New Results on Multiple-Input Multiple-Output Broadcast Channels with Confidential Messages
This paper presents two new results on multiple-input multiple-output (MIMO) Gaussian broadcast channels with confidential messages. First, the problem of the MIMO Gaussian wiretap channel is revisited. A matrix characterization of the capacity-equiv…
Authors: Ruoheng Liu, Tie Liu, H. Vincent Poor
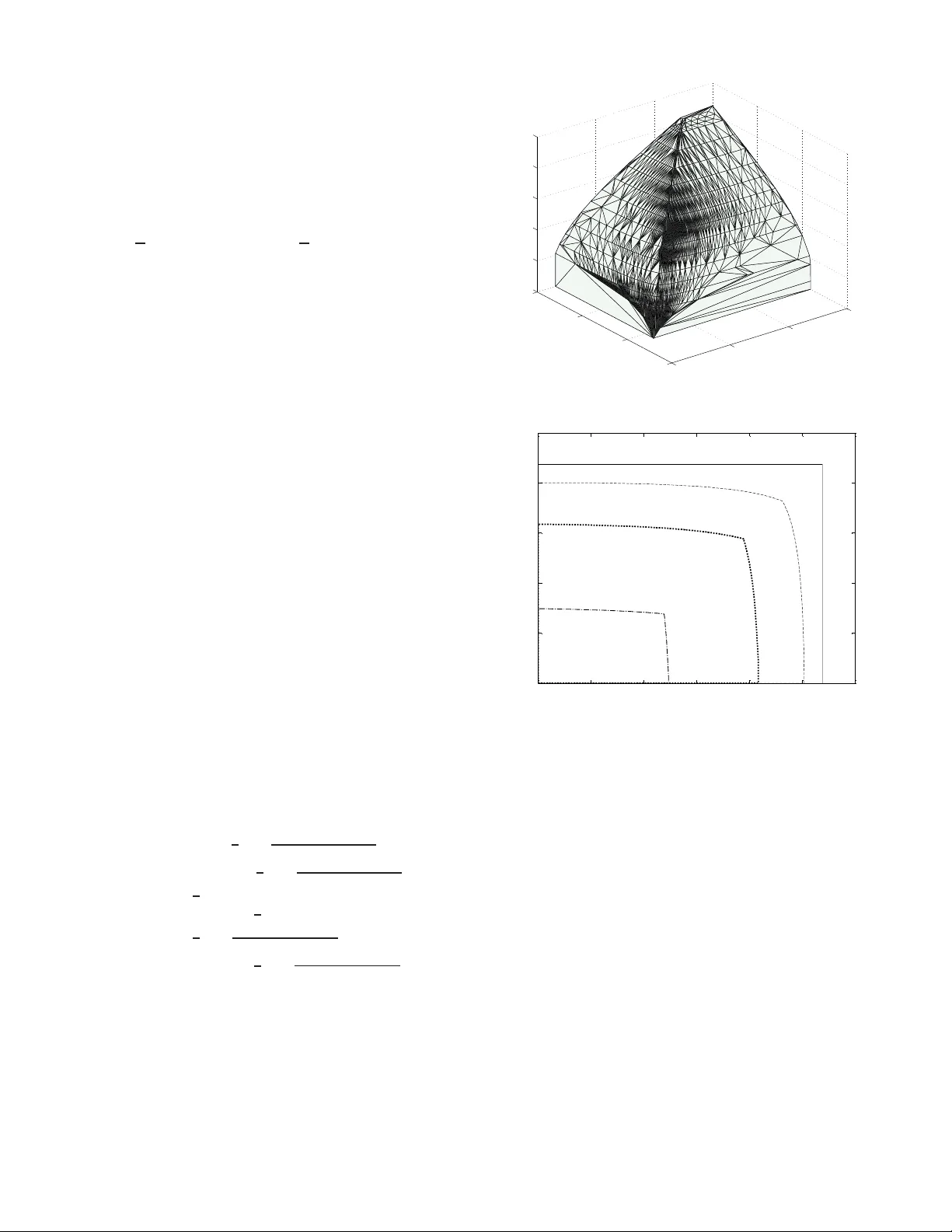
1 Ne w Results on Multi ple-Input Multiple-Output Broadcast Channels with Confidential Me ssages Ruoheng Liu, T ie Liu, H. V incen t Poor , and Shlomo Shamai (Shit z) Abstract —This paper presents two n ew results on multiple- input multiple-outp ut (MIMO) Gaussian broadcast chan nels with confidential messages. First, the p roblem of the MIMO Gaussian wiretap channel is revisited. A matrix character ization of the capacity-equiv ocation region is pr ovided, which ex tends the prev ious r esult on the secrecy capacity of the MIMO Gaussian wiretap channel to th e general, possibl y imperfect secrecy setting. Next, the problem of MIMO Gaussian bro adcast channels with two re ceiv ers and three indepen dent me ssages: a common mes- sage intended f or both recei vers, and two c onfidential messages each intended f or one of the receiv ers but n eeding to be kept asymptotically perfectly secret from the other , is considered. A precise characterization o f the capacity reg ion is pr ovided, generalizing the pr evious results which considered only two out of three possible messages. Index T erms —Multiple-i nput multiple-outpu t (MIMO) com- munication, wiretap channel, capacity-equivocation region, broadcast channel, confidential message I . I N T RO D U C T I O N Inform ation-the oretic secur ity has been a very active area of research r ecently . (See [ 1] and [2 ] for o verviews of re- cent prog ress in this field.) In p articular, significan t progr ess has been made in understand ing the fundamental limits of multiple-inp ut multiple-ou tput (MIMO) secret comm unication . More specifically , the secrecy capacity o f th e MIMO Gaussian wiretap chann el was characterized in [3]–[7]. The works [8] and [ 9] co nsidered th e problem of MIMO Gaussian br oadcast channels with two con fidential messages, each in tended for one r eceiver but needin g to be kept a symptotically p erfectly secret f rom the other, an d pr ovided a pr ecise charac terization of the capacity region. The capacity region of t he MIMO Gaus- sian broadcast channel with two recei vers and two independen t messages, a common message inten ded for b oth receivers an d a co nfidential messag e in tended fo r on e of the receiv ers but This researc h was supported by the Nationa l Science Foundatio n under Grant CNS-09-0539 8, CCF-08-45848 and CCF-09-16867 , by the Air Force Offic e of Scient ific Research under Grant F A9550-08-1-048 0, by the European Commission in the frame work of the FP7 Net work of Excelle nce in W ireless Communicat ions NEWCOM++, and by the Israel Science Foundation. The materia l in this paper was prese nted in part at the IEEE Int ernati onal Symposium on Information Theory (ISIT), Austin, TX, June 2010. Ruoheng Liu is with Alcatel-Luc ent, Murray Hill, NJ 07974, USA (email: ruoheng.li u@alca tel-lucent.com). Tie Liu is with the Department of Electrical and Computer E ngineer - ing, T ex as A&M Uni versity , Colle ge Statio n, TX 77843, USA (e-mail: tieli u@tamu.edu). H. V ince nt Poor is with the Department of Electrical E ngineeri ng, Princeton Uni ver sity , Princeton, NJ 08544, USA (e-mail: poor@princ eton.edu). Shlomo Shamai (Shitz) is with the Department of Electri cal Engineerin g, T echnion-Isra el Institute of T echnology , T echnion City , Haifa 32000, Israel (e-mail: sshlomo@ee.t echnion .ac.il). needing to be kept asympto tically p erfectly secret from the other, was c haracterized in [10]. This paper presents two new results on MIMO Ga ussian broadc ast channels with confiden tial messages 1 : 1) Th e proble m of the MIMO Gaussian wiretap ch annel is r evisited. A m atrix characterization of the capacity- equivoca tion region is pr ovided, which extends the result of [6] on the secrecy capacity o f the MIMO Gaussian wiretap channel to the general, possibly imperfect secrecy setting. 2) Th e prob lem of MIMO Gau ssian br oadcast chann els with two recei vers and thr ee indepen dent messages, a common message inten ded for both r eceiv ers, an d two mutually confid ential me ssages e ach intend ed f or one of the receivers but ne eding to be kept asy mptotically perfectly secret fr om the o ther, is considere d. A precise characterizatio n of the capacity region is provided, gener- alizing the results of [9] and [10] which considered only two out of th ree po ssible messages. Notation . V ectors and matrices ar e written in bold letters. All vectors by default are c olumn vectors. The iden tity m a- trices are denoted by I , where a subscr ipt may be used to indicate the size o f the ma trix to av oid possible con fusion. The transpo se o f a matrix A is den oted by A ⊺ , and the tr ace of a squar e matrix A is denoted b y T r( A ) . Finally , we write A B (or, equivalently , B A ) when ever B − A is p ositiv e semidefinite. I I . T H E C A PAC I T Y - E Q U I V O C AT I O N R E G I O N O F T H E M I M O G AU S S I A N W I R E TA P C H A N N E L A. Channel Model Consider a MI MO Gaussian b roadcast channel with two receivers, one of which is a legitimate receiver and the o ther is an eavesdropper . The received signals at time ind ex m are giv en by Y [ m ] = H r X [ m ] + W r [ m ] Z [ m ] = H e X [ m ] + W e [ m ] (1) where H r and H e are (real) c hannel matrices a t th e legitimate receiver and the ea vesdropper re spectiv ely , and { W r [ m ] } m and { W e [ m ] } m are in depend ent and identically distributed (i.i.d.) additi ve vector Gaussian noise processes with zero means an d iden tity covariance m atrices. 1 The main results of this paper were initi ally posted on the arXiv websit e in January 2010 [11] and were subsequently reported at the 2010 IEE E Interna tional Symposium on Information Theory [12], [13]. Similar results were independentl y reported by Ekrem and Ulukus in [14] and [15]. 2 W X n Y n Tra nsmitt er Legitima te receiver W ^ Z n Eavesdropper R e – ε ≤ H (W|Z n ) 1 n _ Cha nnel p ( y , z | x ) (a) Rate-e qui vo cation setting (W s , W p ) X n Y n Tra nsmitt er Legitima te receiver (W s , W p ) ^ ^ Z n Eavesdropper I (W s ; Z n ) → 0 1 n _ Cha nnel p ( y , z | x ) (b) Simultane ous priv ate-confidenti al communication Fig. 1. Wiret ap channel. The transmitter has a sing le message W , which is uni- formly distributed over { 1 , . . . , 2 nR } where R is the rate of commun ication. The goal of com munication is to deliv er W reliably to the legitimate recei ver while keeping it information- theoretically secure from the eavesdropper . Following th e classical work [16], [ 17], for every ǫ > 0 it is requ ired that 1 n H ( W | Z n ) ≥ R e − ǫ (2) for sufficiently large n , wher e n is th e block len gth of co mmu- nication, Z n := ( Z [1] , . . . , Z [ n ]) , and R e represents the pr ede- termined lev el of security of message W at the eavesdropper known as equivoca tion . T he capa city-equivo cation region is the set of rate-equivocation pairs ( R, R e ) that can be a chieved by any co ding schem e. In the literature, this co mmunicatio n scenario is usually known as the rate-eq uiv ocation setting o f the MIMO Gaussian wir etap channel; see Fig. 1(a) for an illustration. Csisz ´ ar and K ¨ orner [17] stu died the rate-equiv ocation set- ting o f a general d iscrete mem oryless wiretap channel. A single-letter e xpression for the capacity-eq uiv ocation region was derived [17, Theorem 1], which can be written as the set of no nnegative rate-equiv ocation pairs ( R , R e ) satisfying R e ≤ min { R, I ( V ; Y | U ) − I ( V ; Z | U ) } R ≤ I ( V ; Y ) (3) for some p ( u, v, x, y, z ) = p ( u ) p ( v | u ) p ( x | v ) p ( y , z | x ) . Here, p ( y , z | x ) is the tran sition probability of the discrete memor y- less wiretap chann el, and U an d V are two auxiliary rando m variables. I n theory , a comp utable expression fo r the capacity- equiv ocation region can be ob tained by ev aluating the single- letter expression (3) fo r the MIM O Gaussian wiretap ch annel (1). Howe ver , such an e valuation is generally difficult due to the presence of the auxiliary r andom variables U an d V . Sev eral recent works [3]–[7] stud ied the spe cial c ase where the eq uiv ocation R e is set to equal the co mmunica tion ra te R . In this case, th e secrecy constraint (2) can be equ iv ale ntly written as 1 n I ( W ; Z n ) ≤ ǫ (4) i.e., me ssage W needs to be asymp totically perfectly secure from th e eavesdropper . Und er the asympto tic perfec t secrecy constraint (2), th e maximu m rate of co mmunicatio n is called the secr ecy cap acity . For the MIMO Gaussian wiretap channel (1), a matrix char acterization of the secre cy capacity w as obtained in [3]–[5] under an a verag e total power constraint and in [6] an d [7] unde r a mo re general matrix p ower con straint. Similar matr ix characteriza tions of the capacity- equiv ocation region, howe ver , were unkn own . B. Main Results The ma in r esult o f this sectio n is a m atrix character ization of the capacity-eq uiv ocation region of the MIMO Gau ssian wiretap chan nel. More specifically , consid er the MIMO Gaus- sian wir etap cha nnel (1) under th e matrix power constra int 1 n n X m =1 ( X [ m ] X ⊺ [ m ]) S (5) where S is a positiv e semidefinite matrix. Let C ( S , H r ) = 1 2 log | I + H r SH ⊺ r | (6) be the Shannon capacity of a MIM O Gau ssian p oint-to- point channel with channel matrix H r and u nder the matrix power constraint (5), and let C s ( S , H r , H e ) = max 0 B S 1 2 log I + H r BH ⊺ r I + H e BH ⊺ e (7) be the secrecy cap acity of a MIMO Gaussian wiretap ch annel with le gitimate recei ver and eav esdropper chann el matrices H r 3 0 1 2 3 4 5 6 0 0.5 1 1.5 2 2.5 3 3.5 4 R R e (a) Capaci ty-equi vocation region 0 1 2 3 4 5 6 0 0.5 1 1.5 2 2.5 3 3.5 4 R p R s (b) Pri v ate-co nfidentia l m essage capacity regio n Fig. 2. MIMO Gaussian wireta p channel under matrix power constraint. and H e respectively and un der the matrix p ower constrain t (5) [6], [7]. W e then have the fo llowing result. Theor em 1: The capacity-eq uiv ocation region of the MIMO Gaussian wiretap chan nel (1) unde r th e matrix power co n- straint (5) is given by the set of nonnegative rate-equiv ocation pairs ( R, R e ) satisfying R e ≤ min { R, C s ( S , H r , H e ) } R ≤ C ( S , H r ) (8) where C ( S , H r ) an d C s ( S , H r , H e ) ar e defined as in (6) a nd (7), respectively . Fig. 2(a) illustrates th e cap acity-equ iv o cation region of a MIMO Gau ssian wireta p chan nel with channe l matrices H r = 1 . 8 2 . 0 1 . 0 3 . 0 and H e = 3 . 3 1 . 3 2 . 0 − 1 . 5 (which yield s a nonde graded wire tap chann el) and matr ix power constraint S = 5 . 0 1 . 25 1 . 25 10 . 0 . The capacity-e quiv ocation region of the MIMO Gau ssian wiretap chan nel under an av erage total power constraint is summarized in the following corollary . Th e result is a direct consequen ce of Theo rem 1 and [1 8, Lem ma 1] . Cor ollary 1: The capacity-eq uiv ocation region o f the MIMO Gaussian wire tap ch annel ( 1) under the average total power constraint 1 n n X m =1 ( X [ m ] ⊺ X [ m ]) ≤ P (9) is given by the set of non negativ e rate-equ iv o cation pairs ( R, R e ) satisfying R e ≤ min { R, C s ( S , H r , H e ) } R ≤ C ( S , H r ) (10) for som e S 0 , T r ( S ) ≤ P . C. Pr oof o f th e Main Results Next, we prove Theore m 1. As mentioned pr eviously , directly ev aluating the single-letter expression ( 3) fo r the MIMO Gaussian wiretap chann el (1) is difficult due to the presence of the au xiliary rand om variables. W e thus resor t to an indir ect app roach t hat connects the rate-eq uiv ocation setting of a MIM O Gaussian wiretap ch annel to the p roblem of simul- taneously com municatin g priv ate an d con fidential messages. The prob lem of simultaneously comm unicating priv ate and confidential messages over a discrete mem oryless wiretap channel is illu strated in Fig. 1(b). Here, th e transmitter h as a priv ate message W p , wh ich is unifo rmly distributed over { 1 , . . . , 2 nR p } , a nd a confidential message W s , whic h is unifor mly d istributed over { 1 , . . . , 2 nR s } . Th e co nfidential message W s is intended for the le gitimate recei ver b u t needs to be kept asymptotically perfectly secret from th e eavesdropper . That is, for any ǫ > 0 it is required th at 1 n I ( W s ; Z n ) ≤ ǫ (11) for sufficiently large b lock length n . Th e p riv ate message W p is also in tended for the legitimate receiver , but is not subject to any secr ecy constraint. The private-co nfiden tial message capacity region is th e set o f p riv ate-confidential rate pair s ( R p , R s ) that can be achieved by any coding sch eme. The fo llowing lemma provides a sing le-letter character iza- tion o f the priv a te-confiden tial message capacity r egion of the discrete mem oryless wiretap channel. Lemma 1: The priv ate-confiden tial message capac ity re- gion o f th e d iscrete memo ryless wiretap chann el p ( y , z | x ) is giv en by th e set of nonn egativ e private-confidential rate pair s ( R p , R s ) satisfying R s ≤ I ( V ; Y | U ) − I ( V ; Z | U ) R s + R p ≤ I ( V ; Y ) (12) for some p ( u, v , x, y, z ) = p ( u ) p ( v | u ) p ( x | v ) p ( y , z | x ) , where U and V are auxiliary random variables. The achiev ability p art of th e lem ma can b e proved by considerin g a co ding scheme that comb ines super position coding, rand om binnin g, and rate splitting. In particular, part of the private message will be u sed in the binnin g schem e 4 (W 0 ,W 1 ,W 2 ) X n Z 1 Y 1 H 1 Tra n smitt e r + × n n Rec eiv er 1 (W 0 ,W 1 ) ^ ^ I (W 2 ; Y 1 ) → 0 n 1 n _ Z 2 Y 2 H 2 + × n n Rece ive r 2 (W 0 ,W 2 ) ^ ^ I (W 1 ; Y 2 ) → 0 n 1 n _ Fig. 3. MIMO Gaussian broadca st channel with common and confidentia l messages. to protect the co nfidential message against the eavesdropper . The conv erse p roof follows standard infor mation-th eoretic argument. The details of the proo f are deferred to Appe ndix A. A simp le inspec tion of the capacity- equiv ocation region (3) an d th e p riv ate-confidential message capacity region (1 2) reveals th e following interesting fact: F act 1: A non negative rate pair ( R, R e ) = ( R p + R s , R s ) is an achiev able rate-equivocation pair fo r a discrete memor yless wiretap ch annel if an d on ly if ( R p , R s ) is an ac hiev able priv ate-confiden tial rate pair for th e same chann el. The “if” par t of the fact is easy to verify: Sim ply use the sa me co de for both commun ication scenar ios an d view ( W p , W s ) as the single message W for the rate-equivocation setting. Note that 1 n H ( W | Z n ) = 1 n H ( W p , W s | Z n ) ≥ 1 n H ( W s | Z n ) ≥ R s − ǫ = R e − ǫ. Thus, the same code satisfying the secrecy constraint (1 1) fo r simultaneou s private-confidential commun ication also satisfies the secrecy constraint (2) fo r the rate- equiv ocation setting. T he “only if ” p art of the fact c omes as a mild sur prise, as in the rate-equivocation setting which p art of message is secure does not need to be specified a p riori and may ev en de pend on the r ealization o f th e chann el noise. W e n ote here that the above interesting fact was first m entioned in [1 9, pp . 411– 412] witho ut pr oof. In light of Fact 1, next we first establish a ma trix c harac- terization of the priv ate-confiden tial message capacity region using the existing m atrix ch aracterization [6], [7] on the secrecy c apacity of the MI MO Gaussian wiretap ch annel. The result will then be mapp ed to the rate-equ i vocation setting using the afo remention ed equiv alence b etween these two com munication scenarios. Lemma 2: The pr iv ate- confiden tial message capacity region of the MIMO Gau ssian wire tap chan nel (1) u nder the matrix power constraint (5) is given by the set o f n onnegative p riv a te- confidential ra te p airs ( R p , R s ) satisfying R s ≤ C s ( S , H r , H e ) R s + R p ≤ C ( S , H r ) . (13) Pr oo f: Let B ∗ be an optima l solution to the op timization problem on the right- hand side of ( 7). Then, the achiev a bility of the priv a te-confiden tial rate r egion (13) follows from th at of (12) by setting V = X = U + G , where U an d G denote two indepen dent Gaussian vectors with zero means and cov ariance matrices S − B ∗ and B ∗ , r espectively . The fact th at R s ≤ C s ( S , H r , H e ) fo r any achievable confidential rate R s follows from the secrecy capacity r esult of [6] and [ 7] o n th e M IMO Ga ussian wire tap ch annel u nder a matrix p ower constraint, b y ignoring the priv ate message W p . The fact that R s + R p ≤ C ( S , H r ) for any a chiev able pr iv ate- confidential r ate p air ( R p , R s ) fo llows from the well-kn own capacity result on the MIMO Gaussian point-to- point chann el under a matrix power constrain t, by viewing ( W p , W s ) as a single message and ign oring the asymptotic per fect secre cy constraint (11) on the co nfidential message W s . Remark 1: It is particu larly worth m entionin g the co rner point ( R p , R s ) of the private-confidential message capa city region (13) as given by ( R p , R s ) = ( C ( S , H r ) − C s ( S , H r , H e ) , C s ( S , H r , H e )) . Here, u nder the matrix power constrain t, both messages W s and ( W p , W s ) , viewed as a sin gle pr iv ate message, can transmit simultaneou sly at their re spectiv e maximum rates. In particular, transmitting an additional pri vate message W p does not incur any r ate loss for co mmunic ating the c onfidential message W s . Now , Theorem 1 fo llows im mediately from Lem ma 2 an d a Fourier-Motzkin elim ination with R = R p + R s and R e = R s . For comparison , the private-confidential message capacity region of th e same MIM O Gau ssian wiretap chan nel as used for Fig . 2(a) is illu strated in Fig. 2(b). I I I . M I M O G AU S S I A N B RO A D C A S T C H A N N E L S W I T H C O M M O N A N D C O N FI D E N T I A L M E S S A G E S A. Cha nnel Model Consider a tw o-receiver MIMO Gaussian broad cast channe l. The transmitter is equ ipped with t transmit anten nas, and receiver k , k = 1 , 2 , is equ ipped with r k receive antennas. A discrete-time sample of the channel at tim e m can b e written as Y k [ m ] = H k X [ m ] + Z k [ m ] , k = 1 , 2 (14) where H k are the ( real) ch annel matrices of size r k × t , and { Z k [ m ] } m are i.i.d. additive vector Gaussian noise pro cesses 5 with z ero me ans and identity covariance matrices. 2 As illustrated in Fig. 3, the transmitter has a common mes- sage W 0 and two ind epend ent confiden tial messages W 1 and W 2 . The comm on message W 0 is intended for both recei vers. The confidential message W k is intend ed fo r receiv er k but needs to be kept asympto tically perf ectly secret from th e o ther receiver . Math ematically , fo r every ǫ > 0 we m ust have 1 n I ( W 1 ; Y n 2 ) ≤ ǫ and 1 n I ( W 2 ; Y n 1 ) ≤ ǫ (15) for sufficiently large block length n . Our go al h ere is to character ize the en tire capacity region C ( H 1 , H 2 , S ) = { ( R 0 , R 1 , R 2 ) } that can b e achieved by any cod ing schem e, where R 0 , R 1 and R 2 are the commun ication ra tes correspond - ing to the common message W 0 and the confid ential messages W 1 and W 2 , r espectively . W ith both con fidential messages W 1 and W 2 but witho ut the commo n message W 0 , the pro blem was studied in [8] for the mu ltiple-inpu t sin gle-outp ut (MISO) case and in [9] for general MIMO case. Rather surpr isingly , it was shown in [ 9] that, un der a matrix power constrain t both co nfidential mes- sages ca n be simultaneously com municated at the ir r espected maximum rates. W ith the common me ssage W 0 and o nly o ne confidential message ( W 1 or W 2 ), th e ca pacity region o f th e MIMO Gaussian wiretap cha nnel was characte rized in [10] using a cha nnel-enh ancemen t approach [18] and an extremal entropy inequ ality of W eingarten et al. [21]. B. Ma in Results The main result of this section is a prec ise characterization of the capac ity region of th e MIMO Gaussian br oadcast chan- nel with a more co mplete message set that inclu des a commo n message W 0 and two in depend ent confiden tial messages W 1 and W 2 . Theor em 2: The capacity region C ( H 1 , H 2 , S ) of the MIMO Gaussian broadcast channel (1 4) with a co mmon mes- sage W 0 and two con fidential m essages W 1 and W 2 under the matrix p ower constraint (5 ) is given by th e set of nonnegative rate triples ( R 0 , R 1 , R 2 ) such th at R 0 ≤ min n 1 2 log H 1 SH ⊺ 1 + I r 1 H 1 ( S − B 0 ) H ⊺ 1 + I r 1 , 1 2 log H 2 SH ⊺ 2 + I r 2 H 2 ( S − B 0 ) H ⊺ 2 + I r 2 o R 1 ≤ 1 2 log | I r 1 + H 1 B 1 H ⊺ 1 | − 1 2 log | I r 2 + H 2 B 1 H ⊺ 2 | R 2 ≤ 1 2 log I r 2 + H 2 ( S − B 0 ) H ⊺ 2 I r 2 + H 2 B 1 H ⊺ 2 − 1 2 log I r 1 + H 1 ( S − B 0 ) H ⊺ 1 I r 1 + H 1 B 1 H ⊺ 1 (16) for som e B 0 0 , B 1 0 and B 0 + B 1 S . Remark 2: By setting B 0 = 0 we can recover th e result of [9, Theo rem 1] that include s both confidential messages W 1 and W 2 but without the co mmon message W 0 . Similar to [9, Theorem 1], f or any g i ven B 0 the up per bound s on R 1 and R 2 can be simultaneou sly maximized by a same B 1 . I n fact, the u pper bounds on R 1 and R 2 in (16) are fully symmetric 2 The channe l model is the same as that in Section II-A. Howe ver , dif feren t notati on is used here for the con venienc e of presentation . 0 1 2 3 0 1 2 3 0 1 2 3 4 5 R 1 R 2 R 0 (a) Capaci ty region C ( H 1 , H 2 , S ) 0 0.5 1 1.5 2 2.5 3 0 0.5 1 1.5 2 2.5 R 1 R 2 R 0 =0 R 0 =1.60 R 0 =2.40 R 0 =3.45 (b) ( R 1 , R 2 ) -cross sections Fig. 4. MIMO Gaussian broadc ast channe l with common and confidential messages. with respect to H 1 and H 2 , even tho ugh it is n ot immediately evident from the expressions themselves. Remark 3: By setting B 0 = S − B 1 we can recover the result of [1 0, Th eorem 1] that include s the commo n message W 0 and the confidential message W 1 but without the other confidential me ssage W 2 . Fig. 4(a) illustrates th e capacity region C ( H 1 , H 2 , S ) f or the channel matrices and the matrix power c onstraint as given by H 1 = 1 . 8 2 . 0 1 . 0 3 . 0 , H 2 = 3 . 3 1 . 3 2 . 0 − 1 . 5 and S = 5 . 0 1 . 25 1 . 25 10 . 0 . (The channel parameters are the same as those used for Fig. 2.) In Fig. 4(b), we have also plotted the ( R 1 , R 2 ) -cross sectio n of C ( H 1 , H 2 , S ) for several giv en values of R 0 . Note that when R 0 = 0 , the ( R 1 , R 2 ) -cross section is r ectangula r , im- plying that under a matrix power con straint, both confidential 6 messages W 1 and W 2 can be simu ltaneously tr ansmitted at their respec ti ve maximum rates [9]. For R 0 > 0 , howe ver , the ( R 1 , R 2 ) -cross sections are gen erally non-r ectangular as different b ound ary points on th e sam e cr oss section m ay correspo nd to d iffer ent choic e of B 0 . The capacity r egion u nder a n a verage to tal power constrain t is summarized in the following coro llary . T he r esult is a direct consequen ce of Theo rem 2 and [18, Lem ma 1]. Cor ollary 2: The cap acity region C ( H 1 , H 2 , P ) of th e MIMO Gaussian b roadca st chan nel (14) with a co mmon message W 0 and two confidential m essages W 1 and W 2 under the av erage total p ower constraint (9) is given by C ( H 1 , H 2 , P ) = [ S 0 , T r( S ) ≤ P C ( H 1 , H 2 , S ) . (17) C. Pr oo f of the Ma in R esults Next, we prove Theo rem 2. Following [ 18], we shall focu s on the canonical case in which the channel matrices H 1 and H 2 are squa re and inv ertible and the matrix power constraint S is strictly p ositiv e definite. In this case, multiplying both sides o f (1 4) by H − 1 k , the MIMO Gaussian bro adcast chann el (14) can be equivalently written as Y k [ m ] = X k [ m ] + Z k [ m ] , k = 1 , 2 (18) where { Z k [ m ] } m are i.i.d . add itiv e vector Gaussian n oise processes with zero m eans a nd covariance matrices N k = H − 1 k H − ⊺ k . Similarly , the rate region (16) can be eq uiv alently written as R 0 ≤ min n 1 2 log S + N 1 ( S − B 0 )+ N 1 , 1 2 log S + N 2 ( S − B 0 )+ N 2 o R 1 ≤ 1 2 log B 1 + N 1 N 1 − 1 2 log B 1 + N 2 N 2 R 2 ≤ 1 2 log ( S − B 0 )+ N 2 B 1 + N 2 − 1 2 log ( S − B 0 )+ N 1 B 1 + N 1 . (19) Next, we show th at the r ate region (19) over all possible B 0 0 , B 1 0 and B 0 + B 1 S gives the capacity region C ( H 1 , H 2 , S ) for the canonical MIMO Gaussian b roadcast channel (18). Extensions to the general model (14) follo w fro m the well-kn own limitin g argumen t [6], [10], [1 8] and hence are omitted f rom the pap er . T o p rove th e achiev ability of the rate r egion (19), recall that the problem of a two-receiv er discrete memory less bro ad- cast chan nel with a com mon message and two confiden tial common m essages was stud ied in [22]. Ther e, a single-letter expression for an achie vable rate region was established, which is given by the set of rate trip les ( R 0 , R 1 , R 2 ) such that R 0 ≤ min[ I ( U ; Y 1 ) , I ( U , Y 2 )] R 1 ≤ I ( V 1 ; Y 1 | U ) − I ( V 1 ; V 2 , Y 2 | U ) R 2 ≤ I ( V 2 ; Y 2 | U ) − I ( V 2 ; V 1 , Y 1 | U ) (20) where U , V 1 and V 2 are auxiliary random variables satisfying the Markov relatio n ( U , V 1 , V 2 ) → X → ( Y 1 , Y 2 ) . The propo sed coding scheme is a natural comb ination of do uble binning [23] and sup erposition coding. Thu s, th e achiev ability of th e rate region (1 9) follows from tha t of (20) b y setting V 1 = U 1 + FU 2 , V 2 = U 2 , and X = U + U 1 + U 2 where U , U 1 and U 2 are three indepen dent Gau ssian vector s with zero means and covariance matr ices B 0 , B 1 and S − B 0 − B 1 respectively , and F := BH ⊺ 1 ( I r 1 + H 1 BH ⊺ 1 ) − 1 H 1 . T o show th at the rate region (19) over all po ssible B 0 0 , B 1 0 and B 0 + B 1 S is indeed the capacity region, we shall conside r proof by contrad iction and resort to a ch annel- enhancem ent argument akin to that in [ 10]. More specifically , assume that ( R † 0 , R † 1 , R † 2 ) is an achievable rate triple that lies outside the rate regio n (19) for any given B 0 0 , B 1 0 and B 0 + B 1 S . Since ( R † 0 , R † 1 , R † 2 ) is achiev able, we can bo und R † 0 by R † 0 ≤ min 1 2 log S + N 1 N 1 , 1 2 log S + N 2 N 2 = R max 0 . Moreover , if R † 1 = R † 2 = 0 , then R max 0 can be achieved by setting B 0 = S and B 1 = 0 in (19). Thu s, b y the assum ption that ( R † 0 , R † 1 , R † 2 ) is outside the rate region ( 19) fo r any gi ven B 0 0 , B 1 0 an d B 0 + B 1 S , we can always find λ 1 ≥ 0 and λ 2 ≥ 0 such that λ 1 R † 1 + λ 2 R † 2 = λ 1 R ⋆ 1 + λ 2 R ⋆ 2 + ρ (21) for som e ρ > 0 , where λ 1 R ⋆ 1 + λ 2 R ⋆ 2 is given by max ( B 0 , B 1 ) λ 1 f 1 ( B 1 ) + λ 2 f 2 ( B 0 , B 1 ) subject to f 0 ( B 0 ) ≥ R † 0 B 0 0 B 1 0 B 0 + B 1 S . (22) Here, the functio ns f 0 , f 1 and f 2 are defin ed as f 0 ( B 0 ) := min 1 2 log S + N 1 ( S − B 0 ) + N 1 , 1 2 log S + N 2 ( S − B 0 ) + N 2 f 1 ( B 1 ) := 1 2 log B 1 + N 1 N 1 − 1 2 log B 1 + N 2 N 2 and f 2 ( B 0 , B 1 ) := 1 2 log ( S − B 0 ) + N 2 B 1 + N 2 − 1 2 log ( S − B 0 ) + N 1 B 1 + N 1 . Let ( B ⋆ 0 , B ⋆ 1 ) be an op timal solu tion to the optimizatio n progr am ( 22). By assumption , th e matr ix p ower constraint S is strictly p ositiv e definite in the can onical model. Thus, ( B ⋆ 0 , B ⋆ 1 ) must satisfy the following Ka rush-Kuhn- T u cker (KKT) co nditions: ( β 1 + λ 2 )[( S − B ⋆ 0 ) + N 1 ] − 1 + β 2 [( S − B ⋆ 0 ) + N 2 ] − 1 + M 0 = λ 2 [( S − B ⋆ 0 ) + N 2 ] − 1 + M 2 (23) ( λ 1 + λ 2 )( B ⋆ 1 + N 1 ) − 1 + M 1 = ( λ 1 + λ 2 )( B ⋆ 1 + N 2 ) − 1 + M 2 (24) M 0 B ⋆ 0 = 0 , M 1 B ⋆ 1 = 0 , and M 2 ( S − B ⋆ 0 − B ⋆ 1 ) = 0 (2 5) where M 0 , M 1 and M 2 are positi ve sem idefinite matrices, and β k , k = 1 , 2 , are nonn egati ve real scalars such that β k > 0 if 7 and o nly if 1 2 log S + N k ( S − B ⋆ 0 ) + N k = R † 0 . It f ollows that ( β 1 + β 2 ) R † 0 + λ 1 R † 1 + λ 2 R † 2 = β 1 2 log S + N 1 ( S − B ⋆ 0 ) + N 1 + β 2 2 log S + N 2 ( S − B ⋆ 0 ) + N 2 + λ 1 1 2 log B ⋆ 1 + N 1 N 1 − 1 2 log B ⋆ 1 + N 2 N 2 + λ 2 1 2 log ( S − B ⋆ 0 ) + N 2 B ⋆ 1 + N 2 − 1 2 log ( S − B ⋆ 0 ) + N 1 B ⋆ 1 + N 1 + ρ. (26) Next, we shall find a contrad iction to (26) th rough the following three steps. 1) Split each r eceiver into two virtua l r eceivers: Con sider the f ollowing c anonical MIMO Gaussian bro adcast channel with f our receivers: Y 1 a [ m ] = X [ m ] + Z 1 a [ m ] Y 1 b [ m ] = X [ m ] + Z 1 b [ m ] Y 2 a [ m ] = X [ m ] + Z 2 a [ m ] Y 2 b [ m ] = X [ m ] + Z 2 b [ m ] (27) where { Z 1 a [ m ] } , { Z 1 b [ m ] } , { Z 2 a [ m ] } and { Z 2 b [ m ] } are i. i.d. additive vector Gaussian n oise pro cesses with zero m eans and covariance matr ices N 1 , N 1 , N 2 and N 2 , r espectively . Suppose that the transmitter has three indep endent messages W 0 , W 1 and W 2 , where W 0 is intended for both r eceivers 1 b and 2 b , W 1 is intended for receiver 1 a but needs to be kept asymptotically perfectly secret from receiv er 2 b , an d W 2 is intended for receiver 2 a but n eeds to be kept asymptotically perfectly secret fro m rec eiv er 1 b . Mathematically , for ev ery ǫ > 0 , we must have 1 n I ( W 1 ; Y n 2 b ) ≤ ǫ and 1 n I ( W 2 ; Y n 1 b ) ≤ ǫ (28) for sufficiently large block length n . Note that rec eiv ers 1 a and 1 b are statistically id entical to receiver 1 in cha nnel (18), so ar e rec eiv ers 2 a and 2 b to receiver 2 in ch annel ( 18). W e thus c onclude that th e cap acity region of channel ( 27) is the same as that of chan nel (1 8) under the same matrix power constraint. 2) Construct an enh anced channel: Let e N b e a real sym- metric matr ix satisfying e N := N − 1 1 + 1 λ 1 + λ 2 M 1 − 1 (29) which im plies tha t e N N 1 . Since M 1 B ⋆ 1 = 0 , following [18, Lemma 1 1] we have ( λ 1 + λ 2 )( B ⋆ 1 + e N ) − 1 = ( λ 1 + λ 2 )( B ⋆ 1 + N 1 ) − 1 + M 1 and | B ⋆ 1 + e N || N 1 | = | B ⋆ 1 + N 1 | | e N | . (30) Follo wing (24), we m ay also obtain ( λ 1 + λ 2 )( B ⋆ 1 + e N ) − 1 = ( λ 1 + λ 2 )( B ⋆ 1 + N 2 ) − 1 + M 2 (31) which imp lies that e N N 2 . Consider the following en hanced align ed MIMO Gaussian broadc ast channel e Y 1 a [ m ] = X [ m ] + e Z 1 a [ m ] Y 1 b [ m ] = X [ m ] + Z 1 b [ m ] e Y 2 a [ m ] = X [ m ] + e Z 2 a [ m ] Y 2 b [ m ] = X [ m ] + Z 2 b [ m ] (32) where { e Z 1 a [ m ] } , { Z 1 b [ m ] } , { e Z 2 a [ m ] } an d { Z 2 b [ m ] } are i. i.d. additive vector Gaussian n oise pro cesses with zero m eans and covariance matr ices e N , N 1 , e N and N 2 , r espectively . The message set config uration is the same as that for channel (27). Since e N { N 1 , N 2 } , w e conclud e that th e capacity r egion of chann el (32) is at least as lar ge as that of channel (2 7) und er the same matrix p ower c onstraint. Furthermo re, from (31) we h ave [( S − B ⋆ 0 ) + e N ]( B ⋆ 1 + e N ) − 1 = [( S − B ⋆ 0 ) + N 2 ]( B ⋆ 1 + N 2 ) − 1 (33) and h ence ( S − B ⋆ 0 ) + e N B ⋆ 1 + e N = ( S − B ⋆ 0 ) + N 2 B ⋆ 1 + N 2 . (34) Combining ( 23) and (31), we m ay ob tain ( λ 1 + λ 2 )[( S − B ⋆ 0 ) + e N ] − 1 = ( λ 2 + β 1 )[( S − B ⋆ 0 ) + N 1 ] − 1 + ( λ 1 + β 2 )[( S − B ⋆ 0 ) + N 2 ] − 1 + M 0 . (35) Substituting (3 0) and (34) into (2 6), we have ( β 1 + β 2 ) R † 0 + λ 1 R † 1 + λ 2 R † 2 = β 1 2 log S + N 1 ( S − B ⋆ 0 ) + N 1 + β 2 2 log S + N 2 ( S − B ⋆ 0 ) + N 2 + λ 1 1 2 log ( S − B ⋆ 0 ) + e N e N − 1 2 log ( S − B ⋆ 0 ) + N 2 N 2 ! + λ 2 1 2 log ( S − B ⋆ 0 ) + e N e N − 1 2 log ( S − B ⋆ 0 ) + N 1 N 1 ! + ρ. (36) 3) Outer bound the enhanced chann el: Next, we consider a discrete memo ryless broadca st channel with fo ur rece i vers and three indep endent messages and provide a single-letter outer bound on the capacity region. Lemma 3: Consider a discrete m emoryless broad cast chan- nel p ( e y 1 a , y 1 b , e y 2 a , y 2 b | x ) with four r eceivers an d three in - depend ent messages ( W 0 , W 1 , W 2 ) : W 0 is intended for both receivers 1 b and 2 b , W 1 is intended for receiver 1 a but needs to be kept asymp totically perfectly secret from rece iv er 2 b , and W 2 is in tended for receiver 2 a but needs to be kept 8 asymptotically perfe ctly secret fro m receiver 1 b . Assume tha t X → e Y 1 a → ( Y 1 b , Y 2 b ) and X → e Y 2 a → ( Y 1 b , Y 2 b ) form two Markov cha ins. Th en, any achiev able rate triple ( R 0 , R 1 , R 2 ) mu st satisfy R 0 ≤ min[ I ( U ; Y 1 b ) , I ( U, Y 2 b )] R 1 ≤ I ( X ; e Y 1 a | U ) − I ( X ; Y 2 b | U ) R 2 ≤ I ( X ; e Y 2 a | U ) − I ( X ; Y 1 b | U ) (37) for som e p ( u, x ) , wh ere U is an aux iliary rando m variable. The proo f follows stand ard in formatio n-theor etic argumen t and is defer red to Appen dix B. Now , we can combin e all previous three steps an d o btain an upper bou nd on the weigh ted sum rate ( β 1 + β 2 ) R † 0 + λ 1 R † 1 + λ 2 R † 2 . By assumption, ( R † 0 , R † 1 , R † 2 ) is an achiev a ble rate triple for ch annel (18). Then, following Lemma 3 we have ( β 1 + β 2 ) R † 0 + λ 1 R † 1 + λ 2 R † 2 ≤ β 1 2 log | 2 π e ( S + N 1 ) | + β 2 2 log | 2 π e ( S + N 2 ) | + λ 1 2 log N 2 e N + λ 2 2 log N 1 e N + η ( λ 1 , λ 2 ) (38) where η ( λ 1 , λ 2 ) := λ 1 h ( X + e Z 1 a | U ) + λ 2 h ( X + e Z 2 a | U ) − ( λ 2 + β 1 ) h ( X + Z 1 b | U ) − ( λ 1 + β 2 ) h ( X + Z 2 b | U ) . Note that 0 ≺ e N { N 1 , N 2 } , 0 ≺ B ⋆ 0 S , an d B ⋆ 0 M 0 = 0 . By [ 21, Corollar y 4] and (35), we have η ( λ 1 , λ 2 ) ≤ ( λ 1 + λ 2 ) log 2 π e ( S − B ⋆ 0 ) + e N − ( λ 2 + β 1 ) log | 2 π e ( S − B ⋆ 0 ) + N 1 | − ( λ 1 + β 2 ) log | 2 π e ( S − B ⋆ 0 ) + N 2 | . (39) Combining ( 38) and (39), we h av e ( β 1 + β 2 ) R † 0 + λ 1 R † 1 + λ 2 R † 2 ≤ β 1 2 log S + N 1 ( S − B ⋆ 0 ) + N 1 + β 2 2 log S + N 2 ( S − B ⋆ 0 ) + N 2 + λ 1 1 2 log ( S − B ⋆ 0 ) + e N e N − 1 2 log ( S − B ⋆ 0 ) + N 2 N 2 ! + λ 2 1 2 log ( S − B ⋆ 0 ) + e N e N − 1 2 log ( S − B ⋆ 0 ) + N 1 N 1 ! which is a contr adiction to ( 36) as ρ > 0 . W e thus con clude that the r ate region (19) over all po ssible B 0 0 , B 1 0 an d B 0 + B 1 S is indee d the capacity r egion of the cano nical MIMO Gaussian b roadcast chann el (1 8). This com pletes the proof o f Theo rem 2. Remark 4: Note that in the enhan ced chan nel (32), both legitimate r eceiv ers 1 a a nd 2 a hav e th e same noise covariance matrices. This fact gre atly simplified the capac ity analy sis o f the enhan ced channel and is key to the succe ss of the pr oposed channel en hanceme nt ap proach . W e m ention her e that the same technique was also used in [24] to derive the sum-priv ate- v .s. -common message cap acity region of th e M IMO Gaussian broadc ast channel. I V . C O N C L U D I N G R E M A R K S In this paper we hav e p resented two new results on MIMO Gaussian b roadcast channels with confiden tial messages, lead- ing to a more comprehensive understan ding of the fundamental limits of MIMO secret c ommun ication. First, a m atrix ch aracterization of th e capa city-equivocation region of the MI MO Gaussian wir etap channe l h as been obtained, generalizin g th e previous r esults [3]–[7] wh ich dealt only with the secrecy capacity o f the chan nel. T he result has been obtained via an in teresting con nection between the rate-equivocation setting an d simultane ous private-confidential commun ication over a discrete memo ryless wiretap chann el, which allows a matrix char acterization of the entire cap acity- equiv ocation region based on the existing character ization of secrecy capacity f or the MIM O Gaussian w iretap ch annel. Next, the problem of MIMO Gaussian wiretap chan nels with two receivers an d three indepen dent messages, a common mes- sage intended for both receivers, and two mutually confidential messages eac h intend ed for o ne o f the recei vers but needing to be kept asymptotica lly pe rfect secure from the oth er , h as been considered . A precise cha racterization of the capacity region has been obtained via a channel-en hanceme nt argument, which is a n atural extension of the ch annel-en hancem ent arguments of [9] and [24]. A P P E N D I X A P R O O F O F L E M M A 1 W e first p rove the ach iev a bility part o f th e lemma by co n- sidering a cod ing scheme th at combine s superposition coding, random binning, and rate splitting. Fix p ( u ) p ( v | u ) p ( x | v ) . Split the pri vate message W p into two indep endent s ubmessages W ′ p and W ′′ p . Codeboo k generation. Fix δ > 0 . Rand omly and inde pen- dently gener ate 2 n ( R ′ p + δ ) codewords of length n ac cording to p n U . Label each of the cod ew ords as u n j , where j is the codeword numb er . W e will refer to the co deword collection { u n j } j as the U - codebo ok. For each codeword u n j in the U -cod ebook , r andomly and indepen dently gene rate 2 n ( R s + R ′′ p + T ) codewords o f length n accordin g to Q n i =1 p V | U = u j [ i ] . Randomly partition the code- words into 2 nR s bins so th at each bin contains 2 n ( R ′′ p + T ) codewords. Furth er partition each bin into 2 nR ′′ p sub-bins so that each sub-b in contain s 2 nT codewords. La bel each of the codewords as v n j,k,l,t where k den otes the bin nu mber, l den otes th e sub -bin n umber within each bin, and t d enotes the codeword num ber w ithin each sub-b in. W e will re fer to the codeword collection { v n j,k,l,t } k,l,t as the V -sub codebo ok correspo nding to u n j . Fig. 5 illustra tes the overall code book structure. Encodin g. T o send a message tr iple ( w s , w ′ p , w ′′ p ) , the trans- mitter first cho oses th e c odeword u n w ′ p from the U -codebook . Next, the transmitter looks into the V -su bcodeb ook co rre- sponding to u n w ′ p and randomly (ac cording to a unifor m distri- bution) chooses a code word v n w ′ p ,w s ,w ′′ p ,t from the w ′′ p th sub-b in of the w s th bin. Once a v n w ′ p ,w s ,w ′′ p ,t is chosen , an in put se- quence x n is genera ted ac cording to Q n i =1 p X | V = v w ′ p ,w s ,w ′′ p ,t [ i ] and is then sent throug h the cha nnel. 9 . . . . . . bin 1 sub-bin 1 sub-bin 2 sub-bin 2 . . . sub-bin 1 sub-bin 2 nR ′′ p bin 2 nR s sub-bin 2 nR ′′ p . . . . . . V -subcodeboo k U-codebook codeword 2 nR ′ p codeword j codeword 2 codeword 1 Fig. 5. Codebook structure. Decoding a t r eceiver 1. Giv en y n 1 , recei ver 1 looks in to the codebo oks U and V an d search es for a pair of cod ew ords ( u n j , v n j,k,l,t ) that ar e jointly typical with y n 1 . In the case when R ′ p < I ( U ; Y ) (40) and R s + R ′′ p + T < I ( V ; Y | U ) (41) with high pro bability the transmitted codeword pair ( u n w ′ p , v n w ′ p ,w s ,w ′′ p ,t ) is the only on e that is jointly typical with y n 1 . Security at receiver s 2 and 3. Fix ǫ > 0 . In the case wh en R ′′ p + T > I ( V ; Z | U ) (42) we h av e [17, Theorem 1 ] 1 n I ( W s ; Z n | W ′ p ) ≤ ǫ (43) for sufficiently large n . Since W s and W ′ p are in depend ent, we h av e from (43) that 1 n I ( W s ; Z n ) ≤ 1 n I ( W s ; Z n , W ′ p ) = 1 n I ( W s ; Z n | W ′ p ) ≤ ǫ i.e., the message W s is asymp totically perf ectly secure at the eav esdropp er . T o sum marize, fo r any given p ( u ) p ( v | u ) p ( x | v ) an d any T ≥ 0 , any rate triple ( R s , R ′ p , R ′′ p ) th at satisfies (4 0)–(42) is achievable. Note that R p = R ′ p + R ′′ p . (44) Eliminating T , R ′ 2 and R ′′ 2 from ( 40)–(42) an d (44) using Fourier-Motzkin eliminatio n, we ma y con clude that any rate pair ( R s , R p ) satisfying ( 12) is achiev able. T o prove th e con verse part of the lemm a, we first consider an upper b ound o n the confidential me ssage r ate R s . The perfe ct secrecy condition ( 11) im plies that for every ǫ > 0 , H ( W s | Z n ) ≥ H ( W s ) − nǫ. (45) On the other hand , Fano’ s ine quality [20, Ch. 2.11 ] implies that for every ǫ 0 > 0 , H ( W s , W p | Y n ) ≤ ǫ 0 log h 2 n ( R s + R p ) − 1 i + h ( ǫ 0 ) := nδ. (46) Applying (45) and (46), we h av e nR s = H ( W s ) ≤ H ( W s | Z n ) + nǫ + nδ − H ( W s , W p | Y n ) ≤ H ( W s , W p | Z n ) − H ( W s , W p | Y n ) + n ( ǫ + δ ) . (47) By th e chain rule o f the mu tual info rmation [20, Ch. 2 .5], n ( R s − ǫ − δ ) ≤ I ( W s , W p ; Y n ) − I ( W s , W p ; Z n ) = n X i =1 I ( W s , W p ; Y i | Y i − 1 ) − I ( W s , W p ; Z i | Z n i +1 ) = n X i =1 I ( W s , W p ; Y i | Y i − 1 , Z n i +1 ) − I ( W s , W p ; Z i | Y i − 1 , Z n i +1 ) (48) where th e last equ ality follows from [ 17, Lemm a 7]. Let U i := Y i − 1 , Z n i +1 and V i := ( W s , W p , U i ) (49) and we have from (4 8) that n ( R s − ǫ − δ ) ≤ n X i =1 [ I ( V i ; Y i | U i ) − I ( V i ; Z i | U i )] . (50) Next, we con sider an up per bo und o n the sum priv ate- confidential me ssage rate R s + R p . By (4 6), n ( R s + R p ) = H ( W s , W p ) ≤ I ( W s , W p ; Y n ) − nδ. (51) Applying the chain rule of the mutual inform ation [20, Ch. 2.5 ], we have n ( R s + R p − δ ) ≤ n X i =1 I ( W s , W p ; Y i | Y i − 1 ) ≤ n X i =1 I ( W s , W p , Y i − 1 , Z n i +1 ; Y i ) = n X i =1 I ( V i ; Y i ) . (52) Applying the standar d single-letterization procedu re (e.g ., see [20, Ch. 1 4.3]) to ( 50) and (52), we have the desired co n verse result for Lemma 1. 10 A P P E N D I X B P R O O F O F L E M M A 3 The perfect secrecy condition ( 28) implies that for every ǫ > 0 , H ( W 1 | Y n 2 b ) ≥ H ( W 1 ) − nǫ (53a) and H ( W 2 | Y n 1 b ) ≥ H ( W 2 ) − nǫ . (53b) On the o ther hand, Fano’ s inequality [ 20, Chapter 2.11] implies that for every ǫ 0 > 0 , max[ H ( W 0 | Y n 1 b ) , H ( W 0 | Y n 2 b )] ≤ ǫ 0 log 2 nR 0 − 1 + h ( ǫ 0 ) := nδ 0 (54a) H ( W 1 | e Y n 1 a ) ≤ ǫ 0 log 2 nR 1 − 1 + h ( ǫ 0 ) := nδ 1 (54b) and H ( W 2 | e Y n 2 a ) ≤ ǫ 0 log 2 nR 2 − 1 + h ( ǫ 0 ) := nδ 2 . (54c) Let U i := ( W 0 , Y i − 1 1 b , Y n 2 b,i +1 ) (55) which satisfies the Markov chain U i → X i → ( e Y 1 a , e Y 2 a , Y 1 b , Y 2 b ) . (56) W e first boun d R 0 based o n (54 a) as f ollows: nR 0 = H ( W 0 ) ≤ I ( W 0 ; Y n 1 b ) + nδ 0 = n X i =1 I ( W 0 ; Y 1 b,i | Y i − 1 1 b ) + nδ 0 ≤ n X i =1 I ( W 0 , Y i − 1 1 b , Y n 2 b,i +1 ; Y 1 b,i ) + nδ 0 = n X i =1 I ( U i ; Y 1 b,i ) + nδ 0 . (57) Similarly , we have nR 0 ≤ I ( W 0 ; Y n 2 b ) + nδ 0 = n X i =1 I ( W 0 ; Y 2 b,i | Y n 2 b,i +1 ) + nδ 0 ≤ n X i =1 I ( W 0 , Y i − 1 1 b , Y n 2 b,i +1 ; Y 2 b,i ) + nδ 0 = n X i =1 I ( U i ; Y 2 b,i ) + nδ 0 . (58) Next, we boun d R 1 based o n (53 a) and (54b) as follows: nR 1 = H ( W 1 ) ≤ H ( W 1 | Y n 2 b ) + nǫ + nδ 1 − H ( W 1 | e Y n 1 a ) = H ( W 1 | W 0 , Y n 2 b ) + I ( W 1 ; W 0 | Y n 2 b ) − H ( W 1 | e Y n 1 a ) + n ( ǫ + δ 1 ) ≤ H ( W 1 | W 0 , Y n 2 b ) + H ( W 0 | Y n 2 b ) − H ( W 1 | W 0 , e Y n 1 a ) + n ( ǫ + δ 1 ) . (59) Substituting (5 4b) into (59), we may obtain nR 1 ≤ H ( W 1 | W 0 , Y n 2 b ) − H ( W 1 | W 0 , e Y n 1 a ) + n ( ǫ + δ 0 + δ 1 ) = I ( W 1 ; e Y n 1 a | W 0 ) − I ( W 1 ; Y n 2 b | W 0 ) + n ( ǫ + δ 0 + δ 1 ) . (60) Applying [17, Lemm a 7], (60) can be rewritten as nR 1 ≤ n X i =1 I ( W 1 ; e Y 1 a,i | W 0 , e Y i − 1 1 a , Y n 2 b,i +1 ) − I ( W 1 ; Y 2 b,i | W 0 , e Y i − 1 1 a , Y n 2 b,i +1 ) + n ( ǫ + δ 0 + δ 1 ) ≤ n X i =1 I ( X i ; e Y 1 a,i | W 0 , e Y i − 1 1 a , Y n 2 b,i +1 ) − I ( X i ; Y 2 b,i | W 0 , e Y i − 1 1 a , Y n 2 b,i +1 ) + n ( ǫ + δ 0 + δ 1 ) (61) where ( 61) follows from the Ma rkov chain W 1 → X i → e Y 1 a,i → Y 2 b,i . Moreover , due to the Mar kov chain ( W 0 , e Y 1 a,i , Y n 2 b,i +1 ) → e Y i − 1 1 a → Y i − 1 1 b (62) we ca n fur ther bou nd R 1 as nR 1 ≤ n X i =1 I ( X i ; e Y 1 a,i | W 0 , e Y i − 1 1 a , Y i − 1 1 b , Y n 2 b,i +1 ) − I ( X i ; Y 2 b,i | W 0 , e Y i − 1 1 a , Y i − 1 1 b , Y n 2 b,i +1 ) + n ( ǫ + δ 0 + δ 1 ) = n X i =1 I ( X i ; e Y 1 a,i | U i , e Y i − 1 1 a ) − I ( X i ; Y 2 b,i | U i , e Y i − 1 1 a ) + n ( ǫ + δ 0 + δ 1 ) (63) = n X i =1 I ( X i ; e Y 1 a,i | U i ) − I ( X i ; Y 2 b,i | U i ) − I ( e Y i − 1 1 a ; e Y 1 a,i | U i ) − I ( e Y i − 1 1 a ; Y 2 b,i | U i ) + n ( ǫ + δ 0 + δ 1 ) ≤ n X i =1 I ( X i ; e Y 1 a,i | U i ) − I ( X i ; Y 2 b,i | U i ) + n ( ǫ + δ 0 + δ 1 ) (64) where ( 63) fo llows f rom the definition of U i in (5 5), an d (6 4) follows from th e fact that Y 2 b,i is d egraded with respect to e Y 1 a,i so I ( e Y i − 1 1 a ; Y 2 b,i | U i ) ≤ I ( e Y i − 1 1 a ; e Y 1 a,i | U i ) . Follo wing th e same steps as those in (59)–(64), we ma y obtain nR 2 ≤ n X i =1 I ( X i ; e Y 2 a,i | U i ) − I ( X i ; Y 1 b,i | U i ) + n ( ǫ + δ 0 + δ 2 ) . ( 65) Finally , applying the standard single-letter ization pro cedure (e.g., see [20, Chapter 14.3]) to (57), (58), (64) and (65) proves the desired result (37) for Le mma 3. 11 R E F E R E N C E S [1] Y . Liang, H. V . Poor , and S. Shamai (Shitz), Information Theoreti c Securit y . Dordrecht, The Nethe rlands: Now Publisher , 2009. [2] R. Liu and W . Trappe , Eds, Securing W ir eless Communic ations at the Physical Layer . New Y ork: Springe r V erlag, 2010. [3] A. Khisti and G. W . W ornell, “Secure transmission with multiple antenna s I: The MISOME wireta p channel , ” IEEE T rans. Inf. Theory , vol. 56, no. 7, pp. 3088–3104, July 2010. [4] A. Khisti and G. W . W ornell, “Secure transmission with multiple antenna s II: T he MIMOME wiret ap channel , ” IEEE T rans. Inf. Theory , vol. 56, No. 11, pp. 5515–5532, Nov . 2010. [5] F . Oggier and B. Hassibi, “The secrec y capacity of the MIMO wiret ap channe l, ” IE EE T rans. Inf . Theory , to appear . [6] T . Liu and S. Shamai (Shitz), “ A note on the s ecrec y capacity of the multiple -anten na wiretap channel, ” IEE E Tr ans. Inf. Theory , vol. 55, no. 6, pp. 2547–2553, June 2009. [7] R. Bustin, R. Liu, H. V . Poor, and S. Shamai (Shit z), “ An MMSE ap- proach to the s ecrec y capac ity of the MIMO Gaussian wiretap channel, ” EURASIP Journal on W ireless Communications and Networki ng , 2009. [8] R. L iu and H. V . Poor, “Secrec y capac ity region of a multi-ante nna Gaussian broadcast channel with confidenti al messages, ” IE EE T rans. Inf. Theory , vol. 55, no. 3, pp. 1235–1249, Mar . 2009. [9] R. L iu, T . Liu, H. V . Poor , and S. Shamai (Shitz), “Multiple -input multiple -output Gaussian broadcast channels with confidential mes- sages, ” IEEE T rans. Inf. Theory , vol. 56, no. 9, pp. 4215–4227, Sep. 2010. [10] H. D. L y , T . Liu, and Y . Liang, “Multi ple-inpu t multiple- output Gaussian broadca st channels with common and confidenti al messages, ” IEEE T rans. Inf . Theory , vol . 56, no. 11, pp. 5477–54 87, Nov . 2010. [11] R. Liu, T . Liu, H. V . Poor, and S. Shamai (Shitz), “MIMO Gaussian broadca st channe ls with confide ntial and common m essages, ” A va ilable online at http://arxi v .org/ abs/1001.28 06 [12] R. Liu, T . Liu, H. V . Poor , and S. Shamai (Shitz ), “The capacit y- equi vocation regi on of the MIMO Gaussian wiretap channel, ” in Proc. IEEE Int. Symp. Inf. Theory , Austin, T exas, June 2010. [13] R. Liu, T . Liu, H. V . Poor, and S. Shamai (Shitz), “MIMO Gaussian broadca st channel s with confidenti al and common messages, ” in Proc. IEEE Int. Symp. Inf. Theory , Austin, T exas, June 2010. [14] E. E krem and S. Ulukus, “Capacit y reg ion of Gaussian MIMO broadcast channe ls with common and confidential messages, ” IEEE T ran s. Inf. Theory , submitt ed Feb . 2010. [15] E. Ekrem and S. Ulukus, “Capa city-e qui voc ation regi on of the Gaussian MIMO wiretap channel, ” IEEE T rans. Inf. Theory , submitt ed May 2010. [16] A. D. W yner , “The wire-tap channel, ” Bell Sys. T ec h. J ournal , vol. 54, no. 8, pp. 1355–1387, Oct. 1975. [17] I. Csisz ´ ar and J. K ¨ orner , “Broadcast channel s with confidential mes- sages, ” IEE E T rans. Inf. Theory , vol. IT -24, no. 3, pp. 339–348, May 1978. [18] H. W eingarten, Y . Ste inber g, and S. Shamai (Shitz), “The ca pacit y region of the Gaussian multiple-in put multi ple-outp ut broadc ast channel, ” IEEE T rans. Inf . Theory , vol . 52, no. 9, pp. 3936–3964, Sep. 2006. [19] I. Csisz ´ ar and J. K ¨ orn er , Informati on Theory: Coding Theorems for Discr ete Memory less Systems . Budap est: Academic Press, 1982. [20] T . M. Cove r and J. A. Thomas, Elements of Informat ion Theory . Ne w Y ork: John W iley & Sons, Inc., 1991. [21] H. W eingarten, T . Liu, S. Shamai (Shitz), Y . Ste inber g, and P . V iswanat h, “The capaci ty reg ion of the degrade d multiple -input multipl e-output compound broadc ast channel, ” IEEE T rans. Inf . Theory , v ol. 55, no. 11, pp. 5011–5023, Nov . 2009. [22] J. Xu, Y . Cao, and B. Chen, “Capaci ty bounds for broadcast channel s with confidential messages, ” IEEE T rans. Inf . Theory , vol. 55, no. 10, pp. 4529–4542, Oct. 2009. [23] R. Liu, I. Maric, P . Spasoje vic, and R. D. Y ates, “Discrete memoryless interfe rence and broadcast cha nnels with confident ial messages: Secrecy rate re gions, ” IEEE T ran s. Inf . Theory , vol. 54, no. 6, pp. 2493–25 07, June 2008. [24] H. W eingarten, Multiple-Input Multiple-Ou tput Broadc ast Systems . Ph.D. Thesis, Dept. of Electric al Engineering, T echni on-Israel Institute of T echnolog y , 2008.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment