Technical Report: Multi-Carrier Position-Based Packet Forwarding Protocol For Wireless Sensor Networks
Beaconless position-based forwarding protocols have recently evolved as a promising solution for packet forwarding in wireless sensor networks. However, as the node density grows, the overhead incurred in the process of relay selection grows signific…
Authors: Ahmed Bader, Karim Abed-Meraim, Mohamed-Slim Alouini
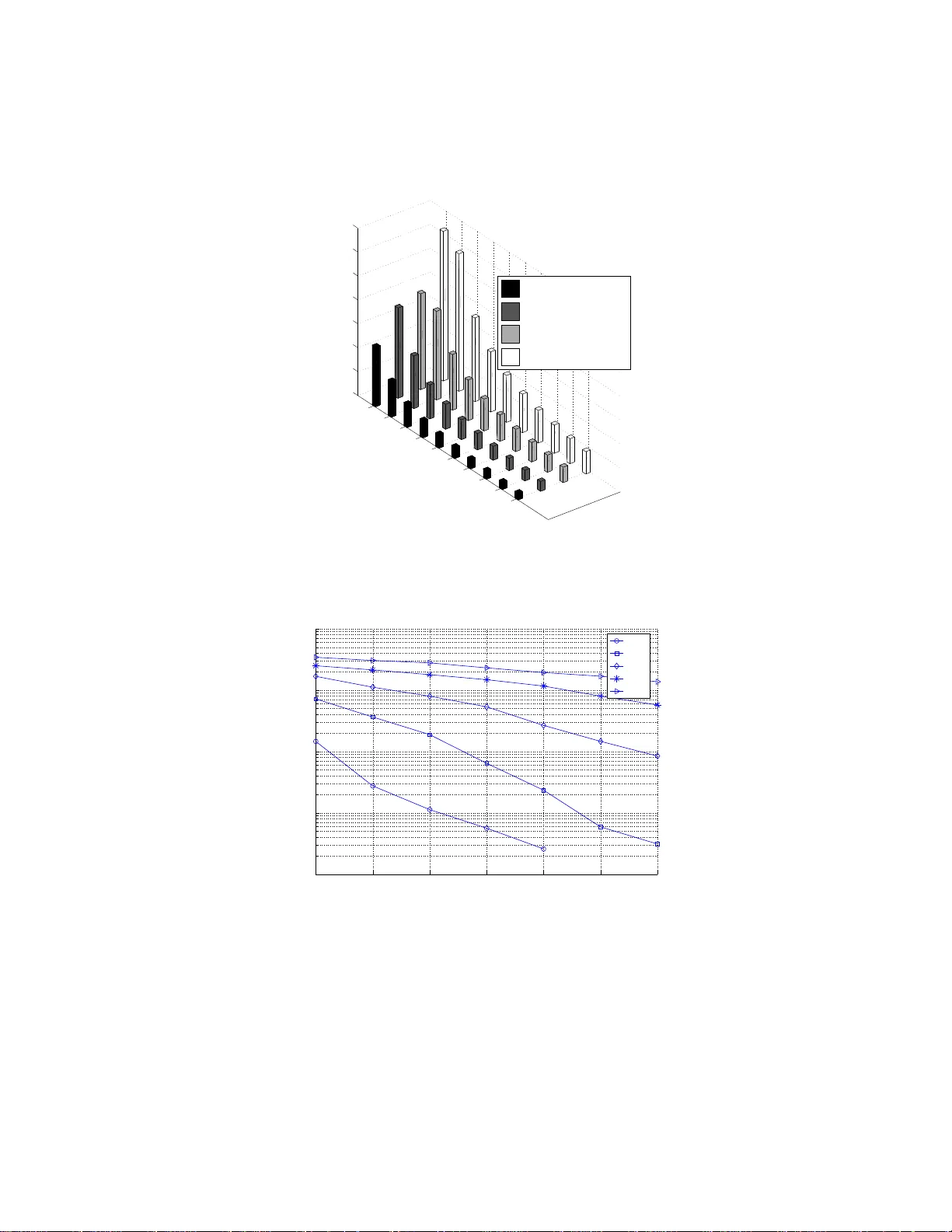
1 T echnical Report: Multi-Carr ier Position-Based P ack et F orw arding in W ireless Sensor Netw orks* Ahmed Bader and Karim Abed-Meraim T elecom P arisT ech, P aris, France { bader ,abed } @telecom-paristech.fr Mohamed-Slim Alouini KA UST , Thuwal, Mekkah Pro vince, Saudi Arabia slim.alouini @kaust.edu.sa Abstract Beaconless position-b ased forwarding protocols ha ve recently e volved as a pro mising solution for packet forwarding in wireless sensor networks. Ho we ver , as the node density grows, th e overhead incurred in the process o f relay selection gr ows sign ificantly . As such, en d-to-en d performan ce in terms of energy and latency i s adversely impacted. W ith the moti vation o f dev eloping a packet forwarding mechanism that is toler ant to node density , an alter native position -based protocol is proposed in this paper . In con trast to existing beacon less proto cols, the pr oposed pro tocol is designed such that it eliminates the need for p otential r elays to un dergo a relay selection p rocess. Rather , any eligible relay may de cide to fo rward the packet ahead, thus significan tly reducing the und erlying overhead. The ope ration of the propo sed protocol is empowered b y exploiting fa vorable features of orthogo nal frequen cy division m ultiplexing ( OFDM) at the physical lay er . The end-to-en d perfo rmance of the propo sed pro tocol is evaluated against existing beaconless position-based protocols a nalytically and as well by means of simulations. Th e propo sed protocol is demo nstrated in this paper to be more efficient. In par ticular, it is shown that for the same amount of energy the p roposed proto col transports on e bit from source to d estination much qu icker . * This work was supported by Qatar National R esearch F und (a member of Qatar Foundation ). 2 I . I N T R O D U C T I O N W ireless sensor net works (WSNs) are b eing increasingly consi dered for a mult itude of mon- itoring and t racking applications in the fields of process automati on, en viron mental moni toring, and tactical operations [1]. WSNs are not limited to terrestrial deployment scenarios but rather extend to subm arine en vironments [2]. The WSN umbrella is also being expanded to fit more specific applicatio ns su ch as smart utility networks [3], [4] and multimedi a applicati ons [5]. The sincere interest i n WSNs coupled w ith the wide sp ectrum of pos sible app lications hav e created a tangibl e research surge across all layers of the p rotocol stack over the past decade. Y et, most research ef forts t end to fine tune the balance between performance and cost. The most im portant factors influencing the design of WSNs are: energy , lat ency , com plexity , and scalabi lity [1], [6]. Pack et forwarding is indeed one of t he research issues which directly impacts all of the aforementioned design factors. Position-based forwarding protocols have emer ged as some of the most ef ficient packet d eliv ery solutions for WSNs [1]. This is mainly d ue to the fact that nodes can locally make their forwarding decision s using ver y lim ited knowledge of the ov erall network topology . Howev er , classical position-based forwarding relies on periodical exchange of beacons in the form of location updates between neighboring nodes. Evidently , the beacon exchange p rocess can often lead t o a waste of bandwidt h [7]. T o alle viate this shortcomi ng, beaconless position-bas ed forwarding techniques hav e e volved as bein g more ef ficient. T wo of the earliest such protocols reported in literature are Geographic Random Forw arding (GeRaF) [8], [9] and Beaconless Routing (BLR) [10]. In beaconless positi on-based forwarding, potential relays undergo a distributed selection process whereby the node with the most fa vorable attributes (e.g. closeness to destination) s hall e ventually win the contention [7]. The sender of a packet first i ssues a request-to-send (R TS) message. U pon the reception of th is message, potential relays lying within the sender’ s cov erage zone enter int o a time-based contention phase. Each potential relay triggers a timer whose expiry depend s on a certain cost function. The first nod e to have its timer expire will transmit a clear -to-send (CTS) message o n the next time s lot. Howe ver , since time is slotted it is quite probable for colli sions to occur . A secondary coll ision resolutio n phase will be required in that case. The ideas presented in [8], [9] and [10] hav e been well-accepted within the re search community and have been furthered and/or adapt ed in [11], [12], [13], [14], [15]. In Contention-Based 3 Forw arding (CBF) [11], response time to a R TS message is rather calculated as function of the adv ancement towards the destination . In [12], a prot ocol dubbed as Impl icit Geographical Forw arding (IGF) is propos ed. IGF ut ilizes residual ener gy and progress tow ards the destinat ion as joint criteria for relay selection. On the other hand, MA CR O [13] wei ghs th e response time of pot ential relays with t he progress that can be made per unit power . Aut hors of [14] propose a technique called Cost- and Collis ion-Minim izing Rout ing (CCMR) whereby contending relays dynamically adjust t heir cost metrics during the selection p rocess. In [15], GeRaF is modified such that it serves wireless sensor networks w ith multi ple si nks. Beaconless posi tion-based forwarding offer ed v aluable improv ements compared to their beacon- based predecessors. Ho w e ver , t hey are pl agued by an overhead which rapidly grows wit h node density . As node densit y grows, collisions betw een candidate relays contending for medium are mo re prob able to occur , and thus the overhead incurred grows not iceably . No t only does this degrade end-to-end delay performance, but it also increases the mean ener gy con sumption. Furthermore, existing beaconless position -based p rotocols hav e been built and e valuated based on the classical “disc” cove rage model. Under realist ic multipath channel models, this causes frequent duplication of packets and obviously leads to the creation of co-channel interference [16]. In this paper , a nov el position -based forw arding protocol is proposed. The protocol’ s main virtue is that it does not resort to any relay selecti on process. At any given hop , potential relays check whether t hey satisfy certain posi tion-based criteria. Any relay that does s atisfy th e criteria decides to forward the packet ahead. It does so without rev erting to any sort of coordinatio n with other potential relays. At the terminals of a receiving node, such a mechanism would undoubtedly create mu ltiple copies o f t he same packe t wit h different propagation delays. T o remedy th is problem, we utilize a phys ical layer (PHY) which is built over the u se of orthogonal frequency division multiplexing (OFDM). By virtue of introdu cing a cyclic prefix (CP) to each OFDM symbol, a packet w hich is being simul taneously forwarded by multi ple nodes can be correctly detected at a recei v ing node [17]. Early generations of WSNs hav e actually employed low-po wer Zigbee radios [18]. Zigbee is an IEEE specification utilizing Di rect Sequence Spread Spectrum (DSSS) and is based on the IEEE 802.15.4 standard for wireless personal area networks (WP ANs)[6 ]. Nev ertheless , considering OFDM radios is a trend wh ich has recently s tarted to pick up and gain tractio n [19], [20]. The 4 adoption of OFDM (also often referred to as multi -carrier modul ation) is m ainly motivated by its ability to con veniently accommodate larger c hannel bandwidths while featuring less susceptibility to common radio channel impairments [17]. The idea of using OFDM for concurrent transmiss ions of the same packet has been actually proposed before in [21], [22]. Nevertheless, the work of [21 ], [22] was p resented in the context of uti lizing OFDM for ef ficiently flooding a message across the whole network. Obviously , this does not fit well i nto the WSN m odel wh ere data from sens ors m ust be effi ciently dissem inated to a very lim ited number of sin ks. In the prot ocol presented in this paper , OFDM is combined with posit ion-based relayi ng in o rder to streaml ine packets towar ds the intended d estination. The protocol presented herein is t he fruit of the marriage between position-based relaying and OFDM. Nodes at a gi ven hop i will decide to relay or not based on the positio ns of the source, the destination, and the relays of the previous h op, i − 1 . OFDM on the o ther hand enables concurrent packet transmis sions. The prop osed proto col dedicates part of the OFDM time-frequency resources for a set of random access chann el (RA CH) slots . Each relay from the ( i − 1) th hop randomly selects one of the RA CH slots and modulates it with its position information. When pot ential relays of th e i th hop receive the packet, they will read the posit ion information on all RA CH slots and accordingly decide whether or not to relay . Obviousl y , it is probable t hat some RA CH s lots may be selected by more than one relay . Nonetheless , it wil l be demonstrated t hat such “collisions” on t he RA CH slots on ly affect the ener gy performance as well as the achiev abl e hop di stances. In other words, they do not impact th e progression of the packet towards its dest ination. Furthermore, i t will be shown that the p roposed proto col im proves the end-to-end delay performance when compared t o existing beaconless schemes. Howe ver , the amount of end-to-end energy consum ed is typically lar g er . Thi s is due to the fact that o ne packet is concurrently t ransmitted b y multi ple nodes ev ery hop. Interestin gly , th e imp rove ment attained in term s of delay performance is suffi ciently l ar ge to offset the impact of additional ener gy consumption . Indeed, th is is the majo r contribution of this paper . The rest of the paper i s organized as foll ows. Section II offers an elabo rate description for the operation of th e protocol. Section III presents a model for the wireless channel and the ph ysical layer . A detailed stati stical analys is of the hoppi ng behavior un der the proposed protocol is given in section V. Ev aluation of the end-to-end performance against existin g beaconless position- based protocols and sim ulation results are provided in section VI. Finall y , the m ain results are 5 summarized in secti on VII. I I . D E S C R I P T I O N O F P R OT O C O L O P E R A T I O N Since t he p roposed prot ocol is b uilt around the concept of utilizin g OFDM, we will refer to it herein as OMR which is short of “OFDM-based M ultihop Relaying”. A. K e y Assumptions The following are ke y assumptions we used i n the course of dev eloping OMR: 1) Positi ons o f packet sinks are known to all nodes. Packet si nks may periodi cally advertise their own po sitions to the rest of t he network by means o f a flooding process. In addition , all nodes have knowledge of their own posit ions. In the analysis, the source node V is located in t he cartesian space at (0 , 0) while the destination Q is at ( L, 0) . 2) Nodes are randomly distributed in the network according to a 2-D Poisson point distrib u tion with densit y ρ . Furthermo re, nodes implement a non-synchronized sleeping schedule wi th a duty cycle of ǫ . 3) If a node i s awak e but does no t have data to transmi t, t hen it will be in a s tate of channel acquisition. In this st ate, the node will be continuously monitoring th e wireless m edium for syn chronization pilots s o as to be able to lock to any nearby transmission / relayin g process. 4) A decode-and-forward relaying strategy is adopted and nodes ha ve om ni-directional an- tennas. 5) Packet sinks are stationary . No des howe ver can be fixed or mob ile. For packet duration s in the range of milliseconds, the node topology during one hop can be con veniently considered to st ay unchanged even for s peeds of up t o 100 k m/hr . 6) A b usy t one is activ at ed d uring listening and receiving to help mit igate the hidden node ef fect. B. P ac ket F orwar ding Pr ocess In the sequel, we wi ll describe in det ail how a packet is relayed towards th e destinat ion. The source node V will first encode its own pos ition information and that of the destinati on Q on two separate packet fields t hat are dedicated for this purpose. Figure 1 ill ustrates th e proposed 6 packet structu re for OMR. Each packet is appended by a CRC sequence. The source nod e then senses the wireless medium. The sensing acti v ity m ust b e performed on the data tones as well as the busy tone [8], [9], [23]. If there e xists any ongoing transmis sion in the vicinity i t backs off . Fixed window with binary exponential decrease back-off alg orithms may be employed to maintain proportional fairness in the network [24]. If the medium is n ot b u sy , the s ource n ode will transmi t the packet. A waken nodes lying within t he transmi ssion range of the source node will first attempt to decode the packet and wi ll activ ate the busy tone meanwhile. Nodes pass ing the CRC check will become part of the d ecoding set of the first hop denoted as D 1 . As a notational standard in t his paper , nodes in a given set are sorted in an ascending order according to their distance to the destinatio n Q . T wo position-based criteria are ev aluated by each n ode in D 1 . The first is proximit y to t he destination compared t o the source. The second i s whether it lies within a forw arding strip of widt h w surrounding the line between V and Q . The main objective of introducin g the second criterion is t o streamli ne the forwarding process into a certain geographical corridor . This will ensure th at the interference created b y the forwarding process is confined t o a certain geog raphical region th us maki ng more room for other forwarding processes. Nodes in D 1 satisfying the two position-based criteria outlined above will become part of the relaying set R 1 . T o proceed, nodes in R 1 will ha ve to con vey their posi tion information to nodes of the second hop. As shown in figure 1, the packet includes B RA CH slots which are used for just that purpose. Each relay random ly s elects one of t hose RA CH slots to m odulate i ts position information. N aturally , it is prob able that one or mo re relays may choose the s ame RA CH slot. In such a case, it will not be possible to resolve the positi on information of neither of those relays. Nodes of the second hop are able to pick up the position i nformation of only those nodes in R 1 which ha ve selected unique RA CH s lots. Relays of th e set R 1 will transm it th e packet after a small guard period. A w aken nodes which correctly recei ve t his transmission will no w form the set D 2 . A node i n D 2 will decide to forward th e packet if: it is inside the forwarding strip, and is closer to the destination than all nodes of R 1 whose po sition i nformation could be resolved. Th e forwarding process continues as described above for the next ho ps and is further illustrated by an example in figure 2 . The so urce gi ves each packet a unique identification (ID) label. Due to the sporadic nature of th e wireless channel, a node may recei ve the sam e packet a second time. By means of th e 7 unique ID, the node will able to determine it is a dupli cate packet and thus will decide to drop it. This shou ld h appen before it conti nues the decoding process, i.e. the node will no t be p art of the decoding set of nodes. C. Ef fect of RA CH Collisions The number of relays at hop i is denoted by e K i such t hat R i = { R i,k } e K i k =1 . A RA CH collision is defined within this context as the ev ent of having two or m ore relays select the same RA CH slot to modu late their position informat ion. As such, next-hop nodes will not be able to resolve the pos itions of those relays. Recalling th at R i is an o rdered set, we define ( j i ) to be the index of the first node in R i whose posi tion is resolvable, i.e. th e positio ns of the first j i − 1 nodes are un resolvable. Accordingly , it is prob able that some nodes at hop i + 1 m ay relay the p acket e ven though they d o not offer positive progress towa rds the destinati on. In other words, they may be farther from the destination compared to some or all of those j i − 1 relays. This is best illustrated by an e xample. Looking at figure 2, node R i, 7 does not offer positive progress with respect to the node R i − 1 , 1 ∈ R i − 1 . Nonetheless , R i, 7 will actually d ecide to relay since the posi tion information o f R i − 1 , 1 happens to be unresolvable. The first node in R i − 1 whose position is resol vable is R i − 1 ,j i − 1 , where in this specific example j i − 1 = 2 . The relaying criteria described above can be formalized by first defining x C i as the arc extended from Q and passing through node R i − 1 ,j i − 1 . Subsequently , a node in D i will relay the pack et if it li es in the area ≬ { x C i , y = ± w 2 } . Throughout thi s paper we use the operator ≬ to denote the area confined between mul tiple contours. D. Carrier S ense Multi ple Access at the Sourc e W e denote the number of nodes forming the decoding set at hop i by e L i = | D i | During hop i , the back-off region produced by the forwarding process is composed of two subareas. The first one i s governed by t he activity on the data channel, i.e. the concurrent transmissions of e K i − 1 relays. The second sub area is actually dictated by the s uperposition o f the busy tone s ignals from all e L i recei ving nodes. As such, the back-of f re gion is substantially larger than th e coverage zone of a sing le node, e.g. a hid den node. Accordingly , relays in the case of OMR can drop the task of sensin g the medium before accessing it. Channel sensi ng is only performed by the packet source node u pon the injection of a brand new packet. In contrast, relays in existing b eaconless 8 protocols cannot afford as much not to list en to the chann el before transm itting. This is because the back-of f region at the final stages of the relay selectio n cycle is dictated by only very few candidate relays. In ot her words, it will be onl y slightly lar ger than the interference zone of a hidden node. Therefore, t he impact of a poss ible hidden node transmis sion i s more drastically felt in the case of traditio nal beaconless protocols. It is worthwhile not ing at this poin t that the hidden node issue has been i mplicitly ov erlooked i n [10], [11], [12], [13], [14], [15]. On th e other hand, it was ignored in [8] and [9] under the assu mption of light to moderate t raf fic loads. E. Retransmission P olicy For the purpose of makin g OMR more reliable, a retransmiss ion policy m ust be devised. Nodes of R i will need to retransmi t if the set R i +1 is empty , i.e. if there are no nodes which decide to transmit the packet at hop i + 1 . T o detect this e vent, each relay in R i must listen to the wireless channel to verify that the packet is being forwarded ahead. A relay in R i will consider that the packet is being forwarded if it is able to detect that packet’ s ID during the listening phase. Th e packet ID is allocated a distinct field in the pack et’ s header as shown in figure 1. For the sake of sa vi ng ener gy , relays do not cont inue listening beyond the packe t ID time mark. Therefore, the listening activity o nly occurs for a limited duration denoted h ere as t I D . Powerful error coding must be utilized for the p acket ID field to make the listening task more robust. Every tim e t he pack et is retransmitted, the width of the forwarding strip, w , is increased by adjusting the corresponding value i n the p acket header (figure 1). This reduces the probabil- ity that anot her retransmissi on w ould be required. An expression for the expected number of retransmissions at a g iv en hop count is deri ved in section V and is gi ven in equation (24). It is also plo tted in figure 3(a) for v ario us values of node density and transmit power . It i s clear from th e figure t hat the expected number o f retransmissions probabil ity decreases as the packet progresses towar ds t he destination or as the node dens ity increases. Similarly , retransmis sion is less l ikely to occur as the transmit powe r increases. Having d escribed the retransmiss ions poli cy , we can now summarize all different p rotocol states along with correspondi ng state transi tions in the diagram of figure 4. 9 F . F alse Alarm Retransmiss ions A special case worthwhile in vestigating here is when a re lay mak es a n err oneous retransmission decision. Th is happens if a packet i s actually being forwarded ahead by nodes of R i +1 , but a relay from R i believ es otherwise, i.e. it was not able to detect the packet ID during the l istening phase. In order to minimize the implications of a such a “false alarm” case, relays must retransmit the packet on ly after th e full packet duration (denoted here by T p ) elapses. M oreover , the num ber of retransmi ssions m ust be also capped to a void infinit e retransmission loop s by the false-alarm relay . If the number of retransm issions i s capped at n r max , then the impact of a f alse-alarm retransmission event is only limited to incrementing the size of the relay sets { R i + n } n r max +1 n =2 by one. W e assume that the guard ti me of the OFDM symb ol is in the range of 120 µ s s imilar to [19]. Consequently , for a false alarm retransmissi on t o cause harmful interference, i t has to lie mo re than 7 . 2 k m away from t he current hop . T ypical dimensions of a WSN makes us easily conclude that it is quite unlikely for harmful interference to occur in the case of false-alarm retransmissio ns. Furthermore, i n case of a dense network and highl y redundant error codi ng of the pack et ID, the false-alarm e vent becomes ev en more unlikely to occur . Indeed, this intuition is v alid ated in figure 3(b). Accordingl y , we are practicall y able t o neglect false-alarm retransm issions i n ou r subsequent analysi s. G. Miscellaneous Finally , i t is worthwhile mentio ning that we have ev aluated the p otential of utilizin g transm it div ersity techniques for OM R. In particul ar , we h a ve considered the us e of random ized transmit codes [25] s ince they do not require relays to coordinate their precoding matrices. Howe ver , the implementati on of such codes m ay prove to induce substanti al ov erhead as they mandate long training sequences for proper channel esti mation. Furthermore, they are su itable for t he specific case of narrow-band fading channels but not necessarily for wideband channels . I I I . P H Y S I C A L L A Y E R M O D E L I N G In this section, a math ematical mo del for the ov erall channel respo nse is presented. Further - more, a condition for successful packet detection is de veloped. 10 A. W ireless Chan nel Model The channel between an arbit rary pair o f nodes is represented by a generic wideband multi path tap-delay line wi th Rayleigh-distributed tap gains [26] as sh own in figure 5. On average , there are n h such taps. Natural echoes due to multipath are g rouped in intervals of duration of T seconds. The delays T ′ 1 , . . . , T ′ e K i − 1 reflect the general case that the start of the e K i − 1 transmis- sions are no t perfectly aligned in time. The duration of t he OFDM sym bol is assumed t o be lar ger t han ( n h − 1) T + max { T ′ k } e K i − 1 k =1 − min { T ′ k } e K i − 1 k =1 ensuring t hat each subcarrier encounters approximately a frequency-flat fading [17]. Amendi ng each OFDM sym bols with a cyclic prefix eliminates in ter -carrier interference (ICI) and resto res orthogon ality between subcarriers. This enables decoupled signal detection at each subcarrier . Given a certain packet is relayed at hop i by e K i − 1 nodes, then the frequenc y response of the total channel at subcarrier f l is given by H ( f l ) = P e K i − 1 k =1 e − j 2 πf l T ′ k P n h n =1 h k ,n e − j 2 πf l ( n − 1) T . It is assumed that the duration of the cyclic prefix of the OFDM symbol is long enough such that all sig nal echoes (natural and artificial) arri ve within the cyclic prefix interv al. Other ongoing packet relaying processes wil l rather contribute to the i nterference signal. This interference howev er wil l be also Gaussian sin ce the individual channel g ains are Gaussian [27]. The exact nature of such an external int erference is beyond the scope of the present paper and is rather a subject of future work. Under the reasonable assumption t hat the fading coef ficients h k ,n are all mutually independent , it follows that H ( f l ) is complex Gaussian such that H ( f l ) ∼ N (0 , σ 2 S ) . | H ( f l ) | 2 is exponentially distrib uted with a m ean of 2 σ 2 S = 2 P e K i − 1 k =1 P n h n =1 E [ | h k ,n | 2 ] . W e not e t hat P n h n =1 E [ | h k ,n | 2 ] represents the mean power content of the chann el between the recei ver and the k th relay and is equal to λ/ 4 π p ( x − x k ) 2 + ( y − y k ) 2 α . Here λ represents the wa velength, α is the large-scale p ath loss exponent, and p ( x − x k ) 2 + ( y − y k ) 2 is t he dis tance from t he recei ver located at ( x, y ) to the k th relay located at ( x k , y k ) . Therefore, we obtain σ 2 S = λ 4 π α e K i − 1 X k =1 1 (( x − x k ) 2 + ( y − y k ) 2 ) α 2 . (1) Phase shift keying (PSK) modulation i s uti lized such that t he transmi t powe r is equal for all subcarriers. The signal to interference plus noise ratio (SINR) at subcarrier f l is giv en by γ ( f l ) = P t | H ( f l ) | 2 N s P n , where P t is th e t ransmit power over the wh ole bandwid th, N s is th e nu mber of sub carriers, and P n is t he noi se plu s interference power within th e subcarrier bandwid th. The 11 a verage SINR is subcarrier- independent and is denoted by γ o = 2 P t N s P n σ 2 S . B. Successful P ack et Detection The outage probability , P o , is the probability that γ ( f l ) < γ t and equals 1 − e − γ t /γ o . W e consider that a packet is su ccessfully detected if P o < τ , where τ is a detection reliability parameter [28]. The value of τ relies on t he underlying coding and interleaving techniques 1 . W ith 0 < τ < 1 , and recalling that γ o = 2 P t N s P n σ 2 S , then the condition for successful detection is expressed as σ 2 S ≥ N s P n γ t 2 P t ln 1 1 − τ . (2) The m ean coverage contour fo r hop i is denoted by x H i ( y ) , | y | ≤ w 2 . Based on th e successful packet detection conditi on of (2) and i n light of (1) we define x H i ( y ) : H i ( x H i ( y ) , y ) = U, (3) where H i ( x H i ( y ) , y ) = e K i − 1 X k =1 1 (( x H i ( y ) − x k ) 2 + ( y − y k ) 2 ) α 2 , U = N s P n 2 P t 4 π λ α γ t ln 1 1 − τ . For t he first hop, we hav e x H 1 ( y ) = q 1 U 2 α − y 2 . I V . P R AC T I C A L C O N S I D E R A T I O N S A. T iming Consideration s W e recall our assump tion that a fairly accurate clock and frequency s ynchronization between nodes is attain ed v ia the sam e p rocess b y which the pos ition inform ation i s acquired [1]. In fact, the forwarding process itself may als o aid to achie ve the s ame goal by means of t he synchronization pilots inserted in the packet header . Furthermore, if an external localization method such as the glob al position ing system (GPS) is used, then nodes can be also aligned to a universal time reference. Ho we ver , GPS is known t o be power -hungry and thus i s generally 1 W ith reference to figure 1, it is assumed that interleaving is only applied to the payload and CRC portions of the pack et. This wi ll enable relays in the listening phase to drop right after the packet ID time mark. 12 unfa vorable for WSNs. When other localization methods are ut ilized nevertheless, we must assume that a u niv ersal tim e reference does not generally exist. Instead, a node in the receiving state will align its t ime reference to the first energy arri val. As such, no des within a decoding set D i will generally ha ve different time references. This concept is illust rated in figure 6. Non-aligned time references obviously results in asynchron ous transm issions by relays. It is important at this po int to study th e implications of asynchronous relaying on the delay spread at the dest ination Q . For an arbitrary node R i,k , the propagati on del ay of the 1st ener gy arriv al with respect t o the packet s ource is given by t he following recursive formula d p i,k = min { R i,k R i − 1 ,n + d p i − 1 ,n + δ r } e K i − 1 n =1 . (4) In (4) we have expressed propagation delay in terms of d istance rather than t ime for no tational con venience. The term δ r in E quation 4 represents the differe nce in length between the specular path and the first m ultipath echo of the Rayleigh channel. W e recall that Rayleig h channels do not include a specular path. For the sake of simplicit y , we assum e that δ r is approximately equal for all pairs of nodes selected from wi thin two consecutive hops. The forwarding delay s pread at the dest ination Q can t hen be expressed as max { QR q − 1 ,k + d p q − 1 ,k } e K q − 1 k =1 − min { QR q − 1 ,k + d p q − 1 ,k } e K q − 1 k =1 . (5) The total delay spread is naturally the sum of the forwarding delay spread and the multipath delay spread. At t he first glance, th e discussion above may induce the impress ion that the forwarding delay spread m ay gro w indefinitely as pack ets progress towards the destination . Howe ver , a closer loo k at the iss ue suggests o therwise. T he first few relays t o receiv e and then transmit the packet at hop i are typically thos e wh o are the closest to the ( i − 1) th hop. At the same time, they are typically t he farthest from the ( i + 1) th hop and thus will hav e t he largest p ropagation delays. It is straightforward to validate t his intu ition analyt ically for a linear network. In fact, it can be shown that for a linear network, packet copies are al igned in time ev ery oth er ho p, i.e. i is e ven. This is t rue when B is s uffi ciently lar g e such that we may ignore the probability of having negati ve progress nodes. For 2-D networks h owe ver , it i s qui te more in volve d to validate such an intuition analyticall y . Rather i t can be more con veniently verified through simulations. figure 7 illustrates the mean and standard de viation of t he forwarding delay spread for strip widths between 100 and 200 meters. Simul ations have been carried out for 3 diffe rent values 13 of node density , ρ . As can be in ferred from the figure, the mean and standard deviation are almost independent of the node density . It is also shown that for t his range of strip width, the mean is approximately 2 µ s with a standard d e viation of no mo re than 0.35 µ s. This is valuable information as it provides guidance on the suitable lengt h of the cyclic prefix. For ins tance t he length o f t he cyclic prefix in L TE is at least 4.7 µ s whil e it is 10 µ s for the IEEE 802.16e standard. Hence it is po ssible to utilize an y o f these two standardized OFDM radios for OMR. This is not the case for th e IEEE 802.1 1g standards where t he duration of the th e cyclic prefix is onl y 0.8 µ s. It can be furth er observed from figure 7(b) that the forwarding delay spread tends to follow a normal distribution. Moreover , figure 7(a) ind icates that the standard de viati on of the forwarding delay spread i ncreases with t he strip wi dth, which is quite i ntuitive. B. Ef fect of T ime Offset on R A CH Signals The si gnal of a non-empty RA CH slot is composed of the superpositi on of the location information of o ne or mo re relays. Each RA CH slot is randomly picked b y a uni que set of relays. As such, each RA CH signal undergoes a different channel to wards a gi ven receiv er . Therefore, RA CH signals are generally expected to be non-align ed in time, as e xemplified in figure 8. Figure 8 is only showing first ener gy arriv als , i.e. subsequent signal echoes are not depicted. The RA CH OFDM symbo l is the aggregation of all t he RA CH signals. As shown in the figure, the receiver aligns its tim e reference to the first energy arriv al of the first OFDM symbol. The FFT w indow is applied every int eger mult iple o f the symbol duration. As a result, some RA CH signals will be suf fering from a time of fset with respect to the st art of t he FFT window . The effect o f time of fset on the detection of OFDM symbols was st udied in d etail in [29]. It was shown in [29] t hat when the time offset is “tow ards” the CP , i.e. the FFT window is partially applied on the CP , then only a phase error is introduced. Interesti ngly , i t is on ly time off sets tow ards the CP are possi ble in the case of OMR. If differential PSK is adopted, then the ef fect of t he time o f fset is greatly mar gi nalized. V . S TA T I S T I C A L M O D E L I N G O F H O P P I N G D Y NA M I C S In this section, an elaborate statisti cal frame work is constructed for the sake of capturing the dynamics of pack et hopping under OMR. W e start of f by rec alling that gi ven e K i relays in R i , then j i represents the index of th e 1 st relay in R i whose p osition information i s resolvable. Our next 14 goal is to derive an expression for the probability density function (PDF) p j i ( j i | e K i ) . T o proceed, we consider that the ordered set R i can be expressed as a blo ck of lengt h e K i constructed from the alphabet { 0 , 1 } . Here “ 0 ” represents the event of being unresolvable w hile “ 1 ” represents the compl ementary event. Furthermore, we represent the “do not care” state wi th “ x ”. Accord- ingly , p j i ( j i | e K i ) is equiva lent to P [ R i, 1 R i, 2 . . . R i,j i . . . R i, e K i = 00 . . . 01 | {z } j i x . . . x] . T o proceed, it is more conv eni ent first to deriv e an expression for the probability P [ R i, 1 R i, 2 . . . R i,j i . . . R i, e K i = 00 . . . 0 | {z } j i − 1 x . . . x] which equals 1 − ( P [00 . . . 01 | {z } j i − 1 x . . . x]+ P [0 0 . . . 10 | {z } j i − 1 x . . . x]+ . . . + P [11 . . . 11 | {z } j i − 1 x . . . x]) . Let us d efine B ( m ) ( · ) as a decimal-to-binary conv ersi on operator and C ( n,m ) ( · ) as a cyclic shift right operator , where m corresponds to the size of t he binary word and n is the order o f t he shift operator . It can be sho wn that t he set represented by { B ( j i − 1) ( k ) } 2 j i − 1 − 1 k =1 is completely co vered by { C ( n,j i − 1) (1x . . . x) } j i − 2 n =0 − { C ( n,j i − 1) (11x . . . x) } j i − 3 n =0 + . . . ( − 1) j i − 1 { C (0 ,j i − 1) (11 . . . 1) } . (6) Furthermore, we define p z as the probabil ity of having exactly z relays in R i whose position information are resolv abl e. p z can be eva luated recursiv ely such that p z = B − 1 B e K i − 1 , z = 1 p z − 1 B − z B − z +1 e K i − z , z = 2 . . . B − 2 0 , z ≥ B − 1 (7) Consequently , it follows from (6) and (7) that P [ R i, 1 R i, 2 . . . R i,j i . . . R i, e K i = 00 . . . 0 | {z } j i − 1 x . . . x] = 1 + j i − 1 X z =1 ( − 1) z j i − 1 z p z . (8) Now since P [ R i, 1 R i, 2 . . . R i,j i . . . R i, e K i = 00 . . . 01 | {z } j i x . . . x] is equal to P [ R i,j i = 1] P [ R i, 1 . . . R i,j i − 1 = 00 . . . 0 | R i,j i = 1] , then we obtain p j i ( j i | e K i ) = B − 1 B e K i − 1 1 + P j i − 1 z =1 ( − 1) z j i − 1 z p z , j i = 1 . . . e K i 1 + P e K i z =1 ( − 1) z j i − 1 z p z , j i = 0 (9) where j i = 0 refers to the ev ent of all relays being unresolvable. The probabi lities p z and p 1 in (9) are re-e valuated by replacing B in (7) with B − 1 . Since p 1 > . . . > p z − 1 > p z , i t can be shown that dp j i ( j i | e K i ) dB < 0 , i .e. p j i ( j i | e K i ) decreases mon otonically in B . This is intuitive since the num ber of RA CH collisions is expected to decrease as B increases. 15 Another i mportant modeli ng aspect is to characterize the m ean cover age contou r at each hop. From (3), i t can be sho wn that x H i ( y ) , | y | ≤ ± w 2 is concav e, i .e. x H i ( y ) has a single maxim um in | y | ≤ ± w 2 . This indicates that x H i ( y ) may be approximated by a circular arc. Furthermore, as w increases, so does e K i − 1 (on av erage). For two st rip widths, w 1 and w 2 , where w 2 > w 1 , we have x H i ( y , w 2 ) > x H i ( y , w 1 ) . This suggest s that if x H i ( y ) is to be approximated by an arc, then its radius depends on w and thus can b e expressed as Ω w c , where Ω and c are network-dependent constants. Indeed, the circularity of t he coverage conto ur and t he dependency of its radius on w hav e been validated numerically through a suf ficient number of simulations. Those simulatio ns hav e also re vealed th at the progress made every hop may be approx imated by a lin ear functi on in e K i − 1 as demo nstrated in figure 9 . In other words, ∆ x H i ( y ) = x H i ( y ) − x H i − 1 ( y ) is equiva lent to ϕ e K i − 1 + β x H 1 (0) , wh ere ϕ and β are network-dependent constant s, and x H 1 (0) = 1 /U 1 α . Consequently , we get the following recursive relationshi p x H i ( y ) = x H i − 1 ( y ) + ϕ e K i − 1 + β U 1 α = ϕ i − 1 X n =1 e K n + ( i − 1) β U 1 α + x H 1 ( y ) . (10) The intuition behind the linear approximation in (10) may be better perceiv ed by considering the hypoth etical case of having e K i − 1 co-located relays. In such a case, we ha ve x H i ( y ) = x k + q ( e K i − 1 /U ) 2 /α − ( y − y k ) 2 using (3). It can be shown th at a linear approxim ation here is good enough to provide a m ean absolut e percentage error (MAPE) of 5.5 % (and as low as 3 % for e K i − 1 > 3 ). T o further s tudy the hopp ing beha vior of OM R, we consider th e prob lem setup shown in figure 10. F o r narrow strips ( w /L relati vely small), t he decisi on cont our x C i ( y ) can b e con veniently assumed to be axially centered around t he line y = 0 . W e recall that for ho p i − 1 , we denoted the 1 st relay in R i − 1 whose position i nformation is resolvable by R i − 1 ,j i − 1 . W e need to find an expression for the dis tance of R i − 1 ,j i − 1 aw ay from th e p oint ( x H i − 1 (0) , 0) which is in return approximately equal to the distance x H i − 1 (0) − x C i (0) . The expectation of the dist ance to the n th nearest neighb or in a sector with angle φ was deriv ed in [28] and is given by q 2 φǫρ ( n − 1 − π 4 ) . W ith reference to figure 1 0, the sector angle φ can be app roximated to extend from ( x H i − 1 (0) , 0) to the intercepts of x H i − 1 ( y ) with | y | = w 2 . Thus, φ can be estimated to be q uite close to π . Therefore we get x C i (0) ≈ x H i − 1 (0) − r 2 π ǫρ j i − 1 − 1 − π 4 . (11) 16 W e further define t he following areas (where | y | ≤ ± w 2 ): A D i = ≬ { x H i − 1 ( y ) , x H i ( y ) } , (12) A R i = ≬ { x C i ( y ) , x H i − 1 ( y ) , x H i ( y ) } , (13) A − D i = ≬ { x H i − 3 , x H i − 1 } , (14) A − R i = ≬ { x C i ( y ) , x H i − 1 ( y ) } . (15) Moreover , the number of relays able to decode the packet at i ts i th hop is denoted by e L i = | D i | . In fact, e L i is composed of two terms such t hat e L i = L i + L − i . The t erms L i and L − i correspond to nodes lying in A D i and A − D i respectiv el y . W e note that L − i can be further broken do wn into two com ponents. The first corresponds to the nodes in ≬ { x H i − 2 , x H i − 1 } wh o were asl eep at the ti me when R i − 2 began their transmission b ut woke up before the t ransmission end ed. Whereas the second encompasses the nodes in ≬ { x H i − 3 , x H i − 2 } who were asleep d uring the whole t ransmission duration of R i − 3 and only woke up before the transmiss ion of R i − 2 ended. For sim plification and concis eness of the su bsequent analysis , we assume that th e sleeping time is equal to T p such that t he second component wi ll hav e a v alue of zero and thus (14) reduces to A − D i = ≬ { x H i − 2 , x H i − 1 } . Similarly , we can define e K i = | R i | as e K i = K i + K − i , where K i and K − i are the relays lying in A R i and A − R i respectiv el y . K − i represents the nodes lying i n A − R i who were asleep at the time when R i − 2 began their transm ission b u t wok e up before the transmissio n ended. In order to ev alu ate the energy and delay performance, we need to ev alu ate the expectations E [ e L i ] and E [ e K i ] . A suit able st arting poin t i s t o s tudy the statist ical dependencies of the areas A R i , A D i , A − D i , and A − R i . Based on (10) and in lig ht of (12), it is clear t he statisti cs of A D i are completely encompassed by e K i − 1 . Similarly , from (10), (11), and (13) it can be shown that the statistics of A R i are dictated by j i − 1 , { e K n } i − 2 n =1 , and { e K n } i − 1 n =1 . On the o ther hand, using (10) and (14), and recalling the assumption that the sleep time is equal to T p it is e vident that the statis tics A − D i can be equiv alentl y represented by thos e of e K i − 2 . Finally , since A − R i is confined by x C i ( y ) and x H i − 1 ( y ) then using (10), (11), and (15) the statistics of A − R i are actually encompassed by j i − 1 and { e K n } i − 2 n =1 . Given S i − v = P i − v n =1 e K n and based on the stati stical dependencies exposed 17 above, we sub sequently obtain p L i ( L i ) = X e K i − 1 p L i ( L i |A D i ) p e K i − 1 ( e K i − 1 ) , (16) p K i ( K i ) = X j i − 1 X S i − 1 X S i − 2 p K i ( K i |A R i ) p ( j i − 1 , S i − 1 , S i − 2 ) , (17) p L − i ( L − i ) = X e K i − 2 p L − i ( L − i |A − D i ) p e K i − 2 ( e K i − 2 ) , (18) p K − i ( K − i ) = X j i − 1 X S i − 2 p K − i ( K − i |A − R i ) p ( j i − 1 , S i − 2 ) . (19) T o take one step ahead, the probability that a node i n A − D i or sim ilarly in A − R i was sleeping when R i − 2 started transmi tting is p w k = 1 − ǫ . Recalling that n odes are dispersed in the field according to a 2-D poisson dis tribution, we obtain p L i ( L i |A D i ) = 1 L i ! ( ǫρ A D i ) L i e − ǫρ A D i , (20) p K i ( K i |A R i ) = 1 K i ! ( ǫρ A R i ) K i e − ǫρ A R i , (21) p L − i ( L − i |A − D i ) = 1 L − i ! ( ǫρ A − D i p w k ) L − i e − ǫρ A − D i p wk , (22) p K − i ( K − i |A − R i ) = 1 K − i ! ( ǫρ A − R i p w k ) K − i e − ǫρ A − R i p wk . (23) W e note t hat p S i − 2 ( S i − 2 ) = ∗ i − 2 n =2 p S n − 1 ( S n − 1 ) , p e K n ( e K n ) , where ∗ is the conv oluti on operator . The joi nt PDF p ( j i − 1 , S i − 2 ) is gi ven by P ∞ S i − 1 =0 p ( j i − 1 , S i − 1 , S i − 2 ) , where p ( j i − 1 , S i − 1 , S i − 2 ) equals the product of p j i − 1 ( j i − 1 | S i − 1 , S i − 2 ) , p S i − 1 ( S i − 1 | S i − 2 ) , and p S i − 2 ( S i − 2 ) . Furthermore, p S i − 1 ( S i − 1 | S i − 2 ) is not hing but p e K i − 1 ( S i − 1 − S i − 2 ) . Also, p j i − 1 ( j i − 1 | S i − 1 , S i − 2 ) is equivalent to p j i − 1 ( j i − 1 | S i − 1 − S i − 2 ) and can be computed by ev aluatin g (9) at i − 1 in stead of i and su bstitutin g e K i − 1 with S i − 1 − S i − 2 . W ith p K − i ( K − i |A − R i ) and p ( j i − 1 , S i − 2 ) readily a vailable, we are no w able to compute p K − i ( K − i ) from (15), (19), and (23) . On the flip side of the coin, p K i ( K i ) can be computed from (13), (17), and (21) knowing th at the joint PDF p ( j i − 1 , S i − 1 , S i − 2 ) has already been computed abov e. Since e K i = K i + K − i , then p e K i ( e K i ) = p K i ( K i ) ∗ p K − i ( K − i ) . From the statistical analysis presented thus far , it becomes clear that th e stati stics at any arbitrary h op can be con veniently obtained by recursion. In other words, a t hop i , p e K i − 1 ( e K i − 1 ) and p e K i − 2 ( e K i − 2 ) will be readily av ailable. Accordingly , p L i ( L i ) is obtained from (12), (16), and (20) while p L − i ( L − i ) is obtained from (14), (18), and (22). 18 Finally , we are in a position now to derive an expression for the expected number of re- transmissio ns E [ n r i ] occurring at h op i . Given the areas A R i and A − R i , then E [ n r i |A R i , A − R i ] = 1 / ( e ǫρ ( A R i + p wk A − R i ) − 1) . If the num ber of RA CH s lots B is sufficiently lar ge, t hen the contri bution of A − R i diminish es and m ay be overlooked in this expression for conv eni ence and tractabilit y of the analysi s. Hence, we get: E [ n r i ] = X j i − 1 X S i − 1 X S i − 2 E [ n r i |A R i ] p ( j i − 1 , S i − 1 , S i − 2 ) . (24) V I . P E R F O R M A N C E E V A L UA T I O N T o appreciate the end-to-end p erformance of OMR agains t other beaconless protocol s, we are going to e va luate it in light of t he i nherent tradeoff between energy and delay . Denoting the mean end-to-end energy consu med in forwarding one packe t by E e 2 e and the mean end-to-end delay by l e 2 e , we define t he end-to-end energy-delay product as EDP = E e 2 e l e 2 e . In order to account for t he fact that OMR and beaconless protocols may employ differe nt modulation and coding s chemes (MCS), EDP must b e no rmalized by the PHY data rate, r . Hence, we can define an end-to-end cost metric C e 2 e = EDP r T p which reflects the amount of energy consumed and delay time spent i n transporti ng r T p bits from source to destinat ion. A. OMR P erform ance Metrics At any give n h op i , there w ould be e K i − 1 nodes who are relaying the packet and e L i nodes recei ving the transm ission. At the next hop , i + 1 , the e K i − 1 relays w ould be l istening to m ake sure the packet is being forwarded ahead. Consequentl y , l e 2 e = T p q X i =1 (1 + E [ n r i ]) , (25) where q : x H q (0) ≥ L is the number of hops trav ersed by the pack et to the destinatio n. Furthermore, the energy expended at hop i to relay the pack et ahead is given by: E i = E [ e L i ] P Rx T p + ( E [ n r i ] + 1) E [ e K i − 1 ] P t T p + ( E [ n r i ] + 1) E [ e K i − 1 ] P Rx t I D + ( E [ e K i − 1 ] t I D + E [ e L i ] T p ) P t N s , (26) where P Rx is t he the power consumed in receiving a packet and P t N s is t he busy t one power . The end-to-end energy consumed is E e 2 e = P q i =1 E i . 19 B. A Spo tlight on the P erforman ce of Beaconless Pr otocols The family of beaconless posi tion-based forwarding protocols includes qui te a fe w variants. Ne vertheless, t he work of [8], [9] constituted a major stepping sto ne tow ards th e de velopm ent of other b eaconless protocols. In addit ion, the analy tical framework provided in [8], [9] is quite comprehensive and detailed. As such, it is goi ng to be ado pted in this paper as the benchmark for com parison. Other beaconless protocols may be considered to a great extent as adaptations and/or enhancements of [8], [9]. Thus, ev alu ation resul ts of this section can be con veniently generalized to other beaconless protocols. For the sake of brevity , we will be often using the term “BCL ” to refer to t he class of existing beaconless posi tion-based p rotocols. T able I explains the different stages of the BCL forwarding process. At a giv en hop, there would be η empty cycles followed by one non-empty cycle. Em pty cycles occur when there are no awak en nodes off ering posit iv e progress within the transmission range of th e sender . Th e transm ission range of the sender is denoted by d m . On a verage, the fraction of nodes within the transmis sion range off ering positive progress tow ards the destination is ξ . Each cycle consis ts of N p slots such that the durati on of one s lots is T s . For the non-empty cycle, there would be m e empty slot s followed by m n collision-resolu tion s lots. Summing up all terms of energy consum ption, th e mean energy consumed in t ransmitting one packet at a certain hop i s given by P t T s (( E [ m e ] + 5 + E [ η ] N p ) N s + (1 + 2 E [ m e ] ξ ) ǫρπ d 2 m + 1 + E [ m e ] + E [ η ] N p + ξ N s ǫρπ d 2 m / N p + (2 + 3 N s )( E [ m n ] − 1) ) / N s . (27) On the ot her hand, the mean energy consumed in receiving: P Rx T s ((1 + 2 ξ E [ m e ]) ǫρπ d 2 max + 2 + E [ m e ] + E [ η ] N p + 3( E [ m n ] − 1) ) . (28) The expectations E [ η ] , E [ m e ] , and E [ m n ] are found in explicit forms in [8] ((3) and (4)). The end-to-end delay is function of the t ime spent p er hop and the number of ho ps trav ersed before reaching the destination. In light of table I, and [8] ((4), (5), and (16)), it can be shown that the time spent on ave rage by a packet in the case of a verage beaconless prot ocols is given by 2 ( E [ η ] N p + E [ m e + m n ]) T s . Furthermore, the expected progress towards the d estination after i hops is given by [9], ((8) and (19 )). 20 C. OMR vs. BCL OMR performance was ev aluat ed from an analyt ical point of vi e w in li ght of the framework provided in Section V. It was then comp ared to [8], [9]. Furthermore, simulation s have been carried out to validate the outcomes of the analytical computations. The strip width w was set to 200 m in the simulation s wit h a source-destination separation of 2 km. T he sleeping duty cycle was set to ǫ = 25% whil e the detection t hreshold γ t was assumed to be 5 d B at τ = 20% . The path loss exponent was cons idered to be α = 3 . The main theme to be con ve yed in this section, is th at OMR starts to striki ngly outperform existing beaconless position-based protocols in terms of end-to-end delay as node density g ro ws. Howe ver , this comes at the price of a dditional ener gy consumption since a larger number of nodes tend to relay the packet. This reasserts the significance of e valuating end-to-end performance based on the interaction between energy and delay . W e are going to show in this section that there is m ore than one s cenario whereby OMR o utperforms BCL protocols from the joint perspectiv e of delay and ener gy . For instance, it wil l be dem onstrated that by tun ing down th e transmit power of OMR, delay performance is not substantiall y impacted whi le energy consumpti on is noticeably reduced. Thus, OMR is able to p rovide an obvious p erformance gain in this case. Moreover , OM R wil l be also shown to hav e an edge for certain classes of modul ation techniques. Finally and before delving into the detailed comparison, it ought to be mentioned t hat the outcome of analytical com putations have been closely matched by simu lation results, as per figure 11. 1) Effect of T ransmi t P ower: It is cl early d emonstrated from figure 11 that for an equiv al ent amount of energy consu mption, OMR offers reduced end-to -end delay . This conclusi on is mainly valid when OMR utilizes a lowe r transmit po wer . W e hav e re verted to us ing a lo wer transmit power for OMR based on the rationale that it reduces ener gy con sumption si gnificantly whi le not really jeopardizing the hop dis tances tra versed by packets. This ar gument stems from the simple fact that t he relationsh ip betw een the transmit power and the achie vable h op distance is in versely s caled by the path loss exponent α . As such, a substanti al drop in transmit power will be countered by only moderate t o marginal shrink in hop distance, dependin g on the value of α . Indeed, this has been verified by plotting t he ratio C e 2 e (OMR) /C e 2 e (BCL) against OMR’ s transmit power for various n ode densities. Result s are depicted in figure 12(a) which i llustrates that OMR offe rs roughly a 40 % enh ancement when the transmit power is in t he range of 6 21 to 9 d B below that of BCL (which is operating h ere at 33 dBm). Nevertheless, reducin g the transmit power furt her b elow a certain threshold will actuall y start to have a counter effect. As the transmit power decreases, t he probability of retransmissio n starts to pick up quickly and rather contributes to the i nflation of OMR’ s EDP . It can be also concluded from figure 12 (a) that the performance gains offered b y OMR is almost indifferent of the underlying node density . Indeed, this is a design objective whi ch has been set forth early o n in t his paper . Since OM R does not resort to any collision resolu tion mechanism , it is also of i nterest to in vestigate the ef fect of the R TS/CTS packet duration, deno ted by T s , relative to the data packet duration, T p . As T s /T p increases, a considerable portio n of the end-to-end energy consum ption in the beaconless case is attributed to R TS/CTS transmissions d uring the collision resolut ion process. End-to-end delay as well increases. Figure 12(b) illust rates that for shorter packe t lengths, or alternativ ely larger T s /T p ratios, OMR is set to of fer substant ial performance gain s over beaconless protocols . 2) Effect of The Number of RA CH Slots , B : For the sake of a comprehensive and fair comparison, we ha ve also studied the im pact of B on the performance of OMR. On one hand, increasing B will reduce the probabili ty of RA CH coll isions. This in return will hav e the ef fect of reducing t he s ize of the area A − R i and thu s will result in reducing energy consum ption. The delay performance will not be af fected noticeably sin ce the si ze of A − R i is typicall y small compared to A R i . On t he other hand, as B g ets larger , th e overhead at the PHY layer also grows effecti vely resulting in a reduction o f th e effec tiv e data rate seen at l ayer 2. This intuition is indeed validated in figure 13(a). 3) Hig her Or der MCS: The performance gain s demonstrated thu s far are actually encouraging to consider a higher o rder MCS for OMR. W e recall here our original choice t o deploy a diffe rential m odulation s cheme in conjunction w ith OMR. Whereas coherent modulation ne- cessitates accurate estimation of the channel fading coefficients, dif ferential modulation does not; thus reducing cost and compl exity of the receiver . The tradeoff howe ver in using M-DPSK instead of coherent M-PSK is a hig her detection threshold . No w , our n ext task would be t o specify the detection t hreshold γ t for each MCS under cons ideration for OMR. The bit error rate (BER) targeted here is 10 − 2 . Under the assumpt ion of two-branch maxi mal ratio com bining (MRC) and Gray encoding, then the detection th resholds for DQPSK, 8-DPSK, and 16-DPSK 22 are approximately 12.8 dB, 15.6, and 18.5 dB respecti vely [30]. There i s no need to consider 2-DPSK as i t has the same detection threshold of DQPSK. On the other hand, for coherent QSPK, the required detection threshold at BER of 10 − 2 approximately ev aluates to 10.85 dB [30]. Furthermore, if rate 1 2 con volutional coding wit h a constraint length of 2 is em ployed then a coding gain of 3 to 4 dB can b e achie ved (at a BER of 10 − 2 ) [31]. Figure 13(b) depicts the end-to-end cost incurred by OMR in com parison to BCL for various MCSs. BCL is assumed to us e coherent QPSK. Figure 13 (b) clearly con veys t hat OMR is able to transpo rt the same amount of bits m uch fa ster whil e consuming the same amount of ener gy . Looking at it from a complementary angl e, O MR d eliv ers more bits tow ards the d estination (by uti lizing a higher order M CS) whil e consumi ng the same amou nt of ener g y and sp ending t he same amount of delay . Finally , sim ulations ha ve been also carried out to in vestigate the behavior of OMR in case of forwarding t wo concurrent but dissimi lar p ackets. A samp le forwarding process i s depicted in figure 14 noting that both packets have the same desti nation. Int erference b etween the two forwarding processes has been accounted for in the simulati on. It can be observed th at one retransmission has occurred at the 4t h ho p of Packet A. This was d ue to the significant interfer- ence induced by the forwarding process of Packet B. As Packe t B progressed further towards the desti nation, the forwarding process of P acket A gained so me room to resume. V I I . C O N C L U S I O N S In this p aper we ha ve proposed a nov el multi-relay b eaconless position-based packet for- warding proto col for WSNs. The protocol couples t he u se of an OFDM-based PHY with position-based routing t o create an improved end-to-end performance over traditional beaconless protocols. A st atistical frame work has been provided to s tudy the hoppi ng dynamics and behavior of the proposed protocol. Numerical and simul ation results hav e shown that the proposed protocol may be tu ned to offer an im provement of up t o 40 % in terms of t he end-to-end performance. In our future work, we will study the applicabili ty and performance of OMR in case of using the ho p count away from t he desti nation instead of geographical positi ons. W e will also analyze the co-channel interference created by one forwarding p rocess on another , ev aluate how it limi ts the overall network capacity , and research means to control it. 23 R E F E R E N C E S [1] J. Y icka, B. Mukherjeea, and D. Ghosal, “W i reless sensor network survey , ” Elsevier Journ al on Comp. Net. , vol. 58, Issue 12, pp. 2292–2330, April 2008. [2] I. Akyildiz, D. Pompili, and T . Melodia, “Underw ater acoustic sensor network s: research challenges, ” Elsevier J ournal on Ad Hoc Networks , vol. 3, no. 3, pp. 257–279, May 2005. [3] V . Gungor , B. Lu, and G. H anck e, “Opportunities and Challenges of Wireless Sensor Networks in Smart Grid, ” IEEE T ransactions on Industrial Electro nics , vol. 57, no. 10, pp. 3557–35 64, O ctober 2010. [4] M. Hatler , D. P haneuf, and D. Gurganio us, “Wireless Sensor Networks for Smart Cities: A Market Study , ” ON W orld Resear ch Report , 2007. [5] I. Akyildiz, T . Melodia, and K. C ho wdhury , “ A surve y on wireless multimedia sensor networks, ” Elsevier Journal on Computer N etworks , vol. 51, no. 4, pp. 921–960, March 2007. [6] I. Akyildiz and M.C. V uran, W ireless Sensor Networks , John W i ley and Sons, L td, 1st edition, 2010. [7] J. Sanchez, P . Ruiz, and R. Marin-Perez, “Beacon-less geographic routing made practical: Challenges, design guidelines, and protocols, ” IE EE Commmunications Magazine , vol. 47, Issue 8, pp. 85–91, August 2009. [8] M. Zorzi and R. Rao, “Geographic random forwarding (GeRaF) for ad hoc and sensor networks: Energy and latency performance, ” IEEE Tr ansactions on Mobile Computing , vol. 2, no. 4, pp. 349–365, October 2003. [9] M. Zorzi and R. Rao, “Geographic random forwarding (GeRaF ) for ad hoc and sensor networks: Multihop performance, ” IEEE Tr ansactions on Mobile Computing , vol. 2, no. 4, pp. 337–348, October 2003. [10] M. Heissenb ¨ uttel, T . B raun, T . Bernoulli, and M. W ¨ alchli, “BLR: beacon-less routing algorithm for mobile ad hoc networks, ” E lsevier Jou rnal on Computer Communications , vol. 27, Issue 11, 2004. [11] H. F ¨ ussler , J. Widmer , M. K ¨ asemann, M. Mauv e, and H. Hartenstein, “Conten tion-based forwarding for mobile ad-hoc networks, ” E lseviers Ad Hoc Networks , vol. 1, Issue 4, pp. 351–369, Nov ember 2003. [12] T . He, B. Blum, Q. Cao, J. St anko vic, S. Son, and T . Abdelzaher , “Robust and timely communication ov er highly dynamic sensor networks, ” R eal-T ime Systems , vol. 37, No. 3, August 2007. [13] D. Ferrara, L. Galluccio, A. Leonardi, G. Morabito, and S. Palazzo, “MA CR O: an integrated mac/routing protocol for geographic forwarding in wireless sensor network s, ” In Pr oceedings of The 24th Annual J oint Confer ence of the IE EE Computer and Communications Societies (INFOCOM’05), Miami, USA , vol. 3, pp. 1770–1781, March 2005. [14] M. Rossi, N. Bui, and M. Z orzi, “Cost- and collisi on-minimizing forwarding schemes for wi reless sensor networks: Design, analysis and experimental v alidation, ” IEEE Tr ans. on Mobile Computing , vol. 8, No. 3, Mar 2009. [15] A. Odorizzi and G. Mazzini, “M-GeRaF analysis: P erformance improvem ent of a multisi nk ad hoc and sensor network geographica l random routing protocol, ” In proce edings of 16th International Confer ence on Software , T elecommunications and Computer Networks (SoftCom 2008), Dubr ovnik, Cr oatia , pp. 193–197, September 2008. [16] M. Heissenb ¨ u ttel, T . Braun, M. W ¨ alchli, and T . Bernoulli, “Ev al uating the limitations of and alternativ es in beaconing, ” Elsevier Journ al on Ad Hoc Networks , vol. 5, Issue 5, pp. 558–578 , July 2007. [17] H. Schulze and C. Lueders, Theory and Applications of OF DM and CDMA , John W i ley and S ons Ltd, 1st edition, 2005. [18] P . Baronti, P . Pillaia, V . Chook, S. Chessa, A. Gotta, and Y . F un Hu, “Wireless sen sor networks: A surve y on the state of the art and the 802.15.4 and ZigBee standards, ” Elsevier Jou rnal Computer Communications , vol. 30, no. 7, pp. 1655–1695 , May 2007. [19] E. Monnerie, J. Buffington , S . Shimada, and K. W aheed, “IEEE 802.15.4g OF DM PHY Overview , ” doc. IEEE 802.11- 10/1305r1 , January 2011. 24 CR C pac ket payload src dst b 1 b 2 b 3 b 4 b B RA CH area pac ket ID sync pilots & pream ble w frequency domain time domain Fig. 1. OMR packet structure. [20] D. W u, G. Zhu, D. Zhao, and L. Liu, “E nergy Balancing in an OFDM-Based WSN, ” I EEE 73r d V ehicular Technolo gy Confer ence (V TC Spring) , 2011. [21] M. Eriksson and A. Mahmud, “Dynamic single frequency network s in wireless multihop networks - energy aw are routing algorithms with performance analysis, ” In pr oceedings of The 10th I EEE International Confer ence on Computer and Information T echn ology , Bradfor d, UK , pp. 400–40 6, May 2010. [22] M. Eriksson and A. Mahmud, “T ransmitter macrodiv ersit y in multihopping - SFN based algorithm for improv ed node reachability and robust routing, ” W orld Academy of Science, Engineering and T echno logy , vol. 64, 2010. [23] Z. J. Haas and J. Deng, “Dual busy tone multiple access ( dbtma) - a multiple access control scheme for ad hoc networks , ” IEEE Tr ansactions on Communications , vol. 50, no. 6, pp. 975–985, 2002. [24] I. Akyildiz, W . Su, Y . Sankarasubraman iam, and E. Cayirci, “W ireless sensor networks: A surv ey , ” Elsevier Jo urnal on Computer N etworks , vol. 38, Issue 4, pp. 393–422, January 2002. [25] A. Scaglione, D. Goeckel, and J. Laneman, “Cooperati ve Communications in Mobile Ad Hoc Networks, ” IEEE Signal Pr ocessing Magazine , vol. 23, Issue 5, pp. 18–29, September 2006. [26] T . Rappaport, W ireless Communications: Priciples and P ractice , Prentice Hall, 2nd edition, 2001. [27] B. Zhao and M.C. V alenti, “P ractical relay networks: a generalization of hybrid-arq, ” IEEE Journ al on Selected Area s in Communications , vol. 23, Issue 1, January 2005. [28] M. Haenggi, “On routing in random Rayleigh fading networks, ” IE EE T ransactions on W ireless Communications , vol. 4, no. 4, April 2005. [29] C. Athaudage, “BER sensitiv ity of OFDM systems t o time synchron ization error , ” The 8th International Confer ence on Communication Systems (ICCS’02), Singapor e , vol. 1, pp. 42–46, November 2002. [30] M. Simon and M.S. Alouini, Digital Communication over F ading Channels , John W iley and Sons, 2nd edition, 2005. [31] Y . Y asuda, K. Kashiki, and Y . Hi rata, “High-Rate Punctured Con volutional Codes for Soft Decision Viterbi Decoding, ” IEEE Tr ansactions on Communications , vol. 32, no. 3, pp. 315–319, March 1984. 25 V Q nodes which are sleeping or did not successfully detect the pack et w D i : deco ding set at hop i x C i R i − 1 : relay set of hop i − 1 R i − 1 , 1 R i − 1 , 1 : closest relay from hop i − 1 to destination V Q pack et source and destination resp ectively x C i − 1 R i − 1 ,j i − 1 R i − 1 ,j i − 1 : 1st relay from the set R i − 1 x C i , x C i − 1 : decision contours for hops i and i − 1 resectively R i : relay set of hop i S whose position information is resolv able R i, 7 ( x = 0 , y = 0) ( x = L, y = 0) Fig. 2. Example of a sample hopping process. 26 1 2 3 4 5 6 7 8 9 10 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 hop number, i expected number of retransmissions, E[n r i ] ρ =1200 km −2 , P t =33 dBm ρ =1200 km −2 , P t =27 dBm ρ =800 km −2 , P t =33 dBm ρ =800 km −2 , P t =27 dBm (a) Expected number of retransmissions. 600 650 700 750 800 850 900 10 −4 10 −3 10 −2 10 −1 10 0 node density, ρ average ratio of false alarm relays γ l =0 dB γ l =1 dB γ l =2 dB γ l =3 dB γ l =4 dB (b) Rate at which false alarm ev ents occur for variou s values of the Pack et ID decoding t hreshold. As more coding redundanc y is associated wi th the Packet ID fi eld, a lower t hreshold will be required. Fig. 3. Eva luation of the proposed retransmission policy . 27 sleep c hannel receiv e rela y/ listen sleeping timer expires w ak e-up timer expires sync pilots acquisition detected rela ying satisfied criteria pac k et ID pac k et rela y ed new pack et retransmit idle channel sensing bac k-off not detected successfully ahead to send c hannel idle to send c hannel busy: Fig. 4. Simplified protocol state diagram. Σ Σ Σ T S h 1 , 1 h 1 , 2 h 1 ,n h h f K i − 1 , 1 h f K i − 1 ,n h h f K i − 1 , 2 N + I T ′ 1 T ′ f K i − 1 T T T T T Fig. 5. W ireless channel model. 28 source transmits nodes of D 1 start to receive relays of R 1 synchronously transmit (assuming R 1 = D 1 ) D 2 ,k ⊂ D 2 starts to receive source transmits nodes of D 1 start to receive relays of R 1 start to transmit (assuming R 1 = D 1 ) asynchronously a) universal time reference, synchronous transmissions. b) lo cal time references, asynchronous transmissions. D 2 ,k ⊂ D 2 starts to receive Fig. 6. When uni versal t ime reference is av ailable in t he network by means of GP S for example, synchronous relaying is possible at each hop. A more general case howe ver is to hav e asynchronous transmissions. 29 100 120 140 160 180 200 3.2 3.25 3.3 3.35 3.4 3.45 3.5 x 10 −7 strip width, meters standard deviation 2.04 2.06 2.08 2.1 x 10 −6 mean 2.04 2.05 2.06 2.07 2.08 2.09 2.1 x 10 −6 2.04 2.05 2.06 2.07 2.08 2.09 2.1 x 10 −6 standard deviation mean (a) Standard de viati on and mean of t he forwarding delay spread as function of the strip width for various node densities ( ρ = 900 , 1200 , and 1500 km − 2 ). The length of the strip is 600m. 0.5 1 1.5 2 2.5 3 3.5 0 0.01 0.02 0.03 0.04 0.05 0.06 delay spread, µ s histogram (b) Delay spread histogram ( ρ = 1500 km − 2 , w = 200 m, 5000 0 iterations). Fig. 7. Statistics of the forwarding delay spread obtained through simulations. 30 first energy arriv al, 1st OFDM RACH OFDM time reference FFT window applied symbol symbol RACH slot 1 RACH slot 2 RACH slot B established Fig. 8. For some RACH slots the FFT windo w will not be aligned to the actual start of the RACH signal. 2 4 6 8 10 12 14 16 18 20 200 300 400 500 600 700 800 900 1000 1100 1200 1300 number of relays at hop (i−1) progress at hop i, ∆ x H i (y) x H 1 (y)=100m, w=100, 200, ..., 500m x H 1 (y)=300m, w=100, 200, ..., 500m x H 1 (y)=500m, w=100, 200, ..., 500m x H 1 (y)=700m, w=100, 200, ..., 500m Fig. 9. Simulation results demonstrating that the progress made ev ery hop is linear in e K i − 1 . T he i mpact of the progress made in the 1 st hop, x H 1 ( y ) , carries on to the subsequent hops. In other words, the larger x H 1 ( y ) is the greater progress is achie ved in subsequent hops. 31 ∆ x H i ( y ) x H i ( y ) x H i − 1 ( y ) x C i ( y ) w V Q (0 , 0) (0 , L ) x H i − 2 ( y ) x H i − 3 ( y ) Fig. 10. Setup to study hopping behavior of OMR. 900 1000 1100 1200 1300 1400 1500 0.5 0.55 0.6 0.65 OMR to Beaconless e2e latency ratio node density, ρ (km −2 ) 0.8 0.85 0.9 0.95 1 OMR to Beaconless e2e energy consumption ratio e2e delay ratio, analytical e2e energy ratio, analytical e2e delay ratio, simulation e2e energy ratio, simulation Fig. 11. End-to-end energy and delay performance of OMR compared to beaconless protocols. OMR is util izing here a transmit po wer that is 9 dB less than beaconless. 32 20 22 24 26 28 30 32 34 0.5 0.6 0.7 0.8 0.9 1 1.1 1.2 1.3 1.4 1.5 OMR transmit power (dBm) C e2e (OMR)/C e2e (BCL) ρ =900 km −2 ρ =1200 km −2 ρ =1500 km −2 (a) End-to-end cost comparison as function of OMR transmit po wer at various node densities. 900 1000 1100 1200 1300 1400 1500 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 node density, ρ (km −2 ) EDP OMR / EDP BCL T s /T p = 0.1 T s /T p = 0.2 T s /T p = 0.3 T s /T p = 0.4 (b) End-to-end energy-delay product of OMR divided by that of the beaconless protocol. The duration of the control pack et (R TS, CTS , ...) utilized by the beaconless protocol has been v aried to study i ts impact on the performance. Here, OMR is operating at a transmit po wer which is 9 dB less than that of the beaconless. Fig. 12. Comparing performance of OMR from and end-to-end perspecti ve to beaconless protocols. 33 900 1000 1100 1200 1300 1400 1500 0.75 0.8 0.85 0.9 0.95 1 node density, ρ (km −2 ) e2e cost OMR / e2e cost Beaconless B=8 B=16 B=24 B=32 (a) End-to-end cost of OMR at v arious v alues of B (number of RA C H slots) di vided by that of the beaconless protocol. 900 1000 1100 1200 1300 1400 1500 0.65 0.7 0.75 0.8 0.85 0.9 0.95 1 node density, ρ (km −2 ) e2e cost OMR / e2e cost Beaconless e2e cost comparison Beaconless: Coherent QPSK 1/2 OMR: various MCS @ Tx power 6 dB less than Beaconless Coherent QPSK 1/2 DQPSK 1/2 8−DPSK 1/2 16−DPSK 1/2 (b) End-to-end cost of OMR at v arious modulation schemes divided by that of the beaconless protocol. Fig. 13. Comparing performance of OMR from and end-to-end perspecti ve to beaconless protocols, continued. 34 200 400 600 800 1000 400 600 800 1000 A1 A1 A1 A1 B1 B1 B1 B1 A2 A2 A2 A2 A2 A2 A2 B2 B2 B2 B2 B2 B2 B2 B2 B2 B2 A3 A3 A3 B3 B3 B3 B3 B3 A4 B4 B4 B4 B4 A5 A6 A6 A6 A6 A6 A6 A6 B4 B4 B4 B4 (a) Snapshots of two concurrent packet relaying processes pack et sink source of pack et A source of pack et B node relays pack et A in its i th hop node relays pack et B in its i th hop node not part of relaying process relaying strip borders (pack et A) relaying strip borders (pack et B) node correctly detects Pack et B node correctly detects Pack et A A i B i (b) Legend Fig. 14. Demonstrating the flow of two concurrent pack ets in the network under OMR. 35 T ABLE I T Y P I C A L E N E R G Y C O N S U M P T I O N C O M P O N E N T S F O R A B E A C O N L E S S P RO T O C O L . η empty cycles Node(s) Count Activity Duration sender 1 transmit RTS T s listening and activ ating BT while listening η N p T s transmits CON TINUE message after each slot not containing CT S η N p T s non-empty cycle Node(s) A verage Count Activity Duration sender 1 transmit RTS T s sender 1 listening and activ ating BT while listening m e T s transmits CON TINUE message after each slot not containing CT S m e T s potential relays ( N p − m e ) N p ξ ǫρπ d 2 m listen t o the channel in anticipation of a CTS message m e T s listen t o CONTI NUE messages from sender m e T s activ ate BT w hile listening 2 m e T s timers expired ξǫρπ d 2 m N p transmit CT S message in ( m e + 1) th slot T s colliding at l east 2 transmit CT S, li sten for CTS-Reply from sender , activ ate B T while listening ( m n − 1) T s sender 1 transmit CO NTINUE message ( m n − 1) T s recei ve colliding CTS messages ( m n − 1) T s successful relay 1 transmit CTS message during ( m e + m n ) th slot T s sender 1 listen t o CTS from successful relay during ( m e + m n ) th slot T s activ ate BT w hile listening T s transmit OK message T s successful relay 1 listen to OK message and activ ate BT while listening T s
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment