The Sender-Excited Secret Key Agreement Model: Capacity, Reliability and Secrecy Exponents
We consider the secret key generation problem when sources are randomly excited by the sender and there is a noiseless public discussion channel. Our setting is thus similar to recent works on channels with action-dependent states where the channel s…
Authors: Tzu-Han Chou, Vincent Y. F. Tan, Stark C. Draper
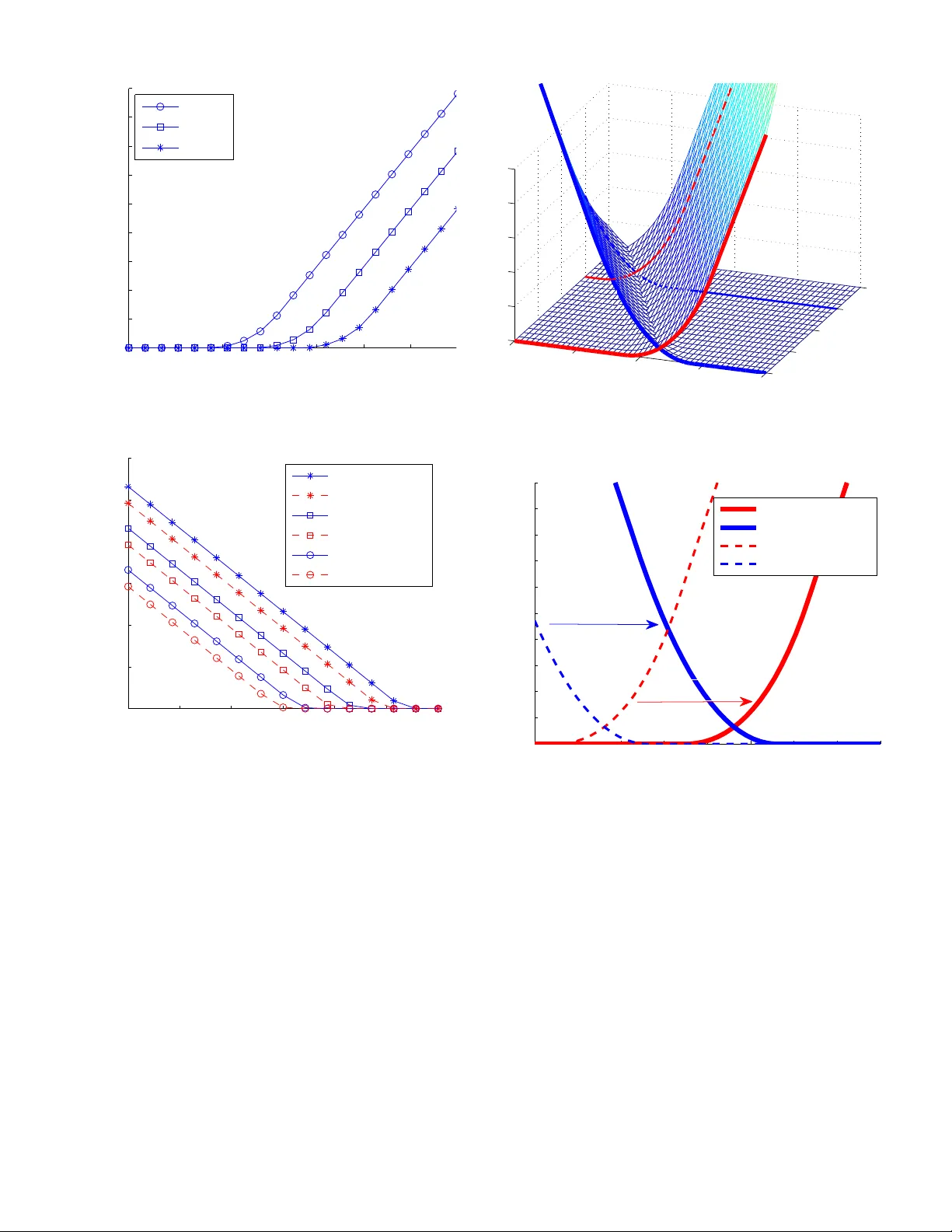
SUBMITTED TO THE IEEE TRANSA CTIONS ON INFORMA TION THEOR Y , OCT 2013 1 The Sender -Excit ed Secret K e y Agreeme nt Mod el: Capacity , Reliability and Secrec y Exponents Tzu-Han Chou, V inc ent Y . F . T an, Stark C. Draper Abstract —W e consid er the secr et key generation pro blem when sources are randomly excited by the sender and t here is a noiseless public discussion channel. Our setting is th us simil ar to recent works on channels with action-dependent states where the channel state may b e infl uenced by some of the parties in vo lved. W e derive single-letter expr essions f or th e secret key capacity through a type of source emulation analysis. W e also derive lower bounds on the achievable reliability and secrecy exponents, i.e., the exponential rates of d ecay of the p robability of decoding error and of t he information leakage. These exponen ts allow us to determine a set of stro ngly-achievable secret key rates. For degraded ea ve sdroppers the maximum str ongly-achievable rate equals the secret key capacity; our exponen ts can also be specialized to previously known results. In deriving our strong achiev ability results we in troduce a cod- ing scheme that combines wi retap coding (to excite the channel) and key extraction (to distill k eys from residual randomness). The secret key capacity is naturally seen to be a combin ation of both source- and channel- type randomness. Through examples we illustrate a fundamental int erplay between the portion of the secr et key rate due t o each type of randomness. W e also illustrate inherent tradeo ffs between the achiev able reliability and secrecy exponents. Our new scheme also natu rally accommodates rate limits on th e pu blic discussion. W e show that und er rate constraints we are able to achiev e larger rates than those that can be attained through a pure source emulation strategy . Index T erms —Secret key capacity , Common randomness, Wiretap channel, Sender-ex citation, Reliab ility exponent, Secrecy exponent, Degraded broadcast channel, Probing capacity I . I N T R O D U C T I O N W ithin the realm of infor mation-th eoretic secrecy [2], the found ations o f sharing a secret key between two parties in the presen ce of an eav esdrop per were initiated in [3], [4]. Ahlswede and Csisz ´ ar [3] studied two models: the sour ce- type model with wir etapp er (Mo del SW) and the chann el- type model with wir etapp er (Mo del CW). In Model SW , users obtain their observations fro m a discrete m emoryless multiple source (DMMS), and comm unicate to e ach other via a noiseless au thenticated public chann el, with the objective of generating jointly held secret keys. In Model CW , one This work was supported in part by the Air Force Office of Scienti fic Researc h unde r gr ant F A9550-09- 1-0140, by a grant from the W isconsin Alumni Research Founda tion, and by the Nationa l Science Foundati on under CAREER grant CCF 084453 9. The work of V . Y . F . T an w as also supported by A*ST AR, Singapor e. This paper was presente d in part at Allerton Conference on Communica tion, Control and Computing in Monticel lo, IL (Septembe r 2011) [1]. T .-H. Chou is with Qualcomm Inc, San Diego , CA. V . Y . F . T an is with the Institut e of Infocomm Research, Singapore and the Departmen t of E lectr ical and Computer Engineering, National Uni versity of Singapore . S. C. Draper is with the Depa rtment of Electrical and Computer Enginee ring, Univ ersity of W isconsin, Madison, WI, 53706, USA (emails: tzuhanc@qt i.qualcomm.com; vtan@nus.ed u.sg; sdraper@ec e.wisc.edu). legitimate user ( the sender) controls the input o f a discrete memory less broadca st channel (DMBC), send ing info rmation based upon which the legitimate receivers generate secret k eys. Howe ver , many a pplications canno t be exactly modeled as either a source- or a c hannel-ty pe scenario . Th is work explores such a setting in which the sender has th e ability to use a pr i vate source of rando mness to excite (or influence) the “state” of the DMMS. T his is similar in spirit to recent works on probing capacity and channels with action-depen dent states [5]–[8]. W e derive capacity , reliability exponent, and secrecy exponent results for this setting. At one extreme, when the sender has an unlimited ability to excite the chan nel, and the ra te of pub lic discussion is similar ly unbo unded, a particular type of source em ulation strategy is capacity achieving. H owe ver , wh en constraints are placed on the rate of public discussion we demo nstrate th at source emulation becomes sub-o ptimal. W e show this throu gh the development of a more n uanced rate-lim ited excitation strategy that exceed s the capacity of the emulation-ba sed appro ach wh en subject to rate constrain ts [9]. Our ne w strategy co mbines a wiretap-ty pe probin g mech anism (Model CW) with a key-distillation step (Model SW) that is applied to th e residual rand omness. In general, we find an interplay to exist between the secr ecy rate derived from the wiretap ping step and th e secrecy rate derived via the key-distillation step. W e illustrate the tradeo ff via examples. I n term s o f ou r large deviation r esults we sh ow that there is a natural tradeo ff between th e reliability an d secrecy exponents. The fo rmer gener alize Gallager’ s classic r esults in in [10, Sec. 5.6 ] an d [11 ]; the latter may be specialized to Hayashi’ s recent work tha t character izes the rate of decay o f informa tion leakage [ 12] of the wiretap channels. A. Related W ork There are other in vestigations that consider non-source , non- channel mo dels. For example, in [13], [14] user s obser ve a DMMS and can also transmit inf ormation via a wiretap channel. Howev er, no pu blic discussion is allowed. The key generation scheme used is b ased on the obser vation that a p ub- lic message can be transmitted via the DMBC confidentially , resulting in a h igher secre t key rate. In [ 9], [1 5], [1 6], pu blic discussion is allowed and there may also be a helper . Ho wever , unlike o ur work, the sender does not also receive a seque nce as part of the chan nel output. The sender’ s ability to use both her channel output and he r sou rce of priv ate random ness to generate the secret key is a cruc ial aspects of our model. The authors in [1 7]–[21] co nsidered th e setting where a wiretap c hannel is influ enced by a random state that is k nown SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 2 by the sender (and possibly by the receiver) and thus can be tr eated as a correlated sou rce. In [17], [18], the sender transmits a confidential message and the random , no ncausally known, state is exploited to con fuse the eav esdrop per . Th e lower bound is pr oved using a co mbination of Gel’fand- Pinsker coding and wiretap chann el coding. A similar prob lem but with causal state informa tion is studied in [ 19] an d the co ding sche me inv olves block Markov cod ing, Shan non strategies, and wiretap coding. In [20], [21], the g oal is to generate a secret key whe n the en coder ( and/or decoders) have noncausal state informatio n. The authors present a single- letter expr ession for the secret key cap acity . The key rate consists of tw o parts. Th e first can be attributed to the rate of th e confidential message sent u sing wir etap ch annel cod ing where the state seq uence is treated as a tim e-sharing seque nce, while a seco nd key , indepen dent of the first, is prod uced b y exploiting the comm on knowledge o f the state at th e sender and the legitimate receiver . The model considered in this paper is a generalization of the “sourc e excitation” model of [22]. T hat mod el is motiv ated by the large b ody o f work on physical-lay er security (see, e. g., [23], [24]) where the unpr edictable variation in th e wire less channel mediu m serves as th e sour ce of common rando mness. One ap proach is to sound the wireless chann el using a rando m signal and measure th e observations generated ( marginalizing over the sounding si gna l). Th is “so urce emulation” strategy is con sidered in [24]. Another appr oach studied in [ 22], [23] uses deterministic sounding ( no marginalization is in volved). Ke y extraction f ollows by d enoising th e observations u sing a public message. Determ inistic sounding requires no sour ce of priv ate randomness (as does s our ce emulation), all randomness is due to the ch annel. The cu rrent genera lization is that we now explore the so urce excitation model when the exciter h as a source of p riv ate random ness. Th is allows us to exploit both random soun ding (using a wiretap code) an d key generation (using condition al randomn ess). W e regard the current model as stepping stone to u nderstand ing the fundame ntal limits of two-way r andomiz ed chan nel so unding in which secrecy rate is d erived from the use of two wiretap codes and from the condition al rando mness produ ced. B. Main Co ntributions: Capa city a nd Err or Expo nents Figure 1 sho ws th e system considered in this paper . W e can think of the term inal labeled Alice as a base station on ear th equippe d with a sensor . Th is b ase station transmits a random message M (the selection of which is based on a priv ate source of rand omness) securely to a satellite enco der . The satellite produ ces sequence S n accordin g to some conditional probab ility law . This sequ ence is the input to a br oadcast chan- nel p ( x, y , z | s ) (the wireless medium ). The ch annel p roduces observations X n , Y n and Z n , respectively received by Alice, the legitimate user Bob, and the malicious user Eve. The g oal of the two legitimate users is to generate a shared secret key – Alice based on ( M , X n ) and Bob based on (Φ , Y n ) , where Φ is a pu blic message kn own to all parties. W e first consider th e situation in wh ich there ar e no rate limits o n either the pub lic discussion ( Φ ) or the excitation Public Channel Alice Bob Eve p ( x, y , z | s ) ✻ ❄ Encoder S n M ❄ Y n ❄ X n ❄ Z n ❄ Φ ❄ K A ❄ K B Φ ✻ Φ ✻ Fig. 1. Our problem setup: Based on her pri vat e source of randomness M , Alice exc ites the channel via the sounding signal S n ( M ) . She generat es a public message Φ( M , X n ) , which is transmitted through the noiseless public channe l and hence known to all parties. Alice and Bob gen erate ke ys K A ( M , X n ) and K B (Φ , Y n ) respecti vel y . The keys should agree, while at the same time, they should be kept secret from Eve. signal ( M ) . W e derive a single-letter e xpr ession for the secret key capacity of this system. Th e resu lt follows throu gh a particular kind o f sou rce emulatio n wher e (i) Alice cho oses the optimum source distribution to indu ce (potentially subject to cost constraints on S n ), and ( ii) Alice has the vector observation ( S n , X n ) . W e then tu rn to the r ate-limited situation an d study the effect of r ate limits on (i) the achievable secr ecy rate, (ii) the probab ility of erroneous decoding at the legitimate recei ver , Bob, and (iii) the key leakag e rate by the eavesdropper, Eve. W e focu s on degrad ed ch annels and ch aracterize the error probab ility in terms of a r eliability exponen t and the key leakage rate in ter ms of a secr ecy exponent . In contr ast to [9] where the secret key capacity of on e-way key gen eration subject to a rate constrain t is c haracterized , we show that the flexibility Alice ha s in choosin g the amoun t of priv ate random ness she uses in the selection of M ca n allow a strictly higher achievable secret ke y rate than can be attained via pure source emulation. W e intro duce a new type of d ecoder for th e legitimate receiver , Bob, to use. This deco der is a combina tion of a maximum likelihood and a m aximum a -posteriori (ML- MAP) decoder . Bob decod es jointly th e send er’ s source X n and the sender’ s pri vate source of rando mness (or message) M . The resulting reliability exponent expression can be specialized to Gallager’ s chan nel cod ing err or expon ent [10, Sec. 5.6] and Gallager’ s source coding error exponent [11 ]. On the other hand, in the key leakage analysis, the secrecy exponen t we derive captures the leakage due to Eve’ s channel p ( z | s ) and the leakage due to the correlation between Alice’ s variable X an d Eve’ s variable Z in a tr ansparent m anner . Our analysis builds on the work by Hayashi in [12], [25], wher e he links the leakage rate of a wiretap chann el to channel resolvability and identification coding [26]. Th is con nection is also e xamine d Bloch and Laneman [27] where they derive the capacity of gen eral wiretap channels fro m an in formation spec trum perspective [26]. Our secrecy exponent r esults, which are developed in Section IV, can be specialize d to the wiretap channel [ 12], [ 25] an d to the secret key gen eration from cor re- SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 3 lated sou rce setting [12], [22], [28], [29]. Th e difference vis- ` a - vis the motivating work [22] is tha t the m ethods used to b ound the exponents for both reliability an d secrecy in volve both wiretap chann el co ding and source co ding. This will be come clear in Section IV wher e we specialize our results to various known pr oblems. Note th at the criter ion for expon ential d ecay of the key leakage rate is m uch stronger than the usual stron g secrecy [4]. W e focus o n this e xpon ential notion b ecause it quantifies h ow fast the error pro bability and in formation rate decays to zero and becau se it re veals a natural tradeoff between the attainable r eliability and secr ecy expon ents. C. P aper Or ganization This p aper is organ ized as follows: In Section II, we describe the system m odel. W e also defin e the secret key capacity , th e capacity-reliability-secr ecy region and the n otion of chan nel degrad edness. Our main re sults pertain ing to th e secret key capacity are provided in Section III. W e also prove a (sometimes loose) up per bound on the secr et key capacity th at does not contain any auxiliary random variables, and hence is am enable to evaluation. W e show tha t th is u pper b ound is tight for degraded channels. W e presen t the re liability and secrecy exponents i n Sectio n IV and conn ect to previous w ork. In Section V, we p resent se veral examples to d emonstrate how the main results can be ap plied to channe ls of inter est. W e show the inheren t tradeoff between the p ortions of th e secret key rate due to sou rce- and to channel- type randomness. W e also show the inherent tradeoff between the reliability exponent and the secrecy expo nent. The p roofs of the ca pacity theorems and the erro r exponent th eorems are provided in Section VI and Section VI I re spectiv ely . D. Notation W e gen erally adopt the notational conventions in the book by E l Gamal and Kim [3 0], some o f which we recap here. All logarithm s are to base- 2 . Random variables are in upper ca se (e.g., X ) and th eir rea lizations in lower case (e .g., x ). The co r- respond ing alph abets of rando m variables are in calligra phic font (e.g., X ) and so are all sets and events (e. g., C ). F or vectors, X i j , ( X j , . . . , X i ) a nd if j = 1 , the a bbreviation X i , X i 1 is used. In addition, X n \ i , ( X i − 1 , X n i +1 ) . The probab ility mass f unction (pmf) of a discrete random variable X is denoted as p X ( x ) or mo re simply as p ( x ) . Rando m codebo oks are denoted by a spe cial script f ont C while a codebo ok realization is deno ted as C . For an a ≥ 0 , we also common ly use the n otation [1 : 2 a ] , { 1 , . . . , 2 ⌈ a ⌉ } . I I . P R O B L E M S E T U P A. The Secr et Ke y Generation Pr otocol The setting is shown in Fig. 1. Consid er a 3-r eceiv er DMBC ( S , p ( x, y , z | s ) , X × Y × Z ) co nsisting of four finite sets S , X , Y , Z and a collection of cond itional pmfs p ( x , y , z | s ) on X × Y × Z . Alice, at ter minal X , controls the c hannel input sou nding sign al s n throug h the enco der v ia n uses of the chann el. A lice has a pr i vate source of ran domne ss used to select an index m , which influenc es s n . The legitimate receiver at terminal Y is known as Bob and the eavesdropper at term inal Z is kn own as Eve. There is also a noiseless pu blic discussion channel which allows Alice to tran smit a m essage Φ to Bob and Eve. Let Λ : S → [0 , Λ max ] be a per-letter , bound ed cost functio n an d let Γ > 0 be an ad missible cost. A (2 nR M , 2 nR Φ , n, Γ) code for the secret ke y generation protocol consists of a tu ple o f f unctions ( f , φ, k A ) . In p articular, 1) Channel E xcitation : Alice selects a message M ∈ [1 : 2 nR M ] unifo rmly at random. The (satellite) encod er sends a m essage-depen dent input sequ ence S n = f ( M ) ∈ S n ( f possibly b eing ran dom) satisfying P " 1 n n X i =1 Λ( S i ) ≤ Γ # = 1 . (1) The inp ut sequence S n is transmitted over n u ses of p ( x, y , z | s ) . The ou tput sequences x n , y n and z n are observed by Alice, Bob ( legitimate receiver) and E ve (eavesdropper) respectiv ely . 2) One-W ay ( F o rwar d) Pub lic Discussion : After ob serving x n , Alice gener ates a one- way public message 1 φ = φ ( m, x n ) ∈ [1 : 2 nR Φ ] , an d transmits it over a noiseless public ch annel. 3) K ey Generation : Alice generate s a key k A = k A ( m, x n ) ∈ N . Af ter rec ei ving h is chann el o utput y n and the pu blic message φ , Bob ge nerates anoth er key k B = k B ( y n , φ ) ∈ N . Note the conditional distribution of ( X , Y , Z ) given S can be factorize d as p ( x | s ) p ( y , z | x, s ) . Th e first conditional distri- bution p ( x | s ) can be roughly thought of as Alice’ s influence on the channel state via th e so unding signal s n , while the second p ( y , z | x, s ) can be th ought of as a state-dep endent chan nel. B. Definitions W e n ow provide the definitio ns of achiev able secret key rates, secret key capacity and error expon ents. As a reminder, the rand om variables K A and K B respectively d enote Alice’ s and Bob’ s key . The p ublic message is den oted as Φ . Definition 1 (W eak Achiev ability) . The secr et ke y r ate R SK ∈ R + is Γ -weakly -achiev able (or simply Γ - achievable) if ther e exists a sequence o f (2 nR M , 2 nR Φ , n, Γ) cod es (for any ( R M , R Φ ) pair) for th e secr et key generation pr otocol such that the following three con ditions are satisfied: lim n →∞ P ( K A 6 = K B ) = 0 , (2) lim n →∞ 1 n I ( K A ; Z n , Φ) = 0 , (3) lim inf n →∞ 1 n H ( K A ) ≥ R SK , (4 ) Definition 2 ((Forward) Secr et Key Cap acity) . The secret key capacity-co st function C SK (Γ) is defined as follows: C SK (Γ) := sup { R SK : R SK is Γ -weakly-achievable } . (5) 1 As in [30], we use a common notation φ to denote both the function φ : [1 : 2 nR M ] × X n → [1 : 2 nR Φ ] as well as the output of the function φ ∈ [1 : 2 nR Φ ] . This applies in the rest of the paper . SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 4 W e will hen ceforth say that C SK (Γ) is the (forward) secr et ke y c apacity ( without reference to the cost Γ ). The r eliability condition in (2) implies that we would like Alice’ s and Bob’ s keys to agree with high p robability . The secr ecy condition in (3) require s that the eavesdropper canno t estimate the key K A ∈ [1 : 2 nR SK ] gi ven her observation Z n and the public message Φ . This is manifested in th at the key lea kage rate 1 n I ( K A ; Z n , Φ) is arbitrarily small for sufficiently large blockleng th n . Th e rate cond ition in (4) imp lies that the entropy of K A should be clo se to R SK . In oth er words the pmf of K A should be clo se to that of a unifo rm pmf on [1 : 2 nR SK ] , so the eaves dro pper can o nly glean a negligible am ount of informa tion. In m any pr actical settings, th e fact that the erro r prob ability in ( 2) and th e key leakage rate in (3) can be m ade arbitrarily small with increasing block length is insuf ficient. See Maurer’ s work in [31] and a m ore rece nt exposition in [27]. I t would, in fact, b e desirable to quantify their rates o f dec ay an d to devise coding schemes to ensure that these decay ra tes are as large as p ossible. W e f ormalize th is by defining the notion o f an achiev able secr et key rate- exponent triple. T o simplify the exposition, in ou r defin itions (and cor respond ing results) of rates with expon ents, we w ill assume th at Γ = ∞ . In other words, we d o n ot im pose a co st constraint on S n as in (1). Definition 3 (Achiev able Secret Ke y Rate-Ex ponen t Triple) . The secr et key rate-e xpone nt triple ( R SK , E , F ) ∈ R 3 + is achiev able if there exists a sequ ence of (2 nR M , 2 nR Φ , n ) co des for the secr et ke y generation pr otoco l such that in addition to (4) , th e following hold: lim inf n →∞ − 1 n log P ( K A 6 = K B ) ≥ E , (6) lim inf n →∞ − 1 n log I ( K A ; Z n , Φ) ≥ F . (7) In (6), E is known as th e r eliability e xponen t and in (7), F is kn own as the secr ecy exponen t . Collecti vely , E an d F are known as err or e xponen ts (though I ( K A ; Z n , Φ) is not, strictly speaking, an erro r prob ability but we abuse ter minolog y to say that both are “erro rs”). Definition 3 can also be interpreted as follows: If a triple ( R SK , E , F ) is achievable, then the er ror probab ility in (2) d ecays 2 as P ( K A 6 = K B ) . ≤ 2 − nE and the key leakage decays as I ( K A ; Z n , Φ) . ≤ 2 − nF . Naturally , the constraint on the entro py of th e secret key in (4) is retained in the a bove definition. Definition 4 (Capacity- Reliability-Secrecy Region) . The (se- cret ke y) capacity-reliability-secr ecy region R ⊂ R 3 + is the closur e of the set of ac hievable secr et ke y r ate-exponent triples. In analogy to the n otion of weak achiev ability , we can also define a more string ent n otion known as stro ng achiev ability , also studied in [3 1], [3 2]. Definition 5 (Stron g Achiev ability) . The secr et key rate R SK is stron gly-achievable if ( R SK , E , F ) is achievable fo r some E > 0 and F > 0 . 2 Here and in th e followin g, for a pair of positi v e sequences { ( a n , b n ) } n ∈ N , we say that a n . ≤ b n if lim sup n →∞ n − 1 log( a n /b n ) ≤ 0 . T he not ation . ≥ is defined analogou sly . W e say that a n . = b n if a n . ≤ b n and a n . ≥ b n . W e conclu de our suite of definitions by fo rmalizing the notion of d egraded chann els. Definition 6 (Degradedn ess) . W e say that the DMBC p ( x, y , z | s ) is degraded if ( X , S ) − Y − Z form a Markov chain, i.e., p ( y , z | x, s ) = p ( y | x, s ) p ( z | y ) . In this case, we also say that the DMBC p ( x, y , z | s ) is de- graded in f avo r of Bob or equi valently that Eve’ s observation is a degraded version of Bob’ s. Note tha t we d o n ot differentiate between p hysical and stocha stic degraded ness [30, Ch. 5 ]. The capacity r esults will turn ou t to b e identical for both cases. I I I . B A S I C C A PAC I T Y R E S U LT S W e present our cap acity results in this section. These correspo nd to Defin itions 1 and 2 and we em phasize that R M and R Φ are uncon strained h ere. W e le verage on a source emulation result by Ahlswede-Csisz ´ ar [3] to gi ve a single-letter expression for the secret key capacity containing two aux iliary random variables takin g into acco unt that S n has to satisfy the cost co nstraint in (1). W e also provide a looser upper bo und that contains no aux iliary random v ariables. The upp er bound is tig ht when the DMBC is degrad ed in f av or of Bob. The capacity results in this sectio n moti vate the more r efined error exponent analy sis in the following section wher e R Φ can be constrained an d we will see that a judicious choice of R M does not r educe C SK in the case of degraded DMBCs. Proposition 1 (Secret Key Capacity) . The secr et key cap acity of DMBC ( S , p ( x, y , z | s ) , X × Y × Z ) is C SK (Γ) = max [ I ( U ; Y | W ) − I ( U ; Z | W )] , (8) wher e the maximization is over all joint d istrib ution s th at fac- tor in accordance to W − U − ( X , S ) − ( Y , Z ) or equ ivalently , p ( w, u , s, x, y , z ) = p ( w ) p ( u | w ) p ( x, s | u ) p ( y , z | x, s ) (9) such tha t E [Λ ( S )] ≤ Γ . By re peated applicatio ns of Bayes rule, th e d ecomposition in ( 9) can be wr itten as p ( w, u , s, x, y , z ) = p ( w | u ) p ( u | x, s ) p ( s ) p ( x, y , z | s ) . (10 ) Since the DMBC p ( x, y , z | s ) is gi ven, the optimizatio n in (8) is over the source distribution p ( s ) and the auxiliary conditional distributions p ( w | u ) an d p ( u | x, s ) . Further more, b y using the Fench el-Eggleston -Carath ´ eod ry Theorem [30, App. C], it can be argu ed that the c ardinalities of the aux iliary random variables W and U can be bo unded as |W | ≤ |X ||S | + 3 and |U | ≤ ( |X ||S | + 3)( |X ||S | + 1 ) respectiv ely . Pr oof of Pr oposition 1: Achiev ability follows from [3, Theorem 1] fo r Model SW with a slight modification to ac- count f or co st constraint o n S n in (1). Fix an ǫ > 0 and a join t distribution in (9) ach ieving E [Λ( S )] ≤ Γ 1+ ǫ . Let S ∼ p S ( s ) be the S -marginal of (9) and let its typical set 3 be T ( n ) ǫ ( S ) . Index all the elemen ts in T ( n ) ǫ ( S ) as [1 : |T ( n ) ǫ ( S ) | ] . W e ar e 3 The typical set defined in T ( n ) ǫ ( S ) [30, Sec. 2.4] consists of all sequence s s n whose typ e (empirical distrib ution) π ( s ; s n ) sati sfies | π ( s ; s n ) − p S ( s ) | ≤ ǫ p S ( s ) for ev ery s ∈ S . The typi cal aver age lemma [30, Sec. 2.4] implies that n (1 − ǫ ) H ( S ) ≤ log |T ( n ) ǫ ( S ) | ≤ n (1 + ǫ ) H ( S ) . SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 5 only going to excite the DMBC p ( x, y , z | s ) using sequences belongin g to T ( n ) ǫ ( S ) . By the typical average lemma [3 0, Sec. 2.4 ], th is ensures that for every n , the almost sure cost constraint in ( 1) is satisfied. The encoder h as the co deboo k T ( n ) ǫ ( S ) , which is known to all parties. Alice gene rates an index M ∈ [1 : |T ( n ) ǫ ( S ) | ] unifor mly at ran dom so in this coding scheme, R M = 1 n log |T ( n ) ǫ ( S ) | = H ( S ) + δ ( ǫ ) f or som e δ ( ǫ ) ↓ 0 as ǫ ↓ 0 . Giv en M , the encoder transmits the sequence indexed by M in the codeboo k. Note that p n S ( T ( n ) ǫ ( S )) is ar bitrarily close to one for large enoug h n . Hence, just as in the pro of of [3, T heorem 1], we can consecutively select mutually disjoint wiretap codes {C i } N i =1 from T ( n ) ǫ ( S ) × X n (with η in [3, Eq. (4.1)] replac ed by 2 η , say) where each codebo ok C i contains codewords of the same ty pe. The rest o f the p roof in [3, Theorem 1] follo ws verbatim with our ( X, S ) in th e role of X there. This allows us to assert that I ( U ; Y | W ) − I ( U ; Z | W ) is a one-way (forward) achiev able key r ate. No te that in our setting, Alice r eceiv es X n and also h as S n (a function of her priv ately gener ated index M ), Bob r eceiv es Y n and Eve receives Z n . The proo f is comp leted b y taking ǫ ↓ 0 and using the continuity of Γ 7→ C SK (Γ) . That C SK (Γ) is co ntinuou s follows f rom the continuity of I ( U ; Y | W ) , I ( U ; Z | W ) and E [Λ( S )] in (9). The con verse proof of Theorem 1 is st and ard and we provide it in Section VI-A for co mpleteness. It relies on a simple application of the Csisz ´ ar-sum-id entity [30, Sec. 2.3] and an approp riate identification of the auxiliar y random v ariables that satisfy the Ma rkov condition s in (9). T o find the secret key c apacity for spec ific channels, two auxiliary rando m v ariables W and U solving (8) h av e to be identified. T his may be a dif ficult task. In the next prop osition, we pr ovide an (alb eit loo ser) upp er bound which does n ot in volve any aux iliary random variables. This resu lt will turn out to b e important in Section V where we present several channels for which we can calcu late the secret key capacity- cost function in clo sed-form . Proposition 2 (Up per Bound in Secret K ey Capa city) . The secr et ke y capacity is up per b ounded a s C SK (Γ) ≤ max I ( X , S ; Y | Z ) , (11) wher e the maximization is over all input d istrib ution s p ( s ) such tha t E [Λ ( S )] ≤ Γ . The proof of this p roposition is given in Section VI-B. Roughly speaking, the expression in (1 1) can be interpreted as the secret key ca pacity when Alice and Bob have full knowledge (side inform ation) o f Eve’ s o bservation Z , h ence the co nditionin g o n Z . W e no te by using the techniques in Ahlswede-Csisz ´ ar [3] (and in par ticular Lemm a 2 .2 therein) that o ur u pper b ound also holds for the scenario where the parties Alice and Bob can exchange multiple messages– the multi-way discussion scen ario. In the case of d egraded p ( x, y , z | s ) , the result in Prop osi- tion 2 is tigh t. Corollary 3 (Secr et Key Capacity of Degraded DMBCs) . If the D MBC p ( x, y , z | s ) is degraded , the secr et ke y capacity is C SK (Γ) = max [ I ( X , S ; Y ) − I ( X , S ; Z )] , (12) wher e the maximization is over a ll inpu t distributions p ( s ) such tha t E [Λ ( S )] ≤ Γ . Pr oof: For achiev ability , we can choose W = ∅ and U = ( X , S ) in (8). The Mar kov condition in ( 9) is satisfied. For the c on verse, we obser ve from Propo sition 2 th at th e secret key cap acity o f the degrade d DMBC can be up per bound ed as C SK (Γ) ≤ I ( X , S ; Y | Z ) (13) = I ( X, S ; Y ) − I ( X, S ; Z ) . (14) The last equ ality is due to the fact th at for degraded channels, ( X, S ) − Y − Z fo rms a Mar kov chain. Notice th at fo r a fixed p ( s ) , the difference of m utual informa tions in (12) c an b e decompo sed into two par ts: I ( X , S ; Y ) − I ( X , S ; Z ) = R ch [ p ( s )] + R src [ p ( s )] , (15) where the channe l a nd sou rce rates are respec ti vely defined as R ch [ p ( s )] , I ( S ; Y ) − I ( S ; Z ) , and (16) R src [ p ( s )] , I ( X ; Y | S ) − I ( X ; Z | S ) . (17) The first rate R ch [ p ( s )] can b e interpreted as the confidential message rate of the wiretap channel p ( y , z | s ) [33]. Th e second rate R src [ p ( s )] is the secret key rate fro m an excited corr elated source ( X, Y , Z ) previously studied in [22] for a particular sounding signal s n with typ e p ( s ) . In th e present setu p, s n is randomly chosen by Alice. As such , we can optimize over its distrib ution p ( s ) to find the largest “sum rate” R ch [ p ( s )] + R src [ p ( s )] . It turns out that there is a natu ral interplay an d tradeoff b etween R ch [ p ( s )] and R src [ p ( s )] . W e illustra te this numerically u sing an example in Section V -A. W e pr ovide an alternative p roof of the capacity of degrad ed DMBCs via th e erro r exponent r oute in the next section. W e note that the flexibility of the amount of priv ate rand omness that Alice has in the form of the rand om message M (which we d id not exploit in this section) allows us to op erate at a lower R Φ and yet result in a p ositi ve c apacity . I V . E R RO R E X P O N E N T T H E O R E M In this section, we present an inner b ound for the secret key capacity-r eliability-secrecy region p er Definition 4. Our general result is then specialized to other known re sults in the literature. Recall that for the error e xpo nent results, we consider th e case when there is no cost constraint o n the codewords for simplicity ( i.e., Γ = ∞ ). W e make th e fo llowing two o bservations when we employ the achiev ability strategy pro posed in this paper which is a ran dom binnin g scheme. First, the decod ing error pro ba- bility P ( K A 6 = K B ) is only a fun ction of margina l distri- bution p ( x, y , s ) = p ( s ) p ( x, y | s ) . Secon d, the key leakag e I ( K A ; Z n , Φ) is only a functio n of m arginal distribution p ( x, z , s ) . Th is means that we can characterize the achiev able reliability and secrecy exponents separately as functio ns of each marginal distribution. SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 6 A. Basic Definitions Before we present ou r r esult, we begin with a few defin i- tions. Let ˜ E (1) o ( p ( s ) , ρ, R Φ ) , ρR Φ − log X s,y p ( s ) p ( y | s ) " X s,x p ( x | y , s ) 1 1+ ρ # 1+ ρ , (18) ˜ E (2) o ( p ( s ) , ρ, R Φ , R M ) , ρ ( R Φ − R M ) − lo g X s " X x,y p ( s ) p ( x, y | s ) 1 1+ ρ # 1+ ρ , (19) ˜ E (3) o ( p ( s ) , ρ, R Φ , R M ) , ρ ( R Φ − R M ) − lo g X y " X s,x p ( s ) p ( x, y | s ) 1 1+ ρ # 1+ ρ . (20) As well, define E o ( p ( s ) , R Φ , R M ) , min n max 0 ≤ ρ ≤ 1 ˜ E (1) o ( p ( s ) , ρ, R Φ ) , max 0 ≤ ρ ≤ 1 ˜ E (2) o ( p ( s ) , ρ, R Φ , R M ) , max 0 ≤ ρ ≤ 1 ˜ E (3) o ( p ( s ) , ρ, R Φ , R M ) o . (21) Similarly , define ˜ F o ( p ( s ) , α, R SK , R Φ , R M ) , − α ( R SK + R Φ − R M ) − log X x,z ,s p ( x, z , s ) p ( x, z | s ) p ( z ) α , (22) F o ( p ( s ) , R SK , R Φ , R M ) , sup 0 <α ≤ 1 ˜ F o ( p ( s ) , α, R SK , R Φ , R M ) . (23) W e now define a rate-exponen t region parameterized by the in- put distribution p ( s ) and th e pair of aux iliary r ates ( R Φ , R M ) : ˜ R ( p ( s ) , R Φ , R M ) = n ( R SK , ˜ E , ˜ F ) ∈ R 3 + : ˜ E ≤ E o ( p ( s ) , R Φ , R M ) ˜ F ≤ F o ( p ( s ) , R SK , R Φ , R M ) o . (24) B. The Inner Bo und The following the orem p rovides an in ner bou nd to th e capacity-re liability-secrecy r egion R . Theorem 4 (In ner Boun d to the Capacity-Reliability- Secrecy Region) . The union of the r e gions in (24) is a n inner bo und to the secret key cap acity-r eliability-secrecy re gion, i.e., [ p ( s ) ,R Φ ,R M ˜ R ( p ( s ) , R Φ , R M ) ⊆ R . (25) The pr oof of this the orem can b e foun d in Section VII an d hinges on an ML-MAP decoding strategy . More p recisely , giv en ( y n , φ ) , Bob first uses the following ru le to estimate Alice’ s so urce of p riv ate random ness ˆ m an d Alice’ s r eceiv ed sequence ˆ x n : ( ˆ m, ˆ x n ) , arg max ( m,x n ): φ ( m,x n )= φ p ( y n | s n ( m )) p ( x n | y n , s n ( m )) . (26) The functio n φ ( m, x n ) is a (ran dom) binning function , which is defined and discussed in greater detail in Section VII-A. The exponents ˜ E (1) o and ˜ E (2) o represent th e m arginal events { ˆ M = M , ˆ X n 6 = X n } and { ˆ M 6 = M , ˆ X n = X n } , respectively . The former is a Slepian-W olf-type e xpo nent [1 1] ( X to be reconstruc ted given vector side-in formation ( Y , S ) ) while the latter is a chan nel coding -type exponen t [10, Sec. 5 .6] (inpu t S and vector outp ut ( X , Y ) ). The expo nent ˜ E (3) o represents the joint er ror event ˆ M 6 = M , ˆ X n 6 = X n and is a hybr id of Slep ian-W olf and chann el cod ing. Upo n the decoding of ( ˆ m, ˆ x n ) , Bob declares h is key to be k B = k ( ˆ m, ˆ x n ) , wh ere k ( · , · ) is another ( random ) binning f unction. Th e pr oof fo r the secrecy exponent le verages on the pr operties of the R ´ enyi entropy as in [12], [22]. The unio n o f the r egions in (25) is likely to be a stric t inner bound since our coding scheme does not in volve the use of any auxiliary rand om variables (un like in Prop osition 1). Howe ver , as we shall see in Sec tion IV -D , our an alysis of the ML-MAP strategy shows that all we akly-achievable rates R SK < C SK are strongly-ach iev able for degra ded chann els. Another reason as to wh y the er ror expon ent region is likely not tight may be distilled from works by Csisz ´ ar-Narayan [15], later exten ded by Go hari-Anan tharam [34], [35]. Co nsider an external agent who can recover X n perfectly after r eceiving Eve’ s info rmation ( Z n , Φ) an d the shared secret key K A . If the agent were not able to recover X n there would be some piece of informatio n about X n , independ ent of ( Z n , Φ , K A ) , that th e external agent would requir e to know X n perfectly . In such a setting, Alice could re veal the needed informatio n on the pu blic ch annel withou t lo wering the secret key r ate. This follows since what would b e revealed is in depend ent of K A , and thus of n o use to Eve. Th us, without lo ss of generality , we can a ssume th e external agent knows X n perfectly . Now , say that Z is a degraded version of Y . In this setting Bob can simulate Z n . Bob also ha s (Φ , K B ) ( note that K B = K A with high probab ility). So, Bob too c an be assume d to recover X n perfectly . In other w ords, in the degraded setting there is no lo ss in generality in requiring Bob to recover X n . Howe ver , when there is a non -trivial joint distribution amongst X , Y and Z (i.e., the non- degraded case), it is not necessarily tru e that Bob can re cover X n . Hen ce the error- exponent strategy may be strictly suboptima l (at least in a capacity sense for no n-degrade d chan nels). This observation is consistent with the “separation” strategy elucid ated in (16) and (17) as the separation strategy–which is optimal in th e degraded case–in effect imp lies that Bob can decode X n as discussed in the pr evious paragrap h. C. P ositivity o f Err o r Expon ents and Interpr etations For a particular choice of in put distribution p ( s ) , the follow- ing pr oposition character izes the bo undar y of the achiev able rate-expone nt region in (24). Proposition 5 (Positivity of E rror Ex ponen ts) . F or a fixed p ( s ) , the exponen t E o ( p ( s ) , R Φ , R M ) in (21) is positive if R Φ > H ( X | Y , S ) and (27) R Φ − R M > H ( X | Y , S ) − I ( S ; Y ) . (2 8) SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 7 R Φ R M H ( S ) I ( S ; Y ) I ( S ; Y ) 0 − H ( X | Y , S ) H ( X | Y , S ) H ( X, S | Y ) R M = R Φ + I ( S ; Y ) − H ( X | Y , S ) E + o A t t B Fig. 2. The re gion where E o ( p ( s ) , R Φ , R M ) is positi ve is denoted by the shaded set E + o . See (27) and (28). Points A = ( H ( X | Y , S ) , I ( S ; Y )) and B = ( H ( X , S | Y ) , H ( S )) respect iv ely den ote the two-ste p approach (of Bob first reco vering M through channel decoding and then recove ring X n via Slepi an-W olf decoding) and the sourc e emulation approac h (with vect or source ( X, S ) giv en Y ju st as in the achie v ability proof of Proposition 1) discussed in greater detail in Section IV -E-III. The semi-infinite ray emanating from A , passing through B , and ext ending northeast is the capacity-a chie ving set of ( R Φ , R M ) for our error exponent s cheme. For source emulation it only starts from B and exten ds northe ast. See Fig . 2. Similarly , the exponent F o ( p ( s ) , R SK , R Φ , R M ) in (23) is po sitive if R SK + R Φ − R M < H ( X | Z, S ) − I ( S ; Z ) . (29) See F ig. 3. The propo sition can be proved by firstly verifying th at ˜ E ( j ) o , j = 1 , 2 , 3 ( resp. ˜ F o ) are concave functions of ρ (resp. α ); secondly by com puting the partial der i vati ve of ˜ E ( j ) o (resp. ˜ F o ) with r espect to ρ (resp. α ); an d finally by ev aluating the slope at ρ = 0 (r esp. α = 0 ). This is a stand ard calculation and as such, we omit the d etails. See [22, Theorem 3] and the accompanyin g remarks for similar calculations. Note that there are on ly two rate con straints for reliability in ( 27) and (2 8). This is because th e ra te constraint req uired for ˜ E (2) o > 0 is R M − R Φ < I ( X, Y ; S ) (30) which is already implied by (28) since I ( S ; Y ) − H ( X | Y , S ) = I ( X , Y ; S ) − H ( X | Y ) ≤ I ( X , Y ; S ) . Note th at in the deriv a- tion of ˜ E (2) o and (30), we tr eat ( X , Y ) as a vector output of a chann el w ith input S . W e had mentio ned pre viously that R Φ can be redu ced and ye t th e secret-key capacity would remain u nchang ed if we red uce R M accordin gly . Howe ver , we observe from (27) that there is nevertheless a lower bound on R Φ due to a margina l error ev ent. Thus, R Φ cannot be r educed arbitrarily , and in particu lar not beyond the conditional entropy H ( X | Y , S ) . Intuitively , the co rner point in Fig. 2 (point A ) where R Φ = H ( X | Y , S ) and R M = I ( S ; Y ) may be achieved from a two-step decod ing procedur e wh ere Bob first recovers M th rough cha nnel d ecoding given Y n and then recovers X n via Slepian- W olf decod ing giv en the vector side-inf ormation R Φ R M 0 R M = R Φ + R SK + I ( S ; Z ) − H ( X | Z, S ) R SK + I ( S ; Z ) − H ( X | Z, S ) E + o ∩ F + o ❅ ❅ ❅ ❘ Fig. 3. This is the same as Fig. 2 with (29 ) also illustra ted. The region w here E o ( p ( s ) , R Φ , R M ) and F o ( p ( s ) , R Φ , R M ) are both positi ve is denoted by the shaded set E + o ∩ F + o . This combine s the rate constraints in (27), (28) and (29). The intuition here is the follo wing: T o maximiz e R SK , the line indicated by the equation R M = R Φ + R SK + I ( S ; Z ) − H ( X | Z, S ) should be shifted upward s unt il the shaded regi on almost v anishes. ( S n ( M ) , Y n ) ( M a ssumed to be decoded correctly). This two- step decod ing procedu re is, howe ver , no t what we do in th e ML-MAP de coding scheme in (26). The ML-MA P deco ding scheme decod es M and X n jointly so its expone nt is likely to b e higher than th e two-step deco ding scheme. The first r ate co ndition in (28) for the reliab ility exp onent to b e positiv e may be rewritten as fo llows: R M < I ( S ; Y ) + [ R Φ − H ( X | Y , S )] . (31) Using ( 31), we see tha t if R Φ > H ( X | Y , S ) (i.e., the compression r ate is strictly larger than the Slepian -W olf limit H ( X | Y , S ) as allowed by (27)), we may transmit the m essage M r eliably at rates higher than I ( S ; Y ) , which is the maximum transmission rate when the input distribution p ( s ) is used fo r the c hannel p ( y | s ) . The rate condition in (2 9) fo r th e secrecy exponent to b e positive m ay be written in th e fo llowing equiv alent f orms: R SK + R Φ < H ( X | Z, S ) + [ R M − I ( S ; Z )] , (32a) R M > I ( S ; Z ) − [ H ( X | Z, S ) − ( R SK + R Φ )] . (32 b) The authors in [ 22, Theore m 3] showed that the secrecy exponent is p ositi ve when R SK + R Φ < H ( X | Z , S ) . Howe ver , we observe f rom (32a) that if R M > I ( S ; Z ) (i.e., the message rate is larger than wha t Eve can resolve with her channel p ( z | s ) ), th e secrecy expon ent is positive e ven though R SK + R Φ may be larger th an H ( X | Z , S ) . Similarly , obser ve from (3 2b) that if R SK + R Φ < H ( X | Z , S ) , then R M may b e smaller th an I ( S ; Z ) for the secrecy expone nt to be p ositiv e. D. Str ong A chievability and Con nections to Degradedness Assume that the DMBC p ( x, y , z | s ) is degrad ed. W e then eliminate th e rates R Φ and R M in (28) and (2 9) a nd conc lude SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 8 T ABLE I S P E C I A L I Z A T I O N O F P R O P O S I T I O N 5 T O E X I S T I N G RE S U LT S Special ization Relia bility E o Secrec y F o I X = ∅ Channel coding W iretap channel R Φ = 0 [10, Theorem 5.6.2] coding [12, Theorem 3] II S = ∅ Source coding with Secret ke y generation with R M = 0 side informati on [11] public discussion [12] Source emulation Source emula tion III R M = H ( S ) ( X, S ) ( X, S ) applie d to [11] applie d to [12 ] that R SK is strongly- achiev able if R SK < H ( X | Z, S ) − I ( S ; Z ) − ( H ( X | Y , S ) − I ( S ; Y )) = I ( X ; Y | S ) − I ( X ; Z | S ) − I ( S ; Z ) + I ( S ; Y ) = I ( X, S ; Y ) − I ( X, S ; Z ) = I ( X, S ; Y | Z ) ; (33) per (27) we also req uire th at R Φ > H ( X | Y , S ) . The last equality holds due to the assumption of degraded ness, cf. Defn. 6. See Fig. 3. This concur s with the result fo r the secret key capacity for degraded channels o btained using pure source emulation in Coro llary 3. This altern ativ e method of deriving the secret key capacity for the degra ded case via the erro r exponent rou te demo nstrates that for degrad ed channels, the weak and strong definition s for achie vability (in Definitions 1 and 5 respectively) c oincide. E. Connections to Pr evious Results The reliability exponent in (20) is akin to a combin ation o f Gallager’ s e xpo nents f or channel coding [10, Sec. 5.6] and for sou rce coding with side infor mation [11]. The secr ecy exponent has been studie d for the secret key agreem ent sourc e model [12], [28], the correspond ing chann el model [1 2], and the sour ce model with extern al deterministic excitation [22]. Hayashi [12], [25] also analyzed the expo nential decay of the info rmation leakage rate for th e wiretap chan nel. The expression in (22) is akin to a com bination of the key leakage rate d ue to Eve’ s DMC p ( z | s ) [1 2] and the secrecy expo nent of the excited DMMS p ( x, z | s ) [22]. In light o f the se o bservations, Proposition 5 may be special- ized to der iv e con ditions for the p ositivity of the exponen ts for the pure channel-typ e and the pu re so urce-typ e models: I. A lice has no access to the channel outpu t ( X ← ∅ ) and no pu blic discussion ( R Φ = 0 ) : This case sp ecializes to the wiretap ch annel p ( y , z | s ) . In this c ase, the reliability exponent E o ( p ( s ) , 0 , R M ) reduces to that of cha nnel coding over a discre te memoryless chan nel (DMC) [10, Theorem 5.6.2] and (28) re duces to the co ndition R M < I ( S ; Y ) , (34) which we reco gnize as the cond ition for reliab le com mu- nication over the DMC p ( y | s ) . In addition , our secrecy exponen t F o ( p ( s ) , R SK , 0 , R M ) reduces to Haya shi’ s wiretap secrecy exponen t in [1 2, Eq. (14 )] and (33) red uces to the co nfidential message rate constraint R SK < I ( S ; Y ) − I ( S ; Z ) , (35) which we recogn ize as the cond ition for reliab le com mu- nication and secrecy for the wir etap channe l. Note that the u sual auxiliary random variable “ U ” [ 30, Theor em 22.1] has been taken to be equal to the source S in (35). II. Alice h as no con tr ol of the channel inpu t : This case specializes to the secret key generatio n mode l wit h pub lic discussion character ized by the DMMS p ( x, y , z ) = P s p ( s ) p ( x, y , z | s ) studied in [4], [15], [1 6], [34], [35]. The reliability e xpo nent was character ized in [11] and was stated as a special case of th e main result in [ 22]. By letting S ← ∅ and R M = 0 , (28) simplifies to R Φ > H ( X | Y ) (36) which we rec ognize as the co ndition for lossless sourc e coding of X given side inform ation Y [36]. This recovers an analogue o f th e r esult in [2 2, The orem 3 ]. Ineq uality (36) also c oncurs with ( 27). W e remark th at W atanabe et al. [29] showed that strong ly secure privac y amplification is not achievable by Slepian- W olf coding . But this does not con tradict o ur error exponent r esult bec ause the c odes u sed in [29] have rates tending to the optimal co mpression rate H ( X | Y ) in (36) at a rate of b / √ n fo r some b ∈ R (cf. [37]) . Howe ver , we operate at rates strictly above H ( X | Y ) in (36) so strong secrecy is indeed possible. The secrecy expo nent F o ( p ( s ) , R SK , R Φ , 0) was der iv ed in [ 12], [22], [28]. Ou r secrecy expo nent result in (29) specializes in this case to R SK + R Φ < H ( X | Z ) (37) which recovers an analogu e of the main result in Ch ou et al. [22, T heorem 3]. III. Alice e xcites the channel with S n generated in an i.i.d. manner accor ding to p S and considers th e joint variable ( X, S ) as her sour ce : This is similar to the sour ce emulation scheme adopted in the pro of of Proposition 1 witho ut cost con straint and ignoring the encoder but considerin g th e three term inals: Alice with ( X, S ) , Bob with Y , and Eve with Z . This is point B in Fig. 2. The reliability and secrecy exponents will be o f th e fo rm in [11] and [12], respectiv ely , with i.i.d. source ( X , S ) . Thus substituting R M = H ( S ) in ( 28) an d ( 29) yields R Φ > H ( X | Y , S ) − I ( S ; Y ) + H ( S ) = H ( X , S | Y ) ( 38) R SK + R Φ < H ( X | Z, S ) − I ( S ; Z ) + H ( S ) = H ( X , S | Z ) . (39) Upon the elimination of R Φ which, by (38), satisfi es the required lower boun d in (27), we hav e R SK < H ( X , S | Z ) − H ( X , S | Y ) = I ( X, S ; Y ) − I ( X, S ; Z ) . (40) Notice that the difference o f mutu al inform ations on the RHS of (40) is I ( X , S ; Y | Z ) for degraded DM BCs. Th is concur s with the secret key capacity of degraded DMBCs in Corollary 3. SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 9 0 0.2 0.4 0.6 0.8 1 0 0.02 0.04 0.06 0.08 0.1 0.12 0.14 0.16 β R SK ( β ) R SK R ch R src Fig. 4. Secret ke y rate of the binary on-off channe l as a function of β . The input S ∼ Bern ( β ) . The parameters are q = 0 . 5 , ˜ q = 0 . 8 , δ = 0 . 1 , δ 3 = 0 . 2 . Note that C SK = max β ∈ [0 , 1] R SK ( β ) and the maximizing β ∗ ≈ 0 . 59 . As is m entioned in th e Introd uction, wh ile the sour ce emulation scheme achieves the secret key capacity , this rate cann ot be strongly achieved (per Definition 5) if R Φ is upper bo unded by some quantity (but nonetheless still satisfies the lower bo und in (27)) if we do n ot also have the flexibility to concur rently set the rate of the sounding signal R M . Ob serve that the lower bound on R Φ in (3 8) resulting from the pure source emula tion strategy ( cf. the achiev ability pro of o f Pro position 1) is H ( X, S | Y ) which is at least as large as H ( X | Y , S ) in (27) in Proposition 5 and, in general, is strictly lar ger . Thus, our erro r expon ent sch eme which inv olves wiretap coding plus key distillation allows us to r educe R Φ from H ( X, S | Y ) to H ( X | Y , S ) –the dif feren ce being H ( S | Y ) . The specializations are summ arized in T ab le I. V . N U M E R I C A L E X A M P L E S W e co nsider two examples in this section. The first exam ple illustrates th e tradeoffs in volved in th e cap acity results in Section III. Th e second example illustrates the tradeoffs in the achiev able erro r expo nent results in Section IV. A. Capacity of the Bin ary On -off Channel For ou r first example consider the b inary o n-off model X = H · S ⊕ N 1 Y = H · S ⊕ N 2 Z = ( ˜ H · H ) · S ⊕ N 3 , where all the variables are b inary and where th e operatio ns are perform ed in the field of size 2 . Hen ce, the addition above is is b inary mod ulo-2 addition . The “ch annel gain” H is Bern ( q ) and ˜ H is Bern ( ˜ q ) . 4 Noise N i is Bern ( δ i ) an d the N i are mutually independ ent. The channel d escribes a model 4 W e say that a binary random vari able X is Bern ( γ ) if Pr[ X = 1] = γ . in which, in the absence of noise, Eve’ s observation is strictly worse than that of Alice’ s and Bob’ s since ˜ H is present. If δ 1 = δ 2 = δ and ˜ q δ < δ 3 , then Eve’ s channel outpu t is a degraded v ersion of Bob’ s. In this case, there e xists a Z ′ , ˜ H ′ · Y ⊕ N ′ 3 for some ˜ H ′ , with the same distribution as ˜ H , and independ ent N ′ 3 ∼ B ern ( δ ′ 3 ) su ch that ( X , S ) − Y − Z ′ , where δ ′ 3 = δ 3 − ˜ q δ 1 − 2 ˜ q δ . Let S ∼ Bern ( β ) . The first term of R ch is I ( S ; Y ) = H ( Y ) − H ( Y | S ) = H b ( β q ∗ δ ) − [ β H ( Y | S = 1) + (1 − β ) H ( Y | S = 0)] = H b ( β q ∗ δ ) − β H b ( q ∗ δ ) − (1 − β ) H b ( δ ) , where H b ( · ) is the bin ary en tropy function and the oper ation a ∗ b , a (1 − b ) + (1 − a ) b . Similarly , the second term of R ch can be expre ssed as I ( S ; Z ) = H b ( β ˜ q q ∗ δ 3 ) − β H b ( ˜ q q ∗ δ 3 ) − (1 − β ) H b ( δ 3 ) . The secret key rate due to sou rce X can be calculated as R src = I ( X ; Y | S ) − I ( X ; Z | S ) = β [ I ( X ; Y | S = 1) − I ( X ; Z | S = 1)] = β [ H b ( q ∗ δ ) − H b ( δ ∗ δ ) − H b ( ˜ q q ∗ δ 3 ) + (1 − q ∗ δ ) H b ( δ ′ 3 ) + ( q ∗ δ ) H b ( ˜ q ∗ δ ′ 3 )] . The second equality follows because if S = 0 , the sourc e is not observed and so there is no mutual inform ation between X and Y (no r between X and Z ). The secret key rate when the inpu t is a Ber n ( β ) sour ce is R SK ( β ) = R ch ( β ) + R src ( β ) which is p lotted in Fig. 4 as a function of β for the fo llowing param eters: q = 0 . 5 , ˜ q = 0 . 8 , δ = 0 . 1 , δ 3 = 0 . 2 . No te that R ch is a co ncave function of β while R src is a lin ear fun ction of β . I f β = 0 then R SK = 0 since X, Y , Z are jointly statistically indepen dent. On the other hand, if β = 1 then S n is the all o nes sequ ence and the R src is maximal since the input excites all common randomness due to the common on-off coefficient H . Howev er, when β = 1 , the secrecy rate of the wiretap channel R ch = 0 . As we decrease β R ch initially incr eases faster than R src decreases, resulting in the maximu m R SK being achie ved at an intermediate value of β . In this example we ha ve observed an inheren t tradeoff between the amount of the secret key rate d ue to common random ness and due to wir etap secrecy . B. Err or Exp onents W e no w illustrate our err or expo nent results. W e assume that all variables are binary valued, i.e., X = Y = Z = S = { 0 , 1 } . W e selected the para meters o f th e DMBC p ( x, y , z | s ) to e nsure that Eve’ s observation Z is a d egraded version of Bob’ s Y . W e do so by fir st selecting the param eters of the condition al distribution p ( x, y | s ) , then we proceeded to choose the p arameters in the conditional distribution p ( z | y ) . W e keep the chan nel p ( x, y , z | s ) fixed throu ghout this subsection. Define the input distribution-optimized r eliability exponen t E r ( R Φ , R M ) , max p ( s ) E o ( p ( s ) , R Φ , R M ) , (41) SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 10 0.7 0.8 0.9 1 1.1 1.2 1.3 1 .4 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 0.45 R Φ E r (R Φ , R M ) R M = 0.1 R M = 0.2 R M = 0.3 Fig. 5. Plot of the random coding reliabi lity exponen t E r in (41) 0.4 0.5 0.6 0.7 0.8 0.9 1 0 0.1 0.2 0.3 0.4 0.5 0.6 R Φ F r (R SK , R Φ , R M ) R M =0.3, R SK =0.01 R M =0.3, R SK =0.05 R M =0.2, R SK =0.01 R M =0.2, R SK =0.05 R M =0.1, R SK =0.01 R M =0.1, R SK =0.05 Fig. 6. Plot of the random coding secrec y expon ent F r in (42) where E o was defin ed in (21) . Also define the input distribution-optimized secr ecy exponent : F r ( R SK , R Φ , R M ) , max p ( s ) F o ( p ( s ) , R SK , R Φ , R M ) , (42) where F o was de fined in (23). Note th at fo r a par ticular set of rates ( R SK , R Φ , R M ) , the optimal input distrib ution s p ∗ ( s ) in (41) and (42) may b e differ ent . Hen ce, one has to use a commo n p ( s ) in (2 5). W e append the subscr ipt r to E r ( R Φ , R M ) and F r ( R SK , R Φ , R M ) to allude to the fact th at in the deriv ation of these expon ents, we use both random coding [10] an d rand om binn ing schem es [11]. The functions E r ( R Φ , R M ) and F r ( R SK , R Φ , R M ) are plot- ted in Figs. 5 an d 6 respec ti vely . Fr om Fig. 5, we obser ve that R Φ 7→ E r ( R Φ , R M ) is a no n-decreasin g function . This is intuitiv e because given mo re informa tion ( i.e., when R Φ is large) and with R M fixed, Bob can decode the ke y K B with grea ter reliability . I n con trast, R M 7→ E r ( R Φ , R M ) is a non-in creasing function. This is also intuitive b ecause Alice’ s 0.8 0.85 0.9 0.95 1 1.6 1.7 1.8 1.9 2 0 0.02 0.04 0.06 0.08 0.1 R M F o (p(s), R SK , R Φ , R M ) E o (p(s), R Φ , R M ) R Φ Fig. 7. Plot of the rel iabilit y exponent E o and secrec y expon ent F o for a fixed input distrib ution p ( s ) = Ber n (0 . 5) with R SK = 0 . 01 . The exponents for two dif ferent value s of R M are sho wn. 1.6 1.65 1.7 1.75 1.8 1.85 1.9 1.95 2 0 0.01 0.02 0.03 0.04 0.05 0.06 0.07 0.08 0.09 0.1 R φ E o and F o E o (p(s), R φ , R M =H(S)) F o (p(s), R SK , R φ , R M =H(S)) E o (p(s), R φ , R M =0.85) F o (p(s), R SK , R φ , R M =0.85) increase R M increase R M Fig. 8. T w o-dimensional visualizatio n of Fig. 7. The thick soli d li nes correspond to R M = H ( S ) = 1 and the thin dashed lines correspond to R M = 0 . 85 . priv ate sour ce of random ness is in creased if R M is increased making it m ore challenging fo r Bo b to d ecode th e key . From Fig. 6, w e ob serve that R Φ 7→ F r ( R SK , R Φ , R M ) is a non -increasing f unction. This is becau se as more public informa tion is made av ailable to Bob, w ith all else fixed, the ke y leakage r ate in creases, resulting in a smaller secr ecy exponent. The functio n R M 7→ F r ( R SK , R Φ , R M ) is n on- decreasing be cause as Alice in creases th e use of h er p riv ate random ness thr ough a larger R M , she can c onceal mo re o f the key from Eve. Finally , R SK 7→ F r ( R SK , R Φ , R M ) is non- increasing becau se R SK can b e inte rpreted as the residu al source of secrecy that can be gener ated by Alice and Bob while keep ing Eve ignoran t of the key gener ated. In Fig. 7, we plot the e xpon ents as a function of R Φ and R M for R SK = 0 . 01 . The inpu t distrib ution p ( s ) is kept fixed. Note SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 11 that th ere is a non- empty region in the ( R Φ , R M ) plan e for which bo th exponen ts are positiv e, indicating that R SK = 0 . 01 is stro ngly ach iev able. For clarity , we also p resent a two- dimensiona l visualization in Fig. 8 which helps to show the utility of our sender-excited model. W e observe th e following: Suppose we want to ha ve a secret key rate of R SK = 0 . 01 and that the pub lic message rate mu st be limited to, say , R Φ ≤ 1 . 68 du e to system constra ints. Then by simply adopting a source emulation strategy , R M = H ( S ) = 1 (i.e., case (III) of Section IV -E), and the reliab ility exponent is zero ev en th ough the secre cy expone nt is h igh. Th e re liability a nd secrecy expon ents for th is choice of param eters is plo tted with the th ick solid lines. Thus, we cannot achieve th e key rate of R SK = 0 . 01 with the fixed inp ut distribution p ( s ) . Howev er, our model affords us the flexibility to tune R M . If, for instance, we reduce it to R M = 0 . 85 while keeping R Φ = 1 . 68 we tradeoff a red uction in the secrecy exponent for an increase in the r eliability exponent. W ith this new choice of R M both exponents will be positive and the key rate R SK = 0 . 01 is (strongly ) achieved with the same fixed p ( s ) . The expon ents for this choice of parameter s are plotted by the thin da shed lines. V I . P RO O F S O F R E S U LT S I N S E C T I O N I I I A. Pr oof of Convers e of Pr oposition 1 W e start with a lemma [3, Lemma 4. 1], which is a con se- quence of th e Csisz ´ ar sum id entity [30, Ch. 2] . Lemma 6. The following equality holds for arbitrary rand om variables K, Φ , Y n , Z n : I ( K ; Y n | Φ) − I ( K ; Z n | Φ) = n X i =1 I ( K ; Y i | Y i − 1 , Z n i +1 , Φ) − I ( K ; Z i | Y i − 1 , Z n i +1 , Φ) . Pr oof of Convers e o f Pr oposition 1: Fix any seq uence of (2 nR M , 2 nR Φ , n, Γ) cod es per Section II-A. Let R SK be any Γ -weakly achiev able rate per Definition 1. Consider, nR SK ≤ I ( K A ; Y n , Φ) + nǫ n (43) ≤ I ( K A ; Y n , Φ) − I ( K A ; Z n , Φ) + 2 nǫ n (44) = I ( K A ; Y n | Φ) − I ( K A ; Z n | Φ) + 2 nǫ n = n X i =1 I ( K A ; Y i | Y i − 1 , Z n i +1 , Φ) − I ( K A ; Z i | Y i − 1 , Z n i +1 , Φ) + 2 nǫ n (45) where ( 43) is due to Fano’ s in equality ( ǫ n → 0 as n → ∞ ) , (44) is d ue to the secrecy cond ition in (3) and (4 5) by app lying Lemma 6. Now we make the following id entifications o f the auxiliary random variables W i , ( Y i − 1 , Z n i +1 , Φ) , and U i , ( K A , W i ) . (46) As c an be readily verified, the chosen variables W i and U i satisfy the Ma rkov condition W i − U i − ( S i , X i ) − ( Y i , Z i ) as req uired by (9). Note that since K A and Φ ( random variables contained in o ur identifications in W i and U i in (46)) ar e bo th fun ctions of ( M , X n ) (see Section II), S i by itself does no t separate ( X i , Y i , Z i ) fro m W i and U i . Howe ver , the separa tion does hold when ( S i , X i ) are grou ped together by the discrete memo ryless nature of the chan nel p ( x, y , z | s ) . Substituting the cho ice o f a uxiliary ran dom variables in ( 46) into (45) yie lds, nR SK ≤ n X i =1 I ( K A ; Y i | W i ) − I ( K A ; Z i | W i ) + 2 nǫ n = n X i =1 I ( K A , W i ; Y i | W i ) − I ( K A , W i ; Z i | W i ) + 2 nǫ n = n X i =1 I ( U i ; Y i | W i ) − I ( U i ; Z i | W i ) + 2 nǫ n . Now , introduc e the time-shar ing rand om variable Q with unifor m distrib ution P ( Q = i ) = 1 /n for all i ∈ [1 : n ] and ind ependen t of ( W n , U n , S n , X n , Y n , Z n ) . Define the random v ariables U , ( U Q , Q ) , W , ( W Q , Q ) , S , S Q , X , X Q , Y , Y Q and Z , Z Q . Then, we h av e R SK ≤ n X q =1 P ( Q = q ) I ( U q ; Y q | W q ) − I ( U q ; Z q | W q ) + 2 ǫ n = I ( U Q ; Y Q | W Q , Q ) − I ( U Q ; Z Q | W Q , Q ) + 2 ǫ n = I ( U Q , Q ; Y Q | W Q , Q ) − I ( U Q , Q ; Z Q | W Q , Q ) + 2 ǫ n = I ( U ; Y | W ) − I ( U ; Z | W ) + 2 ǫ n . (47) Note also that sin ce S n satisfies the almost su re cost con straint in (1), 1 n P n i =1 E [Λ( S i )] ≤ Γ ho lds. This implies from the definition of Q and S that E [Λ( S )] = E Q { E [Λ( S Q ) | Q ] } ≤ Γ . Thus to remove the dependence on the code, we maximize (47) over all joint distributions that satisfy ( 9) and E [Λ( S )] ≤ Γ , i.e., R SK ≤ ma x W − U − ( X,S ) − ( Y , Z ) E [Λ( S )] ≤ Γ I ( U ; Y | W ) − I ( U ; Z | W ) + 2 ǫ n . T aking n → ∞ comp letes the pr oof o f th e co n verse. B. Pr oof of Pr oposition 2 Pr oof: W e prove the u pper b ound in (11). Consider the inequalities: nR SK ≤ I ( K A ; Y n , Φ) + nǫ n (48) ≤ I ( K A ; Y n , Φ , Z n ) + nǫ n = I ( K A ; Y n | Φ , Z n ) + I ( K A ; Φ , Z n ) + nǫ n ≤ I ( K A ; Y n | Φ , Z n ) + 2 nǫ n (49) ≤ I ( K A , Φ; Y n | Z n ) + 2 nǫ n , (50) where (48) follows Fano’ s ineq uality an d (49) is du e to the secrecy cond ition (3). Contin uing fr om (5 0), we have nR SK ≤ I ( X n , M ; Y n | Z n ) + 2 nǫ n (51) = I ( X n ; Y n | Z n ) + I ( M ; Y n | X n , Z n ) + 2 nǫ n ≤ I ( X n ; Y n | Z n ) + I ( S n ; Y n | X n , Z n ) + 2 nǫ n (52) = I ( S n ; Y n | Z n ) + I ( X n ; Y n | S n , Z n ) + 2 nǫ n , (53) where (51) follows because ( K A , Φ) is a fun ction of ( X n , M ) and (5 2) fo llows because the cha nnel on ly dep ends on S n so SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 12 M − S n − ( X n , Y n , Z n ) . 5 Now th e first term (53) can be upper bounde d as follows I ( S n ; Y n | Z n ) = H ( Y n | Z n ) − H ( Y n | S n , Z n ) = n X i =1 H ( Y i | Y i − 1 , Z n ) − H ( Y i | Y i − 1 , S n , Z n ) ≤ n X i =1 H ( Y i | Z i ) − H ( Y i | S i , Z i ) = n X i =1 I ( S i ; Y i | Z i ) , (54 ) where the inequ ality follows by condition ing reduces entr opy and the Markov chain ( Y i − 1 , Z n \ i , S n \ i ) − ( S i , Z i ) − Y i . The second term in (5 3) can b e written as a sum: I ( X n ; Y n | S n , Z n ) = n X i =1 I ( X i ; Y i | S i , Z i ) ( 55) because the chan nel p ( x, y , z | s ) is memoryless. Sub stitut- ing (54) and (5 5) into (5 3) yie lds nR SK ≤ n X i =1 I ( S i ; Y i | Z i ) + I ( X i ; Y i | S i , Z i ) + 2 nǫ n = n X i =1 I ( X i , S i ; Y i | Z i ) + 2 nǫ n . (56) The pr oof can be com pleted using the tim e-sharing techniq ue in the c on verse pr oof o f Pro position 1. V I I . P R O O F S O F R E S U LT S I N S E C T I O N I V In this section , we pr ovide the proof of T heorem 4 on the capacity-r eliability-secrecy region. This section will be split into th ree subsection s: In the first subsection, we collec t some r elev ant d efinitions and d escribe the cod ing schem e. The second and third sub sections contain the proofs of the achiev ability (lower bou nds) of th e re liability and secrecy exponents respectiv ely . This proves the achiev ability of th e region ˜ R ( p ( s ) , R Φ , R M ) defined in (2 4). A. Definitions a nd Coding Scheme W e start with some definitions to d escribe the generation of the cod ew ords s n ( m ) , the key an d th e pu blic message generation p rocedu res. Definition 7 (Random cod e) . A (2 nR M , n ) random code generated accor ding to p ( s ) is a random subset o f S n which contains len gth- n sequen ces s n ( m ) , m ∈ [1 : 2 nR M ] where each seque nce s n ( m ) , ca lled a codeword , is drawn a ccor ding to the p mf Q n i =1 p ( s i ) . Note that we do no t place any cost constraints on p ( s ) because we assume th at Γ = ∞ in Section IV. Definition 8 ( Random binning function [11]) . A 2 nR random binning function for an alphabet U is a random map 6 ψ : u ∈ U → b ∈ [1 : 2 nR ] that satisfies the fo llowing pr operties: • Uniformity : Each element u ∈ U is in depend ently and uniformly assigned to a n eleme nt o f [1 : 2 nR ] . 5 In fact , (52) holds with equali ty because S n = S n ( M ) in addition to the stated Marko v relationship. 6 More precisely , ψ ( b | u ) is a matrix of conditional probabilitie s. • Pairwise Independence : Each pair of d iffer ent u, u ′ ∈ U is mapped u 7→ b , u ′ 7→ b ′ with pr obability 2 − 2 nR for each pair o f elements b, b ′ ∈ [1 : 2 nR ] (not necessarily differ ent). • The random map ψ is indep endent of the random code generation pr ocess a s per Definition 7 . More precisely , P ( { S n = s n } ∩ { ψ ( u ) = b } ) = P ( S n = s n ) P ( ψ ( u ) = b ) W e now intro duce the notion of a random binning code for the secr et key generatio n protoco l (See Section II-A). Definition 9 (Random b inning secret key co de) . A (2 nR SK , 2 nR M , 2 nR Φ , n ) random b inning secret key co de is a (2 nR M , 2 nR Φ , n ) code for the secr et key generation pr otocol in wh ich th e p ublic message an d key are generated via two indepen dent random bin ning fu nctions: φ : M × X n → Φ = [1 : 2 nR Φ ] (57) k A : M × X n → K = [1 : 2 nR SK ] . (58) More precisely , n ote f rom (5 7) th at φ is a 2 nR Φ random binning function for alphabet M × X n and from (58) that k A is a 2 nR SK random binnin g functio n for alpha bet M × X n . Codebook Genera tion and Encoding : Fix p ( s ) . W e use a (2 nR SK , 2 nR M , 2 nR Φ , n ) rando m binning secret ke y code in which the codewords s n ( m ) , m ∈ M belon g to a (2 nR M , n ) random code gener ated a ccording to p ( s ) . Th e codewords and bin assignments are re vealed to all parties before c om- munication starts. W e emphasize that by construction , this (2 nR SK , 2 nR M , 2 nR Φ , n ) code is a (2 nR M , 2 nR Φ , n ) co de (in the sense of Section II-A with Γ = ∞ ) such that secret key rate R SK is achiev able. This is because K A is uniformly distrib uted on [1 : 2 nR SK ] so (4) is satisfied. By the definition of ˜ R ( p ( s ) , R Φ , R M ) in (2 4), it suffices to show the following two assertio ns hold tru e f or any p ( s ) : lim inf n →∞ − 1 n log P ( K A 6 = K B ) ≥ E o ( p ( s ) , R Φ , R M ) , lim inf n →∞ − 1 n log I ( K A ; Z n , Φ) ≥ F o ( p ( s ) , R SK , R Φ , R M ) . This is what we prove in the next two subsections. B. Pr oof for the Reliab ility Exp onent In this section, we will prove that E o is an achiev able reliability e xpo nent. Recall that Bob has access to his channel output y n ∈ Y n and th e public messag e φ ∈ Φ , which was generated by Alice in accord ance to the r andom binning function in (58). In order to analyze the error event th at Bob’ s key does not match Alice’ s E key , { K A 6 = K B } , (59) we stipulate th at Bob decod es both Alice’ s recei ved sequenc e x n ∈ X n and Alice’ s source of random ness m ∈ M . W e restate the ML-MAP d ecoding ru le in (26): Gi ven ( y n , φ ) , Bob d eclares tha t m is the message selected by Alice and x n is the sequence sent to Alice if the pub lic message b in index of ( m, x n ) agrees with φ , i.e., φ ( m, x n ) = φ (60) SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 13 and the p robabilities satisfy p ( y n | s n ( m )) p ( x n | y n , s n ( m )) ≥ p ( y n | s n ( ˜ m )) p ( ˜ x n | y n , s n ( ˜ m )) (6 1) for all oth er p airs ( ˜ m, ˜ x n ) such that φ ( ˜ m, ˜ x n ) = φ . As mentioned previously , this is a hybrid of an ML and an MAP rule. Ob serve that if we were just to maximize p ( y n | s n ( m )) over m , this would corresp ond to a pur e ML decoding rule for the chann el p ( y | s ) as in [10, Sec. 5 .6]. If instead we maximize p ( x n | y n , s n ( m )) over x n giv en m is k nown, this would corr espond to a pure MAP d ecoder fo r th e sou rce x n giv en side in formatio n ( m, y n ) as in [1 1]. By analyzin g the ML-MAP deco der , we now upp er boun d the p robability of e vent E key of th e en semble random bin - ning secret key code C , i.e., P ( E key ) , E C [ P ( E key | C )] = P C p ( C ) P ( E key | C = C ) . Throug hout, we use the no tation C to denote the rando m code (a rand om v ariable) and C to denote a specific code. Define the error event that Bob decodes either M or X n incorrectly E , { ( ˆ M , ˆ X n ) 6 = ( M , X n ) } . (62) Clearly , E key ⊂ E . Th us, an up per b ound for P ( E ) also serves as an upper b ound for P ( E key ) . Similar ly , a lower bound for the expo nent of P ( E ) is a lso a lower bound for the exponent of P ( E key ) . In the interest of tractability , we upper bound P ( E ) [instead o f P ( E key ) ] when the ML- MAP decoder described in (6 0) and ( 61) is used. In o rder to bound P ( E ) , we decomp ose E into the following three disjoint error e vents: E 1 , { ˆ M = M , ˆ X n 6 = X n } (63) E 2 , { ˆ M 6 = M , ˆ X n = X n } (64) E 3 , { ˆ M 6 = M , ˆ X n 6 = X n } (65) Note that the error exponent is the m inimum o f the expon ents for P ( E 1 ) , P ( E 2 ) and P ( E 3 ) . In the fo llowing, we on ly p rovide a d etailed deriv ation for P ( E 3 ) as it is the most interest- ing and unconventional. W e note that for E 1 , if M = m , p ( ˆ x n | y n , s n ( m )) ≥ p ( x n | y n , s n ( m )) (the M AP decodin g part) so this analysis p arallels that by Gallag er for Sl epian - W olf codin g [11] (recon structing X n giv en side informatio n ( Y n , S n ( M )) and M is decoded correctly). Thus, we have lim inf n →∞ − 1 n log P ( E 1 ) ≥ ρR Φ − log X s,y p ( s ) p ( y | s ) X x p ( x | y , s ) 1 / (1+ ρ ) ! 1+ ρ . (66) Similarly for E 2 , we have that p ( x n , y n | s n ( ˆ m )) ≥ p ( x n , y n | s n ( m )) (Bayes rule) so this is simply the error in ML decodin g for chan nel cod ing with v ector ou tput ( X , Y ) a nd input S . Co nsequently , from Gallager’ s bo ok [1 0, Sec . 5. 6], lim inf n →∞ − 1 n log P ( E 2 ) ≥ ρ ( R Φ − R M ) − lo g X s X x,y p ( s ) p ( x, y | s ) 1 / (1+ ρ ) ! 1+ ρ . (67) Here we note that there are . = 2 nR M sounding sequen ces s n ( m ) b ut b y (60), we search within a particu lar bin indexed by φ so effecti vely , the re are only . = 2 n ( R M − R Φ ) sounding sequences expla ining the leading term in (67). Now , we analyze P ( E 3 ) in detail. Consider the prob ability of error g i ven that m is the message sent, s n ( m ) represents the ensemb le of codewords associate d to m (by the rando m codebo ok construction in Definition 7), x n is Alice’ s received sequence and y n is Bob ’ s recei ved sequence. That is, consider P ( E 3 | y n , s n ( m ) , m, x n ) = P [ ˆ m 6 = m,s n ( ˆ m ) , ˆ x n 6 = x n A ( s n ( ˆ m ) , ˆ m, ˆ x n ) . (68) In the above error pr obability , A ( s n ( ˆ m ) , ˆ m, ˆ x n ) is de- fined as the error event that th e messag e ˆ m 6 = m , codeword s n ( ˆ m ) and Alice’ s sequence ˆ x n 6 = x n are selected in su ch a way that the ir ML-MAP objec - ti ve value is h igher than that o f the true pa rameters ( m, s n ( m ) , x n ) , i.e., that p ( y n | s n ( ˆ m )) p ( ˆ x n | y n , s n ( ˆ m )) ≥ p ( y n | s n ( m )) p ( x n | y n , s n ( m )) and also that φ ( ˆ m, ˆ x n ) = φ ( m, x n ) . Note in ( 68) that the erro r event is av eraged over all inc orrect codewords s n ( ˆ m ) due to the rand om codeb ook construction (Definition 7). Now rec all the assum ption tha t the binning process is pairwise indep endent and also independen t of the inputs (Definition 8). More precisely , P ( { S n = s n ( ˆ m ) } ∩ { φ ( m, x n ) = φ ( ˆ m, ˆ x n ) } ) = P ( S n = s n ( ˆ m )) P ( φ ( m, x n ) = φ ( ˆ m, ˆ x n )) = p ( s n ( ˆ m )) X φ ∈ Φ 1 | Φ | 2 = p ( s n ( ˆ m )) | Φ | . (69) Let 1 B be the ind icator variable of the set B . By using the definition of A ( s n ( ˆ m ) , ˆ m, ˆ x n ) and (69), we can upper bou nd the p robab ility of A ( s n ( ˆ m ) , ˆ m, ˆ x n ) as follows: P ( A ( s n ( ˆ m ) , ˆ m, ˆ x n )) = p ( s n ( ˆ m )) | Φ | 1 { p ( ˆ x n ,y n | s n ( ˆ m )) ≥ p ( x n ,y n | s n ( m )) } ≤ p ( s n ( ˆ m )) | Φ | p ( y n | s n ( ˆ m )) p ( ˆ x n | y n , s n ( ˆ m )) p ( y n | s n ( m )) p ( x n | y n , s n ( m )) t , for all t > 0 , where the inequality follows becau se 1 { a ≥ b } ≤ ( a b ) t for all t > 0 . Let ρ ∈ [0 , 1] . By app lying the inequality P ∪ T t =1 A t ≤ [ P T t =1 P ( A t )] ρ [10, pp. 136] to (68), we have P ( E 3 | y n , s n ( m ) , m, x n ) ≤ " X ˆ m 6 = m, s n ( ˆ m ) , ˆ x n 6 = x n p ( s n ( ˆ m )) | Φ | × . . . × p ( y n | s n ( ˆ m )) p ( ˆ x n | y n , s n ( ˆ m )) p ( y n | s n ( m )) p ( x n | y n , s n ( m )) t # ρ (70) for any ρ ∈ [0 , 1] and t > 0 . Now consider the error probab ility P ( E 3 | M = m ) giv en me ssage m is chosen by Alice, i.e., { M = m } occur s. T o boun d th is error pro bability , we average SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 14 over all cod ew ords s n ( m ) , all obser ved sequences y n and all possible sequences receiv ed b y Alice x n , i.e., P ( E 3 | m ) = X y n X s n ( m ) p ( y n | s n ( m )) p ( s n ( m )) × . . . × X x n p ( x n | y n , s n ( m )) P ( E 3 | y n , s n ( m ) , m, x n ) . (71 ) W e now sub stitute the up per bound in (70) into (71). Pulling out p ( x n | y n , s n ( m )) from the innermost term in (70) ( since it does not depen d on ˆ m , s n ( ˆ m ) and ˆ x n ), w e see that P ( E 3 | m ) can be upper b ound ed as P ( E 3 | m ) ≤ | Φ | − ρ X y n X s n ( m ) p ( y n | s n ( m )) p ( s n ( m )) × . . . × X x n p ( x n | y n , s n ( m )) 1 − ρt " X ˆ m 6 = m X s n ( ˆ m ) p ( s n ( ˆ m )) × . . . × p ( y n | s n ( ˆ m )) p ( y n | s n ( m )) t X ˆ x n 6 = x n p ( ˆ x n | y n , s n ( ˆ m )) t # ρ = | Φ | − ρ ( |M| − 1) ρ X y n Ψ 1 ( y n , ρ, t )Ψ 2 ( y n , ρ, t ) , (72) where the fun ctions Ψ 1 ( y n , ρ, t ) and Ψ 2 ( y n , ρ, t ) are defin ed as follows: Ψ 1 ( y n , ρ, t ) , X s n ( m ) p ( s n ( m )) p ( y n | s n ( m )) 1 − ρt × . . . × X x n p ( x n | y n , s n ( m )) 1 − ρt Ψ 2 ( y n , ρ, t ) , " X s n ( ˆ m ) p ( s n ( ˆ m )) p ( y n | s n ( ˆ m )) t × . . . × X ˆ x n p ( ˆ x n | y n , s n ( ˆ m )) t # ρ . Equation (7 2) follows because ˆ m in the line a bove is a dummy variable tha t can take on exactly |M| − 1 values and for each ˆ m , we generate codewords s n ( ˆ m ) in the same wa y in the random co ding construc tion. Now notice tha t if we set t = 1 / (1 + ρ ) , then Ψ 2 ( y n , ρ, 1 / (1 + ρ )) = Ψ 1 ( y n , ρ, 1 / (1 + ρ )) ρ because ˆ x n and ˆ m in the definition of Ψ 2 are dum my v ariables. As such, P ( E 3 | m ) can b e bound ed as P ( E 3 | m ) ≤ | Φ | − ρ |M| ρ X y n Ψ 3 ( y n , ρ ) , (73) where the f unction Ψ 3 ( y n , ρ ) is defined a s Ψ 3 ( y n , ρ ) , " X s n ( m ) p ( s n ( m )) p ( y n | s n ( m )) 1 / (1+ ρ ) × . . . X x n p ( x n | y n , s n ( m )) 1 / (1+ ρ ) # 1+ ρ . Now , we recall the DMS and DMBC assumptions, i.e ., th at p ( s n ( m )) = n Y i =1 p ( s i ( m )) , p ( x n , y n | s n ( m )) = n Y i =1 p ( x i , y i | s i ( m )) . As a r esult, Ψ 3 ( y n , ρ ) simplifies to Ψ 3 ( y n , ρ ) = " n Y i =1 X s i ( m ) p ( s i ( m )) p ( y i | s i ( m )) 1 / (1+ ρ ) × . . . × X x i p ( x i | y i , s i ( m )) 1 / (1+ ρ ) # 1+ ρ , and the sum in (7 3) can be wr itten as a product o f single- letterized terms: X y n Ψ 3 ( y n , ρ ) = n Y i =1 X y i Ψ 4 ( y i , ρ ) , (74) where the f unction Ψ 4 ( y , ρ ) is defined as Ψ 4 ( y , ρ ) , " X s p ( s ) p ( y | s ) 1 / (1+ ρ ) X x p ( x | y , s ) 1 / (1+ ρ ) # 1+ ρ . Because each of th e codewords is gene rated identically , each of the terms in the pro duct in (7 4) is also identical. Hence, X y n Ψ 3 ( y n , ρ ) = " X y Ψ 4 ( y , ρ ) # n . Recall that | Φ | . = 2 nR Φ and |M| . = 2 nR M . In add ition, note that P ( E 3 ) = P m ′ p ( m ′ ) P ( E 3 | m ′ ) = P ( E 3 | m ) for e very m ∈ M . As such, taking the normalized logarithm and limit inferio r of (73) y ields lim inf n →∞ − 1 n log P ( E 3 ) ≥ ρ ( R Φ − R M ) − lo g X y Ψ 4 ( y , ρ ) . (75) Essentially , wh at we have d one is to dev elop a “hybrid” of Gallager-style erro r expon ents for channel and lossless source cod ing with side info rmation. Thus, an achiev able error exponent whe n in put distribution p ( s ) is u sed is E (3) o ( p ( s ) , R Φ , R M ) defined in (21). The re liability exponent part of the the orem is p roved f or the ran dom binn ing secret key cod e by combin ing the bound s f or the exponen ts for P ( E 1 ) , P ( E 2 ) a nd P ( E 3 ) in (66), (67) and (75) respectively . C. Pr o of for the S ecr ecy E xponen t W e now prove that the secr ecy expone nt is at least F o using the same coding sche me. W e can u se steps an alogou s to the proof of the direct part o f Th eorem 2 in [22] to obtain the following boun d on the key leakage I ( K A ; Z n , Φ) . Lemma 7. Defi ne c ( α ) , α − 1 log e for 0 < α ≤ 1 . The key leakage can be boun ded as follows: I ( K A ; Z n , Φ) = E C [ I ( K A ; Z n , Φ | C )] ≤ c ( α ) |K| α | Φ | α X z n p ( z n ) X m,x n p ( m, x n | z n ) 1+ α , (76) SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 15 for all 0 < α ≤ 1 . The p roof is provided at th e e nd f or comp leteness. Now we consider the inner sum in (7 6). By introduc ing the input s n and by repeated ap plications of Bay es rule, X m,x n p ( m, x n | z n ) 1+ α = X x n X m " X s n p ( m, x n , s n | z n ) # 1+ α = X x n X m " X s n p ( m, x n , s n , z n ) p ( z n ) # 1+ α = 1 p ( z n ) 1+ α X x n X m Θ 1 ( m, x n , z n ) 1+ α (77) = 1 p ( z n ) 1+ α |M| 1+ α X x n X m Θ 2 ( m, x n , z n ) 1+ α (78) where the f unctions Θ 1 ( m, x n , z n ) and Θ 2 ( m, x n , z n ) are defined a s Θ 1 ( m, x n , z n ) , X s n p ( m ) p ( s n | m ) p ( z n | s n ) p ( x n | s n , z n ) Θ 2 ( m, x n , z n ) , X s n p ( s n | m ) p ( z n | s n ) p ( x n | s n , z n ) . Equation (77) follows because M − S n − ( X n , Z n ) form a Ma rkov chain so p ( z n | s n , m ) = p ( z n | s n ) and p ( x n | s n , z n , m ) = p ( x n | s n , z n ) . Equatio n (78) fo llows from the unifor mity of the messages m in the message set M , i.e., that p ( m ) = 1 |M| for all m ∈ M . W e now up per bound Θ 2 ( m, x n , z n ) 1+ α . Th is is do ne using th e f ollowing lemma. Lemma 8. Let { ( λ j , a j ) } be a finite collection of non-ne gative numbers such that P j λ j = 1 . Also, let r ≥ 1 . Then, the following inequality holds X j λ j a j ! r ≤ X j λ j a r j . This c an be proven by noticing that t 7→ t r is convex. W e omit the details. W e now make the following id entifications: a s n ≡ p ( z n | s n ) p ( x n | s n , z n ) , λ s n ≡ p ( s n | m ) and r ≡ 1 + α and app ly Lemm a 8 to Θ 2 ( m, x n , z n ) 1+ α . T his yie lds the inequality Θ 2 ( m, x n , z n ) 1+ α ≤ X s n p ( s n | m )[ p ( z n | s n ) p ( x n | s n , z n )] 1+ α . (79) On account of ( 76), ( 78) an d (79), we have E C [ I ( K A ; Z n , Φ | C )] ≤ c ( α ) |K | α | Φ | α |M| − (1+ α ) × . . . X z n p ( z n ) − α X s n ,x n ,m p ( s n | m ) [ p ( z n | s n ) p ( x n | s n , z n )] 1+ α = c ( α ) |K| α | Φ | α |M| − (1+ α ) × . . . X s n ,x n ,z n X m p ( s n , x n , z n | m ) p ( z n | s n ) p ( z n ) p ( x n | s n , z n ) α , where the final eq uality follo ws because p ( s n , x n , z n | m ) = p ( s n | m ) p ( z n | s n ) p ( x n | s n , z n ) by the Markov chain M − S n − ( X n , Z n ) . Now , pulling the p ( m ) = 1 |M| term into th e sum , we get E C [ I ( K A ; Z n , Φ | C )] ≤ c ( α ) |K | α | Φ | α |M| − α × . . . X s n ,x n ,z n X m p ( s n , x n , z n | m ) p ( m ) p ( z n | s n ) p ( z n ) p ( x n | s n , z n ) α = c ( α ) |K| α | Φ | α |M| − α X s n ,x n ,z n Υ( s n , x n , z n , α ) , where the f unction Υ( s n , x n , z n , α ) is defined as Υ( s n , x n , z n , α ) , p ( s n , x n , z n ) p ( z n | s n ) p ( z n ) p ( x n | s n , z n ) α . Now , re call that (i) th e input S n is a DMS when averaged over all codeb ooks and all messages m ∈ M (beca use the g eneration of th e cod ew ords s n ( m ) , m ∈ M is done identically ) and (ii) p ( x, y , z | s ) is a DMBC. Th en, we have the u pper bound E C [ I ( K A ; Z n , Φ | C )] ≤ c ( α ) |K| α | Φ | α |M| − α n Y i =1 X s i ,x i ,z i Υ( s i , x i , z i , α ) = c ( α ) |K| α | Φ | α |M| − α " X s,x,z Υ( s, x, z , α ) # n . (80) Note that the bo und (80) ho lds for all 0 < α ≤ 1 . Recall also that K = [1 : 2 nR SK ] , Φ = [1 : 2 nR Φ ] and M = [1 : 2 nR M ] so |K| α | Φ | α |M| − α . = 2 nα ( R SK + R Φ − R M ) . Now take the n ormalized logarithm and limit infer ior of (8 0) to get lim inf n →∞ − 1 n log E C [ I ( K A ; Z n , Φ | C )] ≥ − α ( R SK + R Φ − R M ) − lo g X s,x,z Υ( s, x, z , α ) . The joint distribution o f ( X , Z , S ) , namely p ( x, z , s ) = p ( x, z | s ) p ( s ) , is induced b y a par ticular input distribution p ( s ) . Essentially wha t we have don e in this part o f the proof is to develop a “hy brid” of th e inf ormation leakage exponent f or th e wiretap c hannel model [ 12, Eq. (14)] and th e excited source m odel [22, Th eorem 3] . Hence, an achiev able exponent for the key leakage given inpu t distribution p ( s ) is F o ( p ( s ) , R SK , R Φ , R M ) defined in (2 3). Th e secrecy exponent p art of th e theorem is pr oved for the r andom binning secret key code. F r om Rando m Codes to a Determin istic Code : Com bining the proof in Section VII-B and p roof in this section, w e ha ve shown that for the (2 nR SK , 2 nR M , 2 nR Φ , n ) random binning secret key code, th e expected pr obability of err or decay s with expon ent ( at least) E o (expectation over codebook s and random b inning fun ctions) and the expected key leak age decays expo nentially with exponent (at least) F o . Sin ce b oth are m easured with respect the same (known) chann el, there exists a binn ing secret key cod e that m eets the en semble behavior . Mor e p recisely , o bserve that P ( E ) = E C [ P ( E | C )] = P C p ( C ) P ( E | C = C ) , whe re C ru ns throug h all binning secr et SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 16 key codes (a random cod e and two rando m b inning func tions) and the event E is d efined in ( 62). By Mar kov’ s ine quality , P C [ P ( E | C ) ≥ 3 P ( E )] ≤ 1 3 . (81) Similarly , when averaged over a ll c odes, the average key lea k- age is E C [ I ( K A ; Z n , Φ | C )] = P C p ( C ) I ( K A ; Z n , Φ | C = C ) , so by Markov’ s in equality , P C [ I ( K A ; Z n , Φ | C ) ≥ 3 E C [ I ( K A ; Z n , Φ | C )]] ≤ 1 3 . (8 2) From (81), by consider ing the complement of the ev ent of inter est, we can co nclude that there exists a subset of binning secret key codes D 1 with to tal pro bability mass that exceeds 2 / 3 (i.e., P C ∈D 1 p ( C ) ≥ 2 / 3 ) suc h that P ( E | C = C ) < 3 P ( E ) for every C ∈ D 1 . Similarly , from (82) there exists a subset of bin ning secret ke y codes D 2 with total probab ility mass that exceeds 2 / 3 (i.e. , P C ∈D 2 p ( C ) ≥ 2 / 3 ) such th at I ( K A ; Z n , Φ | C = C ) < 3 E C [ I ( K A ; Z n , Φ | C )] for every C ∈ D 2 . Note that P ( D 1 ∩ D 2 ) ≥ 1 / 3 so D 1 ∩ D 2 6 = ∅ . Thu s, there exists at least one binning secret key code C ∗ in the ensemble of (good) codes D 1 ∩ D 2 such that P ( E key | C = C ∗ ) ≤ P ( E | C = C ∗ ) . ≤ 2 − nE o and I ( K A ; Z n , Φ | C = C ∗ ) . ≤ 2 − nF o , where the ev ent E key is defined in ( 59). Pr oof of Lemma 7 : Recall the assump tion th at the key and public message binning processes are r andom , unifor m an d indepen dent of the rando m cod ew ords (See Section VII-A for definitions and the cod e con struction). The key leakage can be expressed as follows: E C [ I ( K A ; Z n , Φ | C )] = E C [ H ( K A | C ) − H ( K A | Z n , Φ | C )] = E C [ H ( K A | C ) + H (Φ | Z n , C ) − H ( K A , Φ | Z n , C )] ≤ log |K | + log | Φ | − E C [ H ( K A , Φ | Z n , C )] . (83) The conditioning is on the specific codebo ok used, i.e., C = C . It remains to lower bou nd the conditional entr opy in (83). F or this purpose, let H 1+ α ( X ) , − 1 α log X x ∈X p ( x ) 1+ α (84) be th e R ´ enyi en tr opy of order 1 + α for 0 < α ≤ 1 . Note that lim α ց 0 H 1+ α ( X ) = H ( X ) . Also, by the conca vity o f t 7→ log t , it can b e verified that H ( X ) ≥ H 1+ α ( X ) for all 0 < α ≤ 1 . Consider the conditiona l entropy in (83), E C [ H ( K A , Φ | Z n , C )] = E C " X z n p ( z n ) H ( K A , Φ | Z n = z n , C ) # ≥ X z n p ( z n ) E C [ H 1+ α ( K A , Φ | Z n = z n , C )] (85) ≥ X z n p ( z n ) − 1 α log E C X ( k A ,φ ) ∈K× Φ p ( k A , φ | z n , C ) 1+ α . (86) The last inequality is due to the d efinition of R ´ enyi entropy in ( 84) a nd the ap plication of Jensen’ s inequ ality notin g that the function x 7→ − log x is conve x. Now let ( ˜ M , ˜ X n ) be a pair of rand om variables identically distributed to, b ut conditio nally independen t of ( M , X n ) given the events { Z n = z n } and { C = C } . Recall that k ( · , · ) and φ ( · , · ) are th e key an d pub lic message random b inning function s respectively . S ee (57) and (58) for definitions. Define ( ˜ K A , ˜ Φ) , ( k ( ˜ M , ˜ X n ) , φ ( ˜ M , ˜ X n )) . Then, p ( k A , φ | z n , C ) 1+ α = p ( k A , φ | z n , C ) P h ( ˜ K A , ˜ Φ) = ( k A , φ ) | Z n = z n , C = C i α , (87) by inter preting the R ´ enyi en tropy in (84) in ter ms o f an in- depend ent [from ( K A , Φ) ] and ide ntically distributed ra ndom variable ( ˜ K A , ˜ Φ) . Define a sho rthand notation for th e ind icator fu nction as 1 [ k A , φ | m, x n , C ] , 1 [ k C ( m, x n ) = k A , φ C ( m, x n ) = φ ] . (88) where k C ( · ) and φ C ( · ) are the bin ning functions associated to a specific codeb ook C = C . W e up per bound the expectation in th e logarithm in (8 6) on th e top of the next page. The step (89) is a result of pluggin g (88) into the argument of the logarithm in (86). The step ( 90) fo llows by writing out the prob ability of a collision event in ( 87) explicitly as a sum. Th e step in (91) app lies the law of total probability . W e sum over all possible ( m, x n ) that are assigned b in ind ices ( k A , φ ) for a gi ven pair of binnin g function index ed by C . Equation (92) f ollows by simple reorder ing of the sum s. The step (9 3) is an application of Jensen’ s Inequality to the term in brackets [ · ] α since the sum o ver ( k A , φ ) is a sum over the pro bability mass functio n 1 [ k A , φ | m, x n , C ] (cf. ( 88) for the definition of this ind icator function ). Also, the func tion x 7→ x α is co ncave for α ∈ [0 , 1] . W e recall th at m, x n , and C are all fixed for this inner sum, the last bein g fixed by the o uter expectation over C . Equation (94) follows fr om the same reason ing as (91), i.e., the law of to tal probab ility . Equation (95) f ollows by simple reorder ing of the sum s. In (96), we u sed the “sifting” pro perty of the indica- tor f unction 1 [ k A = k ′ A , φ = φ ′ ] . In (97) we split the sum over ( m ′ , x ′ n ) into two te rms and distributed the su ms over ( k ′ A , φ ′ ) . Note that f or the ( m ′ , x ′ n ) = ( m, x n ) term, P k A ,φ 1 [ k A , φ | m, x n , C ] = 1 . W e next applied the ineq uality ( x + y ) α ≤ x α + y α , for 0 ≤ α ≤ 1 to get (98). In (9 9) we note that the first term is no t a function o f C . Using th e conca vity o f x 7→ x α (for α ∈ [0 , 1] ), we move both the sum over ( m, x n ) and th e expectation ov er codeboo ks inside the function, a step justified by Jensen’ s Ineq uality . In (100) we apply th e uniform ly rand om d esign of the binning functio ns. Since ( m, x n ) 6 = ( m ′ , x ′ n ) fo r every term in the sum, each of the indicator func tions eq uals the ( fixed) pair ( k A , φ ) with equal p robab ility and inde- penden tly . Thus, the probability that both equal ( k A , φ ) is th e square (by the indepen dence) of the r eciprocal of the nu mber o f possibilities ( by the u niformity ), i.e., E C [ 1 [ k A , φ | m, x n , C ] 1 [ k A , φ | m ′ , x ′ n , C ]] = ( |K || Φ | ) − 2 . In (101), we pulled out ( |K|| Φ | ) − α . Finally , we note that p ( m, x n | z n ) p ( m ′ , x ′ n | z n ) is a well defined ( condition al) pmf SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 17 E C ( X k A ,φ p ( k A , φ | z n , C ) P h ( ˜ K A , ˜ Φ) = ( k A , φ ) | Z n = z n , C i α ) (89) = E C ( X k A ,φ " p ( k A , φ | z n , C ) X k ′ A ,φ ′ p ( k ′ A , φ ′ | z n , C ) 1 [ k A = k ′ A , φ = φ ′ ] ! α #) (90) = E C ( X k A ,φ " X m,x n p ( m, x n | z n ) 1 [ k A , φ | m, x n , C ] ! X k ′ A ,φ ′ p ( k ′ A , φ ′ | z n , C ) 1 [ k A = k ′ A , φ = φ ′ ] ! α #) (91) = E C ( X m,x n p ( m, x n | z n ) " X k A ,φ 1 [ k A , φ | m, x n , C ] X k ′ A ,φ ′ p ( k ′ A , φ ′ | z n , C ) 1 [ k A = k ′ A , φ = φ ′ ] ! α #) (92) ≤ E C ( X m,x n p ( m, x n | z n ) " X k A ,φ 1 [ k A , φ | m, x n , C ] X k ′ A ,φ ′ p ( k ′ A , φ ′ | z n , C ) 1 [ k A = k ′ A , φ = φ ′ ] !# α ) (93) = E C ( X m,x n p ( m, x n | z n ) " X k A ,φ 1 [ k A , φ | m, x n , C ] × X k ′ A ,φ ′ X m ′ ,x ′ n p ( m ′ , x ′ n | z n ) 1 [ k ′ A , φ ′ | m ′ , x ′ n , C ] ! 1 [ k A = k ′ A , φ = φ ′ ] !# α ) (94) = E C ( X m,x n p ( m, x n | z n ) " X m ′ ,x ′ n p ( m ′ , x ′ n | z n ) × X k A ,φ X k ′ A ,φ ′ 1 [ k A , φ | m, x n , C ] 1 [ k ′ A , φ ′ | m ′ , x ′ n , C ] 1 [ k A = k ′ A , φ = φ ′ ] !# α ) (95) = E C ( X m,x n p ( m, x n | z n ) " X m ′ ,x ′ n p ( m ′ , x ′ n | z n ) X k A ,φ 1 [ k A , φ | m, x n , C ] 1 [ k A , φ | m ′ , x ′ n , C ] !# α ) (96) = E C ( X m,x n p ( m, x n | z n ) " p ( m, x n | z n ) + X ( m ′ ,x ′ n ) 6 =( m,x n ) p ( m ′ , x ′ n | z n ) X k A ,φ 1 [ k A , φ | m, x n , C ] 1 [ k A , φ | m ′ , x ′ n , C ] !# α ) (97) ≤ E C ( X m,x n p ( m, x n | z n ) ( p ( m, x n | z n ) α + " X ( m ′ ,x ′ n ) 6 =( m,x n ) p ( m ′ , x ′ n | z n ) X k A ,φ 1 [ k A , φ | m, x n , C ] 1 [ k A , φ | m ′ , x ′ n , C ] !# α )) (98) ≤ X m,x n p ( m, x n | z n ) 1+ α + " E C ( X m,x n p ( m, x n | z n ) X ( m ′ ,x ′ n ) 6 =( m,x n ) p ( m ′ , x ′ n | z n ) X k A ,φ 1 [ k A , φ | m, x n , C ] 1 [ k A , φ | m ′ , x ′ n , C ] !)# α (99) = X m,x n p ( m, x n | z n ) 1+ α + " X m,x n p ( m, x n | z n ) X ( m ′ ,x ′ n ) 6 =( m,x n ) p ( m, x n | z n ) X k A ,φ 1 ( |K|| Φ | ) 2 !# α (100) = X m,x n p ( m, x n | z n ) 1+ α + 1 |K| α | Φ | α " X m,x n X ( m ′ ,x ′ n ) 6 =( m,x n ) p ( m, x n | z n ) p ( m ′ , x ′ n | z n ) # α (101) ≤ X m,x n p ( m, x n | z n ) 1+ α + 1 |K| α | Φ | α . (102) SUBMITTED TO T HE IEE E T RANSACTIONS ON INFORMA TION THEOR Y , OCT 2013 18 and that we are missing o ne term in the dou ble sum. Hence, we get ( 102) by u pper b oundin g the doub le sum by one. Substituting ( 102) back into (8 6) giv es E C [ H ( K A , Φ | Z n , C )] ≥ X z n p ( z n ) " − 1 α log 1 |K| α | Φ | α + X m,x n p ( m, x n | z n ) 1+ α !# = log( |K|| Φ | ) − 1 α X z n p ( z n ) × . . . × log 1 + |K | α | Φ | α X m,x n p ( m, x n | z n ) 1+ α ! (103) ≥ log( |K|| Φ | ) − log e α |K| α | Φ | α × . . . × X z n p ( z n ) X m,x n p ( m, x n | z n ) 1+ α , (104) where in (103) we pulled out th e |K| − α | Φ | − α term fr om the logarithm above and in (104) we applied the relation log(1 + t ) ≤ t log e (recall that log = log 2 ). The proo f of the lemma is completed b y u niting (83) and ( 104). Acknowledgments The auth ors would like to acknowledge one of the reviewers whose insigh ts led to the discussion on the conn ection of our work to that in Csisz ´ ar and Naray an [15] and Gohari and Ananthara m [34] in Sec tion IV -B. R E F E R E N C E S [1] T . -H. Cho u, V . Y . F . T an, an d S. C. Draper , “On the cap acity of the s ender -exci ted secret ke y agreement model, ” in Proc. Allerton Confer ence on Communication, Contr ol, and Computing , 2011. [2] Y . Liang, H. V . Poor , and S. Shamai, Information Theor etic Securit y . No w P ublisher s Inc, 2009. [3] R. Ahlswede a nd I. Csisz ´ ar , “Common rando mness in informati on theory and crypto graphy part I: Secre t sharing, ” IEEE Tr ans. Inform. Theory , vol. 39, no. 4, pp. 1121–1132, 1993. [4] U. M. Maurer , “Secre t key a greement by publi c discussion from common informati on, ” IEE E T rans. Inform. Theory , vol. 39, no. 3, pp. 733–742, 1993. [5] T . W eissman, “Capa city of channel s with action-de pendent states, ” IEEE T rans. Inform. Theory , vol. 56, pp. 5396–5411, Nov 2010. [6] H. Asnani, H. Permuter, and T . W eissman, “Probing Capaci ty, ” IEEE T rans. Inform. Theory , vol. 57, pp. 7317–7332, Nov 2011. [7] K. Kittichok echai, T . J. Oechte ring, M. Skogl und, and R. Thobaben, “Source and channel coding with actio n-dependent partial ly known two- sided state infor mation, ” in Proc . Int. Symp. Inf orm. Theory , pp. 629– 633, June 2010. [8] H. Permuter and T . W eissman, “Source coding with a s ide information “ve nding machine”, ” IEEE T rans. Inform. Theory , vol . 57, pp. 4530– 4544, Jul 2011. [9] I. Csisz ´ ar and P . Narayan, “Common randomness and secret ke y generat ion with a helper , ” IEE E T rans. Inform. Theory , vol . 46, no. 2, pp. 344–366, 2000. [10] R. G. Gallager , Information theory and rel iable communication . New Y ork: W ile y , 1968. [11] R. G. Gallag er , “ Source coding with s ide information and uni versal coding, ” M.I.T . LIDS-P-937 , 1976. [12] M. Hayashi , “Exponential decrea sing rate of leaked informati on in uni versal random priv ac y amplification, ” IEEE T rans. Inform. Theory , vol. 57, pp. 3989–4001, June 2011. [13] A. Khisti, S. Digga vi, and G. W orne ll, “Secret-k ey genera tion wit h correla ted sources and noisy channels, ” in Proc. Int. Symp. Info rm. Theory , pp. 1005–1009, July 2008. [14] V . P rabhaka ran, K. E swaran , and K. Ramchand ran, “Secrec y via sources and channels – a secret key-se cret message rate tradeof f regio n, ” in Proc. Int. Symp. Inform. Theory , pp. 1010–1014, July 2008. [15] I. Csisz ´ ar and P . Narayan, “The secret key capacity of multipl e termi- nals, ” IEEE T rans. Inform. Theory , vol. 50, pp. 3047–3061, Dec 2004. [16] I. Csisz ´ ar and P . Narayan, “Secrecy capa cities for multitermin al channe l models, ” IEEE T rans. Inform. Theory , vol. 54, pp. 2437–2452, Jun 2008. [17] Y . Chen and A. J. Han V inck, “W iretap channel with side information, ” IEEE T rans. Inform. Theory , vol. 54, pp. 395–402, Jan. 2008. [18] W . Liu and B. Chen, “W iretap channel with two-sided channel state informati on, ” in Proc. A silomar Conf. Signals, Systems and Computers, 2007 , pp. 893 –897, Nov . 2007 . [19] Y . K. Chia and A. El Gamal, “W iret ap channel with causal state informati on, ” IEEE T rans. Inform. Theory , vol. 58, pp. 2838–2849, May 2012. [20] A. Khisti, S. Digga vi, and G. W ornell , “Secret ke y agreement using asymmetry in chan nel state kno wledge, ” in Proc. Int. Symp. Inform. Theory , pp. 2286–2290, 2009. [21] A. Khisti, S. Diggavi, and G. W ornel l, “Sec ret-ke y agreement with channe l state information at the transmitte r , ” IEEE T rans. on F ore n. and Sec. , vol. 6, pp. 672–681, Sep 2011. [22] T . Chou, S. C. Draper , and A. Saye ed, “K ey ge neration using external source exc itation: Cap acity , reliabili ty , and secrec y e xponent, ” IEEE T rans. Inform. Theory , vol. 58, pp. 2455–2474, Apr . 2012. [23] R. W ilson, D. Tse, and R. A. Scholt z, “Channel iden tification : Secret sharing using reciprocit y in ultrawid eband channels, ” IEE E T ran s. Inform. F oren. and Sec. , vol. 2, pp. 364–375, S ep. 2007. [24] A. Agraw al, Z. Rezki, A. Khisti, and M. Alouini, “Noncoherent capacit y of secre t-ke y agree ment with public discussion , ” IEEE T rans. Inform. F ore n. and Sec. , vol. 6, pp. 565–574, Sept. 2011. [25] M. Hayashi, “General nonasympto tic and asymptotic formulas in chan- nel resolv ability and identific ation capacity and their applic ation to the wiretap channel, ” IEEE T rans. Inform. Theory , vol. 52, pp. 1562–1575, April 2006. [26] T . S. Han, Information-S pectrum Methods in Informati on Theory . Springer , 2002. [27] M. Bloch and J. N. L aneman, “Secrecy from Resolvab ility , ” arXiv:1105.5419 , May 2011. [28] C. Bennett, G. Bra ssard, C. Crepeau, and U. Maurer , “General ized pri va cy ampl ification, ” IEEE T rans. Inform. Theo ry , vol. 41, pp. 1915– 1923, Nov 1995. [29] S. W ata nabe, R. Matsumoto, and T . Uyematsu, “Strongly Secure Priv ac y Amplificat ion Cannot Be Obtaine d by Encoder of Slepi an-W olf Code, ” IEICE T ransact ions on Fundamentals of Elect ron ics, Communication s and Computer Science s , vol. E93.A, no. 9, pp. 1650–165 9, 2010. [30] A. El Gamal and Y .-H. Kim, Network Information Theory . Cambridge Uni versity Press, 2012. [31] U. Maurer and S. W olf, “Informat ion-theoret ic k ey agreement: From weak to s trong s ecrec y for free, ” in Lectur e Notes in Compute r Science , pp. 351–368, Springer-V erlag, 2000. [32] U. M. Maurer , “The strong secret ke y rate of discrete random triple s, ” Communications and Cryptogra phy: T wo Sides of One T apest ry , pp. 271–285, Nov 1994. [33] A. D. W yner , “The wire-tap channel, ” The Bell Syste ms T echn ical J ournal , vol. 54, pp. 1355–1387, 1975. [34] A. A. Gohari and V . Ananth aram, “Information-t heoretic key agreement of multiple terminals – I: Source model, ” IEEE T rans. Inform. Theory , vol. 56, pp. 3973–3996, Aug 2008. [35] A. A. Gohari and V . Anantha ram, “Information- Theoretic Ke y Agree- ment of Multiple T erminal s–Part II: Channel Model , ” IEEE T rans. Inform. Theory , vol. 56, pp. 3997–40 10, Aug. 2010. [36] D. Slepian and J . W olf, “Noiseless coding of correl ated sources, ” IE EE T rans. Inform. Theory , vol. 19, pp. 471–480, Jul 1973. [37] V . Y . F . T an and O. Kosut, “On the dispersi ons of three netw ork informati on theory problems, ” arXiv:120 1.3901 , Feb 2012 . [Online].
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment