Physical-Layer Security: Combining Error Control Coding and Cryptography
In this paper we consider tandem error control coding and cryptography in the setting of the {\em wiretap channel} due to Wyner. In a typical communications system a cryptographic application is run at a layer above the physical layer and assumes the…
Authors: ** *저자 정보는 원문에 명시되지 않았습니다.* **
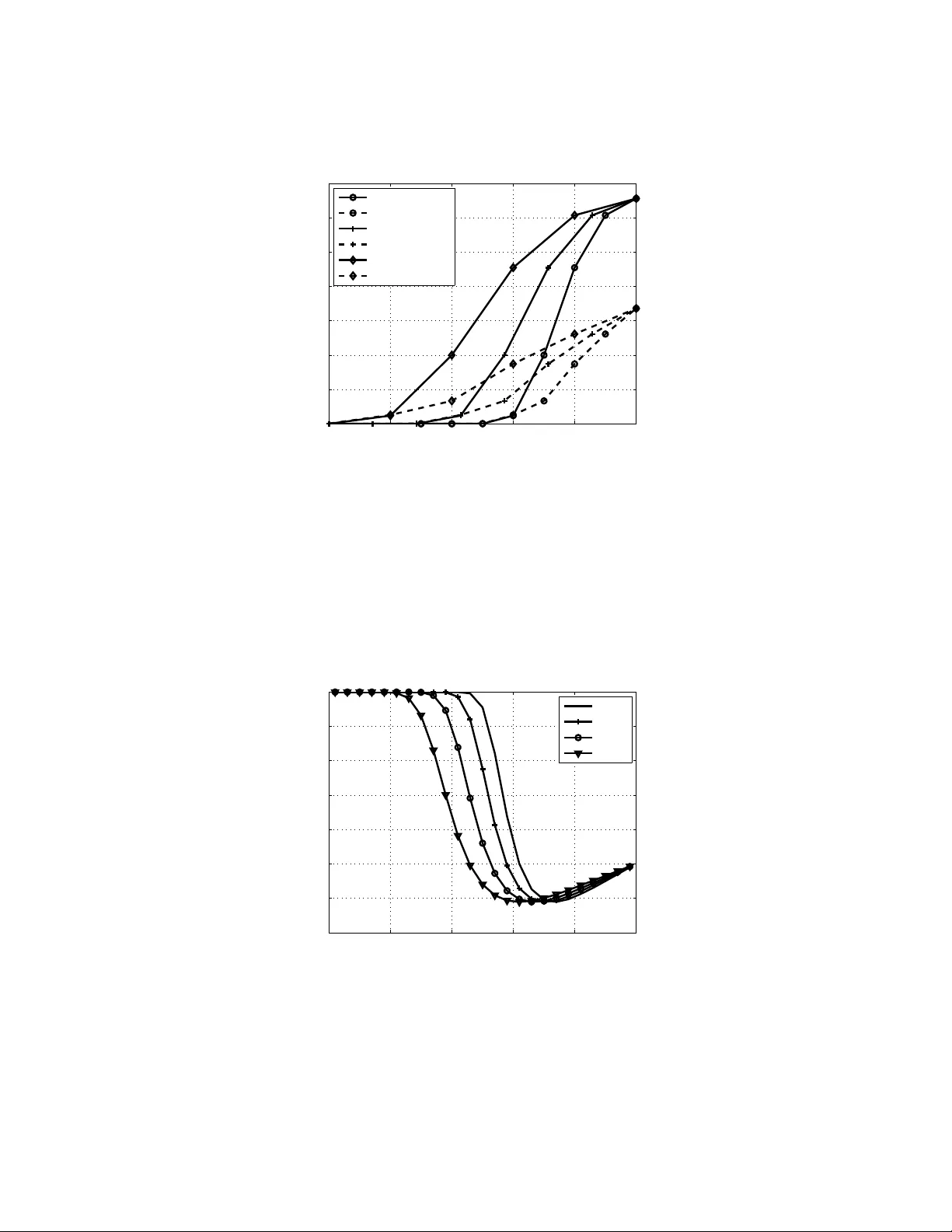
1 Physical-Layer Security: Co mbining Error Control Coding and Cryptography W illie K Harrison and Ste ven W . McLaughlin Abstract In this pap er we consider tande m error contro l c oding and cry ptograp hy in th e setting of the wir etap channel du e to W yner . In a typ ical commun ications system a cr yptogr aphic application is r un at a layer above the physical layer an d assumes th e channel is error free. However , in any real app lication the channels for friend ly users and pa ssi ve eaves d roppe rs are not erro r fr ee and W yner’ s wiretap model addresses th is scenar io. Using this model, we sh ow the secur ity of a commo n crypto graphic primitive, i.e. a keystream gener ator based on linear feedback shift re g isters (LFSR), can be strengthened b y exploiting prop erties o f th e ph ysical layer . A passiv e ea vesdr opper can b e mad e to experience greater difficulty in cracking an LFSR-based cryp tograp hic system insomuch that the com putationa l complexity of discovering the secret key in creases by or ders o f magnitu de, or is altogethe r inf easible. Th is result is shown for two fast correlation attacks o riginally presented by Meie r a nd Staffelbach, in the context o f channel er rors d ue to the wire tap ch annel mod el. I . I N T RO D U C T I O N T raditionally communication systems have implemented s ecurity meas ures b y cryptograph ic means. Howe ver , with the introduction o f the wiretap cha nnel model by W yner [1], it bec ame clear that security can also be ach iev ed through means of c hannel coding. The wiretap cha nnel model portrays two friendly users sharing information over a main communications ch annel c m (e.g. a fading wireless channe l [2]) and a pass i ve eavesdropper observing a degraded version of the information throug h a wir etap channe l c w . As in [1], we will ass ume that both chan nels are discrete and memoryless. Fig. 1 portrays this scena rio using b inary symmetric c hannel (BSC) mode ls for both c m and c w . If the c ommunication over c m is o f a priv ate nature, it then become s necess ary to ac complish two seemingly con flicting tasks of reliability W ill ie K Harrison and Stev en W . McLaughlin are with the School of E CE, Georgia Institute of T echnology , Atlanta, GA. This work has been submitted and accepted to IEE E International Conference on Communications, and will be presented there June 14-18, 2009. October 20 , 2018 DRAFT Fig. 1. Portrayal of a kno wn-plaintext attack on the wiretap channel model where two friendly parties share information ov er a main channel c m and an eavesd ropper observ es commun icati ons through a wi retap channel c w . In practice the keystrea m generator is comprised of M LFSR output sequences combined according to a function f . It is simplified from its true condition and modeled as a single LFSR wi th a B SC. between the friendly users an d sec urity agains t the eavesdropper through some encoding techniqu e. The purpose of this pa per is to qua ntify the a dditional c omplexity that the eav e sdropper f ac es whe n the security problem is address ed with ch annel e rrors at the physical layer in mind. The existence of cod es providing reliability to friendly parties while maintaining some le vel of con- fidentiality is crucial to increasing necess ary compu tations for an eavesdropper , and has b een pro ven by W yner in [1] as well as Csisz ar and Corner in [3]. Practical cod es of this k ind, howe ver , were not discovered until much later [4]. It has since been shown for many varying circumstanc es an d ch annels that practical codes exist w hich satisfy b oth design co nstraints of reliability a nd secrecy . For example, it has be en shown in [5] that practical low-density parity-check (LDP C) code s exist which achieve these two criteria for a noiseles s ch annel c m and a binary erasure cha nnel c w . Similar results have been sh own in [6], also mak ing use of LD PC codes as well as mu ltile vel coding for the case of indepen dent quas i-static fading chan nels c m and c w . In this pape r we ad dress a p ractical scen ario where both c m and c w are treated as BSCs with prob abilities of a bit flip p m and p w , resp ectiv ely . It is a ssumed that the wiretap c hanne l quality is less than that of the main channe l, tha t is p w > p m . This might be the case, for exa mple, in a zo ned-sec urity application where the friendly parties are inside a b u ilding a nd the eavesdropper is outside the buil d ing monitoring communica tions. The res t of the p aper is outlined as follows. First we give so me disc ussion on the ge neral setting. W e 2 focus our attention o n linear feedbac k s hift register (LFSR) cryptographic app lications because attacks against them have bee n well doc umented and we are ab le to quan tify the increa se in complexity tha t the eavesdropper experienc es d ue to errors in the wiretap ch annel. T wo well-known attacks originally giv en in [7] will be co nsidered, a nd it will be shown tha t an eavesdropper can be made to fail in o btaining the secret key in an otherwise su ccess ful scena rio by conside ring the effects o f chan nel errors pres ented by some phy sical me ans. The backg round for the L FSR-based cryptog raphy is given in section II, while the attacks are presented briefly in section III. Afterwards, s ection IV provides evidence of a phys ical-layer of sec urity under the con ditions of the attacks p resented in the previous se ction. Theoretical results as well as simulation o utput for the tw o attacks are also inc luded in this section. Fina lly conclusion s of these findings are provided in section V. I I . B AC K G RO U N D It has b een shown b y Shanno n and others that a on e-time pad can ac hiev e perfect secrecy a s a cryptographic enco ding technique [8], mea ning that kn owing the codeword or e ncoded seque nce gi ves no information on the value of the original messag e. Howev e r , implementation of a one-time pad relies on a perfectly ran dom key se quence . Ass uming that a us er is capable of generating this sequence of elements, the problem of communicating wit h absolute s ecrecy can b e solved, but at the expense of requiring distribut ion of a secret key wh ich is the same length as the original messa ge [9]. Due to the is sue of key distribution inherent in the on e-time pad encoding mecha nism, othe r metho ds are us ed to attempt to emulate the s ecrecy a spects o f the one-time pad while providing a more practical key length. One such system is given in [7], [10 ], [11 ], and [12]. The en coder for this system is c omprised of a keystream gene rator that produc es a ps eudorand om ke y s equen ce ( z n ) by c ombining M LFSR ou tput sequen ces using a function f . T he notation ( z n ) = ( z 0 , z 1 , . . . ) de notes a seque nce or vector whose n th element is z n . Assuming all data sequen ces to be binary , a ciphertext b it sequence ( s n ) is prod uced using a bit-wise exclusive or (XOR) o peration between the mess age sequ ence ( m n ) a nd the keystream sequen ce ( z n ) , as portrayed in Fig. 1 . The sequence ( a n ) is the output seque nce of a single LFSR, say the i th on e. The effecti ve ke y of the s ystem c onsists of the initial conditions of the M shift registers, and hen ce is fixed in length regardless of the length of ( m n ) . Decod ing is accomplishe d using the XOR operation with the same keystream se quence ( z n ) , which friendly p arties can duplicate once they know the key . If it is a ssumed that the bits of ( z n ) are random indepe ndent a nd identically distrib uted (i.i.d.), and therefore that bits in the seq uence ca nnot be predicted by a n eavesdropper , the n the sy stem ac hieves the secrecy of the one-time pa d. 3 This assumption is u ntrue, howev e r , in many ins tances. For example, Siegenthaler showed using only ciphertext t h at the secret key (initial state) o f a contrib uting LFSR ca n be obtained by calculating a correlation metric for all possible initial conditions of the LFSR, and then comparing to a Neyman- Pearson thresho ld d etermined by the statistics o f the da ta [10]. While this pa rticular attack requires 2 k − 1 correlation ca lculations, fast-correlation technique s exist where it is s hown that a lo w-weigh t conne ction polynomial of an LF SR, i.e. one with a small number of feedba ck loop s, produces a more sus ceptible system to correlation methods [7], [11]. Desp ite the shortcomings of LFSR-based generators, they continue to b e used in modern cryp tographic sys tems, inc luding E 0 the system employed by Bluetooth [13]. This is the case due to the relative e ase in compu tations that an LFSR-base d system provides. Many wireless and handhe ld techn ologies ben efit from LF SR-based cryptography . The attack of the LFSR-ba sed cryp tographic primiti ve as sumes tha t the keystream seq uence ( z n ) is correlated to the output s equen ce of the i th LFSR ( a n ) with correlation value 1 − p 1 , and thus can be modeled as a BSC with Pr ( a j 6 = z j ) = p 1 for j = 0 , 1 , . . . , N − 1 , whe re N is taken to be the length of an ob served s equenc e. Fig. 1 shows this modeling of the keystream g enerator . A known-plaintext attac k is portrayed in the figure where an eavesdroppe r has some means of obtaining N bits of the original messag e; therefore, if the sequ ence ( s n ) is obse rved without error , then the first N bits of the keystream sequen ce ( z n ) can be reconstructed exactly . It is assumed tha t p w > p m implying more err o rs in the wiretap cha nnel than in the ma in cha nnel; therefore, an encod ing technique is chos en to guarantee reliable communications betwee n friendly parties while maintaining some perce ntage of b it errors in the wiretap channe l. The effecti ve error rate after a pplying e rror control c oding (ECC) in the wiretap c hannel is g i ven as p 2 , and the model considered for the eavesdropper is simplified to that shown in Fig. 2. This figure indicates a pair of BSCs, where the first mode ls the correlati o n of the seq uences ( a n ) a nd ( z n ) , and the seco nd models bit errors in the wiretap channel after chan nel dec oding. The output s equen ce of the final BSC ( y n ) is obtained in practice b y applying the N known bits of ( m n ) to the decoded seque nce as sho wn in Fig. 1. This sequenc e can be thought of as a no isy version of ( a n ) , wit h a single BSC separating the two sequen ces. Th e probability of a bit flip in this BSC is deno ted p ′ and is c alculated to be p ′ = p 1 (1 − p 2 ) + (1 − p 1 ) p 2 = p 1 + p 2 − 2 p 1 p 2 . (1) The cryptographic system is said to be compromised if an eavesdropper can obtain the initial contents of the i th LFSR using ( y n ) assuming knowledge of the LFSR conn ection po lynomial is public. 4 Fig. 2. W iretap channel model flow diagram relating sequences ( a n ) , ( z n ) , and ( y n ) using a pair of binary symmetric channels. I I I . C RY P T O G R A P H I C A L G O R I T H M S Both attacks pres ented in [7] reconstruct the key of the i t h LFSR using checks which are deri ved from the feedback polyn omial g ( x ) . Th is polyno mial governs the structure of the LFSR, and guarante es a max imal-length output seque nce be fore repeating if an d only if g ( x ) = g 0 + g 1 x + g 2 x 2 + · · · + g k x k is primiti ve in GF(2), where g j ∈ { 0 , 1 } for j = 0 , 1 , . . . , k [14]. Define t to be the number of f e edback loops in the LFSR. For primiti ve g ( x ) of orde r k , g 0 = g k = 1 and the total numbe r of nonz ero co efficients of g ( x ) is o dd [7], thus pro viding an even value of t ( g k does not fee d back ). Let the indice s of the nonzero coefficients in g ( x ) be denoted j 0 , j 1 , . . . , j t ; then j 0 = 0 and j t = k . Now consider the j th bit of the s equenc e ( a n ) . Due to the structure of g ( x ) , a j + j 0 + a j + j 1 + · · · + a j + j t = 0 . This expression is calculated in GF(2), and thus simplifies to a j = a j + j 1 + a j + j 2 + · · · + a j + j t . (2) Except for those within t bits of the end of t h e s equenc e, every b it can be expected to contrib ute to t + 1 c hecks of this kind. Additional chec ks a re generated using a rule some times referred to as freshma n exponentiation which states that for elements x an d y in GF(2), ( x + y ) 2 = x 2 + y 2 [14]. Check expressions giv en by (2) can then be repe atedly s quared un til limited by the len gth of the sequ ence N , providing additional ch eck express ions with each squ aring. Both a ttacks rely on co mputing these checks using the bits of ( y n ) , and counting checks which hold with equa lity . Of course a c heck can still hold if an e ven number o f bits in a ch eck expression have been flipped , hen ce bits a re assigned conditional probabilities of being correct gi ven the number of satisfied checks. These proba bilities are stored in the vector ( p ∗ n ) . Let the nu mber of satisfied c hecks c ontaining y j be de noted as c j s , while the number of total chec ks for which y j plays a role is expressed as c j to . If c j s = h and c j to = m , then p ∗ j = Pr ( y j = a j | c j s = h, c j to = m ) = p ′ s h (1 − s ) m − h p ′ s h (1 − s ) m − h +(1 − p ′ )(1 − s ) h s m − h , (3) where s is defined as the probability t h at an e ven number of err o rs occur in the bit s of the check expression discounting y j [7]. This value can be calculated recu rsi vely as s ( j ) = (1 − p ′ ) s ( j − 1) + p ′ (1 − s ( j − 1)) 5 where s (1) = 1 − p ′ and s = s ( t ) . A. Attack A The first attack in [7] is founde d on the principle tha t bits which satisfy the mo st checks are the most reliable. Using the k bits which have the grea test values in ( p ∗ n ) , a system o f e quations is determined and solved where the solution is the key or initial contents of the LFS R. This system o f equations is constructed u sing the fact that every output of an LF SR is merely a linear combination of the bits in the initial state. The key is ob tained by solving the system using a method suc h as LU de composition tailored to operations in GF(2) [15]. Mea sures mus t be taken to ensure that the grou p of k b its cho sen have linea rly independe nt key bit combinations. In order to determine whether the obtained so lution is the key , a threshold for a c orrelation metric between ( y n ) and a sequ ence generated by the solution to the s ystem of equations must be formed [10]. If the solution is determined to be incorrect b y the thresh old comparison , the algorithm mus t then perform an e xh austive search on poss ible error combinations in the k chose n bits. The ca lculations ne cessa ry to perform this t a sk dominate the performance of the a lgorithm, and he nce define the c omputational complexity of attack A. V ariations of the k bits with Hamming distanc e 1,2,. . . , k are tried until a key is found which sa tisfies the correlation c ondition. In orde r to calcu late a worst-case sce nario, it is as sumed that the eavesdropper is alw ays ab le to detect a c orrect key . B. Attack B The se cond attack presente d in [7] also makes use of the c onditional probabilities ( p ∗ n ) ; howev er , the iterativ e nature of this attack alters these calculations slightly . Attack B is extremely comp arable to Gallager’ s LD PC de coding algo rithm [16]. In the attack all co nditional proba bilities in the s equen ce ( p ∗ n ) are c alculated using (3). A thresh old p thr is derived by calculating the b est poss ible increase in correct bits as suming that all b its with p robability less tha n the thresho ld are flipped . This correction thres hold is set to the value whe re any bit y j with p ∗ j < p thr has a maximum likelihood of being incorrect. If a certain pred etermined numbe r of bits N thr have values in ( p ∗ n ) les s than p thr , then those bits a re flippe d. Otherwise the conditional probabilities p ∗ j for j = 0 , 1 , . . . , N − 1 are recalculated by excha nging the a priori probability p ′ with the previous value of p ∗ j in (3). After a few iterations of p robabilities, or once at least N thr untrustworthy bits are found, the bits a re flipped and the algorithm con tinues in this way until a solution is obtained. 6 I V . P R O O F O F C O N C E P T W I T H S I M U L A T I O N R E S U LT S If a c hannel e ncoding tec hnique can gua rantee bit errors for a p assive eavesdropper regardless of ECC, then these errors can clearly co ntrib ute to the overall security of the system. The ques tions then remain of h ow to qu antify the amount of s ecurity ga ined, and what value of p 2 will p rev en t an eavesdropper from ga ining advantage in a co rrelation-based attack . T o provide ans wers to these two que stions, me trics used in [7] a re analyzed . First in the c ase of attack A, suppos e the re a re exactly r errors in the k chose n bits. Then the maximum number of iterations in an exhaustive sea rch is A ( k , r ) = r X i =0 k i ! ≤ 2 H ( r/k ) k . (4) The inequality makes use of the binary entropy fun ction H ( x ) , a nd is well known. Of cou rse r is n ot readily available in practice, but it can be estimated ma king u se of (3) in the expression ¯ r = k (1 − Pr ( y j = a j | c j s = h ′ , c j to = m ′ )) , where m ′ is the av era ge nu mber of checks relev ant to a ny o ne bit, and h ′ is the maximum integer such that k b its exist which are expected to satisfy at least h ′ checks . Therefore, giv en that the best k bits are chos en, ¯ r of them are s till expec ted to be in error . An estimate on an uppe r bound of the number of trials required is then given as 2 H (¯ r /k ) k . Fig. 3 shows this bound for v arying p 2 values in an example f e aturing a length-32 LFSR whil e as suming that N = 32 × 10 6 bits of ( m n ) are known b y the eavesdropper . The greater the length of the observed data s equen ce, the easier the sys tem will yield to a correlation-based attack. Simulations of the attack are compared with this bound and can be seen in Fig. 4, althoug h for a s horter LFSR. Both the theoretical bounds and the simulations s how chan nel conditions where attacks are expec ted to requ ire a significan t amount of a dditional computations due to nonzero p 2 . A s shown in Fig. 4, the expec ted bo und is much tighter for smaller p ′ values. Clearly as p ′ approach es 0.5, attack A reverts to a brute-force attack which is expected to requ ire 2 k − 1 iterations, while the bound a pproache s 2 k . For s maller p ′ the difference between the bound a nd the simulation results is not as pron ounced . Regardless of this difference, whe n k is large and p ′ is clos e to 0.5 the task of fin ding t h e s ecret key become s overwhelmingly expensive, a nd not feasible in many ca ses. Ph ysical-layer considerations can b e ad dressed in the c hoice of chan nel codes which can then dri ve p ′ to 0.5 by increasing p 2 , and thus obtain this extra level of se curity . A similar an alysis can be co nducted for attack B; however , the attack h as an und erlying bipartite g raph which conn ects c heck node s to probab ilities in ( p ∗ n ) . Since the graph conta ins many cycles , a fter a few iterations probabilities be come dif ficult to track; thus numbers of computa tions are like wis e dif ficult to estimate. T he strength of this attack is instead ca lculated by determining the eff ec t of the first iteration of the algorithm. Recall that a thres hold p thr was determined to max imize the probability tha t y j 6 = a j 7 0 0.1 0.2 0.3 0.4 0.5 10 0 10 2 10 4 10 6 10 8 10 10 p 1 Number of Trials Attack A: Bound on Expected Complexity p 2 =0 p 2 =0.05 p 2 =0.1 p 2 =0.15 Fig. 3. Expected bound on the number of trials required to find t he secret key using att ack A for k = 32 , N = k × 10 6 , and t = 6 . giv en that p ∗ j < p thr . Let N w be the expected numb er of bits such that both a j 6 = y j and p ∗ j < p thr , and let N v be the expec ted nu mber of bits such that a j = y j and p ∗ j < p thr , for j = 0 , 1 , . . . , N − 1 . Also let N i = N w − N v . If N c 0 represents the total number of bits such that a j = y j prior to iteration, then the toggling of all bits with p ∗ j < p thr will result in an expected N c 0 + N i correct bits. Obviously if N i is n egati ve, then the expe cted outcome of the first iteration will leave more bits in error than were originally so. The only way to en sure tha t the algo rithm d oes no t ev e ntually con verge on the c orrect sequenc e is to insist that attack B have no correction c apability . While this would be impossible to guarantee under ev e ry sce nario, we s ay tha t attack B has correction capa bility zero if N i < 0 , i.e. N v > N w . The ratio C = N i N w + N v (5) is use d to sc ale the value of N i to a real numbe r in the ra nge [ − 1 , 1] while maintaining its sign. Fig. 5 shows the value o f the correction ratio C for sev eral BSC parameters p 2 , ov e r a range of p 1 values. It sho uld be noted that while a negativ e value of C implies a c orrection capab ility o f zero, conditions yielding positi ve C values still may not con verge on the correct s equen ce. S imulations of attack B hav e been consistent in a lack of con vergence for ca ses whe re C ≤ 0 . An example is in orde r . Let the primiti ve conne ction polyno mial for the i t h LFSR be writ ten a s g ( x ) = x 31 + x 21 + x 12 + x 3 + x 2 + x + 1 [ 1 7], an d the correlation between ( a n ) and ( z n ) b e 0.8, 8 0 0.1 0.2 0.3 0.4 0.5 0 0.5 1 1.5 2 2.5 3 3.5 x 10 4 Attack A: Theory vs. Simulation p 1 Number of Trials Theory: p 2 =0 Simulation: p 2 =0 Theory: p 2 =0.15 Simulation: p 2 =0.15 Theory: p 2 =0.25 Simulation: p 2 =0.25 Fig. 4. Resu lts from simulations of attack A sho wing necessary computations to crack t he LFSR-based cryptographic system. Here k = 15 , N = k × 1 00 , and t = 4 . 0 0.1 0.2 0.3 0.4 0.5 −0.4 −0.2 0 0.2 0.4 0.6 0.8 1 Attack B: Correction Capability p 1 (N w −N v )/(N w +N v ) p 2 =0 p 2 =0.05 p 2 =0.1 p 2 =0.15 Fig. 5. Correction capability of attack B f or k = 32 , N = k × 10 6 , and t = 6 . Negativ e value s giv e a correction capability of zero indicating an inability to con verg e on the correct sequence. 9 T ABLE I S I M U L A T I O N R E S U LT S O F AT TAC K B C O M PA R I N G S C E N A R I O S W I T H A N D W I T H O U T A D D E D S E C U R I T Y D U E T O T H E P H Y S I C A L L A Y E R . F O R T H E S E S I M U L AT I O N S , k = 31 , N = k × 100 , t = 6 , A N D p 1 = 0 . 2 . Case 1: p 2 = 0 Case 2: p 2 = 0 . 1 Number of T otal Num ber of T otal Round bits flipped correct bits bits flipped correct bits 1 30 2487 1 2276 2 91 2526 3 2277 3 122 2586 6 2277 4 42 2628 8 2275 5 50 2676 11 2268 . . . . . . . . . . . . . . . 14 43 3075 2 2204 15 23 3098 100 2164 16 2 3100 4 2164 . . . - - . . . . . . 34 - - 1 2079 35 - - 0 2079 . . . - - 0 2079 implying p 1 = 0 . 2 . In the fi rst of tw o cases p 2 = 0 , meaning the eav e sdropper is able to decode all channe l errors in the wiretap channel using ECC, thus p ′ = p 1 = 0 . 2 and the correction ratio C is calculated using (5) to be 0 .826. Case two ass umes that p 2 = 0 . 1 indicating an error rate of 10 p ercent in ( y n ) which yields p ′ = 0 . 26 b y (1), and C = − 0 . 034 by (5). Due to thes e values o f C , it is expec ted that a ttack B will succee d in case on e and fail in cas e two. Co mparisons of the attac ks a re s hown in T ab . I, where it is see n that ca se one con verges on the co rrect output sequen ce in 16 roun ds. Ca se two, howe ver , req uires 34 rounds before the algorithm stagna tes a nd fails, a majority of rounds resulting in more bits in error than the previous round. Clearly an eavesdropper h as b een mad e to fail in an otherwise succe ssful scena rio d ue to the increas ed sec urity inhe rent in the system which ca n be produ ced by wise implementation of channe l coding. 10 V . C O N C L U S I O N In conclusion , the wiretap c hanne l model has b een used to show se curity enh ancemen ts for wireless applications by considering the c hannel co ding problem and the cryptograph y problem in tan dem. T hese enhanc ements oc cur due to eff ec ts in the physica l laye r of a communications sys tem. For a variety of applications where a n eavesdropper experiences worse cha nnel co nditions tha n thos e be tween friendly parties, p roper implemen tation of c hanne l coding ca n ensure an increased dif ficulty in cracking crypto- graphic s ystems by preserving b it e rrors in the wiretap ch annel due to the physica l layer . This principle was shown using an LFSR-ba sed cryptograph ic system which is s usceptible to c orrelation attack s in some cases . It has bee n shown us ing theory a nd s imulations for two d if ferent attack s that c hannel coding c an be use d to either increase the dif ficulty of the a ttack or make it altoge ther impossible, thus providing a physical layer o f security to the system. R E F E R E N C E S [1] A. D. W yner . The wire-tap channel. Bell System T echn ical Jou rnal , 54:1355–1 387, Oct 1975. [2] J. Barros and M. R. D. Rodrigues. Secrecy capacity of wi reless channels. Information Theory , 2006 IEEE International Symposium on , pages 356–360, July 2006. [3] I. Csiszar and J. K orner . Broadcast chann els wi th confidential messages . Information Theory , IEEE Tr ansactions on , 24(3):339–3 48, May 1978. [4] V . K. W ei. Generalized hamming weights for l inear codes. I nformation Theory , IEEE Tr ansactions on , 37(5):1412–1418 , Sep 1991. [5] A. Thangaraj, S . Dihidar , A. R. Calderbank, S . W . McLaughlin, and J-M. Merolla. Applications of ldpc codes to the wiretap channel. Information Theory , IEEE T ransactions on , 53(8):2933–2945, Aug 2007. [6] M. Bloch, J. Barros, M. R. D. R odrigues, and S . W . McLaughlin. Wireless information-theoretic security . Information Theory , IE EE T ransactions on , 54(6):2515–2534 , June 2008. [7] W . Meier and O. Staffelbach. Fast correlation attacks on certain stream ciphers. Journ al of Cryptology , 1:159–176, 1989. [8] C. E. Shannon. Communication theory of secrecy systems. Bell System T echnica l J ournal , 28(4):656–715 , 1949. [9] D. W elsh. Codes and C ryptog raphy . Oxford Univ ersity Press, W alton S treet, Oxford O X26DP , 1988. [10] T . Siegenthaler . Decrypting a class of stream ciphers using ciphertex t only . C omputers , IEEE T ransac ti ons on , C-34(1):81– 85, Jan 1985. [11] V . V . Chep yzhov and B.J.M. Smeets. On a fast correlati on attack on certain stream ciphers. In EUROCRYPT , pages 176–18 5, 1991. [12] T . Johansson and F . Jonsson. Theoretical analysis of a correlation attack based on con volutional codes. Information Theory , IEEE T ransactions on , 48(8):2173–21 81, Aug 2002. [13] Promoter Members of Bluetooth SIG. Specification of the Bl uetooth System - Cor e V ersio n 2.1 + EDR . Bluetooth SIG, Inc., July 2007. [14] T . K. Moon. Err or Correction C oding: Mathematical Methods and Algorithms . John Wile y & Sons, Inc., Hoboke n, NJ, 2005. 11 [15] T . K. Moon and W . C. Stirl ing. Mathematical Methods and Algorithms for Signal Pro cessing . P rentice-Hall, Inc., Upper Saddle River , NJ 07458, 2000. [16] R. G. Gallager . Low-Density P arity-Check Codes . MIT Press, Cambridge, MA, 1963. [17] Frank Ruske y . The combinatorial object server (C OS). http:/ /www .theory . cs.uvic.ca/ cos/gen/poly .html, S ep 2008. 12
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment