Generalized Whac-a-Mole
We consider online competitive algorithms for the problem of collecting weighted items from a dynamic set S, when items are added to or deleted from S over time. The objective is to maximize the total weight of collected items. We study the general v…
Authors: Marcin Bienkowski, Marek Chrobak, Christoph Durr
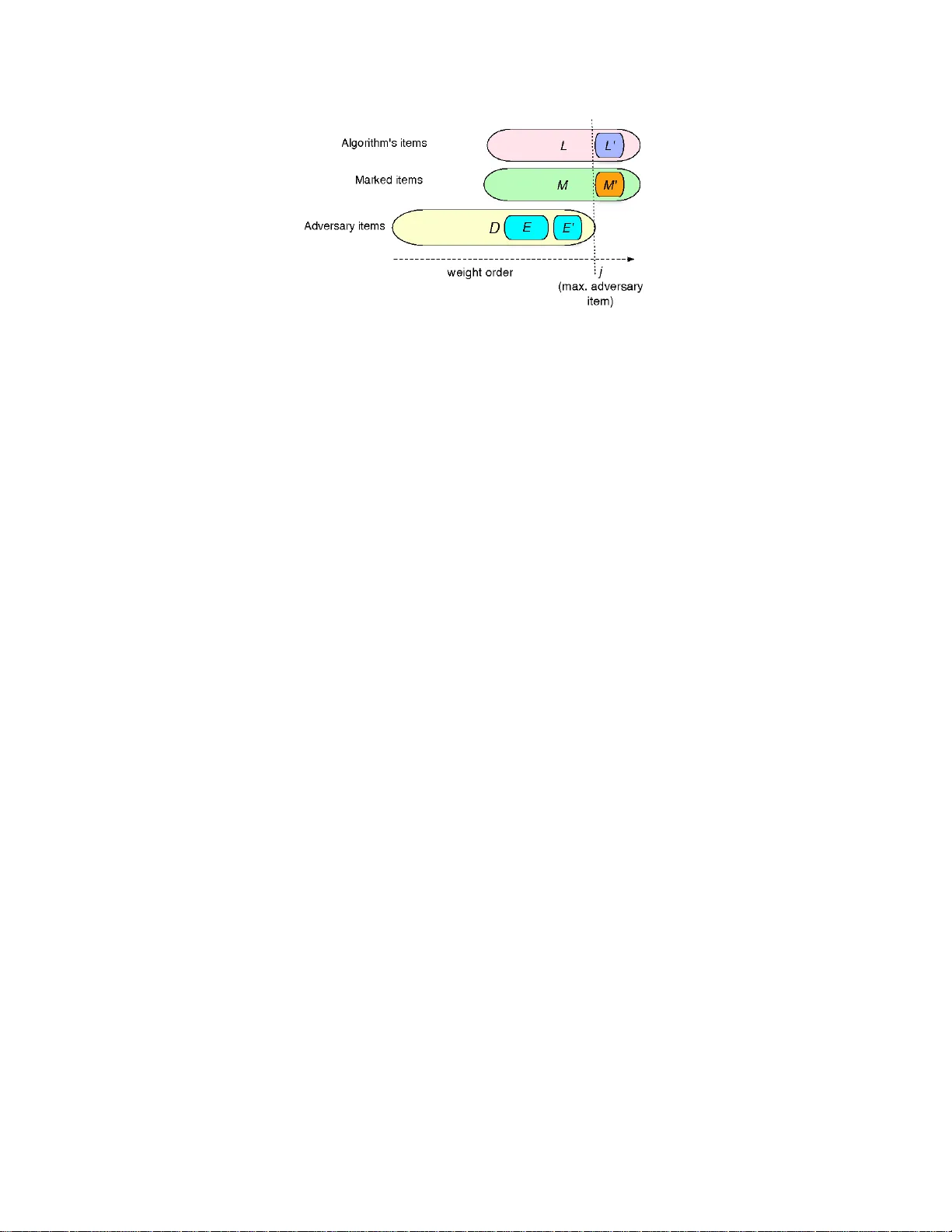
Generalized Whac-a-Mole Marcin Bienk o wski ∗ Marek Chrobak † Christoph D ¨ urr ‡ Mathilde Hurand ‡ Artur Je ˙ z ∗ Luk asz Je ˙ z ∗ Jakub Lopusza ´ nski ∗ Grzegorz Stacho wiak ∗ Abstract W e consider online comp etitive algorithms for the problem of collecting w eighted items from a dynamic set S , when items are added to o r deleted from S ov er time. The ob jective is to maximize the total w eight of collected items. W e study the general version, a s well as v ariants with v a rious restrictio ns, including the following: the un iform c ase , when all items hav e the same weigh t, the de cr emental sets , when all items are pre s ent at the beg inning and only deletion opera tions are allo wed, and dynamic queues , where the dynamic s et is order ed and only its prefixes can b e deleted (with no restriction on ins ertions). The dynamic queue case is a generaliza tion of bounded-de lay packet s chedulin g (also referred to as buffer ma na gement). W e present several upper and lo wer b ounds o n the competitive ratio for these v ariants. 1 In tro du ction Whac-a-mole is an o ld arcade g ame, where plastic “moles” p op out of holes in the mac hine for short p erio ds of time, in some u n predictable w a y , and the pla yer uses a m allet to “whac k” as many moles as p ossible. 1 In the generalized ve rsion that w e consider, m ultiple moles ma y b e present at the same time, an d different moles ma y hav e differen t v alues. In a more form al setting, we think of it as a d ynamic set S of w eight ed items (moles). Be fore eac h step, some items can b e deleted from S and other items can b e added to S . W e are allo wed to collect one item (whac k one mole) from S p er step. Eac h item can b e collected only once (the mallet do es its job). The ob j ective is to maximize the total w eigh t of the collected items. T o our kno wledge, this s imple and fundamenta l p roblem has not b een explicitly addressed in the literature. By placing appr opriate assum ptions on the structure of S or on the t yp e of allo w ed op erations, on e can obtain a num b er of natural sp ecial cases, s ome of which are related to kn own online problems. W e study the general case of d ynamic sets, as w ell as some restricted cases, among w hic h we fo cus on the f ollo wing v ersions: Dynamic Queue : In th is case, S represen ts a list, i.e. the items in S are ordered. Items can b e added to S at an y place, but only a prefix of S can b e deleted. A queue is called a FIF O queue if insertions are allo wed only at the end. ∗ Institute of Computer Science, Universi ty of W roc la w, 50-383 W ro c la w, Pola nd . Supp orted b y MN iSW grants num b er N206 001 31/0436, 2006–2 008 and N N206 1723 33, 2007–2010. † Department of Computer Science, Universit y of California, Riversi d e, CA 92521, U SA. Supp orted by NSF grants OISE-0340752 and CCF-0729071 . ‡ CNRS, LIX UMR 7161, Ecole Polytec hniqu e 91128 Palaisea u , F rance. S upp orted by ANR A lpage. 1 No mole w as harmed in the course of this resea rch. 1 De cr emental Sets: Here, all items are added at the b eginning, and only deletions are allo w ed afterw ards. In particular, one can consider the case of decremen tal q u eues, where only prefix- deletion op erations are allo w ed. The case of d ynamic queues generalizes the well -stud ied problem of b ound ed-dela y pac ke t sc hedulin g (a.k.a. bu ffer managemen t), or, equiv ale ntly , the problem of scheduling un it job s with deadlines for m axim um we ighte d throughput. In this problem, pac k ets with v alues and deadlines arriv e in a buffer of a netw ork link. A t eac h step, w e can send one pac k et along the link. The ob jectiv e is to maximize the total v alue of pack ets sen t b efore their deadlines. This is a sp ecial case of our d ynamic queue problem, where pac ke ts are repr esen ted b y items order ed acco rd ing to dead- lines. The difference is crucial though: in pac ket scheduling, pack et arriv al times are u nkno wn but their departure times are kno wn , while in dynamic queues b oth the arriv al and departure times are not kno wn. The FIF O case generalizes the v ersion of pac k et sc hedu ling w ith agree able deadlines. Comp etitiv e algorithms for v arious versions of b ounded-d ela y pac ket s cheduling p roblem hav e b een extensiv ely studied [1, 4, 5, 8, 9, 10 , 12]. I n particular, it is kno wn that no deterministic online algorithm can ha v e comp etitiv e ratio b etter than φ ≈ 1 . 618 [1, 5], and algorithms with comp etitiv e ratio ≈ 1 . 83 ha v e b een recently devel op ed [12, 6]. These are the b est lo wer and upp er b ound s for this problem and closing this gap remains a tan talizing op en problem. F or agreeable deadlines, an upp er b oun d of φ has b een established in [11]. The dynamic set problem has some indir ect conn ections to other p ac k et s cheduling p roblems, where the ob jectiv e is to maximize the v alue of pack ets reac hing their destination und er v arious scenarios [2, 3 , 9, 10]. A d ifferen t, metric ve rs ion of whac-a-mole w as considered in [7]. I n this appr oac h moving the mallet to a mole tak es time and the duration of moles’ exp osure is kno wn . Ho we ver, their resu lts are inapplicable in ou r mo d el. Our r esults. W e first consider the general case of dynamic sets. F or determin istic algorithms, it is quite easy to show a lo w er b ound of 2 (ev en for tw o items in the decremen tal case), and this ratio can b e ac hiev ed by a simp le greedy algorithm that alw a ys collects the heavie st item. F or randomized algo r ith m s, w e fo cus on the uniform c ase , wh en all items ha v e w eight 1. W e sho w that no memoryless randomized algorithm can ac hieve comp etitiv e r atio b etter than 2. W e then stud y the un iform decremen tal case, for whic h we give an on lin e randomized algorithm with comp etitiv e ratio e / (e − 1) (against an oblivious adv ersary) and pr ov e a matc hing lo w er b ound . Most of our r esults concern dynamic queues. In the deterministic case, ev en for d ecremen tal queues, it is quite e asy to sho w a lo w er b ound o f φ . W e impro ve this b ound , by pro ving a lo w er b ound of ≈ 1 . 63, that applies ev en to the decremen tal case. W e also sho w that n o memoryless algorithm can hav e a ratio smaller than 2. This con trasts with the r esult of Englert and W e sterman [6] who ga v e a memoryless alg orithm for pac k et sc heduling with ratio ≈ 1 . 893. Th us, at least for memoryless algorithms, kno wing the exact deadlines helps. As for up p er b oun ds, we giv e the follo wing deterministic algorithms: (i) A 1 . 737 -comp etitiv e algorithm for decrement al qu eues (b eating the ratio 2 of the na ¨ ıv e greedy algorithm). (ii) A 1 . 8-co mp etitiv e algorithm for FIF O queues. (iii) A φ -comp etitiv e algorithm for dyn amic queues when the item w eigh ts are n on-decreasing (w.r.t. their p osition in the queue). Th is last result h as implications for pac k et scheduling, as all lo w er b ound pro ofs f or that p roblem use in stances wh ere pac k ets’ w eight s increase with deadlines. Thus, either the ratio φ for the pac k et sc heduling problem can b e ac hiev ed, or, to impro ve the lo wer b ound , one w ould hav e to u se non-monotone instances in the pro of. Our comp etitiv e analysis uses a no v el in v arian t technique in v olving dominance relations 2 b et ween sets of num b ers, and is likely to fi n d ap p lications in the analysis of pac k et scheduling. Finally , w e addr ess th e case of dynamic queues and randomized algorithms. The algorithm RM ix [4] can b e easily adapted to d ynamic queues, ac hieving comp etitiv e ratio of e / (e − 1) against an adaptiv e adv ersary . (In spite of the same v alue, this result is not related to our analysis of the uniform dynamic sets.) W e pro ve a matc hing lo w er b oun d, whic h sa ys that no memoryless randomized algorithm for dynamic qu eues can hav e comp etitiv e ratio smaller than e / (e − 1). Due to space limitations some pr o ofs are presented in the app end ix. 2 Preliminaries W e r efer to the items cur ren tly in S a s active . In other w ords, those are th e items that h a v e b een already inserted b ut not yet deleted. An item is called p ending for an algorithm A if it is activ e but not y et collected by A . W e denote the w eight of item x as w x and the total w eigh t of a set of items X as w ( X ). An instance of the problem is defined b y a sequence I of ite m insertions or deletions. A solution consists of a sele ction se quenc e that sp ecifies items selected at eac h step. An optimal solution is computable in p olynomial-time: represen t the instance as a bipartite graph G whose partitions are items and time steps. Item a is connected to the time steps when a is activ e with edges of w eight w a . The maxim um-w eight m atc hing in G represents an optimal collec tion sequence. When S is a dynamic queue, S is represen ted b y a list. W e use sym b ol “ ⊳ ” to represen t the list ordering, i.e. a ⊳ b means that a is b efore b in the list. In case of dynamic queues, optimal solutions ha ve sp ecial structur e that we explore in our comp etitiv eness pro ofs, namely th ey satisfy (w.l.o.g.) the f ollo wing Earliest-Expir atio n- First (EEF) Pr op erty: If a, b are activ e at the same time, a ⊳ b , and b oth a , b are collecte d , then a is collecte d b efore b . An online algorithm A is called R -c omp e titive , if for any instance I , the gain of A on I is at least the optimum gain on I d ivided by R . (An add itiv e constant is sometimes also allo w ed in this b ound ; in all ou r upp er b ound s this constant is 0, as the wei ghts can b e scaled up.) The c omp etitive r atio of A is the smallest R for which A is R -comp etitiv e. 3 Dynamic Sets F or general dynamic sets, it is easy to sho w the low er and upp er b ounds of 2 on the comp etitiv e ratio of deterministic online algo rith m s. T o p ro ve the lo w er b ound, the adv ersary can start with t wo items, sa y a an d b with w a = w b = 1. Assu m e, by symmetry , that th e algorithm first collects a . Then the adv ersary can collect b in the first step, delete it, and collect a in the next step, while the algorithm has n o items to collect. This b ound can b e ac hieved b y a simple Greedy algo rithm : at eac h s tep, if there is at least one p endin g item, collect the maxim um-v alue p ending item. F act 1 Greedy is 2 -c omp etitive for dynamic sets. Pro of: The pro of is a straigh tforwa rd adaptation of the pro of for pac ke t sc hed uling [8, 9], we include it for completeness sak e. Th e items collecte d by the ad versary are c harged to the items collect ed by Greedy . S upp ose the adve rs ary collects an item b at time t . If this item was collec ted 3 at time t or earlier by Greedy , we c harge it to that item in Greedy ’s sequence. Otherwise, w e c harge it to th e item coll ected by Greedy at time t . Let a b e an item collec ted by Greedy at some time u . It receiv es at most t w o c harges: one from itself, if it w as collected by the adv ersary at time u or later, and the other one from the item b collect ed b y the adv ersary at time u . If a receiv es a charge from b , then b is p endin g for Greedy at time t , and therefore w b ≤ w a . Therefore the c harge to a is at most 2 w a . Summarizing, all adv ersary items are c h arged to our items, and eac h our item receiv es a charge of at most t wice its w eigh t. T h us Greedy is 2-comp etitiv e. No w we turn our atte ntion to r andomized algorithms. F or the adaptiv e adv ersary it is n ot hard to sho w a lo w er b ound of 2. The adversary strategy is this: issu e n items of wei ght 1. Collect an y item a that is collected b y the algorithm w ith pr obabilit y at most 1 /n . Let b b e the item collected b y the alg orithm. If b = a , remo v e all ite ms . If b 6 = a , remo v e all ite ms except b and collect b . With probabilit y at most 1 /n , w e h a v e b = a an d b oth the algorithm and the adversary collec t b . With probabilit y at least 1 − 1 /n , the algorithm gets one item and the adv ersary gets tw o items. So the ratio is arbitrarily close to 2. F or oblivious adve r s aries we concen trate o n the uniform decremen tal case. W e sho w that for an y randomized algorithm the optimal s tr ategy for the adv ersary is to rep eatedly tak e and remo v e an activ e item. W e co n sider U niRand algorithm, wh ic h at eac h s tep colle cts one of the p ending items with equal p robabilit y . F or the lo wer b oun d we use the Y ao m in-max principle and consider inp uts wh ic h are constru cted b y the follo wing r andom pro cess: at eac h step c ho ose an activ e item uniformly at rand om, collect it, and delete it after the step. Let E a,p b e th e exp ected n umb er of items collected by an algorithm if a items are activ e and, among them, p items are p ending. It can b e sho wn that b oth in Uni Rand analysis and in the lo we r b ound construction, E a,p satisfies the f ollo wing recursive formula: E a, 0 = 0 , E a, 1 = 1 , E a,p = a − p + 1 a · E a − 1 ,p − 1 + p − 1 a · E a − 1 ,p − 2 + 1 . The unique solution of th is form u la can b e estimated by E a,p ≈ a (1 − (1 − 1 /a ) p ). Using exact appro ximations of E a,p , we ma y pro ve the follo wing theorems. Theorem 2 The c omp etitive r atio of any r andomize d algorithm for the uniform c ase of de cr emental sets is at le ast e / (e − 1) . Theorem 3 Algorithm UniR and is e / (e − 1) -c omp etitive for the uniform c ase of de cr emental sets. 4 Dynamic Queues—Deterministic Algorithms In this sec tion w e consider deterministic online algorithms for the case when S is a d ynamic queue, that is, S is an ordered list and only a prefix of S ca n b e d eleted. In the fully dyn amic case, items can b e in s erted an ywhere, while in the decremen tal case, all items are in s erted at the b eginning. F act 4 Every deterministic algorith m for queu e s has c omp etitive r atio at le ast φ ≈ 1 . 61 8 , even for de c r emental queu e s and with items of “life sp an” at most 2 . 4 Pro of: W e start with t w o items in the list, a ⊳ b , with v alues w a = 1 an d w b = φ . If the algorithm c ho oses b , the adv ersary c ho oses a and deletes it, and in the next step he c ho oses b , so the ratio is ( w a + w b ) /w b = (1 + φ ) /φ = φ . If the algorithm c ho oses a in the fir s t step, the adversary c ho oses b and d eletes b oth items, so the ratio is w b /w a = φ again. This section includes some low er and upp er b ounds for the comp etitiv e ratio of d eterministic online algorithms. Starting with lo wer b ound s, we fir s t p r o v e that no deterministic algo rith m for the dyn amic queue—in fact, ev en for the decrementa l case—can ac h iev e a comp etitiv e r atio b etter than 1 . 63 . F or memoryless algorithms we give a lo wer b ound of 2. Our fir st upp er b ound concerns decremen tal queues, for whic h we present a deterministic online algorithm DecQueEFH with co mp etitiv e ratio ≈ 1 . 737. Next, w e p resen t a deterministic online algorithm FIFOQueEH that ac hiev es comp etitiv e ratio 1 . 8 for FIF O Queues. W e conclude this section with the algorithm MarkAndPick that ac hieves comp etitiv e ratio φ for dynamic queu es in whic h the item weig hts are non-decreasing (this also giv es a φ -competitiv e algo r ith m for scheduling pac k ets with non-decreasing w eigh ts). 4.1 Lo w er Bounds for Decremen tal Queues W e p ro ve that no online d eterministic algorithm can ha ve a comp etitiv e ratio smaller than 1 . 63 for decremen tal qu eues. The pro of is by presenti n g an adversary’s strategy that forces an y d eterministic online algorithm A to gain less than 1 / 1 . 6 3 times the adv ersary’s gain. Adv ersary’s strategy . T o get a cleaner analysis, we first present the argumen t for th e d ynamic case (with insertions allo w ed), and explain later how it extend s to the d ecremen tal case. W e assume that the items app ear gradu ally , so that at eac h step th e algorithm has at most three items to c ho ose from. Fix some n ≥ 2. T o simplify notatio n , in this s ection we refer to items simp ly by their w eigh t, th us b elo w “ z i ” denotes b oth an item an d its w eigh t. The instance consists of a sequence of 2 n items 1 , z 1 , z 2 , ... , z 2 n − 2 , z 2 n (note that th ere is n o item indexed 2 n − 1) suc h that z 2 ⊳ z 4 ⊳ ... ⊳ z 2 n − 2 ⊳ z 2 n ⊳ z 2 n − 3 ⊳ ... ⊳ z 3 ⊳ z 1 ⊳ 1 , and 1 > z 1 > z 2 > . . . > z 2 n − 3 > z 2 n − 2 > z 2 n > 0 . The ev en- and o dd-num b ered items in this sequence form tw o roughly ge ometric sequences. In fact, z 2 i is only sligh tly smaller than z 2 i − 1 , f or all i = 1 , ..., n − 1. Initially , items z 2 ⊳ z 1 ⊳ 1 are present. In step i = 1 , 2 , ..., n − 1, the adversary mainta ins the in v arian t that the act ive items are z 2 i ⊳ z 2 i − 1 ⊳ ... ⊳ 1 , of whic h only three items z 2 i , z 2 i − 1 and 1 are p endin g for A (i.e. A already collect ed z 2 i − 3 , ... , z 1 ). The adv ersary’s mo v e dep end s no w on what A colle cts in this step: (i) A collect s z 2 i . Then the adversary end s the game by deleting all acti ve items. In this case the adv ersary collects i hea viest items: 1 , z 1 , z 2 , z 3 , . . . , z i − 1 . (ii) A collect s 1. The adversary ends the game b y d eleting x 2 i and x 2 i − 1 . Th is leav es A with no p endin g items, and the adversary can n o w collect A ’s items one b y one. O verall, in this case the adv ersary collects 2 i hea viest items: 1 , z 1 , z 2 , . . . , z 2 i − 2 , z 2 i − 1 . 5 (iii) A colle cts z 2 i − 1 . In this case the game contin ues. If i < n − 1, the adversary deletes z 2 i , inserts z 2 i +2 and z 2 i +1 in to the current list (according to the order defined earlier), and we go to step i + 1. The case i = n − 1 is s lightly different : h ere the adversary only inserts the last item z 2 n b efore pro ceeding to step n (describ ed b elo w). If the game reac hes step n , A h as t wo p ending items, z 2 n and 1. In this step, the adv ersary b ehavi or is similar to p revious steps: if A collects z 2 n , then the adv ersary deletes the whole sequ ence and collects n h ea viest ite ms : 1 , z 1 , z 2 , z 3 , . . . , z n − 1 . If A coll ects 1, the adv ersary deletes z n , lea ving A without p ending items, and allo win g the adv ersary to collect the whole sequence. Our goal is to fin d a sequence { z i } , as ab o v e, and a constan t R suc h that R · (1 + P j i =1 z 2 i − 1 ) ≤ 1 + P 2 j +1 i =1 z i for all 0 ≤ j < n (1) R · ( z 2 j +2 + P j i =1 z 2 i − 1 ) ≤ 1 + P j i =1 z i for all 0 ≤ j < n (2) Lemma 5 Supp ose that ther e is a se quenc e 1 , z 1 , ... , z 2 n − 2 , z 2 n , and a c onstant R that satisfy in- e qualities (1) and (2 ). Then ther e i s no R - c omp etitive deterministic online algorithm for dynamic queues, even in the de cr emental c ase. The lemma should b e clear from the description of the strategy giv en earlier, since the sum s in inequalities (1) and (2) represen t the gains of the adv ersary and the algorithm in v arious steps. The only part that n eeds justification is that the lemma holds in the decremental case. T o see this, w e sligh tly mo dify the adversary strategy: The s equ ence { z i } is created all at once in the b eginning, and whenever A deviates from the c h oices (i), (ii), (iii), it m u s t b e collecting an item ligh ter than z 2 i , an d thus th e adversary can fin ish the game as in C ase (i). Lemma 5 and straight forward calculatio ns for n = 3 (6 items) yield the follo wing. Theorem 6 Ther e is no deterministic online algorithm for dynamic queues (even in the de cr e- mental c ase) with c omp etitive r atio smal ler than 1 . 63 29 . A natur al q u estion arises ho w m uch this b ound can b e improv ed with sequences { z i } of arbitrary length. F or n = 5 (10 items) one can obtain R = 1 . 6367 . .. and our exp erimen ts indicate that the corresp ondin g r atios te n d to ≈ 1 . 6378458 , so the impro veme nt is minor. Ho w ev er, it is easy to pro ve a lo w er b oun d of 2 for memoryless algorithms, i.e. alg orithms that decide whic h ite m to collect based only on the w eights of their p ending items. Theorem 7 F or dynamic queues, no memoryless algorithm has c omp etitive r atio smal ler than 2 . 4.2 Upp er Bound of 1 . 737 for Decremen tal Queues Algorithm DecQueEFH : The computation is divided into stages, wh ere ea ch s tage is a single step, a pair of consecutiv e steps, or a triple of consecutiv e steps. By h we denote the maximum- w eigh t p ending item from the fir st step of the stage. W e use t wo parameters, β = ( √ 13 + 1) / 8 and ξ = ( √ 13 + 1) / 6. Not e that β < ξ . Without lo ss of generalit y , we assu m e th at there a r e alw a ys p endin g items, for we can alw a ys insert an y n um b er of 0-we ight items in to the in stance, without c hanging the comp etitiv e ratio. In the pseudo-co de b elow, w e assume that after eac h item collect ion the algorithm pro ceeds to the next step of the pro cess. 6 (E) let h b e the hea viest p end in g item collect the earliest p ending item e with w e ≥ β w h (F) if h is n ot p ending then en d stage and goto (E) collect the earliest item f w ith w f ≥ ξ w h (H) if h is not p end ing then end stage and goto (E) collect h end stage and got o (E) Theorem 8 F or de c r emental queues, the c omp etitive r atio of DecQueEFH is at most R = 2( √ 13 − 1) / 3 ≈ 1 . 7 37 . Pro of: W e fix an instance and we compare DecQueEFH ’s gain on this instance to the adv ersary’s gain. W e assum e (w.l.o.g.) that th e adv ersary has the EEF pr op ert y . The p ro of is b y amortized analysis. W e preserv e the in v arian t that, after eac h stage, eac h item i that is p end ing for the adv ersary bu t has already b een collected by DecQueEFH has credit asso ciated with it of v alue equal w i . The adve rsary ’s amortized gain is equal to his actual gain plu s the total credit c hange. T o pr ov e the theorem, it is then sufficien t to prov e the follo win g claim: ( ∗ ) In eac h stage the adv ersary’s amortized gain is at most R times DecQueEFH ’s gain. T o pro v e ( ∗ ), we consider sev eral cases dep ending on the n um b er of steps in a stage and on relativ e lo cation of items collec ted by the adversary and b y DecQueEFH . W e assume that at eac h step the adv ersary col lects items that w ere not c ollected b y the algorithm b efore or during this stage. Oth er w ise, either the adv ersary collects an item that has b een collected by DecQueE FH earlier and has credit on it, or D ecQueEFH collected this item in this stage, in w hic h case we can think of the algorithm giving the adv ersary credit for this item an yw ay (ev en though it is not needed, for th is item is not p end ing for the adv ersary an ymore). W e first observe that e E f E h (if f is defined for this stage). This follo ws im m ediately fr om β < ξ < 1. An imp ortan t consequence of th is, that p la ys a m a jor role in the argument b elo w, is that when h is deleted, then e and f are d eleted as w ell. Case 1 : h is not p endin g in (F). Th e stage has only one step, and the algo r ith m collec ts an item e with w e ≥ β w h . Let a b e th e item coll ected by the adversary . If h w as deleted after (E) then e wa s deleted as well . T h us w e do not giv e the adv ersary cred it for e , an d h is amortized gain is w a ≤ w h . The ratio is w a w e ≤ 1 β = R . Supp ose that h was collected (i.e. e = h ). If a ⊳ h then w a ≤ β w h , s o, toge ther w ith the credit for h , the amortized adversary’s gain is w a + w h , an d the ratio is w a + w h w h ≤ 1 + β ≤ R . If h ⊳ a , we need not giv e the adv ersary any credit, so the ratio is at m ost 1. Case 2 : h is p ending in (F) bu t is not p end ing in (H). The stage has tw o s teps , and w e collect e and f , gaining w e + w f ≥ ( β + ξ ) w h . The adv ersary collects t wo items, say a and b with a ⊳ b . 7 If h w as deleted after (F), then b oth e and f are deleted as w ell, so we d o not give the adv ersary an y credits. Thus the adversary amortized gain is w a + w b ≤ 2 w h . In this case the ratio is w a + w b w e + w f ≤ 2 β + ξ = 4( √ 13 − 1) / 7 < R . Supp ose now that the algorithm colle cted h in (F) (i. e. f = h ), and th us our gain is a ctually w e + w h ≥ (1+ β ) w h . If b ⊳ e , then the adve r sary amortized gain is w a + w b + w e + w h ≤ (2 β + 1) w h + w e . Th u s the ratio is w a + w b + w e + w h w e + w h ≤ 3 β + 1 β + 1 = 4( √ 13 + 10) / 17 < R . If e ⊳ b ⊳ h , the adv ersary’s amortized gain is w a + w b + w h ≤ (2 ξ + 1) w h , s o the ratio is w a + w b + w h w e + w h ≤ 2 ξ + 1 β + 1 = 2(5 √ 13 + 23) / 51 < R . If h ⊳ b , we n eed not giv e the adv ersary an y credit, gaining w a + w b ≤ 2 w h . So the ratio is less than the one ab o v e b ecause 2 ξ + 1 > 2. Case 3 : h is still p end in g in (H). In this case the stage has three steps and we collect e , f , and h , for the total gain of w e + w f + w h ≥ ( β + ξ + 1) w h . Th e adversary collects thr ee items a ⊳ b ⊳ c and ma y get credit for some items. If c ⊳ e , then the adv ersary gets credit for e , f and h , and his amortized gain is w a + w b + w c + w e + w f + w h ≤ 3 β w h + w e + w f + w h . So the ratio is w a + w b + w c + w e + w f + w h w e + w f + w h ≤ 4 β + ξ + 1 β + ξ + 1 = R . If e ⊳ c ⊳ f , then the adversary gets credit for f , h , and his amortized gain is w a + w b + w c + w f + w h ≤ 3 ξ w h + w f + w h . So the ratio is w a + w b + w c + w f + w h w e + w f + w h ≤ 4 ξ + 1 β + ξ + 1 = R . If f ⊳ c ⊳ h , then he only gets credit for h , so his amortized gain is w a + w b + w c + w h ≤ 4 w h . The ratio is w a + w b + w c + w h w e + w f + w h ≤ 4 β + ξ + 1 = 8(31 − 7 √ 13) / 27 < R . Finally , when h ⊳ c , the adv ersary amortized gain is w a + w b + w c ≤ 3 w h , w hic h is less than in the previous case. W e attempted to extend the idea of Algorithm DecQueEFH to stages with more steps, but according to numerical exp erimen ts we condu cted, this do es not impro ve the comp etitiv e ratio. 8 4.3 Upp er Bound of 1 . 8 for FIFO Queues W e no w extend the idea of the p revious algorithm to FIFO queues. Th e algorithm u ses tw o parameters, α and β . The main idea is this: If the hea viest item h ′ from the pr evious step is no longer p end ing, this is fine and it simp ly b egins another step. If h ′ is still p ending and new items ha ve b een inserted to th e queue, the algorithm in s p ects them. If the h ea viest new item h is not to o heavy (i.e., if αw h ≤ w h ′ ), the algorithm ignores n ew items and collects h ′ . If h is very hea vy ( αw h > w h ′ ), the algorithm f orgets ab out h ′ , resets he avy to h and colle cts the earliest pen d ing item e , suc h that w e ≥ β w h . Algorithm FIF OQueEH : By h we denote th e maxim um -w eigh t p end ing item and b y h ′ the pre- vious maximum-w eigh t p ending item (initially h ′ is an imaginary item of wei ght 0). W e use tw o parameters, 0 < α, β < 1. Wit h ou t loss of generalit y , we assum e that there are alw a ys p ending items, for w e can alw ays insert any num b er of 0-w eigh t items into the in stance, without c hanging the co mp etitiv e ratio. In the pseudo-co d e b elo w, we assume th at after eac h item collection the algorithm pro ceeds to the next step of the pro cess. let h b e th e h ea viest p end ing item and h ′ the previous h ea viest item (E) if ( h ′ is not p endin g) or ( h ′ is p endin g and αw h ≥ w h ′ ) then collect th e earliest item e w ith w e ≥ β w h (H) else collect h ′ Theorem 9 The c omp etitive r atio of FIFOQueEH with α = 3 4 and β = 2 3 is at most 1 . 8 . By insp ecting the d ecremental queue instance a ⊳ b ⊳ c ⊳ d , with w eight s w a = w b = β − ǫ , w c = β , w d = 1, and w eigh ts w a β , w b = w c = 1 − ǫ , w d = 1, one can observ e the follo wing. Theorem 10 The c omp etitive r atio of Algorithm FIF OQueEH is at le ast 1 . 8 , r e gar d less of the choic e of α and β . 4.4 Upp er Bound φ for Non-Decreasing W eigh ts In th is secti on we giv e an online algorithm Ma rkAndPick that is φ -comp etitiv e for dynamic qu eues when item w eigh ts are increasing. More precisely , if ⊳ d enotes the ord ering of th e items in the queue, then we assume that, at any time, for an y tw o activ e items a, b ∈ S , if a ⊳ b then w a ≤ w b . Algorithm MarkAndPick : A t eac h step t = 1 , 2 , ... if there is no p ending item then wai t, else let h b e th e h ea viest unmarked item (not necessarily activ e) mark h , collect th e earliest p end ing item i with w i ≥ w h /φ Basic ide a: The pro of is based on a c harging scheme, where the items collect ed by the adversary are c harged to our items in such a wa y that eac h our item is c harged at most φ times its w eigh t. In other w ords, eac h our item i has a bu dget φw i and it uses its budget to pay f or some items in the adv ersary’s set. In fact, eac h such i pa ys for either one or t wo adve r sary’s items. Th e c harging is 9 done in t wo steps: (1) we c h arge the adversary items to the mark ed items, and (2) we c harge the mark ed items to the algo rith m ’s items. When w e mark an item h , we collect an item i with w i ≥ w h /φ , so its b udget φw i is sufficien t to pa y for h . In a simp le scenario, if w e collect items in all steps, w e can afford to p a y f or all items mark ed in step (2). In step (1), we also show th at the w eigh t of the marke d items exceeds th at of the adv ersary , and these tw o facts easily imply φ -comp etitiv eness. In realit y , the situation is more complicated—in s ome mo ves MarkAndPick do es not h a v e an y items to collect. F or instance, su pp ose that the adve r sary collects an item j ′ in suc h a s tep. T his item is already collect ed b y the algorithm and is no w marke d . Its budget is φw j ′ , and it pa ys for its mark, as we ll as f or another item collected b y th e adve r s ary in th e past. Roughly , this is the item colle cted by the adv ersary when the algorithm w as marking j ′ . The prin ciple is, that any id le step is a consequence of a step in whic h the algorithm marked h = j ′ , collected an item i , and the adversary collec ted an item j smaller than i and still p ending for the algorithm. (This is not exactly correct, but it reflects the main p rinciple. It may happ en that the mark ed item h ”resp onsible” for the idle step in whic h the adv ersary collects j ′ is actually differen t fr om j ′ , but later in the pro cess h ”transfers” this resp onsibilit y to j ′ .) In that case, w j ≤ w j ′ /φ . W e refer to suc h j ’s as ”extra” items (ev en th ough those are not exactly the extra mo v es, but they cause extra mo ves later). This idea can b e f orm alised and pr o v ed rigorously . Theorem 11 Algorithm M a rkAndPick is φ -c omp etitive for dynamic queues if item weights ar e non-de cr e asing. 5 Dynamic Queues—Randomized Algorithms In this section, w e consider randomized algorithms for d y n amic queues. Chin et al. [4] designed a randomized algorithm RMix for b ound ed-dela y pac k et scheduling. This algorithm is memoryless and ac hieve s comp etitiv e ratio e / (e − 1) against an adaptiv e adve r sary . T he comp etitiv eness pro of for RM ix applies, with virtually n o c hanges, to d y n amic queues. In this section w e sho w th at this b ound is tigh t. Theorem 12 F or dynamic queues, any memoryless r andomize d algorith m has a c omp etitive r atio at le ast e e − 1 against an adaptive-online adversary. Basic ide a. W e fi x an online memoryless rand omized algorithm A . At th e b eginning A is giv en n + 1 items: a 0 , a 1 , . . . , a n , wh er e a = 1 + 1 n . W e consider n + 1 strategies for an adversary . Th e k -th (0 ≤ k ≤ n ) strategy is as follo ws: in eac h step collec t a k , d elete items a 0 , a 1 , ... , a k , an d issu e their new copies. If A collected a j for j > k , issue a cop y o f a j as w ell. Th is wa y , in eac h step exactly one cop y of eac h item is p ending for A , while the adv ersary accum ulates copies of the items a j for j > k . S ince A is memoryless, in eac h step it uses the same probabilit y distribu tion ( q j ) n j =0 , where q j is the probabilit y of collect in g a j . This step is rep eated T ≫ n times, and after the last step b oth the adv ersary and A collec t all their p end in g items. Sin ce T ≫ n , we may f o cus only on the exp ected amortized p rofit in a single step, whic h is a k + P i>k q i a i for the adv ersary and P i q i a i for A . By s olving a set of linear equations, w e sho w (non-constructive ly) that for any p robabilit y d istribution ( q j ) j , there exists k , for whic h the ratio b et w een these gains is at least e / (e − 1). 10 6 Final Commen ts W e pr ovided u pp er and lo wer b oun ds for the comp etitiv e ratio of sev eral v arian ts of the item selection p roblem. The most in triguing op en problems are to establish b etter b ounds for (1) dynamic queu e c ase and n on trivial b ound s f or (2) gener al r ando mize d c ase. F or (1), we ha ve sho wn a lo w er b ound of ≈ 1 . 63 (improving the lo w er b ound of φ ), but no upp er b ound b etter than 2 is kno wn. (Bett er b ounds are kno wn for pac k et scheduling [12, 6], but these algorithm u se inform ation ab out pac k et deadlines and d o not seem to app ly to d y n amic queues.) W e h a v e also shown b etter b ound s for some restricted cases: 1 . 8 for the FIF O queue (a generalizatio n of pac k et sc heduling with agreeable deadlines) and ≈ 1 . 737 for the decrementa l qu eue. F or (2), we ha ve an e / (e − 1) lo w er b ound , and w e ha ve sh o wn it is tight in th e uniform decremen tal case. References [1] N. Andelman, Y. Mansour, and A. Zhu. Comp etitive queueing po licies in QoS switches. In Pr o c. 14th Symp. on Discr ete A lgorithms (SODA) , pag es 761–77 0. ACM/SIAM, 2003. [2] Y. Azar and Y. Ric hter. An improv ed algorithm for CIO Q switc hes . In Pr o c. 12th Euro p e an Symp. on Algo rithms (ESA) , volume 3 221 of LNCS , pages 65–76 . Springer , 2004. [3] N. Bansal, L. Fleischer, T. K im br e l, M. Mahdian, B. Schieber, a nd M. Sviridenko. F urther improvemen ts in comp etitive guar antees for QoS buffering. In Pr o c. 31st International Col lo quium on A utomata, L anguages, and Pr o gr amming (ICALP) , volume 3142 of LNCS , pages 196–20 7 . Springer , 2 004. [4] F. Y. L. Chin, M. Chr obak, S. P . Y. F ung, W. Jaw or, J. Sgall, and T. Tich´ y. Online comp etitive algorithms for ma ximizing weigh ted throughput of unit jobs . Journal of Discr ete A lgorithms , 4 :255– 276, 2006. [5] F. Y. L. Chin and S. P . Y. F ung. Online scheduling for partial job v a lues: Does timesharing or randomizatio n help? Alg orithmic a , 37:149–1 64, 2003. [6] M. Englert and M. W esterman. Consider ing suppressed pa ck ets improv es buffer manag emen t in QoS switches. In Pr o c. 18th Symp. on Discr ete Algori thms (SODA) , pages 209–21 8. ACM/SIAM, 2 007. [7] S. Guti´ errez, S. O. Krumke, N. Meg ow, and T. V r edeveld. How to whack moles. The or. Comput. Sci. , 361(2):32 9–34 1 , 2 006. [8] B . Ha jek . On the comp etitiveness of online scheduling o f unit-leng th pac kets with hard deadlines in slotted time. In Confer enc e in Information Scienc es and Systems , pages 434–4 38, 2 001. [9] A. Kesselman, Z. Lotker, Y. Manso ur, B. Patt-Shamir, B. Schieb e r, and M. Sviridenko. Buffer ov erflow management in QoS switches. SIAM J . Comput. , 33 :563–5 83, 2004. [10] A. K esselman, Y. Mansour, and R. v an Stee. Improv ed competitive guarantees fo r QoS buffering. Algo rithmic a , 43 :63–80 , 2005. [11] F. Li, J. Seth ura man, and C. Stein. An optimal online a lg orithm for pack et scheduling with a greeable deadlines. In Pr o c. 16th Symp. on Discr ete Al gorithms (SODA) , pages 801–802. ACM/SIAM, 2005. [12] F. Li, J. Sethuraman, and C. Stein. Better online buffer management. In Pr o c. 18th Symp. on Discr ete Algo rithms (SODA) , pa ges 199–2 08. ACM/SIAM, 2007. 11 A The Uniform Case of Decremen tal Sets: Randomized Algo- rithms against Oblivious Adv ersaries In this part of app endix, we pro ve T heorems 2 and 3, i.e. w e sho w that for the uniform case of decremen tal sets: (i) the competitiv e ratio of an y randomized algo rith m is at least e / ( e − 1), (ii) the algorithm UniRand is e / (e − 1)-competitiv e. Ob viously , the lo wer b ound holds also f or n on-uniform cases as well. A.1 Lo wer B ound Fix any set size n and let R = n n +1 · e e − 1 . The pro of is based on Y ao’s m in-max p rinciple, i.e. w e construct a probabilit y distribu tion π o v er inputs, suc h that (i) the gain of an optimal solution is n on an y input sequen ce from the supp ort of π , and (i i) the exp ected gain of an y deterministic algorithm run on a rand omly chosen input fr om π is at most n/ R . W e constru ct the distribution π implicitly b y the follo wing r andom pro cess: at eac h step, c ho ose uniformly at random any activ e item a , colle ct it, and delete it after the step. Obviously , prop erty (i) holds, and it is sufficien t now to show (ii). Fix any deterministic algo rithm A . Without loss of generalit y , A alwa ys collec ts an item if one is p end ing. Let E a,p b e the exp ected num b er of items co llected b y A if a items are act ive and, among them, p items are p ending. If p = 0 , 1, then A collec ts p items. On the other hand , if p > 1, A collects an item in the first step, reducing the n umber of p endin g items to p − 1, and then, with probabilit y ( p − 1) /a another p ending eleme nt ma y get deleted. Hence, E a,p satisfies th e f ollo win g recurrence for an y a ≥ 1: E a, 0 = 0, E a, 1 = 1, and E a,p = a − p + 1 a · E a − 1 ,p − 1 + p − 1 a · E a − 1 ,p − 2 + 1 for a ≥ p ≥ 2. The follo wing tec h n ical lemma, can b e used to b ound the p erformance of an y deterministic algorithm on π . Lemma 13 F or al l a ≥ p ≥ 0 , we have E a,p ≤ ( a + 1)(1 − e − p/a ) + 1 . Pro of: W e prov e the lemma b y induction on p . Th e case p = 0 holds trivially . F or a ≥ p = 1, E a,p = 1 ≤ ( a + 1)(1 − e − 1 /a ) + 1, as ( a + 1)(1 − e − 1 /a ) > 0. F or a ≥ p ≥ 2, we u s e the ind uctiv e assumption and the recursiv e definition of E a,p , getting E a,p = a − p + 1 a · E a − 1 ,p − 1 + p − 1 a · E a − 1 ,p − 2 + 1 ≤ ( a − p + 1) 1 − e − p − 1 a − 1 + ( p − 1) a 1 − e − p − 2 a − 1 + 2 = a + 2 − e − p/a · h ( a − p + 1)e a − p a ( a − 1) + ( p − 1)e 2 a − p a ( a − 1) i ≤ a + 2 − e − p/a · ( a − p + 1) 1 + a − p a ( a − 1) + ( p − 1) 1 + 2 a − p a ( a − 1) = ( a + 1)(1 − e − p/a ) + 1 , 12 where th e s econd inequalit y follo ws from e x ≥ 1 + x . This completes the ind uctiv e step and the pro of of th e lemma. By Lemma 13, w e hav e that E n,n , the exp ected n umb er of items collected b y A , is at most ( n + 1)(e − 1) / e + 1 = n/ R + O (1). Th us, prop erty (ii) holds an d , applying Y ao’s p rinciple and taking the limit on n , w e obtain our lo we r b oun d. A.2 Upp er B ound In this part w e sh o w that th e algorithm UniRand (whic h at eac h step collec ts one r an d omly c hosen p endin g item) is e / (e − 1)-comp etitiv e. The id ea b ehind the comp etitiv e analysis is to pro ve fi r st that the optimal strategy of the adv ersary can b e easily describ ed: without loss of generalit y , at eac h step the adversary colle cts one item and dele tes the same item. Then w e a n alyze the comp etitiv e r atio of UniRand against suc h an adv ersary . The num b er of items in the initial set is denoted by n . By a w e d enote the num b er of activ e items at a giv en step, and b y p ≤ a the n um b er of p ending items. Note that p is a random v ariable. W e consider s tates of the game b et wee n UniRa nd and the adversary , conditioned on p b eing fixed, and we refer to s uc h a s tate as a c onfigur ation ( a, p ). The defi nition of Un iRand implies that in configuration ( a, p ) eac h activ e item is p ending with probabilit y p/a . Starting fr om eac h fixed configur ation ( a, p ), we analyze the relation b et wee n the gain of UniRand and that of the adv ersary . Since the items are identica l and UniR and ’s p ending items are distributed uniformly , we need not sp ecify wh ic h items are deleted by the adversary in a giv en step, only their n umb er. W e can split these steps into smaller parts: an elementary step consists in either collecting an item or deleting an item. W e can thus describ e the adv ersary’s strategy as a sequence S ∈ { t , d } ∗ , where t means that the adv ersary collects an item (and allo ws UniRan d to collect one as well, pro vided it has some p ending items) and d means that th e adve r sary d eletes an item. In th e follo wing w e consider only the fe asible strat egies S for configuration ( a, p ), i.e. those in wh ic h: (i) the n umb er of d op erations in S is a , (ii) in ev ery s u ffix of S the n umb er of t op erations do es not exceed the n umb er of d op erations. W e call strategy S a k - str ate g y if it con tains k t op erations, i.e. the gai n of the adversary on S is k . By E a,p [ S ] we denote the exp ected gain of Algorithm Un iRand starting from configuration ( a, p ), v ersus adve r s ary strategy S . The follo wing lemma shows that the b est strategy for the adv ersary , which guaran tees that the adv ersary tak es k element s, is ( td ) k run on k -elemen t set. Lemma 14 L et S b e a k -str ate gy for ( a, a ) . Then E a,a [ S ] ≥ E k ,k [( td ) k ] . On the other hand for these simple adversary strategie s, w e ma y appropriately b ound the E a,p v alues. Lemma 15 F or any inte gers p ≤ a , it holds that E a,p [( td ) a ] ≥ a (1 − (1 − 1 /a ) p ) . While w e pro ve the lemmas ab ov e in the follo wing subs ections, we argue now how they imply the comp etitiv eness of UniRan d . 13 Pro of: [of Theorem 3] W e fix an y n -element set and an y adv ersary’s s trategy S . Let k b e the n umb er of items collecte d b y the adv ersary . By Lemmas 14 and 15, the gain of UniRa nd is E n,n [ S ] ≥ E k ,k [( td ) k ] ≥ k (1 − (1 − 1 /k ) k ). Therefore, the comp etitiv e ratio is at m ost k E n,n [ S ] ≤ " 1 − 1 − 1 k k # − 1 < e e − 1 . A.2.1 Relations b et ween Adversary Strategies In this subsection, w e sho w wh y ( td ) k is the b est k -strategy . First, w e prov e tw o tec hnical lemmas. Lemma 16 F or any p < a and str ate gy S , it holds that E a,p +1 [ S ] ≥ E a,p [ S ] . Pro of: W e pro v e the inequalit y b y induction on pairs ( p, S ), where ( p 1 , S 1 ) < ( p 2 , S 2 ) if | S 1 | < | S 2 | or | S 1 | = | S 2 | an d p 1 < p 2 . The inductiv e basis is straigh tforw ard : if S = d a then E a,p +1 [ d a ] = 0 = E a,p [ d a ]. If p = 0, then clearly E a, 1 [ S ] ≥ 0 = E a, 0 [ S ]. In the ind uctiv e step, w e ha v e t w o cases dep endin g on th e fi rst action of S . If S = t S ′ , then E a,p +1 [ t S ′ ] = 1 + E a,p [ S ′ ] ≥ 1 + E a,p − 1 [ S ′ ] = E a,p [ t S ′ ], b y the ind u ctiv e assumption. If S = d S ′ , since w e ha v e p + 1 p ending items, th e adversary deletes a p ending item with probabilit y p +1 a and a non-p endin g item with probabilit y a − p − 1 a . Using the ind uctiv e assumption, w e get E a,p +1 [ d S ′ ] = a − p − 1 a E a − 1 ,p +1 [ S ′ ] + p + 1 a E a − 1 ,p [ S ′ ] ≥ a − p − 1 a E a − 1 ,p [ S ′ ] + 1 a E a − 1 ,p [ S ′ ] + p a E a − 1 ,p − 1 [ S ′ ] = E a,p [ d S ′ ] . Lemma 17 L et S = S 1 td S 2 b e a fe asible str ate gy for ( a, p ) . If S ′ = S 1 dt S 2 is also a fe asible str ate gy, then E a,p [ S ] ≥ E a,p [ S ′ ] . Pro of: Supp ose first that S = td S 2 . If p = 0, then the claim is ob vious, as E a, 0 [ S ] = E a, 0 [ S ′ ] = 0, and if p = 1, then E a, 1 [ S ] = 1 ≥ E a, 1 [ S ′ ]. So consider p > 1. By d ir ect calc ulation an d Lemma 16, w e get E a,p [ td S 2 ] = 1 + E a,p − 1 [ d S 2 ] = 1 + a − p + 1 a E a − 1 ,p − 1 [ S 2 ] + p − 1 a E a − 1 ,p − 2 [ S 2 ] ≥ 1 + a − p a E a − 1 ,p − 1 [ S 2 ] + p a E a − 1 ,p − 2 [ S 2 ] = a − p a E a − 1 ,p [ t S 2 ] + p a E a − 1 ,p − 1 [ t S 2 ] = E a,p [ dt S 2 ] . 14 No w consider the general case, when S = S 1 td S 2 and S ′ = S 1 dt S 2 . Then E a,p [ S ] = E a,p [ S 1 td S 2 ] = X i c i E a − k, p − i [ td S 2 ] E a,p [ S ′ ] = E a,p [ S 1 dt S 2 ] = X i c i E a − k, p − i [ dt S 2 ] for some k , { c i } . By the pr evious calculations, it holds that E a − k, p − i [ td S 2 ] ≥ E a − k, p − i [ dt S 2 ] for all i , and h en ce E a,p [ S ] = E a,p [ S 1 td S 2 ] = X i c i E a − k, p − i [ td S 2 ] ≥ X i c i E a − k, p − i [ dt S 2 ] = E a,p [ S 1 dt S 2 ] = E a,p [ S ′ ] , completing the pro of. Pro of: [of Lemm a 14] W e tak e any feasible k -strategy S starting from configur ation ( a, a ). It is straigh tforwa rd , that we may iterativ ely apply Lemma 17 and sw ap consecutive t and d op erations, obtaining a feasible str ategy d a − k ( td ) k at the end. Thus E a,a [ S ] ≥ E a,a [ d a − k ( td ) k ] = E k ,k [( td ) k ] A.2.2 Bound for the Best Adv ersary Strategy Pro of: [of Lemma 15] F or p = 0 , 1, E a,p [( td ) a ] = p and th e lemma trivially holds. Also if a = p = 2, then E a,p [( td ) a ] = 3 / 2 = a (1 − (1 − 1 /a ) p ) . F or the remaining v alues of a and p we pro ve the lemma by induction on a . W e note that for p ≥ 2 E a,p [( td ) a ] = a − p + 1 a E a − 1 ,p − 1 [( td ) a − 1 ] + p − 1 a E a − 1 ,p − 2 [( td ) a − 1 ] + 1 , as the p ending items are d istributed uniformly among activ e ite ms. Not e that this is the same 15 recurrence as in th e p ro of of the lo wer b ound . Thus, u sing the ind uction assumption, w e get E a,p [( td ) a ] ≥ a − p + 1 a ( a − 1) 1 − a − 2 a − 1 p − 1 ! + p − 1 a ( a − 1) 1 − a − 2 a − 1 p − 2 ! + 1 = a − ( a − 1) 2 a a − 2 a − 1 p − 2 1 + p − 2 ( a − 1) 2 ≥ a − ( a − 1) 2 a a − 2 a − 1 p − 2 1 + 1 ( a − 1) 2 p − 2 ≥ a − ( a − 1) 2 a a − 1 a p − 2 = a 1 − a − 1 a p , completing the pro of. B Deterministic A lgorithms for Dynamic Queues B.1 Lo wer Bo unds Pro of: [of Theorem 6] W e no w exhibit a sequen ce of 6 items for which Lemm a 5 holds with R ≈ 1 . 63. T o simp lify notation, we r ename the items: z 2 , z 4 , z 6 , z 3 , z 1 as x, y, z , u, v , r esp ectiv ely . Otherw ise w e follo w the aforement ioned idea. By Lemma 5, w e wan t to find num b ers x, y, z , u, v su c h that 0 < z < y < u < x < v < 1 and a maximal R for w hic h: R · x ≤ 1 R · 1 ≤ 1 + v R · ( v + y ) ≤ 1 + v R · (1 + v ) ≤ 1 + v + x + u R · ( v + u + z ) ≤ 1 + v + x R · (1 + v + u ) ≤ 1 + v + x + u + z W e can solve it by replacing in equalities by equations, and after doing substitutions, the problem reduces to fin ding a solution of a p olynomial equation x 5 + x 4 + 5 x 3 − x 2 − 1 = 0. This p olynomial has exact ly one real ro ot, x = 0 . 61238 ... , w hic h yields R = 1 . 6 329 ... . Pro of: [of Theorem 7] Fix a memoryless algorithm A . W e give an adv ersary’s strategy where the adv ersary’s gain is 2 − o (1) times A ’s gain. Pic k large integ ers n and T ≫ n , and let X = { x 0 , ... , x n } where w x i = 1 + i n for i = 0 , 1 , ..., n . The adve r sary maintains the inv ariant that at eac h s tep A ’s p ending set is X , with the items ordered b y increasing v alue. Supp ose that f or th is p ending s et A collects s ome item x k . 16 If k = 0, the ad versary collect s item x n , delet es all ite ms, inserts copies of all items from X again into the qu eue, and r ep eats the pro cess T times. A ’s gain is T w x 0 = T wh ile the optimum gain is T w x n = 2 T , so the ratio is 2. Supp ose no w that k ≥ 1. In this case, the adversary collects x k − 1 , d eletes all items x 0 , ... , x k − 1 for i = 0 , 1 , ..., k − 1 and inserts n ew copies of items x 0 , ... , x k . This p ro cess is rep eated T times. After T steps, the adv ersary collects the remaining uncollected items, in particular, all T copies of item x k . A can of course collect th e remaining p ending items. The v alue collected by A is at most T w x k + 2( n + 1) = T (1 + k /n ) + 2( n + 1), while the v alue collec ted b y the adv ersary is at least T ( w x k − 1 + w x k ) = T (2 + (2 k − 1) /n ). So with T = n 3 and n → ∞ the ratio app roac hes 2. B.2 Upp er B ound for FIF O Queues Pro of: [of Theorem 9] W e d efine stages of the algorithm. The first stage b egins b efore FIF OQueEH collects any item. Eac h next stage b egins immediately after previous stage end s. The stage ends when h is d eleted b y the adversary or condition (H) holds. The last step of the stage is th e last step t such that at b eginning of t , h ′ w as p endin g for FIF OQueEH . Let e 1 , e 2 , . . . e k b e th e s et of items collecte d (in this order) by FIFOQueEH in one stage when (E) condition held. Let h 1 , . . . , h k b e the corresp onding hea vy items. F r om the algorithm and the definition of FIF O queues, w e ha ve: F act 18 F or al l i = 1 , ..., k we have e i E h i (with al l r elations strict, e xc ept p ossibly for i = k ) and h i E h i +1 . The p ro of is b y amortized analysis. W e preserv e the in v arian t that, after eac h stage, eac h item i that is p endin g for the adv ersary but has already b een collecte d by FIF OQueEH has credit asso ciated with it of v alue equal w i . Th e adversary’s amortized gain is equal the his actual gain plus the tota l credit c hange. T o pr o v e the theorem, it is then sufficient to pr o v e the follo wing claim: ( ∗ ) In eac h stage the adv ersary’s amortized gain is at most 1 . 8 times FIF OQueEH ’s gain. W e pro ve ( ∗ ) for eac h of the follo wing cases (1) the stage ends b ecause the hea viest item is deleted, or (2) the stage ends b ecause FIF OQueEH collects h ′ . The second case has three sub -cases, dep end in g on whic h condition the latest item a collected b y the adv ersary satisfies: (2a) a ⊳ e l for some l ≤ k , (2b) e k E a ⊳ h k , or (2c) h k E a . Case 1 : The stage ended b ecause item h w as deleted. Th e adve rs ary cannot gain credit for an y items tak en b y the algorithm, as they are not pen d ing after that stage. Hence the ga in of the adv ersary is at most P k i =1 w h i . The gain of the algorithm is P k i =1 w e i . As w e i ≥ β w h i for all i , the comp etitiv e ratio is at most 1 β = 1 . 5. Case 2 : The stage end s, b ecause αw h k +1 < w h k and F IF OQueEH collected h k . Case 2a : S upp ose that a ⊳ e l for some l ≤ k , c ho ose minimal suc h l . Let c i = w e i − β w h i for i = 1 , . . . , l − 1. W e estimate th e amortized adv ersary’s gain: in step i ≤ l − 1 the hea viest p ending item is h i , and in s tep i ∈ { l . . . k + 1 } the adv ersary collects item preceding e l . If this item is still p endin g for the algorithm, its we ight is at most β w h l . If it is not p ending for th e algorithm, it is one of the e i ’s, for some i < l . Then the gain of the adv ersary is w e i = β w h i + c i < β w h l + c i . As w e can collect eac h suc h e i only once, all these steps add to at most ( k − l + 2) β w h l + P l − 1 i =1 c i . The adv ersary ge ts credit for all items ta ken by the algorithm in steps l , . . . , k + 1 that is P k i = l w e i + w h k . 17 Th u s the amortized gain of the adversary is at m ost l − 1 X i =1 w h i + ( k − l + 2) β w h l + l − 1 X i =1 c i + k X i = l w e i + w h k , On the other h and th e gain of the algorithm is k X i =1 w e i + w h k = l − 1 X i =1 ( β w h i + c i ) + k X i = l w e i + w h k . Hence for fi xed l , the comp etitiv e r atio of FIFOQueE H in the stag e is at most R 1 ,l = P l − 1 i =1 h i + ( k − l + 2) β h l + P l − 1 i =1 c i + P k i = l e i + h k P l − 1 i =1 β h i + P l − 1 i =1 c i + P k i = l e i + h k . F act 19 F or any γ , x, m > 0 and n > x , either n m < 1 γ or n − x m − γ x ≥ n m . W e u pp er-b ound R 1 ,l . All the follo wing inequalities follo w from F act 19 (for γ = 1 or γ = β ): R 1 ,l ≤ P l − 1 i =1 h i + ( k − l + 2) β h l + P k i = l e i + h k P l − 1 i =1 β h i + P k i = l e i + h k ≤ P l − 1 i =1 h i + ( k − l + 2) β h l + P k i = l β h i + h k P l − 1 i =1 β h i + P k i = l β h i + h k ≤ ( k − l + 2) β h l + P k i = l β h i + h k P k i = l β h i + h k = 1 + ( k − l + 2) β h l P k i = l β h i + h k . Fix k , l and h l . The f raction ab o v e is m aximal when h l +1 , . . . h k are m inimal. As αh i +1 ≥ h i , minimal h l , . . . h k form a geometric progression with a common ratio of α − 1 . Th us by taking h i = α k − i h k for i ≥ l and fixing m := k − l + 1 ≥ 1, w e obtain R 1 ,l ≤ 1 + ( k − l + 2) β h l P k i = l β h i + h k ≤ 1 + ( m + 1) β α m − 1 P m − 1 i =0 β α i + 1 = B m . F or m = 1 we ha ve B 1 = 1 + 2 β / (1 + β ) = 1 . 8 , and for m = 2 we h a v e B 2 = 1 + 3 β α/ ( β (1 + α ) + 1) = 1 + 9 / 13 < 1 . 8 . As f or m ≥ 3, we show that B m < B m − 1 : B m − 1 = ( m + 1) β α m − 1 β P m − 1 i =0 α i + 1 < ( m + 1) β α m − 1 β P m − 2 i =0 α i + 1 = = α · m + 1 m · mβ α m − 2 β P m − 2 i =0 α i + 1 ≤ mβ α m − 2 β P m − 2 i =0 α i + 1 = B m − 1 − 1 . Th u s all R 1 ,l are upp er-b ounded b y 1 . 8. Case 2b : Supp ose e k E a ⊳ h k . Th e adversary collecte d only the items preceding h k in the queu e, th us gaining at most h 1 + . . . + h k + 2 h k , as in step i ∈ { 1 . . . k − 1 } it can collect item of weig ht 18 greater than h i , in steps k , k + 1 it can collect items with w eigh t almost h k and gain credit for h k . Hence the comp etitiv e ratio of FIF OQueEH can b e upp er-b ounded by R 2 = P k i =1 h i + 2 h k P k i =1 e i + h k ≤ P k i =1 h i + 2 h k P k i =1 β h i + h k = B and b y F act 19 for γ = β either B < 1 β = 1 . 5 or B ≤ h k + 2 h k β h k + h k = 3 1 + β = 1 . 8 . Case 2c : Su pp ose h k E a . Th en he cannot get credit for an y item tak en b y the algorithm, d u e to the EEF prop ert y . In this case the adversary’s gain is at most h 1 + . . . + h k +1 , w hic h give s smaller ratio than the one obtained in case (2b), as α > 1 2 . This concludes the pr o of. Pro of: [of Theorem 10] Consider t w o instances. In the first one, w e ha ve a ⊳ b ⊳ c ⊳ d , with w a = w b = β − ǫ , w c = β , w d = 1. Item a is d eleted righ t after the first step, and item b righ t after the second step. FIF OQueEH collects c in th e firs t step and d in the second step, while the adv ersary collec ts all four items. Adv ersary’s ga in is 1 + 3 β − 2 ǫ and the FIF OQueEH ’s gain is 1 + β . Th u s the comp etitiv e ratio is arb itrarily close to (3 β + 1) / ( β + 1). In the second in s tance, a ⊳ b ⊳ c ⊳ d , with w a = β , w b = w c = 1 − ǫ , w d = 1. Items a , b and c are deleted righ t after the second step. FIFOQueEH col lects a in the first step and d in the second step, so its gain is 1 + β . T h e adv ersary collects b , c , d (in th is ord er), so h is gain is 3 − 2 ǫ . Thus the comp etitiv e ratio is arbitrarily close to 3 / (1 + β ). F rom these tw o instances, we get that the ratio of FIFOQueE H is at least max { 3 β + 1 , 3 } / ( β + 1), and this quan tit y is at least 1 . 8 for any β . B.3 Upp er B ound for Non-Decreasing W eigh ts Set dominance relation. Let X , Y b e t w o finite sets of num b ers. W e sa y that X dominates Y , denoted X Y , if either Y = ∅ or max X ≥ max Y and ( X − max X ) ( Y − max Y ). Note that w e do not require that | X | = | Y | . In particular, X ∅ , for any X . F or any set T and a n umb er u , let ♯ u ( T ) = |{ t ∈ T : t ≥ u }| . W e sho w that the ma j orization can b e d escrib ed in terms of ♯ u The follo wing lemma is routine and we omit the pro of. Lemma 20 The fol lowing thr e e c onditions ar e e quivalent: (i) X Y , (ii) Ther e is an inje ction f : Y → X such that f ( y ) ≥ y for al l y . (iii) F or eve ry x we have ♯ x ( X ) ≥ ♯ x ( Y ) . Lemma 21 Supp ose that X Y 6 = ∅ . Then (i) X − min X Y − min Y . (ii) If x ∈ X ∩ Y then X − x Y − x . 19 (iii) If X, Y ⊆ Z , y ∈ Z − Y , and x ≥ m ax { z ∈ Z − X : z ≤ y } then X ∪ x Y ∪ y . (In p articular , this holds for x ≥ y . ) Pro of: P arts (i) and (ii) are straigh tforwa r d , so we only sho w (iii). Let x ′ = max { z ∈ Z − X : z ≤ y } . It is sufficien t to sho w (iii) for x = x ′ . W e u se Lemm a 20(iii). F or u ≤ x ′ , since X Y , we h a v e ♯ u ( X ∪ x ′ ) = ♯ u ( X ) + 1 ≥ ♯ u ( Y ) + 1 = ♯ u ( Y ∪ y ). F or u > y , we ha v e ♯ u ( X ∪ x ′ ) = ♯ u ( X ) ≥ ♯ u ( Y ) = ♯ u ( Y ∪ y ). Supp ose x ′ < u ≤ y . Since y ∈ Z − Y and X ∩ [ u, y ] = Z ∩ [ u, y ], we ha v e | X ∩ [ u, y ] | > | Y ∩ [ u, y ] | , and therefore ♯ u ( X ∪ x ′ ) = ♯ u ( X ) ≥ ♯ u ( Y ) + 1 = ♯ u ( Y ∪ y ). F or simplicit y , we assume that all weig hts are d ifferen t. If th er e are equal weig hts, w e can p erturb them sligh tly or extend the weigh t ordering us ing the item indices. F or sets B a n d C of items, w e sa y that B d ominates C , writing B C , if { w b : b ∈ B } dominates { w c : c ∈ C } . W e write B aC if { w b : b ∈ B } dominates { aw c : c ∈ C } . Assume that the adv ersary has EEF prop erty . Consider the b ehavio r of the adve rs ary . By the EEF prop ert y , for an y i, j ∈ S , we can assume that if j is the ite m collected in step t and i ⊳ j then the adv ersary will not collect item i in the f uture. Thus, ins tead of considering the whole set of p endin g adv ersary items, w e can restrict our s elv es only to those that are after the one he collected last. Let C t b e the set of these items. W e up date C t as follo ws: at eac h step, the deleted items are remo v ed from C t and released items are ad d ed to C t . Then, if the adv ersary collects an item j , w e remo v e all items i E j from C t . T o organize the ac counting so that w e can pa y for these extra items, w e do t w o things. One, we do not im m ediately giv e Mark And Pick credit for the collect ed items. W e giv e it credit for colle cting i only at the time when the adv ersary collects an item at least as hea vy as i . This is formalized b elo w in Lemm a 22 where the collected items i th at are hea vier than the maxim um adv ersary item con tribute to the b oth sides of in v arian t (a) (they get includ ed in L t and L ′ t ), and only wh en the adv ersary co llects an item greater than i , item i will b e remo v ed from L ′ t and con tribute to preserving the inv ariant. Next, w e k eep trac k of th e adve r s ary’s extra items so that w e can pa y for th em later. When the adve rs ary collects an extra item j and we mark h , we kno w that w j ≤ w h /φ . W e store j in a separate set E ′ and h in M ′ . Later, wh en there is an idle step at whic h the adv ersary colle cts h , since h has already b een collected by the algorithm, its bud get φw h pa ys b oth for w h (for the m ark on h ) and for w j . Once the adv ersary ”consumed” the extra step by co llecting h , we mo v e j to the set E of the extra adv ersary items that w e already paid for. W e r ep resen t our inv ariant s in terms of the domination relations b et w een some v arying sets of items. The r eason for this is that items can b e added and remo v ed from these sets in this pro cess, and it do es not seem p ossible to mainta in appropriate b oun ds only b etw een the total w eights of these sets. Notation: Symbols D t , M t , and L t represent resp ectiv ely the sets of items co llected b y the adv ersary , mark ed b y the algorithm, and collec ted by Algorithm MarkAndPick up to and including step t . L ′ t = L t ∩ C t is the set of algorithm’s items that the adv ersary ma y still collec t in the future. Let also e t = | D t | − | M t | and ℓ t = | L ′ t | . Figure 1 illustrates this notation, as wel l as the sets in tro d uced in the lemma b elo w. Lemma 22 F or e ach time step t , ther e e xi st disjoint sets E t , E ′ t ⊆ D t with | E t | = e t and | E ′ t | = ℓ t , and a set M ′ t ⊆ M t with | M ′ t | = ℓ t , such that 20 Figure 1: Notati on. (a) φw ( L t − L ′ t ) ≥ w ( M t − M ′ t ) + w ( E t ) , (b) φL ′ t M ′ t L ′ t , (c) M t ( D t − E t − E ′ t ) ∪ L ′ t , and (d) M ′ t φE ′ t . Pro of: W e sh o w that the inv arian t in th e lemma is preserve d . F or simplicit y , we omit the sub script t and write D = D t , M = M t , etc. Also, let ∆ w ( D ) = w ( D t +1 ) − w ( D t ), ∆ w ( M ) = w ( M t +1 ) − w ( M t ), and so on. W e view the pro cess as follo ws: at eac h step, (I) The adv ersary first inserts items into S , (I I) then he select s the item j to b e collect ed, (I I I) n ext, the adv ersary d eletes some items f r om S (of course, only the items that are b efore j in S can b e deleted), (IV) finally , b oth the ad versary and the algorithm collect their items. In order to sh o w (a), w e need to sho w that φ ∆ w ( L ) + ∆ w ( M ′ ) ≥ φ ∆ w ( L ′ ) + ∆ w ( M ) + ∆ w ( E ) . (3) In addition, we need to sh o w that (b), (c) and (d) are preserv ed. W e look at all sub -steps separately . (I) In sertions do not affect the in v arian ts. (None of the sets M , D , L , L ′ c hanges, and we do not c hange sets M ′ , E , and E ′ .) In (I I), supp ose the adv ersary s elects j and j ′ w as an item collect ed b y the adv ersary in the previous step. T h ere ma y ha ve b een some items i , j ′ ⊳ i ⊳ j , th at we re in L ′ . Since these items are n o w remo v ed from C , they are also remov ed from L ′ , and w e n eed to up date M ′ and E ′ so that they ha ve the same cardinalit y as L ′ , and in suc h a wa y that the in v ariants a r e preserve d . Let i ∈ L ′ b e suc h an item with min imum w eight , g the minim um-weig ht item in M ′ and e the m inim um-weigh t item in E ′ . W e remo ve i from L ′ , g from M ′ and e from E ′ . Since φw i ≥ w g , b y (b), w e hav e 21 φ ∆ w ( L ) + ∆ w ( M ′ ) = 0 − w g ≥ − φw i + 0 + 0 = φ ∆ w ( L ′ ) + ∆ w ( M ) + ∆ w ( E ), so (a) is preserved. In v arian ts (b) and (d) are preserved b ecause we remo v e the minimum items from L ′ , M ′ , and E ′ . In (c), the left-hand side does not c hange and on the righ t-hand side we remo ve i from L ′ and add e to D − E − E ′ , and by (b) and (d) w e ha ve w i ≥ w g /φ ≥ w e , so the righ t-hand side cann ot in crease. In sub-step (I I I), deletions do not affect the inv arian ts. The rest of the pro of is d ev oted to su b-step (IV). W e examine (3) and the c hanges in (b), (c) and (d) d ue to the algorithm and the adv ersary collecting their items. Case A : There is at least one p ending item. T he algorithm mark s h and collects the earliest p ending item i suc h that w i ≥ w h /φ . Th u s h is added to M and i is added to L . W e do not c hange E . W e ha ve s ome sub-cases. Case A.1 : i E j . Then i is not added to L ′ , and w e do not c hange E ′ . Since φ ∆ w ( L ) = φw i ≥ w h = ∆ w ( M ) and ∆ w ( E ) = 0, to prov e (3 ) it is now suffi cient to show that ∆ w ( M ′ ) ≥ φ ∆ w ( L ′ ) . (4) If j / ∈ L (note that this included the case i = j ), then L ′ do es not c h ange and we do n ot c hange M ′ , so (4) is trivial. In (b) and (d) n othin g change s. W e add the maxim um unm ark ed item h to M and j to D , so (c) follo ws from Lemma 21(iii). If i 6 = j an d j ∈ L and th en let g b e the minimum item in M ′ and e the minimum item in E ′ . Item j is r emo v ed from L ′ and we r emo v e g fr om M ′ and e fr om E ′ . Since, by (b), φw j ≥ w g , we ha ve ∆ w ( M ′ ) = − w g ≥ − φw j = φ ∆ w ( L ′ ), so (4) holds. Since j , g and e are minimal, (b) and (d) are preserved. In (c), moving j from L ′ to D do es not c hange the right-hand side. W e also add h to M and e to D − E − E ′ ∪ L ′ , so (c) is preserved b ecause of the choic e of h and Lemma 21(iii). Case A.2 : i ⊲ j and j / ∈ L . T hen i is added to L ′ . W e also add j to E ′ . Since ∆ w ( L ) = ∆ w ( L ′ ) = w i and ∆ w ( M ) = w h , to sho w (3) it is su ffi cien t to sho w that ∆ w ( M ′ ) ≥ w h . (5) Since | L ′ | increased, w e need to add one item f to M ′ . W e choose th is f as follo ws: If i E h , w e c ho ose f = h . Otherwise, if i ⊲ h then, b y the choic e of h , w e ge t that all ite ms h E f E i are no w marke d . In this case, we c h o ose the largest f E i suc h that f / ∈ M ′ and add it to M ′ . Since h ∈ M − M ′ , h itself is a candidate for f , so we hav e h E f E i . Note that, in this case, b y th e c hoice of i (as the earliest p ending item with w eight at least w h /φ ), j ⊳ i and j / ∈ L , w e ha ve w f ≥ w h ≥ φw j . In particular, this means that j ⊳ h and that all items h E f ′ ⊳ i are in L ′ . Since w f ≥ w h , (5) is trivial. In v arian t (d) is also quite easy , since w f ≥ φw j , by the previous paragraph. In (c), addin g j to D and E ′ do es not c hange the righ t-hand side. W e also add h to M and i to L ′ , w hic h preserves (c) by the c hoice of h and Lemma 21(iii). T o show (b), if i E h then f = h and , since φw i ≥ w h ≥ w i , inv ariant (b) is p r eserv ed. If i ⊲ h , then, φw i ≥ w i ≥ w f , s o the first part of (b) is pr eserv ed. That the second p art of (b) is preserv ed follo ws from the c hoice of f and Lemma 21( iii). Case A.3 : i ⊲ j and j ∈ L . Then we remo v e j from L ′ and add i . W e thus ha ve ∆ w ( L ) = w i , ∆ w ( L ′ ) = w i − w j and ∆ w ( M ) = w h . Th us to sho w (3) it is sufficien t to sho w that ∆ w ( M ′ ) + φw j ≥ w h . (6) 22 W e do not c hange E ′ . T o u p date M ′ , w e pro ceed as follo ws. Let g b e the lightest item in M ′ . Since j is th e minimal ele ment of L ′ , (b) implies w j ≤ w g ≤ φw j . W e first remov e g fr om M ′ . Next, we pro ceed similarly as in the previous case, lo oking for an item f that we can add to M ′ to comp ensate for remo ving g (since | M ′ | cannot c hange in this case.) Let h ′ = max( g , h ). Note that h ′ ∈ M − M ′ . If i E h ′ , we c ho ose f = h ′ . Otherwise, if i ⊲ h ′ then, by the c hoice of h ′ , we get that all activ e items h ′ E f E i are mark ed. In this case, we c ho ose the largest f E i su c h that f / ∈ M ′ and add it to M ′ . Since h ′ ∈ M − M ′ , h ′ itself is a candidate for f , so w e ha v e h ′ E f E i . Note th at, in this case, b y j E g , all items h ′ E f ⊳ i are activ e and, by the c hoice of i , they are all in L ′ . No w, in (6) we hav e ∆ w ( M ′ ) + φw j = ( − w g + w f ) + φw j ≥ w f ≥ w h ′ ≥ w h . In (d), the left-hand side can on ly increase (since f ≥ g ) and the righ t-hand sid e do es not change . I n (c) , mo ving j from L ′ to D do es not change the righ t-hand side. W e also added h to the left-hand s id e and i to L ′ on the righ t-hand side, so (c) is p reserv ed by the c hoice of h and Lemma 21(iii). In (b), remo ving j from L ′ and g from M ′ do es not a ffect the inv arian t. Th en we add f to M ′ and i to L ′ . By the algorithm, we ha ve φw i ≥ w h , wh ile by the case assu mption and (b), we ha ve φw i ≥ φw j ≥ w g . Therefore φw i ≥ w h ′ . Since either f = h ′ or f E i , this implies φw i ≥ w f , sho wing that the fir s t inequalit y in (b ) is preserved. The second part of (b) follo ws again from th e c hoice of f and Lemma 21(iii). Case B : There are no p endin g items for the algorithm. It means that L ′ con tains all activ e items i D j , includ ing j . By the w eight ord ering assumption and th e second p art of (b) this implies that L ′ = M ′ . Since the adversary collects an item and the algorithm d o es not, e = | D | − | M | increases b y 1, so w e also n eed to add an item to E . Let b b e the minim um -weigh t item in E ′ . W e do this: w e r emo v e j f rom M ′ and from L ′ and w e mov e b from E ′ to E . Using the c hoice of b and (d) w e ha ve w j ≥ φw b , so φ ∆ w ( L ) + ∆ w ( M ′ ) = 0 + ( − w j ) = − φw j + w j /φ ≥ ≥ − φw j + 0 + w b = φ ∆ w ( L ′ ) + ∆ w ( M ) + ∆ w ( E ) , and thus (3) h olds. By the c hoice of j and e as the m inim um ite ms in L ′ and E ′ , resp ectiv ely , in v arian ts (b) and (d ) are pr eserv ed. In (c), j mo v es f r om L ′ to D , and b mov es from E ′ to E , so the righ t-hand side do es not c hange. Pro of: [of Theorem 11] By the inv ariants of Lemma 22, at eac h time step it h olds that φw ( L t ) ≥ [ φw ( L ′ t ) − w ( M ′ t )] + w ( M t ) + w ( E t ) ≥ 0 + [ w ( D t − E t − E ′ t ) + w ( L ′ t )] + w ( E t ) = w ( D t ) + w ( L ′ t ) − w ( E ′ t ) ≥ w ( D t ) + w ( M ′ t ) /φ − w ( E ′ t ) ≥ w ( D t ) , and the φ -comp etitiv eness follo ws. C Randomized Algorithms for Dyn amic Queues Pro of: [of Theorem 12] Fix some online memoryless rand omized algorithm A . Recall that by a memoryless algorithm w e mean an algorithm that m ak es a decision on whic h item to col lect based only on the weig hts of the p ending items. 23 W e consider the follo win g sc heme. Let a > 1 b e a constan t w h ic h w e sp ecify later and n b e a fixed integ er. At the b eginning, the adversary inserts items a 0 , a 1 , . . . , a n . (T o simplify notation, in this pro of w e ident ify items w ith their w eigh ts.) In our constru ction w e assure that in eac h step, the list of items which are p ending for A is equal to ( a 0 , a 1 , . . . , a n ). S ince A is memoryless, in eac h step it uses the same probabilit y distribu tion ( q j ) n j =0 , where q j is the probabilit y of collecting item a j . As the algorithm alwa ys mak es a mo v e, P n i =0 q i = 1. W e consider n + 1 strategies for an adv ersary , num b ered 0 , 1 , . . . , n . The k -th strateg y is as follo ws: in eac h step collect a k , d elete all items a 0 , a 1 , ... , a k , an d then issue new copies of all these items. Additionally , if the algorithm collec ted a j for some j > k , then the adv ersary issues a new cop y of a j as wel l. T h is w ay , in eac h step exactly one cop y of eac h a j is p ending for the algorithm, while the adv ersary accum ulates copies of the items a j for j > k . This step is rep eated T ≫ n times, and after the last step the adv ersary collects all uncollected items. Since T ≫ n , we only need to fo cus on the exp ected amortize d profits in a sin gle step. W e lo ok at the gains of A and the adversary in a single step. If the adv ersary c ho oses strategy k , then it gains a k . Add itionally , at the end it collects the item collected by the algorithm if this item is greater than a k . Th us, its amortized exp ected gain in single step is a k + P i>k q i a i . Th e exp ected gain of A is P i q i a i . F or an y probabilit y distribution ( q j ) n j =0 of the algorithm, the adv ersary c ho oses a s tr ategy k whic h maximizes the comp etitiv e r atio. Th us, the comp etitiv e ratio of A is is at least R = max k ( a k + P j >k q j a j P j q j a j ) ≥ X k v k a k + P j >k q j a j P j q j a j , for an y coefficients v 0 , ... , v k ≥ 0 suc h that P k v k = 1. Note that the latter term corresp onds to the ratio forced b y a randomized adversary who chooses k with pr obabilit y v k . In particular, w e may c ho ose v k to b e the v alue f or whic h the comp etitiv e ratio of su c h a r andomized adv ersary strategy against any deterministic algorithm is the same. After solving the set of equations w e get v k = ( 1 M a n − k ( a − 1) if k < n 1 M ( a − n ( a − 1)) if k = n where M = a n +1 − n ( a − 1) . F or these v alues of v k w e get M R P j q j a j ≥ X k M v k a k + X k M v k X j >k q j a j = n − 1 X k =0 M v k a k + M v n a n + X j q j a j X k
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment