Tandem Coding and Cryptography on Wiretap Channels: EXIT Chart Analysis
Traditional cryptography assumes an eavesdropper receives an error-free copy of the transmitted ciphertext. Wyner's wiretap channel model recognizes that at the physical layer both the intended receiver and the passive eavesdropper inevitably receive…
Authors: Willie K Harrison, Steven W. McLaughlin
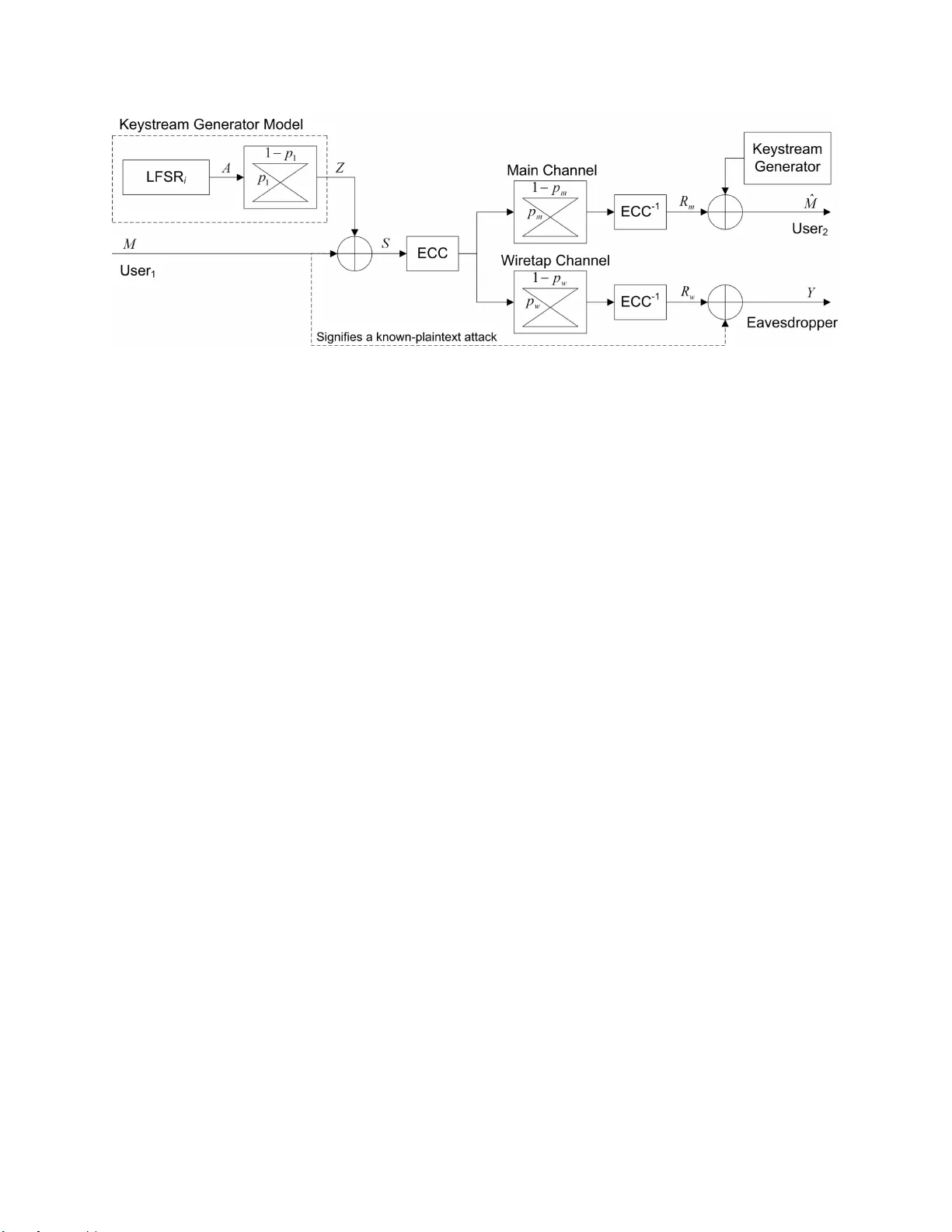
1 T andem Coding and Cryptography on W iretap Channels: EXIT Chart Analysis W illie K Harrison and Ste ven W . McLaughlin Abstract T rad itional cr yptogr aphy assumes an ea vesdrop per r eceiv es an error-free c opy of the transmitted ciphertext. W y ner’ s wiretap channel mod el recogn izes that at the ph ysical layer b oth the in tended receiver and the p assi ve eavesdropper inevitably rec ei ve a n error-prone version o f the transmitted message w hich must be co rrected prior to decryp tion. This p aper consider s the implications of usin g both chan nel and crypto graphic cod es under the wir etap chan nel m odel in a way th at enhanc es the information- theor etic security for the friendly parties by keeping the informatio n transfer to t h e ea vesdropp er small. W e consider a secret-key cry ptogra phic sy stem with a linear feedback shift r egister (LFSR)-based keystream generato r and o bserve the mutual in formatio n between an LFSR-gener ated sequ ence and the receiv ed noise-corr upted ciphertext seque nce u nder a known-plaintext scenario. Th e effecti veness of a noniter ati ve fast correlation attack, which redu ces th e search time in a brute- force attack, is shown to b e correlated with this mutu al info rmation. For an iterative fast correla tion attack on this cryp tograph ic system, it is shown that an EXIT chart and mutu al inf ormation are very good predictors of decodin g success an d failure by a p assi ve eaves d roppe r . I . I N T R O D U C T I O N T ypical communication sys tems use cryptographic primiti ves a t a layer above the physical layer to ac hiev e da ta se curity . Cons idering that both friendly a nd eavesdropping parties inevitably receive codewords co rrupted by errors at the (no isy) phys ical laye r , W yner introdu ced the wiretap channel mode l [1] where it was subseque ntly sho wn that e rror control coding (ECC) c an contribute to the se curity against a passive eavesdropper . In this p aper we consider the practical situation where both error correction coding and cryptograp hy are use d in a wiretap setting an d sh ow how the cha nnel errors sign ificantly inhibit the ability of the eavesdropper to recover the cryp tographic key u sing well-known attacks. W e apply the W ill ie K Harrison and S tev en W . McLaughlin are with the School of ECE, Georgia I nstitute of T echnology , Atlanta, GA. This work has been accepted to 2009 IE EE International Symposium on Information Theory , June 28-July 3, 2009. Nov ember 13, 2018 DRAFT Fig. 1. The wiretap channel model shows friendly parties communica t ing over a main chan nel, and an eav esdropper observing communications through a wiretap channel. widely use d tool of E XIT charts to the wiretap c hannel and show how they can be us ed to predict a threshold behavior on the eavesdropper’ s a bility to recover the cryptographic key u sing a kn own-plainte x t iterati ve attack. The wiretap channe l model that employs coding and cryptog raphy is giv en in Fig. 1. In this paper we a ssume a simple XOR-based cryptog raphic s ystem whos e key is generated using linear feedba ck shift registers (LFSR). Th e noisy c hannel model as sumes two discrete memoryles s binary symmetric channe ls (BSC). Th e main channel links friendly parties, while the wiretap ch annel represe nts a passive eavesdropper o bserving a noise-corrupted version of the communications between the tw o friendly parties. W yn er’ s wiretap model was used to prove the existence of code s which maintain a high lev el of secu rity and guara ntee reliable communica tion between friendly p arties [1], [2]. Practical codes w ere developed by W ei [3], and later examples inc lude [4] a nd [5]. Secrecy capacity C s is a fundamental limit on the rate of se cure trans mission [1], [2]. Wh en the main chan nel and the wiretap channe l are modeled as BSCs , the sec recy capa city is giv e n b y C s = C m − C w where C m and C w are the c apacities of the main channel and the wiretap channel, respectively . Strictly pos iti ve secrecy capa city implies an advantage in the quality of the main chann el over that of the wiretap c hanne l, which implies the crossover probab ility in the wiretap channel p w exceeds that of the ma in ch annel p m such that 0 ≤ p m < p w ≤ 0 . 5 . This c an be the cas e in sce narios where distance between pa rties is a factor in cha nnel qua lity , suc h as a zoned s ecurity ap plication whe re friendly parties communica te ins ide a building and the eav e sdropper monitors communications from ou tside of the building [6]. In app lications which exhibit strictly positiv e se crecy capacity , tandem chan nel and cryptographic code s can potentially provide enhanc ed se curity . It was shown in [6] that an eavesdroppe r can be forced to increase the numbe r of computations nee ded to compromise a cryptographic sys tem if the eavesdropper’ s 2 data vector following the wiretap cha nnel a nd the channel decoder still ma intains a small pe rcentage of errors. Assu ming the quality of the main chan nel is such that the chan nel decoder is able to correct all of the channe l errors, reliable communications c an be maintained. In this pap er we enhance the results of [6] by s howing that mutual information is correlated to the eavesdropper’ s ab ility to recover the secret key o f a c ryptographic system. Iterativ e and noniterative fast co rrelation technique s from [7] developed by Meier and Staff e lbach are a nalyzed in an information-theoretic sense to show that cracking the system for an eavesdropper becomes less feas ible wh en errors from the physical layer remain uncorrected du e to appropriately chosen c hannel codes resulting in a de crease of mutual information. The res t o f the pa per is organized as follo ws . Section II gives the b ackgroun d o f the cryp tographic attacks from [7] which a re later analyze d to sh ow the correlation betwee n mu tual information and system susce ptibility . Se ction III the n provides a d iscussion on mutual information and EXIT cha rts in terms of the attacks, a nd presents simulation resu lts of attacks on the tan dem channel an d c ryptographic co ding scena rio. Conclus ions are included in sec tion IV. I I . F A S T C O R R E L A T I O N A T TAC K S LFSR-based keystream gene rators are used in ma ny cryptographic systems, and have well-kno wn attacks [7], [8], [9], [10]. W e make u se of the se e stablished algorithms in orde r to sh ow how cha nnel coding can enh ance security in a wiretap setting. The encryption technique , as portr a yed in Fig. 2, requ ires a keystream generator with mu ltiple LFSRs which need not be the same leng th [8]. Eac h LFSR ou tput sequen ce is combine d with the others using so me function f to form the keystream generator outpu t Z . The binary messa ge M is e ncrypted by S = M + Z whe re all operations are in GF(2). The sequ ence S is encod ed an d transmitted. A rece i ver decode s the rec ei ved message to obtain R m , and then de crypts using a n identical keystream gen erator which provides a perfect c opy of Z and calculates ˆ M = R m + Z . As lon g as the chann el code c orrects all errors due to the chann el, then ˆ M = M . The secret key is comprised of the initial s tate of each LFSR in the keystream generator . The main assump tion of fast correlation attacks on this system is that the encryp tion tec hnique can be modeled such that a single LFSR output s equenc e A is c orrelated with Z . Thus the keystream ge nerator is p ortrayed in Fig. 2 a s a single LFSR, say the i th one, follo wed by a BSC with Pr ( a j 6 = z j ) = p 1 for j = 0 , 1 , . . . , N − 1 , where a j is the j th bit in the length- N data sequen ce A . Fast correlation attacks on this sys tem a ttempt to retriev e the initial contents of ea ch LFSR in the keystream generator individually , and are built around the existence of check s (checksums) i n A which are then applied to the co rresponding bits o f Z . Ch ecks a re d eri ved from the structure of the LFSR u nder attac k which can be repres ented by 3 Fig. 2. Overvie w of wi retap channel model with channel coding and cryptography in a kno wn-plaintext attack scenario. The ke ystream generator is modeled as a single L FSR preceding a BS C. a co nnection polyn omial g ( X ) = g 0 + g 1 X + g 2 X 2 + · · · + g k X k , w here k is the order of the po lynomial and g j ∈ { 0 , 1 } for j = 0 , 1 , . . . , k . All c onnection polynomials in the keystream gen erator a re a ssumed to be primiti ve yielding maximal-length o utput s equenc es b efore repeating [11]. Defin e t as one less than the numbe r of nonze ro coefficients in g ( X ) , and denote the indice s of the nonzero coe f fic ients as j 0 , j 1 , . . . , j t . Then the expression a j + j 0 + a j + j 1 + · · · + a j + j t = 0 forms a ch eck, and thus a j + j u = a j + j 0 + a j + j 1 + · · · + a j + j u − 1 + a j + j u +1 + · · · + a j + j t . (1) Almost every b it in A takes p art in t + 1 checks of this kind. Additional chec ks are formed by squa ring check expressions in GF(2) [7]. Define w as the total number of checks in volving the bit a j , a nd e numerate these check s from one to w . W e now apply check expres sions to bits in Z . Let the v th check b e z j = z v 1 + z v 2 + · · · + z v t . C learly v ≤ w b ecaus e z j is in the expression. Define b v = P t l =1 z v l and L v = z j + b v . T hen if the v th check holds in Z , L v = 0 . Fu rther define s = Pr ( b v = P t l =1 a v l ) which is the probability of an ev e n number of bit flips in the bits z v 1 , z v 2 , . . . , z v t . It can be shown that s = s ( t − 1) in the recursive calculation s ( l ) = (1 − p 1 ) s ( l − 1) + p 1 (1 − s ( l − 1)) (2) where s (0) = 1 − p 1 . Now suppo se that exac tly h of the first w c hecks hold in Z . W ithout loss of generality , let checks enumerated one t h rough h hold. Then we can de fine 4 p ∗ j = Pr ( z j = a j | L 1 = · · · = L h = 0 , L h +1 = · · · = L w = 1) wh ich is calculated by the express ion p ∗ j = (1 − p 1 ) s h (1 − s ) w − h (1 − p 1 ) s h (1 − s ) w − h + p 1 (1 − s ) h s w − h . (3) Performing the same calculation for all N bits in Z , we form the vector P ∗ = ( p ∗ 0 , p ∗ 1 , . . . , p ∗ N − 1 ) [7]. T wo fast correlation known-plaintext a ttacks originally presented in [7] are n ow briefly summarized. Each attack a ssumes N bits of the message M are av ailable to the eavesdropper . Fu rthermore, it is assume d that the eavesdropper has access to S = M + Z , and thus N bits of Z are readily av ailable. A. Attack 1 The first attack from [7] is noniterative and maintains as its motiv ation that those bits of Z which are included in the grea test numb er of correct c hecks are more likely to be equa l to their c orresponding bits in A . Since each bit in A is a linear comb ination of the initial s tate of the LFSR, it is poss ible to solve for the se cret ke y using k bits with linearly indepe ndent bit co mbinations. An attacker se lects the k most reliable bits from Z (i.e. the k bits with the highe st corresponding values in P ∗ ) that form a linearly ind epende nt system o f eq uations. Of course if one or mo re o f thes e k bits a re in error , then the system of equ ations will not return the s ecret key as its solution. The co rrectness of the solution ca n be d etermined us ing a threshold co mparison on a correlation metric [8]. W e cons ider a worst cas e by assuming the attacker is a lw a ys able to determine wh ether the key obtained is correct or incorrect. If the key is inco rrect, then the values of the k bits are toggled trying alternate pa tterns with Hamming distance 1 , 2 , . . . , k until the correct key is obtained . B. Attack 2 The sec ond attack gi ven in [7] forms an iterati ve up date between s and P ∗ , and employs two nes ted lev els of iteration. In a particular r ound of the attack, the algorithm will perform mu ltiple iterations . The calculation in (2) is mo dified suc h that s takes o n a different v a lue for each bit-check combina tion. A new matrix S is c onstructed to store the se values. Consider the che ck in (1) and ca ll it the v th chec k. Let ( q 0 , q 1 , . . . , q t − 1 ) = ( p ∗ j + j 0 , p ∗ j + j 1 , . . . , p ∗ j + j u − 1 , p ∗ j + j u +1 , . . . , p ∗ j + j t ) , res pectiv e ly . Then the v alue in S correspond ing to the u th bit of the v th check is S u,v ( t − 1) and is calculated recursiv e ly as S u,v ( l ) = q l S u,v ( l − 1) + (1 − q l )(1 − S u,v ( l − 1)) (4) where S u,v (0) = q 0 . Prior to iteration p ∗ thr and N thr are calculated to act as d ecision thresholds. The calculations are based on an o ptimization of expected correction in the first iteration of the first round. 5 Each iteration computes S and P ∗ using (4) and (3) respectively , althoug h (3) must be a ltered to incorporate individual values from S . Th e first c alculation of S assumes p ∗ j = 1 − p 1 for j = 0 , 1 , . . . , N − 1 . An attacker can e stimate the cha nnel p arameter p 1 by counting correct c hecks in Z . If after an iteration there are greater than N thr elements of P ∗ such that p ∗ j < p thr , the n the round is terminated. A round consists of a maximum of α iterations. At the end of the roun d all bits z j such that p ∗ j < p thr , are flipped. All P ∗ values are the n rese t to p 1 . T he attac k proce eds in this fashion u ntil it either stagn ates, or con verges to the correct solution. Ma ny similarities are p resent be tween this attack and Ga llager’ s LDPC decoding messag e-passing algorithm [12]. I I I . M U T UA L I N F O R M AT I O N A T T H E E A V E S D R O P P E R W ith the attacks to b e analyz ed n ow well-defined, we conside r Fig. 2 in its full context. Note that an e av e sdropper h as access to the data se quence Y by applying the known-plaintext to the rec eiv e d vector R w which has alrea dy b een co rrected for chan nel errors a s much as possible. W e a ssume a strictly pos iti ve secrecy capa city an d cho ose a ch annel code which allo ws the friendly p arty to correct all errors d ue to the main c hannel, but which leaves some percen tage of errors due to the wiretap channel for the eavesdropper . Therefore Y is a no isy version o f Z which can be mod eled with a BSC where the prob ability of a bit flip from Z to Y is denoted p 2 . Recall that A and Z are a lso sepa rated by a BSC with Pr ( a j 6 = z j ) = p 1 . A further simplification can occ ur in the mo deling of the relationship between A and Y by c ombining the two cas caded BSCs into a single BSC with Pr ( a j 6 = y j ) given as p ′ = p 1 (1 − p 2 ) + p 2 (1 − p 1 ) = p 1 + p 2 − 2 p 1 p 2 . In o rder to analyz e per-l e tter average mutual information betwee n data s equenc es, let the bits of each sequen ce be mod eled as realizations of an underlying random variable. The n probability mass func tions can be es timated using the av ailable data from eac h s equenc e [13]. Th e s ingle BSC model with parameter p ′ provides a conv en ient mech anism for ana lysis of information-theoretic secu rity . Under this system, mutual information between the random v ariables A and Y is I ( A ; Y ) = H ( Y ) − H ( Y | A ) = H ( Y ) − H ( p ′ ) ≤ 1 − H ( p ′ ) (5) where H ( p ) is the binary entropy func tion. H ( p ) takes its maximum value o f on e w hen p = 0 . 5 [14]. Thus as p ′ → 0 . 5 , then I ( A ; Y ) → 0 which effecti vely reduce s attac k 1 to a brute-force attac k. An estimate for the expected numb er of trials nee ded for attack 1 to s ucceed was originally derived in [7], and refined in [6]. Supp ose attack 1 is applied to the single BS C mo del. The attack c hoose s the k 6 bits with the high est P ∗ values which also form a linearly inde penden t system of equ ations. If exactly r of the k bits hav e bee n fl ipped by the BSC, the n the max imum number of trials req uired to cycle through all possible bit patterns u p to a nd including r errors is gi ven by A ( k , r ) = r X i =0 k i ! ≤ 2 H ( r/k ) k . (6) In practice r is not known, but it c an be estimated. Let w ′ be the av era ge number of checks rele vant to any one bit, and h ′ be the ma ximum integer such that k bits exist which are expecte d to s atisfy a t least h ′ checks . Then ¯ r is e qual to k − k P w ′ i = h ′ w ′ i (1 − p ′ ) s i (1 − s ) w ′ − i P w ′ i = h ′ w ′ i ((1 − p ′ ) s i (1 − s ) w ′ − i + p ′ (1 − s ) i s w ′ − i ) where s is calculated using p ′ in (2). Thus ¯ r of the k ch osen bits are expected to be in error . An estimate on the order of the numb er of trials required is then giv en a s 2 H ( ¯ r /k ) k . T his estimate is nearer to the true value when p ′ is c lose to ze ro b ecaus e when p ′ ≈ 0 . 5 then H ( ¯ r/k ) ≈ 1 and 2 H ( ¯ r /k ) k ≈ 2 k , but the true av e rage in this ca se is on ly 2 k − 1 . T o ca lculate the mutual information for a ttack 1, we note that since the i th LFSR is governed by a primiti ve connec tion polynomial, the interna l s tate of the LFSR will take on all nonze ro bit combinations . By defi nition the least signific ant bit after the j th shift of the LFSR is a j . Thus A is a ma ximal-length sequen ce which repe ats a fter 2 k − 1 bits. If A is mo deled as a random variable, then Pr ( A = 0) = 2 k − 1 − 1 2 k − 1 and Pr ( A = 1) = 2 k − 1 2 k − 1 [15]. For k suf fi ciently lar g e, both of these prob abilities are approximately 0.5. Using this den sity on A , and the cros sover p robability p ′ in the a ggregate BSC, I ( A ; Y ) may be c alculated using the equality in (5). W e find that as p ′ → 0 . 5 (and thus I ( A ; Y ) → 0 ) tha t the number of required iterations to recover the secret key by mea ns o f attack 1 also increases . Fig. 3 gives the simulated number of trials required to crack the s ystem as a function of I ( A ; Y ) for a spe cific examp le along with the estimate from (6). In the case of attack 1, I ( A ; Y ) is con stant throughout the a ttack. The information a bout A imbedd ed in Y is extracted and combined with knowledge of the s tructure o f A to find the se cret key . Howe ver , in attack 2 the values of bits in Y are mod ified at the end of each round, thus altering the density on Y as the attack progresse s. Define Y [ l ] as the Y seque nce after the bit flipping in round l of attack 2. If the attack takes T roun ds for Y [ l ] to either stagnate or con verge to A , then an information-theoretic analysis o f attack 2 requires k nowledge of I ( A ; Y [ l ] ) for l = 0 , 1 , . . . , T − 1 . W e expect I ( A ; Y [ T − 1] ) to equa l one in a succ essful attack, and to be less tha n one in the cas e of a failur e . A tool for vie wing the expected progress of I ( A ; Y [ l ] ) is the extrinsic information transfe r (EXIT) chart. EXIT charts were 7 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 0 0.5 1 1.5 2 2.5 3 3.5 x 10 4 Attack 1: Number of Trials for Successful Attack Number of Trials I(A;Y) Theoretical Estimate Simulation Results Fig. 3. Number of trials required f or a successful att ack versus I ( A ; Y ) using attack 1 where the order of g ( X ) is k = 15 , t = 4 , and N = 1500 . Note that t is small relativ e to k for ease in simulation, but these trends exten d to larger t . designed to giv e a graph ical understand ing o f the decoding p rocess of turbo codes and have been use d to p rovide insight on the con vergence o f LDPC decoding as well [11]. W e implement EXIT analysis on attack 2 in order to cha racterize the expected value of I ( A ; Y [ l ] ) for l = 0 , 1 , . . . , T − 1 , and thus dis play the average results of the attac k u nder any sp ecific channel c onditions. The mutual information between A and Y [ l ] is I ( A ; Y [ l ] ) = X a,y p ( A = a, Y [ l ] = y ) log 2 p ( A = a, Y [ l ] = y ) p ( A = a ) p ( Y [ l ] = y ) where a, y ∈ { 0 , 1 } . Therefore, in o rder to calculate I ( A ; Y [ l ] ) , we mus t estimate the probability mass function of Y [ l ] , as well as the joint mass function of A an d Y [ l ] . Since the channel we are cons idering is symmetric, all of this can be don e through simulation by counting bits wh ich are still in error at the end of each round and dividing by the total numbe r of bits. Rea lize that the increa se in information during round l is I ( A ; Y [ l ] ) − I ( A ; Y [ l − 1] ) ; therefore, we assign the intrinsic and extrinsic information for round l a s I ( A ; Y [ l − 1] ) an d I ( A ; Y [ l ] ) , res pectiv e ly . The EXIT ch art portrays the expected increase in information by plotting I ( A ; Y [ l − 1] ) versus I ( A ; Y [ l ] ) for curve o ne, while the second curve in the EXIT chart is I ( A ; Y [ l ] ) versus I ( A ; Y [ l − 1] ) . Thus the progress of the d ecoder is shown b y refl ecting back and forth between c urves. If I ( A ; Y [ l ] ) go es to one, then the attac k conv erges on the correct s equenc e; therefore, there must exist a gap between the tw o c urves if a su ccess ful attack is to be expec ted. 8 In order to s how average tendencies in the mu tual information during attack 2, we construct EXIT charts using a binn ing technique . The mutua l information I ( A ; Y [ l ] ) is c alculated for ev e ry roun d in a lar ge number of attacks . T hen the expec ted increase in information is obtained for ea ch section of the chart by subdividing the x-axis into D equa l segme nts or bins. The data are sorted acco rding to intrinsic information, an d then the extrinsic information is averaged in ea ch bin. The center o f eac h of the D segments is use d a s the intrinsic information for the co rresponding bin wh en forming the cha rt. Results using this method for a particular set o f system pa rameters av erag ed ov e r 100 attacks are shown in Fig. 4. For this example, we assu me that the eavesdropper co rrects all errors due to the physical lay er yielding p 2 = 0 . W e observe that the EXIT chart predicts an overall tenden cy for the attack to s ucceed due to the gap between c urves. W e also note that the EXIT curves d o not extend to zero. Generating these curves was implemen ted by actually simulating attacks on the sys tem. Although some rounds did yield a negati ve correction, none resulted in zero extrinsic information; the refore, no rounds exhibited zero intrinsic information either , leaving bins a round ze ro empty . Fina lly we observe that the g ap b etween EXIT curves is narrower for lower intrinsic information regimes. This fact defends the tech nique used in [7] and [6] in defining the correction capability of attack 2 u sing only the expected results in the first round o f an attack. If the first round provides good correction, then the c hart indica tes that con vergence to A will proceed quickly . Whe n the first rou nd has mediocre or p oor correction, the a lgorithm must proceed through the pinched region of the gap resulting in s lo we r co n ver g ence. Another EXIT chart for a s imilar se tup as that in Fig. 4 is sh own in Fig. 5 . The only diff e rence in the two scenarios is the non zero value of 0.1 for p 2 in the attacks de picted by Fig. 5. This figu re s hows that attack 2 is likely to fail due to the crossover in the EXIT cha rt wh en a channe l co de is assumed which deliv ers a 10% error rate to the e av e sdropper . Again this be havior can be pred icted from the average correction in the first round. Fig. 5 portrays more errors on average follo wing the first rou nd than the re were prior to launching the attack. In this sce nario, the expected progress of a n attack c on verges on the crossover point in the E XIT c hart rather than conv erging to one as in Fig. 4. Th us a n a ttack that would be otherwise succ essful c an be expected to fail if a channe l code can be us ed to ensure enough errors in R w to create a c rossing p oint in the EXIT chart. I V . C O N C L U S I O N In co nclusion, we see that mutua l information is a me aningful metric in d ev e loping the concep t of information-theoretic sec urity . It is verified using mutua l information a nd EXIT ch arts that fast c orrelation attacks c an be made mo re difficult or impossible wh en c hannel e rrors a t the physical lay er a re c onsidered. 9 0 0.2 0.4 0.6 0.8 1 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Attack 2: EXIT Chart Averaged Over 100 Attacks I(A;Y [l] ), I(A;Y [l−1] ) I(A;Y [l−1] ), I(A;Y [l] ) Curve One Curve Two Expected Progress Fig. 4. EXIT chart wi th D = 20 formed by av eraging the results of 100 simulations of att ack 2 with k = 31 , t = 6 , α = 5 , N = 3100 , and p 1 = p ′ = 0 . 2 . Channel errors ca n be b rought to bea r a gainst an eavesdropper throug h implementing s ecurity-enhanc ing channe l c odes. Noniterati ve a ttacks which effecti vely shrink the av e rage s earch area to find the key can expec t an increas e in n ecess ary co mputations for success ful deco ding. EXIT ch arts provide an excellent an alysis tool in determining the increase in s ecurity due to cha nnel codes whe n iterativ e cryptographic attacks a re employed, signifying a n average failure to dec ode w hen the c urves in the EXIT chart cross. Finally EXIT analysis may also provide more ins ight into optimizing a ttacks on the LFSR-based encryption scheme presented. R E F E R E N C E S [1] A. D. W yner . The wi re-tap channel. Bell System T echnical Journal , 54:1355–13 87, Oct 1975. [2] I. Csiszar and J. K orner . Broadcast channe l s with confidential messages. Information Theory , IEEE T ransactions on , 24(3):339–3 48, May 1978. [3] V . K. W ei. Generalized Hamming weights for linear codes. Information Theory , IE EE T ransaction s on , 37(5):1412–1418, Sep 1991. [4] A. Thangaraj, S. Dihidar, A. R. Calderbank, S. W . McLaughlin, and J-M. Merolla. Applications of LDPC codes to the wiretap channel. Information Theory , IE EE T ransac ti ons on , 53(8):2933–2 945, Aug 2007 . [5] M. Bl och, J. Barros, M. R. D. Rodrigues, and S . W . McLaughlin. Wireless i nformation-theoretic security . Information Theory , IEEE T ransactions on , 54(6):2515–253 4, June 2008. [6] W . K. Harrison and S. W . McLaughlin. Physical-layer security: Combining error control coding and cryptography . Accepted at ICC 2009 and posted on arXiv .org , arXiv :0901.0275v1 [cs.IT], Jan 2009. 10 0 0.05 0.1 0.15 0.2 0.25 0.05 0.1 0.15 0.2 0.25 Attack 2: EXIT Chart Averaged Over 100 Attacks I(A;Y [l] ), I(A;Y [l−1] ) I(A;Y [l−1] ), I(A;Y [l] ) Curve One Curve Two Expected Progress Fig. 5. EXIT chart wi th D = 20 formed by av eraging the results of 100 simulations of att ack 2 with k = 31 , t = 6 , α = 5 , N = 3100 , p 1 = 0 . 2 , and p 2 = 0 . 1 yielding p ′ = 0 . 26 . [7] W . Meier and O. Staffelbach . Fast correlation att acks on certain stream ciphers. J ournal of Cryptology , 1:159–17 6, 1989. [8] T . Siegentha ler. Decrypting a class of stream ciphers using ciphertext only . Computer s, IEEE T ransactions on , C-34(1):81– 85, Jan 1985. [9] V . V . Chepyzho v and B. J.M. Smeets. On a fast correlation attack on certain stream ciphers. In E UR OCRYPT , pages 176–18 5, 1991. [10] T . Johansson and F . Jonsson. Theoretical analysis of a correlation attack based on con volutional codes. Information Theory , IEEE T ransaction s on , 48(8):2173– 2181, Aug 2002. [11] T . K. Moon. Err or C orr ection Coding: Mathematical Methods and A lgorithms . John Wiley & Sons, Inc., Hobok en, NJ, 2005. [12] R. G. Gallager . Low-Density P arity-Check Codes . MIT P ress, Cambridge, MA, 1963. [13] A. Ashikhmin, G. Kr amer , and S. t en Brink. Extrinsic information transfer functions: Model and erasure channel properties. Information Theory , IEEE T ransactions on , 50(11):2657–2 673, Nov . 2004. [14] T . M. Cover and J. A. Thomas. E lements of Information Theory . John W iley & Sons, I nc., Hobok en, NJ, 2006. [15] D. W elsh. Codes and Cryptogra phy . Oxford Uni versity Press, W alton Street, Oxford O X26DP , 1988. 11
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment