Weakness in a Mutual Authentication Scheme for Session Initiation Protocol using Elliptic Curve Cryptography
The session initiation protocol (SIP) is a powerful signaling protocol that controls communication on the Internet, establishing, maintaining, and terminating the sessions. The services that are enabled by SIP are equally applicable in the world of m…
Authors: Debiao He
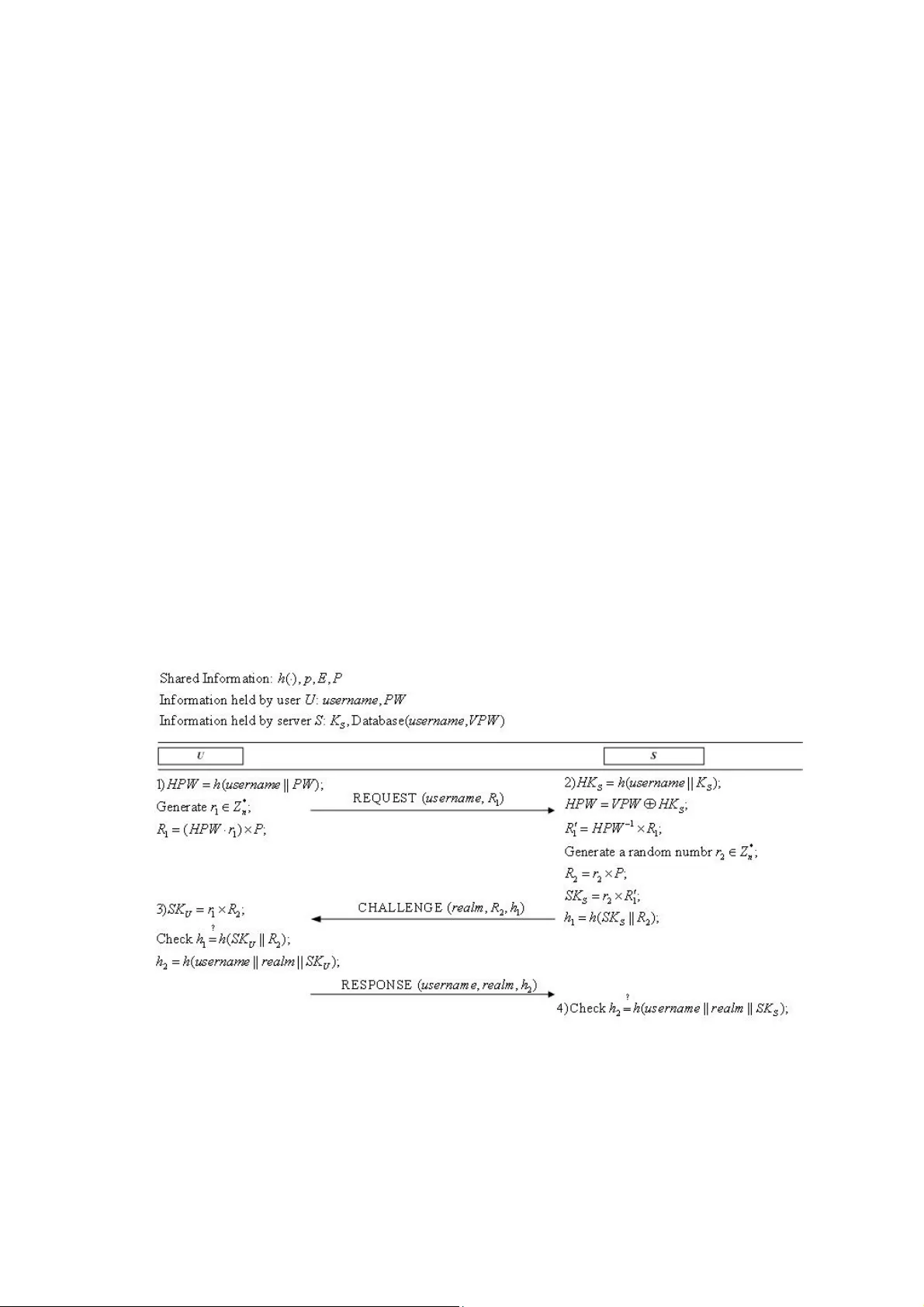
Weakness in a Mutual Authentication Scheme for Session Initiation Protocol using Elliptic Curve Cryptography Debiao He School of Mathematics and Statistics, Wuhan University, Wuhan, Peopl e’s Repu blic of Chi na hedebiao@16 3.com Abstract —The session initiation protoc ol (SIP) is a powerful signaling protocol th at controls communication on the Internet , establishing, maintaining, and te rminating th e sessions. The s ervices that a re en abled by SIP are equally applicable in t he wor ld of mobile and ubiquitous computing. In 2009, Tsai proposed an authenticated key agreement scheme as an enhancement to SIP. Very recently, Arsh ad et al. demonstrated that Tsai’s scheme was vulnerable to offline pass word guessing attac k and stolen-verifier attack. They also pointed that Tsai’s scheme did n ot provide known-key secr ecy and perfect for ward secrecy. In order to overcome the weaknesses, Arshad et al. also prop osed an improved mu tual authentication scheme based on elliptic curve discrete loga rithm pro blem for SIP and claimed that their scheme can withstand various attacks. In this p aper, we do a cryptanaly sis of Arshad et al.’s sc heme and show that Arshad et al.’s scheme is vulnerable to th e pa ssword gues sing attack. Keywords- Authentication; Elliptic cu rve cryptos ystem; Security; Session initia tion protocol I. I NTRODUCTION In today's an d future wire d or wireless networks, m ultimedia service i s a great im portance applicat ion class. Especial ly, the next generation of wireless n etworks will be b ased on all-IP architectu re. One of the most importan t protocols supporting multimedia services is the session initiation protocol (SIP) [1] . In 1999, the Internet Engine er ing Task Force (IETF) proposed the SIP for the IP-based telephony prot ocol [2-7]. Because SIP is a te xt-based peer-to-peer prot ocol , it uses Internet protocols su ch a s hyper text transport protoc ol (H TTP) and si mple mail transport protocol (SMTP) [8] . When a user wants to acces s an SIP service , he/she has to perform an aut hentication process in or der to get va rious services f rom the rem ote server. There fore, the securit y of SIP is becoming m ore impor tant [4],[6] ,[8] and the SI P authentication sc heme is the most im portant i ssue for SIP. Ho wever, the original a uthenticat ion scheme fo r SIP does not provide st rong securi ty because it is based on the HTTP digest authe ntication [ 2] . The services that are enabled by SIP are e qually applicable in the world of mobile and ubiqu itous computing . For example, a use r registers his/her location with a SIP server and then the server knows if the user is available and where the user ca n be found . In addition, the location could be home, work, or mobile. Now, SIP has been defined by the 3GPP (the 3rd Generation Partnership Project) as a signal protocol for the third -generatio n communicat ion system [9] . Yang et al. [10] pointed o ut that the procedu re of the original S IP authenticat ion scheme based on HTTP digest authentication is vulnera ble to the off-line p assword guessi ng attack and the server s poofing att ack. They also proposed a secu re authentication scheme for SIP to resist the attacks. Ho wever, the computational c ost of Ya ng et al.’s s cheme i s very high, maki ng it unsuitabl e for pract ical appl ications. To im prove the per formance, D urlanik et al . [11] pr oposed an a uthentication scheme us ing the elliptic curve cryptogr aphy(ECC)[12, 13]. Later, Tsai [14] propo sed an efficient nonce-b ased authenticatio n scheme. Since a ll the communi cation messages are enc rypted/decry pted by u sing one-way h ash functio n and XOR ope ration, its com putation c ost is low, making it promising for low-power processors. Unfortunately, Arshad et al.[15 ] found Tsai’s scheme[14 ] was still vulnerabl e to offline passwor d guessing attack and stol en-verifier attack while. They also dem ons trated that Tsai’s schem e did not provi de known-key secrecy and p erfect forward secrecy[ 9]. To overcome th e weaknesses, Arshad et al.[15] also proposed an improved authentication u sing ECC for SIP. In this letter, we show that Arshad et al.’s scheme may suff er fro m off-line password guessing attack if only one ellip tic curve scalar multiplication is required in the generation of passwo rd verifier from password. The rest of the paper is organize d as follows. Sectio n 2 gives the revi ew of the Arsha d et al.’s scheme . Section 3 discusses th e cryptanalysis of A rshad et al.’s sch em e. Finally, we conclude the paper in Section 4. II. R EVIEW OF A RSHAD ET AL .’ S SCHEME FOR SIP In this section, we briefly review Arsh ad et al.’s nonce-based authentication sche me for SIP [1]. There are two phases i n Arshad et al. ’s scheme: regi stration a nd authenti cation. Nota tions used in this paper a re defined a s follows . z U : the client user; z S : the server; z D : a uniform ly distribut ed dicti onary; z PW : a low-entropy password of U extracted from D ; z S K : a high-entropy secret key of S , which is only known by the server and must be safeguarded; z SK : a shared comm on session ke y between U and S ; z , p n : two large prime numbers; z p F : a finite field; z E : an elliptic curve defined on finite field p F with large order; z G : the group of elliptic curv e points on E ; z P : a point on elliptic curve E with order n ; z () h ⋅ : a secure one- way hash funct ion; z ||: a string concatenation operation z ⊕ : a string XOR operation A. Regi stration phas e When U wants to register and become a new legal user, U and S execute t he following steps over a secure channel. 1) U → S : ( use rname , PW ) U submit his username and PW to S . S computes two secret values (| | ) HPW h username PW = and (| | ) SS HK h username K = . 2) S computes the pass word verifier S VPW HPW HK = ⊕ for U . 3) S stores U ’s use rname and VPW in the user account database. B. Authentication phase If a legal user wants to logi n into S , he must type hi s username and PW . All steps of authentication phase, as shown in Fig. 1, execut ed as follow s. 1) U → S : REQUEST ( use rname , 1 R ) U computes (| | ) HPW h username PW = . Then U generates a random n umber * 1 n rZ ∈ , computes 11 () R HPW r P =⋅ × and sends a reque st message as REQUEST ( username , 1 R ) to S . 2) S → U : CHALLENGE ( realm , 2 R , 1 h ) Upon receiving the request message, S extracts HPW fr om VPW by comput ing (| | ) SS HK h username K = and S HPW VPW HK =⊕ , wh ere VPW is a stored password verifier fo r U in the user account database. Then, S computes 1 11 R HPW R − ′ =× . Now, S ge nerates a random number * 2 n rZ ∈ , and computes 22 R rP =× , 21 S SK r R ′ = × and 12 (| | ) S hh S K R = . At last, S s ends a challenge m essage CHALLENGE ( realm , 2 R , 1 h ) to U . 3) U → S : RESPONSE ( username , realm , 2 h ) Upon receiving the c hallenge message, U computes 12 U SK r R = × and checks whether the equation 12 (| | ) U hh S K R = holds . If the equat ion doe s not hold, U rejects the server c hallenge message. Otherwise, U authenticates S and com putes 2 (| | | | ) U h h use rname realm SK = . Finally, U sends a response m essage RESPONSE ( username , re alm , 2 h ). 4) Upon receiving the response message, S computes (| | | | ) S h username realm SK and verifies whether it is equal to the received response 2 h . If they are no t equal, S rejects the user response message. Otherwise, S authenticates U and accepts the user’s login request. After mutual authentication between U and S , 12 US SK SK SK r r P = == × is used as a shared session key . Fig. 1. Authe ntication p hase of Arshad et al.’s schem e III. C RYPTANALYSIS OF A RSHAD ET AL .’ S SCHEME FOR SIP Off-line password gue ssing attack succeeds when there is inform ation in communications, which ca n be used to verify the correctness of the gues sed passwords. In [1 5], Arshadet et al. claimed that their protoc ol can resist the off-line pass word gue ssing attack. However, in this section, we will show that the off-line p assword guessing attack, no t as they claimed, is still effect ive in Arshadet et al.'s protocol. Our attack c onsists of two phases. Phase 1 : 1) The adv ers ary A chooses a random number * 1 n rZ ∈ , computes 11 R rP = × , then impersonates U and sends a request message REQUEST ( username , 1 R ) to S . 2) Upon receiving the request message, S extracts HPW from VPW by computing (| | ) SS HK h username K = and S HPW VPW HK =⊕ , where VPW is a stor ed password verif ier for U in the user account databa se. Then, S computes 11 11 1 R HPW R HPW r P −− ′ =× =⋅ × . Now, S generates a ran dom number * 2 n rZ ∈ , and computes 22 R rP =× , 1 21 1 2 S S K rR H P W r rP − ′ =× = ⋅ ⋅ × and 12 (| | ) S hh S K R = . At last, S sends a challenge m essage CHALLENGE ( realm , 2 R , 1 h ) to the adversary A . Phase 2 : The adve rsary A then launches the off-line passwo rd guessi ng attack as foll ows: 1) A guesses a candidate passwords PW , and com putes (| | ) HPW h username PW = . 2) A computes 1 12 S SK HP W r R − =⋅ × . 3) A checks whether 1 h and 2 (| | ) S hS K R are equal. If 1 h and 2 (| | ) S hS K R are equal, the adversa ry can concl ude that U ’s password PW PW = . Otherwise, adversary repeat steps 1), 2) and 3) until the correct password is found. From the above descri ption, we kno w the adversary ca n get the passwor d. Therefore, Arshad et al.’s scheme is vul nerable to the off-line password guessing attack. IV. CONCLUSIONS In this letter, we have shown th at Arshad et al.’s authenticati on scheme for session initiatio n protocol is vulnerable to passw ord guessing attack. The analysis shows Arshad et al.’s au t hentication scheme is not f or practical applicati on. R EFERENCES [1] D. Geneiatakis, T. Dagiuklas, G. Kambourak is, C. Lambrinoudakis, S. Gritzalis, and S. Ehlert. "Survey of security vulnerabilities in session initiation protocol," IEEE Communications Surveys and T uto rials, vol. 8, no. 3, pp. 68-81, Jul. 2006. [2] J. Franks, P. Hallam-Baker, J . Hostetler, S. Lawrence , P. Leach , and A. Luotonen. HTTP Authentication: Basic and Digest A ccess Authentication. IETF RFC2617, Jun. 1999. [3] M. Handley, H. Schulzrinne, E. Schooler, and J. Rosenberg. SIP: Session Initiation Protocol . IETF RFC2543, Mar. 1999. [4] M. Thomas. SIP Security Requirements. IETF Internet Draft (d raftthomas-sipsec-reg- 00.txt), Work In Progress, Nov. 2001. [5] J. Rosenberg, H. Schulzrinne, G. Camarillo, A. Johnston, J. Peterson, and R. Sparks . SIP: Session Initiation Protocol. IETF RFC 3261, Jun. 2002. [6] J. Arkko, V. Torvinen, G. Cam arillo, A. Niemi, and T. Haukka. Security Mechanism Agreement for SIP Sessions. IETF Internet Draf t (draft-ietf- sipsecagree-04.txt), Jun. 2002. [7] A. B. Johnston. SIP: Understanding the Session Initiation Protocol. 2nd ed. Artech House; 2004. [8] L. Veltri, S. Salsano, and D. Papalilo. "SIP security is sues: the SIP authentication procedure and its processing load," IEEE N etwork, vol. 16, no. 6, pp. 38- 44, 2002. [9] M. G. Martin, E. Henrikson, and D. Mills. Private Header (P -H eader) Extensions to the Session Initiation Protocol (SIP) for the 3rd-Generation Partner ship Project(3GPP). IETF RFC3455. 2003. [10] Yang CC, Wang RC, Liu WT (2005) Secure authenticati on scheme for session initia tion protocol. Comput Secur 24:381 –386 [11] Durlanik A, Sogukpinar I (2005) SIP Authentication Scheme using EC DH. World Enform atika Socity Trans Eng Comput Technol 8:350–3 53 [12] Miller V.S. (1985) Use of elliptic curves in cryptography. In: Proceedings of the Adva nces in Cryptology-CRYPTO’85, New York, U SA, 417–426. [13] Koblitz N. (1987) Elliptic curve cryp tosystem , Mathematics of Computation 48: 203–209. [14] Tsai JL (2009) Efficient nonce-based au thentication sche me for session initiation protocol. Int J Netw Secur 8(3):312–316 [15] Arshad R., Ikram N., Elliptic cu rve cryptography based mutual authentication scheme for session initiation protocol, Multimedia Tools and Applications, DOI: 10.1007/s11042-011- 0787-0
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment