Actor-network procedures: Modeling multi-factor authentication, device pairing, social interactions
As computation spreads from computers to networks of computers, and migrates into cyberspace, it ceases to be globally programmable, but it remains programmable indirectly: network computations cannot be controlled, but they can be steered by local c…
Authors: Dusko Pavlovic, Catherine Meadows
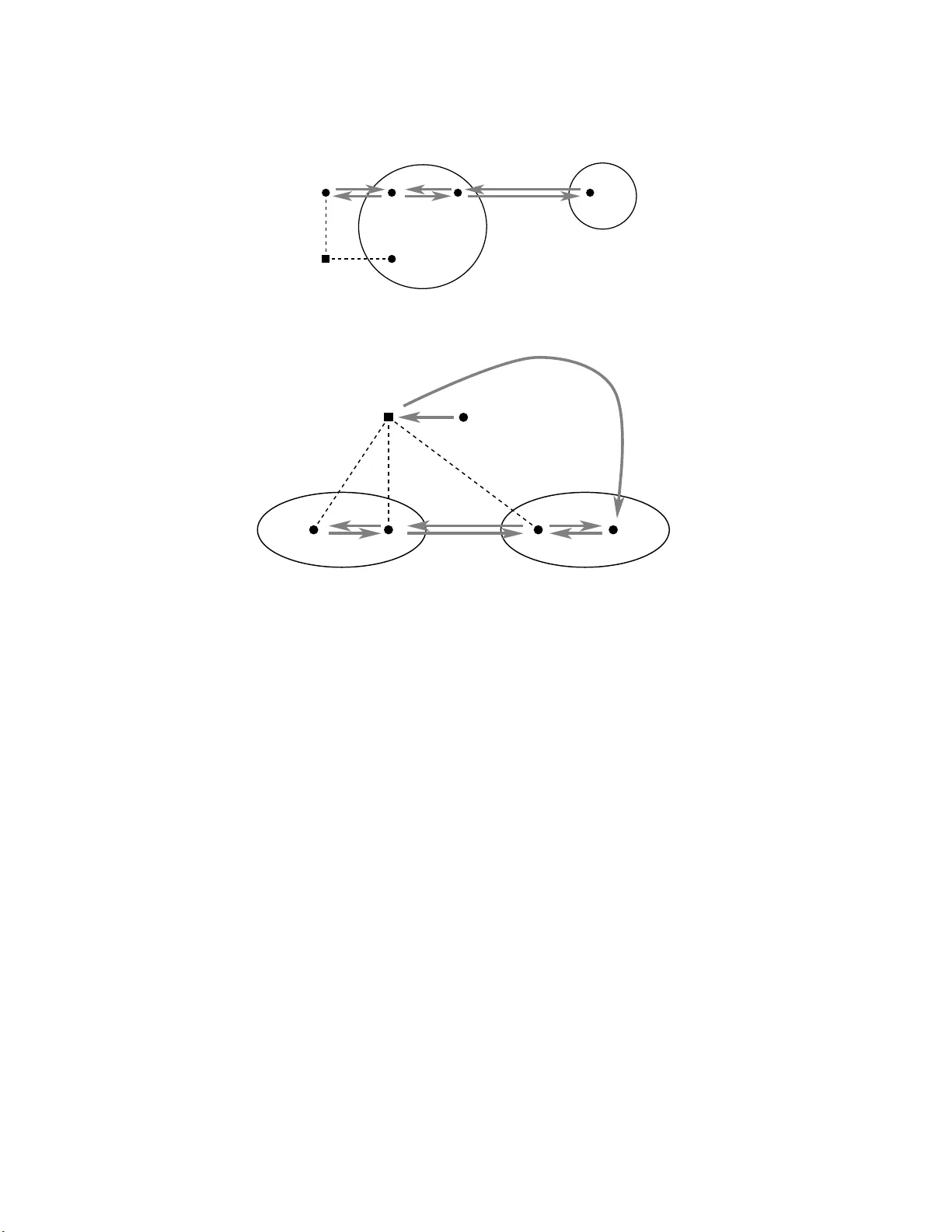
Under consideration for publication in F ormal Aspects of Computing Actor-net w ork pro cedures: Mo deling m ul ti-factor auth en ticati on, device pairing, so cial in teractions Dusk o P a vlovic 1 and Catherine Meadow s 2 1 Ro y al Hollow ay Univ ersit y of Lon don and Unive rsiteit Twe n te; Email: dusko.p avlovic@ rhul.ac. uk 2 Nav al Research Laboratory , W ashington, DC, USA; Email: meadows@itd. nrl.navy .mil Abstract. As computation spreads from computers to netw o rks of computers, and migrates int o cyb ers pace, it cea s es to b e globa lly pr ogrammable , but it remains prog rammable indir ectly and pa r tially: netw ork com- putations cannot be controlled, but they can be steered by imp osing lo ca l co nstraints on net w ork no des . The tasks of ” progra mming” global b ehaviors through loca l cons traints b e lo ng to the are a of se cu rity . The “progr am particles” that assure that a s ystem of loca l interactions leads towards some desired global goals are ca lled se cu rity pr oto c ols . They are the s oft ware connecto r s of mo der n, w orld wide soft ware systems. As c o mputation sprea ds b eyond cyb erspa ce, into physical and so cial spaces, new security ta sks a nd prob- lems ar ise. As computer netw orks are extended by no des with physical sensors and co n trollers, including the hu mans, and in terlaced with so cial net w orks, the eng ineering co nc e pts and tec hniques of co mputer se curity blend with the so c ial pro cesses of security , that evolv ed since the dawn of mankind. The s e new connectors for co mputational and so cial softw ar e requir e a new “ dis cipline of progra mming” of g lobal b ehaviors throug h lo cal constr aint s. Since the new discipline seems to b e emerg ing from a co m bination of established mo dels of security pr o to cols with older metho ds o f pro cedura l pro gramming, we use the name pr o c e dur es for these new co nnectors, that generalize proto cols . In the present pap er w e prop ose actor-networks as a fo rmal model of co mputation in heterog enous net- works of co mputers, h umans and their devices, wher e these new pro cedures run; and we in tro duce Pr o c e dur e Derivation L o gic (PDL) a s a framework for reas oning ab out security in actor-netw orks. On the w ay , we survey the g uiding ide a s of Pr oto c ol Derivation L o gic (a lso PDL) that ev olved through our work in security in last 10 years. Both formalis ms are gea r ed tow a rds graphic rea soning and, ultimately , to o l suppo rt. W e illustrate their workings by analys ing a p opular for m of tw o-factor authentication, a nd a multi-c hannel dev ice pairing pr o cedure, devised for this occa sion. 1. In tro duction 1.1. Motiv at ion and bac kground In [55] we p onder ed ab out the “ unreasona ble ineffectiveness of security engineer ing”, a nd suggested that one of the main ca uses w as that the widely used methods for p erv as ive softw are desig n were low level. The Corr esp ondenc e and offprint r e quests to : D. Pa vlovic and C. Meado ws 2 D. P a vlo vic and C. Meado ws age ancient times midd le ages mo dern times platform computer operating s ystem net w ork applicati ons Quick sort, compilers MS W ord, Oracle WWW, b otnets requirements correctness, termination livene ss, safety in tegrit y , confiden tialit y to ols programming languages specification languages scripting languages T able 1 . Paradigms of co mputatio n high level metho dolog ies to spe cify and design re usable softw a re pro ce dures were not lifted fro m traditional computer systems to mo der n net work based computation. In Section IV o f [55], we provided a sketc h of a net work computatio n mo del that might fill the ga p, and b e used a s a hig h level to ol to sp ecify and ana ly ze net work pro cedures. But the sketc h was very crude, a nd we did not even ha ve space to provide any examples of net w ork pro cedures. So the final part of that story remained rather obscure. W e attempt to rectify that in the present pap er. 1.2. Con text 1.2.1. The ages of softwar e In the b eginning, engineers built computers, and wrote progr ams to c ont rol co mputations. The platform of computation was the computer, and it was used to execute algorithms and calculations, allowing p eople to discov er, e.g., fr a ctals, and to inv en t co mpilers, that allow ed them to write and execute mor e alg orithms and more calc ula tions more efficiently . Then the op era ting system b ecame the pla tform of computatio n, and softw a re was developed on top o f it. The era o f pe r sonal computing and enterprise softw are bro k e out. And then the In ternet happ ened, follow e d by cellular netw o rks, and wireles s netw orks, and a d ho c netw orks, and mixed net w orks. Cyber s pace emerged as the distance-free space of instant, costless co mm unication, wher e any pa ir of net w ork no des is directly connected. No w adays softw are is dev elope d to r un in cyb erspac e . The W eb is, strictly sp ea k ing, just a soft w are s ystem, alb eit a formidable one. A b otnet is also a so ft w are sy stem. As so cial spa ce blends with cyber s pa ce, many s o c ial (business, colla bo rative) pro cesses can be usefully construed as so ft w are systems, that r an on so cial netw orks as hardware. Ma n y so cial and co mputational pro cesses b ecome inex tricable. T a ble 1 gives a crude pictur e o f the par adigm shifts that led to this r emark a ble situation. But as every p erson g ot c onnected to a computer, and e very computer to a netw ork, and every netw ork to a netw ork o f netw orks, co mputatio n b ecame interlaced with co mm unication, and ce a sed to b e pro grammable. The functioning o f the W eb and of web applications is not determined b y the co de in the sa me se nse as in a traditional soft w are system: after all, web applicatio ns do include the human user s as a par t of their run time. The fusion o f s o c ial a nd computationa l pro cess es in cyb er-so cia l space leads to a new t ype o f informa tio n pro cessing, wher e the purp o seful prog ram ex ecutions at the netw ork no des are supplemented by sp ontaneous data-driven evolution of net work links. While the net work emerg es as the new computer, da ta and metadata bec ome insepara ble, and new t yp e s of security pro ble ms arise. 1.2.2. The ages of softwar e se c urity In early computer systems, s ecurity tas ks mainly co ncerned sharing of the computing reso urces. In computer net works, security goals expanded to include information protection. Both computer security and informatio n security e ssentially dep end on a clear distinction betw een the secure areas, and the insecure a reas, separa ted by a security p erimeter. Security engineer ing ca ters fo r co mputer security and for information security by providing the to ols to build the secur ity p erimeter. In cyb er space, the secur e areas are separa ted from the insecure areas b y the “walls” of cryptogra ph y; and they are connected b y the “ gates” of cryptographic proto cols. But a s net w orks of computers and devices spread throug h physical and so cial spaces, the distinctions betw een the secur e and the insecur e areas b ecome blurr ed. With netw ork computation, the s o ft w are-har dw are distinction a cquires a new meaning. In contrast with the purp osefully built and progra mmed electronic computers, the new sp ontaneously evolving c o mputer-as-a - net w ork includes so c ia l netw o rks a s a part of its Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 3 age midd le ages mo dern times p ostmo dern times space computer cen ter cy ber s pace cyber-s o cial space assets computing resources information public and priv ate resources requirements a v ailability , authorization int egrit y , confident iality trust, priv acy to ols lo cks, tok ens, passwords cryptograph y , pr otocols mining and classi fication T able 2 . Paradigms of secur it y hardware, while so cial pr o cesses are b ecoming a part of its so ftw are. T o follow these de velopments, co mputer science is endorsing themes and to ols of so cial sciences [66, 26], while so cial sciences are increasing ly concerned with computatio n [67, 7 ]. The fo r malism of actor-networks arises on this background. 1.3. Goals and ideas Our go al is to contribute tow ards a formal fra mew ork for fo r r eliable and pr actic al reasoning a bo ut compu- tation and commu nication in net w orks. Since net w ork computation involv es adversaria l b ehaviors, security stands out a s the cen tral concer n in netw o rk computation. But reliable rea soning ab out secur ity , even in the familiar end-to-end netw orks, us ually requires complicated mo dels. Hence the tensio n be t w een the require- men ts of reliability a nd of practica lit y: reliable rea soning requires a precise forma l mo de l, but formal mo dels of security tend to be impractically complex. One a pproach is to mitigate this co mplexity through a uto - mated supp or t. W e ha ve b e en studying this s olution for man y years [45, 47, 28, 3], and it has b een br oadly suppo rted in the resea r ch co mm unit y [2, 6, 5, 13]. Another a pproach is to try to decr ease the complexity through mo del abstraction and refinement, and thro ugh sea rch for co n venien t and intuitiv e notations. In the present work, we put mor e emphasis on this seco nd a pproach, building up on o ur prev io us a ttempts [48, 11, 56] to extend to reasoning ab out securit y the incremen tal mo deling methodolo gies, well established in s oft w are engineer ing. T ow ards this goal, we draw our formal mo dels from the informa l reasoning practices, and a ttempt to make them mathematically precise, while trying to keep them as succinct and intuitiv e as po ssible. The main feature of our formalism is that it provides supp o rt for diagr ammatic al ly based security pro ofs. Although they cannot b e directly automated, these pr o ofs ar e as for ma l a nd a s pr ecise a s the pro ofs in similar diagr a mmatic fo rmalisms acr oss mathematics, which also cannot b e directly automated. After all, very few of the forma l pro ofs pr e s en ted in mathematics pa per s and textbo o ks ar e “forma l enough” to be ent ered in to a theorem prov er. The hop e is, how ev er, that in the end, the t w o t ypes o f security mo dels, those designed for so ft w are too ls, and those desig ne d fo r hum an cons umption, will conv erge into a theory that will allow automating complex arg umen ts, while resolving some complexities through insigh tful notations. An imp ortant instrument of user-friendly mathematical formalis ms is the “syntactic sugar”, where we subsume a whole gamut of notational and graphica l abbr eviations, co n ven tions and abuses. Although unsound informal rea s oning ca n b e a source of man y troubles, and the p edago gical empha sis is usua lly pla ced squar ely against it, so und informal reaso ning can b e a so urce of many insights. After all, the formal pr o ofs and constructions are seldom bo rn fully shap ed and formalized, but b egin their life as insights and ideas. A useful formalism supp or ts such tra ns formations from insights in to formal pro ofs. The soundness of such transformatio ns often dep e nds on a natural selection o f notational co n ven tions and abuses. Not entirely unin ten tionally , our formalisms turn out to b e rich in graphic a nd syntactic s ug ar, and in sound no tational abuses. W e b egin b y explaining some terminolog ical abuses, sta rting from the first three w ords of the title. 1.3.1. “A ctor-network” Net w orks hav e become an immensely p o pular mo del of computation acr oss sciences, from physics and biolog y , to so ciolog y a nd c o mputer scie nc e [22, 52, 50]. Actor- networks [3 9] a re a par ticularly influential pa radigm in so ciolog y , emphasizing a nd analyzing the wa ys in which the in teractions b et ween p eople and ob jects, as equal factors, drive so cial pr o cesses, in the sense that most people cannot fly without an airplane; but that most air planes also ca nnot fly without p eople. Our go al in the present pa per is to formalize and analyze some security pro ce sses in netw o rks of p eople, computers, and the ever ex pa nding range of dev ices and o b jects used for co mm unication and netw o rking, blurring many boundar ies. The idea that p eople, computers, and ob jects are eq ua l actors in such net works imp osed itself on us, throug h the need for a usable for mal mo del, 4 D. P a vlo vic and C. Meado ws even b efore we had heard of the so ciological actor -netw o r k theor y . After we heard o f it, we to ok the lib erty of adopting the name actor -netw or k for a cr uc ia l c o mpo nen t of o ur mathematical model, since it conv enien tly captures many relev ant ideas. While the orig ina tors of actor-ne tw ork theory never prop osed a forma l mode l, we b e lieve that the task s, metho ds and logics that we prop ose are not a lien to the spirit of their theory . In fact, we contend that c o mputation and so ciety have p erv aded ea ch other to the po in t where computer science and so cial sciences already share their sub ject. It should be noted, thoug h, that the go als o f this w ork are completely differe nt from the go a ls of so ciolog y of actor-netw orks, and that our actor -netw or k formalism devia tes from the original idea s in a substa n tial wa y , even by being a formalism. W e make no claims o r a ttempts to faithfully in terpret any o f the actor-netw ork authors; but we rema in faithful to the spir it of their endeav or, since they all discourag e ortho doxy . 1.3.2. “Pr o c e dur es” In computer prog rams, frequently used seq ue nc e s o f o p era tions ar e encaps ula ted into pr o c e dur es , also called r outines . A pro cedure can b e ca lle d from an y p oint in the prog ram, and thus supp orts r euse of co de. In computer netw orks, frequent ly used seq uenc e s o f op erations ar e sp ecified and implemented as network pr oto c ols , or a s crypto gr aphic pr oto c ols . So proto cols are, in a se nse, netw ork pro cedures. Conceptually , if not technically , proto col ana lysis can th us b e viewed as an extension of the venerable science of progr a m semantics, and of the metho ds of pro cedura l progra mming, adapted for the purp os es of netw o rk computation. Beyond computer net w orks, there ar e now hybrid netw orks, where b esides co mputers with their end- to-end links, there may b e diverse devices, with their heterog enous communication c hannels, cellular, shor t range e tc. O nline banking and o ther ser vices ar e now adays usua lly sec ur ed by tw o-factor and multi-factor authentication, co m bining pa sswords with smart ca rds, or cell phones. A v ast ar e a of multi-channel and out- of-b and proto co ls ope ns up, together with the web service chor e o gr aphies a nd or chestr ations ; and we ha ve only scratched its surface . And then ther e ar e of course also so cial netw o rks, where p eople congregate with their phones, their ca meras and their smiling fa ces, and ov erlay the wide sp ectrum o f their so cial ch annels ov er computer netw or ks a nd hybrid netw o rks. Many se quences of freq uen tly used oper ations within these mixed co mm unication structures have evolved. This is what w e call actor-network pr o c e dur es . Conceptually , actor-netw ork pro cedures ex tend progr am pro ce dur es from co mputers to netw orks; and they furthermo re extend netw ork proto cols, and multi-c hannel proto co ls , a nd web service choreographies and orchestrations, into so cial netw orks. T echnically , a ctor-netw ork pro cedures a re, of cour se, immensely mor e complicated than their conceptual relatives in computer science, because humans use many types of ph ysical resources, comm unicate thro ugh many pa rallel co mm unication channels, with many levels of enco ding interleav e d over ea ch other . If we ignore computers a nd devices, actor- net w ork pr o cedures already capture the main complexities o f so cial life, as a ctor-netw ork theorists are explaining. They ar e a so ciologis ts’ problem. In any case, they a re completely out o f reach for computer scientists’ pr oto col mo dels, symbolic, information theoretic, a nd computationa l, all desig ned for simple e nd-to-end co mmunication. So a co mputationally minded reader may wonder why bo ther to bring them up here. The reaso n is that the most frequent transactions that we engage with our computers and even among ourselves inv olve actor-netw ork pro cedures. Online banking and shopping, as well as the check o ut in the sup e rmarket, trav el search on the web, as well as the secur it y line on the a irp ort inv o lve actor-netw ork pro cedures. Time and again, it has b een recognized and reco nfirmed that most security br eaches nowada ys o ccur not through cryptanalys is , and not through buffer ov erflow, but through v ar ious forms o f “s o c ia l engineering” and channel interactions. Y et “ so cial engineer ing” has remained a margina l note in technical resear ch. An effor t to change this may b e fo olhardy , but it leads to ideas a nd structures that seem interesting to explor e — even indep endently of their utilit y . 1.4. Related work 1.4.1. The exp anding c onc ept of a pr oto c ol In so cia l and computational net works, pro c e dur es come in man y flavors, and hav e been studied from ma ny angles. Besides cryptog r aphic proto cols , used to secur e end-to-e nd netw orks, in h ybrid ne tw orks we incr eas- ingly rely on m ulti-channel proto cols [64], including device pair ing [37]. In web ser vices, s ta ndard pro cedures Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 5 come in tw o flav o rs: c horeogra phies a nd orchestrations [60]. Ther e ar e, of c ourse, also so cial proto co ls and so cial pro cedures, which were developed and studied first, although not formally mo deled. As so cia l net- works a re incre a singly s uppor ted by electro nic netw or ks, and on the W eb, s o c ial proto co ls and cryptog r aphic proto cols o ften blend together . Some resear chers hav e suggested that the no tio n of proto col s hould be ex- tended to study such combinations [9, 2 7, 3 5]. On the other side, the adven t of ubiquitous co mputing has led to extensive, car eful, but largely informal analyses of the problems o f device pa ir ing, and o f security int eractions o f using multiple channel t yp es [64, 34, 5 1]. One family of the device pa iring prop osa ls has b een systematically analyzed in the computational mo del in [65, 5 3, 40, 41]. 1.4.2. Pr oto c ol lo gics and gr aphics There is a substantial and extremely successful b o dy of resear ch on the formal sp ecification and verification of security pro toc ols. As we hav e remar ked, it is largely gea red to supp orting sound and efficient mechanisms for sp ecification and verification, while conside r ably less attention has b een paid to appr oaches that suppo rt the use r’s understanding of the str ucture of a proto co l a nd how it contributes to its secur it y . Ther e hav e b een some notable exceptions, howev e r . In this section we des crib e the work in this direction that has contributed to our o wn efforts. One o f the mos t s uccessful, and in our opinion most interesting formal metho ds for reas oning ab out security proto cols are str and sp ac es [29]. Among its many sa lient features, the conv enien t diagr ammatic proto col descr iptions were an imp or tan t reas on for its wide a cceptance and p opula rity . It is imp ortant to note tha t the strand s pace dia grams ar e not just an intuitiv e illustration, but that they are formal ob jects, corres p onding to precis e ly defined comp onents of the theor y , while o n the other ha nd clo sely re s em bling the informal “ arrows-and-messa ges” proto col de pic tio ns, fo und in almost every resear c h pap er and on almost every white boa rd where a proto col is discussed. Proto col Compo sition Logic (PCL) was, at least in its ear ly v ersions [2 5, 18, 16, 24, 17], an attempt to enrich the str a nd mo del with a v ar iable binding and sco ping mechanism, making it into a pro cess calculus with a formal ha ndle o n da ta flows, which would th us allow attaching Floyd-Hoare- s t yle annotations to proto col executio ns, along the lines of [58, 5 9]. This was necessary for incremental refinement o f pro toc ol sp ecifications, and for tr uly comp ositional, and th us sc alable proto col a nalyses, whic h w ere the ultimate go al of the pro ject. Unfortunately , with these extensions, the handy diagrammatic nota tion of the stra nd mo del got los t. Proto col Deriv ation Logic (PDL) has b een an ongoing effort [48, 1 1, 56, 3, 49, 57] tow ar ds a s calable, i.e. incremental proto col formalism, allowing comp osition and refinement like PCL, but equipp ed with an int uitiv e and succinct diagra mmatic no tation, like str a nd spaces. The b elief that these tw o requirements ca n be re c onciled is ba sed on the observ ation that the reaso ning of proto col pa rticipants is co ncerned mo s tly with the order of even ts in pr o to col executio ns. 1 It follows that the proto co l executions and their log ical annotations both actually describ e the sa me structur es, which can b e viewed as partially ordered m ultisets [62], and manipula ted within the same dia grammatic la nguage. This has be en the guiding idea o f P DL. Several ca se studies of standa rd proto cols, a nd the taxonomies of the co rresp onding proto col suites, have bee n pr esented in [48, 11, 56, 3]. An applica tion to a family of distance b ounding proto cols ha s b een presented in [49]; a nd an extension suppor ting the proba bilistic r easoning necessa ry for another such family ha s b een prop osed in [57]. In the pr esent paper , we prop ose the br oadest view of PDL so far — which sho uld he r e be re a d as Pr o c e dur e Deriv ation Logic. The underlying pr o c ess mo del is enric hed by a new net w ork mo del, to supp ort r e asoning ab out netw o rk pr o cedures. The lo gical annotations are ex tended accor dingly — s till geared tow a rds the diagrammatic reaso ning, which still seems lik e a rea sonable s trategy , s ince pr incipals’ reasoning towards security remains la rgely concer ned with or der of actions . 1.4.3. Computation al soundness? Security is an old so cia l pr o cess, but it is a re la tively new technical problem. As man y o ther new pro blems, it often lo oks unreas onably co mplicated: a couple of lines o f a proto col c a n conceal a subtle pro blem for many years. This is s ometimes ment ioned as the characterizing feature of the field o f security . A direct 1 E.g., in order to achiev e m utual authen tication, eac h participan t of a run must b e able to prov e that their and their p eers’ actions in their con versation mu st ha v e happened exactly in the order prescrib ed b y the pr otocol: i.e., that the receive d messages we re previously s en t as claim ed, and vi ce versa. 6 D. P a vlo vic and C. Meado ws analysis lea ds to convoluted reas oning, o ften with an exp onential e x plosion of the cases to b e co nsidered. As mentioned in Sec. 1.3, this natura lly leads to the idea of automa ted reas oning [3 6], which we pursued through several different frameworks [4 5, 4 6, 3, 28]. As this idea came to b e a widely accepted, it led to a co n vergence o f resea rch to a small num b er of standard for malisms, based on a sha rp division b et w een the symbolic and the computational mo dels of security . T his division or iginally s tarted from the e mpir ic observ ation, that mo tiv ated the s e minal pa p er [1], that the extant secur ity r esearch was broa dly based on tw o differe nt mo dels. Since the computational mo del is mo re pr ecise, whereas the symbolic mo del is easier to us e, the way to get the bes t of b oth worlds is to demo ns trate that the pr o ofs in the simpler mo del remain v alid in the more prec ise mo del; in o ther worlds, that the sym bo lic mo del w as c omput ational ly sound . This approach le d to ma n y imp ortant res ults and useful to ols [8, 4, 14]. But the fo cus on computational soundness led some res earchers to b egin viewing a ll formal mo dels of security as approximations o f the standard computationa l mo del, fo r getting that all mo dels ar e approximations of so me real pro cesses. In the ensuing co nfusio n, even the mo dels inv o lving the features that ostensibly g o b eyond the computational mo del (such as timed channels [57]) were required to demonstra te their computational so undness. This is, of co urse, a meaningless requirement, since a model can only b e sound or unsound with resp ect to a mo del where it can b e faithfully interpreted. Our curre n t effor t is again of this type, as the actor-netw ork mo del includes several features that preclude computational interpretations, a nd r ender the question o f its computationa l soundness meaningless. O ne such fea tur e is the fact that the actor s needn’t b e standar d computer s : in this pap er, we will see netw orks inv o lv ing h umans, with their fre e will; but they could a ls o b e, e.g. ants, drawing un usual computational powers fro m their pheromones [21]. Indeed, a framework that attempts to ca pture some so cial interactions, as a nnounced in the title of this pape r , can not b e captured by a purely co mputational mo del, and th us ca n hardly b e ex p ected to b e computationa lly sound. On the o ther hand, even if we a ccept to simulate all actors by T ur ing machines, including a n ts and humans, the r e s ulting ac tor-netw ork will still not boil down to the computational mo del, since the diverse co mm unication channels, that can b e s pecified in a n acto r-netw o rk, cannot b e reduced to in teractions of T uring machines. This is further discuss ed in Sec. 2. Undoubtedly , the fact that our mo del cannot b e pr ov en computationa lly s ound, or ev en given a compu- tational interpretation, can b e interpreted as the e vidence that we are mo deling what ca nnot b e mo deled; whereas the fact that our pr o o fs canno t b e a utomated ca n b e viewed as the evidence that they a re no t completely forma l. Bo th in terpretations are true, for some s uita ble meanings of the w ords “formal”, and “mo del”. Instead of arg uing whether these mea nings ar e reasona ble or not, we present our formal mo del. W e co n tend that o ur actor-netw ork based pro ofs in Pro cedur e Deriv ation Logic are a s rig orous as the pro ofs in an y of the sta nda rd ma thematical formalisms; and hopefully somewha t insigh tful for the rea der. In par - ticular, our dia grammatic pr o ofs ca n b e viewed as a formal method similar to diagr am chasing in category theory [4 2, 54], from which we drew inspiration. Outline of the pap er Sec. 2 int ro duces the formal mo del of acto r -netw o rks. Sec 3 ex plains how acto r-netw o rks compute, a nd int ro duces the formalisms to represent tha t computation, a ll the way to actor-netw ork pro cedur es. Sec. 4 presents P r o cedure Deriv atio n Log ic (PDL) as a metho d for reaso ning ab out actor- netw ork pr o cedures. In Sec. 5 we provide the fir st case studies using PDL: we analyz e the tw o-factor authentication in online banking, and a device pairing pro c edure combining physical and bio metric channels. Sec. 6 contains a discussion of the re s ults and the future work. 2. Actor-netw ork mo del 2.1. A computer is a netw ork is a computer The standard mo del of computation is a T ur ing machine. It uses a tap e as a stor age medium. So metimes additional tap es are used to repres e nt the input and the output int erfaces. Pro babilistic T urning machines also read so me r andom strings from a dev oted tap e, whereas oracle T uring ma chines communicate with the oracle through an additional tap e. Las t but not lea st, interactive computation is often mo dele d using several Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 7 T uring machines that interact with ea ch other on joint tap es. Such joint tape s ar e actually the c ommunic ation channels betw een the T uring mac hines. Int eractive T uring machines can b e viewed as a co mputatio nal netw o rk, with the machines a s no des, and the join t tap es as links b e t w een them. How ever, p er v asive netw orks that compute in the world aro und us nowada ys include a wide v a riety o f computatio nal agents at their no des, including humans, and the v ario us devices with different computatio na l p ow ers. Luckily , an a bstract v iew of the no des suffices for most analyses. W e usua lly just need to s pecify that the sta te, i.e. the v ar ia bles where the node can stor e its data ; and we p ostulate which computations ca n b e effectively p erformed by the no de, and whic h computations are unfeas ible. The c hannels betw een the no des can b e viewed as a genera liz ation o f the join t tapes , shared by T uring machines in their interactions. But while the joint tap es trivia lly pass information from one ma chin e to the other , nontrivial c hannels p erform no n trivial data tra nsformations. E.g., a pair o f no des (whic h may or may not be T uring machines) can b e co nnected by a no isy binary channel, flipping each bit with a certain pro bability while passing it fro m one no de to the other. Another pair of computationa l age nts can be co nnec ted by a cyb er channel, controlled b y a n adaptive attack er, who can change and mo dify the data flows at will. In symbolic proto col a nalysis, such attack ers a re usua lly spec ifie d as simple sta te machines. In cryptogr aphy , they are usually mo deled as probabilis tic po lynomial-time T uring machines. In netw ork mo dels, it is conv enien t and intuitiv e to view them a s pro cesses encapsula ted in channels. In summary , the simplest mo del of net w ork computation consists o f • computational agents, some o f them con trolled by v arious par ties , others av ailable a s reso urces; a nd • communication channels b et w een the agents, supp orting differen t types of information flo ws. 2.2. Idea of actor-net w orks Actor-netw orks depict so cia l pr o cesses as computations, and computatio n a s a so c ial pro cess. An example of an actor -netw o r k is a configur ation consisting of a musician and her instrument. Their intended interaction is the mu sic. The pr o cess and the res ult a re hig hly struc tur ed, and the netw ork repr esentation helps with the a nalysis. The netw o rk first of a ll displays the symmetry of this interaction: the musician cannot play without the instr umen t, a nd the instrument cannot play without the musician. The fact that some m usician’s instrument may b e a pa r t of her b o dy (e.g., her voice), and that some instrument’s musician may b e a computer makes the picture only more interesting. A smart card a nd a smar t car d reader form another net work of this type. But this netw ork is complicated by the need for so meone to key in the pin of the ca rd. The netw ork grows still further if the ca rd reader is connected to a bank, and p erhaps dis p enses money . When netw orks in v olve heteroge nous nodes , and heterog enous commun ication channels, then the diverse computational resources lead to different c omputational pow ers. This is where net work computation essen- tially devia tes from machine computation, where a ccording to Church’s Thes is, all the different machines hav e the sa me computationa l p ow ers. In a netw ork, one computer may b e eq uipped with a camera and may provide a visual channel to a remo te user , whereas another computer may b e equipp ed with s ensors and controllers, allowing it to stabilize the flight o f an air craft. A sma rt ca r d can p erform some cry ptographic op erations when inserted in a reader, and other ones in the c o nt actless mo de. A musical instrument can pro duce one t ype of music with one m usician, and something completely differen t with somebo dy else. The m usician also dep ends o n the instrument. F urthermore, after they are configure d with their instruments, the m usicians may fur ther configure themselv es into a hig her -order co nfig uration: an or chestra. And the orchestra can also b e view ed as a n actor within the configur ation of a n op era p erfo rmance. . . Such configura tions are what we c a ll actor-networks . A c o mputational agent who par ticipates in a co n- figuration is an actor , in the sense that she plays a particular r ole as signed to it b y a particular netw ork pr o c e dur e . As computationa l netw orks sprea d and diversify , it is b ecoming increasing ly imp ortant, and in- creasingly difficult, to a ssure that pr o cedures provide the desire d actor a nd net w ork b ehaviors. T ow ards this goal, w e forma lize the ab ov e int uitions ab out a ctor-netw orks, a nd build a framework for rea s oning ab out their pr o cedures. Remark. The hierar ch ical structure of our actor- net w ork formalism is a lien to the spirit and the letter of original a ctor-netw ork idea from so ciology [3 9]. But it is essential for the goa ls of our logica l analyses, which 8 D. P a vlo vic and C. Meado ws are different from the go als of so ciolog ical analyses. It may b e of interest to explore the relation b etw een the t wo sets of go a ls. 2.3. F ormalizing actor-net w orks Definition 2.1. An actor-net work consis ts of the following sets: • identities , o r princip als J = { A, B , . . . } , • no des N = { M , N , . . . } , • c onfigur ations P = { P, Q, . . . } , where a configuration can b e – a finite set of no des, or – a finite set of co nfigurations; • channels C = { f , g , . . . } , and • channel typ es Θ = { τ , ς , . . . } given with the following structure: Θ ϑ ← − C δ ⇒ P c ⇀ J where • the partial map c : P ⇀ J tells which pr incipals control which c o nfigurations, • the pair of maps δ, : C → P as sign to each channel f a n entry δ f and a n exit f , and • the map ϑ : C → Θ assigs to each channel a type. An actor is an element of a configur ation. Actors formally . By the a bove definition, a config ur ation is thus a tree whose leav es ar e a nnotated b y net work no des. A configur ation is a n actor when viewed as a n element of another configuration. In other words, a n a ctor is forma lly a maxima l subtree of a configura tion tre e . It is use ful to distinguish the trees that co me together to form a nother tree becaus e this is what they do to p erform s ome action together. F or instance, a hand, a p e ncil and a piece of pap er come toge ther as acto rs to re c o rd a thoug h t. A ha nd itself is a c onfiguration of fingers, whic h come together to hold the p encil. The p encil is a co nfiguration of graphite and woo d. A do o r, a lo ck a nd a key co me together to enfor ce so meone’s authority ov er a space. The lo c k is a config ur ation of its metal comp onents. The writing configuratio n and the lo cking configuratio n c o me together to put a nov el in a drawer. And a ll of it is just trees. Notation. W e denote by N B a no de N cont rolled by the pr incipal c N = B . W e write g = ( P τ − → N B ) for a channel g of t ype ϑg = τ , with the en try δ g = P , and with the exit g = N controlled b y c N = B . Since there is usua lly at most one channel of a given type betw een t w o given co nfigurations, w e us ually o mit the lab el g , and write just P τ − → N B to denote this channel. 2.4. Examples of netw orks 2.4.1. Cyb er networks Cyb er netw orks ar e built following the “end-to-end“ a r chitecture [63]. In our formalism, a cy ber netw ork is characterized b y the fact that • C = { cyb } , i.e. ther e is just o ne channel type, which we call cyb er channel. This is ar e the insecure channel ov er which cryptogr aphic pro toc o ls are usua lly run. • P = N , i.e. the only config ur ations are the nodes . • There is a channel M → N for every pair M , N ∈ N . Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 9 C A B Fig. 1. Cyb erspace as completely connected C A B M Fig. 2 . Cyb ers pa ce as completely adversar- ial • All communication is done b y bro adcast fr om the sender to all nodes in the netw o rk. The recipien t do es not observe the sender directly (although, of cour s e, the sender can identify , or misidentif y hers elf in the message). If a principa l co ntrols several no des, it makes no difference which node he uses to send a message. Without loss of g enerality , w e can thus assume that each principal co n trols exactly o ne no de, i.e. that N = J . The actor-netw ork structure of a cyb er netw ork is thus degenerate, a nd b oils down to a single t yp e P = N = J , since the only configura tions are the no des, a nd the no des ar e in o ne-to-one cor r esp ondence with the principals . That is why in crypto proto co l a nalysis, we usually just sp ecify how many different pr inc ipa ls should play different roles. The fact that any t w o principals, viz netw ork node s , ar e directly connected by a completely insecure cyb er c hannel is as sumed tacitly . The cyb er ne twork with three no des/principals is presented o n Fig 1. The fact that the cyb er channels are insecure can b e captured in the mo del of a cyb er netw ork b y assuming that all traffic is routed through the attack er , i.e. that A lice, B ob and C aro l are all linked with each other through M allory . In a sens e, the attacker Mallor y is the embo dyment of cyb erspace. This architecture is presented o n Fig. 2. 2.4.2. An actor-network for two factor authentic ation T o mitigate phishing attacks, most online banks hav e rolle d o ut tw o factor a uthentication. This means that they do not just verify that the use r k nows a password, but also so mething else — which is the second authent ication factor. This sec o nd factor often re q uires some additional netw ork resour ces, b esides the internet link b etw een the customer and the bank. This is the first, quite familiar step b eyond s imple cyb er netw orks. In the simples t case, the bank authenticates the browser used to access the service, by leaving a p ers isten t co okie. The server often also re c o rds some data a bo ut user’s computer and net work lo catio n. The user only notices this when she tries to a ccess the bank from another lo cation, or using another browser: s he is then asked to go through a round o f “mo ther’s maiden name” type of challenge questions. A more interesting t ype of seco nd factor ar e the single-use T ra nsaction Authentication Numbers (T ANs) that the server ma y generate. Initially , they were b e predistributed on pap er. Now a days they are often sent to user’s mobile phone in a n SMS messa ge when login is initiated. The user is thus authenticated as the owner of her mobile phone. The other wa y around, the ser v er is a uthen ticated to b e in p os session of user’s pho ne num b er , which eliminates the g eneral phishing attacks. Some banks authenticate that the user is in po ssession of her smart card. The underlying acto r-netw o rk is on Fig. 3. The user A lice controls her co mputer C A and her smart card S A . She is also given a p ortable smart card rea der R . She inserts the c a rd in the rea de r to fo rm the configura tion Q . The r e ader is av aila ble to Alice, but a n y other r eader w ould do as well. Config ur ed into Q , the sma r t ca rd and the r e a der verify that Alice knows the P IN, and then gener ates the log in credentials, which Alice copies fr om R ’s screen to her computer C A ’s keyboard, which forwards it to bank Bob’s computer C B . The details of the a uthen tication pro cedure will be analyzed la ter. In summary , the net w ork th us co nsists of • principals J = { A, B } , • no des N = { I A , C A , S A , R , C B } ; • configuratio ns P = N ∪ { Q } , where Q = { S A , R } , 10 D. P a vlo vic and C. Meado ws I A C A R C B Q vis k ey A cyb cyb vis S A B k ey Fig. 3. A pe rv asive netw o rk: Online banking with a smart ca rd reader I A D A D B I B S Q A vis vis vis bio bio B A shk cyb cyb Fig. 4. Acto r -netw o rk for device handshake • and the follo wing six c hannels – c y ber c hannels C A ⇆ C B betw een A lice’s and B ank’s computers, – v isual channel C A → I A from A lice’s computer to her human I A , – keyb oard I A → C A from A lice’s h uman to her computer, – v isual channel R → I A from the smart card reader to A lice’s human, – keyb oard I A → R from A lice’s hum an to the car d reader. 2.4.3. An actor-network for devic e handshake Suppo se that Alice and Bob have some hand held devices a nd that they wan t to pair them, i.e. set up a secure cr yptographic channel, without any pre vious encounters or infrastructure. Ther e is a whole industry of metho ds to do this. W e describ e a metho d inspired by [43] and [1 0]. Alice’s a nd Bob’s devices D A and D B are equipp ed with ac c e lerometers. If a device with an acceler ometer is s haken, then the acceler ometer can b e used as a source of r andomness. If tw o device s are shaken to gether, their acce le rometers will genera te roughly similar random strings. A sha red random s tring can b e extra cted by the techniques des crib ed in [43], or using fuzzy extractor s [19]. W e simply assume tha t a joint ly samplable sour ce is given, and denote id by the no de S . W e now describ e an actor -netw o rk s uppor ting a devic e handshake pr o c e dur e , where the usual device pairing task is strengthened by the requirement that the secret shared by the devices D A and D B is also bo und to the identities o f their human owners I A and I B . Fig. 4 shows an actor-netw ork suppor ting, in a sense, a half of this task: it will allow Alice to sha ke t wo device s together, to extract the shared secret; and mor e over Alice’s dev ic e D A will biometr ically verify that it is being shaken by Alice’s human I A , and not by someone else . If the devic e D A signals whether this verification succeeds in a wa y visible to Bob’s human I B , then Bo b knows that the key e x tracted into his device D B is shar ed w ith D A , and bo und to the identit y of I A . Alice’s human I A can obtain similar ass urances in an analog ous round o f the same pro cedure. The net work for both rounds is depicted o n Fig. 5. F ormally , in the ac tor-netw ork for one round, depicted o n Fig. 4, Alice controls the configura tion Q A , Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 11 I A D A D B I B S Q A Q B vis vis vis bio bio B A shk cyb cyb vis shk Fig. 5 . Actor-netw ork for t w o-round device handshake which consists of her device D A , Bo b’s device D B , and Alice’s hand I A , holding the t wo dev ices tog ether. Alice’s action of shaking the devices is represented a s Q A ’s action of sampling a source of ra ndomness S along a devoted channel. The accelerometer s a r e abstr acted aw a y , and reduced to the no de S . The fuzzy extractor s are abs tracted awa y and r educed to the fact that the r andomness co nv eyed to Q A is distr ibuted to bo th of the a ctors D A and D B participating in it. The details of the pro cedure are analyzed la ter. Here we just summarize that the actor -netw or k for device handshake c o nsists of the following data: • t wo principals in J , A lice and B ob, • five no des in N : – D A and D B are Alice’s and Bob’s dev ices – I A and I B are Alice’s and Bob’s h uman identities, – S is a s o urce of r andomness; • one config ur ation in P – Q A is the co nfiguration wher e Alice holds her a nd Bob’s devices in her hand: it co nsists of I A , D A and D B ; • eight channels in C : – tw o cyb er channels D A ⇆ D B betw een A lice’s and B ob’s devices; – o ne biometric channel: · I A → D A from Alice’s hand to her device – thr ee visual channels: · D A → I A from Alice’s device to her eyes, · D B → I B from Bob’s device to his eyes, · Q A → I B from Alice’s hand, holding bo th her and Bob’s device to Bob’s eyes; – o ne physical channel: · S → Q A from the source o f randomness to Alice’s c onfiguration, which conv ey s the randomnes s to D A and D B . T o as sure that ea c h principal co n tributes to the randomness, the a bove pro c e dure can b e rep eated with Bob shaking. The actor- net w ork where b oth Alice and Bob see ea ch other shaking bo th devices is depicted on Fig. 5 12 D. P a vlo vic and C. Meado ws 2.5. Metaph ysics of securit y 2.5.1. Knowing, H aving and B e ing It is often rep eated that security is ba s ed on: • something you know : dig ital keys, passwords, and other secrets, • something you have : ph ysical keys and lo cks, smart ca rds, tamp er-r esistant devices, o r • something you ar e : biometric features, such a s finger print s, eye ir ises, and other unmo difiable pro per ties of your b o dy; or the capabilities that you ca nnot conv ey to others, such as your handwriting . An identit y can th us b e determined by its secrets, its tokens, and its features. In our mo del, this is ca ptured by three levels o f control that a principal may hav e ov er its nodes : • se cr ets: wha t you know can be copied a nd sent to others, • tokens: what you hav e ca nnot b e co pied, but can b e given aw ay , wherea s • fe atur es: what you a re cannot b e copied, or given aw ay . Comments. The commo n e nd-to-end sec ur it y goals ar e usually realiz ed b y means of cry pto graphic softw are, and the principa ls prove their identities by their se c r ets. In cyb er netw orks, a princip al c an b e identifie d with the list of se cr ets that she knows . If Alice and Bob share all their secr ets, then there is no way to distinguis h them b y the challenges that ca n b e issued on the standar d completely insecure net w ork channels 2 . F or all purp oses, they mu st b e co nsidered as the same principal. In per v asive netw orks, o n the o ther hand, security is a lso s uppor ted b y ph ysical security tokens and hardware. F o r mally , this is wher e the netw ork mo del b eco mes no n trivial: security tokens c orresp ond to net work no des which may be controlled by one principal at one point in time, and b y another one at another po in t. Finally , security fea tur es corresp ond to netw o rk no des which are co nt rolled by a single princ ipa l, a nd cannot be r elinquished. Suc h no des corr esp ond to biometric prop erties. Their c ount erpart are the no des that represent biometric devic es . When all is well, a biometric channel th us ha s a biometric pr op erty at its entry , and a biometric device capable of observing this pr o pe r t y at the exit. 2.5.2. What is an identity? In a cy ber netw ork, a ny o ne who k nows all my secrets can imper sonate me, and the standa rd mo dels thus assume that a n identit y is a set of sec r ets. 3 In a p erv asive netw ork, ev en if so meone knows all my sec r ets, we can still be dis tinguished as lo ng as o nly one of us ha s m y smar t card, o r my fingerprints, or if only one of us is standing at the do o r . In the actor-netw ork mo del, b esides the secrets, there ar e also the v ar ious tokens and features that a principal ma y control. An identit y is thus a set of actors , which may include to kens and features. F ormally , the s et of pr incipals J can b e represented • in a cyber net w ork along the injection Γ : J ֒ → ℘ T which ass ig ns to ea c h identit y the set of terms that she knows [5 6 ]; and • in an actor-netw ork, along the injection r : J ֒ → ℘ C A 7→ { P ∈ C | c P = A } which ass ig ns to ea c h identit y the set of configurations that she controls. 2 Here we assume that they share the secrets with eac h other dynamically: the secrets it will immediately b e shared with the other. This implies that they also observe the even ts on the same set of netw ork no des. 3 In reality , even in an end-to-end net w ork, tw o principals wi th the same set of secrets but, say , differen t computational p o w ers, can b e distinguished by timing their responses. Or they may be distinguished by their histories, since si nce ma y hav e derived their s ecrets f rom different i nitial data, as explained in [55, Sec. IV.D.1]. The standard mo dels, how ev er, abstract a w a y all that. Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 13 F or simplicit y , we assume here that the stor age containing the terms from Γ ( A ) is s ubsumed among the no des r A . More ab out this in Sec. 3.2. Wh y do w e use the words “principal” and “identit y” as synony ms? F or the b enefit of the readers with a background in pro toc o l analysis , let us emphasize that princip als do not p erform any actions in the present mo del. The principals control their actors, and the actors per form the actions, and play role s. A principal determines if and when its actors p erform a n action, and can thus co ordinate the order in which the actio ns of her a ctors will b e executed. But without the actors , a principal ca nno t execute a n y actions. That is why the alternative term “ identity” may b e preferr ed ov er “princip al” . On the other hand, for the sp ecial c ase of proto cols, the concept still b oils do wn to the familia r idea of principals, who play their roles in pro to cols, etc. So w e retain tha t term as well. Metaph ysics of actors and principals. Intuitiv ely , the relation b et w een a pr inc ipa l and her ac to rs in an actor-netw ork can b e construed in terms of the mind-b o dy duality : the principal is the mind, and the acto rs are some parts of the bo dy , that the mind can use to observe the w orld and to act in it. The data r eceived or sampled by so me a ctors through the suitable channels are directly av aila ble to the pr incipa l: e.g., the principal may control a ca mera, and observe the visual signal that the camera receives. O n the other hand, some other actors may no t c onv ey their data to the principa l that controls them: the camer a may hav e no cable, or not enough lig ht. The b o dy has its limitations. Which type of infor mation e a ch a c to r conv eys to its principal must b e sp ecified by the pro cedure sp ecific axioms. Such specifica tions determine the semantics of ea ch mo del and the inten t of ea ch actor - net w ork pro cedur e. 2.5.3. What ar e the channel typ es? Some of the channel t yp e s that w e shall study are: • cyb er channels: ea ch node broadca s ts to a ll no des ; there is no notion of distance; the recipient c annot observe the sender 4 • visual channel: the even ts at all no des within some distance a re o bserved; the o bserved no des may or may not observe that they ar e o bserved; • binary channel: streams bits from one node to a nother, flipping them with so me given probability . The binary c hannel is one of the basic concepts of information theory , capturing a s imple notion of random noise. Intuitiv ely , the cy ber attack er can b e v ie wed a s “ adaptive noise” , dis turbing the integrity of the messages. 3. Actor-netw ork pro cesses 3.1. Computation and comm unication Computation in a netw o rk consists of events , which are loca lized a t no des or configurations. An even t that is controlled by a principal is an action . Communication in a netw o rk co nsists of information flows a long the channels. Each flow cor resp onds to a pair of even ts: • a write even t a t the entry of the ch annel, and • a r e ad e ven t a t the exit of the c hannel. There ar e tw o k inds of flows: • messages , whic h consist of a send action at the en try of the c hannel, a nd a r e c eive c o action at the exit; and • sour c es , which consist of a n sample action at the exit, and a emit c o action at the en try . 4 W e can assume that the sender alwa ys includes her iden tit y int o the message, within some standard format such as email. But suc h s ource clai ms can be easily sp oofed in cyb er space. 14 D. P a vlo vic and C. Meado ws ev en ts (actions • ) write read flo ws message send • receiv e source emit sample • T able 3 . Flows and events The information flows and the c orresp onding even ts are summarize d in T a ble 3. The black dots mar k the actions. A c o nsistent actio n- coaction pair is called an inter action : i.e., an interaction consis ts of a send action and a r eceive co action, o r of a emit c oaction a nd a sample action. W e presently consider only these tw o t ypes of int eractions. Both the receive coactio ns and the emit coa ctions are constr ued as passive events: neither the principal who receives a message, nor the one who emits fro m a so urce c o n trols when this happ ens. Of course, in reality a principal may , e.g. actively refuse to receive a messag e, o r to emit emit a sour ce, etc. But our go al is to enable simple analyses, and w e leav e these details outside the s cop e of the general mo del. A co mputational pro ce s s that is loca lized at a no de pro ceeds as in the traditional mo dels of computatio n. The no de c a n b e thought of a s a sta te machine (e.g. a T ur ing machine), a nd the computational even ts change its state. An e ven t a t a co nfiguration P may changes the states of any of the actor s N ∈ P . In the ac tual analyses, the state changes often need to be traced, but we did not encoun ter an example where an actual state machine would need to b e s pecified. The most a bs tract mo dels that c a pture the relev an t feature s usually supp ort the simples t analyses, hiding the implementation details. Besides transfer ring information fr om one co nfiguration to ano ther, the flows als o synchronize the even ts that take place a t different lo calities, b ecause: • every rec e ive coaction m ust b e preceded b y a cor resp onding send actio n, and • every sa mple action must b e preceded by a co rresp onding emit coaction. If a source has not b een emitted to anywhere, then ther e is nothing to sa mple, a nd no sampleion of that source can o ccur. If a message ha s not been sent , then the corres po nding r eceive even t cannot o ccur. So • when I receive a message, then I know that it must hav e b een sen t previo usly b y someone ; and • when I sample a so urce, then I know that someone must hav e emited to this source. That is how I draw conclusions about non-lo cal e vents fro m the o bserv atio ns of my own lo cal actio ns. This is formalize d in Sec. 4.3.1. In tuitions and ide as. A config ur ation can b e thought o f as a mec hanism, assembled from separate com- po nen ts that may b e owned and co n trolled by different principa ls . Another view is tha t a configura tion is like a team, co mpo sed of the play ers that came to act together tow ards some g oal, but will separ ate and go their own ways when they are done. The usual (physical) handshake, confir ming a so cial contact, c an be viewed as a configuration. A couple da ncing together is a c o nfiguration. A band pla ying m usic together is a configuratio n. A channel is like a wire, connec ting tw o co nfig urations. The messa ges and the sources are tw o t ypes of flows thro ugh a ch annel. If Alice w ants to send a messag e, s he needs a c hannel to send it on. B ob is on the other side of the c hannel, pa ssively waiting to receive the message. If Bob wan ts to sample a source, he ne e ds a channel for tha t. Alice is on the o ther side of the c hannel, passively emiting. In bo th cases, Alice is at the ent ry of the channel, and Bob is at the exit of the channel. Besides the channels that connect it to other config urations, a co nfiguration may have internal metho ds for co ordinatio n among its no des. E.g., a handshake is co ordina ted by tw o hands s ensing each other. A couple of dancers develop signa ls that co or dinate their dance. In some cases, suc h signals need to be ma de explicit as information flows. A configuration may need to s e nd itself a message, or to sample itself as a source: e.g., to a ssure that genuine rando mnes s is extracted. While the internal signaling and co ordination capture controlled pro cesses within a co nfiguration, there a re many pro cesses that ta ke place within a single configuratio n that are not entirely controlled. Dance gr oups a nd the bands of musicians have, bes ides the subtle fo rms of internal s ignaling, evolved complex externa l pro cedure s to synchronize and co ordinate. Such pro cedures can b e thought of a s primordial so cial softwar e . Analyzing them within a formal mo del might conceiv ably ope n int eresting p oss ibilities of electronic supp ort. Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 15 3.2. F ormalizing data as terms Each flow ca rries s ome data, whic h con tain information. In abstract mo dels, data are represented as terms of an algebra: the co nten t o f a mes s age is an element of an algebra . W e sha ll a ls o repr esent the emissio n fro m a source as an element from the same algebr a. The algebraic op erations corr espo nd to the data pro cessing op erations. In the standard symbolic proto col mo del [2 0], the messages the terms of a free algebra of encryp- tion a nd decryption op era tions. More genera l algebraic mo dels allow additiona l op erations, and a dditional equations [12]. Recall that an algebra ic theor y is a pair ( O , E ), where O is a set of finitary op eratio ns (given as s ym bo ls with a rities), and E a set of well-formed equatio ns (i.e. wher e each op eration has a corre ct num b er of a rguments) [31]. Definition 3.1. An algebraic theor y T = ( O, E ) is called a data the ory if O includes a bina ry pair ing ( − , − ) op eration, and the unary ope r ations π 1 and π 2 such that E co n tains the equatio ns π 1 ( u, v ) = u , π 2 ( u, v ) = v , and (( x, y ) , z ) = ( x, ( y , z ) ). A data algebr a is a p oly no mial extension T [ X ] o f a T - a lgebra T . F unction notation. When no confusion seems likely , we elide the function applications to concatenation, and write f .x instead of f ( x ). A function of tw o ar gument s e ( x, y ) is th us identified identified with its curried form e.x.y , and e .x abbreviates e ( x, − ). By a buse of notation, the pair ( x, y ) can thus be written as x, y , and ( x, ( y , z )) = (( x, y ) , z ) a s x, y , z . When no confusion is likely , we even elide the dot fro m the concatenatio n and simply write f x instea d of f .x , or f ( x ) . T upling. T he e quation ( x, ( y , z )) = (( x, y ) , z ) in the ab ov e definition implies that there is a unique n - tupling op eration for every n . T he first tw o equations imply that the comp onents of any tuple can be recovered. Random v alues are repres e n ted by i ndeterminates. A p olynomia l extension T [ X ] is the free T - algebra generated by adjoining a set of indeterminates X to a T -alg ebra T [31, § 8]. The e le men ts x, y , z . . . of X are used to represent nonces a nd o ther randomly genera ted v a lues. This is justified b y the fact that indeterminates can b e consis ten tly renamed: nothing changes if we permute them. Tha t is just the prop erty required from the random v alues genera ted in a run of a proto col. Of course, this is not the o nly requirement impo sed on nonces and random v alues: the other require ment is tha t they are known only lo cally , i.e. only by those principa ls who genera te them, or who r eceive them in a r eadable message . This re q uirement is not formalized within the algebr a of mes sages, but b y the binding rules o f pro ces s ca lculus [17, 56]. Here we capture it b y the fr eshness axio ms in Sec. 4.3.2. Stores are no des . While the rando m v alues are thus alg ebraically presented a s the indetermina tes (i.e. as the v ariables in the p olynomial extension), the stores (i.e. the v ariables use d in computation) can b e mo deled as netw ork no des , each with a devoted r ead channel a nd a write channel. The pr o per t y of such a no de which is that it c an store a v alue. The term stored in suc h a no de determines its state. In this wa y , the usual no tion of sta te, as a partial as s ignment of v alues to v ariables, is included within the netw ork mo del. The state of a configur ation is th us the pro duct o f the states of its actors, wher e some o f the ac tors only task is to store some v a lues. Easy s ubterms. W e a ssume that every data algebra comes equipp ed with the e asy subterm r elatio n ⊑ . The idea is that tha t s ⊑ t implies that s is a subter m of t s uc h that every principal who knows t also knows s . In o ther words, the views Γ A are low er clos e d under ⊑ , as ex plained in [5 6]. This is in contrast with hard s ubterms, which canno t b e extracted: e.g., the plaintext m and the key k are hard subterms of the encryption E .k .m . In the Dolev-Y ao alg e br a, it is stra ightf orward to define the easy subterm rela tio n inductively . F or general algebraic theories, the task of discerning the subterms gets complicated. A gener al treatment was attempted in [56]. 3.3. F ormalizing ev e nts and pro cesses In this section w e define pro cesses, the ev en ts that pro cesses enga g e in, and the ordering of ev ent s within a pro cess. 16 D. P a vlo vic and C. Meado ws 3.3.1. Events An even t or a ction is ge ne r ally written in the for m a [ t ] where • a is the even t iden tifier, • t is the term o n which the even t may dep end. When an even t do es not depend on data, the ter m t is taken to be a fixed consta n t t = X , and we often abbreviate a [ X ] to a . The most imp orta n t even ts for our ana lyses are the action-coa ction c o uples send-receive, and sample-emit, for which we in tro duce sp ecial no ta tions: • send h· t ·i , r eceive ( · t · ), • emit h : t : i , sample ( : t :). Generically , we wr ite • h t i for a write actio n, which can b e either h· t ·i or h : t : i , and • ( t ) for a read action, which can be either ( · t · ) or (: t :). Another often used actio n is • generate a random v a lue ν [ x ], It could also b e implemen ted as sa mpling a s o urce of r andomness repr e sent ed as a devoted no de. In addition, the no des are capable of p erfor ming v arious lo cal op era tions. Most are able to execute the standard pseudo- co de co mma nds, like comparis ons ( t = s ) or ass ignment s ( t := s ). But the differences in their co mputational r esources will be e s sential in some of the security analyses o f the pro cedures below. F urther examples of application sp ecific ev ent s and a c tions will b e in tro duced in the b elow. F or actions , such as h· t ·i and (: t :), the configur a tion P must b e controlled, i.e. the pa rtial function c : N ⇀ J must hav e a definite v a lue c P . Representing even ts as terms. How do we represent pr incipals’ observ ations of events a nd of other principals’ actions? The lo catio n o f an even t may b e viewed a s a so urce for sa mpling; the lo cation of an action must be con trolled by a pr inc ipa l, who may b e viewed a s the sender o f the message a bo ut the a ction that to ok place. But since only da ta can b e sent as messages, or sampled fr om so ur ces, each observ able action a [ t ] P m ust b e repres en ted a s a ter m h a [ t ] P i . In gener al, this is done b y a dding to the presentation of the alg ebra T a mapping [ − ] : E → T which g enerates a r epresentation of each event from E . A similar map assig ning to each action a logica l formula leads to dyna mic log ic [32]. W e’ll see a typical example of a mes sage a bo ut a n actio n in Sec. 3.5.3, where we re tur n to the device handsha ke pr o cedure. B ob can only conclude tha t the secr et shar ed b y his and Alice’s device is authen tic if he sees Alice shaking the devices. Self-sampli ng. A less typical, but not less in teresting example arises if we assume that a configuratio n has a channel to s ample its own event s. Such a config uration can then sa mple its own sampling, i.e. execute the actio n ( : [ (::) ] :). The principa l who controls such a config ur ation can then obser ve some of her own observ ations. It is interesting to explo re the authenticit y of such observ atio ns. W e shall touc h this a gain in Sec. 4 .4.1. 3.3.2. Pr o c esses Definition 3.2. A pr o c ess F is a partially ordered mult iset o f lo calized even ts, i.e. a mapping F = hF E , F P i : F → E × P where • ( F , ) is a well-founded pa rtial or der, representing the structure time, Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 17 • E is a family of even ts, and • ( P , ⊆ ) the partial or der of configura tions, and they satisfy the requirements that (a) if F E φ is an action, then c ( F P φ ) is w ell defined, and (b) if φ ψ in F then F P φ ⊆ F P ψ or F P φ ⊇ F P ψ in P . Notation: The p oi n ts in time are denoted b y ev en ts . B y abuse of notatio n, we usua lly write a [ t ] P for φ ∈ F where F E φ = a [ t ] and F P = P . Of c o urse, if the there are several points in time φ 1 , φ 2 , . . . ∈ F where the same P executes the same a [ t ], then this notation is ambiguous, s ince it is not clear to which φ i do es a [ t ] P refer. But such situations are rare. On the other ha nd, with this no tation the ab ove co nditions bec ome: (a) if a n action takes place at a configuration P , then P is controlled, i.e. c P must be well defined, and (b) if a [ t ] P b [ s ] Q then P ⊆ Q o r P ⊇ Q . Remarks. The subset order ing of ( P , ⊆ ) ar ises fro m Def. 2 .1, which says that co nfig urations are finite sets. Partially o r dered multisets, or p omsets were intro duced and extensively studied by V aughan Pratt and his students [62]. Condition (a) sp ecifies wha t we already said info r mally: that the configuratio n where an action takes place must b e controlled. Condition (b), on the other hand, means that ther e is no subliminal synchr onization : the or dering of even ts can only b e imp osed within a configur ation that enables all o f them. If Alice p erfo rms one action controlling a c o nfiguration P A , a nd then another action co n trolling a configura tion Q A , then she mu st control a configura tion R A ⊇ P A ∪ Q A , that will allow her to control the o rder of the actions with P A and with Q A . The intended use of config ur ations, including any constra in ts that would require that so me parts of P A and Q A should not b e used together, must b e imp osed throug h axioms, in the PDL langua ge in tro duced in Sec. 4. Definition 3.3. W e say that the ter m t originates at the po in t φ ∈ F if φ is the earlie s t write o f a term containing t . F or ma lly , φ th us satisfies • F E φ = h s i where t ⊑ s , and • F E ξ = h s i ∧ t ⊑ s = ⇒ φ ξ ho lds for all e v ent s ξ . Notation: Origination. W e extend the notationa l con ven tions describ ed ab ov e by denoting by p hh t ii P the even t φ wher e the ter m t o riginates. The configuration P is the originator of t . 3.4. F ormalizing flo w s, runs and pro cedures W e now extend our discussion to the definition of communication b etw e e n pr o cesses, and extend our or dering to even ts o ccurring within a pro ce dur e as well as individual pro cesses. W e beg in by defining a more g e neral version of c hannel betw een tw o configur ations, called a flow channel. A flow channel exists b etw een any tw o co nfigurations if a channel exis ts betw een any t w o no des o n the configuratio n trees. It is ca lled a flow channel because the information passed a long the channel flows up w ards to the configuration as a whole. It is defined formally b elow. Definition 3.4. F or configurations P , Q ∈ P , a flow channel P τ − → Q can b e either • a channel P τ − → Q , or • a flow channel P τ − → Q ′ , wher e Q ′ ∈ Q , or • a flow channel P ′ τ − → Q , where P ′ ∈ P , o r • a flow channel P ′ τ − → Q ′ , where P ′ ∈ P and Q ′ ∈ Q . A flow a [ t ] P τ − → b [ s ] Q is g iven by • a flow channel P τ − → Q , and 18 D. P a vlo vic and C. Meado ws • an interaction pair a [ t ] , b [ s ], i.e. a pair where – e ither a [ t ] = h· t ·i and b [ s ] = ( · s · ), – o r a [ t ] = h : t : i , and if b [ s ] = (: s :). A flow a [ t ] P τ − → b [ s ] Q is c omplete if s = t . Definition 3.5. Let F be a pro cess. A run , or exe cution E F of F is an assignment for each coaction b [ s ] Q of a unique flow a [ t ] P τ − → b [ s ] Q , which is r equired to be sound , in the sense that b [ s ] Q 6 a [ t ] P in F . A r un is c omplete if a ll o f the flows that it ass ig ns are complete: the terms that ar e r eceived a re just those that were sent, and the ins pectio ns find just those terms that w ere submitted. A run is a p om set extending its pro cess. Setting a [ t ] P b [ s ] Q whenever there is a flow a [ t ] P τ − → b [ s ] Q of some type τ makes a r un E F int o an extension of the orde r ing o f the pro cess E , as a partia lly ordered m ultiset. The p omse t E F do es not have to satisfy condition (b) of Def. 3.2 any more. Indeed, the who le p oint of running a pr o cess is to extend in E F the internal synchronizations, g iven b y the o rdering o f F , with the additional exter nal synchronizations. Ov erloading arro ws. T he view of the runs a s or der extensions o f the pro cesses justifies the ov erloading of the ar row notation, whic h is us e d b o th • as a [ t ] P b [ s ] Q , saying tha t a [ t ] P precedes b [ s ] Q in the partial or dering ( F , ), and • a [ t ] P τ − → b [ s ] Q , denoting a flow of type τ from a [ t ] P to b [ s ] Q in a run E F . This o verloading is co nsistent , b ecause a flow fro m a [ t ] P to b [ s ] Q implies that a [ t ] P precedes b [ s ] Q ; and it will be useful whe n w e pass fro m the r uns, e.g. in Figures 6 –8, to forma l reaso ning ab out them in Figures 9 –12. The arrows in the latter family of diagra ms arise from the arr ows in the former family . But the former represent re a lit y , wher eas the la tter repres en t a ssertions ab out it. Definition 3.6. A n et work pr o c e dur e L is a pair L = hF L , E L i where • F L is a pro cess, and • E L = {E F L 1 , E F L 2 , E F L 3 . . . } is a set of runs of F L . The elements of E L are called se cur e runs. All other runs are inse cur e . A pro cedure is said to be secure if every ins e c ure run ca n be detected by a given logical deriv a tion from the observ ations of a s p ecified set of participants. Pro cedures generali ze proto cols. A pr oto c ol is a sp ecial case of a netw o rk pro c e dur e, where the un- derlying netw ork is a cyb er net w ork. Since c yber channels offer no s ecurity guar antees, the s e curity goa ls of proto cols are g enerally realized by cryptogra phic functions co mputed at the no des. That is why cyb er security is large ly conce r ned with crypto gr aphic pro toc o ls. It is thus ba s ed on the end-to-end par a digm, where the security tasks ar e pushed to the lo cal computations at the smart “ ends”, i.e. no des, leaving the net work simple and efficie nt. The ab ov e definition of a secure pro cedure gener alizes the definition of a secure proto col used in P r oto col Der iv ation Log ic [4 8, 56, 57], as well as in Proto col Comp osition Logic [24, 17, 15 ]. Net w ork pro cedures and their security pro ofs thus extend cr yptographic proto cols, and their security pro ofs. What is the difference? First of all, any no de in a cyb er netw o rk is as g o o d as any other no de, so it do es not matter which ones you co n trol, or how many . Without loss of generality , config urations can th us b e reduced to single no des , a nd the channel flows to the messag e s on cyb er channels. A proto col run th us b oils down to a sequence of messages among the principals, ea c h us ua lly con trolling a single no de, with so me lo ca l computations in-b etw een the mess ages. Nontrivial config ur ations arise in per v asive netw orks. E.g., a smart ca rd can only co mpute when inser ted int o a c o rrect co nfig uration with a car d rea der. Moreover, the info r mation c a n flow throug h a p erv asiv e net work in many differen t ways: by mess ages sent alo ng a v ar ie ty of different channels, short range, c e llular, so cial, etc.; or by obser v ations along visual channels, etc. The distinction b etw een computation and commu- nication in per v asive net works be c o mes blur r ed, as the tw o b ecome int ertwined in subtle and co mplicated wa y s. Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 19 A B cyb ◦ ◦ cyb c AB x ◦ ◦ r ◦ ν [ x ] r := r AB x Fig. 6. Challenge-Resp onse (CR) proto col template Graphic present ations of pro cedures . T o sp ecify a pr o c e dure L , we draw a picture of the p omset F = F L , and then each of its e xtensions E = E F L i . Because of condition (b) of Def.3.2 , the even ts compara ble within the or dering o f a pro cess F must happ en within a ma x imal co nfiguration. Ther efore, if the diagram of the partially ordered multiset F is drawn together with the underlying netw o rk, then each co mpo ne nt of the c o mparable e vents can all b e depicted under the corresp onding configuration. W e can thus dr aw the net work ab ov e the pro cess , and place the even ts o ccurr ing at ea ch c o nfiguration along the imaginary vertical lines flowing, say , down wards from it, like in Fig . 7. The a dditional ordering, imposed when in a run E the messages get sent and the facts g e t observed, usually run across, from config uration to configuratio n. This ordering c an thus b e drawn along the imaginar y horizontal lines b etw een the even ts, or parallel with the channels of the net w ork. Suc h messa ge flows can also b e s een in Fig. 7 . The dashed lines represent the data sharing within a config uration. This discipline of drawing • the internal ordering of even ts along the verticals and • the exter nal ordering, imp osed b y the flo ws, along the horizontal lines is of course, familiar from strand spac es, wher e the v erticals are the strands, and the hor izontals the bundles [29]. Our dia grams indeed b oil down to stra nd diagr ams whenever the netw ork configuratio ns are sing le no des connected by cy b er channels, and when the only flows are messa ges. This g raphic conv en tion for depicting the internal and exter nal o rdering of ev en ts go es ba c k to the early da ys of distributed computing resear c h, see e.g. [38, 44]. 3.5. Examples of pro cedures 3.5.1. Chal lenge r esp onse authentic ation pr oto c ols W e b egin a familiar sp ecia l case of a pro cedure: a proto col. A large family of challenge-res po nse authentication proto cols is s ubsumed under the template depicted on Fig. 6 . Bob want s to make s ur e that Alice is online. It is ass umed that Alice and Bob shar e s ome sort of a secret k AB , which allows them to define functions c AB and r AB such that • r AB x can be computed from c AB x using s AB , but • r AB x can not be computed from c AB x alo ne , without s AB . So Bob gener a tes a fresh v alue x , s ends the challenge c AB x , and if he rec eives the res po ns e r AB x back, he knows that Alice must hav e bee n o nline, bec a use she must have o riginated the res po ns e. The idea b ehind this template has b een discussed, e.g., in [48, 11, 56, 57]. The template instantiates the concrete pro to co l comp onents by refining the a bstract functions c AB and r AB to co ncrete implementations, which satisfy the ab ov e requir emen ts: e .g ., c AB may b e the encryption by Alice’s public key , and r AB may b e the encryption by Bob’s public key , p erhaps with Alice’s iden tit y . Recall from in Sec. 2.4 .1 that cyb er net w orks are dege nerate, in the sense that the actor s boil down to the principa ls. Alice’s and Bob’s unique actors a re thus s imply denoted b y A and B . 20 D. P a vlo vic and C. Meado ws 3.5.2. Two-factor authentic ation pr o c e dur e Next we descr ibe the first nontrivial pro ce dur e, over the actor - net w ork descr ibed in Sec. 2.4.2. It ca n b e viewed as a n extensio n of the s imple challenge-resp onse authentication. There, B ob a uthen ticates Alice using her knowledge of a s ecret s AB , which they b oth know. Her e Bob authenticates that that k nows a secret p A that B ob do es not k now, a nd that she ha s a security token S A , in this case a smart card. T he secret and the smart card are the “ t wo fa ctors“. This is the idea of the pro cedur e standardized under the name Chip Authentic ation Pr o gra mme (CAP) , a nalyzed in [23]. The desired run of the challenge-resp onse option of this pro cedur e is depicted on Fig. 7. W e ass ume that, prior to the display ed run, Alice the custo mer iden tified herself to Bo b the bank, and requested to b e a uthen ticated. Bob’s computer C B then ex tr acts a secr et s AB that he sha r es with Alice. This time, though, the shar ed secret is too long for Alice’s human I A to memorize, so it is is s tored in the smart card S A . Just like in CR proto co l above, Bob issues a challenge, suc h tha t the resp onse can only be formed using the secret. So Bob in fact authen ticates the smar t ca r d S A . He entrusts the smart car d S A with authenticating Alice’s human I A . This is done using the secret p A shared by I A and S A . The secret is s tored in b oth nodes . T o form the resp onse to Bob’s challenge, Alice forms the configuration Q b y inserting her car d S A int o the reader R . The configur ation Q requests that I A ent ers the secret PIN (Personal Identification Num ber ) p A befo re it forms the resp onse for B ob. There is no ch allenge from Q to I A , and th us no freshnes s guarantees in this authentication: any one who sees I A ’s resp onse can re play it at any time. Indeed, the hu man I A cannot be exp ected to p erform computations to authenticate herself: most of us hav e trouble even submitting just the sta tic PIN. The so lution is th us to hav e the card-rea der c o nfiguration Q computes the resp onse, which Alice relays it to B ob. The old PIN authentication is left to just convince Q that Alice’s hu man I A is ther e : Q tes ts p A , sent through the keybord ch annel from I A to the reader R , co incides with p A stored in the card S A , and then generates a keyed hash H s AB x using the shared secret s AB and the challenge x . This hash is display ed for Alice on the card rea der R as the resp onse r , whic h Alice then sends to her computer C A by the k eyb o ard channel, and further to C B by the cyber channel. This tw o-factor pr o cedure is thus more secure than the simple pas s w ord authentication of I A to D B bec ause • there is a fre s h c hallenge, a nd the a ttac ker ca nnot impers onate Alice just by recording o ne session (lik e phishermen do); • even in the option without the challenge, the secr et s AB , s ha red b et w een tw o computing devices, is generally str o nger than a h uman memora ble s ecret p A , and finally • the PIN authentication to the sma r t car d is not cryptogr aphically strong , but it is do ne o n a physical channel, which is ha rder to attack. If a thief comes in the p osses s ion of the s ma rt ca rd S A , he cannot use it without p A , stored in I A . This leads to the muggings, i.e. attacks where S A is stolen, a nd then I A is co er ced to disclose the PIN p A . The authors o f [23] point out that in tro ducing the p ortable, generic r eaders R simplifies for the attack er the verification that the num ber given to him by I A is indeed the co rrect p A . 3.5.3. Devic e handshake pr o c e dur e Going ba c k to Fig. 4, we describ e the desired r un on the Device Handshake. The r un beg ins by Alice bringing together the no des fo r the c onfiguration Q A . This means that she takes her device D A and Bob’s device D B int o her hand I A , to shake them together. W e also assume that the configur ation cont ains the no de S , whic h is the s ource of r andomness. This no de do es not corre s po nd to a physical ob ject, but embo dies the sour ce that is b eing sampled b y shaking . In reality , the tw o devices (i.e. their accelero meters) recor d the join t ac tion of shaking together, and sample the share d secret out of it. The method to achieve this is describ ed in [43 ], and we take it as g iven. The desire d run on the netw ork fr om Fig. 4 is depicted on Fig . 8. It co nsists of five flows, tr ig gered by Q A ’s shaking of the dev ic es: • (: x :) Q A shk ← − − h : x : i S , ca used by Q A ’s sampling of x from S ; • : f A : D A bio ← − − : f A : I A , simmultaneously caus ed by I A ’s sampling of I A ’s fing erprint f A ; • D · h (::) Q A i · E Q A vis − − → · h (::) Q A i · I B , wher e Q A shows I B how she shakes the de v ices to sample x ; Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 21 I A C A R C B Q vis kyb cyb S A ◦ ◦ ◦ p A , x p A , x s AB r r r := H s AB x vis kyb cyb p A p A = p A x x ◦ ◦ ◦ ◦ ◦ ◦ ◦ ◦ ◦ ◦ r r ◦ ◦ ν [ x ] r = H s AB x Fig. 7. Chip Authen tication P rogr a m (CAP) pro c edure I B I A S D A Q A D B ν [ x ] x [ (::) ] ok shk vis f A bio ◦ ◦ ◦ ◦ ◦ ◦ ◦ ◦ ◦ ◦ ◦ ok ◦ ◦ X vis X vis x x Fig. 8 . Device handshake pro cedure 22 D. P a vlo vic and C. Meado ws • h· X ·i D A vis − − → ( · X · ) I B , confirming to I B that D A received x and co rrect f A ; and • h· X ·i D B vis − − → ( · X · ) I B , confirming to I B that D B received x . Remark. Note that the third flow contains an example of a mess age ab out an ac tio n, alo ng the lines explained in Sec. 3.3, in the parag raph about repres en ting even ts as terms. Here Bo b’s human I A receives from Alice’s configuration Q A the visua l message [ (::) ] that she has s a mpled the r andomness. Tw o-round device handshak e. If b oth Alice a nd Bo b need to b e assured that a s e cret is shared, then the last tw o messages, where D A and D B confirm tha t they succ e eded to sample x , and one of them confirms that the fingreprint is co rrect, should be s e n t to b oth I A and I B . Running t w o rounds of the device handshake, with b oth Alice and Bob shak ing their device s in the acto r -netw o rk from Fig. 5, would require such pro ce dur e in ea ch of the t w o rounds. 4. Pro cedure Deriv ation Logic 4.1. Pro cedures are distributed predicates F ormal metho ds for soft ware engineering hav e b een built up o n Ho are’s slogan that “ Pr o gr ams ar e pr e dic ates” [33]. The view that computations can b e adequately approximated by their logica l descriptio ns, a nd prov en correct, was the g uiding principle of theory and prac tice of softw a re sp ecifications from the o utset in the 1960s [30]. The underlying as s umption is that s oft ware is r un within a single c omputer, with a global obser ver asserting the predicates. In contrast, the essence of a netw ork is that there is no g lobal o bserver. The even ts at ea ch no de may b e dir ectly observed only b y the principa l who controls that node. In addition, they may be indirectly observed alo ng an authentic channel tha t ends a t that node. The upshot is that each participant o f net w ork computation may obser ve different even ts, and asser t different predicates. Each of them sees just bits and pieces of the netw ork pr o cess. In most ca ses of interest, their co mmon goal is to co ordinate their observ ations, and arr ive at a coherent join t view of the even ts in which they jointly participate, so that they can a ll asser t the s ame predicate, which is the re q uired security prop erty . T ow ards this g oal, they use the channels b etw een them to exchange messages, and to obs erve ea ch other. In summary , our goa l is th us to extend formal metho ds from pr ograms as predicates to netw o rk pro cedures as families o f predicates, a sserted at different netw ork no des. The task of r e conciling these lo ca l assertions is usually forma lized as authentic ation . In this section, we gradually introduce the language and the a xioms that allow participants of netw o rk computations to annotate their lo cal observ ations by global predicates, building up from the basic communication axioms, tow ards authentication, and b eyond. 4.2. The language of PDL A statement o f PDL is in the form A : Φ, where A ∈ J is a principal, and Φ is a pr edicate asserted by A . The pr e dicate Φ is formed by applying log ical connectives to the atomic predic a tes, which ca n b e • a [ t ] P — meaning “ the even t a [ t ] P happ ened”; or • a [ t ] P b [ s ] Q — meaning “the event a [ t ] P happ ened b efore b [ s ] Q ”. Notation: Statemen ts assert ev en ts , and e v e nts describ e p oi n ts of time. Reca ll that the expres sions like a [ t ] P refer to p oints in time descr iptively , i.e. by sp ecifying what ha pp ened and where. As explained in Sec. 3 .3, this is a notatio na l abuse, but an imp or tan t one. The descriptions a [ t ] P are sometimes r efined to p a [[ t ]] P , which say that the even t a [ s ] to ok place at the c o nfiguration P , for some s ⊒ t , and that the ter m t o r iginates there. The ess ence of PDL. Here, the even t descr iptions like a [ t ] P and p a [[ t ]] P moreov er denote the asse r tions that the describ ed even t to ok place. The des criptions of pro cesses and of their runs ar e us ed as the predica tes to a nnotate them, and to r eason ab out them. T his no tational abuse is justified by the isomorphism of Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 23 pr o c ess exe cutions and their lo gic al annotations . This is the basic design dec ision on which PDL is bas e d: The descriptions of pr o c esses and of their runs as p artial or ders ar e use d as t he lo gic al assertions to annotate these pr o c esses and their runs. This is the formal implementation of the guiding pr inciple of PDL, explained in Sec. 1.4.2. This isomorphism do e s no t only simplify nota tion, but s ubstantially simplifies the logic that we work with. A statement in a n y proto col or pro cedure lo gic is an ass e rtion of a participa n t — made at a c ertain p oint of a run . In PCL, this dep endency on the run was ex pressed us ing dynamic mo dalities. In PDL, though, the pro ce s s expression within a mo dality isomorphic to a log ical formula. So instead o f • A : [ ψ ]Φ, saying that A knows that Φ is v alid after the ex ecution p oint ψ is reached, we can write • A : Ψ = ⇒ Φ, saying that A knows that Φ is v a lid whenever the descr iption Ψ o f ψ is v alid. The tw o for m ulas are semantically eq uiv alent b ecaus e the formula Ψ is a complete description of the pro cess ψ . The PDL ass e r tions thus usually app ear in the form A : Ψ = ⇒ Φ, where Ψ describ es A ’s view of the run, and Φ her conclusion abo ut it. The examples follo w. 4.3. Comm unication a xioms The statements o f PDL describ e the e vents that happ en in a run o f a pro cess, and their order. T he basic PDL statements are its axioms, which we describ e next. They are taken to b e v alid in all runs of all pro cesses. The o ther v alid statemen ts ar e der ived fro m them. 4.3.1. Origination The or igination axioms say that any message that is re c eived must hav e b een sent, and that a n y source that is sampleed must have b een emitted to . This has b een expla ine d e a rly in Sec.3. Mor e pr ecisely , a n y pr incipal that controls a configuration P w her e a messag e is received knows that it m ust hav e b een sent by so meo ne, no later than it w as received; a nd similar ly for a source that is sampleed. F ormally c P : ( · t · ) P = ⇒ ∃ X . h· t ·i X ( · t · ) P ( orig.m) c P : (: t :) P = ⇒ ∃ X . h : t : i X (: t :) P ( orig.s) 4.3.2. F r eshness In Sec. 3.2 w e explained the idea of mo deling random v a lues as the indeter minates in p olynomia l a lgebras of messages. The freshness axiom extends this idea to pro cesses, by requiring that each indeterminate x m ust be • fr eshly gener ate d by an action ν [ x ] b efore it is us ed anywhere; and • that it ca n only be used elsewher e after it has passe d in a message or a source. which fo rmally b ecomes c P : a [ t.x ] P = ⇒ ∃ X. ν [ x ] X a [ t.x ] P ( fresh.1) c P : ¬ ν [ x ] P ∧ a [ t.x ] P = ⇒ ∃ X. ν [ x ] X q hh· x ·ii X ( ( · x · )) P a [ t.x ] P ∨ ν [ x ] X q hh : x : ii X ((: x :)) P a [ t.x ] P ( fresh.2) where, using the easy subterm order ⊑ from Sec. 3.2, • hh· x ·ii X abbreviates ∃ t. x ⊑ t ∧ h· t ·i X , • (( · x · )) X abbreviates ∃ t. x ⊑ t ∧ ( · t · ) X , etc. 24 D. P a vlo vic and C. Meado ws 4.4. Authen tication axioms In classica l log ic, a statemen t may b e true or false. In cla ssical formal methods , an assertion ab out a com- putation is a ls o either true o r fals e, and it is ass umed that w e ca n observe which one it is. The idea is that we can, e.g. inspe ct the program v a riables in the debug mo de. In netw o rk computation, an as s ertion is still either true o r false — yet no ne of the participants may be able to o bs erve whether it is true or false. E.g ., when Alice receives a message o n a cyb er c hannel, she may not be able to verify whether the statement “ This message is fr om Bob” is true or false. The pr o cess of verifying suc h non- lo c a l sta tements by loca l means is authentic ation . In our model, there ar e tw o fo r ms of authen tication: • int eractions alo ng authen tic channels, and • challenge-resp onse a uthen tication. 4.4.1. Inter actions along authentic channels An authentic channel allows at least one of the participants to observe not only the even ts on their own end of the channel, but also on the other end. So there are four types of authentic channels, supp orting the following assertions: c P : h· t ·i P ( · t · ) Q ( auch.m.1) c Q : h· t ·i P ( · t · ) Q ( auch.m.2) c P : h : t : i P ( : t :) Q ( auch.p.1) c Q : h : t : i P ( : t :) Q ( auch.p.2) Channels that sa tisfy auch.m.1 o r auch.p.1 ar e called write -authentic; channels that satisfy auch.m.2 or auch.p.2 a re called r e ad -authentic. Here ar e some ex amples from e a ch family: • A k eyb oard channel guarantees to the sender that the device at which she is t yping is receiving the message, and th us satisfies (auch.m.1) . • A visual c hannel used for sending a messa ge allows the receiver to see the sender, and satisfies (auch.m.2) . • When m y fingerpr in ts ar e taken, I obs e r ve that they are tak en, and can see who is tak ing them, so this biometric channel satisfies (auch.p.1) . • Moreov er, the p ers o n taking my fingerprints a lso observes that they ar e tak ing my finger prints, so (auch.p.2) is also satisfied. • If a v isual channel is used for surveying, then the surveyor sees wher e the display a ppea rs, and th us satisfies (auch.p.2) as well; etc. Besides these asser tions abo ut the order o f even ts, some a uthen tic channels supp ort o ther asser tions. They are usually applicatio n sp ecific, a nd we impo se them a s pro cedure specific axioms. Authen ticit y of self-s ampling. One particular authenticit y axiom worth mentioning is the statement that the self-observ ation channel is a uthen tic, at least for sampling the s ampling actions , i.e. c P : : (::) P : P = ⇒ (::) P ( cog) In other words, “ If I observe that I hav e obser ved something, then I have rea lly obser v ed something”. This is the PDL version of Desc artes’ authentication of the w orld: “Co gito, er go sum” . 4.4.2. Chal lenge- r esp onse authentic ation The challenge-res po ns e axio m is in the form c P : Lo cal P = ⇒ Global P Q ( cr) where, using the notation from Sec. 4 .3.2 Lo cal P = ν [ x ] P · c P Q x · P · r P Q x · P Global P Q = ν [ x ] P · c P Q x · P · c P Q x · Q q hh· r P Q x ·ii Q · r P Q x · P T rans la ted into words, (cr) says that the owner c P of the configuration P knows that Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 25 P ν [ x ] h · c P Q x · i hh · r P Q x · ii (( · c P Q x · )) ( · r P Q x · ) Q = ⇒ Fig. 9 . The graphic view of (cr) a xiom P ν [ x ] h· x ·i hh · ς P x · ii (( · x · )) ( · u | V Q .u.x · ) X = Q 1 2 3 4 Fig. 10. Challenge - resp onse using signa- tures • if he g enerates a fresh x , sends the challenge c P Q x , and receives the resp onse r P Q x , • then Q must hav e received a mess age containing c P Q x a fter he sent it, and then she must have sen t a message containing r P Q x b efore he received it. Using (cr) , fro m certain obser v ations o f the lo cal e ven ts at P , the principal c P can th us draw the conclusions ab out cer tain non-lo cal even ts at Q , which he cannot dir ectly o bs erve. Fig. 9 shows depicts this r easoning diagramma tica lly . This axio m should b e v ie w ed as an assertion ab out the functions c P Q and r P Q . They m ust b e suc h that Q can compute r P Q x from c P Q x , but no one else can do it. 5 Remark. The (cr) axiom, and the cor r esp onding proto co l template, displayed on Fig. 9, has b een one of the cr ucia l to ols o f the Pr oto col Deriv atio n Logic, a ll the way sinc e [48, 11], through to [5 7]. 5. Examples of reasoning in P DL 5.1. On the diagrammatic metho d In its diagra mmatic form depicted on Fig. 9 , axiom (cr) says that the verifier P , observing the lo cal path on the left, can derive the path aro und the non-lo cal actions on the right . This pattern of rea s oning res e m bles the categ orical practice o f diagr am chasing [42, 54]. Catego rical diagrams ar e succinct enco dings of lengthy sequences of equations. Just lik e the tw o s ides of the implication in (cr) corr esp ond to t w o paths a round Fig. 9, the tw o sides of an equa tion ar e repr e s en ted in a ca teg orical dia g ram as tw o paths aro und a face o f that diagram. The comp onents of the terms in the equations corres po nd to the individual arr ows in the paths. The equatio ns can b e fo r mally recons tr ucted from the diagrams. Moreover, the diag rams can b e fo rmally combined into new pro o fs. The a lgebraic s tructures are th us formally transformed in to g eometric patterns. After some practice, the ge o metric intuitions beg in to guide algebraic constructions in the for mal la ng uage of dia g rams. W e a pply a similar stra tegy to PDL. 5.2. Cryptographic (single-factor) authentication W e begin with a v ery simple ex ample of diagrammatic rea s oning, present a lready in [48]. 5 In the cases when c P Q and r P Q are based on a secret shared b et w een P and Q , then P can compute r P Q as well. In suc h cases, the soundness of (cr) depends on c P ’ s observ ation that P has not done that. 26 D. P a vlo vic and C. Meado ws Theorem. The functions c P Q x = x r P Q x = ς Q x implemen t (cr) , provided that the abstr a ct signature function ς satisfies the following ax ioms: (a) ς Q u = ς Q v = ⇒ u = v , i.e., ς Q is injective, (b) p hh ς Q t ii X = ⇒ X = Q , i.e., ς Q t must originate fro m Q , (c) V Q .u.t ⇐ ⇒ u = ς Q t , i.e., the predicate V Q is s a tisfied just fo r the pair s u, t where u = ς Q t , and that these axio ms a re known to the principal Bob = c P . Pr o of. T o prove the cla im, we chase the diagram on Fig. 10. The n um bere d arrows ar ise from the following steps: 1. Bob = c P observes ν [ x ] P h· x ·i P · r | V Q rx · , i.e. after sending a fresh v a lue x , he receives a resp onse u which pas ses the verification V Q rx . 2. Using the axioms (c) and (o rig.m) , he co ncludes that there is some X such that · V Q x · X · r | V Q rx · P . 3. Using (fresh.2) he further derives that for the s ame X holds h· x ·i X (( · x · )) X · V Q x · X . 4. Using (a ) and (b), Bob concludes that V Q x must hav e or iginated from Q . Bob can, of cours e, o nly b e sur e that Q was online b etw een his h · x ·i P and · r | V Q rx · , and not that Alice = c Q rea lly intended to resp ond to his challenge. I t is well known that this form of authentication is o p en to imp ersonatio n, since r = V Q x contains no r eference to Bob or to P . 5.3. P e rv asive (t w o-factor) authe ntication Next we describ e how Bob the bank a uthen ticates Alice the customer in the CAP pro cedure. Theorem. The pro cedure o n Fig . 7 implements authentication, i.e . satisfies (cr) , pr ovided that the following assumptions a re true, a nd known to Bob: (a) H u = H v = ⇒ u = v , i.e., H is injective; (b) p hh s AB ii X = ⇒ X = S A ∨ X = C B , i.e., s AB m ust or iginate from S A or C B ; (c) p hh p A ii X = ⇒ X = I A ∨ X = S A , i.e., p A m ust origina te fr o m I A or S A ; (d) · H s AB x · Q = ⇒ · p A , x · Q · H s AB x · Q ∧ p A = p A , i.e., S A and R are ho nest. Pr o of. Pr ior to the display ed execution, Alice is a ssumed to hav e sent to Bo b her iden tit y , a nd a r equest to b e authenticated. F ollowing this request, Bob’s co mputer C B has extracted the secr et s AB from a s tore, which he will use to verify that S A has gener ated the respo nse. T o prov e the cla im, we chase the diagra m on Fig. 11. The enumerated steps in the diagr a m chase corres p ond to the following steps in Bob’s rea soning: 1. Bob observes ν [ x ] C B h· x ·i C B · H s AB x · C B . 2. Using (or ig.m) he concludes that there is some X such that h· H s A x ·i X · H s AB x · C B . 3. Using (fresh.2) he further derives that for the s ame X holds h· x ·i C B ( ( · x · )) X · H s AB x · X . 4. By (a) and (b), from the observ ation that he did not use s AB , Bob concludes that H s AB x must have originated in a configur ation Q containing S A . 5. By (c), · p A · I A · p A · Q p A = p A H s AB x , where the last action abbreviates r := H s AB x , and we write o ut r as H s AB x in the rest of the diagram. (See Rema rk b elow.) 6. Since Q had to a lso rece ive x b efor e computing the r esp onse in · p A , x · R H s AB x follows b y (d). So · p A · Q from 5 is · p A , x · R . 7. By (or ig-m) , there is Y with · p A , x · Y · p A , x · R . By (e), · p A · I A from 5 m ust b e · p A , x · I A . Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 27 I A C A R C B Q S A ν [ x ] h· x ·i ( · x · ) h · p A ,x · i ( · p A ,x · ) p A s AB ( H s AB x ) ( p A = p A ) h · H s AB x · i hh · H s AB x · ii (( · x · )) ( · H s AB x · ) X 1 2 3 4 5 6 7 8 8 h : H s AB x : i ( : H s AB x : ) 9 10 Fig. 1 1. B ’s reasoning in CAP 8. The fres h v a lue x ha s thus be e n sent to Q b y I A . It follows that in 2 a nd 3 above must be X = I A . 9. Since A controls S A and I A , and S A ∈ Q g enerated the res po ns e H s AB x , o nly I A could have sampled H s AB x alo ng the visua l channel. 10. Since A cont rols I A and C A , only I A could hav e s en t H s AB x to C A along the keyboar d channel. These logical steps suffice to assure Bob that if he obser ves the lo cal flow on the right in Fig . 11, then the non-lo cal flow along the external b ounda r y , a ll the way to the left side of the diagra m a nd back, m ust hav e taken place. Comparing this diagra mmatic conclusion with the pattern o f (cr) on Fig. 9, we see that Bob has proven an instanc e of authentication. More explicitly , Bob’s co nclusion in Fig. 11 is h· x ·i C B ( · x · ) C A h· x ·i C A ( · x · ) I A · p A , x · I A · p A , x · R ( p A = p A ) Q H s AB x Q : H s AB x : R : H s AB x : I A · H s AB x · I A · H s AB x · C A · H s AB x · C A · H s AB x · C B where we also a dded the tr ivial relay flows o mitted from the figure, na mely • h· x ·i C A cyb − → ( · x · ) I A on the wa y out, and • · H s AB x · I A kyb − → · H s AB x · C A on the wa y back. Again, it is clear that this conclusion is clea rly an instance of (cr) a nd thus realizes authentication. 28 D. P a vlo vic and C. Meado ws I B I A S D A Q A D B ν [ x ] h : x : i (: x :) x, ok h· [ (::) ] · i x, ok ( · [ (::) ] · ) shk vis h : f A : i bio ( : f A : ) h· X ·i ( · X · ) ( · X · ) h· X ·i vis vis Fig. 12. B ’s view of A ’s round of device handshake Remarks. The reader may note that the stor e r , to which the res po ns e H s AB x is assigned at run time, was present in Fig. 7, but elided in Fig. 11. This is a minor quirk her e , but we w anted to adher to the custom established in the informal pro toc o l a nalyses, and propag ated, e.g. through the stra nd s pace notation: stor es and pr ogram v aria bles are by conv en tion a voided, and denoted b y the ter ms as s igned to them at r un time. Although such a term, strictly sp eaking, do es not have a static v alue, a nd denoting the stor e s rea dy to receive it when it is ev alua ted by its unev aluated expres sion is a buse of notation — it seems to b e an eminen tly reasona ble abus e , since it displays the path of the term dur ing the run, whereas the names of all the lo ca l stores rea dy to rec e ive it, only conceal its path. So the diagr ammatic conv en tion wins the da y . Honesty assumptio n . It w ould be easy and na tur al to eliminate the assumption that S A is honest by storing p A also at I A , and including it into the resp onse. That would reduce the ab ov e reasoning to “ S A has b een on the path of the message ” and a dded a separate thread ” I A has also b een on the path of the message” . W e chose to pr esent the above version as slig htly more informative, alb eit slig h tly weak er. Do es Bob nee d to b e authenticated? In practice, the attack ers us ua lly imper sonate Bob, to s teal Alice’s credential and use that to imp ersona te her to the actual Bo b, the bank. The mos t freq uen t for m of that attack is, o f cour se, phishing. Two factor authentication is devised to av oid that: her e Alice do es not give her credentials to Bob, but to the smart card rea de r . Why is that b etter? Ho w do es Alice know that reader R ’s r equest for PIN is authentic? She se es on the visua l channel that the only card in R is S A , which she had put there herse lf. This is a simple but typical example of use of an authentic channel. 5.4. Device pairing by handshake F or the final example, we re tur n to the device handshake pro cedure. F or reasons of space, we omit pr o of o f the theor em, but pre s en t that dia gram that is used to supply the pro of. Theorem. Up on the co mpletion o f a run of the pro cedure des crib ed in Sec. 3.5 .3, Bob can b e s ure that his and Alice’s device share a key , provided that he knows that the following assumptions a re v a lid: Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 29 (a) c P : h· [ a Q ] ·i Q vis − − → ( · [ a Q ] · ) P , i.e. the vis ua l channel s atisifies (auch.m.2 ) at le a st for events; (b) (: x :) Q A = ⇒ x ∈ Γ D A ∩ Γ D B , i.e., Q A distributes the same v alue to D A and D B ; (c) (: t :) Q A = ⇒ ν [ x ] S h : x : i S (: t :) Q A ∧ t = x , i.e. Q A is honest ; (d) h· X ·i D A = ⇒ o k D A ∧ : f A : I A : f A : D A h · X ·i D A , i.e. D A is honest; and (e) h· X ·i D B = ⇒ o k D B , i.e. D B is honest. Bob’s formal reasoning is displayed o n Fig 12. 6. Conclusion, discussion, and some last min ute philosoph y Summary W e hav e presented a logical framework for reasoning ab out security of proto cols that make use of a heterog eneous mixture of humans, devices , and channels. W e hav e shown how different prop erties of channels and config urations can b e expresse d and reaso ned ab out within this framework. A key feature o f this framework is that it supp orts explicit reasoning ab out both the str uctur e o f a pr oto col a nd the cont ributions made by its v arious comp o nent s, using a combination of diagra mmatic a nd logical metho ds. Beca use of this, we b elieve that our approach can b e particular ly useful in giving a more rigor ous foundation for w hite- bo a rd discussions, in whic h proto cols ar e us ually display ed g raphically . By annotating the diag ram with the pr o of using the metho ds demonstrated in this paper , formal reasoning could b e brought to bea r at the very ea rliest states of the design pro cess. But we also b elieve that it should be po ssible to dev elop to ol suppo r t as w ell, in which a proo f engine w ould execute the logic, and the pro of itself would b e demonstrated on a gra phical template. Bo th av en ues ar e a que s tion for future resear ch. Post ho c er go pr opter ho c? Althoug h we sp eak of co mplete runs, a s sp ecified in Def. 3 .5, and the information flows seem completely display e d in such runs, it is alwa ys p ossible to r aise the question w he ther a demonstrated tempor al order of events r eflects their ca usal o rder. Ca n it b e that Bob has received the same messa ge tha t Alice had s en t, but that by some coincidence Ca rol had sent a n ident ical messag e, and that Bo b actually r eceived Caro l’s mes sage? If the tw o messages a r e really identical, how can we tell? Should we try to dis tinguish the causal connections from temp o ral coi ncidences? Mo re specifi- cally , would it b e p ossible to refine PDL by working with s tatemen ts that would sp ecify not just the order of even ts, but also which interactions o ccur red thr ough w hich c hannels? The idea would thu s be to discern whether Bob has rece ived Alice’s or Carol’s message by following the messa ges as they trav el from c hannel to channel, and s e eing which one go e s wher e. W e believe that this would just complicate logic, without bringing essentially mo re informatio n. Even if we could follow tw o messa ges, with the same payload s ay m 1 and m 2 on their res pective paths acro ss the net work, could we be sure that their paths nev er cross? Net works a r e busy places, a hop from no de to node may concea l man y in termediary steps, and m 1 ’s hop a 1 → b 1 may pass through an in visible no de x at the same time a s m 2 ’s hop a 2 → b 2 passes through x . If tha t ha ppens, then m 1 may emerge a t b 2 and m 2 at b 1 . Or the other wa y a round. W e will never know. It will remain uncertain which of the tw o messages has reached Bob in the end. Logic has no business chasing the ghos t o f causality . The b est we can do is describ e the order of the even ts. Partially order ed m ultisets will remain a r obust foundation for reas o ning abo ut netw ork interactions and pro cedure s for many applications to come. Can w e reall y mo del s o cial i n teractions and computations wi thi n the same mo del? People a re not computers and so c iet y is not a computer netw o rk. How could I ever predict the b ehavior of a so cial group, when I am una ble to predict the behaviors within my own family? Sometime I don’t even understand m y own behavior. Humans are hop eless ly irrational. E nd of the story . But science has s tr ange tric ks. It is una ble to mo del the tra jectory o f a single particle in the air, but it mo dels hurricanes and pr edicts weather. Similarly , the p olling exp erts and the web advertisers ha v e developed impressive tec hniques to predict and influenc e the b ehaviors of la rge groups of p eople with a significant precision, a lthough no one seems to b e able to pr edict or influence what an y particular indiv idua l will do. Most sciences try to mo del rea lity . But p eople do not ob ey mo dels, groups of p eople do not ob ey mo dels, 30 D. P a vlo vic and C. Meado ws so the sciences concerned with p eople and with so cial groups larg ely to ok e x ception to the mo deling task. It turns out, thoug h, that the task may beco me easier when so cial net w orks are interlea v ed with netw orks of computers a nd devices, and when peo ple a r e mo deled together with other so cial and computational ac tors. Can it be that mo dels better fit p eople beca us e p eople b etter fit mo dels? Ac knowledgement. The first author would like to thank W olter Pieters [61] for intro ducing him to Bruno Latour’s ideas abo ut actor -netw o rks. References [1] M. A badi and P . Rogaw ay . R econciling t w o views of cryptograph y (the computational soundness of f ormal encryp- tion). J. of Cryptolo gy , 15(2):103–127, 2002. [2] Mart ´ ın Abadi, Bruno Blanc het, and Hub ert Comon-Lundh. Mo dels and pro ofs of proto col securit y: A progress repor t. In Ahmed Boua j j ani and Oded Maler, editors, CA V , v olume 5643 of L e ctur e Notes in Computer Scienc e , pages 35–49. Springer, 2009. [3] Matthias Anlauff, Dusk o Pa vlo vic, Ri c hard W aldinger, and Stephen W estfold. Proving authent ication prop erties in the Protocol Deriv ation Assistant. In Pierpaolo D egano, Ralph K ¨ usters, and Luca Vigano, editors, Pr o c e e dings of FCS-ARSP A 2006 . ACM, 2006. [4] Gilles Barthe, Daniel Hedin, Sant iago Zanella B´ e guelin, Benjamin Gr´ egoire, and Sylv ain Heraud. A machine- c hec k ed formalization of sigma-proto cols. In CSF , pages 246–260. IEEE Computer So ciet y , 2010. [5] Da vid A. Basin, Manuel Clav el, and Mari na Egea. A decade of model- driven security . In Ruth Breu, Jason Crampton, and Jorge Lob o, editors, SACMA T , pages 1–10. ACM, 2011. [6] Giampaolo Bella. F ormal Corr e ctness of Se curity Pr oto c ols . Information Securit y and Cr yptograph y . Springer V er lag, 2007. [7] Y o chai Benkler. The We alth of Networks: How So ci al Pr o duction T r ansforms Markets and F r e e dom . Y ale Univer- sity Press, 2006. [8] Bruno Blanchet . A computationally sound mechan ized prov er for security proto cols. IEEE T r ans. Dep endable Se c . Comput. , 5(4):193 –207, 2008. [9] Matt Blaze. T ow ard a broader view of security protocols. In Br uce Christianson, Bruno Cris p o, James A. Malcolm, and Michael Roe, editors, Se curity Pr oto c ols Workshop , vo lume 3957 of L e ctur e N otes in Computer Scienc e , pages 106–120. Springer, 2004. [10] Ileana Buhan, Bas Bo om, Jero en Doumen, Pieter H. Hartel, and Raymond N. J. V eldhuis. Secure pairing with biometrics. IJSN , 4(1/2):27–42, 2009. [11] Iliano Cerv esato, Catherine Meado ws, and Dusko Pa vlo vic. An encapsulated authen tication logic for r easoning about key distri bution protocols. In Joshu a Guttman, editor, Pr o c e e dings of CSFW 2005 , pages 48–61. IEEE, 2005. [12] V. Cortier, S. Delaune, and P . Lafourcade. A surv ey of algebraic prop erties used in cryptograph ic protocols. J. Comput. Se cur. , 14(1):1–43, 2006. [13] V ´ eronique Cortier and Stev e Kr emer, editors. F ormal Mo dels and T e chniques for Analyzing Se curity Pr oto c ols , v olume 5 of Cryptolo gy and Information Se curity Series . IOS Press, 2011. [14] V ´ eronique Cortier, Steve Kremer, and Bogdan W arinsch i. A survey of symbolic methods in computational analysis of cryptographic systems. J. Autom. R e asoning , 46(3-4):225–25 9, 2011. [15] A. D atta, A. Derek, J. Mitchell, and A. Ro y . Proto col Composition Logic (PCL). Ele ctr onic Notes in The or etic al Computer Scienc e , 172:311–358, April 2007. [16] An upam Datta, Ant e Derek, John M itc hell, and Dusko Pa vlovic. Secure proto col comp osition. E. Notes in The or. Comp. Sci. , pages 87–114, 2003. [17] An upam D atta, Ante Derek, John Mitchell, and Dusko Pa vlo vic. A deriv ation system and compositional l ogic for securit y protocols. J. of Comp. Se curity , 13:423–482 , 2005. [18] An upam Datta, Ante Derek, John C . Mi tc hell, and Dusko Pa vlovic. A deriv ation system for security protocols and its logical formalization. In Dennis V olpano, editor, Pr o c e ed ings of CSFW 2003 , pages 109–125. IEEE, 2003. [19] Y evgeniy Do dis, Leonid Reyzin, and Adam Smi th. F uzzy extractors: How to generate strong k eys f rom biometrics and other noisy data. In Christian Cac hin and Jan Camenisch, editors, EUR OCR YPT , volume 3027 of L e ctur e Notes in Computer Scienc e , pages 523–540. Springer, 2004. [20] Dann y Dolev and Andrew C. Y ao. On the securit y of public ke y protocols. Information The ory, IEEE T r ansactions on , 29(2):198– 208, 1983. [21] Marco Dorigo and Thomas St ¨ utzle. Ant c olony optimization . MIT Press, 2004. [22] S. N. Dorogo vtsev and J. F. F. Mendes. Evolution of Networks: F r om Biolo gica l Net s to the Internet and WWW . Oxford Univ ersity Press, 2003. [23] Saar Drimer, Stev en J. M urdoch, and Ross J. Anderson. Optimised to f ail: Car d readers for online banking. In Roger Dingledine and Philipp e Golle, editors, Financial Crypto gr aphy , v olume 5628 of L e ctur e Notes in Computer Scienc e , pages 184–200. Springer, 2009. [24] Nancy Durgi n, John Mi tc hell, and Dusk o Pa vlo vic. A comp ositional logic for proving securit y prop erties of proto- cols. J. of Comp. Se curity , 11(4):677–7 21, 2004. [25] Nancy Durgin, John C. Mitchell, and Dusko Pa vlovic. A composi tional logic for proto col correctness. In Stev e Sc hneider, editor, Pr o ce e dings of CSFW 2001 , pages 241–255 . IEEE, 2001. Actor-net w ork pro cedures:Modeli ng m ulti-factor authent ication, device pair i ng, so cial inte ractions 31 [26] D. Easl ey and J. Kleinberg. Ne tworks, Cr owds, and Markets: Re asoning Ab out a H i ghly Conne c te d World . Cam- bridge Unive rsity Press, 2010. [27] Carl E l lison. Ceremony design and analysis. Cryptology ePrint Ar c hiv e, Rep ort 2007/399, October 2007. [28] San tiago Escobar, Catherine Meadows, and Jos´ e Meseguer. Maude-NP A: Cryptographic protocol analysis mo dulo equational prop erties. In Alessandro Aldini, Gilles Barthe, and Rob erto Gorrieri, editors, F OSAD , volume 5705 of L ectur e Notes in Computer Sc ienc e , pages 1–50. Springer, 2007. [29] Ja vier Tha y er F abrega, Jonathan H er zog, and Josh ua Guttman. Strand spaces: What make s a security proto col correct? Journal of Computer Security , 7:191–230, 1999. [30] Robert W. Fl oyd. Assigning meaning to programs. In J. T. Sch w artz, editor, Pr o c e e dings of the Symp osium on Applie d Maths , volume 19, pages 19–32. AMS, 1967. [31] George A. Gr atzer. Unive rsal Algebr a . V an Nostrand Pr inceton, N .J.,, 1968. [32] Da vid Harel, Dexter Kozen, and Jerzy Tiuryn. Dynamic L o gic . M IT Press, Cambridge, MA, 2000. [33] C. A. R. Hoare. Programs are predicates. Phil. T r ans. R. So c. L ond. , A 312:475–489, 1984. [34] Jaap-Henk Ho epman. Ephemeral pair ing on anonymous netw or ks. In D ieter Hutter and Markus Ul lmann, editors, SPC , v olume 3450 of Le ctur e Notes in Computer Scie nce , pages 101–116. Springer, 2005. [35] Chris K ar lof, J. D. Ty gar, and David W agner. Conditioned-safe ceremonies and a user study of an application to web authen tication. In Pr o c e e dings of t he 5th Symp osium on U sable Privacy and Security , SOUPS ’09, pages 38:1–38:1, New Y ork, NY, USA, 2009. ACM. [36] Ric hard A. Kemmerer, Catherine Meado ws, and Jonathan K. Mill en. Three system for cryptographic protocol analysis. J. Cryptolo gy , 7(2):79–13 0, 1994. [37] Arun Kumar, Nitesh Saxena, Gene Tsudik, and Ersin Uzun. A comparativ e study of secure device pairi ng m ethods. Pervasive Mob. Comput. , 5:734–749, Decem ber 2009. [38] Leslie Lamp ort. Time, clo ck s, and the or dering of even ts in a distributed s ystem. Commun. ACM , 21(7):558–565, 1978. [39] Bruno Latour. R e assembling the So cial: A n Intr o duction to A ctor-Network The ory . Oxford Universit y Press, 2005. [40] Sv en Laur and Kaisa Nyb erg. Efficient mut ual data authen tication using manually authen ticated s trings. In David Po int c hev al, Yi Mu, and Kefei Chen, editors, CA N S , volume 4301 of L e ctur e Notes in Computer Scienc e , pages 90–107. Springer, 2006. [41] Sv en Laur and Sylv ain P asini. User- aided data authen tication. IJSN , 4(1/2):69–86 , 2009. [42] Saunders M ac Lane. Cate g ories for the Working Mathematici an . Number 5 in Graduate T exts in Mathematics. Springer-V erlag, 1971. [43] Rene Ma yrhofer and Hans Gellers en. Shak e well b efore use: In tuitiv e and secure pair i ng of mobile devices. IEEE T r ans. Mob. Comput. , 8(6):792–80 6, 2009. [44] D. McCull ough. A hookup theorem for m ultilev el security . IEEE T r ansactions on Softwar e Engineering , 16(6):563– 568, 1990. [45] Catherine Meadows. The NRL Proto col Analysis T ool. In Pr o c e e dings of the Computer Se c urit y F oundations Workshop , page 227. IEEE, 1991. [46] Catherine Meadows. A mo del of computation for the NRL P r otocol Analyzer. In Pr o c e e dings of the Computer Se curit y F oundations Workshop , pages 84–89. IEEE, 1994. [47] Catherine Meado ws. The NRL Proto col Analyzer: A n o v erview. J. L o g. Pr o gr am. , 26(2):113– 131, 1996. [48] Catherine Meadows and Dusk o Pa vlo vic. Deriving, attac king and defending the GDOI proto col. In Pete r Ry an, Pierangela Samarati, Dieter Gollmann, and Refik M olv a, editors, Pr o c e e dings of ESORICS 2004 , vo lume 3193 of L ectur e Notes in Computer Sc ienc e , pages 53–72. Springer V er l ag, 2004. [49] Catherine Meado ws, Radha Poov endran, Dusko Pa vlo vic, LiW u Chang, and Paul Syverson. Distance b ounding protocols: authen tication logic analysis and collusion attac ks. In R. Poov endran, C. W ang, and S. Roy , editors, Se cur e Lo ca lization and Time Sy nchr onization in Wireless A d Ho c and Sensor Networks . Springer V erlag, 2006. [50] Mark Newman. Ne tworks: An Intr o duction . Oxford Universit y Pr ess, 2010. [51] Long Hoang Nguyen and Andrew Willi am Rosco e. Authent ication protocols based on low-bandwidt h unsp o ofable c hannels: a comparativ e survey . Journal of Computer Se curity , 2011. to appear. [52] Bernhard O. Palsson. Sy stems Biolo gy : Pr op erties of R e c onstructe d Networks . Cambridge Uni versity P r ess, 2006. [53] Sylv ain Pasini and Serge V audenay . Sas-based authen ticated key agreemen t. In M oti Y ung, Y evgeniy Dodis , Aggelos Kiayias, and T al Malkin, editors, Public Ke y Crypto gr aphy , v olume 3958 of Le ctur e Notes in Computer Scienc e , pages 395–409. Springer, 2006. [54] Dusk o P a vlo vic. M aps I I: Chasing diagrams in categorical proof theory . J. of the IGPL , 4(2):1–36 , 1996. [55] Dusk o Pa vlo vic. The unreasonable ineffectiv eness of security engineering: An o v erview. In Jos´ e Luiz Fiadeiro and Stefania Gnesi, editors, Pr o c e e dings of IEEE Confer enc e on Softwar e Engine ering and F ormal Metho ds, Pisa, Italy, 2010 , pages 12–18. IEEE, 2010. [56] Dusk o Pa vlo vic and Catherine Meadows. Deriving secrecy pr operties in k ey establishmen t pr otocols. In Dieter Gollmann and Andrei Sabelf eld, editors, Pr o c ee dings of ESORICS 2006 , v olume 4189 of L ectur e Notes in Computer Scienc e . Spri nger V erlag, 2006. [57] Dusk o Pa vlovic and Catherine Meado ws. Bay esian authen ticat ion: Quan tifying security of the Hanc k e-Kuhn pro- tocol. E. Notes in The or. Comp. Sci. , 265:97 – 122, 2010. [58] Dusk o Pa vlo vic and Douglas R. Smith. Comp osition and refinement of behavioral sp ecifications. In Automate d Softwar e Engine ering 2001. The Sixte ent h International Confer enc e on Automa te d Softwar e Engine ering . IEEE, 2001. [59] Dusk o Pa vlo vic and Douglas R . Smith. Guarded transitions in evolving specifications. In H. Kirchner and 32 D. P a vlo vic and C. Meado ws C. Ringeissen, editors, Pr o c e e dings of AMAST 2002 , v olume 2422 of L ectur e Notes in Computer Scie nc e , pages 411–425. Springer V erl ag, 2002. [60] Chris P eltz. W eb services orch estration and c horeograph y . Computer , 36:46–52, October 2003. [61] W olter Pieters. Represen ting h umans in system s ecuri ty mo dels: An actor-netw ork approac h. Journal of Wireless Mobile Networks, Ubiquit ous Computing, and Dep endable Applic ations , 2(1):75–92, 2011. [62] V aughan Pratt. Mo delling concurrency with partial orders. Internat. J. Par al lel Pr o gr amming , 15:33–71, 1987. [63] J. H. Saltzer, D. P . Reed, and D. D. Clark. End-to-end argumen ts in system design. ACM T r ans. Comput. Sy st. , 2:277–288, No v em ber 1984. [64] F rank Sta jano, F ord-Long W ong, and Bruce Christianson. Multichann el protocols to prev en t rela y attacks. In Radu Sion, editor, Financial Crypto gr aphy , volume 6052 of L e ctur e Notes in Comp uter Scienc e , pages 4–19. Springer, 2010. [65] Serge V audena y . Secure commu nications ov er insecure channels based on s hort authen ticated strings. In Vi ctor Shoup, editor, CR YPTO , volume 3621 of L e ctur e Notes in Computer Science , pages 309–326. Springer, 2005. [66] Duncan J. W atts. Six De g re es: The Scienc e of a Conne cte d Age . W. W. Norton, New Y ork, 2003. [67] Barry W ell man, Janet Salaff, Dimitri na Dimitrov a, Laura Garton, Mi lena Gulia, and Caroline H aythorn th waite. Computer netw orks as s ocial netw orks: Collabor ativ e work, telework, and vir tual communit y . Annual R eview of So ciolo g y , 22(1):213–238, 1996.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment