A Model of the IEEE 802.11 DCF in Presence of Non Ideal Transmission Channel and Capture Effects
In this paper, we provide a throughput analysis of the IEEE 802.11 protocol at the data link layer in non-saturated traffic conditions taking into account the impact of both transmission channel and capture effects in Rayleigh fading environment. Imp…
Authors: Refer to original PDF
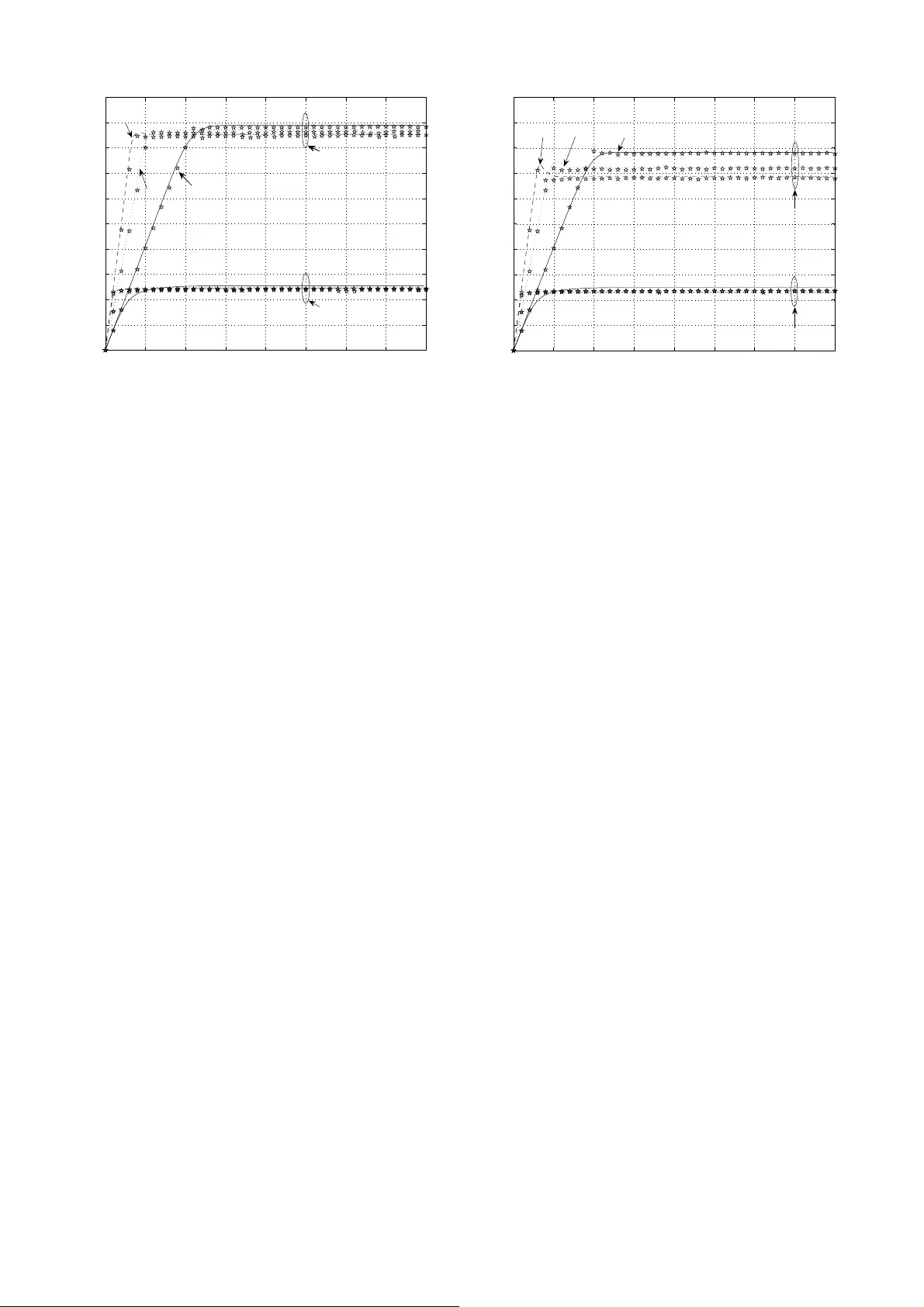
1 A Model of the IEEE 802.11 DCF in P resence of Non Ideal T ransmission Channel and Capture Ef fects F . Danesh garan, M. La ddomada, F . Mes iti, a nd M. Mondin Abstract —In this paper , we prov ide a throughput analysis of the IEEE 802.11 protocol at th e d ata link lay er in non- saturated tr affic conditions taking into account the impact of both transmission channel and capture effects in Ra yleigh fading en vironment. Impacts of both non-i deal channel and capture become imp ortant in terms of the actual observ ed throughput in typical network co nditions where by traffic i s mainly unsaturated, specially in an en viro nment o f high interference. W e extend the multi-dimension al M arko vian state transition model characterizing the behavior at th e MA C layer by including transmission states that account for packet transmission failures due to errors caused b y propagation through th e ch annel, along with a state characterizing the system when there are no packets to be transmitted in th e b uffer of a station . Index T erms —Capture, DCF , Distributed Coordination Func- tion, fading, IEEE 802 .11, MA C, Rayleigh, ra te adaptation, saturation, thro ughput, unsaturated, non-saturated. I . I N T RO D U C T I O N W ir eless Local Area Networks ( WLANs) u sing the IEEE80 2.11 series of standard s have experience d an expone n- tial growth in the recent past [1]-[13]. T he Medium Access Control (MAC) layer of many wireless p rotocols resemble that of IEEE80 2.11. Hence, while we f ocus on this protoc ol, it is evident th at the results easily exten d to o ther protoco ls with similar MA C layer o peration. The most rele vant works to what i s presented here are [3], [4]. In [3] the author provided an analy sis of the saturation throug hput of the b asic 802.11 pr otocol assuming a two dimensiona l Markov model at the MAC layer , while in [4] the autho rs extended the underlyin g model in or der to conside r unsaturated traffic cond itions by intr oducing a new idle state, not present in the original Bianchi’ s mode l, accoun ting for the case in wh ich the station buf fer is empty , after a successful completion of a packet tr ansmission. In th e modified model, howe ver , a packet is discarded after m backoff stages, wh ile in the Bianchi’ s mod el, the station keeps iterating in th e m -th backoff stage until th e packet gets successfully transmitted. In [5], the autho rs look at th e impact of channel induced errors and th e rec eiv ed SNR on th e achiev able thro ughp ut in a system with r ate adaptation whereby the transmission rate of the terminal is adapted based on either direct or indirect Accepted to IEEE Globecom 2007 This work has been supported by PRIN-2005 ICONA. F . Da neshgaran is wit h ECE Dept., Califor nia State Univ ersity , Los Angel es, USA. M. Laddomada (laddoma da@polit o.it), F . Mesiti and M. Mondin are with DELEN, Politecni co di T orino, Ital y . measuremen ts o f the lin k quality . In [6], the authors deal with the extension of Bianchi’ s Markov model in o rder to accoun t for chan nel errors. Paper [7] pro poses an extension of the Bianchi’ s mo del considering a ne w state for each backoff stage accountin g for the absence of new packets to be tran smitted, i.e., in unlo aded tra ffic co nditions. In real networks, t raffic is m ostly unsaturated, so it is importan t to derive a model accou nting for practical network operation s. In this paper [2], we extend the pr evious works o n the subject by loo king at all the thre e issues outline d be fore together, nam ely re al chan nel conditio ns, unsatura ted traffic, and capture effects. Our assumptions are essentially similar to those o f Bian chi [3] with the exception th at we do assume the presence of both channel induced errors and capture effects due to the transmission over Rayleigh fading channe l. The pa per is o rganized as follows. Section II extend s the Markov mod el in itially proposed b y Bianchi, presenting modification s that a ccount for transmission er rors and captu re effects over Rayleigh fading ch annels employin g the 2-way handshak ing techniqu e in unsatu rated traffic con ditions. Sec- tion II I p rovides an expression f or the un saturated thro ughpu t of the link . In section IV we p resent simu lation results where typical MA C laye r parameters f or I EEE802 .11b are used to obtain throug hput values as a f unction of various system level parameters, cap ture pr obability , and SNR unde r typical traffic condition s. Finally , Section V is dev oted to co nclusions. I I . D E V E L O P M E N T O F T H E M A R KOV M O D E L In [3], an analytical model is pr esented fo r the co mputation of th e throughp ut o f a WLAN using the IEE E 80 2.11 DCF under ideal chan nel cond itions. By virtue o f the strategy employed for reducing the collision p robability of the packets transmitted fro m the stations attemptin g to access the chann el simultaneou sly , a rando m pro cess b ( t ) is used to represen t the backoff cou nter o f a given station. Backoff counter is decremen ted a t th e start of e very idle backoff slot and when it reaches zero, th e station transmits and a new value for b ( t ) is set. The v alue of b ( t ) after each t ransmission depend s on the size of th e con tention window from which it is d rawn. Theref ore it depend s on the stations transmission history , renderin g it a non-Ma rkovian pr ocess. T o overcome this p roblem and g et to the d efinition of a Markovian pro cess, a second pr ocess s ( t ) is defined representing the size of the contention win dow from which b ( t ) is drawn, ( W i = 2 i W , i = s ( t )) . 2 ... ... ... ... m,1 m,W -1 m 1 1 1 ... ... ... ... ... 0,1 0,W -1 0 1 1 1 ... ... ... ... i,0 i,1 i,W -1 i 1 1 1 ... ... ... ... ... 0,0 P/W eq 1 P/W eq i + 1 m,0 P/W eq m ... ... ... P/W eq i P/W eq m ... ... I (1-q) (1-q)(1-P) eq q/W 0 q q(1-P)/W eq 0 Fig. 1. Marko v chain for the conte ntion model in unsaturated traf fic conditi ons, based on the 2-way handshaki ng t echniqu e, considering the effec ts of capture and channe l induced errors. A two-dimension al Mar kov p rocess ( s ( t ) , b ( t )) c an now be defined, based on two assertions: 1) the proba bility τ tha t a station will attempt tra nsmission in a gen eric time slot is constant acr oss all time slots; 2) the pro bability P col that a ny transmission experiences a collision is constan t and independen t of the num ber of collisions already suffered. The main aim of this section is to propo se an ef fectiv e modification of the b i-dimension al Mar kov pro cess pro posed in [3] in or der to account for unsaturated traffic conditions, channel err or prop agation and capture effects over a Rayleigh fading c hannel under the hyp othesis of e mploying a 2-way handshak ing acce ss mecha nism. On the basis of this assump tion, collisions can o ccur with probab ility P col on the transm itted packets, while transmission errors due to the ch annel, can occur with pr obability P e . W e assum e that co llisions and tran smission error e vents are statistically indepe ndent. In this scenario , a packet is suc- cessfully transmitted if ther e is no collision (th is ev ent h as probab ility 1 − P col ) an d the packet e ncounter s n o ch annel errors d uring tran smission (this event has prob ability 1 − P e ). The pro bability of successful transmission is therefo re eq ual to (1 − P e )(1 − P col ) , from wh ich we can set an equiv alen t probab ility of failed transmission as P eq = P e + P col − P e P col . Furthermo re, in mo bile radio environmen t, it m ay h appen that th e chan nel is captu red by a station w hose power lev el is stronger than other stations tr ansmitting at th e same time. This may be du e to relative d istances an d/or ch annel co nditions fo r each user an d may ha ppen wh ether o r not the term inals exer- cise power con trol. Captur e effect often re duces the c ollision probab ility o n the channel since the s tations whose power level at the receiver are very low due to pa th attenuation , shadowing and fading, are con sidered as interfere rs at the AP raising th e noise floor . T o simplify the analysis, we make th e a ssumption that the imp act of the ch annel ind uced errors o n the R TS, CTS and Acknowledgment (A CK) p ackets are negligib le because of their short length. This is ju stified on the b asis of the assumption that the b it erro rs inflicting the tran smitted data are indepen dent of each other . W e note that with sufficient interleaving we ca n always ensur e that th e er rors inflicting individual bits in a data p acket are indepen dent of each other [14], [1 7]. Practical networks operate in unsaturate d traffic con ditions. In this case, Bianchi’ s m odel [3] assuming the p resence of a packet to be transmitted in each and ev ery station’ s buffer , is not valid anymor e. Howe ver , th e simplicity of such a model can be r etained also in unsatu rated con ditions b y introd ucing a n ew state, labelled I , a ccounting for the f ollowing two situations: • imme diately after a successful transmission, the buf fer of the transmittin g station is em pty; • the station is in a n idle state with an empty buffer un til a n ew packet arr i ves at the buf fer for transmission. W ith the se considerations in min d, let us d iscuss the M arkov model shown in Fig. 1, modelling unsaturated tr affic c ondition. The Markov Process of Fig. 1 is g overned by th e following transition p robabilities 1 : P i,k | i,k +1 = 1 , k ∈ [0 , W i − 2] , i ∈ [0 , m ] P 0 ,k | i, 0 = q (1 − P eq ) /W 0 , k ∈ [0 , W 0 − 1] , i ∈ [0 , m ] P i,k | i − 1 , 0 = P eq /W i , k ∈ [0 , W i − 1] , i ∈ [1 , m ] P m,k | m, 0 = P eq /W m , k ∈ [0 , W m − 1] P I | i, 0 = (1 − q )(1 − P eq ) , i ∈ [0 , m ] P 0 ,k | I = q/W 0 , k ∈ [0 , W 0 − 1] P I | I = 1 − q (1) The first equation in (1) states tha t, at the beginnin g of e ach slot time, the bac koff time is decrem ented. The second equa- tion acco unts for the fact that after a successful transmission, a new pa cket tra nsmission starts with backoff stage 0 with probab ility q , in case ther e is a n ew packet in the buf fer to be transmitted . Third and fourth eq uations deal with unsuccessful transmissions an d the need to reschedule a new contention stage. The fifth equation deals with the p ractical situation in which after a successful transmission, th e buffer o f the station is empty , and as a consequ ence, the station transits in th e idle state I waiting fo r a new pa cket arriv al. The sixth equation mo dels the situation in which a n ew packet arrives in the statio n buf fer, and a new backoff p rocedur e is sched uled. Finally , the sev enth equation models the situation in which there are n o packets to be transmitted an d the station is in the idle state. I I I . M A R KOV I A N P R O C E S S A NA L Y S I S A N D T H RO U G H P U T C O M P U TA T I O N Next line o f pursuit consists in finding a solu tion o f the stationary d istribution: b i,k = lim t →∞ P [ s ( t ) = i, b ( t ) = k ] , ∀ k ∈ [0 , W i − 1] , ∀ i ∈ [0 , m ] 1 P i,k | j,n is short for P { s ( t + 1) = i, b ( t + 1) = k | s ( t ) = j, b ( t ) = n } . 3 that is, th e prob ability of a station o ccupying a g iv en state at any discrete tim e slot. First, we n ote the f ollowing relatio ns: b i, 0 = P eq · b i − 1 , 0 = P i eq · b 0 , 0 , ∀ i ∈ [1 , m − 1] b m, 0 = P m eq 1 − P eq · b 0 , 0 , i = m (2) whereby P eq is the equ iv a lent prob ability of failed transmis- sion, th at takes in to accoun t th e need for a new contention due to either packet co llision ( P col ) or channel er rors ( P e ), i.e., P eq = P col + P e − P e · P col . State b I in Fig. 1 con siders both the situation in which after a successful transmission there ar e no packets to be transmitted, and th e situation in wh ich the packet qu eue is empty and the station is waiting for new pac ket arriv al. Th e stationary pro bability to be in state b I can be ev aluated a s follows: b I = (1 − q )(1 − P eq ) · P m i =0 b i, 0 + (1 − q ) · b I = (1 − q )(1 − P eq ) q · P m i =0 b i, 0 (3) The expression above reflects the fact that state b I can be reached after a succ essful p acket transmission f rom any state b i, 0 , ∀ i ∈ [0 , m ] with p robability (1 − q )(1 − P eq ) , or because the station is waiting in idle state with proba bility (1 − q ) , whereby q is the pro bability of having at least o ne packet to be tran smitted in the buffer . The statistical mod el of q will be discussed in the next section. The other stationary pro babilities for any k ∈ [1 , W i − 1] follow by resorting to the state transition dia gram shown in Fig. 1: b i,k = W i − k W i q (1 − P eq ) · P m i =0 b i, 0 + q · b I , i = 0 P eq · b i − 1 , 0 , i ∈ [1 , m − 1] P eq ( b m − 1 , 0 + b m, 0 ) , i = m (4) Employing the no rmalization con dition, after lengthy alge - bra, and rememb ering the relatio n P m i =0 b i, 0 = b 0 , 0 1 − P eq , it is possible to obtain : 1 = b 0 , 0 2 " W m − 1 X i =0 (2 P eq ) i + (2 P eq ) m 1 − P eq ! + 1 1 − P eq + 2(1 − q ) q # (5) Normalization condition y ields the f ollowing equation for computatio n of b 0 , 0 : 2(1 − P eq )(1 − 2 P eq ) q q [( W +1)(1 − 2 P eq )+ W P eq (1 − (2 P eq ) m )]+2(1 − q ) (1 − P eq )(1 − 2 P eq ) (6) Equ. (6) is then used to compu te τ , the probab ility that a station star ts a transmission in a random ly c hosen time slot: τ = 2(1 − 2 P eq ) q q [( W +1)(1 − 2 P eq )+ W P eq (1 − (2 P eq ) m )]+2(1 − q ) (1 − P eq )(1 − 2 P eq ) (7) The collision pr obability needed to compute τ can be fou nd considerin g that usin g a 2-way hand -shaking mechanism, a packet fro m a transmitting station encou nters a collision if in a g i ven time slot, at least one of the remain ing ( N − 1) stations tra nsmits simultan eously anoth er packet, and there is no capture. In ou r m odel, we assume that captur e is a subset of the c ollision e vents. This is indeed ju stified b y th e fact that there is no capture without collision, and that capture occurs only because of collisions b etween a certain nu mber of tran smitting stations attem pting to tr ansmit simultaneo usly on the chan nel. P col = 1 − (1 − τ ) N − 1 − P cap (8) As far as the captu re effects ar e co ncerned , we resort to the m athematical formulatio n proposed in [9 ], [1 0]. I n particular, under the h ypothesis of power-controlled stations in in frastructur e mo de, the captur e prob ability conditioned on i in terfering frames can be defined a s f ollows: P cp ( γ > z o g ( S f ) | i ) = 1 [1 + z 0 g ( S f )] i (9) whereby , γ , defined as P u / P i k =1 P k , is the ratio of th e power P u of th e useful signal and the sum of the p owers of th e i interfering channel contender s transmitting simultaneou sly i frames, g ( S f ) is the in verse o f th e processing gain of the correlation receiver , an d z 0 is the captu re ratio, i.e. , th e value of the signal-to-in terference power ratio ide ntifying the capture threshold at the receiver . Notice that (9) signifies the fact that capture p robab ility corresp onds to the prob ability th at the power ra tio γ is above the c apture threshold z 0 g ( S f ) which considers the in verse of the p rocessing g ain g ( S f ) . For Direct Sequence Spread Spectrum (DSSS) using a 11-ch ip spreadin g factor ( S f = 11 ), we have g ( S f ) = 2 3 S f . Upon defining the pro bability of gen erating exactly i + 1 interfering frames over N contend ing stations in a generic slot time: N i + 1 τ i +1 (1 − τ ) N − i − 1 the fram e captu re p robability P cap can be o btained as fo llows: P cap = N − 1 X i =1 N i + 1 τ i +1 (1 − τ ) N − i − 1 P cp ( γ > z o g ( S f ) | i ) (10) Putting together Equ.s (7), (8), and (10), alo ng with P eq , the following nonlin ear system can be defined and solved numerically , obtain ing the values of τ , P col , P cap , an d P eq : τ = 2(1 − 2 P eq ) q q [( W +1)(1 − 2 P eq )+ W P eq (1 − (2 P eq ) m )]+2(1 − q ) (1 − P eq )(1 − 2 P eq ) P col = 1 − (1 − τ ) N − 1 − P cap P eq = P col + P e − P e · P col P cap = P N − 1 i =1 N i +1 τ i +1 (1 − τ ) N − i − 1 1 (1+ z 0 g ( S f )) i (11) The final step in the analysis is th e com putation of the normalized system th rough put, d efined as th e fractio n of time the c hannel is used to successfully transmit pay load bits: S = P t · P s · (1 − P e ) E [ P L ] (1 − P t ) σ + P t (1 − P s ) T c + P t P s (1 − P e ) T s + P t P s P e T e (12) where the meaning o f th e und erlined sy mbols is as follows. P t is th e proba bility that the re is at least one transmission in the co nsidered tim e slot, with N stations co ntending for the channel, each transmitting with pr obability τ : P t = 1 − (1 − τ ) N (13) P s is the condition al pr obability that a p acket tran smission occurrin g on the c hannel is suc cessful. This event corr esponds 4 to the case in wh ich exactly one station tr ansmits in a gi ven time slot, or two o r m ore stations transmit simultaneou sly and capture by the desired station occ urs. The se con ditions y ields the f ollowing pr obability: P s = N τ (1 − τ ) N − 1 + P cap P t (14) T c , T e and T s are the average tim es a chann el is sensed b usy due to a collision , error affected data fr ame transmission time and successful data frame transmission times, respectively . Knowing the time d urations for A CK frames, A CK timeo ut, DIFS, SIFS, σ , data packet length ( P L ) an d PHY and MAC headers dura tion ( H ), and propagation delay τ p , T c , T s , and T e can be co mputed as sugg ested in [11]. E [ P L ] is the av erage packet paylo ad length . σ is the dura tion of an empty time slot. A. Modelling offer ed lo ad a nd estimation of pr obability q In our analysis, the offered load related to each station is characterized by param eter λ rep resenting the rate at wh ich packets arrive at the station buffer from the upp er layer s, and measured in pk t/s . The time betwee n two packet arriv als is defined as interarrival time , and its mean value is ev a luated as 1 λ . One of the most co mmonly used tr affic mode ls assumes packet arriv al process is Poisson. The r esulting interar riv al times are expon entially distributed. In the prop osed model, we ne ed a p robability , id entified by q , that in dicates if at the end o f a given tran smission there is at least o ne pac ket in the q ueue to b e tr ansmitted. Proba bility q c an be well app roximated in a situation with small buffer size [1 3] thro ugh the following relation: q = 1 − e − λE [ S ts ] (15) where, E [ S ts ] is the expected time per slot , which is usefu l to relate th e state o f th e Mar kov chain with th e actual tim e spen t in ea ch state. A more accu rate mo del can be d erived upon considerin g different values of q for each backoff state. Howe ver , a rea- sonable solution co nsists in using a m ean pro bability valid for the wh ole Ma rkov model [13], d erived f rom E [ S ts ] . Th e value of E [ S ts ] can be ob tained by resorting to the durations and the respective pro babilities of the idle slot ( σ ), th e successful transmission slot ( T s ), the err or slo t due to collision ( T c ), and the e rror slot due to chan nel ( T e ), as follows: E [ S ts ] = (1 − P t ) · σ + P t (1 − P s ) · T c + + P t P s P e · T e + P t P s (1 − P e ) · T s (16) Upon r ecalling that p acket inter-arriv al times are expon entially distributed, we can use th e average slot time to calcu late the prob ability q that in such a time interval a gi ven station receives a p acket from u pper layer s in its transmission que ue. The pr obability that in a gen eric tim e T , k e vents occur, is: P { a ( T ) = k } = e − λT ( λT ) k k ! (17) from w hich we obtain the relatio n ( 15) r eferred to earlier: q = 1 − P { a ( E [ S ts ]) = 0 } = 1 − e − λE [ S ts ] (18) T ABLE I T Y P I C A L N E T WO R K PA R A M E T E R S MA C header 24 bytes τ p 1 µ s PHY header 16 bytes Slot time 20 µ s Payl oad size, E[PL] 1024 bytes SIFS 10 µ s A CK 14 bytes DIFS 50 µ s R TS 20 bytes EIFS 300 µ s CTS 14 bytes A CK,CTS timeout 300 µ s m 5 W 32 T s 8.812 ms T c 8.812 ms I V . S I M U L A T I O N R E S U LT S A N D M O D E L V A L I DAT I O N S This section focuses on simulation results f or validating the theoretical models and d eriv ations presented in the previous sections. W e have developed a C++ simulato r mod elling b oth the DCF pro tocol details in 802.1 1b and the b ackoff p roce- dures of a specific numb er of ind epende nt transmitting sta- tions. The simu lator also takes into accou nt all real operations of each tran smitting station, including p hysical prop agation delays, etc. T yp ical MAC layer parameters fo r the lowest rate IEEE80 2.11b are giv en in T a ble I [1]. In so far as the computatio n of the FER is concer ned, it should be noted that d ata transmission rate of various packet types d iffer . For simplicity , we assume that data p ackets transmitted by different station s are affected by the same FE R. The FER as a function of the SNR can be compu ted as follows: P e ( S N R ) = 1 − [1 − P e ( P LC P, S N R ) ] · [ 1 − P e ( DA T A, S N R )] (19) where, P e ( P LC P, S N R ) = 1 − [1 − P b ( B P S K, S N R )] 8 × P LC P , (20) and P e ( DA T A, S N R ) = 1 − [1 − P b ( T Y P E , S N R )] 8 × ( DAT A + M AC ) . (21) P b ( B P S K , S N R ) is the BER as a fu nction of SNR fo r the lowest data transmit rate employing DBPSK m odulation , D A T A deno tes the data b lock size in byte s, and any oth er constant byte size in above expression represen ts overhead. Note that the FER, P e ( S N R ) , imp licitly depen ds on the modulatio n for mat u sed. Hence, for each sup ported rate, one curve for P e ( S N R ) as a function of SNR can be g ener- ated. P b ( T Y P E , S N R ) is modulation depend ent whereby the parameter T Y P E can be any of th e fo llowing T Y P E ∈ { D B P S K , D QP S K , C C K 5 . 5 , C C K 11 } 2 . For DBPSK and DQPSK modulation formats, P b ( T Y P E , S N R ) can b e well appr oximated by [18]: 2 max(log 2 M , 2) max( M 4 , 1) X i =1 1 π Z π 2 0 1 1 + γ 1 sin 2 θ log 2 M si n 2 “ (2 i − 1) π M ” dθ (22) whereby M is the num ber of bits per modulated sy mbols, γ is th e signal-to-n oise r atio, and θ is th e signal d irection over the Ray leigh fading ch annel. 2 The acronyms are short for Dif ferenti al Bina ry Phase Shift Keyi ng, Dif ferenti al Quadrature P hase Shift K eyi ng and Complementar y Code Keyi ng, respect i vely . 5 0 5 10 15 20 25 30 35 40 0 1 2 3 4 5 6 7 8 9 10 x 10 5 λ [pkt/s] Throughput [bit/s] SNR=45dB SNR=45dB SNR=20dB N=10 N=10 N=20 N=30 Fig. 2. Theoret ical and simula ted throug hput for the 2-w ay mec hanism as a functio n of the packet rate λ , for three differe nt number of contending stations and two di f ferent v alues of SNR as noted in th e le gend. C apture thresholds is z 0 = 6 dB. Simul ated points are identified by star-mark ers over the respecti ve theoret ical curves. Paylo ad size is 1024 bytes. Fig. 2 sho ws th e beh avior of the throughp ut as a function of λ , i.e., the packet rate, f or thr ee different values of the number of co ntending stations and fo r two values of SNR. The capture th reshold is z 0 = 6 dB. Beside n oting the throug hput improvement ach iev a ble f or hig h SNR, notice th at for a spec- ified num ber of conten ding stations, the thro ughp ut ma nifests a linear beh aviour f or low values of packet rates with a slope depend ing mainly on the num ber of station s N . Howe ver , for increasing values o f λ , the saturation b ehavior occurs qu ite fast. Notice that, as exemplified in (18), q → 1 as λ → ∞ . Actually , saturated traffic conditions ar e achieved quite fast for values of λ on th e order o f te n packets per seco nd with a number o f conten ding stations g reater than or equal to 10. Fig. 3 sho ws th e beh avior of the throughp ut as a function of λ , fo r three different values of the nu mber of contending stations an d for two d ifferent SNRs. The captu re threshold is z 0 = 2 4 dB. W e can draw conclusions similar to the o nes derived for Fig. 2. Upon comparin g the curves shown in Fig.s 2 and 3, it is easily seen that cap ture e ffects allow the system throug hput to be almost the same independ ently fro m the number of stations in saturated c onditions, i.e., for high values of λ . Fig. 3 also sho ws the presence of a peak in th e throughp ut as a fu nction o f λ , which character izes the tr ansition between the linear and saturated throu ghput. Such a peak tends to m anifest itself for increa sing values of λ as the numb er of statio ns N d ecreases. A com parative analy sis of the curves shown in Fig.s 2 and 3 reveals that the pea k of the throug hput tend s to disapp ear b ecause of th e presenc e of captur e effects durin g transmission. V . C O N C L U S I O N S In this p aper, we hav e provided an extension o f th e Mar kov model ch aracterizing the DCF behavior at the M A C layer of the IEEE 802.1 1 series of standard s b y accoun ting for ch annel 0 5 10 15 20 25 30 35 40 0 1 2 3 4 5 6 7 8 9 10 x 10 5 λ [pkt/s] Throughput [bit/s] SNR=45dB SNR=20dB N=10 N=20 N=30 Fig. 3. Theoretic al and simulated throughput for the 2-way mechanism as a functi on of the packet rate λ , for three dif feren t number of conte nding station s and two dif ferent values of SNR as noted in the legend. Capt ure threshold is z 0 = 24 dB. Simulated point s are identified by star -marke rs over the respecti ve theoretic al curves. Payload size is 1024 bytes. induced error s and ca pture effects typical of fading envi- ronmen ts under un saturated tra ffic cond itions. The mo delling allows takin g into consider ation the imp act of channe l co n- tention in th rough put analy sis which is often not considere d or it is con sidered in a static mod e by usin g a mean co ntention period. Simu lation r esults con firm th e validity o f the propo sed theoretical m odels. R E F E R E N C E S [1] IEEE Standar d for W ir eless LAN Medium Access Contr ol (MAC ) and Physical Layer (PHY) Specificati ons , N ov ember 1997, P802.11 [2] F . Daneshgaran, M. Laddomada, F . Mesiti, and M. Mondin, ”Unsatu- rated T hroughput Analysis of IEEE 802.11 in Presence of Non Ideal Tra nsmission Channel and Capture Effec ts”, IEEE Tr ans. on W ir eless Communicat ions, 2008. [3] G. Bianch i, ”Performance analysis of the IEEE 802.11 distrib uted coordina tion function” , IEEE JSAC , V ol .18, No. 3, March 2000. [4] L. Y ong Shyang, A. Dadej , and A.Jayasuriya, ”Perfo rmance analysis of IEEE 802.11 DCF under limited load”, In Proc . of Asia-P acific Confer ence on Communications , V ol.1, pp.759 - 763, 03-05 Oct. 2005. [5] D. Qiao, S. Choi, a nd K.G. Shin ”Goodput a nalysis and link adaptat ion for IEEE 802.11a wire less LANs”, IEE E T rans. On Mobile Co mputing , V ol.1, No.4, Oct.-Dec. 2002. [6] P . Ch atzimisi os, A.C. Boucouva las, and V . V itsas, ”Influence of cha nnel BER on IE EE 802.11 DCF”, IEE Electr onics Letters , V ol.39, No. 23, pp.1687-1689, Nov . 2003. [7] K. Duffy , D. Malone, and D.J. Leith, ”Modeling the 802.11 distribut ed coordina tion functi on in non-satura ted conditions”, IEEE Communica- tions Letters , V ol.9, No.8, pp.715-717, Aug. 2005. [8] Jae Hyun Kim and Jong Ky u Lee ” Capture ef fect s of wirele ss CSMA/CA protocol s in Raylei gh and shadow fa ding channels”, IEEE T rans. on V eh. T ech. , V ol.48, N o.4, pp.1277-1286 , July 1999. [9] M. Zorzi and R. R. Rao, ”Capture and retransmission control in mobile radio”, IEEE JSAC , V ol.12, No.8, pp.1289 - 1298, Oct. 1994. [10] Z. Hadzi-V elko v and B. Spaseno vski, ”Capture ef fect in IEEE 802.11 basic service area under influence of Rayleigh fading and near/f ar ef fect” , In Proc. of 13th IEE E PMRC , V ol.1, pp.172 - 176, Sept. 2002. [11] Z. K ong, D. H.K. Tsang, B.Bensaou, and D.Gao, ”Performance analysis of IEEE 802.11e con tention -based channel access”, IEE E JSAC , V ol.22, No.10, Dec. 2004. [12] T . S. Ho and K. C. Chen, ”Performance e v aluat ion and enhancement of the CSMA/CA MA C protoco l for 802.11 wireless LANs”, In Pr oc. of IEEE PIMRC , T aipe i, T aiwan, Oct. 1996, pp. 392396. 6 [13] D. Malone, K. Duffy , and D.J. Leith, ”Modeling the 802.11 distribute d coordina tion functi on in non-saturat ed heteroge neous condi tions”, T o appear on IE EE-ACM Tr ans. on Networking . [14] F . Daneshgara n and M. Laddomada, “Reduce d complexity interle av er gro wth algori thm for turbo codes, ” IEEE Trans. on W irele ss C ommuni- catio ns, vol.4, no.3, pp.954-964, May 2005. [15] F . Daneshgara n, M. Laddomada, and M. Mondin, “Interle av er desig n for serially concat enate d con v olutiona l codes: Theory and applic ation, ” IEEE Trans. o n Inf. Theory , V ol.50, No. 6, pp. 1177-1188, June 2004. [16] F . Daneshgaran , M. Laddomada, and M. Mondin , “ An extensi ve search for good punct ured rate k/k+1 recu rsi ve con volut ional codes for seriall y concat enated con volutio nal codes, ” IEEE Trans. on Inform. Theory , vol.50, no.1, pp.208-217, January 2004. [17] F . Daneshga ran, M. Laddomada, and M. Mondin, “High rate recursiv e con volutiona l codes for conc atenat ed channel codes, ” IEEE Trans. on Communicat ions, vol.52, no.11, pp.1846-1850, Nov . 2004. [18] M.K. Simon and M. Alouini, Digital Communicati on over F ading Ch an- nels: A Unified Appr oac h to P erformance Analysis , W ile y-Intersci ence, 1st edition, 2000.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment