High Performance Cooperative Transmission Protocols Based on Multiuser Detection and Network Coding
Cooperative transmission is an emerging communication technique that takes advantage of the broadcast nature of wireless channels. However, due to low spectral efficiency and the requirement of orthogonal channels, its potential for use in future wir…
Authors: Zhu Han, Xin Zhang, H. Vincent Poor
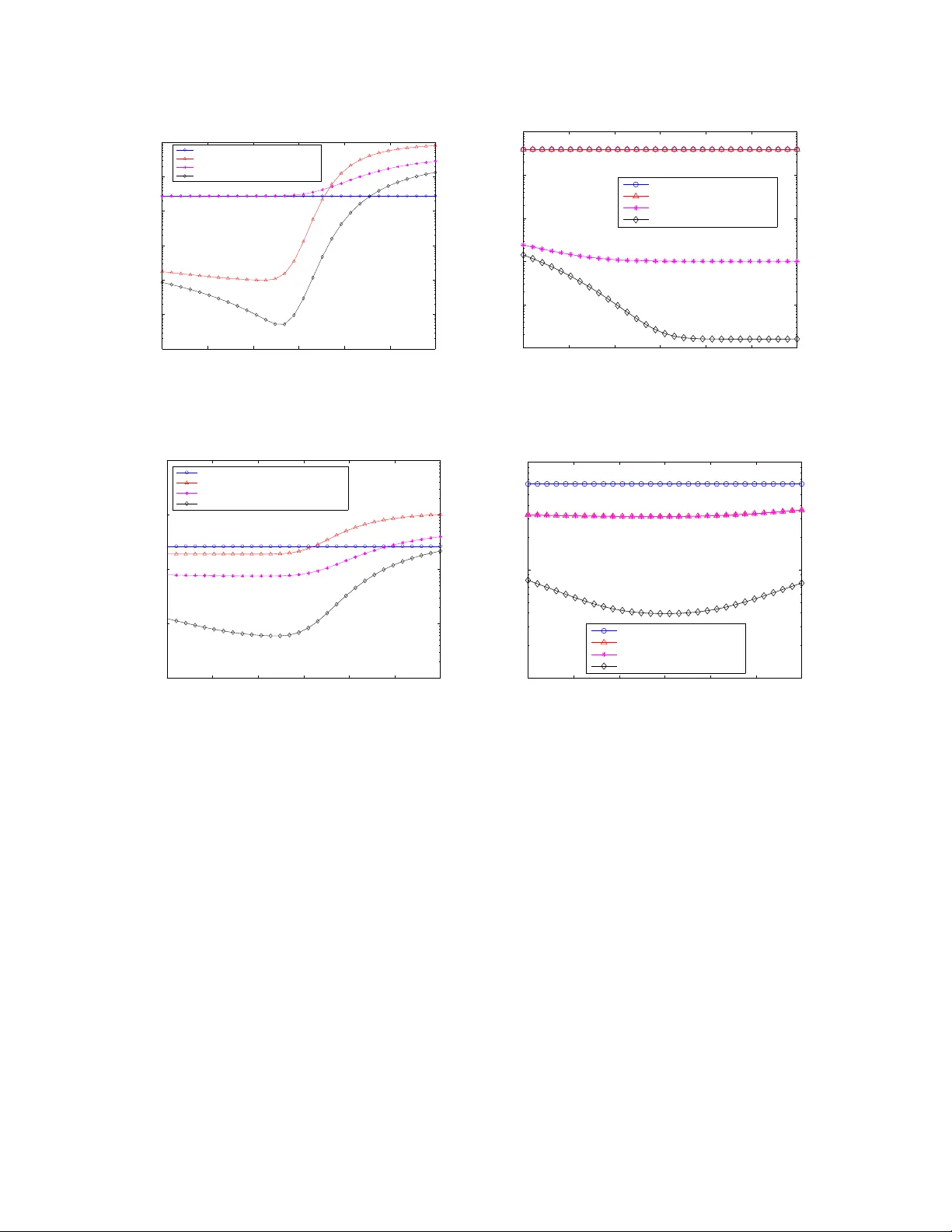
1 High Performance Cooperati ve T ransmission Protocols Based on Multiuser Detection and Network Coding Zhu Han 1 , Xin Zhang 2 , and H. V ince nt Poor 3 1 Department of Electrical and Computer Engineering, Boise State Universit y , Idaho, USA 2 The United T echno logies Research Center , 41 1 Silver Lane, East Hartford, Conne cticut, USA 3 School of Enginee ring and Applied Science , Princeton Univ ersity , New Jersey , U SA. Abstract — Cooperativ e transmission is an emerging com- munication technique that takes adv antage of th e broa dcast nature of wireless channels. H owev er , d ue to low spectral efficiency and the requirement of orthogonal ch annels, its potential fo r use in future wireles s networks is li mited. In this p aper , b y makin g u se of multiuser d etection (MUD) and network coding, coopera tive transmission protoco ls with h igh spectral efficien cy , diversity order , and codin g gain are developed. Compared with the traditional coop- erativ e transmission protocols with single-user d etection, in which t he diversity gain is only for one source user , the proposed MUD cooperati ve transmission p rotoco ls have the merit that the impr ove ment of one user’ s link can also benefit the other users. In addition, usin g MUD at the re lay prov ides an env ironment in which network codin g can be employed. The coding gain and high diversity order can b e obtained by fully utilizing the lin k between th e relay and the destination. From the analysis and simulation re sults, it is seen that t he proposed protoco ls achieve higher diversity gain, better asymptotic efficiency , and lower bit error rate, compared to traditional MUD schemes and t o existing cooperativ e tra nsmission pr otocols. From the simulation results, th e performa nce of the proposed scheme is near optimal as the performance gap i s 0 . 12 dB for aver age bit error rate (BER) 10 − 6 and 1 . 04 dB for aver age BER 10 − 3 , compared to two performance upper bounds. I . I N T R O D U C T I O N Cooperative tran smission [1 ], [ 2] takes a dvantage of the broadc ast natu re of wireless channels to im prove data transmission through co operation a mong network nodes. No tably , relay no des can be employed as v irtual antennas for a source node, so that the mu ltiple inpu t multiple outp ut (MIMO) tech nology can be explo ited ev en with sing le-antenna term inals. Recen t work has explored coo perative tran smission in a variety o f sce- narios, in cluding cellu lar network s [3], ad ho c/sensor networks [4 ]–[6] , W iFi/W iMax [7] and ultra-wideba nd [8]. On e dr awback of existing coo perative transmission schemes is a consequen t reduction of spectral efficiency due largely to the fact that most such tech niques require orthog onal channe ls for the transmissions of cooperating This research was supported by the National Science Foundat ion under Grants ANI-03-38807 and CNS-06 -25637. nodes 1 . This require ment is limiting, as many wirele ss networks, such as 3G cellular n etworks, canno t provide orthog onal ch annels. In this paper, we co nsider coop erative transm ission protoco ls for ne tworks that do not req uire or thogo- nality amo ng the sign aling chan nels of the no des in the network. Such a scenario naturally motiv ates the use of multiuser d etection (MUD) [9] to m itigate the interferen ce c aused by no n-orth ogon al sign aling. Th e perfor mance of MUD is g enerally g ood when interfering users have significantly different link cond itions from one an other . In trad itional MUD, the link cond itions are determined by users’ location s and channel gain s, which are no t contro llable by the designer . However , with co operative tran smission, we have th e op portun ity to optim ize such c onditions by decidin g which re lay will retransmit which user’ s in formation so that th e selected u sers’ link co nditions c an b e optimized fo r overall sy stem p erform ance. A link lev el ana lysis fo r MUD over coopera ti ve transmission can be found in [10]. Recently [11] has considered the join t optimization of MIMO systems with M UD. Howe ver , unlike MIMO MUD in wh ich all info rmation fr om different anten- nas can be obtaine d without limitation, in coop erativ e commun ications the infor mation tr ansmission between the relay (i.e., the virtual anten na) and the destina tion is restrained b y a lossy relay-d estination wireless link. T o overcome this limitation, ne twork cod ing [12 ], [13] provides a poten tial solution. The core no tion of network coding is to allo w mixing of data at intermediate network nodes to impr ove the overall r eliability o f tran smission across the n etwork. A destination receives these code d data packets from various nodes and deduces from them the m essages that were orig inally inten ded fo r that desti- 1 It is worth mentioning that the spectral efficie ncy in the cooperati ve transmission literature is defined as the number of orth ogonal chan nels require d for direct transmission div ided by the overa ll number of channe ls for both direct transmission and relayi ng. This definition is dif ferent from that of spect ral efficie ncy typically used in the adapti ve modulati on literatur e [20]. nation. In [14], it is seen th at in formation exch ange can be efficiently perfor med b y exploiting n etwork coding and th e b roadcast n ature o f the wireless medium . I n cooper ati ve transmission, the relay can b e v iewed as an in termediate network node. In [15], the network coding gains of various co operative diversity protoco ls are examined in d etail. I n this paper, we consider the situation in which MUD is employed at the relays, so tha t a relay ca n o btain info rmation fro m various users an d the n use n etwork co ding by m ixing multiple users’ data and transmittin g co ded inform ation throug h the limited relay-destina tion link. In o ther words, MUD provides an environment for d eploying network coding , and network c oding can ach iev e sub stantial co ding g ain and h igh d iv ersity to overcome the limitatio ns of the relay-destina tion link . In particular, we propose two cooperative transmission protoco ls that utilize MUD and network codin g. In the first p rotocol, realizing that improvement in one user’ s detection can help the detectio n o f the other users in certain types of m ultiuser detector s (e.g., in terference cancelers), we de cide which relay s to use an d whose informa tion the selected relays will retr ansmit such that the overall system per forman ce can be o ptimized at the sink node. In the second proto col, we assume the relays are equipped with MUD. Then th e selected u sers’ informa tion is co ded by ne twork coding and is relayed to the base station. At the base station, the cod ing gain is no t only realized fo r the selected users but also for th e other u sers becau se of M UD. More over , we develop two perf ormance upper bo unds to ev aluate the propo sed schemes. Pr actical implementatio n issues are a lso discu ssed. From both an alytical and simulatio n results, it is seen that the p roposed protoco ls achiev e higher di versity and codin g gains, better asymptotic efficiency , and lower bit err or r ate (BER) than existing schemes without sacrificing spectral efficiency . The pro- posed scheme ac hiev es perfo rmance less th an 0. 12dB away from the perf ormance up per boun ds when the av erage BER equals 10 − 6 , and 1.04dB when BER equals 10 − 3 . This paper is o rganized as fo llows: I n Section II, system models a re given for coo perative transmission and MUD in a network consisting of a so urce node (e.g., a mobile term inal), a sink nod e (e.g ., a base station or access po int) and a set of relays. I n Sec tion III, the two above-men tioned pro tocols are construc ted. In Section IV, the pr operties o f th e p roposed proto cols are analyzed. Simulation results are shown in Section V, and conclusion s are drawn in Sectio n VI. 1 2 3 K Base Station Stage 1 Stage 2 MUD D D D MUD Data from Stage 2 Fig. 1. Proposed Cooperati v e System model I I . S Y S T E M M O D E L W e co nsider an uplink synch ronou s cod e-division multiple-acce ss (CDMA) system with Gaussian am bient noise 2 . Th ere are K synch ronou s uplink users ( i.e., terminals) ea ch with a single antenna. He re th e num- ber of users is no more th an the numb er of available CDMA codes. Among these termin als, N can ser ve as relays. This system model is illustrated with N = 1 in Figure 1. At the first transmission stage, all users except the relay s send info rmation, and the r elays listen (and perfor m MUD if they have the ability) . At the second stage, the oth er users send the ir next inf ormation signals, while the relay s send a certain user’ s inf ormation or the network ing-cod ed info rmation from th e results o f MUD applied at the fir st stage. I n the sink n ode, which for conv enience we will refer to as the a b ase station, all o f the other users’ in formation fro m the first stage is delayed by one time slot an d jo intly detected with the inf ormation sent by the r elays at the seco nd stag e. Since the users cannot tran smit and r eceiv e at the same time or on the same fr equency , to r elay on ce costs at least two time slots fo r listening an d relayin g. So the spectral e fficienc y is K − N K , and thus when the nu mber of u sers is much larger than the numb er of relays the spectral efficiency app roaches one. On the other han d, in the trad itional cooperative transmission with o ne-relay and one-sou rce pair , N = K 2 . In this case, th e spectral efficiency is 1 2 . W e d enote by R the g roup o f r elay termin als, and by L th e gr oup of terminals that are listening an d will serve as relay s in the next time slot 3 . Define the set K for all K users. In the first stage, the rec ei ved signa l a t th e ba se 2 Note that asynchrono us CDMA can be treated simila rly . 3 This is beca use of half duple x. 2 station can be exp ressed a s y ( t ) = X k ∈ K \ R \ L A k b k s k ( t ) + X k ∈ R A k z k s k ( t ) + σ n ( t ) , (1) and at user i ∈ L , who is listening and p reparin g for a relay in the n ext time slo t, as y i ( t ) = X k ∈ K \ R \ L A i k b k s k ( t ) + X k ∈ R A i k z k s k ( t ) + σ i n i ( t ) , (2) where A k is the rec ei ved am plitude o f th e k th user’ s signal at the b ase station, A i k is the received amplitud e of the k th user’ s signa l at relay i , b k ∈ {− 1 , + 1 } is the data sy mbol transmitted by the k th user , z k is the relayed bit, s k is the unit-en ergy sig nature wa veform ( i.e. Pseud o-rand om cod e) of the k th user , n ( t ) and n i ( t ) are the normalized white Gaussian n oise, an d σ 2 and ( σ i ) 2 are the b ackgro und n oise po wer densities. For simplicity , we assume σ = σ i , although the more general case is straightfo rward. The rece i ved signal vectors at the base station and at the relay after p rocessing b y a m atched filter bank can be written as y = RAb + n , (3) and y i = RA i b + n i , (4) where R is the signal cross-corr elation matrix, whose elements can be written as [ R ] ij = Z T 0 s i ( t ) s j ( t ) dt, (5) with T the in verse of the data r ate, A = diag { A 1 , . . . , A K } , A i = d iag { A i 1 , . . . , A i K } , E [ nn T ] = E [ n i n iT ] = σ 2 R , and b = [ b 1 , . . . , z i , . . . , 0 , b K ] T consists of symbo ls of d irect-transmission, r elay , an d listening users. In pa rticular, b i is th e dire ct-transmission symbol, z i is th e relay sy mbol, an d the listenin g r elay has zer o to tr ansmit d ue to th e h alf dup lex assumptio n. From the co operative transmission perspective, in the first stage u ser k ∈ K \ R \ L transmits its sig nal directly to the base statio n, and u ser i ∈ L listens. In th e second stage, the users listening in the first stage become relays (set R ) a nd relay the infor mation to the base station. At the b ase station, the info rmation a t th e first stage is delayed by one time slot and then is combin ed with the informa tion at the second stage. In this paper, we will in vestigate th e BER performan ce of MUD under cooper ativ e tra nsmission. Specifically , we will consider optimal MUD and the successive can cella- tion detector, wh ich is one type of de cision-driven MUD. As poin ted out in [9 ], there is n o explicit expression for the erro r probab ility of the o ptimal multiuser dete ctor , and bounds must be u sed. A tight upper boun d is provided by the following propo sition f rom [9]. Pr oposition 1: The BER o f the i th user for optimal MUD is given by P i,opt r ≤ X ǫ ∈ F i 2 − ω ( ǫ ) Q k S ( ǫ ) k σ (6) where ǫ is a possible error vecto r for user k , an d k S ( ǫ ) k 2 = ǫ T H ǫ = ǫ T ARA ǫ . ω ( ǫ ) is th e n umber of nonzero elements in ǫ , and F i is the subset of indecomp osable vectors. (See [9] f or details.) For the successi ve can cellation detector, a r ecursive approx imation fo r th e erro r prob ability is given by the following p roposition [9]. Pr oposition 2: The BER o f the i th user for successive cancellation is given app roximately b y P i,sc r ≈ Q A i q σ 2 + 1 M P i − 1 j =1 A 2 j + 4 M P K j = i +1 A 2 j P j,sc r , (7) where M is the spr eading g ain. The cancellation ord er is th at u ser K is de tected first, then user K − 1 and so on. In the deno minator in the argument of the Q -f unction in (7), if erro rs exist for the previously de tected u sers, the interfer ence cau sed to the latter dete cted u sers is at four times th e power lev el of the or iginal sign al. So if the error proba bilities o f the previously detected users can be r educed by coop erativ e transmission, the overall perfor mance can be g reatly imp roved. Notice that the BERs in (6) and (7) are function s o f the users’ received amplitu des. Th ese in turn are functio ns of the user locations and the network top ology , which are fixed in traditional m ultiuser chan nels. As will be shown later , in o ur pr oposed schemes, we have the freed om to select wh ich users will serve as re lays and which users’ informa tion to r elay . Th is f reedom allows us to mod ify the link qua lities an d achieve th e optimal perfor mance in terms of overall BER at th e base station. I I I . T W O C O O P E R AT I V E T R A N S M I S S I O N P R OT O C O L S In this section, we p ropose two coo perative tra nsmis- sion proto cols. T he first p rotocol seeks to exploit the fact th at MUD ca n im prove the recep tion of all signals because of the mitig ation of interference fro m th e stron g ones. MUD is u sed in the base station, while at th e relay single u ser detection is employed. The second p rotocol further exploits n etwork co ding in the r elay to make fu ll use of the relay -destination channe l and to p rovide better 3 T ABLE I C O O P E R ATI V E T R A N S M I S S I O N P R O T O C O L S 1. At S tage 1, the sources send pack ets, the base s t a t i o n s t o r e s them, and the relays decod e them. 2. After Sta ge 1, the base station decides which us e r s ’ p a c k e t s are to be relayed ac cording to (9). 3. At S tage 2, using the fee dback from the base st a t i o n , t h e relays forward the select ed users’ inf ormation so a s t o optimize the decodin g. 4. After Sta ge 2, two-stage combi ning and MUD a r e p e r f o r m e d at the base station. coding gain and di versity g ain. I n this proto c o l , M U D i s employed at both the base station an d the r e l a y . A. Pr otocol 1: Joint MUD and Coo perati v e T r a n s m i s - sion Suppose termin al i is selected as the r e l a y a n d i t forwards user m ’ s inform ation. At the b a s e s t a t i o n , following a match ed filter bank, max ima l r a t i o c o m - bining (MRC) is used to com bine the s i g n a l s f r o m these two term inals. Since o ptimal MUD a n d d e c i s i o n driven MUD algorithm s are no nlinear, a c l o s e d - f o r m expression for MRC is not a vailable. In our a n a l y s i s , w e assume that so me me thod, such as a th res h o l d t e s t [ 2 ] or cyclic red undan cy check (CRC), is emp l o y e d s o t h a t the potential r elays an d the b ase station c a n d e t e r m i n e with som e cer tainty wheth er or not the det e c t e d s i g n a l s are co rrect. In stead of MRC b efore decod i n g , t h e fi n a l decision is based on the de coded signals in b o t h s t a g e s . Thus, an error o ccurs on ly if the signals in b o t h s t a g e s are wron g. So the pro bability o f error can b e w r i t t e n a s P m r = P m 0 r (1 − (1 − P mi r )(1 − P i 0 r ) ) . ( 8 ) The e rror probabilities of d ata transmission f r o m u s e r m to the base station, fro m user i (i.e., the relay) to the base station, and from user m to user i are d enoted as P m 0 r , P i 0 r , and P mi r , respe ctiv ely . Notice that the re is no need fo r MUD at the relays f or the first protoco l. The issues to be considere d here are which relays to select among th e po tential u sers ( selecting i ), and wh ose data to retransmit (selecting m ) . The per forman ce ind ex for system op timization is the overall BER. If on ly one relay is selected 4 , the prob lem f ormulatio n to minimize the overall BER can be written as min ( i,m ) X j ∈{ K \ i } P j r . (9) 4 For the multip le relay case, if no user’ s inf ormation can be relaye d more than once, the problem formula tion is the same. Otherwi se, we need to change (8). As a result, the searching s pace will increase expo nentiall y with the number of relay s. In that case, low comple xity heuristi cs must be dev eloped, which is beyond the scope of this paper . 1 2 3 K MUD t 1 t 2 t 3 Network Coding Selection t K Base Station MUD b 2 b 3 b K b K b 2 b 3 b 2 ⊕ b 3 b 2 ⊕ b 3 b 2 ⊕ b 3 Fig. 2. Joint considerati on of MUD and net work codi ng T o optim ize (9), we propo se an algorithm shown in T able I. The basic idea is that the base station can k now after Stage 1 which u sers’ links need to b e improved so as to max imize the network perfor mance. Mo reover , the informa tion o f the relay such as P mi r and P i 0 r can also be feeded back to the b ase station. So the o ptimal parameter pair ( i, m ) can b e selected 5 , and th e co rrespond ing informa tion is sent. At the base station, the info rmation sent at th e first stage is stored and co mbined with the relay’ s infor mation at the seco nd stage. Consequ ently , the perfor mance of all users can be improved. The only control sig naling req uired is to send information thr ough a control ch annel to info rm the corr espondin g relay which user ’ s infor mation to forward. B. Pr otocol 2: W ith Consideration of Network Co ding The secon d protoco l seeks to exploit the fact th at MUD in th e base station and the relay provid es a possi- ble d ata-flow structure for jointly optim izing MUD and network codin g. In Figure 2, we illustrate an example in which ther e are K users and user 1 is assigned as the relay . At the first stag e, users 2 through K send their own in formation , while th e base station and user 1 listen. At the seco nd stage, user 1 sends the c oded informa tion (here b 2 L b 3 , wh ere L is XOR function ). Then the base station ca n improve the decoding of user 2 5 Here we use the exhaust iv e search for the optimal pair . Some heuristi c fast algorithms such as greedy solution can be easily con- structed . 4 and u ser 3 . Th e p erform ance gain is du e to the ne twork coding. In gen eral, we can f ormulate joint MUD and network coding as fo llows: As a relay , user i selects a set of users M i , and th en transm its b m L · · · L b n , wh ere m, . . . , n ∈ M i . No tice that M i is a subset of all users that are successfu lly decoded at the first stag e by user i . At the base station, the user’ s error p robability is given by: P m r = P m 0 r { 1 − (1 − P mi r )(1 − P i 0 r ) · Y n ∈ M i /m [(1 − P ni r )(1 − P n 0 r )] } , ∀ m ∈ M i (10) and P j r ≤ P j 0 r , ∀ j / ∈ M i . (11) The first term in (10) repre sents the direc t transm ission error prob ability . The ter m in the paren theses of (10) represents the error prob ability fr om the relay using network cod ing. Successful transmission fro m the relay occurs only if, withou t network coding gain, all users in M i are decod ed c orrectly by user i , the tran smission from user i to the base station is correct, and all other users are co rrectly d ecoded at the b ase station . Notice th at co mpared with (8), the error pr obability for a spe cific user migh t be worse. Howev er, since in ( 10), multiple users’ BERs ca n be imp roved, the overall BER of the system can be further improved under careful optimiza tion. Th e inequality in ( 11) holds sinc e the c ancellation of some successfu lly decod ed users’ informa tion can improve the other users’ d ecoding . W e need to select relay i from the set R of size N , and the set M i which rep resent whose in formatio n should be relayed by user i . So the general problem formulatio n fo r both Pro tocol 1 and Pro tocol 2 can be written as min R , M i X j ∈{ K \ R } P j r . (12) The algo rithm f or Proto col 2 is similar to th at of Protocol 1 except that, in Proto col 2, the r elays transmit the n etwork cod ed symbol in the second stage. Com- pared with the first pro tocol, Protocol 2 ca n impr ove more than one users’ signal strength at the b ase station in Stage 2 . This is because several u sers’ infor mation can be carried u sing n etwork coding . H owe ver , if too many users’ info rmation is c oded with network codin g, the e rror c orrection cap ability in the base station will be redu ced. So the re is a tradeoff on h ow m any user s’ informa tion to be encoded. Mo reover , Protocol 2 r equires MUD at th e r elay whic h cou ld be a mo bile han dset. Since th is requ irement in creases the cost and power consump tions of relay s, this co uld be an issue. I V . P E R F O R M A N C E A N A L Y S I S In this section, we first examin e the div ersity order and coding gain of the prop osed pro tocols. Th en, we give a perf ormance up per bound using MIMO- MUD. Next, we study a special case for how the relay changes the asymptotic multiuser effi ciency . Finally , we gi ve an exact expression for a symmetric case. A. Diversity Or der a nd Coo perative MUD Gain First we study the d i versity or der for the user s who se informa tion is relay ed. Then we provide another p erfor- mance gain metric, coop erative MU D gain, to q uantify the additio nal gain to the o ther u sers. For Protoco l 1, the div ersity order (i. e., the nu mber of in depend ently received signals) can be u p to N + 1 for the relay ed user, while the remaining un-relay ed users h av e d iv ersity or der 1 . F or Pro tocol 2, th e diversity order for all u sers is up to N + 1 . Fro m th e simula tion results presen ted below , we see tha t the h igh d iv ersity order c an b e achieved compared to a perform ance bound (which has b een shown to have the h igh diversity or- der). Rigo rous proo f for th e hig h diversity order of the propo sed scheme is very difficult to achieve, due to the intractability of BER expressions for MUD detec tors. Howe ver , we provide an intuitive a nalysis in the sequel. For P roto col 1 after Stage 1, we order the received sig- nals at the base station acco rding to their SINRs, where user K has the hig hest SINR (i.e. th e lowest BER). W e assume all N relays select user K ’ s in formation to retransmit if the relay decod es it co rrectly . T he re ason to select user K with the high est SINR is to limit error propag ation in ( 7). The diversity order f or user K is N + 1 since N + 1 copies of user K ’ s inf ormation are transmitted via 1 dire ct link and N relay links an d all those link respon ses are indepe ndent. Becau se only user K ’ s copy o f the info rmation at Stag e 1 is retransm itted, the d iv ersity o rder o f th e o ther users is still 1 . If th e N relays select different users’ inf ormation to r elay , the div ersity orders of these users depend o n how many relays retran smit their in formatio n. For Protocol 2, at the second stage th e relays retrans- mit the following informa tion z i = M b j , j ∈ M i . (13) Here we assume M i includes all users, i.e., M i = K . When the SINRs are sufficiently high (i.e. the multiple access interf erence is sufficiently low), th e ch annels between the senders and r elays approa ch id eal links. All direct links are indepen dent a nd approach ideal l inks. For example in Figu re 2 , at the second stage after network decodin g, t 2 will receive two copies of b 2 from direct 5 transmission an d fr om t 1 if b 3 has sufficiently small BER. In a g eneralized case, if the size o f M i is K , the div ersity o rder fo r every user is N + 1 f rom the N relays and the dir ect link , when the SINRs are sufficiently high. An other interp retation is that wh en the SINRs become sufficiently large, the links b etween th e relays and base station are sufficiently g ood. Consequen tly , the co operative system with Pro tocol 2 is eq uiv alent to MIMO MUD system with diversity order of N + 1 . On the o ther hand, if th e diversity o rders of cer- tain users increase, the remaining users have better perfor mance since their inter ference (user K ’ s signal) can be mor e successfully c ancelled. T o quantif y th e perfor mance g ain, we d efine the f ollowing qu antity . Definition 1: Th e cooperative MUD gain ρ i is defined as the SINR improvement ratio for the remaining users, due to th e link improvement g ained wh en the oth er users use co operative MUD rec eiv ers. For the successiv e c ancellation mu ltiuser d etector of Protocol 1, we have ρ K − 1 = σ 2 + 1 M P K − 2 j =1 A 2 j + 4 M A 2 K P K r σ 2 + 1 M P K − 2 j =1 A 2 j + 4 M A 2 K ˆ P K r , (14) where ˆ P K r is user K ’ s new BER an d ˆ P K r ≈ ( P K r ) N +1 . If 1 M A 2 K >> σ 2 + 1 M P K − 2 j =1 A 2 j , th e MUD ga in can be significantly large. For the MUD gains o f oth er users, we can calculate P K − 1 r , . . . , P 1 r recursively . For th e optimal MUD of Protocol 1, for each possible error vector ǫ , the MUD gain can b e ap proxima ted by ρ ǫ ≈ ǫ T diag { A i , ˆ A j } R diag { A i , ˆ A j } ǫ, (15) where ˆ A j is the impr ovement of the j th user’ s sign al strength and diag { A i , ˆ A j } is the sam e as m atrix A (d e- fined in (3)) e xcep t that A j is replaced by ˆ A j . Notice that the ch annel improvement ˆ A j is upp er b ounded by that of MRC of direct tran smission and relay tran smission. For th e successi ve can cellation detector of Protoc ol 2, the MUD gain fo r the user with th e second stron gest link is the same as (14). For the remaining user s, the MUD gain is larger since higher diversity order for all the users with larger SINR reduces the er ror pr obabilities, wh ich affect the noise of this user . For th e optim al MUD of Protocol 2, the elemen ts of th e matrix A increa se (i.e., ev ery link A i is enhanced with d iv ersity N + 1 ). So the BER for each po ssible error vector is also r educed and so is the overall BER. B. P erformance Bo unds W e develop two per forman ce bounds f or the proposed cooper ati ve transmission protoco l with MUD. First, in MIMO MUD [1 1], we can assume infinite band width between the relays and the base st ation. Th e performance under these cir cumstances gives us an uppe r boun d f or Protocol 2 of coo perative transmission MUD. Her e we assume that the relay is p erfectly connected to the desti- nation, and that combinatio n is performed after decoding. Decoding er ror occu rs when the dire ct transmission and all of the N sou rce-relay links fail, i.e. for the high SINR case we have the first perfor mance up per bo und given by P k r ≥ P k 0 r Y i ∈ R P ki r , (16) where P k 0 r is th e BER for dire ct tran smission and P ki r is the transmission f rom user k to relay i . For MI MO MUD, the diversity ord er is N + 1 . Second, if we assume that the links between the source and relays are p erfect and the SI NRs f or the two stages can be d irectly add ed before the d ecoding , we can obtain another perfor mance upp er bou nd fo r Pr otocol 1. If we assume all relays retra nsmit user k ’ s infor mation, for the successiv e cance llation detecto r , we can d eriv e a bou nd in the following recursive form: P k,sc r ≥ Q A k + P i ∈ R A i q σ 2 + 1 M P i − 1 j =1 A 2 j + 4 M P K j = i +1 A 2 j P j,sc r . (17) Notice th at the interference terms fro m the stronge r users in the denom inator still hav e amplitude s A j ’ s, since the interferen ce co mes fr om the first stage of the cooper ati ve transmission. For optimal MUD, the second perfor mance upp er boun d can b e obtain ed by setting A = d iag { A 1 , . . . , A k + P i ∈ R A i , . . . A N } . Another interpretatio n of th e ab ove two boun ds is as follows. For the boun d in (16), all rela ys are located close to th e base station so that t he relay-destinatio n link s are sufficiently go od. For the b ound in ( 17), all source users and relays are assumed to be closely located in a cluster away fr om th e base station. The sou rce-relay links are assumed to be perfect. In reality , the sourc e nodes and re lay nod es are located ra ndomly . So the real perfor mance is worse th an the two p erform ance upp er bound s - i.e., the bou nds may n ot be tight. C. Asymp totic Multiuser Efficiency In th is subsection , we stud y a special case in which there are two users a nd on e re lay to investigate the perfor mance improvement that results fr om u sing MU D. First, we revie w the definition of asympto tic multiuser efficiency . 6 Definition 2: T he asymptotic multiuser efficiency is defined as η k = lim σ → 0 σ 2 A 2 k log 1 P k r (18) which quantifies th e degradation in SINR suffered by a user due to the presen ce of o ther user s in th e ch annel. Similarly to the second perfor mance upp er bo und in the previous subsectio n, we make the app roximatio ns that the relay can always deco de corr ectly and that the base station can u se maxima l ra tio co mbining of th e direct and relay transmissions. In this id eal case, the multiuser efficiency of optimal MUD can been expre ssed as η 1 ≈ min 1 , 1 + ( A 2 + A r ) 2 A 2 1 − 2 | ρ | A 2 + A r A 1 , 1 + A 2 2 ( A 1 + A r ) 2 − 2 | ρ | A 2 A 1 + A r , (1 9) where ρ is the c ross-correlatio n, and A 1 , A 2 , and A r are the chann el gains to the base station for user 1 , user 2 and the relay , respectively . In Figu re 3, we show the asympto tic multiuser effi- ciency with A 1 =1 and ρ = 0 . 8 . The key id ea here is that the asymp totic multiuser efficiency is bad when the ratio of A 2 and A 1 is around ρ , but with the relay’ s help this ratio can b e changed so that the asymptotic multiuser efficiency can be greatly improved. W e can see that when the relay is close to the destination (i.e. A r is large), th e asymptotic multiuser efficiency can be alm ost 1 . This is because the r elay can alw ays im prove the strong er user’ s link so that the difference is even larger . Conseq uently , the multiu ser efficiency can b e greatly improved. When the r elay m oves far aw ay from the destination , the asymptotic m ultiuser e fficienc y imp rovement is reduced, since A r decreases and the relay is less effective. W e note that this compar ison is un fair , since the bandwidth is incr eased with the presen ce of the r elay . Howev er, when the nu mber o f u sers is sufficiently larger than the number o f relays, this incr ease is n egligible. D. Special Ca se Ana lysis In this subsection, we stud y a special case to examine issues such as how m any r elays sho uld be used for network co ding and which r elays sh ould be selected. W e consider th e case in wh ich several source no des are loca ted close to each othe r and far away fro m the base station. I n this situation, th e links betwe en the sources to one relay are the same an d the links from the different sour ces to the destinatio n are eq ual. T his special case fits the scen ario in which th ere is no base station in a com munity . The er ror pro babilities in curred 0 0.5 1 1.5 2 2.5 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 User 2 Channel Gain/User 1 Channel Gain: A 2 /A 1 Asymptotic Efficiency User 1 Cooperative MUD Improvement, ρ =0.8 No Relay Relay A r =0.5A1 Relay A r =A1 Relay A r =1.5A1 Fig. 3. Asymptotic multiuser ef ficienc y improv ement as a function of users’ cha nnel gains A 2 / A 1 in tr ansmission from source to destinatio n, fro m source to relay an d from relay to destination a re P sd r , P sr r , and P r d r , r espectively . W e assume Protocol 2 is used and we suppose the r elay includes M o ut o f K sources for networking c oding. The co ded users’ error probability is giv en by P r = P sd r [1 − (1 − P sr r ) M (1 − P sd r ) M − 1 (1 − P r d r )] . (20) There are K − M users without network codin g gain and M u sers with network cod ing ga in. T o minim ize the overall average BER, we h av e min M P ave r = 1 K { P sd r ( K − M ) + M P sd r [1 − (1 − P sr r ) M (1 − P sd r ) M − 1 (1 − P r d r )] } . (21) It is easy to show that th e op timal nu mber of users to be includ ed in network coding is M ∗ = min { K, ar g min[ P ave r ( M 1 ) , P ave r ( M 2 )] where M 1 ≤ − 1 log[(1 − P sr r )(1 − P sd r )] ≤ M 2 (22) where M 1 and M 2 are the two non -negative integers closest to − 1 log[(1 − P sr r )(1 − P sd r )] . From (22), we can make th e fo llowing observations. First, if the source-to-relay and relay-to-de stination chan- nels are relati vely g ood, it is optimal to inclu de all user s in network cod ing. For example, when (1 − P sr r )(1 − P sd r ) = 0 . 99 , a s long as K < 100 , it is optimal. Second, in ord er to minimize P r , th e relay needs to have a large value of (1 − P sr r )(1 − P sd r ) . Th is fact suggests a rela y selection criter ion in p ractice. 7 E. Implementa tion Discussion In this sub section, we discuss some implementation issues. First, ou r pro posed proto cols do n ot work for certain typ es of MUD. For th e decorr elating detector , the propo sed schem es are not suitable, since the performanc e is c ontrolled by the cross correlation. For the m ini- mum mean squ are error (M MSE) receiver , the prop osed scheme is not effecti ve, since the im provement of o ne user’ s detec tion does no t impr ove th at of the o thers for linea r detector s. MMSE detector perfor mance und er cooper ati ve commu nication is inves tigated in [16] . A variety of o ther MUD recei vers can still be used , such as the decision feedback MUD, m ultiple stage MUD, b lind MUD, and their com binations with the linear MUD. Bu t, this complica tes the an alysis o f th e pro posed schemes due to the nonlinear ity of these o ther MUD techn iques. Second, we discuss the asymptotic behavior of large systems [17] [18] [19]. Denote by β the system load (i.e., the number of active users divided by the numb er of cod es in CDMA). For the d ecorrelato r , the multiuser efficiency is given by decorre lator: η = 1 − β . (23) W e c an see that our pr oposed schem e cannot work at all in this case. For th e MMSE detector, the m ultiuser efficiency is ob tained b y solving the follo wing equation: MMSE MUD: η + β E η P σ 2 n + η P = 1 , (24) where σ 2 n is the noise power le vel and P is the rec eiv ed power , over wh ich the expectation is c arried. From (24), we can see that our pr oposed scheme can improve th e relayed users’ rando m received powers. So the r esulting η is larger . Howe ver , th is im provement is for th e relayed users only and can not “p ropag ate” to benefit the o ther users. For optim al MUD, the following eq uations [17 ] [18] [19] can be solved with the variables are E , F , m , and q : E = 1 σ 2 + β (1 − m ) , (25) m = 1 − E P 1 + P E , (26) F = σ 2 n + β (1 − 2 m + q ) [ σ 2 + β (1 − m )] 2 , (27) q = E P 3 E 2 + P 2 F (1 + P E ) 2 , (28) where σ 2 equals σ 2 n when individual MUD is used and equals 0 wh en jo int MUD is used. Then , the multiu ser efficiency is ob tain by optimal MUD: η = E 2 F σ 2 n . (29) From (25) to ( 28), we can see that if the expectation over the rando m rec ei ved po wer is improved by the pro posed scheme, the para meters af fect each oth er recursively . As a result, the m ultiuser efficiency in (2 9) can be greatly improved. This is another d emonstration of our main idea that improving one u ser’ s link can benefit the others. Finally , we d iscuss some prac tical implemen tation issues and h ow the p roposed schemes ca n be in tegrated into existing network s such as cellu lar networks. Be- cause of handware limitations, it is often d ifficult to implement MUD in a mo bile terminal. Howe ver , we can implement Protocol 1 in the m obile terminal to relay th e o ther u sers’ info rmation. I n the ba se station, the M UD perfo rmance can thereby be improved. T o optimally improve the system perform ance, the issues of r elay selection and who se in formatio n to relay need to be solved. If a service provider can set u p fixed relays which are much cheaper than the base station, the second protoco l can b e employed to h av e MUD in th e fixed relays. Mor eover , netw ork co ding can be used to pr ovide full div ersity g ain. The issues of wher e the fixed relays should be lo cated and how many users shou ld participate in n etwork co ding ne ed to be examin ed. The simulation s in the next section examine all o f these issues. V . S I M U L A T I O N R E S U LT S In ord er to demo nstrate the effecti veness o f the p ro- posed pr otocols, we present simu lations with the follow- ing setup . First, we conside r a one -dimension al model in which a b ase station, a relay , and users are located along a line. T he base station is located at position 0 in the coor dinate system, the two users ar e located at position 4 an d position 6 , and the relay c an m ove fr om position 0 . 5 to position 3 . 5 . T he lo ss factor for large scale prop agation is 3 . In the simu lation, we assum e that all users an d the re lay use the same tran smitted power , i.e., there is no power contr ol. W e a lso assume the rece i vers have the same add iti ve noise with power lev el 0 d B. MUD is used only fo r Protoc ol 2 . Figure 4(a) and Figur e 4(b ) show the average BER at the b ase station as a f unction o f th e tran smitted p ower of the u sers and of the rela y fo r succ essi ve can cellation and optimal MUD, respectively . The relay’ s lo cation is fixed at position 1 . 6 . W e can clearly see the hig her diversity order of BER vs. power for th e pr oposed protoc ols. When the transmitted p ower is sufficiently high, the limiting factor o f successive cancellatio n’ s per formanc e is the interf erence. And that is why we see th e curve 8 10 2 10 3 10 4 10 5 10 −7 10 −6 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 trasmitting power BER BER vs. Transmitting Power, Successful Cancellation w/o relay relay bit of user 1 relay bit of user 2 relay XOR of bits from both users MIMO−MUD bound bound 2 (a) Successi ve can cellati on 10 2 10 3 10 −6 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 trasmitting power BER BER vs. Transmitting Power, Optimal MUD w/o relay relay bit of user 1 relay bit of user 2 relay XOR of bits from both users MIMO−MUD bound bound 2 (b) Optimal MUD Fig. 4. The averag e BER as a function of the transmitted po wer with the relay loca ted at 1.6. flattens when the transmitted p ower gr ows. W e a lso note the large d ifference in per forman ce between the case with the relay and th e case without. Anoth er intere sting observation is that, for successive ca ncellation in a certain transmitted power range, relayin g the first user’ s symbol is better, wh ile in ano ther transmitted power range, relayin g the seco nd user’ s sym bol is better . For optimal MUD, to relay th e symbol of u ser 2 is always the best choice. Relaying the XOR o f bo th users’ symbo ls is always the best p rotocol, but this r equires the use of M UD at the relays. W e also show the MIMO-MU D perfor mance bound and boun d 2 which assumes per fect channels from source to relay . Th e two bounds are similar except when suc cessi ve can cellation hits an err or floor . The bounds f or optimal MUD are tighter especially when the BER is sufficiently low . When BER = 10 − 6 , for optimal MUD , the pe rforman ce gap between the bound s and the p rotocol in which the relay XORs bits from bo th users is 0 . 12 dB. When BER = 10 − 3 , the gap is 1 . 04 dB. Figure 5 (a) and Figure 5(b ) show the average BER at the b ase station as a fu nction of th e relay loc ation. The re are two users, and b oth users and the relay u se high transmitted power of 40 dB for suc cessi ve cancellatio n and 30 dB for optima l MUD. Th e cu rves corr espond to the case with out the re lay , with the relay re-transmittin g user 1’ s (lo cated at po sition 4 ) sym bol, with r elay re- transmitting user 2’ s (located at po sition 6 ) sym bol, and with the r elay re-tr ansmitting the XOR of both users’ symbols (n etwork coding) , respectively . The first o bservation is that the location of the relay plays a vital r ole in the system p erform ance, espe cially for the successive cance llation d etector . For successiv e cancellation, the system with a relay performs better than the system withou t a relay , on ly if the relay’ s distance from the base station is below position 2 . 8 using network coding and b elow po sition 2 . 2 wh en the relay helps user 1. If the successive cancellation d etector is used, the system p erform s better without a r elay if th e relay is too close to the user group. This is because, f or successiv e cancellation, the p erform ance is better if the users have different received p ower levels. A relay that is too close to the user g roup will increase the err or rate of the successiv e cancellation detecto r becau se o f its inter ference. O n the other han d, for o ptimal MUD, the perfor mance is alw ays better with a relay , especially when the relay is clo se to th e users. H owe ver , the perfor- mance improvement has a floor . The second observation is th at there is a “sweet spot” for suc cessi ve canc ellation eith the location of the r elay ar ound po sition 1.8. This is beca use the relay’ s d ecoding p erform ance dro ps if it is located too far away from the sources. The thir d observation is that th e network coding p rotocol with the relay re-transmitting th e XOR of both user s’ sym bols always perf orms b etter than that when the relay ju st re- transmits one user’ s symbo l. Figure 6(a) and Figure 6(b ) correspo nd to sim ilar setups except th e tran smitted power is low h ere ( 30 d B for successive cancellation and 20 d B for optimal MUD). For su ccessi ve cancellation, we observe perfo rmance behavior similar to the high transmitted p ower case, except that the relay can still h elp when its location is close to the users. Th e “sweet spot” remains essentially at the same place. For optim al MUD, there exists a 9 0.5 1 1.5 2 2.5 3 3.5 10 −7 10 −6 10 −5 10 −4 10 −3 10 −2 10 −1 location of relay BER BER as a Function of Relay Location, Successive Cancellation, High SINR w/o relay relay bit of user 1 relay bit of user 2 relay XOR of bits from both users (a) Successi ve can cellati on, po wer = 40 dB 0.5 1 1.5 2 2.5 3 3.5 10 −7 10 −6 10 −5 10 −4 10 −3 10 −2 location of relay BER BER as a Function of Relay Location, Optimal MUD, High SINR w/o relay relay bit of user 1 relay bit of user 2 relay XOR of bits from both users (b) Optimal MUD, po wer = 30 dB Fig. 5. The averag e BER as a function of the location of the relay with high a verage SINR. 0.5 1 1.5 2 2.5 3 3.5 10 −4 10 −3 10 −2 10 −1 10 0 location of relay BER BER as a Function of Relay Location, Successive Cancellation, Low SINR w/o relay relay bit of user 1 relay bit of user 2 relay XOR of bits from both users (a) Successiv e cancel lation, power = 30 dB 0.5 1 1.5 2 2.5 3 3.5 10 −3 10 −2 10 −1 location of relay BER BER as a Function of Relay Location, Optimal MUD, Low SINR w/o relay relay bit of user 1 relay bit of user 2 relay XOR of bits from both users (b) Optimal MUD, power = 20 dB Fig. 6. The averag e BER as a function of the location of the relay with low ave rage SINR “sweet spot” as we ll at the position aro und 2 . Fr om the network designer ’ s poin t of view , if a fixed relay can b e added to the network to improve the perfor mance, the above ob servations on the relay locations can provide guidanc e o n where to place such a fixed r elay . Figure 7(a) and Figure 7(b ) show th e average BER as a fun ction of the n umber of users. He re we explore the cases with two to six users. In each case, the u sers are uniformly distributed in th e range [4 , 8] . The relay is located at 1 . 6 , and transmits the XOR of th e nearest two users’ sym bols. For successive can cellation, the power settings are 20 d B, 30 dB, 40 dB, and 50 d B for the lower , mid-low , m id-high, an d h igh power setups. For optimal MUD, the power settings are 1 0 dB, 16 . 7 dB, 23 . 3 dB, and 30 dB instead. As expected, the perform ance is b est when there are only two users. T he perf ormance for th e case with mo re u sers can be imp roved by intro ducing more relays or having the relay transmittin g XOR o f more users’ symb ols. Finally , we stud y the p roblem o f wh ose inf ormation should b e coded with n etwork codin g. Figure 8 shows the average BER as a fun ction of the nu mber of users fo r the re lay to be coded with network co ding with different av erage SNR and different MUDs. W e can ob serve th at, in th is case, codin g m ore user s can improve th e system perfor mance. Fro m the above ob servations, we can see that the system perfo rmance degrades as the nu mber of users in the network increases, while the p roposed approa ch with network coding and cooperative M UD can significantly imp rove the perf ormance by enc oding mor e 10 2 3 4 5 6 10 −4 10 −3 10 −2 10 −1 10 0 number of users BER BER as a Function of No. of Users, Successive Cancellation w/o relay low power w/o relay mid−low power w/o relay mid−high power w/o relay high power w/ relay low power w/ relay mid−low power w/ relay mid−high power w/ relay high power (a) Successiv e cancel lation 2 3 4 5 6 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 number of users BER BER as a Function of No. of Users, Optimal MUD w/o relay low power w/o relay mid−low power w/o relay mid−high power w/o relay high power w/ relay low power w/ relay mid−low power w/ relay mid−high power w/ relay high power (b) Optimal MUD Fig. 7. The ave rage BER as a functi on of the number of users uniformly distributed in the range [ 4 , 8] and with the relay locate d at 1 . 6 . T he po wer settin gs are 20 dB, 30 dB, 40 dB, and 50 dB for the lo wer , mid-lo w , m id-high, and high powe r setups, respecti vely . 1 2 3 4 10 −4 10 −3 10 −2 10 −1 10 0 Number of users which relay included in the network coding, | M i | Average BER Network Coding Gain as a Function of the Number of Users that the Relay retransmits SC detector with 3.883dB average receiving SNR SC detector with 5.883dB average receiving SNR Optimal detector with 3.883dB average receiving SNR Optimal detector with 5.883dB average receiving SNR Fig. 8. A verag e BER as a function of the number of users for the relay to be coded with network coding with diff erent a verage SNR and dif ferent MUDs users. V I . C O N C L U S I O N S In this pa per , based on the fact that the enhance ment of some users’ tra nsmissions by cooper ativ e transmission can impr ove the other users’ performan ce in certain types of multiuser detector s, we h av e propo sed two new cooperativ e t ransm ission protocols that utilize MUD as well as network cod ing. Unlike tradition al MUD in which the link s ar e determined by the users’ location s and chann els, the pr oposed cooper ati ve transmission protoco ls imp rove the link qu alities so that the mu l- tiuser detectors ca n work in th eir m ost efficient region s. Moreover , deploying MUD at the relay provides an oppor tunity to use ne twork coding, which can provide additional cod ing g ain and achieve fu ll diversity . Fro m our an alytical and simulation results, it is seen that the propo sed pro tocols achieve much lower average BER, higher di versity order and coding gain, and better asymp- totic e fficiency , co mpared to co operative transmission in network s u sing single user d etection and tradition al MUD. The p erforma nce g ap between the propo sed ap- proach an d the MIMO-MUD b ound is less than 0 . 12 dB when the BER is 1 0 − 6 and 1.04 dB when th e BER is 10 − 3 . A C K N O W L E D G M E N T The au thors would like to th ank Dr . Huaiy u Dai of North Caro lina State Un iv ersity , Dr . Hu sheng Li of the University of T ennessee, and ano nymous revie wers fo r their con structive discussions and suggestion s. R E F E R E N C E S [1] A. Sendona ris, E. Erkip, and B. Aazhang, “User coopera tion di versit y , Part I: System descripti on, ” IEEE T ransactions on Com- municati ons , vol. 51, no. 11, pp. 1927-193 8, Nov ember 2003. [2] J. N. Laneman, D. N. C. Ts e, and G . W . W orne ll, “Cooperat iv e di versit y in wireless networks: ef ficient protocols and outage beha vior , ” IEEE T ransactions on Informati on Theory , vol. 50, no. 12, pp. 3062 -3080, December 2004. [3] A. K. Sadek, Z. Han, and K. J. Ray L iu, “Distrib uted relay assignment algo rithm for coope rati ve communica tions in wireless netw orks, ” in Pr oc. IEEE Internat ional Confer ence on Communi - cations , Istanbul , Tur key , June 2006. 11 [4] J. Luo, R. S. Blum, L. J. Greenstei n, L. J. Cimini, and A. M. Haimovi ch, “New approaches for cooperat iv e use of multiple antenna s in ad hoc wireless networks, ” in Proc . IEEE V ehicul ar T echnol ogy Confer ence , vol.4, pp.2769- 2773, Los Angeles, CA, September 2004. [5] T . Himsoon, W . Siriwo ngpairat, Z. Han, and K. J. Ray Liu, “Lifetime maximiza tion with coopera ti ve div ersity in wireless sensor networks, ” in P r oc. IEE E W ir eless Communication s and Network ing Confer ence , Las V egas, NV , April 2006. [6] Z. Y ang, J. Liu, and A. Host-Madsen, “Cooper ati ve routing and po wer allocation in ad-hoc networks, ” in Proc. IEE E Global T elecommuni cations Confer ence , Dalla s, TX, November 2005. [7] Z. Han, T . Himsoon, W . Siriwongpaira t, and K. J . Ray Liu, “Energ y ef ficient cooperat iv e transmission o ver multiuser OFDM netw orks: who help s whom and ho w to cooperate, ” in Proc. IE EE W ir eless Communications and Network ing Confere nce , vol. 2, pp.1030-1035, New Orleans, Marc h 2005. [8] W . Siriwongpa irat, W . Su, Z. Han, and K. J. R. Liu, “Enhancement for multiband UWB systems using co operati ve communica tions, ” in Pro c. IEEE W ir eless Communications and Net working Con fer- ence , Las V egas, NV , April 2006. [9] S. V erd ´ u, Multiuser Detecti on , Cambridge Uni versity Press, Cam- bridge, UK, 1998. [10] L. V enturino, X. W ang and M. Lops, “Multiuser detecti on for co- operati ve net works and performance ana lysis, ” IEEE T ransact ions on Signal P r ocessing , vol. 54, no. 9, pp. 3315-3329, September 2006. [11] H. D ai, A. F . Molisch, and H. V . Poor , “Downl ink capacity of interfe rence-limi ted MIMO systems with joint detection, ” IEEE T ransa ctions on W ir eless Communicati ons , vol. 3, no. 2, pp. 442- 453, March 2004. [12] R. Ahlswede, N. Cai, S.-Y . R. L i, and R. W . Y eung, “Network informati on flow , ” IEE E T ransacti ons on Information Theory , vol. 46, no. 4, pp. 1204 -1216, April 2000. [13] Y . Chen, S. Kishore, and J. Li, “W ireless dive rsity through netw ork coding, ” in Proc . IEEE W ir eless Communications and Network ing Confer ence , Las V egas, NV , April 2006. [14] Y . Wu, P . A. Chou and S. -Y . Kung, “Informat ion exchange in wireless network s with network cod ing and physical -layer broad- cast, ” in Pro c. 39th Annal Confer ence on Information Science s and Systems , The Johns Hopkins Uni versity , Baltimore , MD, March 2005. [15] J. N. Laneman, “Network cod ing gain of co operati ve div ersity , ” in Pr oc. IEEE 2004 Military Communicati ons Confer ence , Monter ey , CA, October 2004. [16] Y . Cao a nd B. V ojci c, “MMSE multiuser det ection for coopera ti ve di versit y CDMA systems, ” in Proc . IEEE W ir eless Communica- tions and Net working Confer ence , Atlanta, GA, March 2004. [17] D. N. C. Tse and S. V . Hanly , “Linear multiuser recei v ers: Effe cti ve interference , ef fecti ve bandwidth and user capaci ty , ” IEEE T ransac tions on Information Theory , vol. 45, no. 2, p.p. 641-657, March 1999. [18] T . T anaka , “ A statistic al-mechani cs approac h to lar ge-system analysi s of CDMA multiuser detectors, ” IE EE Tr ansactions on Informatio n Theory , vol. 48, no. 11, p.p. 2888-2910, Nov ember 2002. [19] D. Guo and S. V erd ´ u , “Randomly spread CDMA: Asymptotics via statistic al physics, ” IEEE T ransact ions on Information Theory , vol. 51, no. 6, p.p. 1983 -2010, June 2005. [20] S. Chung and A. Goldsmith “Degree s of freedom in adapti ve modulati on: A unifie d vie w”, IEEE T ransact ions on Communica- tions , vol. 49, no. 9, pp. 1561-1571 , September 2001. 12
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment