Void Traversal for Guaranteed Delivery in Geometric Routing
Geometric routing algorithms like GFG (GPSR) are lightweight, scalable algorithms that can be used to route in resource-constrained ad hoc wireless networks. However, such algorithms run on planar graphs only. To efficiently construct a planar graph,…
Authors: Mikhail Nesterenko, Adnan Vora
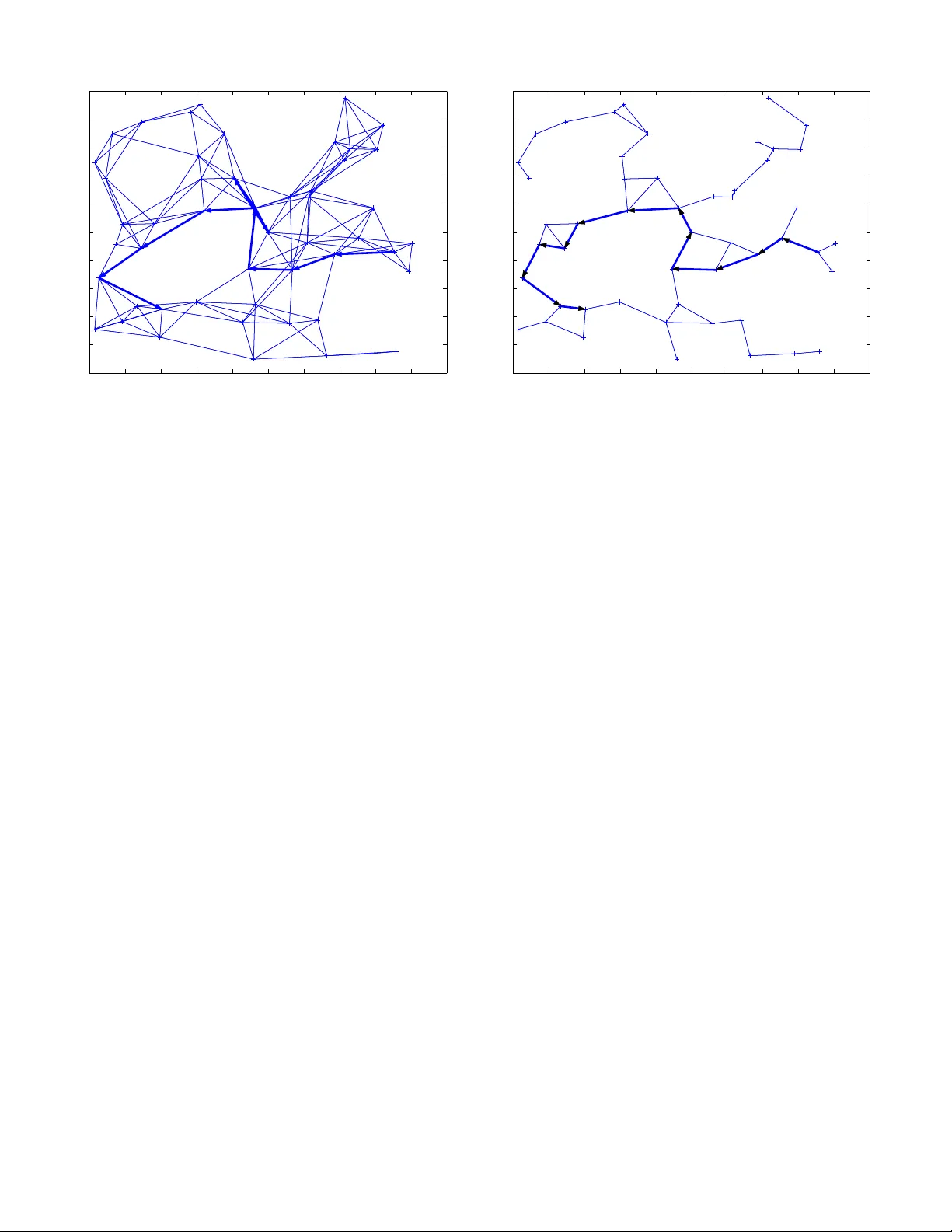
V oid T ra versal for Guaranteed Deli ve ry in Geometric Routing Mikhail Nesterenko and Adnan V ora Computer Science Department Kent State Universit y Kent, OH, 44242 mikhail@cs.kent.edu, avora@cs.kent.edu Abstract — Geometric routing algorithms like GFG (GPS R) are lightweight, scalable algorithms that can be used to route in resour ce-constrained ad hoc wire less networks. Howev er , such algorithms run on p lanar graphs only . T o efficiently construct a planar graph, th ey require a u nit-disk graph. T o make the topology unit-disk , the maximum link length in the network has to be selected conserv ativ ely . In practical settin g thi s leads to the design s where the node d ensity is rather high . Moreov er , the network diameter of a planar subgraph is grea ter than the o riginal graph, which leads to longer r outes. T o r emedy this p roblem, we propose a vo id tra v ersal algorithm th at works on arbitrary geometric graphs. W e describe ho w to use this algorithm for geometric routing wi th guaranteed delivery and compare its perf ormance with GFG. I . I N T RO D U C T I O N Geometric routing is a p romising approach for message transmission in ad h oc wireless n etworks. Un like traditional ad hoc routing, geometric routing algorithms hav e n o control messages or rou ting tab les, the no des maintain no inf ormation about data message s between transm issions and each d ata message is of con stant size. Hence, geometric routing is quite scalable. Ge ometric ro uting is particularly ap propriate for wireless sensor networks. Networked sen sors usually h av e limited resources for routing infor mation, yet many applica- tions for sensor networks require ad hoc configuration s of large scale. In geo metric routing , eac h node kn ows it own geogr aphic coordin ates. Each node is also aw are of the coord inates of other nodes a nd links in a part of the network around it. The coord inates are either obtain ed fro m GPS r eceiv ers or a localization algorithm [1]. Th e sou rce no de of a data message has th e coord inates of the target but the source doe s no t know the complete route to i t. The source s elects one of its neighbors and send s the message to it. After gettin g the message the receiver for wards the message fu rther . Th e objective of the algorithm is to deli ver the message to the target. The simplest version of a geometric rou ting algorithm is gr eedy routing. In gr eedy routing the source, as well as each intermediate n ode, examine s its neighbo ring n odes and forwards the m essage to the one that is the closest to the target. Unfortun ately , the gree dy routin g algorithm fails if the message recipient is loca l min imum : all its neig hbors are further away f rom the target than the nod e itself. In compass ro uting [2], the next hop is selected such that the angle between th e direction to the next h op no de and to the destination is minim al. Howev er , compass routing livelocks ev en on planar grap hs. GFG [3] (also known as GPSR [4]) is the first algorithm that guaran tees delivery of the message. The algor ithm is designed for p lanar g raphs. It uses g reedy ro uting. T o get ou t o f a local minimu m GFG seq uentially traverses the faces of the planar g raph th at intersect the line between th e source and target. GFG assumes th at the original commu nications graph is a unit-disk gra ph. For this g raph, the authors constru ct its Gabriel sub graph. This sub graph pr eserves th e conn ectivity of the o riginal gr aph and it can be constructed locally b y ea ch node. Datta et a l [5] pro pose further imp rovements to GFG. Kuhn et al [6] present a similar algo rithm with asymptotically optimal worst-case p erform ance. Our contribution . The g uaranteed delivery geometr ic rou t- ing algo rithms, of which we are aware, have th e fo llowing shortcomin g. Their local minimum av oidance part r uns over a p lanar gr aph. The efficient construction o f a planar graph requires that the orig inal graph is unit-d isk. As recent work [7] demon strates this assumption is n ot realistic for c onnection topolog ies formed by comm on networked sensors such as Berkeley m otes [8]. Motes’ radio propagation patters prove to be quite in tricate. In this paper we demonstrate how to c arry o ut geo met- ric r outing with gua ranteed delivery on a rbitrary no n-plan ar graphs. The fo undatio n o f our ap proach is a void tra versal algorithm . W e describe algorithm s V OID-1 and VOID-2 that incorpo rate void traversal for ro uting acr oss the wh ole n et- work. W e also present GVG — an algorith m that uses gr eedy routing and void traversal to g et o ut of local minima. T he void trav ersal is based on each no de storing the network topo logy of its neigh borho od. The neighborhoo d size needs to meet a con dition we call in tersection semi-closure . Most pr actical geometric grap hs meet this condition such that the storage requirem ents for e ach nod e are indep endent o f the size of the network an d rather small. W e com pared the pe rforman ce o f V OID-2 with F ACE-2 which is the foun dation o f GFG. W e used rand omly g enerated graphs as a b ase for co mparison. A large numbe r of graphs did not have u nit-disk subgr aphs. Hence F ACE-2 cannot be run. On graph s whe re F AC E-2 and VOID-2 are ru n, dependin g on the g raph generation parameter s, the paths selected b y V OID- 2 were 35 -75% sh orter . The m emory storage req uiremen ts for V OID-2 were indep endent of the network size and only modestly increased compared to th ose of F A CE-2. Paper organization. This paper is organized as follows. W e g iv e definitions and describe our no tation in Section II. W e present our v oid tr av ersal algorithm in Section III. In Section IV we describe h ow th is algorithm can be u sed for geometric routing. In Section V we describe the results of the perfor mance com parison of the v oid trav ersal versu s face trav ersal algorithms. Sectio n VI concludes th e paper . I I . P R E L I M I N A R I E S Notatio n. W e model a sensor n etwork as a geom etric graph. A geometric gr aph G = ( V , E ) is a set of n odes ( vertices ) V on a E uclidean plan e conn ected by edges E . The num ber of nodes is n = | V | . Such grap h is plan ar if its edges in tersect only at vertices. V oid is a region on a pla ne su ch th at any two points of this region can b e co nnected b y a curve tha t does not inter sect any of the ed ges of the grap h. A bound ary of a void con tains the segments of the edges adjacent to the void. In every fin ite grap h there is one u nbou nded external void. A void in a plana r grap h is face . Observe th at the bound ary of a face f orms a simple c ycle. More over , each edge of a planar graph borders at most two faces. An edge of a non -planar graph may contain the segments of the bo rders of arbitrar ily many faces. Neighborho od N ( u ) of a no de u is a su bgraph of G . A neighbo rhood r elatio n N ( G ) ov e r graph G associates each vertex o f V with a su bgraph of G . Deno te ( u, v ) ∈ E an edge between n odes u and v . Denote path ( u, v ) a p ath f rom u to v . Den ote also | u, v | the Euclid ean distance between u and v . Intersection semi-closure. Definition 1: A neig hborh ood r elation N ( G ) over a geo - metric graph G is d -inciden t edge intersection semi-clo sed ( or just d -intersection semi-closed ) if , for every two intersecting edges ( u, v ) and ( w, x ) , eithe r: • there exist path ( u, w ) , path ( u, x ) , either one no more than d h ops an d ( w , x ) , path ( u, w ) and path ( u, x ) be- long to N ( u ) ; or • there exist path ( v , w ) , path ( v , x ) , either o ne n o more than d h ops a nd ( w, x ) , path ( v , w ) , an d p ath ( v , x ) belong to N ( v ) . The attractive f eature o f th e intersection semi-closed neigh- borho od rela tion is that for any edge ( u, v ) , the information about every edge that intersects ( u, v ) as well as how to reach such edge is conta ined in th e union of N ( u ) and N ( v ) . Observe that for a par ticular graph , depen ding on the value of d , such a r elation may not exist. Howe ver , for any gra ph there always exists a n -incident edge semi-closed relatio n. T o illustra te Definition 1, we apply it to unit- disk grap hs. Unit-disk graph is a ge ometric graph where two n odes u and Fig. 1. Edge ( w , x ) belongs to N ( u ) in a unit-disk graph v are connected by an edge if an only if | u, v | ≤ 1 . Lemma 1: A neighbo rhood relatio n over a unit-d isk graph is 2 -intersection semi-closed if for e very nod e u and ev ery edge ( w, x ) such that | u, w | ≤ 1 and | u, x | ≤ 2 / √ 3 it follows that ( u, w ) ∈ N ( u ) . Proof: By defin ition N ( G ) is 2-inter section semi-closed if for every edge ( u, v ) and every edge ( w, x ) inte rsecting ( u, v ) , and the route to w and x ar e either in N ( u ) or N ( v ) . These routes are no lo nger than 2 h ops. Let N ( u ) an d N ( v ) be accor ding to the con ditions of the lemma. Since G is un it-disk, if | u , w | ≤ 1 an d | u, x | ≤ 1 then ( u, w ) ∈ E and ( u, x ) ∈ E . Accord ing to the co nditions of th e theorem, b oth of the se edg es as well as ( w , x ) itself belong to N ( u ) . If this is the case, then both th e rou te to the en dpoints and the edge itself belon g to N ( u ) . More over , these routes are at most 1-h op long. Henc e, the definition of intersection semi-closure is satisfied. Similar argum ent applies to v . Suppose th at | u, x | > 1 and | v, x | > 1 . Refer to Figure 1 for illustration. Since ( w , x ) intersects ( u, v ) , x could not be f urther away from ( u, v ) than 1 . H ence, | u, w | < 1 and | v, w | < 1 . Since G is a unit-disk, ( u, w ) ∈ G and ( v , w ) ∈ G . By the cond itions of the lem ma ( u, w ) ∈ N ( u ) and ( v , w ) ∈ N ( v ) . Supp ose th at x is clo ser to u tha n to v . Then, the th e distance between x and u is at mo st 2 / √ 3 . By the cond itions of the lem ma ( w , x ) ∈ N ( u ) . Which me ans that N ( u ) contains the edge ( w, x ) and , since N ( u ) also contains ( u, w ) , N ( u ) contain s th e routes to both w an d x . Moreover , the path ( u, x ) is just 2 -hops lo ng: ( u, w ) , ( w , x ) . The argument for v is similar . The lemma follows. ✷ Geometric routing. Consider a conne cted geom etric grap h G = ( V , E ) , a neigh borho od r elation N ( G ) over it and a pair of nod es ( s, t ) ∈ V . Source s has a message to tran smit to target t . T he source k nows the coordin ates of th e target. The message may be transmitted via interm ediate n odes. E ach node may potentially add data to the transmitted message. I n the sequel we ig nore the pay load of the m essage and assum e that it contains o nly the routing inf ormation . A ro uting algor ithm specifies a proced ure for intermediate node selection. A g eometric r outin g algorith m with guaranteed delivery ensure s the eventual message d eliv ery under the Fig. 2. Tra versal of void j ef k . following two con straints: ea ch node u receiving th e message, selects the next node only on the basis of N ( u ) and the contents o f th e message u received; the message size is indepen dent of ne twork size. Observe that the no des are not allowed to keep any information abou t the transmitted message after it has been f orwarded. I I I . V O I D T R A V E R S A L A L G O R I T H M Overview . The alg orithm tr av erses an intern al void clock wise following the segments of the edges that comprise the bord er of the void. The extern al void is traversed coun ter-clockwise. Refer to Figure 2 for th e illustration. Given an edge, for example ( d, h ) , that contain s th e segmen t of th e void’ s borde r , the algorithm has to select the next ed ge. For this the algorithm needs to determine the ends of the segment of ( d, h ) that border s th e void. On e of the ends — e is the in tersection of the previous ed ge ( a, j ) a nd ( d, h ) . The oth er end — f is the point of the in tersection of ( d, h ) and another edge ( b, k ) such that f i s closest to e in the d irection of the traversal of the void. Recall that in the intersection semi-closed neighborh ood relation, the union of the ne ighborh oods of d and h con tains ev ery edg e inte rsecting ( d, h ) as well as a route to this edge. Hence, to acco mplish its objecti ve the algorithm has to examine the neigh borho ods of d a nd h . Details. The algorithm uses two types of messages: edge change , and e dge selection . edge change contains: previous ed ge, current edge and the direction of the traversal of the curr ent ed ge. edge se lection m essage contains: previous edge, and suggested next ed ge. When a n ode d recei ves edge change message from node a , it d etermines the intersection point e between the previous ed ge ( a, j ) and the cu rrent edge ( d, h ) . Notice that the inter section point may be d itself. Then d examines N ( d ) to find the edg e whose intersection point is the clo sest to e in the direction of traversal. Th is edge is the suggested next edge. Note tha t the g raph is in tersection semi-closed and N ( d ) may not con tain some of some edges that intersect ( d, h ) . For example: ( b, k ) 6∈ N ( d ) . Hence, d selects ( c, i ) as the suggested next edge. Ed ge ( c, i ) in tersects ( d, h ) at poin t g . If d d oes not find any ed ge that in tersects ( d, h ) , it keeps the suggested next ed ge field empty . No de d sends edge selection to the o ther node h incident to the cu rrent edge. When nod e h r eceiv es edge sele ction from d , h com- pares the sug gested next edge ( c, i ) that h recei ves fro m d with the edg es in N ( h ) . I f h finds an edge ( b, k ) ∈ N ( h ) intersecting ( d, h ) whose intersection point f is closer to e than g , then h makes ( b, k ) th e sug gested n ext edge. Oth erwise, th e suggested next e dge rema ins the same. If neither d nor h find the su ggested next ed ge in this manner, h c onsiders the edges incident to itself. No de h selects the e dge nearest to ( d, h ) counter-clockwise. Node h forms an edge change message. This m essage contains ( d, h ) as the previous e dge and ( b, k ) as th e curr ent edge. From the informatio n containe d in edge selection that h re ceiv es fro m d , h is able to determine the dir ection of the traversal of ( d, h ) . Th e trav er sal direction is included in edge change . After composin g edge change , h sends th is message to either b or k . Since the graph is intersection semi-closed , N ( h ) may not contain the route to either nodes. In this case h retu rns the message to d and d forwards it to the appro priate n ode. The above discussion is summarized in the following theo- rem. Theor em 1 : The V oid T raversal Algorithm corre ctly tra- verses an arbitrary void in a geo metric g raph with intersection semi-closed neighborh ood relation. I V . U S I N G V O I D T R A V E R S A L T O G U A R A N T E E D E L I V E RY V OID-1 and V OID-2 . The g eometric routing algo rithms we d iscuss are V OID- 1 a nd VOID-2. They are rather straight- forward exten sions of algorithms F A CE-1 and F ACE-2 re- spectiv ely . The latter two ar e p lanar graph geom etric routing algorithm s presented by Bose et al [3]. F ACE-1 h as a better worst-case perfor mance. Howe ver F ACE-2 is m ore efficient in practice . Hence, we describe VOID-2 in detail and men tion briefly h ow V OID- 1 is designe d. Our algor ithms are based on the following observation. Pr oposition 1: Let p 1 and p 2 6 = p 1 be two arbitrary poin ts on the edg es or vertices of a geo metric graph . Let V be th e void such that p 1 lies on its bor der an d the line segment ( p 1 , p 2 ) intersects V . If there is a po int p 3 where ( p 1 , p 2 ) intersects the border of V th en | p 3 , p 2 | < | p 1 , p 2 | . Both V OID -1 and V OID-2 sequentially trav erse the voids that intersect th e line ( s, t ) . Refer to Figure 3 for illustration. While trav ersing a void, V OID- 1 and V OID-2 loo k for an intersection point with line ( s, t ) . Observe that there m ay be multiple such poin ts. For example, void V 2 in Figure 3 has four such points. VOID-1 and V OID-2 differ in th eir actions when an intersectio n point is encounter ed. V OI D-1 traverses the w hole void, selects the intersection po int that is closest to t , moves the message to this point and switches to th e trav ersal of the ne xt void. For e x ample, V OI D-1 w o uld tra verse Fig. 3. Example route of V OID-2. Algorithm : V OID-2 p 1 ← s p 2 ← t repeat /* let V be the v o id with p 1 on its bound ary that intersects ( p 1 , p 2 ) */ trav erse V u ntil reaching an edge containing point p 3 intersecting ( p 1 , p 2 ) p 1 ← p 3 until p 1 = p 2 /* target reach ed */ Fig. 4. Pseudocode for VOID-2 . VOID-2 uses void traversa l to guarante e deli very . V 2 completely and switch to V 4 . V OID- 2, on the other hand , switches to the next void as soo n as the first inter section p oint is f ound. Th e p seudocod e for VOID-2 is g iv e n in Figu re 4 and an example r oute th at V OID- 2 selects is shown in Figure 3. On th e basis of Theo rem 1 and the discussion above we state the following. Theor em 2 : Given an arb itrary geometric gr aph, an in ter- section semi-closed neighborho od relation and an arbitrar y pair of node s in th is gr aph, both VOID-1 and V OID- 2 ev en- tually deli ver a message fro m the first nod e to the second . GVG. As in GFG, void traversal is on ly n eeded f or a message to leav e a local minimum . Othe rwise greedy r outing can be used. Care must be taken to a void a livelock whe n me ssage returns to th e same local minim um. Th e comp lete alg orithm – gr eed y-void- gr eed y (GVG) works as follows. T he message is at first forwarded acc ording to greedy routing . When a no de discovers that it is a lo cal m inimum, it notes the distance to target and the r outing switches to V OI D-1 or VOID-2. The routing switches back to greed y if the distance to target is less th an that of the local minimum. Th e pro cess repeats if necessary . Ob serve that, accor ding to Theo rem 2 , the deliv ery of a message by either V OID- 1 or VOID-2 is gu aranteed. Hence, either GVG eventually switches to greedy routing or delivers th e message to the target. Hence the fo llowing theorem. Theor em 3 : Given an arb itrary geometric gr aph, an in ter- section semi-closed neighborho od relation and an arbitrar y Fig. 5. Edge existe nce probabilit y with respect to the distanc e between nodes. pair of nodes in this graph, GVG e ventually deliv e rs a message from the first n ode to the second on e in that pair . V . P E R F O R M A N C E E V A L UAT I O N Note that the greedy phase of GFG and GVG is the same. Hence we o nly comp are the perf ormance of local minimu m av oida nce p arts: void and face tra versal. W e use F A CE- 2 and V OID- 2 for comparison a s they are m ore efficient in practice then F A CE-1 and V OID-1. As a p rimary m etric we co mpare the le ngth, in the number of hops, of the routes selected by face and void traversal algorithm s. Note that a void traversal algorithm makes r outing decisions o n the basis o f lar g er neighb orhoo d in formatio n. Therefo re, we compar ed the individual no de mem ory r equire- ments for face and void traversal alg orithms as well. Graph Generatio n. W e u sed randomly generated sets of graphs with 50, 100 and 20 0 nodes in a fixed area of 2 by 2 units. The nodes we re u niform ly distributed over the ar ea. W e used a rath er simple mode l for fading effect of radio receptio n. For each set of graph s we selected the conne cti vity u nit u to be 0 . 3 , 0 . 25 and 0 . 2 respectively . W e also selected a fading factor f to be eith er 1 , 2 and 3 . The connectivity between nodes was determined as follows. W e determin istically added an edge for ev ery pair of nodes that we re no more than u away from each o ther . See Figure 5. If th e d istance between two nod es was between u and f · u , the ed ge betwee n th em is added prob abilistically . The pro bability linea rly decreased from 1 to 0 . Notice that when the fading factor f is eq ual to one, the random graphs that we gen erated were un it-disk. In o rder to comp are F ACE-2 and V O ID-2 we needed to compute unit-d isk sub graphs of the the generate d g raphs. Howe ver, freq uently the subgra phs were disconn ected: out of 3 50 of rando mly generated 50-no de g raphs with f eith er 2 or 3 , only a single graph had a connected unit-d isk sub - graph. These sub graphs had to be discarded as unsuitable f or F A CE-2. T o make the perf ormanc e compar ison, we ad opted a dif f erent g raph selection strate gy . W e gener ated random, connected u nit-disk grap hs and added extra links according to the co nnectivity rules above. No tice that this strategy fav or s F A CE-2 as it discoun ts the graphs that ar e not u sable by F A CE- 2. 0 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 1.8 2 0 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 1.8 2 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 0 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 1.8 2 0 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 1.8 2 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 Fig. 6. Example routes select ed by V OID-2 and F A CE-2 between nodes 27 and 11 in a 50-node graph and its unit-disk based subgraph respecti vely . The fadi ng factor f is 2. W e genera ted 5 graph s for each n umber of no des and fading factor . Th is yielded the to tal of 45 graphs and their p lanar subgrap hs. Route Length Comparison. W e imp lemented the F A CE-2 and VOID-2 a lgorithms in Ja va and Matlab. W e generated 10 random pairs of n odes for eac h set of g raphs and used VOID-2 and F A CE-2 to compu te the routes between the n odes in eac h pair . V OID-2 u sed the original graph and F AC E-2 — its unit- disk based pla nar subgraph . The example routes are shown in Figure 6. W e used paired comparison to estimate the improve- ment fro m F ACE-2 to VOID-2 in the length o f th e se- lected ro utes as fo llows. For e ach pair o f source and des- tination no des we calculated the d ifference in the h op- count between routes an d no rmalized it to the ho p cou nt of the route selected b y F AC E-2. That is the co m- parison is based on the fo rmula: ( H opC ou nt F AC E − H opC ount V O I D ) /H opC oun t F AC E . Figure 7 summ arizes the r esults. Ob serve that even on un it-disk gra phs ( f = 1 ), V OID- 2 g enerates routes that ar e 35-45% shorter tha n the rou tes selected by F A CE-2. The r elativ e perfo rmance of V OID- 2 fur ther improves as the fading factor and d ensity of the graphs increases. Memory Usag e Co mparison. In both VOID-2 and F A CE- 2, each node v stores the info rmation ab out its neighborho od nodes N ( v ) . Th e size of the ne ighbor hood differs in the two algorithm s. In e valuating the mem ory usage, we estimated the average size of the neig hborh ood. For the F A CE- 2, the av erage size of the neighbo rhood is th e average d egree d of the p lanar subgrap h. In our experim ents, the average size of neighbo rhood in V OID- 2, was f ound to be f · d where f is the fading factor . V I . C O N C L U S I O N The elegance and efficiency of geometric routing algor ithms is remarkable. Recent advent of large-scale wireless sensor networks increased the relev ance of such algorithm s. Ho wever , the algorithms’ demand for unit-disk b ased graph planarity hampere d th e attractiveness of g eometric rou ting. W ith this paper, we lift th is restriction an d help the adoption o f g eo- metric r outing algorithms as the routing solu tion o f choice in sensor networks. A C K N O W L E D G M E N T S W e would like to thank I van Stojmenovic of the University of Ottawa and M. Kazim Kh an of Kent State University for their helpful comments. R E F E R E N C E S [1] N. Bulusu, J. Heidemann , D. Estrin, and T . T ran, “Sel f-configuri ng local- izati on systems: Desig n and experiment al ev aluati on, ” ACM T ransactions on Embedded Computing Systems , vol. 3, no. 1, pp. 24–60, Feb . 2004. [2] E. Kranaki s, H. Singh , and J. Urrutia, “Compass routing on geometric netw orks, ” in Proce edings of the 11th Canadian Confere nce on Compu- tationa l Geometry (CCCG-99) , V ancouve r , BC, Canada, Aug. 1999, pp. 51–54. [3] Bose, Morin, Stojmenovic, and Urrutia, “Routin g with guarantee d de- li very in ad hoc wireless netw orks, ” in W ir eless Network s: The Journal of Mobile Communicati on, Computati on and Informati on, Kluwer , 2001, vol. 7. [4] B. Karp and H. T . Kung, “GPSR: Greedy perimeter stateless routing for wireless network s, ” in Pr oceedings of the 6th A nnual International Confer ence on Mobile Computi ng and Networking (MOBICOM-00) . N. Y .: ACM Press, Aug. 6–11 2000, pp. 243–254. [5] S. Datta, I. Stojmeno vic, and J. W u, “Internal node and shortcut based routing with guaranteed deli very in wireless network s, ” Cluster Comput- ing , vol. 5, no. 2, pp. 169–178, Apr . 2002. [6] F . Kuhn, R. W attenhofer , and A. Zolling er , “ Asymptoticall y optimal geometri c mobile ad-hoc routing, ” in Pro ceedi ngs of the 6th Internatio nal W orkshop on Discrete Algorith ms and Met hods for Mobile Computing & Communicat ions (DialM-02 ) . Ne w Y ork: A CM Press, Sept. 28 2002, pp. 24–33. 0 2 0 4 0 6 0 8 0 5 0 1 0 0 2 0 0 Num be r of nod e s in gr ap h H op c ount im pr ov e m e n t, % Fac tor o f 1 Fac tor o f 2 Fac tor o f 3 Fig. 7. Route length improvemen t from F A CE-2 to V OID-2. [7] D. Ganesan, B. Krishnamachar i, A. W oo, D. Culler , D. Estrin, an d S. W ick er , “Comple x behavior at scale: An experimenta l study of low- po wer wireless sensor network s, ” UCLA, T echnical Report CSD-TR 02- 0013, 2002. [8] J. Hill and D. Culler , “Mica: A wireless platform for deeply embedded networks, ” IEEE Micr o , vo l. 22, no. 6, pp. 12–24, Nov ./Dec. 2002. [Online]. A vail able: http:/ /dlib . computer .org/mi/books/mi2002/pdf/m6012.pdf;http://www .computer .org/micro/mi2002/m6012abs.htm
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment