schemes are based on specific network model s. As there is a lack of c ombined effort to take a common model to ensure securi ty for each layer, in future though the security m echanisms become well-established for each indivi dual layer, c ombining all the mechanisms toge ther for making the m work in collaborati on with each other will incur a hard resear ch challenge. Even if holistic securi ty could be ensured for w ireless sensor networ ks, the cost-effec tiveness and energy efficienc y to employ such m echanisms could stil l pose great resea rch challenge in the coming days. R EFERENCE S [1] Culler, D. E a nd Hong, W., “Wireless Se nsor Networks”, Comm unication of the ACM, Vol. 47, No. 6, June 2004, pp. 30-33. [2] Akyildiz, I. F., Su, W., Sa nkarasubramaniam, Y , and Cayirci, E., “Wireless Sensor Netw orks: A Survey”, Computer Networks, 38, 2002, pp. 393-422. [3] Dai, S, Jing, X, and Li, L, “Research and analysis on routing protoc ols for wireless sensor ne tworks”, Proc. Internationa l Conference on Communications, C ircuits and Systems, V olume 1, 27-30 May, 2005, pp. 407-411. [4] Pathan, A-S. K., Islam, H. K., Sa yeed, S. A., Ahmed, F. and Hong, C. S., “A Framework for Providing E-Service s to the Rural Areas using Wireless Ad Hoc and Sensor Ne tworks”, to appear in IEEE ICNEWS 2006. [5] Undercoffer, J., Avancha, S ., Joshi, A., a nd Pinkston, J., “Security for Sensor Networks”, CADIP Research Sym posium, 2002, available at, http://www.cs.sfu. ca/~angiez/persona l/paper/sensor-ids.pdf [6] Perrig, A ., Szewczyk, R. , Wen, V., Cull er, D., a nd Tygar, J. D., “SPINS: Security Protocols for Sensor Ne tworks”, Wireless Networks, vol. 8, no. 5, 2002, pp. 521-534. [7] Jolly, G., Kuscu, M.C., Kokate, P., and Younis, M., “A Low-Energy Key Management Protoc ol for Wireless Sensor Ne tworks”, Proc. Eighth IEEE International Symposium on Computers and Communication, 2003. (ISCC 2003). vol.1, pp. 335 - 340. [8] Rabaey, J.M. , Ammer, J., Karala r, T., Suetfei Li., Otis, B., Sheets, M., and Tuan, T., “PicoRa dios for wireless sensor networks: the next challenge in ultra-low power design” 2002 IEEE International Solid-State Circuits Confe rence (ISSCC 2002), Volume 1, 3-7 Feb. 2002, pp. 200 – 201. [9] Hol lar , S, “C OTS Dus t ”, M ast er’ s Th esi s, E le ctr ic al E ngi ne eri ng an d Computer Science De partment, UC Berkeley, 2000. [10] Saleh, M. and Khatib, I. A., “Throughput Analysis of WEP Security i n Ad Hoc Sensor Ne tworks”, Proc. The Second International Confe rence on Innovations in Inform ation Technology (IIT’05 ), September 26-28, Dubai, 2005. [11] Kurak, C and McHugh, J, “A Caut ionary Note on Image Downgrading in Computer Security Appli cations”, Proceedings of the 8th Computer Security Applica tions Conference, San Antonio, December, 1992, pp. 153-159. [12] Mokowitz, I. S ., Longdon, G. E., a nd Chang, L., “A New Paradigm Hidden in Steganogra phy”, Proc. of the 2000 workshop on Ne w security paradigms, Ba llycotton, County Cork, Irela nd, 2001, pp. 41 – 50. [13] Kim, C. H., O, S. C., Lee, S. , Yang, W. I., and L ee, H-W. , “Steganal ysis on BPCS Steganogra phy”, Pacific Rim Workshop on Digital Steganography (STE G’03), July 3-4, Japan , 2003. [14] Younis, M., Akkaya , K., Eltowei ssy, M., and Wa daa, A., “On handli ng QoS traffic in wireless sensor networks” , Proc. of the 37th Annual Hawaii International Confere nce on System Sciences, 2004, 5-8 January, 2004, pp. 292 – 301. [15] Orihashi, M., Nakagawa, Y., Mura kami, Y., and K obayashi, K., “C hannel synthesized modula tion employing singular vec tor for secured access on physical layer”, IEEE GLOBECOM 2003, Volume 3, 1-5 December, 2003, pp. 1226 – 1230. ISBN 89-5519-129-4 - 1047 - Feb. 20-22, 2006 ICACT2006 [16] Zhou, L. and Haas, Z. J., “Securing ad hoc networks”, IEEE Ne twork, Volume 13, Issue 6, Nov.-D ec. 1999, pp. 24 – 30. [17] Strulo, B., Farr, J., and Smith, A., “Securing Mobile Ad hoc Networks — A Motivational Approach”, BT Technology Jou rnal, Volume 21, Issue 3, 2003, pp. 81 – 89. [18] Yang, H., Luo, H., Y e, F., Lu, S. , and Zhang, L. , “Security in Mobile Ad Hoc Networks: C hallenges and Solutions” , IEEE Wireless Communications, Volume 11, Issue 1, February 2004, pp. 38 – 47. [19] Pathan, A-S. K., Alam, M., Monowa r, M., and Rabbi, F., “An Efficie nt Routing Protocol for Mobile Ad H oc Networks with Neighbor Aw areness and Multicasting”, Proc. IEEE E-Tech, Karachi, 31 July, 2004, pp. 97-100. [20] Blackert, W. J., Gregg, D.M., Castner, A.K., Ky le, E.M., Hom, R.L., and Jokerst, R.M., “Analyzing inte raction between distribute d denial of service a ttacks and mitigation technologies”, P roc. DARPA Informa tion Survivability Conference and Exposition, Volume 1, 22-24 April, 2003, pp. 26 – 36. [21] Wang, B- T. and Schul zrinne, H., “An I P traceback mechanis m for reflectiv e DoS a ttacks ”, Canad ian Con feren ce on El ectrical and Computer Engineeri ng, Volume 2, 2-5 May 2004, pp. 901 – 904. [22] Pfleeger, C. P. and Pfleeger, S. L., “Security in Computing”, 3rd e dition, Prentice Hal l 2003. [23] Douceur, J. “The Sybil Attack”, 1st Inte rnational Workshop on Peer-to-Peer Sy stems (2002). [24] Newsome, J., Shi, E. , Song, D, and Perrig, A, “The sybil attack in sensor networks: analysis & defenses”, Proc. of t he third international symposium on Informa tion processing in sensor networks, ACM, 2004, pp. 259 – 268. [25] Culpepper, B.J. a nd Tseng, H.C., “Sinkhole intrusion indicators in DSR MANETs”, Proc. First Internationa l Conference on B road band Networks, 2004, pp. 681 – 688. [26] Karlof, C. and Wagner, D., “Secure routing in wire less sensor networks: Attacks and c ountermeasures”, Elsevie r's Ad Hoc Network Jou rnal, Special Issue on Sensor Ne twork Applications and Protocols, Septem ber 2003, pp. 293-315. [27] Hu, Y.-C., Perrig, A., and Johnson, D.B ., “Packet leashes: a defense against wormhole at tacks in wireless networks”, Twe nty-Second Annual Joint Conference of the IEEE Computer and Communica tions Societies. IEEE INFOCOM 2003, Vol. 3, 30 March-3 April 2003, pp. 197 6 – 1986. [28] Kulkarni, S. S., Gouda, M. G., and Arora, A. , “Secret instantiat ion in adhoc networks, ” Special Issue of Else vier Journal of Com puter Communications on Dependable Wirele ss Sensor Networks, May 2005, pp. 1–15. [29] Du, W., Deng, J. , Han, Y. S., and Va rshney, P. K., “A pairwi se key pre-distribution sche me for wireless sensor ne tworks”, Proc. of the 10th ACM confere nce on Computer and c ommunications security, 2003, pp. 42-51. [30] Oniz, C. C, Tasci, S. E, Savas, E., Ercetin, O., and Levi, A, “Se FER: Secure, Flexi ble and Efficient Routing Protocol for Dis tributed Sensor Networks”, from http://people.saba nciuniv.edu/ ~levi/SeFER_EWSN.pdf [31] Wood, A. D. and Stankovic, J. A., “Denial of Service in Sensor Networks”, Compute r, Volume 35, Issue 10, Oct. 2002 pp. 54 - 62. [32] Slijepcevic, S., Potkonja k, M., Tsiatsis, V ., Zimbeck, S., and Sriva stava, M.B., “On communica tion security in wireless a d-hoc sensor networks”, 11th IEEE International Workshops on Ena bling Technologies: Infrastructure for Collaborative Enterprise s, 2002, 10-12 June 2002, pp. 139 – 144. [33] Ye, F., Luo, H., Lu, S, a nd Zhang, L, “Statistical e n-route filtering of injected false data in sensor ne tworks”, IEEE Journal on Selecte d Areas in Communications, V olume 23, Issue 4, April 2005, pp. 839 – 850. [34] Yuan, L. and Qu, G., “Design s pace exploration for energy-efficient secure sensor ne twork”, Proc. T he IEEE Internati onal Conference on Applicat ion-S pecifi c Systems , Arch itectur es an d Proces sors , 2002, 17-19 July 2002, pp. 88 – 97. [35] Karlof, C., Sastry, N. , and Wagner, D., “Tiny Sec: a link layer security architecture for wire less sensor networks”, Proc . of the 2nd international conference on Embedded networke d sensor systems, Baltimore, MD, USA, 2004, pp. 162 – 175. [36] Younis, M., Yousse f, M., and Arisha, K., “Ene rgy-aware routing i n cluster-based sensor net works” Proc. 10th IEEE Interna tional Symposium on Mode ling, Analysis and S imulation of Computer a nd Telecommunica tions Systems, 1-16 Oct. 2002 pp. 129 – 136. [37] Avancha, S, “A Holistic Approac h to Secure Sensor Netw orks”, PhD Dissertition, Uni versity of Maryland, 2005. [38] Wood, A.D., Stankovic , J.A., and Son, S. H., “JAM: A Jammed-Area Mapping Service for Sensor Networks” , 24th IEEE Real-T ime Systems Symposium, RT SS 2003, pp. 286-297. [39] Cagalj, M., Capkun, S., a nd Hubaux, J-P. , “Wormhole-ba sed Anti-Jamming Tec hniques in Sensor Networks” from http://lcawww.e pfl.ch/Publications/Cagalj/Ca galjCH05-worm.pdf [40] Hamid, M. A ., Rashid, M-O. , and Hong, C . S., “Routing Security in Sensor Network: Hell o Flood Attack and Defense”, to a ppear in IEEE ICNEWS 2006, 2-4 January , Dhaka. [41] Chan, H, Perrig, A., and Song, D., "Random key pre distribution schemes for sensor networks", In IEEE Symposium on Sec urity and Privacy, Berkeley, Cali fornia, May 11-14 2003, pp. 197–213. [42] Eschenauer, L. and Gligor, V. D., "A key-managem ent scheme for distributed sensor netw orks", Proc. ACM CCS'02, 18-22 Novem ber 2002, pp. 41-47. [43] Karakehayov, Z., "U sing REWARD to detec t team black-hole atta cks in wireless sensor ne tworks", in Workshop on Real-World Wirele ss Sensor Networks (REALWS N'05), 20-21 June, 2005, Stockholm , Sweden. ISBN 89-5519-129-4 - 1048 - Feb. 20-22, 2006 ICACT2006
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment