Multi-Channel MAC Protocol for Full-Duplex Cognitive Radio Networks with Optimized Access Control and Load Balancing
In this paper, we propose a multi-channel full-duplex Medium Access Control (MAC) protocol for cognitive radio networks (MFDC-MAC). Our design exploits the fact that full-duplex (FD) secondary users (SUs) can perform spectrum sensing and access simul…
Authors: Tan Le Thanh, Long Bao Le
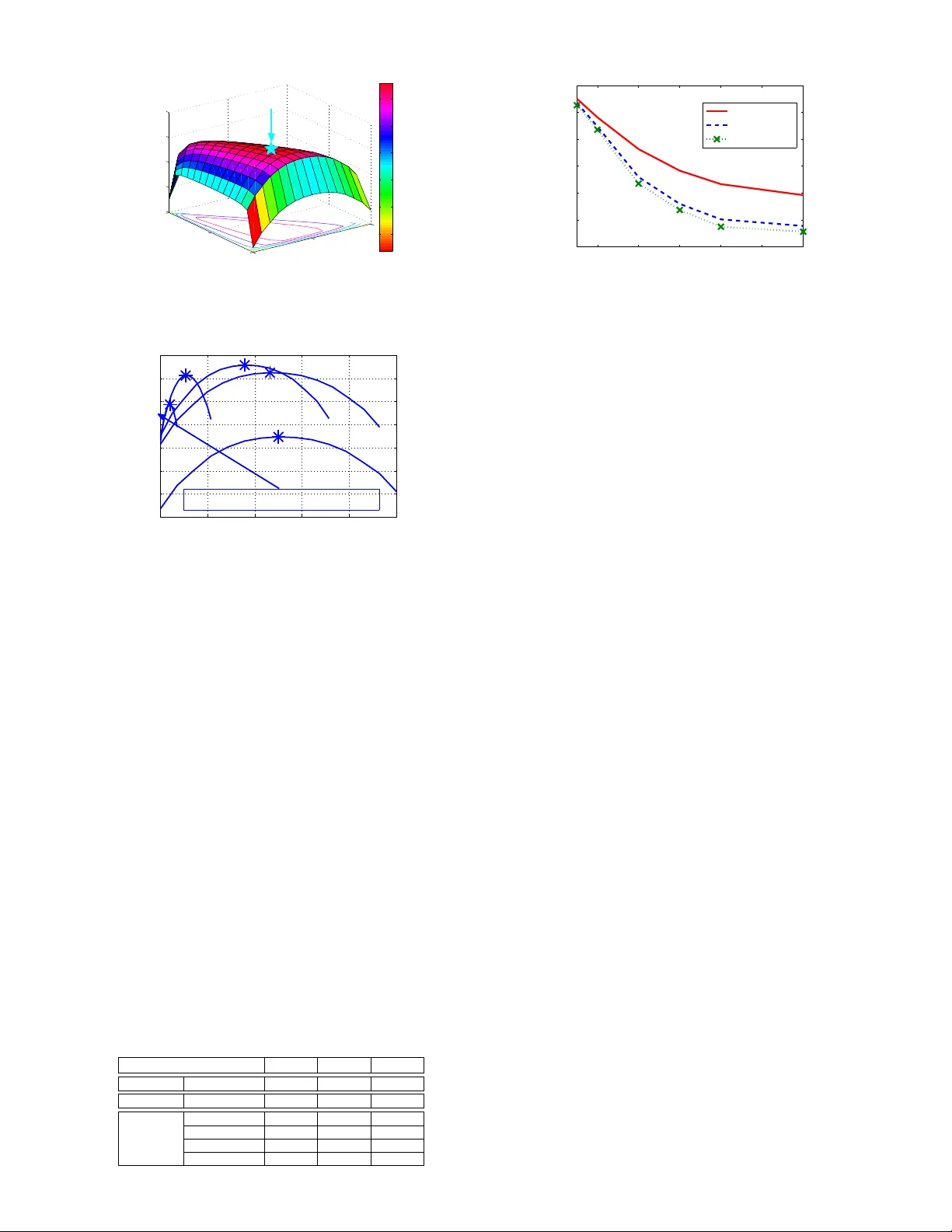
1 Multi-Channel MA C Protocol for Full-Duple x Cogniti v e Radio Netw orks with Optimized Access Control and Load Balancing Le Thanh T an and Long Bao Le Abstract —In this paper , we pr opose a multi-channel full-duplex Medium Access Control (MA C) protocol f or cognitive radio networks (MFDC–MA C). Our design exploits the fact that full- duplex (FD) secondary users (SUs) can perform spectrum sensing and access simultaneously , and we employ the randomized dynamic channel selection for load balancing among channels and the standard backoff mechanism for contention resolution on each a vailable channel. Then, we develop a mathematical model to analyze the throughput performance of the proposed MFDC– MA C protocol. Furthermore, we study the protocol configuration optimization to maximize the network throughput wher e we show that this optimization can be performed in two steps, namely optimization of access and transmission parameters on each channel and optimization of channel selection probabilities of the users. Such optimization aims at achie ving efficient self- interference management f or FD transceivers, sensing ov erhead control, and load balancing among the channels. Numerical results demonstrate the impacts of different protocol parameters and the importance of parameter optimization on the throughput performance as well as the significant performance gain of the proposed design compared to traditional design. Index T erms —MA C protocol, spectrum sensing, optimal sens- ing, throughput maximization, full-duplex cognitive radios. I . I N T R O D U C T I O N Design of MA C protocols for efficient sharing of white spaces and appropriate protection of transmissions from pri- mary users (PUs) on licensed frequency in cognitive radio networks (CRNs) is an important research topic. In the tra- ditional design and analysis of a half-duplex (HD) MA C protocol [1], [2], [3], [4], [5], SUs typically employ a two- stage sensing/access procedure due to the HD constraint [3], [4], [5]. This constraint also requires SUs be synchronized during the spectrum sensing stage, which could be difficult to achiev e in practice. Moreover , sophisticated design and parameter configuration of cognitive MA C protocols can result in significant performance enhancement while appropriately protecting SUs [4], [5]. Furthermore, dif ferent multi-channel cognitiv e MAC protocols were proposed considering either different spectrum sensing and access methods [1], [2]. By employing the advanced FD transceiv er , each SU can transmit and receiv e data simultaneously on the same fre- quency band [7]. Practical FD transceivers, howe ver , suffer from self-interference, which is caused by power leakage from the transmitter to the recei ver . The self-interference may indeed lead to serious communication performance degrada- tion of FD wireless systems. Emplo yment of FD transceiv ers for more efficient spectrum access design in cognitive radio networks has been very under explored in the literature. The cognitiv e MAC design in one recent work [6] allo ws SUs to The authors are with INRS-EMT , Uni versity of Quebec, Montr ´ eal, Qu ´ ebec, Canada. Emails: { lethanh,long.le } @emt.inrs.ca. perform sensing and transmission simultaneously; howe ver , the work [6] assumes simultaneous spectrum access of the SU and PU networks. This design is, therefore, not applicable to the hierarchical spectrum access in the CRNs where PUs should hav e higher spectrum access priority compared to SUs. In this paper , we propose a nov el MFDC–MAC protocol that allo ws concurrent spectrum sensing and transmission on each channel as well as efficient access and load balancing among the channels. In our design, each SU adopts the randomized channel selection to choose its channel, which is slowly updated over time for load balancing. Moreover , SUs employ the standard p -persistent CSMA mechanism for contention resolution on the selected channel, and the winning SU follows a two-stage procedure for spectrum sensing and access. Specifically , the winning SU performs simultaneous sensing and transmission during the first stage and transmis- sion only in the second stage. This design enables appropriate protection of PUs and efficient exploitation of white spaces on all the channels. W e develop a mathematical model for throughput perfor- mance analysis of the proposed MFDC-MA C protocol con- sidering the imperfect sensing and self-interference effects. Moreov er , we study the optimal configuration of different protocol parameters for spectrum sensing, access, and load balancing (i.e., channel access probabilities) to achieve the maximum throughput. Extensiv e numerical results are then presented to illustrate the impacts of different protocol pa- rameters on the throughput performance and the significant throughput gains of the proposed MFD-MA C protocol with respect to conv entional designs. The remaining of this paper is organized as follows. Section II describes the system and PU activity models. MA C protocol design and throughput analysis are performed in Section III. W e discuss the protocol optimization in Section IV . Section V demonstrates numerical results followed by concluding remarks in Section VI. I I . S Y S T E M A N D P U A C T I V I T Y M O D E L S A. System Model W e consider a network setting where N pairs of SUs oppor- tunistically exploit white spaces on M frequency channels for data transmission. W e assume that each SU is equipped with one full-duplex transcei ver , which can perform sensing and transmission simultaneously . Howe ver , any SU suffers from self-interference from its transmission during sensing (i.e., transmitted signals are leaked into the received signal). At channel j , we denote I j as the average self-interference po wer , which is assumed to be modeled as I j = ζ ( P sen ,j ) ξ [7] where P sen ,j is the SU transmit po wer , ζ and ξ ( 0 ≤ ξ ≤ 1 ) are 2 Active sensing SU DATA time CTS RTS/CTS exchange DIFS RTS SIFS SIFS DATA SIFS ACK Data Transmission DATA 1 DATA 2 FD Channel is available DATA 1 FD Channel is not available I C . . . C I U Contention and access cycle . . . DATA RTS DIFS Collision . . . Collision (C) Idle (I) Successful channel reservation (U) Contention and access cycle eva T T eva T T Active sensing SU ove T PU activity 1 t Data phase Contention phase PU activity 1 t PU activity 00 h 00 h 01 h 11 h 00 h 01 h S T T S T T Sensing stage Tx stage Sensing stage Tx stage Case 1 ! 00 00 , h h Case 2 ! 00 01 , h h Case 3 ! 01 11 , h h Fig. 1. T iming diagram of the proposed full-duplex MAC protocol. predetermined coefficients which capture the self-interference cancellation quality . W e design an asynchronous MA C pro- tocol where no synchronization is required between SUs and PUs as well as among SUs. W e assume that different pairs of SUs can ov erhear transmissions from the others (i.e., a collocated network). In the following, we refer to pair i of SUs simply as SU i . B. Primary User Activity W e assume that the PU’ s idle/busy status follows two independent and identical distribution processes. In particular, each channel is av ailable and busy for the secondary access if the PU is in the idle and b usy states, respectively . Let H 0 and H 1 denote the events that the PU is idle and acti ve, respectiv ely . T o protect the PU, we assume that SUs must stop their transmission and ev acuate from the channel within the maximum delay of T eva , which is referred to as channel ev acuation time. Let τ j ac and τ j id denote the random variables which represent the durations of channel activ e and idle states on channel j , respectiv ely . W e assume that τ j ac and τ j id are larger than T eva with high probability . W e denote probability density functions of τ j ac and τ j id as f τ j ac ( t ) and f τ j id ( t ) , respectiv ely . In addition, let P H j 0 = ¯ τ j id ¯ τ j id + ¯ τ j ac and P H j 1 = 1 − P H j 0 present the probabilities that the channel is av ailable and busy , respectiv ely . I I I . M U LT I - C H A N N E L F U L L - D U P L E X C O G N I T I V E M AC P RO TO C O L In this section, we describe our proposed MFDC-MA C protocol and conduct its throughput analysis considering im- perfect sensing and self-interference of the FD transceiv er . A. MFDC–MAC Pr otocol Design In our MFDC-MA C protocol, each SU randomly selects one channel by using a randomized channel selection mechanism where channel j is selected with probability p sec j . In this paper, we consider the general heterogeneous scenario where the statistical parameters τ j ac and τ j id of different channel j can be different. This channel selection is repeated once after a predetermined long period, which is an order of magnitude larger than the av erage contention/access time to transmit one data frame (packet) on each channel (e.g., every K max data frames). After channel selection, each SU employs the follo wing single-channel contention, spectrum sensing, and transmission to exploit the white space. Specifically , SUs choosing the same channel j is assumed to employ the p -persistent CSMA principle [9] for contention resolution where each SU attempts to capture the channel with a probability p after the channel is sensed to be idle during the standard DIFS interval (DCF Interframe Space). If a particular SU decides not to transmit (with probability of 1 − p ), it will carrier sense the channel and attempt to transmit again in the next slot with probability p . T o complete the reservation, the four-way handshake with Request-to-Send/Clear-to-Send (R TS/CST) exchanges [9] is employed to reserve the av ailable channel for transmission in the next phase. After each successful transmission of du- ration T j , an ackno wledgment (A CK) from the SU’ s receiv er is transmitted to its corresponding transmitter to notify the successful reception of a packet. Furthermore, the standard small interval, namely SIFS (Short Interframe Space), is used before the transmissions of CTS, A CK, and data frame as in the standard 802.11 MA C protocol [9]. Then, the data phase after the channel contention phase comprises two stages where the winning SU performs concur- rent sensing and transmission in the first stage with duration T S,j (called FD sensing stage) and transmission only in the second stage with duration T j − T S,j (called transmission stage). Here, the SU exploits the FD communication capability of its transceiver to realize concurrent sensing and transmission the first stage where the sensing outcome at the end of this stage (i.e., an idle or activ e channel status) determines its further actions as described in the following. If the sensing outcome indicates an av ailable channel then the SU transmits data in the second stage; otherwise, it remains silent for the remaining period of the data phase with duration T j − T S,j . W e assume that the duration of the SU’ s data phase T j is smaller than the channel ev acuation time T eva so timely ev acuation from the busy channel can be realized. Therefore, our design allows to protect the PU with ev acuation delay at most T j if the carrier sensing before the contention phase and the spectrum sensing in the data phase are perfect. Furthermore, we assume that the SU transmits at power lev els P sen ,j and P dat during the FD sensing and transmission stages, respectively where the transmit power P sen ,j will be chosen to effecti vely mitigate the self-interference and achiev e good sensing-throughput tradeoff. The timing diagram of the proposed MFDC–MA C protocol is illustrated in Fig. 1. B. Throughput Analysis W e now analyze the saturation throughput. Recall that for each channel j , the PU is activ e and idle with the correspond- ing pdfs of τ j ac and τ j id are f τ j ac τ j ac and f τ j id τ j id . Moreover , we assume that the receiv ed PU’ s signal po wer at the SU’ s receiv er for channel j is P j p . The throughput is a function of following parameters: probability of transmission p , sensing 3 time T S,j , frame length T j , and SU transmit power P sen ,j for each channel j . For brevity , we ignore the dependence of throughput on p and T j in the following. T o calculate the throughput of the MFDC–MA C pro- tocol, denoted as N T , we consider all possible cases where each case is represented by the corresponding sets of users selecting different channels (each set of users is for one channel). W e no w define the set Ω = n ω k = { n k, 1 , . . . , n k,j , . . . , n k,M } : P M j =1 n k,j = N o where its k -th element ω k has its components n k,j representing the number of users who select channel j . The probability for the set ω k is Q M j =1 p sec j n k,j . Then, the network throughput can be expressed as N T ~ P sec , ~ T S , ~ P sen = | Ω | X k =1 N { n k,j } ! M Y j =1 p sec j n k,j M X j =1 N T j ( T S,j , P sen ,j | n k,j ) I ( n k,j > 0) , (1) where N T j ( T S,j , P sen ,j | n k,j ) I ( n k,j > 0) represents the throughput contributed by channel j giv en that n k,j users select this channel; and I ( . ) denotes the indicator func- tion. Moreov er , N { n k,j } ! is the multinomial coefficient which is defined as N { n k,j } ! = N n k, 1 , n k, 2 , . . . , n k,M ! = N n k, 1 ! n k, 2 ! ...n k,M ! . Furthermore, the throughput of channel j N T j ( T S,j , P sen ,j | n k,j ) can be calculated as N T j ( T S,j , P sen ,j | n k,j ) = B j T ove ,j + T j . (2) where T ove ,j represents the time overhead required for one successful channel reservation on channel j (i.e., successful R TS/CTS exchanges), B j (bits/Hz) denotes the av erage num- ber of bits transmitted per one unit of system bandwidth for one contention/access (CA) c ycle on channel j . T o complete the throughput analysis, we deriv e the quantities T ove , j and B j , which are conducted in the follo wing. 1) Derivation of T ove , j : The av erage time ov erhead for one successful channel reservation can be written as T ove , j = T cont ,j + 2 S I F S + 2 P D + AC K, (3) where AC K is the length of an ACK message, S I F S is the length of a short interframe space, and P D is the prop- agation delay where P D is usually small compared to the slot size σ , and T cont ,j denotes the average time overhead due to idle periods, collisions, and successful transmissions of R TS/CTS messages in one CA cycle. T o calculate T cont ,j , we define some further parameters as follows. Denote T coll as the duration of the collision and T succ as the required time for successful R TS/CTS transmission. These quantities can be calculated as follows [9]: ( T succ = D I F S + RT S + S I F S + C T S + 2 P D T coll = D I F S + RT S + P D, (4) where DI F S is the length of a distributed interframe space, RT S and C T S denote the lengths of the R TS and CTS messages, respectiv ely . As being shown in Fig. 1, there can be sev eral idle periods and collisions before one successful channel reservation. Let T i idle ,j denote the i -th idle duration between two consecutiv e R TS/CTS exchanges on channel j , which can be collisions or successful exchanges. Then, T i idle can be calculated based on its probability mass function (pmf), which is derived as follows. In the following, all relev ant quantities are defined in terms of the number of time slots. W ith n k,j SUs joining the contention resolution on channel j , let P succ ,j , P coll ,j and P idle ,j denote the probabilities that a particular generic slot corresponds to a successful transmission, a collision, and an idle slot, respectiv ely . These probabilities can be calculated as follows: P succ ,j = n k,j p (1 − p ) n k,j − 1 (5) P idle ,j = (1 − p ) n k,j (6) P coll ,j = 1 − P succ ,j − P idle ,j , (7) where p is the transmission probability of an SU in a generic slot. In general, the interv al T cont ,j , whose average v alue is T cont ,j giv en in (3), consists of sev eral intervals correspond- ing to idle periods, collisions, and one successful R TS/CTS transmission. Hence, this quantity can be expressed as T cont ,j = N coll ,j X i =1 T coll + T i idle ,j + T N coll ,j +1 idle ,j + T succ , (8) where N coll ,j is the number of collisions before the successful R TS/CTS exchange on channel j and N coll ,j is a geometric random variable (R V) with parameter 1 − P coll ,j / P idle ,j where P idle ,j = 1 − P idle ,j . Therefore, its pmf can be expressed as f N coll ,j X ( x ) = P coll ,j P idle ,j x 1 − P coll ,j P idle ,j , x = 0 , 1 , 2 , . . . (9) Also, T idle ,j represents the number of consecutiv e idle slots on channel j , which is also a geometric R V with parameter 1 − P idle ,j with the following pmf f T idle ,j X ( x ) = ( P idle ,j ) x (1 − P idle ,j ) , x = 0 , 1 , 2 , . . . (10) Therefore, T cont ,j (the av erage value of T cont ,j ) can be written as follows [9]: T cont ,j = N coll ,j T coll + T idle ,j N coll ,j + 1 + T succ , (11) where T idle ,j and N coll ,j can be calculated as T idle ,j = (1 − p ) n k,j 1 − (1 − p ) n k,j (12) N coll ,j = 1 − (1 − p ) n k,j n k,j p (1 − p ) n k,j − 1 − 1 . (13) These expressions are obtained by using the pmfs of the corresponding R Vs giv en in (9) and (10), respectiv ely [9]. 2) Derivation of B j : T o calculate B j , we consider all pos- sible cases that capture the activities of SUs and status changes of the PU in the data phase of duration T j . Because the PU’ s activity is not synchronized with the SU’ s transmission, the PU can change its activ e/inactiv e status any time. W e assume that there can be at most one transition between the idle and activ e states of the PU during the interval T j . This is consistent with the assumption on the slo w status changes of the PU as described in Section II-B since T j < T eva . Furthermore, we assume that the carrier sensing of the MFDC-MA C protocol 4 is perfect; therefore, the PU is idle at the beginning of the data phase. Note that the PU may change its status during the SU’ s sensing or access stage, which requires us to consider different possible events in the data phase. W e use h kl ( k , l ∈ { 0 , 1 } ) to represent ev ents captur- ing status changes of the PU in the FD sensing stage and transmission stage where i = 0 and i = 1 represent the idle and acti ve states of the PU, respectiv ely . For e xample, if the PU is idle during the FD sensing stage and becomes activ e during the transmission stage, then we represent this ev ent as ( h 00 , h 01 ) where sub-ev ents h 00 and h 01 represent the status changes in the FD sensing and transmission stages, respectiv ely . Moreover , if the PU changes from the idle to the activ e state during the FD sensing stage and remains active in the remaining of the data phase, then we represent this event as ( h 01 , h 11 ) It can be verified that we must consider the following three cases with the corresponding status changes of the PU during the FDC-MA C data phase to analyze B j . • Case 1 : The PU is idle for the whole FDC-MAC data phase (i.e., there is no PU’ s signal in both FD sens- ing and transmission stages) and we denote this e vent as ( h 00 , h 00 ) . The average number of bits (in bits/Hz) transmitted during the data phase in this case is denoted as B j, 1 . • Case 2 : The PU is idle during the FD sensing stage b ut the PU changes from the idle to the activ e status in the transmission stage. W e denote the e vent corresponding to this case as ( h 00 , h 01 ) where h 00 and h 01 capture the sub- ev ents in the FD sensing and transmission stages, respec- tiv ely . The average number of bits (in bits/Hz) transmitted during the data phase in this case is represented by B j, 2 . • Case 3 : The PU is first idle then becomes acti ve during the FD sensing stage and it remains active during the whole transmission stage. Similarly we denote this event as ( h 01 , h 11 ) and the average number of bits (in bits/Hz) transmitted during the data phase in this case is denoted as B j, 3 . Then, we can calculate B j as follows: B j = B j, 1 + B j, 2 + B j, 3 . (14) Theoretical deriv ation for B j, 1 , B j, 2 , and B j, 3 is given in the online technical report [8] due to the space constraint. I V . M F D C – M AC P RO TO C O L C O N FI G U R A T I O N F O R T H RO U G H P U T M A X I M I Z A T I O N In this section, we study the optimal configuration of the proposed MFDC–MA C protocol to achieve the maximum secondary throughput while satisfactorily protecting the PU. A. Problem F ormulation W e are interested in determining suitable configuration for ~ P sec , ~ T S , and ~ P sen to maximize the secondary throughput, N T ~ P sec , ~ T S , ~ P sen . Suppose that the PU requires that the av erage detection probability be at least P j d . Then, the through- put maximization problem can be stated as follows: P1: max p, ~ P sec , ~ T S , ~ P sen N T ~ P sec , ~ T S , ~ P sen s.t. ˆ P j d ε j , T S,j ≥ P j d , 0 ≤ P sen ,j ≤ P max , 0 ≤ T S,j ≤ T j , 0 ≤ p sec j ≤ 1 , P M j =1 p sec j = 1 (15) where p sec j is the probability of channel selection ( ~ P sec = p sec j ), P sen ,j is the SU’ s transmit power on channel j and P max is the maximum power for SUs, and T S,j is upper bounded by T j . In fact, the first constraint on ˆ P j d ε j , T S,j im- plies that the spectrum sensing should be sufficiently reliable to protect the PU. Moreover , the SU’ s transmit power P sen ,j must be appropriately set to achie ve good tradeof f between the network throughput and self-interference mitigation. T o solve problem (15), we propose the two-step approach where we solve the following two subproblems P2 and P3 in the two steps, respectiv ely . In the first stage, we optimize the parameters for each individual channel j and n k,j contending SUs on this channel to achiev e maximum throughput of each channel j , i.e., N T j ( T S,j , P sen ,j | n k,j ) . This problem can be presented as P2: max T S,j ,P sen ,j N T j ( T S,j , P sen ,j | n k,j ) s.t. ˆ P j d ε j , T S,j ≥ P j d , 0 ≤ P sen ,j ≤ P max , 0 ≤ T S,j ≤ T j (16) After solving problem P2 with optimal results N T ∗ j T ∗ S,j ( n k,j ) , P ∗ sen ,j ( n k,j ) | n k,j for all channels j and possible cases with dif ferent n k,j contending SUs. Then, the network throughput with gi ven ~ T ∗ S , ~ P ∗ sen only depends on the channel selection probabilities in ~ P sec . Problem P3 maximizes the throughput with respect to ~ P sec as P3: max ~ P sec N T ~ P sec s.t. 0 ≤ p sec j ≤ 1 P M j =1 p sec j = 1 . (17) Here, N T ~ P sec can be written as N T ~ P sec = | Ω | X k =1 M Y j =1 p sec j n k,j B ( { n k,j } ) (18) where B ( ω k ) = B ( { n k,j } ) = N { n k,j } ! M X j =1 I ( n k,j > 0) × N T ∗ j T ∗ S,j ( n k,j ) , P ∗ sen ,j ( n k,j ) | n k,j . (19) Due to the decomposed structure of the throughput expression N T ~ P sec , ~ T S , ~ P sen in (1), it can be seen that the proposed two-step approach does not loose optimality . B. Configuration for MFDC–MA C Pr otocol 1) Configuration for Sensing and Access Stages: W e will solve problem P2 in the following. In the follo wing analysis, we assume the exponential distribution for τ j ac and τ j id where ¯ τ j ac and ¯ τ id denote the corresponding a verage v alues of these activ e and idle intervals on channel j . Specifically , let f τ j x ( t ) 5 denote the pdf of τ j x ( x represents ac or id in the pdf of τ j ac or τ j id , respectiv ely) then f τ j x ( t ) = 1 ¯ τ j x exp( − t ¯ τ j x ) . (20) W e assume a homogeneous case with same frame length T j . W e are interested in determining suitable configuration for T S,j , and P sen ,j to maximize the secondary throughput, N T j ( T S,j , P sen ,j | n k,j ) . T o gain insights into the parameter configuration of the MFDC–MAC protocol, we first study the optimization with respect to the sensing time T S,j for a given P sen ,j . For a fixed T S,j , we would need to set the sensing detection threshold ε j so that the detection probability constraint is met with equality , i.e., ˆ P j d ε j , T S,j = P j d as in [3], [4]. Since the detection probability is smaller in Case 3 (i.e., the PU changes from the idle to activ e status during the FD sensing stage of duration T S,j ) compared to that in Case 1 and Case 2 (i.e., the PU remains idle during the FD sensing stage) considered in the previous section, we only need to consider Case 3 to maintain the detection probability constraint. The av erage probability of detection for the FD sensing in Case 3 can be expressed as ˆ P j d = Z T S,j 0 P j, 01 d ( t ) f τ j id ( t | 0 ≤ t ≤ T S,j ) dt, (21) where t denotes the duration from the beginning of the FD sensing stage to the instant when the PU changes to the activ e state, and f τ j id ( t |A ) is the pdf of τ j id conditioned on e vent A capturing the condition 0 ≤ t ≤ T S,j , which is gi ven as f τ j id ( t |A ) = f τ j id ( t ) Pr {A} = 1 ¯ τ j id exp( − t ¯ τ j id ) 1 − exp( − T S,j ¯ τ j id ) . (22) Note that P j, 01 d ( t ) is derived in Appendix A and f τ j id ( t ) is giv en in (20). W e consider the following single-variable optimization problem for a gi ven P sen ,j : max 0
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment