A new graph perspective on max-min fairness in Gaussian parallel channels
In this work we are concerned with the problem of achieving max-min fairness in Gaussian parallel channels with respect to a general performance function, including channel capacity or decoding reliability as special cases. As our central results, we…
Authors: Marcin Wiczanowski, Holger Boche
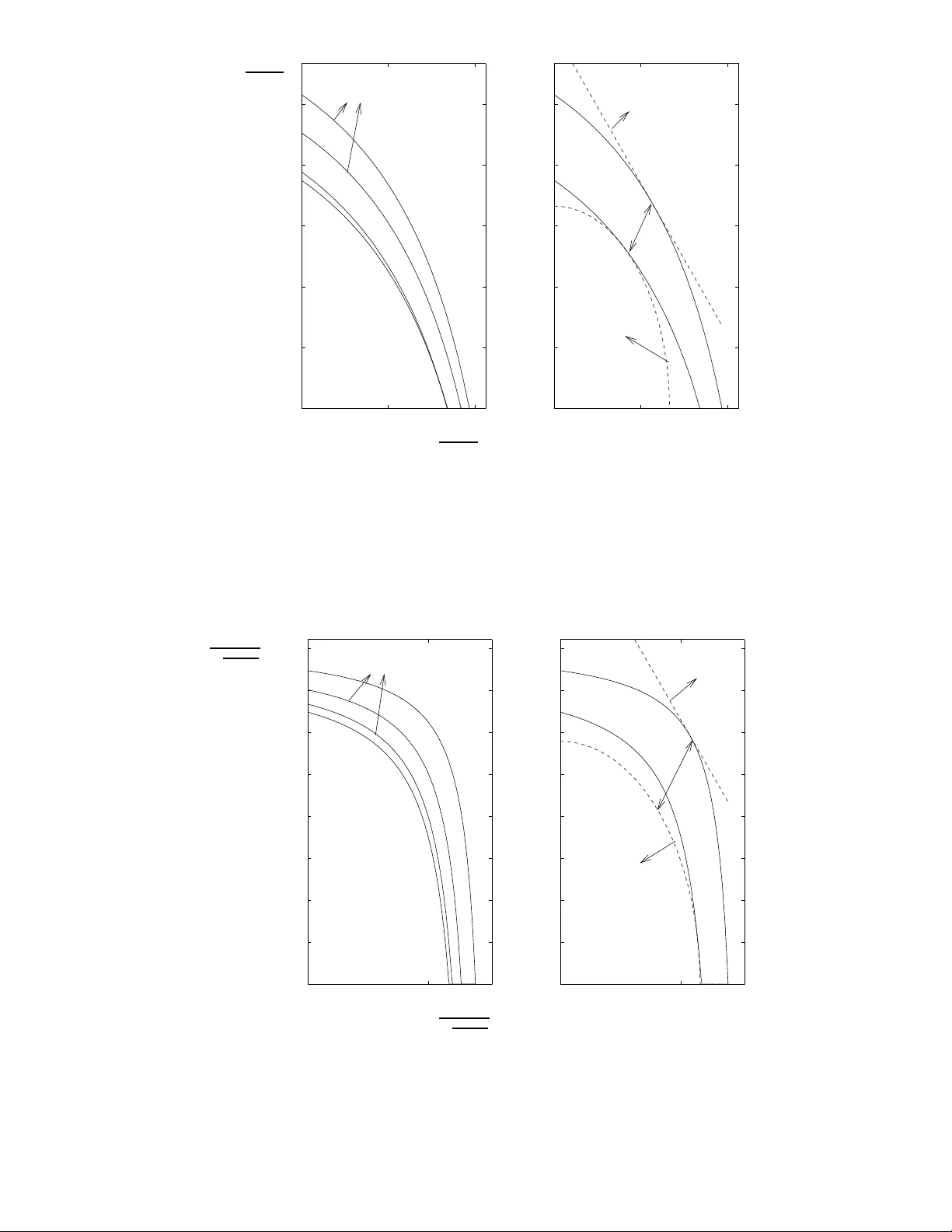
1 A ne w graph perspecti v e on max-min f airness in Gaussian para llel channels Marcin W iczanows ki † , Holger Boche ∗† ∗ Heinrich-Hertz Group for Mobile C ommunications, EECS, Berlin Uni versity of T echnology , Einsteinufer 25, 10587 B erlin, Germany † Fraunhofer German-Sino Lab for Mobile C ommunications (MCI) Einsteinufer 37, 10587 Ber lin, German y Email: { marcin.wi czanowski ,boche } @hhi.fraunhofer.de Phone: +4930-314-28462, Fax: +4930-314-28320 Submitted to IEEE T ransactions on Information Theory , August the 6th, 2008 Abstract In this work we are concern ed with the proble m of achieving ma x-min fairn ess in Gau ssian parallel channels with respect to a g eneral perfo rmance function, inc luding chann el capacity or decodin g reliability as special cases. As our central results, we characterize the la ws which determine the v alue of the achiev able max -min fair performa nce as a f unction of chan nel shar ing policy and power allocation (to ch annels a nd users). In particular, we show that the max-m in fair perf ormance behaves as a sp ecialized version of the Lovasz function, or Delsarte bo und, of a certain gra ph induced b y chan nel sharing com binatorics. W e also prove that, in ad dition to such grap h, merely a certain 2 -norm distan ce depend ent o n the allowable power allocation s a nd used p erforman ce function s, is sufficient for the ch aracterization of max-min fair perform ance u p t o some candidate interval. Our results show also a spe cific role playe d b y odd cycles in the gr aph induced by the channel shar ing policy and we presen t a n intere sting relation betwe en max-m in fairness in para llel channels and optimal thro ughpu t in an associated interf erence c hannel. Index T erms Lovasz fu nction, Delsarte bo und, pa rallel channels, max-m in fairness, grap hs I . I N T R O D U C T I O N Fairness r epresents an important goal in the design of po wer , bandwidth and time a llocation policies for multi-us er channels. It is usu ally desired to achiev e fairness with respect to com- munications and information theory met rics, such as spectral ef ficiency , decoder reliabi lity , etc. [1], [2]. The m ostly used notion of fairness is the max-min fairness, which is an ins tance of equity in terms of economy m arkets and consi sts in the m aximal possi ble im prove ment of the worst performance metric [3] [4], [5]. The singl e-user communi cation ov er parallel channel s is a well-studied topi c both from t he viewpoint of information theoretic optimality as well as s uboptimal practical power a llocation approaches, see e.g. [6], [7], [8], [9], [10] and references therein. Howe ver , the max-min fair allocation of power , bandwidth and tim e to multipl e users sharing the parallel channels access still p oses practical problems and needs a deeper u nderstanding [1], [11]. The issue of max- min fairness in (multi -user) parallel channels has been addressed in [11], [12], [13], [14] and references therein. Concurrently , a cellular downlink or uplink using Orthogonal Frequency Division Multi plex (OFDM) appears to be the most relev ant example of parallel channels shared among multiple users. In [11], the m ax-min fair carrier and antenna assignm ent is studied for a multiple antenna OFDM downlink. More generally , in [ 12], [13] the performance 2 of max-min fa ir power allocation and max-min fair assignm ent of parallel channels is characterized withi n the framework of so -called blocking and antibl ocking po lyhedra [15], [16]. The characterization of user performance achieved und er max-min fairness is provided in [12], [13] in the form of bounds and dualit y-like o ptimization p roblems. Se veral impo rtant aspect of the fairness problem in parallel chann els, such as e.g. th e optimum interrelations b etween the combinatorics of channel s haring and t he real-v alued power all ocation, are still open in th e general case. Also the essential s traight quest ions such as ”what is the us er performance under max-min fairness in parallel channels equal to?” or ”what is the power/time/bandwidth function describing it?” remain unanswered so far . In this work we make a s tep t ow ards satisfying answers t o th e above questions in Gaussian parallel channels, when the interest is in max-mi n fairness with respect to user performance measured by a general performance/QoS functi on; this includes t he m ost celebrated cases of channel capacity , spectral effi ciency , decoder reliabi lity (unity mi nus decoder error rate), etc. W e state insig htful optimis tic and pess imistic bounds o n the user performance (Sections IV, V). The essence o f our results is that, under constrain ts on transmit power , the max- min fair performance b eha ves as a speciali zed version of the Lova sz function [17], [18 ] of a specific graph, wh ich is ind uced by the channel sharing t opology , or com binatorics. W e prove further that, in add ition to such g raph d escription, a certain 2 -no rm distance dependent on the allowable power allocations and users’ performance functions is sufficient for enclosin g the max-min fair performance by som e lower and upper bo unds. These bounds prove to be especially insightful as th ey o f fer a separation of influences of the channel sharing po licy and the real-valued problem of p owe r allocation. W e aid the int erpretations of the i ntroduced channel sharing topol ogies and the proposed bounds by severa l parallel channel examples and visualizations. Our results exhibit a specific rol e of odd cycles in the graph ind uced by the channel s haring policy . W e present also an interesti ng relation between max-min fairness in parallel channels and optimal throughput i n an associat ed interference channel. Furthermore, the presented bounds show a link between the user performance under max-min fairness and (zero-error) graph ca pacity [19], [ 17]. The proofs of our results are constructive and allo w for the design of sev eral n ovel power and tim e allocation algorithm s for parallel channels with predetermi ned channel sharing topology; this can be mot iv ated by regulations o n processing of traf fic classes or standardization/hardware constraints (Section VI). The proposed algorithms offe r a bett er performance-complexity trade off than con ventional solution m ethods and achiev e user performance withi n som e specified distance from the max-min fairness. I I . M O D E L A N D P R E L I M I NA R I E S W e consider t he set of Gaussian (in the sense of Addi tiv e-White-Gaussian-Noise) parallel channels, treated as one mul ti-user channel 1 . The transmi tter-r ecei ver pairs comm unicating with each other over this channel are referred to abs tractly as users and are grouped i n t he s et K = { 1 , . . . , K } . The parallel channels are assumed to be deterministic and frequency-flat. 1 Notation: T he nonne gati ve and positiv e orthants in R K × N , where we set R K × 1 = R K and C K × 1 = C K , are denoted as R K × N + and R K × N ++ , respecti vely . By S K we denote the set of symmetric matrices in R K × K and t he cones of doubly nonne gati ve matrices and completely positiv e matrices in R K × K are denoted as D K and P K , respecti vely (see Appendix A for the definitions). By S ǫ ( X ) we denote a ball with radius ǫ centered at X ∈ C K × N . By we denote the usual partial order on t he set of symmetric matrices and X ◦ Y , denotes the Kronecker product of X , Y ∈ C K × N . For any vector x = ( x 1 , . . . , x K ) ∈ C K we define ( x ) k = x k . Giv en a matrix X ∈ C K × N with elements x kl , 1 ≤ k ≤ K , 1 ≤ l ≤ N , we w rite simply X = ( x kl ) and define similarly ( X ) kl = x kl . By X ′ we denote t he conjugate t ranspose of X ∈ C K × N . Giv en X ∈ C K × K , diag ( X ) ∈ C K × K is such that ( di ag ( X )) kk = ( X ) kk and ( diag ( X )) kl = 0 , k 6 = l , 1 ≤ k , l ≤ K . Further , give n x = ( x 1 , . . . , x K ) ∈ R K + , a vector x 1 2 is defined as ( x 1 2 ) k = √ x k . The identity matrix is denoted by I , e k is t he unit vector such that ( e k ) k = 1 and ( e k ) l = 0 , k 6 = l , and we also define vector 1 as ( 1 ) k = 1 , where in all three cases the matrix/vector dimension follows from t he context. By h x , y i we denote the inner product of x , y ∈ C K . W ithout introducing ambiguity , we do not differ in the notation between random v alues and deterministic value s. The mean of a random matrix (variable) X ∈ C K × N is denoted as E ( X ) . 3 A. The parallel channels The set of parallel channels i s denoted as N = { 1 , . . . , N } . Let x k = ( x k 1 , . . . , x k N ) ∈ C N be a random vector grouping the independent (zero-mean) sym bols of user k ∈ K transmit ted over the channels n ∈ N equidi stantly , at distance T s . Then, the sampled s ignal of user k ∈ K recei ved over th e parallel channels can be written as y k = ( y k 1 , . . . , y k N ) , with y k n = h k n x k n + n k n , n ∈ N , where h k = ( h k 1 , . . . , h k N ) ∈ C N collects the path coef ficients between the transmi tter and recei ver of user k ∈ K on channels n ∈ N and n k = ( n k 1 , . . . , n k N ) ∈ C N is a random vector whi ch contain s (zero-mean, ind ependent o f x k ) Gaussi an noise variables perceiv ed at the receiver of user k ∈ K o n channels n ∈ N , where we assume σ 2 k n = E ( | n k n | 2 ) > 0 . Th e transmit power allocation t o u sers and channels (in short, power allocation ) can b e written as P = ( p 1 , . . . , p K ) ′ ∈ R K × N + , where vector p k = ( p k 1 , . . . , p k N ) is such that p k n = E ( | x k n | 2 ) is th e trans mit p owe r allocated to user k ∈ K on channel n ∈ N . Let A = ( a 1 , . . . , a K ) ′ ∈ R K × N + denote the s haring matri x of the channels among u sers such that a k = ( a k 1 , . . . , a k N ) collects th e relative fractions of time which are assigned to user k ∈ K for t he exclusiv e access to channels n ∈ N . T hus, as in practice the operation time i s partitioned into frames of some fixed duration T ≫ T s , the coll ection of times T a k is reserved for user k ∈ K for t he exclusive access to the respecti ve channels n ∈ N wi thin each frame. The set of all owe d sharing matrices o f t he p arallel channels takes the form A ( r ) = { A ∈ R K × N + : k a k k 1 ≤ r k , k ∈ K , ( X k ∈K a k n ) ≤ 1 , n ∈ N } , r ∈ R K ++ . (1) According to the first constraint in (1), a predefined vector r = ( r 1 , . . . , r K ) ∈ R K ++ , with k r k 1 ≤ N , is such t hat r k / N represents the fraction of the set of parallel channels which is assign ed to user k ∈ K over t ime (over each frame). It proves useful in the remainder to introduce als o R ∈ R K × K + such that ( R ) k l = 0 , k 6 = l , and ( R ) k k = r k , k , l ∈ K . For instance, under r = N K 1 any user is assign ed an equal 1 /K -fraction of the ensemble of parallel channels over ti me (over each frame). The second inequal ity in the definition (1) models then th e o bvious const raint t hat the aggregate ti me of exclusi ve uses of a s ingle channel n ∈ N by the users k ∈ K do es not exceed the total operation time (the tot al duration o f each frame). Currently , the mo st celebrated i nstance of the considered parallel channels is t he multi-t one/multi-carrier channel accessed b y multi ple users, as considered e.g. in [20], [21]. In this case, a k groups us er’ s k ∈ K relative times of exclusiv e uses of carriers n ∈ N and r k / N represents t he fraction of the multi-carrier spectrum wh ich he is assigned over tim e [22]. Giv en a sharing matrix A ∈ A ( G, r ) under use, we assume an arbitrary set P ( A ) of allowed power allocatio ns, requirin g merely that P ( A ) ⊇ ( S ǫ ( 0 ) ∩ R K × N + ) , for some ǫ > 0 , ǫ = ǫ ( A ) , (2) Such condit ion means, broadly , that all power al locations whi ch are sufficiently small for the used sharing matrix are allowable. In particular , assuming frames of duration T , we can take either of the sets P ( A ) = { P ∈ R K × N + : X k ∈K T h a k , p k i ≤ E } , A ∈ A ( r ) , (3a) P ( A ) = { P ∈ R K × N + : T h a k , p k i ≤ E k , k ∈ K} , A ∈ A ( r ) , (3b) for some E , E k > 0 , k ∈ K , which m irror the limitat ions of ener gy per frame as a crucial constraint in current and fut ure wireless communicati on syst ems [23], [24]. The latter s et corresponds to con ventional lim itations of energy per frame in a mult i-user Gaussian channel with user ener gy per frame budgets constrained by E k , k ∈ K . The first set m odels the 4 possibili ty of energy coordinatio n among all users und er the join t ener g y per frame budget constrained by E . Thi s is th e case, for ins tance, when the considered parallel channels are a means of representation of t he orthogon alized broadcast channel which appl ies, suboptim ally , single-user precoding instead of m ulti-user precoding [25], [26] (for the combination of parallel channels and the broadcast channel see also [27]). Complementarily to frame ener gy constraints it is sometimes desired to account for transmit power cons traints at an y tim e in a frame. In analogy to (3), under lim itation of transmit power of any user k ∈ K by P k > 0 and under the joint transmit power budget of all users constrained by P > 0 we take, respectively , P ( A ) = P = { P ∈ R K × N + : | || P | || 1 ≤ P } , (4a) P ( A ) = P = { P ∈ R K × N + : k p k k 1 ≤ P k , k ∈ K } . (4b) It is interesti ng t o not e that transmit power constraints at any ti me within a frame make the set of allow able power allo cations independent of sharing matrix A ∈ A ( r ) under use, which will be of ke y impo rtance at sev eral points in th e remaind er . B. The user performance For any u ser k ∈ K accessing th e parallel channels , we assu me a g eneral vector -v alued performance/ QoS functi on p 7→ f k ( p ) ∈ R N , p ∈ R N + , where we h a ve f k ( p ) = ( f k 1 ( p 1 ) , . . . , f k N ( p N )) , with p 7→ f k n ( p ) , p ≥ 0 , n ∈ N . Function f k n expresses the performance of user k ∈ K on channel n ∈ N , as a functi on of power allocated to channel n ∈ N , when the user accesses t his channel exclusi vely throughout the operation t ime. W e restrict us t o nonnegati ve QoS functions f k ( p ) ∈ R N + , p ∈ R N + , k ∈ K , (5) and to av oid later technical qu eerness we assume th at ∂ ∂ p k f k ( p ) > 0 , k ∈ K , for p ∈ S ǫ ( 0 ) ∩ R K + and some ǫ > 0 (that is, p erformance fun ctions are compon entwise Frechet- diffe rentiable and increasing at least for sufficiently small p ower allocatio ns). Due t o (5) and the assumed independent s ymbols of a user on each one of the parallel channels, it is reasonable to consid er ( a , p ) 7→ h a , f k ( p ) i , ( a , p ) ∈ R N + × R N + , k a k 1 ≤ r k , as the performance/Qo S metric of user k ∈ K . Such m etric represents the aggregate perfor - mance achi e ved by user k ∈ K on the entire channel ensemble, through out the operatio n tim e (throughout each frame), as a functio n of powe rs allocated to channels n ∈ N and relativ e time fractions o f exclusi ve channel uses. W e refer to a value of the performance metric of a user , for some A ∈ A ( r ) and P ∈ P ( A ) , as user performa nce under policy ( A , P ) . Let any predefined requirement/expectation of user k ∈ K with respect to the user per- formance be denoted as γ k > 0 , k ∈ K . Then, min k ∈K h a k ,f k ( p k ) i γ k can be seen as the worst relative performance am ong the users accessing the parallel channels und er a poli cy ( A , P ) ∈ A ( r ) × P ( A ) . H ereby , we impli citly assume that a smaller user performance implies a worse perceiv ed service quality at the correspon ding recei ver . Such assumpti on complies with t he nature of the very mo st QoS functions used in communications and information th eory , but does not necessarily require strict componentwise increasingness of f k , k ∈ K . W e give a few celebrated examples of such performance functions. 5 Example 1 (Symbol decoding re liabilit y): Let user k ∈ K access channel n ∈ N and use uncoded constant-en velope modulation. Then, the achie ved probability of error -free symbol decoding i s f k n ( p ) = 1 − Q ( s c log 2 M p | h k n | 2 σ 2 k n ) , (6) with Q denoting the Marcum Q -function, M denotin g the const ellation size, and c > 0 as some const ant (e.g., c = 2 for b inary Phase Shift Ke yi ng or c = 1 for binary Frequency Shift Ke y ing) [28 ]. By (6) and the uniform symbol distance T s , the map ( a k , p k ) 7→ T T s h a k , f k ( p k ) i , ( A , P ) ∈ A ( r ) × P ( A ) , expresses the aggregate (over chann els n ∈ N ) av erage number o f error -free decoded sym bols of user k ∈ K in a frame as a funct ion of policy . Example 2 (Mean squar e detection r eliabil ity): If t he recei ver of user k ∈ K utilizes the Minimum Mean Square Error (MSE) recei ver and the user accesses channel n ∈ N , then the achie ved MSE can be expressed as 1 1+ p kn | h kn | 2 σ 2 kn [29]. As a consequence, f k n ( p ) = 1 − 1 1 + p | h kn | 2 σ 2 kn , (7) can be regarded as a kind of sym bol detecti on reliabili ty in t he m ean squ are sense. Thus, giv en (7), ( a k , p k ) 7→ T T s h a k , f k ( p k ) i , ( A , P ) ∈ A ( r ) × P ( A ) , describes the mean square detection reliability of user k ∈ K , aggregated over all sym bols receiv ed in a frame, as a function of poli cy . Example 3 (Spectral efficiency): Let the mod ulation constellation si ze of user k ∈ K which accesses channel n ∈ N be constrained b y M . The spectral effi ciency , in the sense of maxi mum nu mber of reliably decodable bits/nats per symbols under given modul ation constellation 3 , is not expressible analytically b ut can be approximated b y a function f k n ( p ) = g ( p | h k n | 2 σ 2 k n ) such that th e map x 7→ g ( x ) , x ≥ 0 , i s nondecreasing, and g (0) = 0 and g ( x ) = log 2 M , x ≥ x 0 , for some x 0 = x 0 ( M ) [8]. Then, it is easily seen that map ( a k , p k ) 7→ T T s h a k , f k ( p k ) i , ( A , P ) ∈ A ( r ) × P ( A ) , describes the achiev able number of reliably d ecoded bi ts/nats in a frame, as a function of pol icy . Example 4 (Capacity): If us er k ∈ K utilizes the Maximum Li kelihood (ML) recei ver , then f k n ( p ) = log (1 + p | h k n | 2 σ 2 k n ) (8) represents t he (information) capacity 3 , achiev able by user k ∈ K when accessing the channel n ∈ N , that is, the ove rall maximum number of reliably decodable bits/nats per symbol. Thus, giv en (8), the function ( a k , p k ) 7→ T T s h a k , f k ( p k ) i , ( A , P ) ∈ A ( r ) × P ( A ) , corresponds to the achie v able (under Gaussian codebook) num ber of reliably decoded bits /nats per frame. W ith the give n assumption s o n user performance, the m aximum attainable performance of the worst-case user accessing the parallel channels among po licies from A ( r ) × P can be expressed as max ( A , P ) ∈A ( r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i γ k . (9) According to the common understanding of fairness in various multi-user channels, see e.g. [1], [2], [11], [14], we refer to (9) as the max-mi n fair performance (in /of the considered par- allel channels), and we say that a pair ( A , P ) = arg ma x ( A , P ) ∈A ( r ) ×P ( A ) min k ∈K h a k ,f k ( p k ) i γ k , is a m ax-min fair pol icy , which is, in general, not unique. 3 Obviou sly , the notions of spectral efficiency and capacity are meaningful only when t he duration of the considered channel access is sufficiently long, in the sense T a kn ≫ T s . 6 I I I . G R A P H O F PA R A L L E L C H A N N E L S S H A R I N G For any sharing m atrix A ∈ A ( r ) we d efine an undirected graph of parallel channels sharing, in short a shar ing graph , which is induced by A . For the definition, recall that any graph is a pair , say G = ( K , E ) , where K i s the set of graph vertices, and E is the set of edges; any edge is represented by a pair ( k , l ) ∈ E such that k , l ∈ K are the vertices which are joined/connected by this edg e (are adjacent) [30]. Definition 1: F or N ≥ K a nd a ny A ∈ A ( r ) , a corr espond ing shari ng graph G = G ( A ) is su ch that G = ( K , E ) wher e ( k , l ) ∈ E , k 6 = l , if h a k , a l i > 0 . The prop osed i nduction of a sharing g raph G by A i s a version of orthogonal graph labeling from [31], whi ch further diffe rs slightl y from the original concept of ort honormal r epr esentation of a graph in [17]. Precisely , a (not nec essarily nonnegati ve) matrix A ∈ R K × N is referred to as an orthon ormal representation of g raph G = G ( A ) = ( K , E ) , which we wri te as A ∈ A 0 ( G ) , if h a k , a k i = 1 , k ∈ K , and ( k , l ) ∈ E , k 6 = l , wh ene ver h a k , a l i 6 = 0 . By Definition 1, any t wo vertices k , l ∈ K , k 6 = l , of the sharing graph are adjacent if som e of the parallel channels are shared by users k , l , where a channel is said to be shared by some two us ers if both users access this channel exclusi vely some fraction of time. The con verse is also clear: If t wo nodes k , l ∈ K , k 6 = l , of th e sharing graph are nonadjacent, then no one of the channels n ∈ N is shared by users k , l . It is readily seen that, for any fixed A ∈ A ( r ) , an induced sharing g raph G = G ( A ) i s in general not unique. Besides this, the graph characterization of parallel channels sharing provides merely the inform ation on th e topology , or combinatorics, of sharing relations hips. Thus, given any graph G = ( K , E ) , dif ferent sharing m atrices induce G as a sharing graph and we can group them in the set A ( G, r ) = { A ∈ A ( r ) : G = G ( A ) } , r ∈ R K ++ . The illustration is provided in the foll owing example. Example 5: Consider parallel channels as a m ulti-tone/m ulti-carrier channel wit h N = 7 tones accessed by K = 4 users in the proportions r = (2 , 2 , 1 , 2) . Let the sharing of the tones be described by t he sharing matrix A = 0 0 . 2 0 0 . 5 0 . 5 0 0 . 8 1 0 0 0 . 5 0 . 5 0 0 0 0 . 3 0 . 3 0 0 0 . 3 0 . 1 0 0 . 5 0 . 7 0 0 0 . 7 0 . 1 ∈ A ( 2 , 2 , 1 , 2) , Then, the three possible sharing graphs G = G ( A ) are depicted in Fig. 1, wit h the graph on t he right hand sid e as the sharing graph wi th the minimal num ber of edges. On the ot her hand, for G as the m inimum sharing graph from Fig. 1, the s et A ( G, (2 , 2 , 1 , 2)) of sharing matrices inducing it i ncludes, in particular , col umn permutations of all matri ces of the form A = 0 a 12 0 a 14 a 15 0 a 17 a 21 0 0 a 24 a 25 0 0 0 a 32 a 33 0 0 a 36 a 37 0 a 42 a 43 0 0 a 46 a 47 , with a ij > 0 , 1 ≤ i ≤ 4 , 1 ≤ j ≤ 7 . A special role in our consi derations of sharing g raphs is played by t he subgraphs called cycles . Definition 2 ([30], [32]): A cycle o f length M in a graph G = ( K , E ) is a sequence of distinct graph vertices k i ∈ K , 1 ≤ i ≤ M , which s atisfy ( k i , k i +1 ) ∈ E , 1 ≤ i ≤ M − 1 and ( k M , k 1 ) ∈ E . 7 4 4 4 1 3 1 3 3 1 2 2 2 G = ( K , E ) G = ( K , E ) G = ( K , E ) Fig. 1. Three sharing graphs of the multi-carrier channel with K = 4 users considered i n Example 5; such graphs are induced, in the sense G = G ( A ) , by the matri ces A from Example 5. G = ( K , E ) G = ( K , E ) Fig. 2. T wo exemplary sharing graphs of parallel channels with K = 7 and K = 12 users with marked exemplary cycles of length 3 (dotted edges), 4 (dash-dotted edges) and 5 (dashed edges). In simp le words, a cycle represents a sim ple closed path in a graph 2 . Note that t he length of a cycle is t he numb er of edges, or equiv al ently vertices, constit uting th e cycle. As an illustration , in Fig. 2 particular cycles are emphas ized in two exemplary sharing g raphs. A cycle o f a sharing graph has an easy interpretation in terms of sharing poli cies: A cycle of length, say , M corresponds to a chain/sequence of M users accessing t he p arallel channels such that any pair of subsequent users shares some channel and the last us er shares a channel with t he first user . In Fig. 3 we show examples of M -partite sharing graphs fo r M = 2 , 3 , 4 . As can b e seen from the figure, such graphs contain o nly edges between some disjoint vertex sub sets: The verte x set of an M -partite graph G = ( K , E ) is d ivided int o partiti ons K i , 1 ≤ i ≤ M , such that ( k , l ) / ∈ E whenev er k , l ∈ K i , 1 ≤ i ≤ M . It is easily deduced that an M -parti te g raph can not contain any cycle longer than M . An M -partite sharing graph i s induced by sharing policies of parallel channels whi ch dis tinguish M classes of us ers with the prop erty that users within one class are not allowed, or not able, to share any channels over time. Such constraint is likely t o be im posed by traffic processing regulations and/or the impl ementation 2 In the context of undirected graphs, some works prefer the notion of a circuit to the notion of a cycle used here. In such a con vention, the cycle is understood as the analog to the circuit in directed graphs. 8 G = ( K , E ) G = ( K , E ) G = ( K , E ) K 1 K 1 K 4 2 1 3 5 4 K 2 K 2 K 3 4 5 3 1 2 7 6 K 2 K 3 K 1 Fig. 3. Three ex emplary M -partite sharing graphs of parallel channels with K = 5 , 7 , 12 users and for M = 2 , 3 , 4 , respecti vely . The graph on the l eft-hand side i s a sharing graph of the multi-carrier channel from Example 6 and is induced (in t he sense G = G ( A ) ) in particular by the matrix A from E xample 6. The graph in the mi ddle can be a sharing graph of the multi-carrier channel considered in E xample 7. ef fort, as is illustrated b y the following examples. Example 6: Consider parallel channels as a mul ti-carrier channel w ith N = 9 carriers and K = 5 users accessing the carrier set in t he proportions r = (2 , 2 , 0 . 5 , 1 . 5 , 3) and having a common transmitt er . Let the traffi c of users 1 , 2 ∈ K 1 be the real-tim e traf fic, like v oice or multimedi a, while us ers 3 , 4 , 5 ∈ K 2 transmit and receiv e so-called background traffic, such as file transfer , signaling or system informatio n. From the viewpoint of percepted QoS and traf fic processin g complexity , it may be required to assign a carrier t o real-time traf fic for a large relativ e t ime fraction, say , no less than h alf of the to tal time, so that no carrier can be shared by two real-time users. Due to the processing effort, it may b e also undesired to share a carrier between mul tiple users carrying the minor background traffi c. These conditions enforce that the single carriers are either user-specific or carry mostly the real-time traffic of users K 1 with some add-on background traffic of users K 2 from time to t ime. Th us, an exe mplary s haring matri x can take the form A = 0 0 . 75 0 . 8 0 . 7 0 0 0 0 . 75 0 0 . 6 0 0 0 0 . 6 0 0 0 0 . 8 0 0 0 0 0 0 0 0 . 25 0 0 0 . 25 0 0 0 1 0 0 0 0 . 4 0 0 . 2 0 . 3 0 . 4 0 1 0 0 . 2 ∈ A ( 3 , 2 , 0 . 25 , 1 . 25 , 2 . 5 ) , which induces the bipartite sharing graph G = G ( A ) on the left hand side of Fig. 3. Example 7: Let a mult i-carrier channel with N = 1 3 carriers accessed by K = 7 users in the proportions r = ( 3 , 2 , 2 , 1 , 1 , 3 , 1) be the considered parallel chann els with a com mon recei ver . Let the users be grouped in classes 1 , 2 ∈ K 1 , 3 , 4 , 5 ∈ K 2 and 6 , 7 ∈ K 3 such that for any two users within one class the diff erence between their propagation times is larger than some critical propagation time dif ference (note that such classification is not alw ays possible). Then, the sharing of a carrier between t wo u sers from one class can be undesired d ue to the required effort of t ime- and frequency syn chronization to com e up with t he propagation ti me diffe rence. This impli es t hat the carriers are either user-specifi c or shared only across the classes K 1 , K 2 , K 3 , and that a particular sharing m atrix A ∈ A (3 , 2 , 2 , 1 , 1 , 3 , 1) can induce the 3 -partite sharing graph G = G ( A ) in the middl e of Fig. 3. 9 As shown i n the remain der , the description o f t he channel sharing topo logy by a sharing graph plays a key rol e i n the problem of ensuring max-mi n fairness (9). A. Selected algebraic graph characterizations W e make use of th e description of a graph by it s so-called f easible matr ix , wh ich is a symmetric matrix i ndicating an edge by a no nzero entry [33], [34], [35], [36 ]: Th e set of feasible matrices of a graph G = ( K , E ) is C ( G ) = { C = ( c k l ) ∈ S K : c k l 6 = 0 , k 6 = l , iff ( k , l ) ∈ E } . Giv en G , another set of interest here is parameterized by a vector v ∈ R K + of it s vertex weights and can be written as B 0 ( G, v ) = { B = ( b k l ) ∈ S K : b k l = ( v k v l ) 1 2 , ( k , l ) / ∈ E or k = l } . (10) For v = 1 , t his concept has i ts origin in th e seminal work [17 ] where it was used in an approach to the problem of graph capacity . The generalization to the case v ∈ R K + was provided l ater in the study of relaxations of the vertex packing problem [18]). The graph capacity p roblem, as the key probl em of zero-error information th eory , remains still unsolved in the general case [19]. The set (10) is , howe ver , a central element of the concept of so- called weig hted Lovasz function, wh ich in unweighted form (i.e. for v = 1 ) represents a general up per bou nd on graph capacity and is equal to the capacity for a certain graph class, including e.g. self-complement ary graphs with vertex-transitiv e automorphi sm groups [17], [30]. Precisely , the weight ed Lovasz function (later , simpl y Lovasz function ) of a graph G = ( K , E ) is defined as the m ap ( G, v ) 7→ θ 0 ( G, v ) = min A ∈A 0 ( G ) , c ∈ R L : k c k 2 =1 max k ∈K v k h a k , c i 2 , v ∈ R K + , (11) with A 0 ( G ) as the set of orthonorm al representati ons of G , and it has the following property . Pr opos ition 1 ([18 ], [31] ): F or any graph G = ( K , E ) , we have θ 0 ( G, v ) = min B ∈B 0 ( G, v ) λ max ( B ) , v ∈ R K + . In [18], [31], [37] one can find further i nteresting characterizations of the Lovasz functi on. A similar set which we make use of is B 1 ( G, v ) = { B = ( b k l ) ∈ S K : b k l ≥ ( v k v l ) 1 2 , ( k , l ) / ∈ E o r k = l } , (12) for any graph G = ( K , E ) and v ∈ R K + is a vector of its vertex weights. For t he case v = 1 , the concept of the set (12) is known from the considerations on the Delsarte bound , or Delsarte numb er , in [38], and the generalization to the case v ∈ R K + is straightforward. The unweighted (i.e. for v = 1 ) Delsarte bound was proposed within the algebraic framework of coding theory i n [39], as an upper b ound on the cardinality of an M -clique, M ⊂ { 1 , . . . , M } , i n an association scheme wi th M associate classes denoted here as ( K , {E i } M i =1 ) . As t he notion of associatio n scheme is only loosely related with our top ic, we refer here to Appendix B for an outline of t he theory . One can relate the Delsarte bound for an association scheme ( K , {E i } M i =1 ) to the graph G = ( K , E ) , ∪ M i =1 E i , i.e. the graph wh ose edge set correspon ds to the un ion of ass ociate classes: The unweighted Delsarte number u pper bounds the in dependence number of such graph [38] and the weight ed Delsarte number (later , simply Delsarte num ber/bound), denoted as map θ 1 , has then t he foll owing characterization. Pr opos ition 2 ([38 ]): F or any graph G = ( K , E ) , we have θ 1 ( G, v ) = min B ∈B 1 ( G, v ) λ max ( B ) , v ∈ R K + . 1 0 Further form ulations of th e Dels arte nu mber which are direct analogs of the origin al char- acterizations of the Lov asz function from [17] can be found , partly without proof, in [40] and [41]. In particular , the auth ors apply the framework of graph Laplacians and identify the Delsarte number with th e so -called σ -function of a graph and the Lovasz function with a related version o f it. Similar characterizations of the Lov asz functi on and Dels arte bound and their properties in terms of edge orbits are studied in [42]. For our purposes, we define two further s ets of the type (10), (12) and two related graph functions in the spirit of Propositions 1 and 2. First, we associate with a graph G = ( K , E ) and a weight vector v ∈ R K + , the set B 2 ( G, v ) = { B = ( b k l ) ∈ S K : b k l = ( v k v l ) 1 2 , ( k , l ) / ∈ E or k = l , b k l ≤ ( v k v l ) 1 2 , k , l ∈ K} . (13) In analogy to Propositio n 1, we define for any graph G the map ( G, v ) 7→ θ 2 ( G, v ) = min B ∈B 2 ( G, v ) λ max ( B ) , v ∈ R K + . (14) Second, als o the set B 3 ( G, v ) = { B = ( b k l ) ∈ S K : b k l = ( v k v l ) 1 2 , ( k , l ) / ∈ E or k = l v 1 2 v 1 2 ′ − B + λ max ( B ) I ∈ P K } (15) associated with any G = ( K , E ) and v ∈ R K + proves to be of key us e in the remainder . By the definition of the class P K of completely positive matrices in R K × K (Appendix A), the latter condition in (15) can be written equi valently as v 1 2 v 1 2 ′ − B + λ max ( B ) I = V ′ V , for some V ∈ R M × K + , M ∈ N . (16) Furthermore, it is worth n oting here that the condition v 1 2 v 1 2 ′ − B + λ max ( B ) I ∈ P K is implied by a slight ly stronger requirement th at v 1 2 v 1 2 ′ − B is included in the clos ure of P K : This is an i mmediate consequence of λ max ( B ) I = P k ∈K p λ max ( B ) e k p λ max ( B ) e ′ k and the characterization in Appendix A. By analo gy to Proposition 1, for any G = ( K , E ) we define a furth er m ap ( G, v ) 7→ θ 3 ( G, v ) = min B ∈B 3 ( G, v ) λ max ( B ) , v ∈ R K + . (17) The relati ons between (10), (12) and t he prop osed sets (13), (15) are readily seen. It is immediate that B 0 ( G, v ) ⊂ B 1 ( G, v ) and that the second cond ition in (13) can be written as v 1 2 v 1 2 ′ − B ∈ R K × K + . Thus, b y th e form (16) of t he second condit ion in (15) and by inspection of (10) and (13), i t can be seen that B 3 ( G, v ) ⊂ B 2 ( G, v ) ⊂ B 0 ( G, v ) ⊂ B 1 ( G, v ) , and thus θ 3 ( G, v ) ≥ θ 2 ( G, v ) ≥ θ 0 ( G, v ) ≥ θ 1 ( G, v ) (18) for any G = ( K , E ) and v ∈ R K + on hand. It is worth noti ng here that, gi ven v = 1 , the classes of matri ces (10), (12) generalize the set of so-called (1 , δ ) -adjacenc y matrices of graph G introduced in [43]. Any (1 , δ ) -adjacency matrix i s further affi nely transformable to a Seidel adjacency m atrix [32]. 1 1 B. Some r elat ions of the characterizations The algebraic graph descriptio ns introduced in Section III-A hav e som e sim ple properties which turn out to be central to our result s. The first lemma b elow can be partially deduced from the proof of Th eorem 3.5 in [35]. W e g iv e the proof for completeness and refer to Appendix A for t he notions related to t he s et of completely posit iv e matrices P K , such as the cp-rank. Lemma 1: Given any graph G = ( K , E ) , we have C ( G ) ∩ P K 6 = ø . and th e cp-rank satisfies φ ( C ) ≤ K ( K + 1) 2 , C ∈ C ( G ) ∩ P K . Pr oof : Associate any edge ( k , l ) ∈ E with e = e ( k , l ) , 1 ≤ e ≤ |E | , and let B = ( b k l ) ∈ R K ×|E | + be defined as 3 b ek > 0 , b el > 0 iff e = e ( k , l ) . Then it i s readily seen that ( B B ′ ) k l > 0 , k 6 = l iff ( k , l ) ∈ E , s o that C = B B ′ satisfies C ∈ C ( G ) and, by Definiti on 6, we also have C ∈ P K . This proves C ( G ) ∩ P K 6 = ø . According to the known bound on cp-rank, see e.g. Section 1 in [33 ], if additi onally C ∈ P K , then we can find B ∈ R K × N + such that C = B B ′ for some N ≤ K ( K + 1) / 2 , which completes the proof. The l emma says essentially that the set of feasibl e mat rices inclu des a completely positive matrix for any graph on hand and any such matrix remain s complet ely posit iv e if all diagonal elements are replaced by th e largest eigen value. Furthermore, for any graph with K vertices, e.g. a sharing graph of parallel channels accessed by K users, any of its compl etely p ositive feasible m atrices has a cp-rank no larger t han K ( K + 1) / 2 . The latter boun d on the cp-rank is th e best known, but likely not the best po ssible b ound [33]. Lemma 2: Given any graph G = ( K , E ) and v ∈ R K + , consid er the set D i ( G, v ) = { v 1 2 v 1 2 ′ − B + λ max ( B ) : B ∈ B i ( G, v ) } , i = 0 , 2 , 3 . Then, we have D 0 ( G, v ) ⊂ ∪ G ′ ⊂ G C ( G ′ ) , D 2 ( G, v ) ⊂ ∪ G ′ ⊂ G C ( G ′ ) ∩ R K × K + , D 3 ( G, v ) ⊂ ∪ G ′ ⊂ G C ( G ′ ) ∩ P K , wher e G ′ ⊂ G denotes tha t G ′ = ( K ′ , E ′ ) is a subgraph of G in t he sense th at K ′ ⊆ K and E ′ ⊆ E . More over , we have D 2 ( G, v ) = D 3 ( G, v ) , equivalent to B 2 ( G, v ) = B 3 ( G, v ) , if eit her K ≤ 4 or G has no odd cycles longer than 4 . Pr oof : Let any C = ( c k l ) ∈ R K × K such that C = v 1 2 v 1 2 ′ − B + λ max ( B ) , (19) for an arbitrary B ∈ B i ( G, v ) , i = 0 , 2 , 3 , be given. Then, by the definitions (10), (13), (15) we h a ve c k l = 0 , k 6 = l , if ( k , l ) / ∈ E , but also c k l = 0 , k 6 = l , if ( k , l ) ∈ F , for some F ⊆ E , where F = ø is allowed. This implies c k l 6 = 0 , k 6 = l , iff ( k , l ) ∈ E ′ , 3 In the particular case b ek = 1 , b el = 1 iff e = e ( k , l ) , matrix B represents the so-called incidence matrix of graph G [30], [32 ]. 1 2 with E ′ = E \ F . Thus, for any matrix C we hav e C ∈ C ( G ′ ) for some subg raph G ′ ⊂ G , with G ′ = ( K ′ , E ′ ) . If now i = 2 , then it is e vident by the definit ion (13) and by 4 λ max ( B ) ≥ 0 th at C ∈ D K (see Definitio n 5). By the result i n [44 ] th is imp lies C ∈ P K whenev er K ≤ 4 (see Appendi x A). Since C ∈ C ( G ′ ) for som e G ′ ⊂ G is prov en for any (19), we have further by Theorem 3.1 in [34], or by [45], that C ∈ P K holds also i f G h as n o odd cycles longer than 4 . By the definition (15), this completes the proof. An i mplication of the lemm a is th at any matrix C ∈ D i ( G, v ) , v ∈ R K + , is a feasible matrix of some subg raph of G . Further , any matrix C ∈ D 2 ( G, v ) is compl etely positive whenev er either a graph G with no m ore than 4 vertices is con sidered o r when the maxi mum odd cycle l ength in the graph is no longer th an 4 edges (the existence of some completely positive matrix C ∈ D 2 ( G, v ) is ensu red already by Lemm a 1). In p articular , any such matri x is completely positive for G as a sharing graph if the parallel channels are accessed by no more than 4 users, or if there are M ≤ 4 class es of parallel channel s users, where channel sharing within a class is not allowed/possible due to restriction s on implementation or QoS. Recall that such parallel channels are ill ustrated by Examples 6, 7 and thei r graphs are give n in Fig. 3. I V . U P P E R B O U N D S O N M A X - M I N F A I R P E R F O R M A N C E In this section we deriv e sev eral up per bounds on the worst-case us er performance in t he considered parallel channels. According to our pe rformance model, a n upper bound represents an optimistic case, i.e. a b etter value of user performance than the upp er bou nded one. The bounds in this section are not proven to be tight and thus, are not very interesting when considered alone. They become, howe ver , interesting and lead to the central conclusions of this work when considered to gether with the lower boun ds from Section V. A. Upper bounds In the following Proposition , a p olicy-specific bound on the worst p erformance wi thin the user population is proposed. Pr opos ition 3: Given N ≥ K , any G = ( K , E ) and any ( A , P ) ∈ A ( G, r ) × P ( A ) , r ∈ R K + , we have min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≤ min f ∈ ˇ F ( A , P ) h f , f i θ i ( G ( A ) , w ) , i = 0 , 1 , 2 , (20) with w ∈ R K + such that w k = γ 2 k r 2 k , k ∈ K , (21) and wher e we defined ˇ F ( A , P ) = { f ∈ R N + : h ¯ a k , f i ≥ h a k , f k ( p k ) i , k ∈ K , for some ¯ A ∈ A ( G, r ) } . Pr oof : Gi ven any A ∈ A ( G, r ) , f ∈ R N + and any P ∈ P ( A ) s uch that h a k , f k ( p k ) i 6 = 0 , k ∈ K (which b y our assu mptions in Section II exists) , let us define Z = ( z 1 , . . . , z K ) ′ ∈ R K × N such that z k = z k ( ¯ a k ) = r w k h f , f i f − p w k h f , f i h a k , f k ( p k ) i ¯ a k , k ∈ K , 4 This is readily seen by the feature that f or any C = B B ′ we have λ max ( C ) = max x ∈ R K : k x k 2 =1 x ′ B ( x ′ B ) ′ ≥ e ′ k B ( e ′ k B ) ′ = ( B B ′ ) kk ≥ 0 , k ∈ K . 1 3 with an arbitrary ¯ A = ( ¯ a 1 , . . . , ¯ a K ) ′ ∈ R K × N . Then, we have h z k , z l i = √ w k w l − √ w k w l h ¯ a k , f i h a k , f k ( p k ) i − √ w k w l h ¯ a l , f i h a l , f l ( p l ) i + √ w k w l h f , f ih ¯ a k , ¯ a l i h a k , f k ( p k ) ih a l , f l ( p l ) i , k , l ∈ K , (22) for any ¯ A ∈ R K × N . Let now f ∈ ˇ F ( A , P ) , and note that then we can find a parti cular ¯ A ∈ A ( G, r ) which satisfies h ¯ a k , f i = h a k , f k ( p k ) i , k ∈ K (23) (in fact, the sy stem (23) has alw ays a solut ion ¯ A ∈ R K × N and si nce by f ∈ ˇ F ( A , P ) there exists some ˜ A ∈ A ( G, r ) such that h ˜ a k , f i ≥ h a k , f k ( p k ) i , k ∈ K , it i s imp lied that ¯ A ≤ ˜ A , and thus ¯ A ∈ A ( G, r ) ). When ¯ A ∈ A ( G, r ) satisfying (23) is taken in (22), we yield h z k , z l i ≥ − √ w k w l , k , l ∈ K , (24) where in particul ar h z k , z k i = − w k + w k h ¯ a k , ¯ a k ih f , f i h a k ,f k ( p k ) i 2 , and, si nce by Definition 1 ( k , l ) / ∈ E implies h a k , a l i = 0 , also h z k , z l i = − √ w k w l , ( k , l ) / ∈ E , k 6 = l . (25) Thus, b y the definition (13), we can write − B = Z Z ′ − h f , f i G ( ¯ A ) , for som e B ∈ B 2 ( G, w ) , (26) where the map ˜ A 7→ G ( ˜ A ) , ˜ A ∈ R K × N + , follows by the definit ion of w as ( G ( ˜ A )) k k = γ 2 k h ˜ a k , ˜ a k i r 2 k h a k ,f k ( p k ) i 2 , k ∈ K , and ( G ( ˜ A )) k l = 0 for k , l ∈ K , k 6 = l . Feature (26) im plies then max k ∈K γ 2 k h f , f i h a k , f k ( p k ) i 2 I − B Z Z ′ , (27) since by s uch definition of G and b y the property h ¯ a k , ¯ a k i r 2 k = h ¯ a k , ¯ a k i h ¯ a k , 1 i 2 ≤ 1 we ha ve ( G ) k k ≤ max k ∈K γ 2 k h a k ,f k ( p k ) i 2 , k ∈ K . For the particular B ∈ B 2 ( G, w ) in (26) we have then max k ∈K γ 2 k h a k , f k ( p k ) i 2 ≥ λ max ( B ) h f , f i , f ∈ ˇ F ( A , P ) , so that for i = 2 t he result follows by the definition (13). For the cases i = 0 , 1 t he proposition follows t hen from the definiti ons (10), (12) and from the property (18), which completes the proof. By the proposition, the w orst squared user performance achiev ed under a ny policy ( A , P ) ∈ A ( r ) × P ( A ) in parallel channels is no bett er than t he ratio of the least 2 -norm achieve d among the vectors within the s et ˇ F ( A , P ) and the fun ction θ 2 e valuated for a sharing graph induced by A and for the vector w su ch that (21). According to (18), when such value of θ 2 is replaced by the Lov asz functi on value or Delsarte bound v alue assumed by the sh aring graph and th e vector w , the bound from Proposition 3 is loosened. Since γ k is a predefined performance requi rement and r k the fraction of th e channel s et N assigned to user k ∈ K over time, w can be int erpreted as t he vector of squared user performance requirements normalized b y assigned channel fractions. It is readily seen t hat ˇ F ( A , P ) i s the set of values of performance functions 5 which • are equal for any user accessing the parallel channels and, • for som e sharing m atrix whi ch induces the same sharing graph as A (i.e. under fixed sharing graph), attain user performance no worse than under policy ( A , P ) . 5 The value of the performance function f k , k ∈ K , i s a vector in R N + and shall not be confused wit h the user performance , see our performance model in S ection II-B. 1 4 Thus, i n som e sense, ˇ F ( A , P ) can b e seen as a set of d ominating values of QoS functions for the po licy ( A , P ) . Note that a QoS function value f ∈ ˇ F ( A , P ) may be not achi e va ble by an allowable power all ocation from P ( A ) , as such value leads t o a superior multi- user performance under the penalty of being equal for all users. The set ˇ F ( A , P ) is not a po lyhedron for a general ( A , P ) ∈ A ( r ) × P ( A ) . Nevertheless, for any given policy ( A , P ) , ˇ F ( A , P ) contains the polyhedron { f ∈ R N + : h a k , f i ≥ h a k , f k ( p k ) i , k ∈ K} (28) and its further polyh edral subset { f ∈ R N + : f ≥ f k ( p k ) , k ∈ K} wh ich depends merely on P . Both polyhedra give rise to obvious s implifications of (20): In particular , for any ( A , P ) ∈ A ( r ) × P ( A ) and for f max ( P ) = (max k ∈K f k 1 ( p k ) , . . . , max k ∈K f k N ( p k )) , we hav e min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≤ h f max ( P ) , f max ( P ) i θ i ( G ( A ) , w ) ≤ h P k ∈K f k ( p k ) , P k ∈K f k ( p k ) i θ i ( G ( A ) , w ) , i = 0 , 1 , 2 , with w su ch that (21). Thus, give n any policy i n parallel channels, the worst squared user performance can be no better than the squ ared 2 -norm of the channel-wise maximum, respectiv ely sum, of performance function s of u sers divided by the function θ 2 (or t he Lovasz function o r the Dels arte boun d) ev alu ated for the induced sharing graph and the vector of squared user performance requirements per assig ned channel fraction. The technicality o f the bound (20) lies in the structure of the optimization domain ˇ F ( A , P ) , while the weight vector w is easily in terpretable. As Corollary 8 in Appendix C, we prove an alternativ e version of Proposition 3 which sim plifies the optimi zation dom ain i n t he bo und at the expense of a m ore compl ex weight vector s tructure. Th e bounds from Proposition 3 and Corollary 8 yi eld t he following imp lication o n the max-min fair performance under given sharing t opology of parallel channels. Cor ollar y 1: G iven N ≥ K , any G = ( K , E ) and r ∈ R K ++ , we have max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≤ min f ∈ ˇ F ( G, r ) h f , f i θ i ( G, w ) , i = 0 , 1 , 2 , (29) wher e w is such that (21) and wher e ˇ F ( G, r ) = { f ∈ R N + : h ¯ a k , f i ≥ h ˆ a k , f k ( ˆ p k ) i , k ∈ K , f or some ¯ A ∈ A ( G, r ) } , with ( ˆ A , ˆ P ) = arg max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k . By Proposition 3 it is e v ident that ˇ F ( G, r ) is equiv alent to the set of dominating QoS function values ˇ F ( ˆ A , ˆ P ) , where ( ˆ A , ˆ P ) ∈ A ( G, r ) × P ( ˆ A ) i s a max-min fair pol icy under a fixed sharing graph G . As ˇ F ( ˆ A , ˆ P ) contains the polyhedron (28) for P = ˆ P , we get the following loosened version of (29). Cor ollar y 2: G iven N ≥ K , any G = ( K , E ) and r ∈ R K ++ , we have max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≤ min f ∈ ˜ F ( G, r ) h f , f i θ i ( G, w ) , i = 0 , 1 , 2 , (30) wher e w is such that (21) and wher e, with ˆ A defined as in Cor ollary 1, ˜ F ( G, r ) = { f ∈ R N + : k f k 1 ≥ k f k ( p k ) k 1 , k ∈ K , P ∈ P ( ˆ A ) } . Pr oof : First not ice that for the policy ( ˆ A , ˆ P ) defined in Corollary 1 we necessarily hav e k ˆ a k k 1 = r k , k ∈ K . Further , as for any A ∈ A ( G, r ) such that k a k k 1 = r k , k ∈ K , 1 5 it follows that P k ∈K a k = 1 , we can write the condi tion h f , 1 i ≥ h f k ( p k ) , 1 i , k ∈ K , P ∈ P ( ˆ A ) , specifically as X k ∈K h f , a k i ≥ max l ∈K h f l ( p l ) , X k ∈K ˆ a k i = X k ∈K h max l ∈K f l ( p l ) , ˆ a k i , A ∈ A ( G, r ) , P ∈ P ( ˆ A ) . This furt her im plies for a particular P = ˆ P that X k ∈K h a k , f i ≥ X k ∈K h ˆ a k , f k ( ˆ p k ) i , A ∈ A ( G, r ) . (31) Let now A be defined as a k = αf k ( ˆ p k ) ◦ ˆ a k ◦ f − 1 , k ∈ K , where f − 1 = (1 /f 1 , . . . , 1 /f N ) and α > 0 is chosen to ensure k a k k 1 ≤ r k , k ∈ K , and thus A ∈ A ( G, r ) (it is e vident that any sufficiently smal l α satisfies su ch condition). For this particular A we have h a k , f i = α h ˆ a k , f k ( ˆ p k ) i , k ∈ K , so that together with (31) it i s im plied t hat α ≥ 1 and on the ot her hand h a k , f i ≥ h ˆ a k , f k ( ˆ p k ) i , k ∈ K . Consequently , ˜ F ( G, r ) ⊆ ˇ F ( G, r ) which, by Corollary 1, completes the proof. The set ˜ F ( G, r ) includes all QoS function values, equal for all users, w hich are in the sum over all channels superior to any QoS fun ction value achiev ed by an allow able (for some ˆ A ∈ A ( G, r ) ) power allocation. Thus, ˜ F ( G, r ) can be seen as a hull of any u ser dimension of the feasible QoS/perfo rmance set of parallel channels, which we define in analogy to the theory for channels with interference as [46] { ( f 1 ( p 1 )) , . . . , f K ( p K )) : P ∈ P ( ˆ A ) } , (32) (equiv alentl y , × k ∈K ˜ F ( G, r ) is a hull of the feasible QoS set). Corollary 1 implies that a s quared m ax-min fair performance under the condit ion of a fixed sharing graph G in parallel channels can n e ver exceed the ratio of the minimum squared 2 - norm within the hull ˜ F ( G, r ) of any user dimension of (32) and the value of the function θ 2 (or the Lov asz function, or the Delsarte number) assumed by G and the vector w satisfyin g (21). Consider now const raints on transm it power at any ti me (in a frame), as expressed e.g. by (4a), in which case we hav e P ( A ) = P , A ∈ A ( r ) (allowable power allocati ons are independent of sharing matrices and sharing graphs). In such case it is readily seen th at also set ˜ F ( G, r ) is independent of the sharing graph on hand, i .e. ˜ F ( G, r ) = ˜ F ( r ) regardless of G , and thus the bound (30) ass umes a specific separated st ructure. Precisely , the max-mi n fair performance under a fixed sharing graph is upper-bounded by a ratio of a value dependent solely on th is graph and a vector norm determined completely by the the attain able power allocations. Thus, (30) provides a separation between th e influence of the combi natorial topology in duced b y the channel sharing poli cy via Definition 1 and th e im pact of (the structure of) the set of allowable power allo cations. The optimisti c boun d (30), alth ough looser than the o ne from Corollary 1 , proves in t he next section t o be particularly ins ightful, since a complementary p essimistic b ound of t he s ame t ype can be given. Again, recall that according to (18), Corollary 1 and (30) provide the tight est boun ds when th e extension θ 2 of the Lovasz functi on and the Delsarte boun d is incorporated. Obviously , w e can reformulate Coroll ary 1 and (30) for the m ax-min fair performance nonrestricted i n term of the sharin g graph. Precisely , max ( A , P ) ∈A ( r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≤ min f ∈ ˇ F ( ˆ G, r ) h f , f i θ i ( ˆ G, w ) ≤ min f ∈ ˜ F ( G, r ) h f , f i θ i ( ˆ G, w ) , i = 0 , 1 , 2 , 1 6 with ˆ G as th e max-min fair s haring graph in th e sense that ˆ A ∈ A ( ˆ G, r ) (equiv al ently , ˆ G = G ( ˆ A ) ), where now ( ˆ A , ˆ P ) = arg max ( A , P ) ∈A ( r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k (33) is th e (graph-non restricted) max-mi n fair p olicy of the parallel channels. B. Relations to coding and zer o-err or capaci ty Relations of m ax-min fair performance in parallel channels to codi ng and zero-error information th eory resul ts are obtained in the setting γ k r k = 1 , k ∈ K . (34) This can be assumed for a homogeneous u ser popul ation, that is, if an equal fraction of the parallel channels i s to be assigned (over time) to any user and all users ha ve equal performance requirements. By th e celebrated resul t in [17], the Lovasz functio n of G, w satisfies in such case θ 0 ( G, w ) ≥ Θ( G ) , where Θ( G ) = lim n →∞ n p α ( G n ) represents the (zero-error) capacity of G ; α expresses hereby the independence number of a graph and G n denotes an n -fold concatenatio n, or power , of graph G [30]. The capacity interpretation of Θ( G ) originates from the fact t hat α ( G n ) represents the maximum numb er of n -lett er messages which w ill not be confounded when k ∈ K correspond to alphabet letters and any edge ( k , l ) ∈ E models the (dang er of) confusion of letters k , l [17]. As a consequence of Corollary 1, (30) and th e result of Lovasz we y ield for any s haring graph G that max ( A , P ) ∈A ( G, 1 ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 ≤ min f ∈ ˇ F ( G, 1 ) h f , f i Θ( G ) ≤ min f ∈ ˜ F ( G, r ) h f , f i Θ( G ) . In words, un der a homogeneous user p opulation accessing the parallel channels and und er sharing graph fixed to G , the max-min fair performance never exceeds the mini mum 2 -norm within the set ˇ F ( G, 1 ) (respectively , within the hull ˜ F ( G, r ) ) divided by the square root of the sharing graph capacity . Thi s means also that t he m ax-min fair performance scales at mos t with the capacity of the corresponding sharing graph G = ( K , E ) , i.e. with the effec tive size of the alphabet needed for error-fr ee communi cation of the letters K where th e letter pairs E are confusable [17]. Giv en (34), we have als o the central relation of the Delsarte bou nd of G and the graph’ s independence number according to [38] θ 1 ( G, w ) ≥ α ( G ) , (recall th at by (18) we h a ve additi onally θ 0 ( G, w ) ≥ θ 1 ( G, w ) ). Thus, max ( A , P ) ∈A ( G, 1 ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 ≤ min f ∈ ˇ F ( G, 1 ) h f , f i α ( G ) ≤ min f ∈ ˜ F ( G, r ) h f , f i α ( G ) , which, with definiti on of the i ndependence number , m eans that th e ratio of min f ∈ ˇ F ( G, 1 ) h f , f i (respectiv ely , min f ∈ ˜ F ( G, r ) h f , f i ) and the m aximum cardinali ty of a vertex subs et of a shar- ing graph G such that no two vertices in it are adjacent upper b ounds the m ax-min fair performance under fixed sharing graph. Thi s im plies that the m ax-min fair performance in parallel channels scales at most with the independence number of the sh aring graph. W e close the discussion of the u pper bound s by poin ting out two crucial iss ues. First, the giv en upper bounds on the max-min fair performance apply to the case N ≥ K , i.e. t o the parallel channel instances with the channel ensemb le no sm aller than the us er population 1 7 accessing t hem. Thus, th e boun ds apply to, in some sense, non-overloaded parallel channels, which allow the possibil ity of permanent (i.e. in each frame) access to a channel for any us er . Second, the generality of the upp er bounds has to be underlined. The bounds apply to any performance function for which the form ulation of the m ax-min fair performance according to (9) is meaningful , that is, when a larger user performance im plies a better percei ved service quality le vel at the user recei ver (Ex amples 1-4). V . L OW E R B O U N D S O N M A X - M I N FA I R P E R F O R M A N C E The lower bound s on max-min fair p erformance presented in this section correspond t o pessimist ic values, in the sense that the max-min fair p erformance is guaranteed to be no worse. These b ounds are analogs, or comp lements, o f the optimis tic bounds from Section IV, and tog ether embrace the max-min fair performance in parallel channels. A. Some notes on mat rix scali ngs The proposed b ounds make use of some novel elements of t he theory of matrix similarity and m atrix s caling wh ich are outl ined in the following. Let us define a scaling of a nonneg- ativ e m atrix by straightforwardly extending the idea of scaling of a square posit iv e matrix from [47]. Definition 3: A mat rix A ∈ R K × N + is sa id to be ( r , c ) -scalable, wher e r ∈ R K ++ and c ∈ R N ++ , if k r k 1 = k c k 1 and if there exist X = dia g ( X ) ∈ R K × K + and Y = dia g ( Y ) ∈ R N × N + such that X A Y 1 = r , 1 ′ X A Y = c ′ . (35) The pa ir ( X , Y ) is then r eferr ed to as an ( r , c ) -scaling of A . Thus, an ( r , c ) -scaling of a non negati ve matrix collects scaling factors of rows and columns, in the form of two diagonal matrices, such th at row sum s grouped in r and column sums grouped in c are obtained under row-wise and column-wise scaling. A related noti on wh ich proves u seful in later considerations i s the set X ( A , r , c ) = { x = X 1 , y = Y 1 : ( X , Y ) is ( ¯ r , ¯ c ) -scaling of A ∈ R K × N + , ( ¯ r , ¯ c ) ≤ ( r , c ) } . In words, X ( A , r , c ) cons ists of vector p airs which collect diago nal entries of those ( ¯ r , ¯ c ) - scalings of A ∈ R K × N + which are no larger than 6 ( r , c ) . Giv en predefined r ∈ R K ++ and c ∈ R N ++ , it is obvious that matrices w hich are not ( r , c ) -scalable exist in R K × N + . Nev ertheless, for any non negati ve matrix we can always find a s caling which leads to ro w and column su ms no larger than the predefined ones. Lemma 3: Given any A ∈ R K × N + and any ¯ r ∈ R K ++ , ¯ c ∈ R N ++ , ther e e xist r ≤ ¯ r a nd c ≤ ¯ c s uch that A i s ( r , c ) -scalable. Pr oof : Let A = ( a 1 , . . . , a K ) ′ , with a k ∈ R N + , k ∈ K , and define ¯ A = X A , where X = diag ( X ) is such th at X 1 = x and x k = ¯ r k h a k , 1 i , k ∈ K . Then, letting ¯ A = ( ¯ a 1 , . . . , ¯ a K ) ′ , we have ¯ A 1 = ¯ r , so that if 1 ′ ¯ A ≤ ¯ c , the proof is completed. Otherwise, let ˆ A = ¯ AY , where Y = diag ( Y ) is such that Y 1 = y , with y n = min n ∈N ¯ c n ( 1 ′ ¯ A ) n , n ∈ N . Then, it is evident that 1 ′ ˆ A ≤ ¯ c ′ . Further , as ( 1 ′ ¯ A ) n > ¯ c n for som e n ∈ N (by assumptio n), we h a ve 0 < y < 1 , which imp lies also ˆ A 1 < ¯ A 1 = ¯ r and completes the proof. 6 Here and hereafter we refer to a scaling as larger/smaller than an other scaling if the obtained column and ro w sums are componentwise larger/smaller . 1 8 The o riginal characterization of a scaling (of a square positive matrix) was given in [47] in terms of a nonlinear program. The currently known description s of scalings of n onnegati ve matrices are mostly in terms of optim ization problems, see e.g. [48] and references therein. In the foll owing we p rovide a novel (to t he best of o ur knowledge) characterization wh ich extends the concept from [49]. Lemma 4: Let A ∈ R K × N + be ( r , c ) -scalable f or some r ∈ R K ++ , c ∈ R N ++ . Then, i f we define ¯ r = ( r ′ 0 ) ′ ∈ R N + and if y ∈ R N ++ satisfies ∇ ϕ ( y ) ≤ 0 (36) for t he f unction z 7→ ϕ ( z ) = − X n ∈N log z c n n ( Az ) ¯ r n n , z ∈ R N ++ , and if x ∈ R K ++ is su ch that x k = x k ( y ) = r k ( Ay ) k , k ∈ K , (37) then ( X , Y ) such th at X 1 = x and Y 1 = y is an ( r , c ) -scaling of A . Mor eover , (36) is satisfied if and only if y i s a global minimizer y = arg min z ∈ R N ++ − X n ∈N log z c n n ( Az ) ¯ r n n . (38) Pr oof : By the definition, we can write ( ∇ ϕ ( z )) n = P k ∈K a k n r k ( A z ) k − c n z n , n ∈ N , for any z ∈ R N ++ , so that with (37) we hav e in particular for z = y that ( ∇ ϕ ( y )) n = ( A ′ x ) n − c n y n = ( A ′ X 1 ) n − c n y n , n ∈ N . This i mplies tog ether wi th (36) that 1 ′ X AY ≤ c . (39) Further , we ha ve ( X A Y 1 ) k = x k ( Ay ) k = r k , k ∈ K , by the definition (37), and thus 1 ′ X A Y 1 = 1 ′ c , since 1 ′ c = 1 ′ r holds by assumption (Definition 3). Consequently , (39 ) is satisfied only if X AY = c , and thus ∇ ϕ ( y ) ≤ 0 only if ∇ ϕ ( y ) = 0 . T o prove that the latter condit ion is equiva lent to (38), apply the transform v = log z , z ∈ R N ++ , and then re w rite ϕ wit h the properties of the logarithm as ϕ ( e v ) = − X n ∈N ¯ r n log e v n ( A e v ) n − X n ∈N ( c n − ¯ r n ) v n , v ∈ R N . As ¯ r ∈ R N + and the map v 7→ e v n ( A e v ) n , v ∈ R N , is known to be log-concav e (see, e.g., [46], Chapter 6), it is imm ediate that v 7→ ϕ ( e v ) is con ve x for v ∈ R N . T hus, ∇ ϕ ( e w ) = 0 is equiv alent t o w = arg min v ∈ R N ϕ ( e v ) , wh ich by the one-to-one s etting w = log y g iv es (38) and completes the proof. It is worth ment ioning that fun ction ϕ from the lemma is multi plicative ly homogeneous in the sens e that ϕ ( z ) = ϕ ( α z ) for any z ∈ R K ++ and α > 0 (so that any m inimizer (3 8) scaled by s ome α > 0 is a m inimizer of ϕ as well). This is readily seen from the exponential transformation e ϕ ( z ) = Q K k =1 ( Az ) r k k Q N n =1 z c n n , as used ori ginally in [49], and from th e conditi on k r k 1 = k c k 1 . Furthermore, there is a surprising relation of function ϕ to th e throughput optimization under interference. Let 1 9 us i nterpret z ∈ R N + as a transm it power vector of the user po pulation N accessing the interference channel whi ch has ( A ′ 0 ) ′ ∈ R N × N + as its interference matrix, defined in the usual way as e.g. in [46 ], [50] (this im plies that the channel gains of N − K users are zero). Then, by defining the Signal-to-Interference functions of users in the i nterference channel as z 7→ SIR n ( z ) = z n ( A z ) n , n ∈ N [50 ], we can write ϕ ( z ) = − K X k =1 r k log SIR k ( z ) − K X k =1 ( c k − r k ) log z k − N X k = K +1 c k log z k . (40) By this form, − ϕ can be recognized as the weigh ted throughput fun ction o f t he d escribed interference channel with additional cost fun ctions. When c k ≥ r k ≥ 0 , k ∈ K , such cost functions penalize log arithmically the excessiv e use o f transmit power by the users. By the proof of Lemm a 4, the weighted throughput function (40) is known to be con vex as a function of the logarithm ic power vector v = log z , z ∈ R N ++ (e.g. power allocation in dB). Lemma 4 and the above interpretatio n l ead to the conclusion that ( X , Y ) , with Y 1 = y and X 1 = x , i s an ( r , c ) -scaling of an ( ( r , c ) -scalable) A if y represents a power allocation which gl obally mini mizes the p enalized weighted throughput fun ction (40) in th e described interference channel and x is determi ned by y via (37). Finally , we n eed th e fol lowing scalin g-related function. Definition 4: Given r ∈ R K ++ , let the map V 7→ µ ( V ) , V ∈ R K × N + , be defined as 7 µ ( V ) = max ( x , y ) ∈X ( V , r , 1 ) min ( n,k ) ∈N ×K ( x k y n ) 2 . Such fun ction represents the mi nimum squared g eometric mean of pairs of di agonal entries of an ( ¯ r , ¯ c ) -scaling of a give n matrix , achieva ble among all ( ¯ r , ¯ c ) -scalings no larger than ( r , c ) . In the spirit of [51], we can regard µ as a (kind of) metri c, or measure, of the entire class of su ch scalings of a given m atrix. As the simple property of lat er int erest, we obs erve that if t he row and column sum vectors of V do not exceed ( r , 1 ) , i.e. V 1 ≤ r and 1 ′ V ≤ 1 ′ , then µ ( V ) ≥ 1 . B. Lower bounds Using Definit ion 4 we can form ulate t he fol lowing lower bo und on t he max-min fair performance in parallel channels under fixed s haring graph. Pr opos ition 4: Given any G = ( K , E ) and r ∈ R K ++ , we ha ve max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max B ∈B 3 ( G, w ) , V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I µ ( RV ) max f ∈ ˆ F ( G, r ) h f , f i λ max ( B ) , (41) wher e w is such that (21), wher e N ≥ K ( K + 1) 2 , (42) and wher e, with ˆ A defined as in Cor ollary 1 , ˆ F ( G, r ) = { f ∈ R N + : f = f k ( p k ) , k ∈ K , for so me P ∈ P ( ˆ A ) , f = arg max ¯ f ∈ R N + max A ∈A ( G, r ) min k ∈K h a k , ¯ f i 2 γ 2 k h ¯ f , ¯ f i } . Mor eover , for a pa rticular B = arg min ¯ B ∈B 3 ( G, w ) λ max ( ¯ B ) (43) 7 W e omit here the indication of the dependence on r , since i t does not introduce any ambiguities in the remainder . 2 0 (41) implies fu rther max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I µ ( RV ) max f ∈ ˆ F ( G, r ) h f , f i θ 3 ( G, w ) . (44) Pr oof : Let any G = ( K , E ) and any B ∈ B 3 ( G, w ) be given, a nd let V = ( v 1 , . . . , v K ) ′ satisfy V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B ) + I , V ∈ R K × N + , (45) where by the definition (15 ) it i s known that such V exists whene ver N = N ( B ) satisfies N ≥ φ ( λ max − 1 ( B )( w 1 2 w 1 2 ′ − B ) + I ) . Defining W 1 2 = diag ( W 1 2 ) as ( W 1 2 ) k k = ( w 1 2 ) k , k ∈ K , the right-hand side of (45) can be rewritten due to − B + λ max ( B ) I 0 as λ max − 1 ( B )( w 1 2 w 1 2 ′ − B ) + I = λ max − 1 ( B ) W 1 2 C C ′ W 1 2 + X X ′ , (46) with any C = ( c , . . . , c ) ′ ∈ R K × N such that h c , c i = 1 and with any X = ( x 1 , . . . , x K ) ′ ∈ R K × N which satisfies X X ′ = − B + λ max ( B ) I and ( x k ) n = 0 , n > K , k ∈ K . Letting now N ≥ max { K + 1 , φ ( λ max − 1 ( B )( w 1 2 w 1 2 ′ − B ) + I ) } , we can find for any su ch X s ome C = C ( X ) ∈ R K × N + satisfying h c , x k i = 0 , k ∈ K , (47) so that (46) can be rewritten as λ max − 1 ( B )( w 1 2 w 1 2 ′ − B ) + I = ( λ max − 1 2 ( B ) W 1 2 C ± X )( λ max − 1 2 ( B ) W 1 2 C ± X ) ′ . (48) By (45), it follows now th at any vector tuple x k + q w k λ max ( B ) c , k ∈ K , yielding (48 ) satisfies h x k + r w k λ max ( B ) c , x l + r w l λ max ( B ) c i = h v k , v l i , k , l ∈ K , i.e., vector t uple x k + q w k λ max ( B ) c , k ∈ K , h as t he same lengths and mutu al ang les as any vector t uple v k , k ∈ K , yielding (45). As a consequence, for any tuple v k , k ∈ K , satis fying (45) and for any c and x k , k ∈ K , from (48), there exists a rotation matrix Q ∈ R N × N (a real-v alued orthogonal matrix with unit determin ant) for which [52] v k = Q ( x k + r w k λ max ( B ) c ) , k ∈ K . By orth ogonality of Q we hav e h Qc , Qc i = h c , c i and h Qx k , Qx l i = h x k , x l i , k , l ∈ K , and (47) implies h Qc , Qx k i = 0 , k ∈ K . Thus , it fol lows now that any factor in (45) can be written as V = q λ max − 1 ( B ) W 1 2 C ± X (49) for some C = ( c , . . . , c ) ′ ∈ R K × N + , h c , c i = 1 , and for some X ∈ R K × N satisfying (47) (where X i s such that X X ′ = − B + λ max ( B ) I ). This further yields that h v k , c i = r w k λ max ( B ) , k ∈ K , (50) and, by the Definition (15), als o h v k , v k i = 1 , k ∈ K , h v k , v l i = 0 , k 6 = l, i f ( k , l ) / ∈ E . (51) By (50 ) we have λ max ( B ) h f , f i = w k h v k , f i 2 , k ∈ K , (52) 2 1 for any f ∈ R N + chosen to satisfy f √ h f , f i = c for the particular vector c in (50). By Lem ma 3 it is further impl ied that there exist ( Z , Y ) ∈ R K × K + × R N × N + which represent an ( ¯ r , ¯ c ) - scaling of RV such th at ( ¯ r , ¯ c ) ≤ ( r , 1 ) : By setting Z 1 = z , Y 1 = y this means that we can take any ( z , y ) ∈ X ( R V , r , 1 ) , so that by (51) and Definition 1 it follows that U = Z R V Y satisfies U ∈ A ( G, r ) . Furthermore, w riting U = ( u 1 , . . . , u K ) ′ , we have then by the definition of w that w k h v k , f i 2 = γ 2 k ( P n ∈N r k ( v k ) n f n ) 2 = γ 2 k z 2 k ( P n ∈N 1 y n ( u k ) n f n ) 2 ≥ γ 2 k min ( k, n ) ∈K×N ( z k y n ) 2 h u k , f i 2 , k ∈ K , (53) which implies wit h (52) and Definiti on 4 finally that λ max ( B ) µ ( RV ) h f , f i ≥ γ 2 k h u k , f i 2 , k ∈ K . (54) Note now that (54) holds for any f ∈ R N + with f √ h f , f i = c for the parti cular c in (50) and, by the assumpti on (2) and the assumpt ions with respect to f k , k ∈ K , we can always find a particular f s uch that additionally f = f k ( p k ) , k ∈ K , for an arbitrary A ∈ A ( G , r ) and for s ome P ∈ P ( A ) 8 . Consequently , it is further impli ed that λ max ( B ) µ ( RV ) ≥ min A ∈A ( G, r ) , f ∈ R N + : f = f k ( p k ) ,k ∈K , for some P ∈P ( ˆ A ) max k ∈K γ 2 k h f , f i h a k , f i 2 = max k ∈K γ 2 k h ˆ f , ˆ f i h ¯ a k , ˆ f i 2 , ˆ f ∈ ˆ F ( G, r ) , (55) where ˆ A is defined as in Corollary 1 and ¯ A = arg min A ∈A ( G, r ) max k ∈K γ 2 k h ˆ f , ˆ f i h a k , ˆ f i 2 . Th us, finally it is im mediate that λ max ( B ) µ ( RV ) h f , f i ≥ min ( A , P ) ∈A ( G, r ) ×P ( A ) max k ∈K γ 2 k h a k , f k ( p k ) i 2 , f ∈ ˆ F ( G, r ) , (56) for a ny B ∈ B 3 ( G, w ) , for any V sati sfying (45) a nd N ≥ max { K +1 , φ ( λ max − 1 ( B )( w 1 2 w 1 2 ′ − B ) + I ) } . According to Lemmas 1, 2 , the latter conditi on is satisfied regardless of B ∈ B 3 ( G, w ) if N ≥ K ( K + 1) / 2 . As (56) is satisfied in particular for ¯ B s uch that λ max ( ¯ B ) = max B ∈B 3 ( G, w ) λ max ( B ) = θ 3 ( G, w ) , the proof is completed. The proposition says that the squared max-min fair performance achiev ed in parallel channels under fixed sharing topology is guaranteed to be no worse th an the maximum ratio of some two expressions. The denominator expression is the maximum eigen va lue o f a matrix B from B 3 ( G, w ) , which is determi ned by the g iv en sharing graph G and the vector of squ ared user performance requirements normalized by ass igned channel fractions. The numerator corresponds to th e squared 2 -norm of a vector from the set ˆ F ( G, r ) multipli ed by the value of the metric µ of the class of ( ¯ r , ¯ c ) -scalings n o l ar ger than ( r , 1 ) , of a n onnegati ve factor of R ( λ max − 1 ( B )( w 1 2 w 1 2 ′ − B ) + I ) R . (57) By Lemma 2, the m atrix (57) represents a particular feasible m atrix of a subgraph of the sharing graph. Obviousl y , the lo oser b ound (41) is obtained by replacing the maximizati on of µ ( RV ) /λ max ( B ) , conducted ov er B ∈ B 3 ( G, w ) and the factors of (57), by the minim ization 8 Equi v alently , by these assumptions, { f ∈ R N + : f = f k ( p k ) , k ∈ K , P ∈ P ( A ) } has a nonempty intersection with the ray { f ∈ R N + : f √ h f , f i = c } for any c ∈ R N + , and A ∈ A ( G, r ) . 2 2 of the eigen value o nly . By Coroll ary 1 and Proposition 4 we ha ve now min f ∈ ˇ F ( G, r ) h f , f i θ 2 ( G, w ) = max B ∈B 2 ( G, w ) min f ∈ ˇ F ( G, r ) h f , f i λ max ( B ) ≥ max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max B ∈B 3 ( G, w ) , V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I µ ( RV ) max f ∈ ˆ F ( G, r ) h f , f i λ max ( B ) ≥ µ ( RV ) max f ∈ ˆ F ( G, r ) h f , f i θ 3 ( G, w ) , (58) where RV in the out er lower bound denotes any nonn egati ve f actor of (57) for the particular matrix (43), achieving the value of the θ 3 function (see (17)). Wh ile ˇ F ( G, r ) was shown to be the set of dominating performance functi on values for some pol icy ( ˆ A , ˆ P ) , set ˆ F ( G, r ) includes precisely th ose QoS function v alues which • are equal for any user accessing the parallel channels, • are attainable by some allowable power all ocation (und er som e ˆ A ∈ A ( G, r ) ) and, • optimize the worst user performance under fixed sharing graph G and under QoS function v alues normali zed to unit 2 -no rm and equal for all users. It is immediate th at ˆ F ( G, r ) is inclu ded in the feasible performance set (32) of the parallel channels and has the property that f ∈ ˆ F ( G, r ) implies α f ∈ ˆ F ( G, r ) , α < 1 . The inequality (58) contains the tightest propos ed bound s whi ch utilize the extensions θ 2 , θ 3 of the Lovasz function and Dels arte number . Since the intricacy of these bounds lies e vidently in the st ructure of the sets ˇ F ( G, r ) , ˆ F ( G, r ) , we proceed b y proving some loosened lower bo unds whi ch together with the loos er lower bound (30) lead to our central i nsights. Cor ollar y 3: G iven a ny G = ( K , E ) and r ∈ R K ++ , we have max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max B ∈B 3 ( G, w ) , V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I µ ( RV ) max f ∈ ¯ F ( G, r ) h f , f i λ max ( B ) , with w such that (21), with N ∈ N sa tisfying (42), an d, given ˆ A defined as in Cor ollary 1, ¯ F ( G, r ) = { f ∈ R N + : h ¯ f , ¯ f i ≤ h f , f i ⇒ ¯ f = f k ( p k ) , k ∈ K , for some P ∈ P ( ˆ A ) } . Mor eover , given a part icular (43), this further i mplies max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I µ ( RV ) max f ∈ ¯ F ( G, r ) h f , f i θ 3 ( G, w ) . Pr oof : The definition o f ¯ F ( G, r ) impli es that f ∈ ¯ F ( G, r ) if and only if h f , f i ≤ max δ> 0 δ sub ject to B ( δ ) ⊆ ∩ k ∈K { f = f k ( p k ) : P ∈ P ( ˆ A ) } , (59) where we define B ( δ ) = { f ∈ R N + : h f , f i ≤ δ } . On the oth er hand, we can writ e by the definition of ˆ F ( G, r ) (quite redundantly) max f ∈ ˆ F ( G, r ) h f , f i = min ¯ δ> 0 ¯ δ sub ject to B ( ¯ δ ) ⊇ ( ∩ k ∈K { f = f k ( p k ) : P ∈ P ( ˆ A ) } ∩ { f = α ˆ f : α ≥ 0 } ) , (60) where ˆ f = arg min f ∈ R N + min A ∈A ( G, r ) , f ∈ R N + max k ∈K γ 2 k h f , f i h a k , f i 2 . Now , as any ˆ f is arbitrarily nonnegativ ely scalable (that is, the l atter set in the constraints in (60) i s a ray in R N + ), it is im plied further by (60) that max f ∈ ˆ F ( G, r ) h f , f i ≥ min ¯ δ > 0 ¯ δ subject t o B ( ¯ δ ) ⊇ B ( δ ) , (61) 2 3 for any δ satisfying the const raints in (59). Thus, by (59), (61) i t follows finally h f , f i ≤ max ¯ f ∈ ˆ F ( G, r ) h ¯ f , ¯ f i , f ∈ ¯ F ( G, r ) , which is, according to Proposition 4, suffic ient for t he proof for any given G = ( K , E ) and r ∈ R K ++ . By (30 ) and Corollary 3 we have now min f ∈ ˜ F ( G, r ) h f , f i θ 2 ( G, w ) = max B ∈B 2 ( G, w ) min f ∈ ˜ F ( G, r ) h f , f i λ max ( B ) ≥ max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max B ∈B 3 ( G, w ) , V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I µ ( RV ) max f ∈ ¯ F ( G, r ) h f , f i λ max ( B ) ≥ µ ( RV ) max f ∈ ¯ F ( G, r ) h f , f i θ 3 ( G, w ) , (62) with RV in the l ast expression as any nonnegativ e factor of the parti cular matrix (57), with (43). From the proo f of the corollary it is evident that ¯ F ( G, r ) can be interpreted as the lar gest, say , ball (in the 2 -norm) of performance functio n values, equal for all u sers, i ncluded in each user d imension of the feasible QoS set (32 ) of the parallel channels. On th e ot her hand, recall that th e hull ˜ F ( G, r ) , determini ng the optimist ic bound in (62), contains any such user dimension of the feasible QoS set. Thus, the ball ¯ F ( G, r ) and the hull ˜ F ( G, r ) determine the interval (62) of candi date max-m in fair performance values in t erms of th e structure of t he feasibl e performance set of parallel channels; that is, i n t erms of t he st ructure of t he s et of allowable power allocati ons P ( ˆ A ) and the features of the QoS functions f k , k ∈ K . In precise terms, t he only such feature which is d ecisiv e for th e bounds (62) is the (squared 2 -norm of the) minimum gap between ˜ F ( G, r ) and ¯ F ( G, r ) , measured as min f ∈ ˜ F ( G, r ) h f , f i − max f ∈ ¯ F ( G, r ) h f , f i . Such gap is visuali zed, t ogether with the hull ˜ F ( G, r ) and the ball ¯ F ( G, r ) for exemplary instance of parallel channels i n Figs. 4 and 5 9 . Consider now sp ecifically the case of limitatio ns of t ransmit powers at any time (in a frame), e.g. constrained t ransmit power of any user or const rained joint power budget of all users resulting i n (4a), respectiv ely . As in such case P ( A ) = P , A ∈ A ( r ) , it is readily seen that also ¯ F ( G, r ) = ¯ F ( r ) for any sharing graph G (i.e., ¯ F ( G, r ) is independent of the ind uced sharing graph). A s a consequence, the influence of the features of the channel sharing policy on t he interv al (62) of candidate values of max-min fair performance is in such case compl etely separated from the impact of the allow able p owe r allocations. The com binatorial properti es of the s haring graph G govern th e inner bounds i n (62) via the m inimum achiev able eigen values λ max ( B ) among matrices B ∈ B 2 ( G, w ) and the normalized eigen va lues λ max ( B ) /µ ( RV ) among matrices B ∈ B 3 ( G, w ) ; the no rmalization is by the (values of) the m etrics µ o f the associated factors of (57). Analogously , the ou ter bound behavior is described by the fun ction values θ 2 ( G, w ) and n ormalized function values θ 3 ( G, w ) /µ ( RV ) , for the sharing graph G and th e vector of squared user performance requirements per assigned channel fraction w , where the normalizati on is now by the metric µ of the correspond ing factor of (57) such that λ max ( B ) = θ 3 ( G, w ) . Thus, t he tightest pessimist ic bound is obtained for a m atrix B ∈ B 3 ( G, w ) and a nonnegativ e factor RV of (57) which p rovide the mi nimum n ormalized eigen value λ max ( B ) /µ ( RV ) . Sim ilarly , the 9 Note here t hat the main results of this work are not prov en to hold for the parallel channels instances from F igs. 4, 5 as the condition N ≥ K is violated in these cases. Figs. 4, 5 serve, howe ver , only as an exemplary visualization of the notions. 2 4 0 0.5 1 0 0.2 0.4 0.6 0.8 1 0 0.5 1 0 0.2 0.4 0.6 0.8 1 ˜ F ( r ) f k 1 ( p k 1 ) = l og(1 + | h k 1 | 2 p k 1 σ 2 k 1 ) δ ¯ F ( r ) { f k ( p k ) : P ∈ P } f k 2 ( p k 2 ) = l og(1 + | h k 2 | 2 p k 2 σ 2 k 2 ) Fig. 4. T he user dimensions of the feasible QoS set of parallel channels under the per-user power constraints ( 4b) and capacity (8) as performance function (left hand side), as well as the resulting hull ˜ F ( r ) , the ball ¯ F ( r ) and the gap δ = min f ∈ ˜ F ( r ) h f , f i − max f ∈ ¯ F ( r ) h f , f i (right hand side). W e simulated the parallel channels with K = 4 users k = 1 , 2 , 3 , 4 accessing N = 2 channels n = 1 , 2 . The channels h kn and t he v ariances σ kn were picked randomly from uniform distributions resulting in an averag e Signal-to-Noise Ratio of 6 dB. 0 0.5 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0 0.5 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 ¯ F ( r ) ˜ F ( r ) { f k ( p k ) : P ∈ P } f k 1 ( p k 1 ) = 1 − 1 1+ p k 1 | h k 1 | 2 σ 2 k 1 f k 2 ( p k 2 ) = 1 − 1 1+ p k 2 | h k 2 | 2 σ 2 k 2 δ Fig. 5. The user dimensions of the feasible QoS set of parallel channels under the per-user power constraints (4b) and mean square reliability (7) as performance function (left hand side), as well as the resulting hull ˜ F ( r ) , the ball ¯ F ( r ) and the gap δ = min f ∈ ˜ F ( r ) h f , f i − max f ∈ ¯ F ( r ) h f , f i (right hand side). W e simulated the parallel channels as in Fig. 4, but for an av erage Signal-to-Noise Rat io of 9 dB. 2 5 outer bounds in (62) are tightest for a factor RV of the particular (57), with (43), which maximizes metric µ . The outer bounds in (62 ) can be made in some sense symmetric whene ver there exists a nonnegativ e factor RV of t he matrix (57) satisfyin g (43) which has row sums not exceeding r and each col umn sum no larger t han 1 : In fact, as it is immediate from the Definition 4 that th en µ ( RV ) ≥ 1 , we can embrace the m ax-min fair performance according to min f ∈ ˜ F ( G, r ) h f , f i θ 2 ( G, w ) ≥ max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max f ∈ ¯ F ( G, r ) h f , f i θ 3 ( G, w ) , (63) where we have purely spectral dependence on the sharing graph G in t he form of functi ons (14), (17). By the t heory of matrix scaling [49], [48], t he existence of s uch particular factor depends on the patt ern of its zero entries, wh ich is shown by the following paraphrased resul t from [53]. Pr opos ition 5 ([53 ]): Let denote by RV ( L|M ) , with L ⊂ K , M ⊂ N , the s ubmatrix of RV ∈ R K × N + which is o btained by deleting all r ows k ∈ L a nd all columns n ∈ M fr om RV . Then, we have µ ( R V ) ≥ 1 if X k ∈L ¯ r k < X n ∈M ¯ c n if RV ( K \ L|M ) = 0 , RV ( L|N \ M ) 6 = 0 , X k ∈L ¯ r k = X n ∈M ¯ c n if RV ( K \ L|M ) = 0 , RV ( L|N \ M ) = 0 , (64) holds for some ( ¯ r , ¯ c ) ≤ ( r , 1 ) . Thus, the max-min fair performance satisfies (63) if ther e exists a nonne gative fa ctor RV of the matr ix (57), such that (43) and (64) for some ( ¯ r , ¯ c ) ≤ ( r , 1 ) . Recall here from Lemma 2 that any matrix (57) is a feasible matrix of some subgraph of the sharing graph. Thus, b y the above proposition, the existence of a factor ensuring µ ( RV ) ≥ 1 , depends on the existence/nonexistence of certain edges in the sharing graph. C. Ro le o f scali ngs The row and col umn sums of factors of the certain feasibl e matrix (57) of som e sharing subgraph in fluence the max-min fair performance in a specific way , whi ch we show more explicitly here. Proposition 7 in Appendix C provides a technical alternative version of the bounds from Coroll ary 3 and we sim plify it in the following. By the proof, one can readily see that the bounds from Propositio n 7 are slig htly t ighter than those from Corollary 3, at the expense of higher complexity 10 Under apriori setting y = 1 in Proposition 7 and using the definition of w ( x ) and (15), we obtain a more insi ghtful, loos ened version of the bounds: T ogether with (30), we yield then precisely min f ∈ ˜ F ( G, r ) h f , f i θ 2 ( G, w ) = max B ∈B 2 ( G, w ) min f ∈ ˜ F ( G, r ) h f , f i λ max ( B ) ≥ max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max B ∈B 3 ( G, w ) , ( x , 1 ) ∈X ( RV , r , 1 ) , V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I min k ∈K x k max f ∈ ¯ F ( G, r ) h f , f i λ max ( B ) ≥ min k ∈K x k max f ∈ ¯ F ( G, r ) h f , f i θ 3 ( G, w ) , (65) where in the last expression we can take any x satisfyi ng ( x , 1 ) ∈ X ( RV , r , 1 ) for any nonnegativ e factor RV of the matrix (57) for (43) (note here that for ˜ F ( G, r , y ) , y ∈ R N ++ , 10 Note also that the proof of Proposition 7 allows for an eve n ti ghter bound formulation which generalizes Proposition 4; set ¯ F ( G, r , y ) has to be merely replaced by ˆ F ( G, r , y ) giv en in (82 ). 2 6 defined in Proposit ion 7 we have ¯ F ( G, r , 1 ) = ¯ F ( G, r ) ). If the con straints of transm it power at any t ime in a frame are considered (e.g. either of (4a)), then one can see the same separate imp act of allowable power allocations and the channel sharing combinatorics on the bo unds (65) as in the case of (62): In terms of P ( A ) = P , A ∈ A ( G, r ) , the interval of max-min fair performance v alues is determined by the di stance between the lar gest in cluded ball ¯ F ( G, r ) and the hul l ˜ F ( G, r ) of each user dimension of the feasible QoS set. Independent ly , t he minimum achiev able ei gen values λ max ( B ) within sets (13) and (15), or the s pectral characterizations θ 2 and θ 3 , govern the bounds in terms of the chann el sharing t opology expressed by the sharing graph G . By the definition of X ( RV , r , 1 ) , it i s further evident t hat the outer lower bo und in (65) is a linear function of the minim um row scaling factor which is required to scale a nonnegativ e factor RV of (57) down, until each column su m does not exceed unit y and the vector o f row sums is n o larger than r . This leads to a conclusion that the out er bound s (65) embrace the max-min fair performance value as tightly as possib le if such a nonnegative factor R V is taken which h as componentwise smallest row su m vector relative to r . Note that, as (57) represents some feasible matrix of some sharing subgraph G ′ ⊂ G , t he row sums o f a factor of (57) are determi ned by th e channel sharing combi natorics, t hat i s, by the existence/nonexistence of certain edges in t he sharing graph (and by the vector w of s quared user performance requirements per assigned channel fraction). By the bounds (65) it can be again seen that a symm etric embracing of max-m in fair performance according to (63) is impli ed whenev er there exists a factor R V of (57), for the particular (43), which has all column sums no lar ger than unity and all ro w sums componentwise not exceeding r (see Proposi tion 5): In fact, in such case we can find a particular x such that min k ∈K x k ≥ 1 among all ( x , 1 ) ∈ X ( RV , r , 1 ) . Consider now the compl ementary simpli fication of Proposit ion 7, where x = 1 is set apriori. Then, togeth er with (30) we yield immediately min f ∈ ˜ F ( G, r ) h f , f i θ 2 ( G, w ) = max B ∈B 2 ( G, w ) min f ∈ ˜ F ( G, r ) h f , f i λ max ( B ) ≥ max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max B ∈B 3 ( G, w ) , ( 1 , y ) ∈X ( R V , r , 1 ) , V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I max f ∈ ¯ F ( G, r , y ) h y ◦ f , y ◦ f i λ max ( B ) ≥ max f ∈ ¯ F ( G, r , y ) h y ◦ f , y ◦ f i θ 3 ( G, w ) , (66) where in t he outer l owe r bou nd we can choos e any y such that ( y , 1 ) ∈ X ( RV , r , 1 ) , wit h RV as any nonnegativ e factor of (57), where (43). It is e vident from the definiti on t hat the set ¯ F ( G, r , y ) consists of performance function v alues which • are equal to, say , f ∈ R N + for all users accessing the parallel channels and, • when weighted by y i n th e sense y ◦ f , are included i n each user dimension of the feasible performance set of p arallel channel s. By analogy to ¯ F ( G, r ) , we can i nterpret the s et ¯ F ( G, r , y ) as a ki nd of largest b all which is included in each user dimensi on of set (32), but which size is measured in a weighted (by y ) Euclidean norm. Thus, the interval of max-min fair performance values (66) i s influenced by the structure of the set P ( ˆ A ) and fun ctions f k , k ∈ K , through the included weighted-norm ball ¯ F ( G, r , y ) and the hull ˜ F ( G, r ) o f any user dimensi on of set (32); the im pact i s purely via the weighted norm gap min f ∈ ˜ F ( G, r ) h f , f i − max ( 1 , y ) ∈X ( R V , r , 1 ) , ¯ F ( G, r , y ) h f , f i , 2 7 where RV is a factor of (57) for B ∈ B 3 ( G, w ) achieving the tighter lower bound, or a factor of (57) for (43) when the out er lower bound is cons idered. Recall that under constraints on transmi t po wer at any ti me in a frame, such as (4a), we hav e ¯ F ( G, r ) = ¯ F ( r ) and ˜ F ( G, r ) = ˜ F ( r ) regardless of G , and thus t he power allocations and chann el sh aring graph influence separately the numerator and denom inator of the bounds (66). In addition to the impact of channel sh aring com binatorics through t he m inimum o f λ max ( B ) withi n (13) and (15) (respecti vely , via the Lov asz function and Delsarte bound extensions θ 2 , θ 3 ), we see th at the looser lower bound in (66) is proporti onal to the weight ed squared 2 -norm of y subject to ( 1 , y ) ∈ X ( RV , r , 1 ) . Thus, the lower bound scales bilinearly with the vector of scaling factors which are needed in col umn-wise scaling of a nonnegativ e factor RV of (57) to att ain row sums and colum n sum s compo nentwise not exceeding ( r , 1 ) . Again, as (57) is a feasible matrix of a certain s ubgraph of the sharing graph, the column sums of RV are d etermined by t he channel sharing t opology and by the vector w . It can be observed t hat a factor RV which achie ves smallest possi ble column s ums is desired t o provide as t ight as possibl e ou ter interval of max-min fair performance values i n (66). The bounds (66) confirm the conclusi on that w e have the symm etric bounds (63) whenever matrix (57) satis fying (43) h as a nonnegative factor with row sum vector no l ar ger t han r and no column sum excee ding unity (in this case (63) is implied b y (66) by taking y = 1 , and we also ha ve ¯ F ( G, r , 1 ) = ¯ F ( G, r ) ). W e can finall y conclude that each of the inequaliti es propo sed so far allows us to embrace by bounds also the non restricted max-mi n fair performance of parallel channels, i.e. the max-min fair performance when no sharing graph is given apriori. For in stance, (62) imp lies min f ∈ ˜ F ( ¯ G, r ) h f , f i θ 2 ( ˆ G, w ) = max B ∈B 2 ( ˆ G, w ) min f ∈ ˜ F ( ¯ G, r ) h f , f i λ max ( B ) ≥ max ( A , P ) ∈A ( r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max B ∈B 3 ( ˆ G, w ) , V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I µ ( RV ) max f ∈ ¯ F ( ¯ G, r ) h f , f i λ max ( B ) ≥ µ ( RV ) max f ∈ ¯ F ( ¯ G, r ) h f , f i θ 3 ( ˆ G, w ) , where ˆ G is a max-min fair sharing graph, i .e. a graph induced by the max-min fair sharing policy ˆ A , su ch t hat (33) (that is, we have ˆ G = G ( ˆ A ) and ˆ A ∈ A ( ˆ G, r ) ). Clearly , th e other bounds (58), (63 ), (65 ), (66) give rise to analogous enclosi ng of graph-nonrestricted m ax-min fair performance, when a max-mi n fair sharing graph is incorporated. D. Relation to the int erfer ence channel By (66), one can recognize an interesti ng relation between max-min fair performance in parallel channels and the (weighted) throug hput opt imization in the i nterference channel considered in Section V -A. Lemma 4 and the definition of X ( RV , r , 1 ) make e vid ent that vector y in th e l owe r bounds in (66) corresponds t o a certain power allocation i n the associated in terference channel. Cor ollar y 4: Let an interfer ence channel with user population N h ave an i nterfer ence matrix (( RV ) ′ 0 ) ′ ∈ R N × N + , descri bing the int erfer ence among u sers a ccor ding to [46], which cor r esponds t o a ny nonne g ative factor of (57) such th at (43). Then, y in th e outer lower b ound (66) is a power allocation in such in terfer ence channel which maximizes the weighted thr ough put X k ∈K ¯ r k log SIR k ( z ) , z ∈ R N ++ , with addit ive logarit hmic power penalty terms ( ¯ c k − ¯ r k ) log z k , k ∈ K , and ¯ c k log z k , k ∈ N \ K , for s ome ( ¯ r , ¯ c ) ≤ ( r , 1 ) . 2 8 Precisely , by Lemma 4, the weight vectors ( ¯ r , ¯ c ) in the th roughput function collect ro w and colum n su ms obtained und er columnwise scaling of RV by y . The interesting point is that the throughpu t-optimal power allocation y i n the described i nterference channel influ- ences the pessimis tic boun ds on max-min fair performance in the related p arallel channels. For instance, the out er l owe r bound (66) b ecomes ti ghter if the taken nonnegative factor (( RV ) ′ 0 ) ′ of the matrix (57) for t he particular (43) represents such an interference matrix of the asso ciated int erference channel, which enforces higher user powe rs for optim izing the weighted throughput from the coroll ary . Recall here t hat (57) is a feasibl e matrix of some sharing subgraph G ′ ⊂ G , so t hat the candidate interference matrices of the ass ociated interference channel depend on t he channel sharing top ology in th e original parallel channels. E. Role of sharing graph cycles What is apparent in all p roposed inequalities enclosin g the max-min fair performance so far , is the d iff erence i n th e dependence on the channel sharing combinatorics between the upper and lowe r bounds. Upp er bounds depend on the giv en sharing graph G (and weight vector w ) t hrough the minimu m eigen v alue λ max ( B ) am ong matrices B ∈ B 2 ( G, w ) , respectiv ely through t he associated value of the function θ 2 . The lower bounds depend on the chann el sharing p olicy via the minimu m of λ max ( B ) among matrices B from the sm aller set B 3 ( G, w ) , respecti vely via the value which the function θ 3 assumes for G and w . By t he recent resul ts on completely positive graphs, we can, howe ver , unify the dependence on the sharing graph for a lar ge class of sharing graphs/topologi es. Pr opos ition 6: Let G = ( K , E ) be an y sha ring graph with K ≤ 4 or includi ng no odd cycles lo nger th an 4 . Then, the bounds f r om Pr o positions 4, 7 and Cor olla ry 3 and the bounds (58), (62), (63), (65), (66) ar e sa tisfied with B 2 ( G, w ) = B 3 ( G, w ) , and thus, θ 3 ( G, w ) = θ 2 ( G, w ) . The proposi tion is an immediate consequ ence of Lemma 2 and the definitions (14), (17). The key t o the above identi ty of θ 2 and θ 3 is that, for any sharing g raph G with n o m ore th an K = 4 vertices or no odd cycles longer than 4 , any feasible matrix (57) of a sharing subgraph, for any B ∈ B 2 ( G, w ) , is completely pos itive and not o nly do ubly nonnegative (see proof of Lemma 2). Proposit ion 6 i mplies that whenev er the p arallel channels are accessed by no more than K = 4 users, the value of the fun ction θ 2 assumed for the sharing graph G (and vector w ) is a s uffi cient characterization of the sharing pol icy for enclo sing the max-m in fair performance from above and from below , according to (58), (62), (63), (65) or (66). Similarly , the value θ 2 ( G, w ) , for the given sharing graph G , is a sufficient description of the channel sharing for the propos ed bounds (58 ), (62), (63), (65), (66) on max-min fair performance, when there is no odd chain of m ore than K = 4 users s uch that any two subsequent users share so me channel and t he last user shares a channel with the first one (this makes up a cycle in the sharing graph). In particul ar , we hav e s uch property when t he u sers accessing the parallel channels can be partition ed i nto no more than M = 4 groups such that no pair of us ers wit hin one group is allowed (or able) to s hare a channel; for instance, due to certain constraints on traf fic class p rocessing or hardware. The channel sharing i s represented i n such case by an M -partit e sharing graph, M = 2 , 3 , 4 , with particular examples depicted in Fig. 3. T w o parallel channel in stances of this type, and thus such th at the bounds (58), (62), (63), (65), (66) are determined solely be the function θ 2 , were presented in Examples 6 and 7: In the multi-user multi -carrier channel from Ex ample 6 certain us er constell ations are not allowed to share channels due to regulations on traffi c p rocessing, whi le in Example 7 the sharing of channels wit hin some user classes is prevented/undesired because of excessiv e diffe rence of delay times. T o summarize, we note that wh ene ver the parallel channels are shared according to any sharing graph G from Propositi on 6, the propo sed bounds enclosin g the max-mi n fair performance are determin ed by t he spectral properties of the channel sharing combinatorics 2 9 via s ome value of λ max ( B ) among matrices B ∈ B 2 ( G, w ) , respectively via the value of θ 2 assumed by graph G and vector w collecting squared user performance requi rements per assigned channel fraction. The structu ral features of the sharing topolog y ha ve impact on the boun ds th rough the metric µ , o r row-sums, or column sum s of a nonnegativ e factor o f a feasible matrix (57) of som e sharing subgraph. As far as transmi t power constraint s at any tim e (in a frame) are considered, e.g. (4a ), t he impact of the (set o f) all ow able power allocations and the curva ture o f QoS function s is decoupled from the influence of the sharing graph; it is mirrored by the gap separating the hull ˜ F ( r ) from t he largest included ball ¯ F ( r ) of each user dimension of the feasible QoS set. W e cl ose the discussion on th e max-min fair p erformance by d iscussing the i ssue of the channel ensemb le. It is evident from Corollary 1 and Propos itions 4, 7 that the max- min fa ir performance of parallel channels can be enclosed by bounds (58), (62), (63), (65), (66) whenev er the number of accessed parallel channels satisfies (42). Thi s means that th e proposed bounds apply to non-overloaded parallel channels for which t he (cardinality of) channel population exce eds the (cardinality of) user pop ulation K at least by the factor ( K + 1) / 2 . From the proofs o f Propositions 4, 7 it i s evident that such conditi on results from the use of the general nont ight b ound on cp-rank of matrix (57) implied b y Lemmas 1, 2. As a consequence, the class of parallel channels inst ances sati sfying (42) can be generalized, depending on the particular matrices B ∈ B 3 ( G, w ) achie ving the lower bounds in Proposition s 4, 7. Precisely , the bou nds (58), (62), (63), (65), (66) apply , more generally , when N ≥ max { K + 1 , φ ( λ max − 1 ( B )( w 1 2 w 1 2 ′ − B ) + I ) } is satisfied for th e corresponding matrices B ∈ B 3 ( G, w ) in the lower bounds . In oth er words, the proposed bou nds apply , m ore generally , when the channel populati on exceeds the user popul ation K b y a factor no smaller than max { K + 1 , φ } /K , wi th φ as the cp-rank of matrix (57 ), for B achieving the lower bound of interest. V I . C H A R AC T E R I Z A T I O N O F S O M E FA I R P O L I C I E S The proofs of the lower bounds from Propositions 4, 7 are constructive, that is, they contain implicit specifications of certain parallel channels policies. This allows us in t his section to derive some algo rithms for the computation of fair policies in the case of p redefined topology , or equiva lently graph, of parallel channels sharing . A fair policy is understo od here as a policy which ensures user performance of any user b e no worse than som e specified pessi mistic bound. According to Definiti on 1, a predefined sharing graph m eans predetermined b inary relatio ns cons isting i n sharing /no sharing of channels by t he sin gle user pairs. W e already explained in Section III that the p redetermination of channel sharing topology can be motivated by regulations on processing of different traffic classes, e.g. in the manner as in the multi-user multi-carrier channel from Example 6. T he fixing of a channel sharing graph can be also necessary under certain const raints on hardware and/or signal processing, similarly to the Example 7 of parallel channels. In o rder to sim plify the presentation, we assume that the p redefined sharing topol ogy results in a sharing graph with no odd cycles longer t han 4 , so that we hav e the equivalence from Proposition 6 throughout this s ection. Also, we restri ct our attention to cons traints on transmit power , e.g. by assuming i ndividually constrained user power or constrained joi nt power budget of users at any time (in a frame) according to (4a): As a con sequence, in what follows we hav e ˜ F ( G, r ) = ˜ F ( r ) and ¯ F ( G, r ) = ¯ F ( r ) regardless of the sharing graph G . It is, howe ver , easily verified th at all the algorithmi c concepts proposed in t he following are straightforwardly extendable t o the case of energy cons traints (per frame). 3 0 A. F air p olicy as ortho normal-like r epr esentation Using the con ventional optimization formulation, the problem of ensuring max-min fa irness under gi ven channel sharing topology can be written as min ( A , P ) max k ∈K − h a k , f k ( p k ) i γ k , subject to ( ( A , P ) ∈ A ( r ) × P h a k , a l i ≤ 0 , ( k , l ) / ∈ E , (67) where the set E i s such t hat K 2 \ E collects all user pairs which are not allowed to share a channel or , equivalently (Definition 1), G = ( K , E ) is a given sharing graph 11 . Con ventional optimizatio n methods (e.g. interior point methods [54]) allo w for a global solution basically in the case of con vexity of the problem. Such feature is prev ented in (67 ) sin ce a bilinear form, used in the constraint s, is not a con ve x functi on. Additionall y , we cons ider very general performance functions f k , k ∈ K , and arbitrary constrain ts on transmit power , so that a standard meth od solu tion of (67) i s expected, in general, to be only local. In this light, resorting to ef ficient com putation methods of (suboptimal) fair policies seems to be an attractiv e alternative. One poss ible method i s im plied in th e proof of Proposit ion 7 by the inequality (a refor- mulation of the first inequality in (81)) h y ◦ ˆ f , y ◦ ˆ f i λ max ( B ) ≤ min k ∈K h ˆ a k , ˆ f i 2 γ 2 k , ( ˆ A , ˆ f q h y ◦ ˆ f , y ◦ ˆ f i ) = arg min ( A , c ) max k ∈K − h a k , c i γ k subject t o ( A , c ) ∈ A ( r ) × R N + h a k , a l i ≤ 0 , ( k , l ) / ∈ E h y ◦ c , y ◦ c i ≤ 1 , (68) giv en any B ∈ B 2 ( G, w ( x )) , with map z 7→ w ( z ) , z ∈ R K ++ , defined in Propos ition 12 7. Hereby , any vectors x , y satisfying ( x , y ) ∈ X ( RV , r , 1 ) for (45) can be chosen. It is evident by (11) that the prob lem i n (68) is closely related to the computati on of an orthon ormal representation and a unit vector which achie ve t he va lue of t he Lovasz function (11) (recall the definiti on of orthonorm al representati on from Section III): In (68), the unit vector c is, howe ver , considered in weight ed norm and i s addition ally restricted to be nonnegative, while the cons traints on A are expressed in 1 -norm. The comp lexity of the problem i n (68) i s significantly reduced in relation to the orig inal problem (67). W e can restate th is problem as an instance of so-called b ilinear pro gram b y replacing the objective by some variable s and by add ing the inequalities h a k , c i /γ k − s ≤ 0 , k ∈ K , to the constraints. Although a bili near program d oes not represent a conv ex problem , th ere exists a variety of efficient methods for its global and local solut ion; w ithout giving furt her details we refer for a selection of such methods to [55], [56] and references therein. Clearly , in the o rthonormal-like representation ( ˆ A , ˆ f √ h y ◦ ˆ f , y ◦ ˆ f i ) obtained from t he bilinear program in (68 ) vector ˆ f is arbitrarily scalable by α > 0 . Due to our assumption (2), a power allo cation ˆ P ∈ P satisfyi ng f k ( ˆ p k ) = α ˆ f , k ∈ K , (69) alwa ys exists and i s t rivially constructed whenev er α > 0 i s chosen sufficiently small: Under an appropriate α , any us er k ∈ K accessing t he parallel channels simpl y assi gns on any channel n ∈ N a transmit power ˆ p k n which achieve s performance α ˆ f n and the resulti ng power allocation ˆ P remains allowable. By iterativ e increasing o f α in s uitably small steps, 11 Note, that the inequality in the second constraint in ( 67) is equi v alent to equality as nonne gati vity is implicit from A ∈ A ( r ) . 12 From the objective of the problem it is readily seen that the last inequality constraint can be replaced by equality . 3 1 we achiev e, with some accuracy , the particular largest α for wh ich (69) is yet fulfilled for some ˆ P ∈ P . Under a simple structure of the set of allowable power allocatio ns, e.g. (4a), such value of α is often computable directly/no n-iterativ ely o nce the performance functions f k , k ∈ K , are known. For such particular α we achieve the tightest lower bound in (68) among all α ˆ f i nside the set ˆ F ( r , y ) which is further smaller than t he corresponding bound for any α ˆ f ∈ ¯ F ( r , y ) (recall (82), (83)). By (the proof of) Lem ma 4, a candidate vector y i n (68) is computable as a soluti on of an unconstrained con vex problem. As a first approach we prefer , howe ver , to apply the simplification y = 1 , which imp licitly enforces x to satis fy ( x , 1 ) ∈ X ( RV , r , 1 ) . This results in the foll owing simp le procedure, for wh ich r , γ k , k ∈ K , and the set E of us er pairs not allowed to share a channel (equiv alently , sharing graph G = ( K , E ) ) are given as input parameters along with some s uitably small α , δ > 0 . Algorithm 1 : 1: F ind a shari ng matrix ˆ A and vector ˆ f fr o m (68), y = 1 , by any bilinear pro gramming method [ 55], [56]. 2: Compute a power allocation ˆ P fr om (69). 3: If ˆ P ∈ P then set α 7→ α + δ an d go to step 2, otherwise stop. W ith Propos ition 6, the us er performance of t he obtained fair po licy ( ˆ A , ˆ P ) is imm ediately e vident from the proof of Propositi on 7 (see bounds (65)). Cor ollar y 5: G iven E such that G = ( K , E ) has no odd cycles l onger than 4 , the policy ( ˆ A , ˆ P ) from Al gorithm 1 satisfies the bound s fr om Pr opositio n 7 for y = 1 , which implies min f ∈ ˜ F ( r ) h f , f i θ 2 ( G, w ) ≥ min k ∈K h ˆ a k , f k ( ˆ p k ) i 2 γ 2 k ≥ min k ∈K x k max f ∈ ¯ F ( r ) h f , f i θ 2 ( G, w ) , wher e ( x , 1 ) ∈ X ( RV , r , 1 ) subj ect to (45) an d B = arg min ¯ B ∈B 2 ( G, w ) λ max ( ¯ B ) . (70) Thus, min k ∈K h ˆ a k ,f k ( ˆ p k ) i 2 γ 2 k is at most min f ∈ ˜ F ( r ) h f , f i − min k ∈K x k max f ∈ ¯ F ( r ) h f , f i θ 2 ( G, w ) , (71) away f r om the m ax-min fai r perfor mance under given E . Fig. 6 provides an exemplary comparis on between the user performance achieved by the policy from Al gorithm 1 and the m ax-min fair performance. For t he e va luated ensemble of parallel channels (with their sh aring graphs) we observe a loss of about 20 % to t he max-min fair performance. One can also s how by simulation that such los s decreases if the diffe rences between the user channel vectors h k , k ∈ K , and the di f ferences between th e var iance ensembl es σ k n , n ∈ N , of users k ∈ K dim inish. In fact, this behavior can be recognized already from th e feature (69) of th e policy from Algo rithm 1, which means t hat the resulting p erformance function value is the sam e for all u sers. Us ing Corollary 5, t he same l imit behavior can be also deduced from Figs. 4 and 5 since in the case of simil ar channel vectors and variance ensembl es the (forms of) user dimensio ns of the feasible QoS set become similar as well and make th e 2 -norm g ap between the hul l ˜ F ( r ) and t he ball ¯ F ( r ) vanish. As can be expected con versely , un der variations between the channel vectors and variance ensembles of users becoming mo re se vere, the loss of the pol icy fr om Algorit hm 1 increases. The advantageous complexity-performance trade of f of Algorithm 1 becom es e vident when the bilinear program in (68) and th e original problem solution (67) are both computed by the same local optimization method. As shown i n Fig. 7 for some selected parallel channel 3 2 20 40 60 80 100 0 1 2 3 4 5 6 7 8 9 10 j max ( A , P ) ∈A ( G ( j ) ,N /K 1 ) ×P min k ∈K h a k ,f k ( p k ,j ) i 1 min k ∈K h ˆ a k ( j ) ,f k ( ˆ p k ( j ) ,j ) i 1 Fig. 6. The comparison of user performance under the polic y ( ˆ A , ˆ P ) from Algorithm 1 (dashed line) with the max-min fair performance (solid line), with sum-po wer constraint (4a) and with t he capacity (8) as performance function. W e simulated parallel channels with K = 4 users accessing N = 6 channels, equal user performance requirements γ k = 1 , k ∈ K , and r = N /K 1 . The sharing graphs G ( j ) , 1 ≤ j ≤ 100 , were picked randomly from all graphs with vertex set K and edges occurring independently with probability 0 . 5 . The channels h kn ( j ) and the variances σ kn ( j ) , 1 ≤ j ≤ 100 were picked randomly from uniform distributions resulting in an averag e Signal-to-Noise Ratio of 20 dB. instances (and sharing graphs), t he efficient and widely used Broyden-Fletcher -Goldfarb- Shanno (BFGS) method may be attracted by hi ghly subopt imal local opt ima of th e original nonlinear problem. On t he ot her hand, the values of the local optim a of the b ilinear program in (68) are apparently much l ess scattered, so that the same BFGS method is able t o find a good (local) solut ion (68) quite reliably . As a result, the worst user performance under policy from Algorith m 1 happens to be s uperior to the locally com puted max-mi n fair policy (under gi ven sh aring graph). As a second approach to the scaling of RV , instead of the simp lification y = 1 we can find a scalar s caling so that ( 1 , y 1 ) ∈ X ( RV , r , 1 ) for some y > 0 . In this case, w ( x ) reduces to w defined as (21) and thus matrix B , which giv es rise to the nonnegative factorization (45), needs t o s atisfy B ∈ B 2 ( G, w ) . In the best case, a particular matrix (70 ) is d esired. Since the constraints d etermining the set (13 ) are linear , the problem i n (70) corresponds to eigenv alue minimizati on over a polyh edron, which is a canonical probl em in optimizati on theory and a variety of efficient soluti on methods exists [54]. For th e nonnegative factorization of any giv en B ∈ B 2 ( G, w ) , or the particular (70), we us e one of the two celebrated method s which are proposed in [57] and are further extended and analyzed e.g. in [58], [59]. Precisely , for any m ∈ N , we apply th e particul ar form ( V ( m + 1)) k n = ( V ( m )) k n ( 1 ′ V ( m )) n X l ∈K ( V ( m )) ln ( λ max − 1 ( B )( w 1 2 w 1 2 ′ − B ) + I ) k l ( V ( m ) V ′ ( m )) k l , ( k , n ) ∈ K×N , (72) of the factorization iteration from Theorem 2 in [57]. The s equence RV ( m ) , m ∈ N , obtained by (72) con ver ges monoto nically to a m atrix RV w hich achieve s a st ationary point of the generalized Kullback-Leibler (KL) diver gence bet ween RV V ′ R and (57) (for the definition of t his diver gence and further di scussion we refer t o [57]). The minimizatio n of the generalized KL diver gence between a matrix and its factorization is an int ricate problem with mult iple lo cal m inima, so that R V V ′ R obtained from (72) can happen t o remain at a nonzero, but relativ ely sm all, generalized KL diver gence to (57). For this reason, we can resort also to al ternativ e factorization iteration s, such as the gradient d escent meth od, wh ich 3 3 0 2 4 6 8 10 −10 −9 −8 −7 −6 −5 −4 −3 −2 −1 0 min k ∈K −h a k ( j ) ,f k ( p k ,j ) i 1 min k ∈K −h ˆ a k ( j ) ,f k ( ˆ p k ( j ) ,j ) i 1 j Fig. 7. The comparison of user performance under the policy ( ˆ A , ˆ P ) from Algorithm 1 using the BFGS method in step 1 (dashed line), and under policy ( A , P ) as a local BF GS solution to problem (67) (solid line), wit h sum-power constraint (4a) and with the capacity (8) as performance function. W e simulated t he parallel channels as in Fig. 6, but for K = 3 , N = 4 and an averag e Signal-to-Noise Ratio of 10 dB. seem, howe ver , t o be inferior to the methods from [57 ] in terms of complexity-con ver gence trade o f f [57 ], [59]. The above discussion leads to the following second procedure w hich uses r , γ k , k ∈ K , and E as input d ata and some suffic iently sm all parameters α, δ > 0 . Algorithm 2 : 1: Compute a matrix (70) by any con vex eigen value minimizatio n method [54]. 2: Compute V by the iteration (72). 3: Compute the lar gest solution y > 0 of the inequalities y 1 ′ RV ≤ 1 ′ , y RV 1 ≤ r . 4: F ind a sharing ma trix ˆ A and vector ˆ f fr om (68), y = y 1 , by any bilinear pro gramming method [ 55], [56]. 5: Compute a power allocation ˆ P fr om (69). 6: If ˆ P ∈ P then set α 7→ α + δ an d go to step 5, otherwise stop. By Proposition 6, Theorem 2 in [57] and the proof of Propositio n 7 we have the following result on the user performance u nder the fair poli cy ( ˆ A , ˆ P ) from Algorit hm 2. Cor ollar y 6: A ssume the generalized KL diver gence between (57) and R V , with V com- puted i n step 3 of Algori thm 2, be zer o and l et E such that G = ( K , E ) has no odd cycles longer than 4 be gi ven. Then, the policy ( ˆ A , ˆ P ) fr om Algor ithm 2 sa tisfies the bounds fr om Pr opos ition 7 for y = y 1 , with y computed in step 3 , which impl ies min f ∈ ˜ F ( r ) h f , f i θ 2 ( G, w ) ≥ min k ∈K h ˆ a k , f k ( ˆ p k ) i 2 γ 2 k ≥ max f ∈ ¯ F ( r ,y 1 ) h y f , y f i θ 2 ( G, w ) . (73) Thus, min k ∈K h ˆ a k ,f k ( ˆ p k ) i 2 γ 2 k is at most min f ∈ ˜ F ( r ) h f , f i − max f ∈ ¯ F ( r ,y 1 ) h y f , y f i θ 2 ( G, w ) (74) away f r om the m ax-min fai r perfor mance under given E . Obviously , by adding more technicality , Corollary 6 can be extended to the case when t he factorization iteration in step 3 happens to con ver ge on ly locally , i.e., when the KL div er gence between RV V ′ R and (57) does not vanish. 3 4 The p erformance and complexity-performance trade off of the poli cy from Algorit hm 2 beha ves, essentially , quite identically to the policy from Algorithm 2 (see Figs . 6, 7). The potential nonzero KL dive r gence remaining after iteration by (72) is hereby hardly visible. B. F air p olicy fr om fact orization T o summ arize so far , by th e Algorithm s 1 , 2, the sol ution of the original i ntricate problem (67) is replaced by som e algebraic operations and the sol ution of canonical, m ore effi ciently solvable optim ization problems: The sharing matrix i s obtained directly from the solution of a bilinear program, while the power allocation resul ts from s imple scaling (Algo rithm 1), respectively , from the so lution of eigen value minimi zation, nonnegative factorization and scaling (Algorithm 2). As the price payed for this sim plification, the resulting fair parallel channels poli cies are subo ptimal, but achieve the worst u ser performance withi n the dis tances (71) and (74), respectiv ely , from the optimum under given sh aring graph G . The proof of Proposit ion 7 implies, howe ver , that a bilin ear program can be further exchanged here by nonnegati ve factorization and a solu tion of a simple equatio n sy stem. The key step of the proof which gives rise to such alternative algorithm is the equal ity (see (80)) h y ◦ ˆ f , y ◦ ˆ f i λ max ( B ) = h ˆ a k , ˆ f i 2 γ 2 k , k ∈ K , B ∈ B 2 ( G, w ( z )) , (75) for the giv en sharing graph G , for any B ∈ B 2 ( G, w ( z )) , for map x 7→ w ( x ) , x ∈ R K ++ , defined i n Proposition 7 and for some z ∈ R K ++ , ˆ A ∈ A ( G, r ) , ˆ f ∈ R N + related as follows. • Any sharing matrix ˆ A results from scaling of a factor RV , su ch that (45), by a scaling ( Z , Y ) with ( z , y ) ∈ X ( RV , r , 1 ) , where Z 1 = z , Y 1 = y . • Fa ctor RV can be split as (49), w = w ( z ) , with X = ( x 1 , . . . , x K ) ′ as a factor of I − λ max − 1 ( B ) B , where C = ( c , . . . , c ) ′ ∈ R K × N + is orth ogonal according to (47) and determines ˆ f as y ◦ ˆ f √ h y ◦ ˆ f , y ◦ ˆ f i = c . Again, in the best case, a nonnegati ve factor RV of a particular matrix (70), w = w ( z ) , obtained from canonical eigen value minimizatio n [54], is desired. As above, such factor is computable by the version (72) of a factorization m ethod from [57]. Once a factor RV is computed, vector ˆ f follows as a s olution of a simple vector equ ation. Precisely , combining (49) wit h the definition y ◦ ˆ f √ h y ◦ ˆ f , y ◦ ˆ f i = c and t he orthog onality conditio n (47) shows th at ˆ f is a s olution to the equation V y ◦ f p h y ◦ f , y ◦ f i − λ max − 1 ( B ) W 1 2 ( z ) = 0 , f ∈ R N + , (76) where th e definit ion W 1 2 ( z ) = d iag ( W 1 2 ( z )) , ( W 1 2 ( z )) k k = w 1 2 ( z ) k , k ∈ K , is obvious . W e are free t o solve the equation (76) by any a va ilable numerical m ethod; we refer here to [60] for a wide selectio n of such m ethods. Any sol ution to (76) is arbitrarily scalable by a positive α and from the discussio n in Section VI-A it is clear how a power allocati on ˆ P ∈ P sati sfying (69) is constructed for a suffi ciently small α . Again, by gradual i ncreasing the particular largest α is found, for which (69) y et holds for s ome allowa ble powe r allocation ˆ P ∈ P . For such an α , α ˆ f achiev es t he value of the left hand s ide of (75), which is further no smaller than the corresponding m aximum value among all α ˆ f ∈ ¯ F ( r , y ) . As a sim plified approach to th e scaling of RV , w e find a scalar scaling whi ch yields ( 1 , y 1 ) ∈ X ( RV , r , 1 ) , for som e y > 0 . Since then w ( z ) reduces to w give n by (21) and matrices B ∈ B 2 ( G, w ) hav e to be considered, the above d iscussion results in the following procedure (as above, E , r , and γ k , k ∈ K , together with sui tably small α , δ > 0 are give n as input parameters). Algorithm 3 : 3 5 20 40 60 80 100 0 1 2 3 4 5 6 7 8 max ( A , P ) ∈A ( G ( j ) ,N /K 1 ) ×P min k ∈K h a k ,f k ( p k ,j ) i 1 min k ∈K h ˆ a k ( j ) ,f k ( ˆ p k ( j ) ,j ) i 1 j Fig. 8. The comparison of user performance under the polic y ( ˆ A , ˆ P ) from Algorithm 3 (dashed line) with the max-min fair performance (solid line), with sum-po wer constraint (4a) and with t he capacity (8) as performance function. W e simulated the parallel channels as in Fig. 6, but for K = 6 and N = 7 . 1: Compu te a matr ix (70) by any con ve x ei gen value mini mization method [54]. 2: Compu te V by the iteration (72). 3: Compu te th e sha ring mat rix ˆ A = y RV , for t he la r gest s olution y > 0 of the inequaliti es y 1 ′ RV ≤ 1 , y RV 1 ≤ r . 4: Compu te a sol ution ˆ f to equation (76) by any numerical metho d [60]. 5: Compu te a power allocati on ˆ P fr om (69). 6: If ˆ P ∈ P then set α 7→ α + δ an d go to step 5, otherwise stop. According to Proposition 6, Theorem 2 in [57] and Propos ition 7, the fair poli cy ( ˆ A , ˆ P ) computed by Algorith m 3 achie ves the following user performance. Cor ollar y 7: A ssume the generalized KL diver gence between (57) and R V , with V com- puted i n step 2 of Algori thm 3, be zer o and l et E such that G = ( K , E ) has no odd cycles longer than 4 be given. Then, th e policy ( ˆ A , ˆ P ) fr om Algorithm 3 sati sfies the bounds fr om Pr oposi tion 7 for y = y 1 , with y computed in step 3 , which imp lies (73). Thus, min k ∈K h ˆ a k ,f k ( ˆ p k ) i 2 γ 2 k is at most (74) away fr om the max-min f air per formance und er given E . Fig. 8 shows an exemplary comp arison o f user performance achie ved under the policy from Algorithm 3 and th e max-min fair performance. It is evident that the average loss to the max-min fair performance is abo ut 23 % for the simulated ins tances of parallel channels and their sharing graphs (th us, the potential nonzero KL d iv er gence remaining after iteration (72) does hardly manifest it self in a gap to th e performance of Algorithm 1). By the feature (69), or by Corollary 7 and th e Figs. 4, 5, we recognize again th at such loss ev olves analogous ly as i n the case of Algorit hms 1 and 2; i t decreases with the user channel vectors and user noise va riance ensembles con ver ging to common values, and increases with the corresponding var iations becomi ng stron ger . V I I . C O N C L U S I O N S This work allows for several novel conclusions on the b eha vior of the max-min fair perfor- mance in parallel channels, understoo d as the m aximum attainable worst user performance. W e assumed a very general performance function which is subject to the m ax-min fairness criterion; i t includes t he most celebrated functio ns in com munications and i nformation theory (capacity , s pectral efficienc y , decoder reliabil ity) as very special cases. W e succeeded in 3 6 embracing the max-mi n fair performance by optim istic and pess imistic b ounds which show , under constraints on transmit po wer , the same behavior as functions of the channel sharing topology . This lead to the fi rst central conclusion that the max-min f air performance in pa rallel channels beha ves a s a special e xtension of the Lov asz function, or Delsarte bound, of a certain graph G (the sharing graph) characterizing the combin atorial topology of chann el sharing among t he u sers. An essential rol e i s played hereby by the minim um spectral characterization λ max ( B ) achieva ble withi n certain G -dependent sets B 2 ( G, w ) , B 3 ( G, w ) wi th vector w as a parameterizing vector determined by th e user performance requirements. When s uch sp ectral characterization of the channel sharing topology is o btained, the characterization of t he real- valued subproblem of power allocatio n t o users and sh ared channel s by a simpl e 2 -norm distance is suf ficient for embracing the max-min fa ir performance by the proposed bounds: The i nfluence o f all properties of the allowable power allocations and all anal ytic features of the u sed QoS functions on th e max-m in fair performance is accumulated in a sim ple 2 -norm gap between a certain hull and a certain includ ed ball of th e feasible QoS s et of the parallel channels. Our results sh owe d also t hat a key rol e is p layed by the existence/nonexistence of cycles i n the sharing graph, interpretable as clos ed chains of users su ch that any two subsequent users in such a chain share a channel: W e showed th at under nonexistence of long odd chains of such t ype, the m ax-min fair performance is characterized by the minim um achiev able λ max ( B ) in the specific s et B 2 ( G, w ) as a function of the channel sharing topol ogy (and the gap between the proposed bounds i s equal precisely to the 2 -no rm gap between s ome hul l and some i ncluded ball o f the feasible QoS set). As a byproduct of our calculations, we also il lustrated a relation of t he max-min fair performance in parallel channel t o the graph capacity and in dependence number of th e graph describing the channel sharing topology . The constructiv e proofs of our bounds allowed furth er for th e formulation of t hree novel power and ti me allocation algorithm s for parallel channels with predefined channel sharing topologies (which is the case, e.g., under certain regulations /constraints on QoS class pro- cessing). The algorithms offer a ni ce performance-complexity trade o f f and incorporate some surprising techniques, such as nonnegati ve factorization. A P P E N D I X A. Doubly nonne gative and completely positive matri ces Definition 5 ([44]): A matrix X ∈ R K × K is said to be doubly nonne gat ive, and we write X ∈ D K , if D ∈ R K × K + and D 0 . In simp le words, a matrix X ∈ D K is nonnegativ e in th e con ventional order ≥ on R K × K and in the partial order on the set of symmetric matrices in R K × K . Definition 6 ([44]): A matrix X ∈ R K × K is said to be complet ely positive, and we write X ∈ P K , if ther e exists so me N ∈ N such that X = Y Y ′ for s ome Y ∈ R K × N + . (77) The smallest number N fo r which we ha ve (77) is r eferr ed to as the cp-rank of X and is denoted as N = φ ( X ) . Condition (77) is frequently used i n its equiv alent form as X = N X i =1 y i y ′ i for s ome y i ∈ R K + , 1 ≤ i ≤ N , where Y = ( y 1 , . . . , y N ) is assumed. By Definiti on 6, it is readily seen that X ∈ P K implies X ∈ D K ( P K ⊂ D K ). By the celebrated result from [44] it is further known th at P K = D K whenev er K ≤ 4 , while otherwise examples of m atrices X ∈ D K such that X / ∈ P K can be constructed. 3 7 B. Association schemes From th e view of graph t heory , the m ost accessible definiti on of an association s cheme is based on the notion of edge coloring of a graph, as a partition of its edge set into vertex- disjoint edge classes. Precisely , an edge M -coloring of a graph G = ( K , E ) corresponds to the tuple ( K , {E i } M i =1 ) , where ( k , l ) , ( m, n ) ∈ E i implies th at k 6 = m and l 6 = n [30]. Definition 7 ([61]): An association scheme wit h M asso ciate cla sses o n a set K is an edge M -coloring of a (complet e) graph G = ( K , K 2 ) such that i.) for any 1 ≤ k , l , m ≤ M ther e exists so called intersection number p m k l ∈ N such that p m k l = | { n ∈ K : ( i, n ) ∈ E k , ( n, j ) ∈ E l }| whenever ( i, j ) ∈ E m , ii.) for any 1 ≤ k ≤ M ther e exists q k ∈ N s uch that q k = |{ ( i, j ) ∈ E k : i = n }| f or any n ∈ K . iii.) E k 6 = ø , 1 ≤ k ≤ M . Definition 8: Given an association scheme ( K , {E i } M i =1 ) and a ny M ⊂ { 1 , . . . , M } , we r efer to L ⊂ K as an M -clique of the association scheme if i, j ∈ L , i 6 = j , implies ( i, j ) ∈ ∪ m ∈M E m . For any asso ciation schem e ( K , {E i } M i =1 ) and any it s M -clique L ⊂ K , the unweighted Delsarte number can be formulated as the map (( K , {E i } M i =1 ) , L , M ) 7→ m ax a ∈A 1 (( K , {E i } M i =1 ) , L , M ): 1+ h a , σ i≥ 0 1 + h a , 1 i , (78) where A 1 (( K , {E i } M i =1 ) , L , M ) denotes the s et of so-called inner dis tributions of the M - clique L and σ = ( σ 1 , . . . , σ M ) ∈ R M collects especially no rmalized eigen values of th e adjacency matrices of graphs ( K , E m ) , 1 ≤ m ≤ M , having a common eigen vector [39]. C. Ad ditional b ound fo rmulations Cor ollar y 8: G iven N ≥ K , any G = ( K , E ) an d any ( A , P ) ∈ A ( G, r ) × P ( A ) , r ∈ R K ++ , we have min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≤ min f ∈ R N + h f , f i θ i ( G ( A ) , w ( f )) , i = 0 , 1 , 2 , (79) wher e f 7→ w ( f ) , f ∈ R N + , is such th at, for any k ∈ K , w k ( f ) ≤ γ 2 k h a k , f i 2 r 2 k h a k , f k ( p k ) i 2 if i = 1 , w k ( f ) = γ 2 k h a k , f i 2 r 2 k h a k , f k ( p k ) i 2 if i = 0 , 2 . Pr oof : The proof i s a sli ght modification of th e proof of Proposition 3. For any A ∈ A ( G, r ) , f ∈ R N + and P ∈ P ( A ) such that h a k , f k ( p k ) i 6 = 0 , k ∈ K (which b y o ur assumption s on P ( A ) and f k , k ∈ K , exists), let Z = ( z 1 , . . . , z K ) ′ ∈ R K × N , be give n as z k = s w k ( f ) h f , f i f − γ k p h f , f i r k h a k , f k ( p k ) i a k , k ∈ K . Then, h z k , z l i = p w k ( f ) w l ( f ) − γ k p w l ( f ) h a k , f i r k h a k , f k ( p k ) i − γ l p w k ( f ) h a l , f i r l h a l , f l ( p l ) i + γ k γ l h f , f ih a k , a l i r k r l h a k , f k ( p k ) ih a l , f l ( p l ) i , for any k , l ∈ K , so that by th e definiti on o f w in the case i = 0 , 2 we yi eld again (24), with w = w ( f ) and with h z k , z k i = − w k ( f ) + γ 2 k h a k , a k ih f , f i r 2 k h a k ,f k ( p k ) i 2 in particul ar , whi le by Definition 1 again (25) for w = w ( f ) is sati sfied. In the case o f i = 1 , t he definition of w impl ies h z k , z k i ≤ − w k ( f ) + γ 2 k h a k , a k ih f , f i r 2 k h a k ,f k ( p k ) i 2 and together with Definition 1 also h z k , z l i ≤ − p w k ( f ) w l ( f ) , ( k , l ) / ∈ E , k 6 = l . 3 8 Thus, g iv en i = 0 , 2 , we can write (26) with ¯ A = A and w = w ( f ) by the definition (13), while − B Z Z ′ − h f , f i G ( A ) i s satisfied for s ome B ∈ B 1 ( G, w ( f )) in the case i = 1 . In either case (27 ) i s implied and u p from (27) the proo f g oes as the proof of Proposi tion 3. Pr opos ition 7: Given any G = ( K , E ) and r ∈ R K ++ , we ha ve max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max B ∈B 3 ( G, w ( x )) ( x , y ) ∈X ( R V , r , 1 ) , V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I max f ∈ ¯ F ( G, r , y ) h y ◦ f , y ◦ f i λ max ( B ) , wher e x 7→ w ( x ) , x ∈ R K ++ , is such th at w k ( x k ) = γ 2 k ( x k r k ) 2 , k ∈ K , wher e N ∈ N satisfies (42), and wher e, given ˆ A defined as in Cor ollary 1 , we defined ¯ F ( G, r , y ) = { f ∈ R N + : h y ◦ ¯ f , y ◦ ¯ f i ≤ h y ◦ f , y ◦ f i ⇒ ¯ f = f k ( p k ) , k ∈ K , for some P ∈ P ( ˆ A ) } , y ∈ R N ++ . Mor eover , given a particul ar B = a rg min ¯ B ∈B 3 ( G, w ( x )) λ max ( ¯ B ) , this further imp lies max ( A , P ) ∈A ( G, r ) ×P ( A ) min k ∈K h a k , f k ( p k ) i 2 γ 2 k ≥ max ( x , y ) ∈X ( R V , r , 1 ) , V ∈ R K × N + : V V ′ = λ max − 1 ( B )( w 1 2 w 1 2 ′ − B )+ I max f ∈ ¯ F ( G, r , y ) h y ◦ f , y ◦ f i θ 3 ( B , w ( x )) . Pr oof : Under the substi tution w = w ( x ) , w ith an arbi trary x ∈ R K ++ , the proof g oes exactly as the p roof of Propositi on 4 up to t he i mplication (52) for any f ∈ R N + such that f √ h f , f i = c is sati sfied for the particular c from (50). Ag ain, by Lemma 3, it follows that we can always find some ( z , y ) ∈ X ( RV , r , 1 ) such that (45), w = w ( x ) , and thus we have U ∈ A ( G, r ) for U = Z RV Y with Z 1 = z , Y 1 = y . Writing now f = y ◦ ¯ f , for some ¯ f ∈ R N + , and U = ( u 1 , . . . , u K ) ′ and setting x = z , we have by the definitio n of the map x 7→ w ( x ) , x ∈ R K ++ , that w k ( z k ) h v k , y ◦ ¯ f i 2 = γ 2 k ( P n ∈N z k r k ( v k ) n y n ¯ f n ) 2 = γ 2 k ( P n ∈N ( u k ) n ¯ f n ) 2 = γ 2 k h u k , ¯ f i 2 , k ∈ K . W ith (52), w = w ( z ) , this yields λ max ( B ) h y ◦ ¯ f , y ◦ ¯ f i = γ 2 k h u k , ¯ f i 2 , k ∈ K , (80 ) for any ¯ f ∈ R N + such that y ◦ ¯ f √ h y ◦ ¯ f , y ◦ ¯ f i = c is satisfied for c from (50). By our assum ption (2) and the assumpt ions on f k , k ∈ K , we can alwa ys find a particular ¯ f s uch that ¯ f = f k ( p k ) , k ∈ K , for an arbitrary A ∈ A ( G, r ) and some P ∈ P ( A ) , so t hat it is i mplied then with (80) that λ max ( B ) ≥ min ( A , f ) ∈A ( G, r ) × R N + max k ∈K γ 2 k h y ◦ f , y ◦ f i h a k , f i 2 = min A ∈A ( G, r ) , f ∈ R N + : f = f k ( p k ) ,k ∈K , for some P ∈P ( ˆ A ) max k ∈K γ 2 k h y ◦ f , y ◦ f i h a k , f i 2 = min A ∈A ( G, r ) max k ∈K γ 2 k h y ◦ ˆ f , y ◦ ˆ f i h a k , ˆ f i 2 (81) 3 9 for any ˆ f ∈ ˆ F ( G, r , y ) . Hereby , we defined (as a straight generalizatio n of ˆ F ( G, r ) ) ˆ F ( G, r , y ) = { f ∈ R N + : f = f k ( p k ) , k ∈ K , for some P ∈ P ( ˆ A ) , f = arg max ¯ f ∈ R N + max ¯ A ∈A ( G, r ) min k ∈K h ¯ a k , ¯ f i 2 γ 2 k h y ◦ ¯ f , y ◦ ¯ f i } . (82) Thus, i t follows finally that λ max ( B ) h y ◦ f , y ◦ f i ≥ min ( A , P ) ∈A ( G, r ) ×P ( ˆ A ) max k ∈K γ 2 k h a k , f k ( p k ) i 2 , for any B ∈ B 3 ( G, w ( z )) , any V such that (45), w = w ( z ) , any y satisfying ( z , y ) ∈ X ( RV , r , 1 ) and N ≥ max { K + 1 , φ ( λ max − 1 ( B )( w 1 2 ( z ) w 1 2 ( z ) ′ − B ) + I ) } . Hereby , by Lemmas 1, 2, the l ast conditi on is impl ied by N ≥ K ( K + 1 ) / 2 and addit ionally , along exactly the same lin es as in the proof of Corollary 3, it is readily shown that h y ◦ f , y ◦ f i ≤ max ¯ f ∈ ˆ F ( G, r , y ) h y ◦ ¯ f , y ◦ ¯ f i , f ∈ ¯ F ( G, r , y ) . (83) This com pletes the proof of the first inequalit y of the proposition, while the second in- equality i s obtain ed b y taking a particular ¯ B with λ max ( ¯ B ) = max B ∈B 3 ( G, w ( z )) λ max ( B ) = θ 3 ( G, w ( z )) . R E F E R E N C E S [1] L. T assiulas and S. Sarkar , “Maxmin Fair S cheduling in W ireless Networks, ” Pr oc. IE EE Confer ence on Computer Communications (Infocom) , Jun 2002. [2] B. Radunovic and J.-Y . L . Boudec, “W hy Max-min F airness I s Not Suitable F or Multi-Hop Wi reless Networks, ” Ecole Polytechnique Federale de Lausanne (EPFL ), Lausanne, Report, 2000. [3] D. K. Foley , “Resource Allocation and the Public Sector , ” Y ale Economic Essays , vol. 7, 1967. [4] H. R. V arian, “Equity , En vy , and Efficienc y , ” J ournal of Economic Theory , vol. 9, pp. 63–91, 1974. [5] H. Boche, M. Wiczano wski, and S. S tanczak, “Unifying View on Min-Max Fairness, Max-Min F airness, and Utility Optimization in Cellular Networks, ” Eurasip Jou rnal on W ireless Communications and Networking , vol. 2007, p. ID 34869, 2007. [6] A. Lozano, A. M. Tulino, and S. V erdu, “Optimum Power Allocation for Parallel Gaussian Channels With Arbitrary Input Distributions, ” IEEE T ransa ctions on Information Theory , vol. 52(7), pp. 3033–3051, Jul 2006. [7] D. P . Palomar and J. R. Fonollosa, “Practical algorithms for a family of waterfilling solutions, ” IEEE Tr ansactions on Signal Pr ocessing , vol. 53(2), pp. 686–695 , Feb 2005. [8] G. D. Forney , Jr . and G. Ungerboeck, “Modulation and Coding for Linear Gaussian Channels, ” IEEE Tr ansactions on Information Theory , vol. 44(6), pp. 2384–2415, Oct 1998. [9] J. A. C. Bingham, P . S. Chow , and J. M. Cioffi, “ A practical discrete multitone transceiv er loading algorithm for data transmission ov er spectrally shaped channels, ” IEEE T ransa ctions on Communications , vol. 43(2), pp. 773–775, Feb 1995. [10] A. Lozano, A . M. Tu lino, and S. V erdu, “Mercury/wa terfilling for fixed wireless OF DM systems, ” in Pr oc. IEEE Radio and W ireless Symp. (RWS’06) , S an Diego, CA, Jan 2006, pp. 211–214 . [11] I. T oufik and R. Knopp, “Multiuser Channel Allocation Algorithms Achiev ing Hard Fairness, ” in Proc. IEEE Global T eleco mmunications Confer ence (Globecom) , 2004. [12] M. Wicz ano wski, H. Boche, and S . Stanczak, “Characterization of Optimal Resource Assignments in the Framework of Blocking System T heory , ” in Pr oc. I EEE International Symposium on Information Theory and its Applications (ISIT A) , Seoul, K orea, Nov 2006. [13] —— , “Power Allocation and Resource Assi gnment in the View of Blocking and Antiblocking Polyhedra, ” in Pr oc. IEEE Information Theory W orkshop (ITW) , Chengdou, China, Oct 2006. [14] Y . J. Zhang and K. B . Lataief, “ Adapti ve Resource Allocation for Multiaccess MIMO/OFDM Systems with Matched Filtering, ” IEEE T ran sactions on Communications , vol. 53(11), Nov 2005. [15] D. R . Fulkerson, Blocking P olyhedr a , ser . Gr aph t heory and it s applications. Acad emic Press, 1970, pp. 93–112. [16] —— , “ Antiblocking Polyhedra, ” Jou rnal on Combinatorial Theory , Series B , vol. 12, pp. 50–71, 1972. [17] L. Lov asz, “On the S hannon C apacity of a Gr aph, ” I EEE Tr ansaction s on I nformation Theory , vol. 25(1), pp. 1–7, 1979. [18] M. Gr ¨ otschel, L. Lov asz, and A. Shrijver , “Relaxations of Vert ex Packing, ” Jou rnal of Combinatorial Theory , Series B , vol. 40, pp. 330–343, 1986. [19] J. K ¨ orner and A. Orlit sky , “Zero-error information theory , ” IEEE T ransactions on Information T heory , vol. 44(6), pp. 2207–2 229, Oct 1998. [20] X. Qin and R. B erry , “Dist ributed power allocation and scheduling for parallel channel wir eless networks, ” in Pr oc. International Symposium on Modeling and Optimization in Mobile, A d Hoc, and W ir eless Networks ( WIOPT) , 2005, pp. 77–85. 4 0 [21] C. Y . W ong, R. S. Cheng, K. B. Letaief, and R. D. Murch, “Multiuser OF DM with Adapti ve Subcarrier , Bit, and Power Allocation, ” IEEE Jou rnal on Selected Areas in Communications , vol. 17(10), pp. 1747–1758, Oct 1999. [22] H. B ¨ olcskei, “MIMO-OFDM Wireless Systems: Basics, P erspecti ves, and Challenges, ” IEEE W ire less Communica- tions , pp. 31–37, Aug 2006. [23] 3rd Generation Partnership Project (3GPP ), “Evolv ed Univ ersal Terrestrial Radio Access (E-UTRA) and E volv ed Univ ersal Terrestri al Radio Access Network (E-UT RAN) (Release 8), ” 3GPP Support Office, V albonne, France, T echnical Specification, 2007. [24] —— , “Evolved Universa l Terrestrial Radio Access ( E-UTRA); Base St ation (BS) radio t ransmission and reception (release 8), ” 3GPP Support Office, V albonne, F rance, T echnical S pecification, 2008. [25] T . M. Cov er , “Comments on Br oadcast Channels, ” IE EE T ransactions on Information Theory , vol. 44(6), pp. 2524– 2530, Oct 1998. [26] N. Jindal and A. Goldsmith, “Capacity and Optimal Power Allocation for Fading Broadcast Channels With Minimum Rates, ” IEEE T ransactions on Information T heory , vol. 49(11), pp. 2895–290 9, Nov 2003. [27] D. N. Tse, “Optimal P o wer Al location ov er Parallel Gaussian Broadcast Channels, ” in Pr oc. IE EE International Symposium on Information Theory (ISIT) , 1997, p. 27. [28] D. Tse and P . V i swanath, Fundamentals of Wireless Communication . Cambridge: Cambridge Unive rsity Pr ess, 200 5. [29] S . V erdu, Multiuser Detection . New Y ork: Cambridge University Press, 1998. [30] B. B ollobas, Modern Graph Theory . Ne w Y ork : Springer-V erlag, 1998. [31] D. E . Knuth, “The Sandwich Theorem, ” E lectr onic Journ al of Combinatorics , vol. 1, 1994. [32] D. M. Cvetko vic, M. Doob, and H. Sachs, Spectra of Graphs . New Y o rk: A cademic P ress, 1980. [33] J. H. Drew , C. R. Johnson, and R. Loewy , “Completely Positiv e Matrices Associated with m -Matrices, ” Linear and Multilinear Algebra , vol. 37, pp. 303–310, 1994. [34] N. K ogan and A. Berman, “Characterization of completely positiv e graphs, ” Discr ete Mathematics , vol. 114, pp. 297–30 4, 1993. [35] A. Berman and D. Hershko witz, “Combinatorial Results on Completely Positive Matrices, ” Linear Al geb ra and its Applications , vol. 95, pp. 111–125, 1987. [36] C. Xu, “Nearly Completely Positiv e Graphs, ” Applicable Al gebr a in Engineering Communication and Computing , vol. 13, pp. 1–8, 2002. [37] C. J. L uz and A. Schrijver , “ A Conv ex Quadratic Characterization of the Lov asz Theta Number , ” SIAM Journal on Discr et e Mathematics , vol. 19(2), pp. 382–387, 1979. [38] A. S chrijver , “ A Comparison of t he Delsarte and Lov asz Bounds, ” IEEE T ransactions on Information Theory , vol. 25(4), pp. 425–429, Jul 1979. [39] P . Delsarte, “ An algebraic approach to the association schemes in coding theory , ” Philips Res. Reps. Suppl. , vol. 10, 1973. [40] F . Chung and R. M. Richardson, W eighted Laplacians and the Sigma Function of a Graph , ser . Quantum Graphs And Their Applications - Contemporary Mathematics. American Mathematical S ociety , 2006, ch. 7, pp. 93–108. [41] A. Galtman, “Spectral Characterizations of the L ov asz Number and the Delsarte Number of a Graph, ” Journal of Algebr aic Combinatorics , vol. 12, pp. 131–143, 2000. [42] R. J. McEliece, E. R. Rodemilch, and H. C . Rumsey Jr ., “The Lov asz Bound and Some Generalizations, ” Journa l of Combinatorics Information & System Sciences , vol. 3(3), pp. 134–152, 1978. [43] C. R. Johnson and M. Newman , “ A note on Cospectral Graphs, ” J ournal of Combinatorial T heory , Series B , vol. 28, pp. 96–103, 1980. [44] L. J. Gray and D. G. W ilson, “Nonn egati ve factorization o f positiv e semidefinite nonneg ativ e matrices, ” Linear Algebra and its Applications , vol. 31, pp. 119–127, 1980. [45] A. Berman, Completely positive graphs , ser . Quantum Graphs And Their Applications - Contemporary Mathematics. American Mathematical Society , 2006, ch. 7, pp. 93–108. [46] S . Stanczak, M. Wiczano wski, and H. Boche, R esour ce Allocation in Wir eless N etworks . New Y ork: Lecture Notes in Computer Science, Springer-V erlag, 2006. [47] A. W . Marshall and I. Olkin, “Scaling of matrices to achie ve spec ified row and column sum s, ” Numerische Mathematik , vol. 12, pp. 83–90, 1968. [48] U. G. Rothblum and H. Schneider , “Scalings of Matrices Which Have Prescribed Row Sums and Column Sums via Optimization, ” Linear Algebra and its Applications , vol. 114, pp. 737–765, 1989. [49] D. London, “On matrices with a doubly stochastic pattern, ” Journal of Mathematical Analysis and Applications , vol. 34, pp. 648–652, 1971. [50] M. S chubert and H. Boche, QoS-Based Resour ce Allocation and Transceiver Optimization , ser . Foundations and T rends i n Communications and Information Theory . Now Publishers, 2005, vol. 2(6). [51] U. G. Rothblum and H. Schneider , “Characterization of Optimal Scalings of Matrices, ” Mathematical Pro gramming , vol. 19, pp. 121–136, 1980. [52] F . Murnaghan, The Unitary and Rotation Group s . W ashington: Spartan Books, 1962. [53] R. A. Brualdi, “Conv ex sets of nonnegati ve matrices, ” Canadian Journal of Mathematics , vol. 20, pp. 144–157, 1968. [54] D. P . Bertsekas, Nonlinear Pro gra mming . Athens: Athena S cientific, 1999. [55] D. J. White, “ A linear programming approach to solving bilinear programmes, ” Mathematical Pr ogr amming , vol. 56, pp. 45–50, 1992. [56] H. D. Sherali and C . M. Shetty , “ A finitely con ve rgent algorithm for bilinear programming problems using polar cuts and disjuncti ve face cuts, ” Mathematical Pro grammin g , vol. 19, pp. 14–31, 1980. [57] D. D. Lee and H. S. S eung, “ Algorithms for non-nega tiv e matrix factorization, ” A dvances in Neural Information Pr ocessing , vol. 13, pp. 556–562 , 2000. 4 1 [58] P . O. Hoyer , “Non-ne gati ve Matrix Factorization with Sparseness Constraints, ” Journa l of Mac hine L earning Resear ch , vol. 5, pp. 1457–1469, 2004. [59] C. -J. L in, “On t he Con vergence of Multiplicativ e Update Algorithms for Nonnegati ve Matrix F actorization, ” IEEE T ransactions on N eura l Networks , vol. 18(6), pp. 1589–1596, 2007. [60] J. M. Ortega and W . C. Rheinboldt, I terative Solution of N onlinear Equations in Several Variables . New Y ork : Academic Press, 1970. [61] R. A. Bailey , Association Schemes: Designed experimen ts, Al gebr a and Combinatorics . Cambridge: Cambridge Univ ersity Press, 2004.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment