A Graphical Adversarial Risk Analysis Model for Oil and Gas Drilling Cybersecurity
Oil and gas drilling is based, increasingly, on operational technology, whose cybersecurity is complicated by several challenges. We propose a graphical model for cybersecurity risk assessment based on Adversarial Risk Analysis to face those challenges. We also provide an example of the model in the context of an offshore drilling rig. The proposed model provides a more formal and comprehensive analysis of risks, still using the standard business language based on decisions, risks, and value.
💡 Research Summary
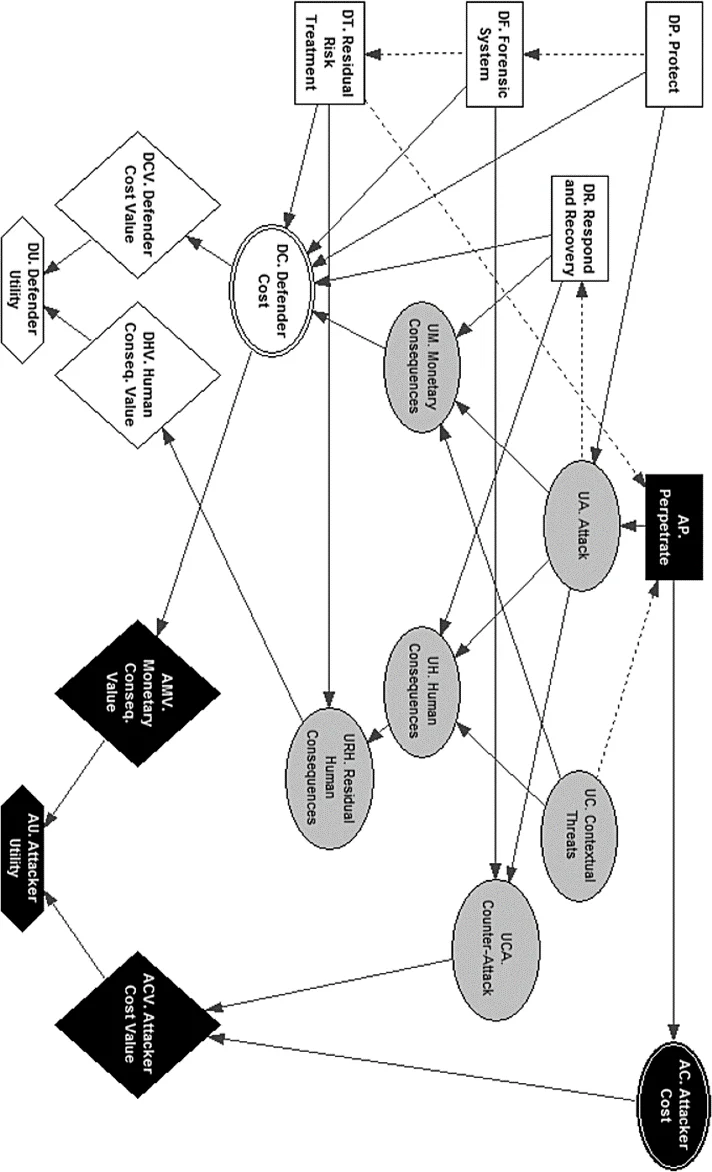
The paper addresses the growing reliance of offshore oil‑and‑gas drilling on operational technology (OT) and the associated cyber‑security challenges that arise when physical processes are controlled by networked digital systems. After reviewing the limitations of existing approaches—such as vulnerability‑based IT models, attack graphs, attack trees, game‑theoretic formulations, and Bayesian risk models—the authors propose a novel, graph‑based framework grounded in Adversarial Risk Analysis (ARA). ARA treats the defender (the drilling operator) as a decision‑maker who must anticipate the actions of an adversarial attacker, modeled as an expected‑utility maximizer. By representing the problem as a Multi‑Agent Influence Diagram (MAID), the authors capture the full decision‑risk‑utility chain for both parties in a visual, modular structure.
The defender’s side includes four primary decision nodes: Protect (selection of technical safeguards such as firewalls, encryption, and training), Forensic System (deployment of capabilities that enable attribution and possible retaliation), Residual Risk Treatment (pre‑emptive strategies like risk avoidance, sharing, or acceptance), and Respond & Recovery (post‑attack mitigation actions). Each decision incurs deterministic costs, and the defender’s overall utility aggregates monetary costs, potential loss of life, environmental damage, reputational impact, and risk attitude.
The attacker’s side is simplified to a binary Perpetrate decision (attack or not) and an associated deterministic cost. The attacker is assumed to be a business‑oriented Advanced Persistent Threat (APT) seeking monetary gain, possibly hired for sabotage. The attacker’s utility function reflects expected financial payoff minus costs, and the defender models the attacker’s beliefs about the effectiveness of protective measures and the likelihood of contextual threats (e.g., severe weather or operational windows).
Uncertainty nodes capture contextual threats, the stochastic occurrence of an attack (conditioned on both defender and attacker choices), the distribution of consequences (human, environmental, reputational, financial), residual consequences after risk‑treatment actions, and the possibility of a counter‑attack enabled by forensic capabilities. The model assumes a single, atomic attack, perfect detection, and deterministic cost structures to keep the illustration tractable while still reflecting the essential dynamics of OT cyber‑risk.
The analytical process proceeds as follows: the defender specifies prior distributions over the attacker’s cost and utility parameters, propagates these through the MAID to obtain a probability distribution over the attacker’s optimal action, and then uses this forecast to evaluate her own expected utility across the protective, forensic, risk‑treatment, and response options. The resulting optimal defense policy is one that maximizes the defender’s expected utility given the anticipated attacker behavior.
Key insights include: (1) modeling the attacker as an uncertain but rational agent provides richer strategic guidance than static threat‑catalogues; (2) the graphical MAID format makes complex interdependencies transparent to non‑technical stakeholders; (3) separating pre‑attack risk treatment from post‑attack response allows the defender to allocate resources efficiently across avoidance, sharing, acceptance, and mitigation; (4) incorporating a forensic node and counter‑attack probability introduces a deterrence mechanism that can shift the attacker’s expected payoff.
Overall, the proposed graphical ARA model offers a systematic, quantitative, and decision‑oriented tool for offshore drilling operators to assess cyber‑risk, anticipate adversarial actions, and design integrated security strategies that balance technical safeguards, legal/forensic capabilities, and business‑level risk‑treatment options. By embedding attacker behavior within the risk analysis, the approach moves beyond traditional risk matrices and static vulnerability assessments, providing a more realistic and actionable framework for protecting critical OT assets in the oil‑and‑gas sector.
Comments & Academic Discussion
Loading comments...
Leave a Comment