A New Trusted and Collaborative Agent Based Approach for Ensuring Cloud Security
In order to determine the user's trust is a growing concern for ensuring privacy and security in a cloud computing environment. In cloud, user's data is stored in one or more remote server(s) which poses more security challenges for the system. One o…
Authors: Shantanu Pal, Sunirmal Khatua, Nabendu Chaki
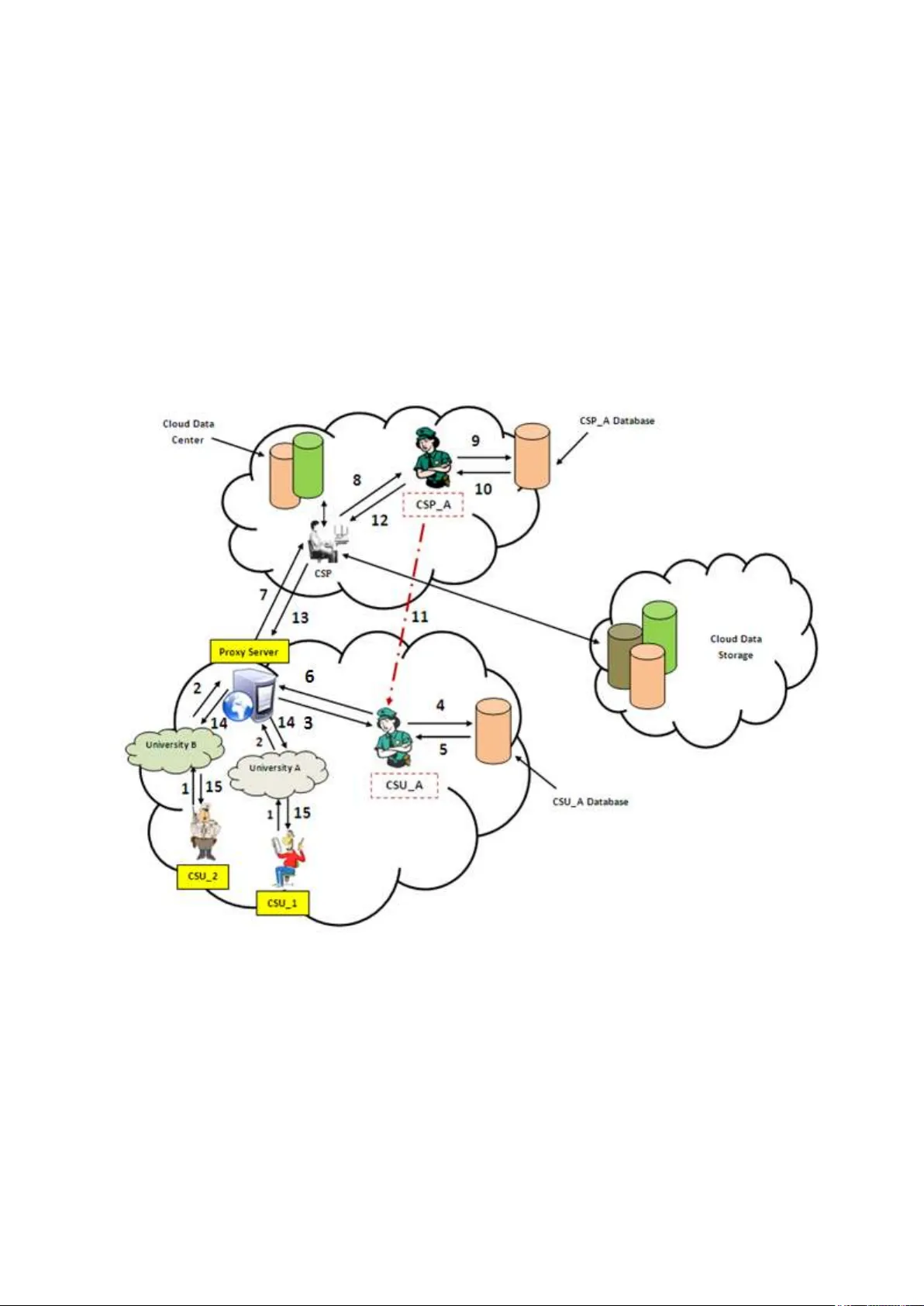
A New Trusted and Collabora tive Agent Bas ed Approach for Ensuring Clo ud Security 1 Shan tan u P al , 2 Suni r mal Kh atua , 3C or r esp on di ng Aut ho r Nab end u C hak i, 4 Sug at a S any al [1, 2 , 3 ] 92 A. P . C . R oad , Un ive rsi ty of Cal cut ta, Ind ia 4 Tata In sti tut e of Fund ament al Re sear ch, Ind ia . 1 shan tan u. smi t@gma il .com ; 2 engg ni mu_ju @ yahoo .com; 3 naben du@ ieee .o rg; 4 sany al@ ti fr.r es.i n Abstract: In order to determine the user’s trust is a growing concern for ensuring privacy and security in a cloud com puting environment. In cloud, user’s dat a is stored in one or more remote server(s) which poses more securit y challenges for the syste m. One of the most important concerns is to protect user’s sensitive information from other users and hackers that may cause data leakage in cloud storage. Having this securit y challenge in mind, this paper focuses on the development of a more secure cloud environment, to determine the trust of the service r equesting authorities b y using a novel VM (Virtual Machine) monitoring s ystem. Moreover, this research aims towards proposing a new trusted and collab orative a gent-based two-tier framework, titled WAY (Who Are You? ), to protect cloud resources. The framework can be used to provide securit y in network, infrastr ucture, as w ell as data storage in a heterogeneous cloud platform. If the trust updating polic y is based on network activities, then the framework can provide network security. Simi larly , it provides storage securit y b y monitoring unauthorized access activities by t he Cloud Service Users (CSU). Infrastructure security can be provided b y monit oring t he use of privilege d instructions within the isolated VMs. The uniqueness of the proposed securit y sol ution lies i n t he fact that it ensures security and privacy both at the s ervice provider l evel as well as at the user level in a cloud environment. 1. Introduction In recent times, cloud computing is evolving as a revolutionar y technique for th e way we compute. In its way of evolution, st arting from cluster computing throu gh grid computing, it considered two i mportant parameters of distributed computing paradigm namely flexibility and uti lization. While cluster computing provides high flexibi lity of managing th e resources at t he cost of lower resource utilization and grid computing provides b etter uti lization of resources at the cost of lesser flexibilit y of managing those resources, c loud computing provides both high flexibility as well as high resources uti lization. However we are gaining those advantages at the cost of high securit y threats and privac y challenges since c loud computing deals with the computation and data a t third party’s infrastructure. Cloud computing deals with providing st orage and computation resources as a ser vice to the Cloud Service Users (C SU) in the form o f Software as a Se rvice (SaaS), Platform as a Service (PaaS), Infrastructure as a Servi ce (IaaS), Storage as a Service (S aaS) etc. Software as a S ervice [ 3] ensures t o provide s ervices as pa y-as-you-g o pricing scheme where customer does not need to install configure or run the appli cation on their l ocal computers. Platform as a Service offers a software execution environmen t to deploy Web-based applications. Users do not need to think about the cost and co mplexit y of buying servers or setting the infrastructure. Therefore PaaS refers to provide a development platform to deplo y, host or maintains their applications. Infrastructure as a Service shares hardware resources for executing services using virtualization. To date from a small investor to a big IT company everyone i s now rel y ing on this s ystem. Cloud computing has several advantages such as ease to us e and maintenance, need low power consumption for operation and reductions in the overhead for storing and servicing the data. In spite of several a dvantages cloud also suffers from different security threats and risks to pr otect its resources from unauthorized users and hackers. These security thre ats and attacks are the bi ggest concern towards the improvement of a more s ecure cloud infrastructure. Traditional m y thologies are not enough to adopt for protecting cloud resources as the y becom e obsolete with respect to the ever evolving security t hreats a s well as to avoid data losses in the cloud environment. Moreover d ata stored i n cloud is not just merel y stored, but rather this data gets accessed by l arge num ber of times and changes in the form of insertion, deletion or updation that take plac e from time to time. Security and privac y even with traditional information security s ystems and networks has been difficult to s atisfy and this is also a challenging job for cloud environment [1] . The primary focus of this paper is to introduce a novel and trusted security framew ork for securing cloud resources. The rest of t he paper is org anized as foll ows: Section 2 provides a state of the art security review in cloud computing environment. Section 3 describes the proposed security mod el in details. S ection 4 analyzed the per formance of the pr oposed scheme in a simulated test bed. Finally, in section 5 the concluding c omments are drawn. 2. State of the Art Review on Security for Cloud Environme nt I ssue of data sec urity is mentioned as the bigg est factor for the cloud computi ng [2]. S ecuri ty challeng es in a cloud computi ng environme nt may be classified as: (1) Protec tion of data towards use r’s side . (2) Protec tion of data towards se rvice pr ovider’ s end and (3) Pro tectio n of data i n stor age se rver or Cloud Da ta Center (CDC ). Most of the security models so far are based on traditio nal cryptog raphic approac hes. Some referr ed to d y namic secu rity measures for a cloud environmen t [3] w hile other doma in based applica tion s discuss ed the growing security concerns of cloud infra structure. In [2] domain trust concept is u sed to develo p a secure cloud i nfra struc ture. In [4], Ji n-Song Xu et al, separa tes conta in and format from docume nts, before handl i ng and storin g of data in to the remote clo ud data ce nter to prot ect clou d resour ces from unau thorize d user s or hacker s. An optimi zed authoriza tion metho d (using encry ption functi ons) is used for access ing data base for tru st ed CSUs. In Software as a Service, S QL injection attacks are one of the m ost important factors to be considered. In a S QL injection attack [5], an attacker introduces m alicious codes with the standard SQL codes. In t his way atta ckers get informed about th e s ensitive information from secure databases. This is an important concern for the cloud stora ge from non-trusted CSUs. Another important attack known as Cross Site S cripting (XSS), in which an attacker inje cts malicious scripts into the W eb contents. If an y user clicks on them, the s ensitive information will automaticall y redirects to the attacker machine. In cloud computing this may happen if any attacker affects the cloud service interface, as cloud application sho uld requires Web interfaces for their services. Domain Name Service (DNS) attacks routed the secure web pages to the non-trusted users [6] where an y s ecure dom ain redirects to any o f those CSUs. Attackers are also hacks sensitive information from any s ecure domain using the time la g for a reuse of an y IP (Internet Protocol) address. In cloud domain address are changing ev ery time for any sp ecific CSU, hence this attacks does malicious activities in cloud stora ge. In Deni al of Service Attacks (DoS) attackers sends a huge number of requ ests are sent b y the attackers, t hus the actua l service become unavailable to the t rusted users. In Distributed Denial of S ervice (DDoS) attack, in order to d eny the i mportant se rvices running on a server, the destination sever is flooded with an umpteen number of packets such that the target server is not able to handle it. 3. Proposed Cloud Security Framework Figure 1. Proposed Cloud Security Fr amework The term ‘ WAY’ denotes a way of secure data communication between the Cloud Service Provider (CSP) and the Cloud Service User ( CSU) in a he terogeneous cloud computing environment. I t i s don e by asking ‘Who Are You?’ to dete rmine and satisf y the basic trust requirements of t he service requesting CSUs. Two-tier architecture has been proposed in this paper. One is Broker Domain and another is C loud Service Provider Domain where Broker Domain is denoted b y Level_1 and Cloud Service Provide Domain is denoted by Level_2. This two level communication authenticates the trusted CSUs for accessing private information from cloud data storage. The system architecture is presented in Figure 1. Proposed novel VM m onitoring techniques assures the trustworthiness of the s ystem b y calculating current or u pdated trust degree for each service requesting CSU and t he domain from where the request is coming. In this model CSU (such as CSU_1 in Figure 1) requests i nformation from the Cloud S ervice Provider (CSP). As t he first step, when an y CSU who w ants to send any request to the CSP , t hey have to pass t he correct authentication data (such as user id and password set for t hem by the system) through a prox y server situated in its do main. In this approach p roxy server is used as a communication channel between two domains. As an ex ample, University A and University B is denoted for a specific group of users who requires their University specific authentication data for sending their r equests to CSP through the prox y server. When the request passes throu gh the proxy server i t reac hes to the trusted-agent situated at broker domain (denoted as Cloud Service User A gent, simpl y CSU_A in Fi gure 1). The trust degree of the service requesting CSU is then chec ked by this CSU_A with its local databases presents in th e same domain (in Broker Domain or in Level_1). If the current (or updated) trust value for this CSU is greater t han the threshold value set for this communication, then only the request reaches to the CSP (situated in CSP Domain or in L evel_2). When this request for inf ormation reaches to the CSP, it’s imm ediately passes the r equest to the trusted-agent (denoted as Cl oud Service Prov ider Agent, simpl y CSP_A) sit uated in the same domain to check the t rust degree of the do main from where this request came. A gent CSP_A then checks the current or upd ated (this updation is done b y t he previous successful of unsuccessful iteration information) trust de gree for this particular dom ain and then sends this result back to the C SP, only if trust degree is greater than the current threshold value set for this domain. Then the CSP will allow passing the requested information back to that particular CSU through the proxy server. CSP_A w ill update the trust degree after successfully ex ecuting the task. If the domain trus t is less than that of the curre nt or updated trust degree, or the CSU does an y malicious activities, CSP_A immediately inform this report to the CSU_A situated at broker domain f or taking necessary actions. C SU_A will in turn decrease t he trust value for this particular user. After few (depending on the t ypes of communications) non-trusted activities or reports, CS U_A will remove this particular CSU from its domain. One of the major adv antages of this framework is that, domain remains unaffected (with onl y decreased amount of trust degree than that of non- trusted users) when a said non-trusted CSU does malicious activities in the system. The trust degree of the do main will decrease accordingly with the malicious activities and updating policies. The CS P_A and CSU_A maintain their own databases, user activities i nformation and updated trust de grees for calculating updated trust degree . The flow of i nformation as denoted in Figure 1 is discussed below to understand the process of the proposed model. Step 1: CSU provides credentials to the prox y server to request an i nformation (using credentials set for this University). Step 2: Au thentication information of this u ser reache s to the proxy server. If this information is correct, request will reaches to the CS U_A similarly for any incorrect information request will be dropped. Step 3: Request came to CSU_A for checking current (or updated) trust degree for this CSU. Step 4: The CSU_A checks the trust degree w ith its database. Step 5: Update result. Step 6: I f the trust degree of the service requesting CSU is greater than the threshold value, CSU_A sends this request to CSP via proxy server. Step 7: Request reaches to the CSP. Step 8: CSP passes request to the CSP_A for checking the trust degree of the domain from where the request came. Step 9: CSP_A checks it local databa ses. Step 10: Update result. Step 11: If th e domain’s t rust degree is not greater t han the threshold trust degree set for this domain, the request will be dropped and update this information t o CSU_A for further action. Step 12: Request for information satisfies the basic trust degree. Step 13: CSP will send data to the service re questing CSU via proxy server. Step 14: ‘Data’ determines and reaches to the cor rect CSU through the prox y se rver. Step 15: CSU get the desired data . *DAO represents database Figure 2. Sequence Diagram of the Proposed Fr amework * 3.1 Architecture and Design Figure 3. Proposed Two-Tier Security Architecture for Cloud Computing The proposed two-tier securit y framework for cloud along with its com ponents has been introduced in thi s section. The proxy server in tier 1 and CSP in tier 2 tog eth er maintain the cloud security. Cloud Service User (CSU): Reque st services from cloud storage. Cloud Service Provider (CSP): Provides ser vices to the requesting trusted CSU. Proxy Server: To ch eck the preliminary authentication information set for the CS U of a particular domain and maintain the way of communication. Cloud Service User Agent (CSU_A): Checks the trust degree set for a service requesting CSU and updates the corresponding trust degree, after performing one or more successful or unsuccessful communication. Cloud Service Provider Agent (CSP_A): Checks the domain’s trust degree of the service requesting CSU. 3.2 Algorithms In this section, two proposed algorithms are discussed to determine the trust worthiness of an y service requesting C SU and getting information if the request satisfies the basic trust requirements. The algorithm for requesting informa tion operates for a cloud service use r η that sends request Г to cloud service provider Ś for an information ξ. The user id I , password p and the current trust valu e ν are to be passed as input arguments to the algorithm. The algorithm works for all three types of users; i.e., user could be trusted, innoc ent or non-trusted. It ma y be noted that this algorithm would be hosted in the proxy s erver, say P. Algorithm for Requesting Inform ation Input: User id I; User password p; User Trust Value ν; se rvice request Г( ξ ) Output: Г to be accepted or rejected Begin Algorithm Proxy server P Checks (I, p); If validation succeeds P passes the request to Cloud Service U ser Agent (CSU_A); CSU_A Checks ν; If ν > threshold Request Г for information ξ reaches Ś; else Drop the request Г; End. The second algorithm is for delivering information. This would be oper ational when a successful requ est Г r eaches to Cloud Service Provider Ś for an Information ξ from domain D. The trust value for the user would be revised according l y. Algorithm for Delivering Information Input: Cloud service request Г, trust value V for domain D Output: Delivering information ξ to user i or reject service Begin Algorithm Ś sends incoming request for Г to Cloud Service Prov ider Agent (CSP_A); If V> threshold Send ξ to user I via Proxy Server P; CSP updates the database for the trust value; else Drop the request Г; CSP_A inform CSU_A about I; CSU_ A updates databases for I; End. 3.3 Simulation and Experime ntal Results In a cloud computin g environment di fferent services are carried out on behalf of customers on hardware to which t he customers have no access. The input data for cloud services is uploaded by t he user to the cloud storage that me ans they t ypically r esult in user’s data being present i n unencr ypted form on a machine that the user does not own or control [7] . This poses some inherent chal lenges in terms of security and privacy for the system where one of the t op risks is the deliver y of p rivate data t o an unauthorized user. The basic motivation of developing this proposed architecture is to stop the services of a non-trusted CSU in a heterogeneous cloud environment after unsuccessfull y executing an y re quest. For simulation t hree types of CSU have been considered, the y are as Trusted, Innocent and Non-Trusted. Ther e a re two t ypes o f tasks th e y may be carried out automatically during the communication and the y are d enoted as t rusted task and non-trusted t ask. There are seve ral requests that can be pro cessed in a c ertain interval of time to perform these tasks. User id, Task id and Domain id for corresponding CSU, task and domains are given in the sytem. Simulation code is written in Java pro gramming lang uage, the performance anal ysis is done on a computer having following configuration: 2 GB RAM, 500 GB Ha rd disk an Intel core i3 processor @2.27 GHz. 3.4 Assumptions for this simulation CSU’s trust is the user’s identity trust. User’s id entity trust in cloud is not enough, the issues of us er’s behav ior trust should also b e evaluated and managed. So i t needs a mutual mechanism to establish trust between the CSUs and the CSPs as (1) user’s trust to the provider and (2) provider’s trust to the users. A trusted m onitoring fu nction should be integrate d into the system to supervise the participant CSU’s behavior and dependin g on use r’s beha vior a trust ma nagement mechanism must be incorporated to update CSU’s trust value. After evaluatin g user’s b ehavior, it is required to manage t histrust value efficientl y. Proposed novel trusted and collaborative agent-based security framework takes users behavior evidence from CSP and manage user trust value from it. 4. Performance Analysis The proposed securit y framework is based on a trust model. The trust degree of an y CSU increases after performing any trusted communication. Similarl y for any non-trusted communication the trust degree decreases and the corresponding trust table updated by the trusted-agents for next task. The probability of executing a task successfully for an y non- trusted user is very low than that of any truste d and innocent users in the same domain. A novel trust-based algorithm [ 8] is used to determine the trust of any service requesting user to deliver the requested information from cloud d ata storage. Suppose there are U numbe rs of users present in a do main D whe re U = {u 1 , u 2 , u 3 ,…, u n }. These users ma y be trusted, innocent or non-trusted. U Є {T 1 , T 2 , T 3 }. Where T 1 represent t rusted user, T 2 represent innocent user and T 3 represent non-trusted user. S imilarly t here are two kind of tasks that may be performed during any communication; th ey a re t rusted task, denoted b y T t and non- trusted task denoted by T n . There are N numbers of tasks (where N Є {n 1 ,n 2 ,n3,…,n n }) that can be performed in a simulation. For any instance a user u 1 belongs to T 1 can perform the task of type T t for n 1 times. As for example, a trusted user after successfull y com pletion of a given task T the trust degree will be increased and after an unsuccessful comm unication the trust degree will be decreased accordingly to the performance. Probabilit y function i s used to determine the trust degree of any service requesting CSU and t hen marked them as trusted, innocent or non-trusted. It should be noted that the probability of getting higher trust value by performi ng a trusted task by a trusted user, is alway s better than a non-trusted or an innocent user. Actions for any task can be positive or negative. However, i t is not assumed that all negative actions are not the s ame that is the reason because we distinguish between wrong actions and malicious actions [8]: Positive , i.e. right actions done by the trusted use r; W rong , i.e. bad actions that do not cause any d amage or may cause damages done b y the innocent user; and Malicious , i.e. harmful actions such as attac ks done by the non-trusted user. Accesses to authorized r esources and suitable us e of them are considered right actions. An entity can make wrong actions by mistake or intentionally, but it is difficult to know. To calcul ate the action v alue V a , we take into account the performed a ction weight, but this value i s penalized or re warded by the past behavior. This function increases or de creases according to the performed positive and negative actions respectively. The equation is denoted as follows: ). ……………. (1) Where 0 ≤ V a ≤1 In equation (1), ) represents the past behavior of any CSU. This value tends to 0 when t he behavior is ne gative, and it tends to 1 when the behavior is positive. is the number of negative actions and T otal a is the total number o f performed actions. W a is the action’s weight according to its nature (positive, wrong, and malicious) depending upon the requesting cloud service user and performance of task (0 ≤ w a ≤1). Parameter m i s the securit y level, where m>= 1. This security l evel affects the action weight, for this reason we raise the action weight to the power of ( m ). The exponential rea lly influences when the actions are wrong. We will show later in following diagrams how the security level affects the action values. When a n ew action is performed, Va is recalculated, reflecting the present b ehavior of the entity. The new t rust value wil l take it into account and modify the current trust value of the service requesting CSU. If it is assumed that, 1. Initially trust value V a = 1 2. w a for positive action = 1 and for malicious action = 0.8, and 3. Security level m = 1 The trust degree is updated according to action, as follows in Table I : Table I: Representative computation of trust value f or any CSU Iteration Action Behavior A N Total a V a 1 Positive 0 1 1 2 Malicious 1 2 0.4 3 Positive 1 3 0.7 4 Malicious 2 4 0.4 5 Malicious 3 5 0.3 A CSU can perform positive or negative activit y i n its VM. Depending on its activit y trust value in Domain Trust Table (DTT) as well as in User Trust Table ( UTT) are updated. In this simulation we have chosen three t ypes of CSUs: Trusted, Non-Trusted and Innocent. Each type of user has differe nt probability to perform positive activity as, • Trusted User have the probability 0.8 • Non Trusted User have the probability 0.2 • Innocent User have the probability 0.5 In this simulation the following parameters are also assumed f or the two layers of the framework. For Domain Layer (Level 1 or Br oker Domain) 1. For positive activity W a =1 & nega tive activity W a =0.9 2. Security level m=1 3. Threshold value is 0.1 For User Layer (Level 2, Cloud Service Provider Domain) 1. For positive activity Wa =0.9 & negative activity Wa =0.8 2. Security level m=1 3. Threshold value is 0.2 We simulate the experiment for 3 t ypes of CSU for a specific task r equest. We randoml y choose two users for five tasks. They sent 150 r equests for a particular task id 1001. Figure 4: Trust Value Updating - Case 1 The above experimental result shows t hat the probabilit y of doing malicious communication is much le ss in c ase of a trusted user than that of innocent and non-trusted users. We simulated several experiments in this test-simulated environment to get th e results. It is clear from each si mulation t hat the probability of reaching the threshold value in case of a non- trusted user is much higher t han t hat of any other users. From Figure 5 it is cle ar that trust degree for non-trusted users is increase d after performing some trusted t asks and decreases after performing malicious activities. Figure 5: Trust Value Updation- Case 2 From Figure 5, the trust d egree of an innocent cloud service user is much g re ater after successfully performing some trusted communication with CSP. The t rust degree of trusted user decreased after some time and gradually reaches high after performing several trusted communication with the cloud service provider. The non-trusted user reaches to the threshold rapidl y. In this simulation we took 3 CSU ser and 10 numbers of t asks. C SUs requested for 100 tasks with the task id 1001. 5. Conclusion The proposed framework tries to ma intain the domain reputation as lo ng as possi ble by discarding malicious users from t he domain r educing the CS P’s workload. It also increases some workload of domains and this framework fails to prevent m alicious activit y without CSP’s information. I n fu ture malicious activity id entifying approach can b e imposed into the proposed framework which in turn makes the s ystem to work independent of CSP’s information about malicious activit y . This would help t o prevent unauthorized accesses to cloud data. Research is currentl y going on to evaluate the performance of thi s framework in a real-time environment. The framework ma y also be extended to eradicate data leakages in a heterogeneous cloud computing platform. References: [1] C y ril Onwubiko, “Security Issues to C loud Computing”, in Cloud Computing: Principles, Systems and Applications, Computer Communications and Networks, N. Antonopoulos and L. Gillam (Eds.), Springer-Verlag London L i mited 2010, DOI 10.1007/978-1-84996-241- 4_16, pp. 271-288, 2010. [2] Wenjuan Li and Lingdi P ing, "Trust Model to Enhance S ecurity and Interoperability of Cloud Environment", Proc. of C loudCom 2009 , S pringer-Verlag Berlin Heidelberg 2009, LNCS 5931, pp. 69–79, 2009. [3] J eff Seda yao, Steven Su, Xiaohao Ma, Minghao Jiang, and Kai Miao, "A Simple Technique for Securing Data at Rest Stored in a C omputing Cloud" , Proc. of CloudC om 2009 , Springer-Verlag Berlin Heidelberg 2009, LNCS 5931, pp. 553–558, 2009. [4] J in-Song Xu, Ru-Cheng Huang, W an-Ming Huan g, and Gen g Yang, "Secure Document Service for Cloud Computing", Proc. of CloudCom 2009 , Springer-Verlag B erlin Heidelberg 2009, LNCS 5931, pp. 541–546, 2009. [5] Marios D. Dikaiakos, Dimitrios Katsaros, Pankaj Mehra, George P allis and Athena Vakali, “Cloud Com puting: Distributed Internet Computing for IT and Scientific Research” in IEEE Internet Compu ting, IEEE Computer S ociety, pp. 10-13, September/October 2009, Vol. 13 No. 5, DOI: doi:10.1109/MI C.2009.103 [6] Char Sample, Senior Scientist, BBN Technologies, Diana Kelley, Partner, Security Curve, “Cloud computing security : Routing and DNS security thre ats,” http://searchsecurity.techtarget.c om/tip/0,289483,sid14_gci1359155_mem1,00.html [7] Siani Pearson, Yun Shen and Miranda Mowbray, “A Privacy Manager fo r Cloud Computing”, in CloudCom 2009, LNCS 5931, M.G. J aatun, G. Zhao, and C. Rong (Eds.), Springer-Verlag Berlin Heidelberg 2009, pp. 90–106, 2009. [8] Florina Almen´arez, Andr´es Mar´ın, Celeste Campo and Carlos Garc´ıa R., “PTM: A Pervasive Trust Management Model for D ynamic Open Environments”, Proceedings of First Workshop on Pervasive Security , Privac y a nd Trust PS PT’04, Boston, MA, U SA, 2004.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment