Parameterized Verification of Safety Properties in Ad Hoc Network Protocols
We summarize the main results proved in recent work on the parameterized verification of safety properties for ad hoc network protocols. We consider a model in which the communication topology of a network is represented as a graph. Nodes represent s…
Authors: Giorgio Delzanno, Arnaud Sangnier, Gianluigi Zavattaro
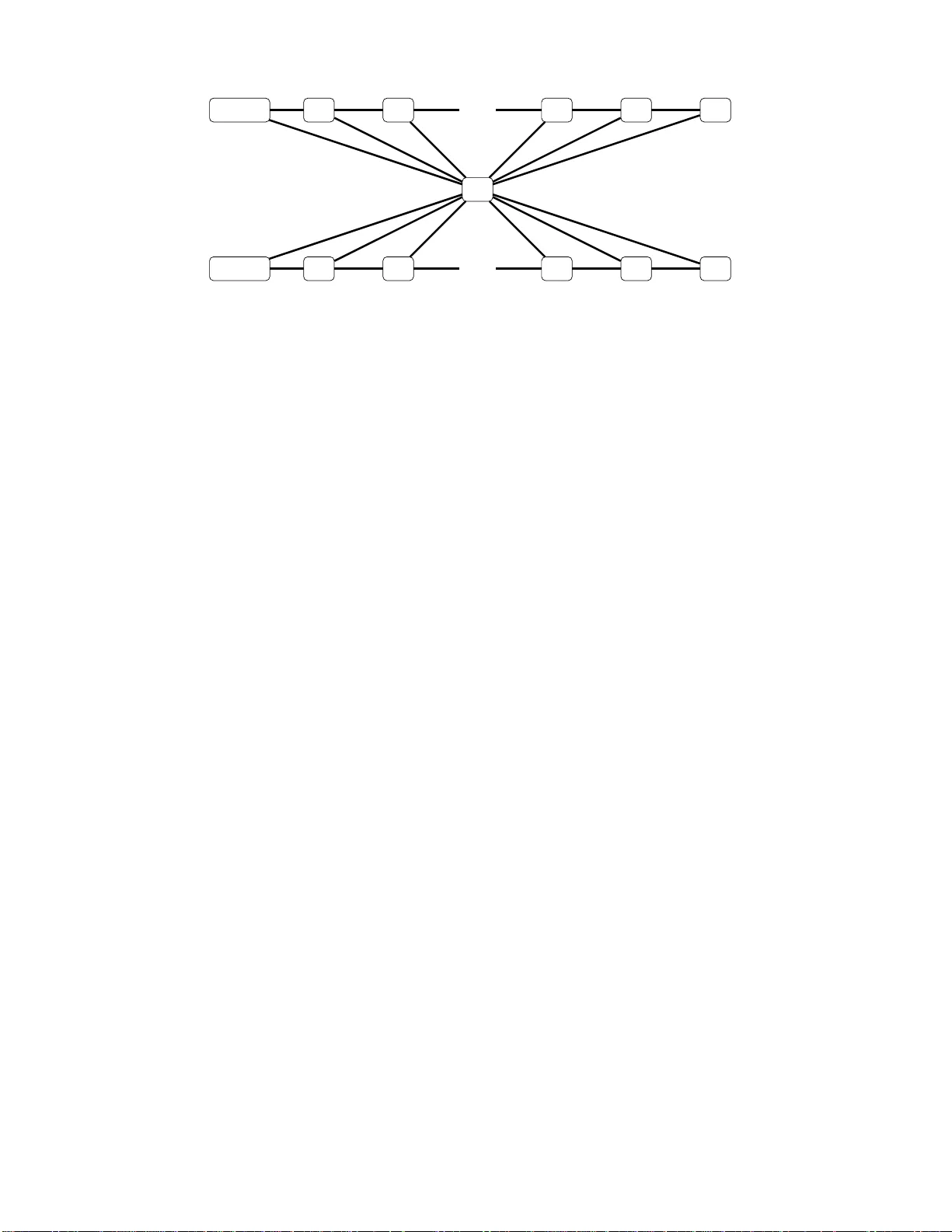
L. Aceto and M.R. Mousa vi (Eds.): P A CO 201 1 EPTCS 60, 2011, pp. 56–65, doi:10.4204 /EPTCS .60.4 c G. Delzanno, A. Sangnier , and G. Zav attaro This work is licensed under the Creativ e Commons Attribution License. Parameteriz ed V erificatio n of Safety Pr operties in Ad Hoc Network Pr otocols Giorgio Delza nno Univ ersity of Geno v a - Italy delzanno@d isi.unige.i t Arnaud Sangnier LIAF A, Univ ersity Paris 7 - France sangnier@l iafa.jussie u.fr Gianluigi Zav attaro Univ ersity of Bologna - Italy zavattar@c s.unibo.it W e summarize the main results prov ed in recent work on the parameterized verification of safety proper ties for ad hoc network pro tocols. W e consider a m odel in which the communica tion topolog y of a network is represented as a graph. Nodes represen t states of individual processes. Adjacent nodes represen t single-hop neighbo rs. Pro cesses are finite state au tomata that comm unicate via se- lectiv e br oadcast messages. Reception of a broadcast is restricted to single-hop n eighbor s. For this model we consider a de cision p roblem that can be expre ssed as th e verification of the existence of an initial top ology in which the execution of the protocol ca n lead to a configur ation with at least one node in a certain state. Th e de cision p roblem is p arametric b oth on the size and on the form o f the co mmunica tion topology of the in itial c onfigura tions. W e draw a complete pictu re o f the decid- ability and complexity bound aries of this p roblem acco rding to various assump tions on th e possible topolog ies. 1 Introd uction Ad ho c net works co nsist of w ireless hosts that, in t he abs ence of a fixed infrastruc ture, communicate sendin g broadcast messages. In this context protocols are typica lly supposed to work independen tly from the communication topology and fr om the s ize (number of nodes) of th e network. As suggeste d in [ 3, 4 ], the contr ol state r eachabil ity pr ob lem (or cover abilit y pr oble m ) seems a particu larly adequa te formaliza tion of p arameteri zed verificat ion probl ems for ad hoc n etwor ks. A n etwork is repres ented as a grap h in which nodes are indi vidu al processes a nd edges repre sent communication links. Each node ex ecute s a n instance of the same protoco l. A protocol is described by a finite state communicating automato n. The control state reachab ility problem co nsists in chec king wheth er ther e e xists a n i nitial graph (with unkno wn s ize and topology) t hat can e v olv e into a configura tion in w hich at least one node is in a giv en error state. Since the size of the initial configuration is not fi xed a priori, the state-s pace to be expl ored is in general infinite. In this paper we summarize the main results that we hav e pro ved in two recent publicati ons [3 , 4]. The first result is nega ti ve: control state reachab ility is undeci dable if we do not fi x any restriction on the possible topologie s. As for other communicat ion models [16, 25], finding interest ing classe s of netwo rk t opolog ies fo r which verificati on is, at least theoretical ly , possible is an important research proble m. As a first positi v e result, we hav e prove d in [3] that control state reachabil ity tu rns out to be decida ble for the class of bounded path graph s . Graphs ha ve boun ded path if there exists a value k such that all simple paths in the cons idered graph hav e length smaller than k . Although for a fixed k this class of graph s is infinite, it appears of limited inte rest as it does not incl ude clique graphs. Cliques are appe aling for at least two reason s. First, they rep resent the best possib le scenario for optimizi ng broadc ast communicati on (one bro adcast t o re ach all nodes). Second, when rest ricting configu ration s only to cliques, control sta te reacha bility can be red uced to co v erabili ty in a Broad cast Protocol, i.e., G. Delzanno , A. Sangnier , and G. Zav attar o 57 in a model in which configuratio ns are multisets of proces ses defined by communicatin g a utomata [6]. Cov erabil ity is decidable in Broadcast Protocols in [8]. For these reas ons, in [4] w e hav e de cided to in v estig ate classes of graphs th at at least includ e the clique graphs. More precise ly , we hav e considere d networks in which the underly ing topology is in between the class of cliques and the strictly large r class of bounded diameter graphs . Graphs ha ve bound ed diameter i f th ere ex ists a va lue k such that t he minima l pa th bet ween e ver y p air of nodes of the same graph has length smaller than k . Graphs with bounded diameter (also called clusters) are particu larly rel e v ant for the domain of ad hoc networks. They are o ften used to partitio n a network in order to increa se the efficienc y of broadca st communication [10]. The restric tion to bounded diameter follo ws the approa ch taken for point- to-poin t communicati on in [16, 25]. Diff erently from [16, 25] we hav e pro ve d that for our model of selecti v e broad cast control state reacha bility is un decida ble when rest ricting the topologi es to gra phs whose diameter is bounded by k (for a fixed k > 0). Then, we h a ve in v estiga ted further rest riction s hav ing in mind the constraint tha t they must allo w at least cliques of arbitrary order . By using an original well-quasi ordering result, we hav e pro ved th at co ntrol state reachabi lity becomes decid able when c onside ring a cla ss of g raphs in which the corres pondin g maximal cliques are connected by paths of bounded length. Further more, b y exploiti ng a recent result of Schnoebelen [21 ] and a reduction to cov erab ility in reset nets, we hav e sho wn that the resulti ng decision procedur e is Ackerman n-hard. Interestingl y , the same comple xity result alre ady holds in the subclass of clique topolog ies. Related W ork Ethernet- like broadcast communicatio n has been analyzed by P rasad [18] using the Calculus o f Bro adcast ing Systems, in which a ll processes rece i ve a bro adcast messag e at once. A similar type of broadcast mechanism is used in the Broadcas t P rotoco ls of Emerson and Namjoshi [6]. In our setting , this is similar to the case in which all nodes share a common group (the underly ing g raph is a clique ). Ene and Muntean presented the b π -calcu lus [7 ], an extensio n of the π -calcu lus [19] w ith a broad- cast such t hat only no des l istenin g on the right channel can recei v e emitted mes sages. W ireless broadca st communica tion has been in v estiga ted in the context of process calculi by Nanz and Hankin [17], Singh, Ramakrishn an and Smolka [22 , 2 3], Lanese and San gior gi [14], Godsk esen [12], and Merro [ 15]. In particu lar Nanz and Hankin [17] consid er a graph represen tation of node localities to determine the re- cei ve rs of a message, w hile Godskes en [12 ] makes use of a neighbou r relation. On the contrary , L anese and Sangior gi [14] and Merro [15] associate physical locations to processe s so that the recei vers depen d on the location of the emitter and its transmissi on range. As already mentioned, we hav e been directly inspir ed by the ω -calcu lus of Singh, Ramak rishnan and Smolka [22, 2 3]. The ω -calcu lus is base d on t he π -calcu lus. T he π -calcu lus [19] intermixes the communi cation and mobility o f processes by expr ess- ing mobili ty as change of intercon nectio n structure among proc esses through communicati on. In the ω -calcu lus mobility of processes is abstracted from their communicat ion actions, i.e., mobility is spon- taneou s and it does not in v o lve any communicati on. In [24] the same authors define a constrain t-based analys is for configurations with fixed topolo gies and a fi xed n umber of nodes. The authors also mention that checking rea chabil ity of a configuration from an in itial o ne is de cidable f or t he fragment withou t restric tion. This property is an immedia te consequ ence of the fact th at there is no dy namic genera tion or deletio n of proces ses (i.e. it boils do wn to a finite-state reachability problem). T he symbolic approach in [24] s eems to improv e verification results obtained with more s tandard model checking t echniq ues. For ins tance, in [9] model checking is used for automa tic verification of finite-stat e and timed models of Ad Hoc Network s. In these works the numbe r of nodes in the initia l configurations is kno wn and fixed a priori. In ord er to detec t protoc ol vulne rabiliti es tools lik e Uppaal ar e e xecu ted o n all possi ble topo logies 58 Paramete rized V erificatio n of Safety Properties in Ad Hoc Networks (modulo symmetries) for a giv en number of nodes. In [20] Saksena et al. define a symbolic proced ure based on graph-tran sformatio ns to analyz e routing protocol for Ad Hoc Networks. The symbolic repre- sentat ion is based on upward closed sets of graphs ordered w . r .t. sub graph inclusion . T heir proced ure is not gua ranteed to te rminate. In our p aper we c onside r a non tri vi al class of g raphs (b ounde d path config- uratio ns) for which backward analysis with a similar symbolic represent ation (upwar d closure of graphs w .r .t. induced subg raph ordering) is g uarant eed to terminate for fini te-stat e descriptio ns of indi vidu al nodes . Structur e of the p aper In Section 2 we formally in troduc e our model for ad hoc network protoco ls, we define the parametri c version of the control state reachabi lity problem, and we recall the result from [3], i.e. that cont rol state reachabili ty is undecidab le if we do not impose any restri ction on the class of possib le topolo gies, while it turns out to be decidable w hen restricting to bounded path topologies . In Sections 3 and 4 we consid er other restricted classes that include clique graphs: bounded diameter and bound ed path on the maximal clique graph, respecti ve ly . For these classes we report the results prov ed in [4]: contro l state reacha bility is und ecidab le when restric ted to graphs with a bou nded diameter (b u t it turns out to be decidable if we addition ally assume bo unded d egre e), while for the class of g raphs ha v ing a correspondi ng maximal clique graph w ith bounded path, the problem is decidab le. Section 5 contains conclu ding remarks and directions for future work. 2 Ad Hoc Network Pr otocols 2.1 Pr eliminaries on Graphs In this section we assume that Q is a finite set of elements. A Q-labeled undir ected grap h (shortly Q - graph or graph ) is a tuple G = ( V , E , L ) , where V is a finite set of vertices (sometimes called nodes ), and E ⊆ V × V is a finite set of edges , and L : V → Q is a labeling functio n. W e consider here undirecte d graphs , i.e., such that h u , v i ∈ E if f h v , u i ∈ E . W e denote by G Q the set of Q -graphs . For an edge h u , v i ∈ E , u and v are called its endpoi nts and we say that u and v are adjacent vertices. For a node u we call vicin ity the set of its adjacent nodes (neighb ors). Giv en a verte x v ∈ V , the de gr ee of v is the size of the set { u ∈ V | h v , u i ∈ E } . The degree of a graph is the maximum degree of its vertices . W e will sometimes denote L ( G ) the set L ( V ) (which is a subset of Q ). A path π in a graph is a finite sequen ce v 1 , v 2 , . . . , v m of verti ces such that for 1 ≤ i ≤ m − 1, h v i , v i + 1 i ∈ E and the integer m − 1 (i.e. its number of edges) is called the length of the path π , denoted by | π | . A path π = v 1 , . . . , v m is simple if for all 1 ≤ i , j ≤ m with i 6 = j , v i 6 = v j , in other words each verte x of the graph occurs at most once in π . A cycle is a path π = v 1 , . . . , v m such that v 1 = v m . A graph G = h V , E , L i is connecte d if for all u , v ∈ V with u 6 = v , there exists a pat h from u to v in G . A clique in an undirect ed graph G = h V , E , L i is a su bset C ⊆ V of vertices , such that for ev ery u , v ∈ C with u 6 = v , h u , v i ∈ E . A clique C is said to be maximal if there exist s no verte x u ∈ V \ C such that C ∪ { u } is a clique. If the entire set of nodes V is a clique, we say that G is a clique graph. A bipartite Q-graph is a tuple h V 1 , V 2 , E , L i suc h that h V 1 ∪ V 2 , E , L i is a Q -graph, V 1 ∩ V 2 = / 0 and E ⊆ ( V 1 × V 2 ) ∪ ( V 2 × V 1 ) . The diameter of a graph G = h V , E , L i is the length of the longes t shortest simple path between any two vertices of G . Hence, the diameter of a clique graph is always one. W e also need to define some graph orderings. Gi ven two graphs G = h V , E , L i and G ′ = h V ′ , E ′ , L ′ i , G is in the subgr aph relation with G ′ , written G s G ′ , whene ver there exis ts an injecti v e function f : V → V ′ such that, for eve ry v , v ′ ∈ V , if h v , v ′ i ∈ E , then h f ( v ) , f ( v ′ ) i ∈ E ′ and for ev ery v ∈ V , L ( v ) = L ′ ( f ( v )) . Furthermore, G is G. Delzanno , A. Sangnier , and G. Zav attar o 59 in the induced subgr aph relation w ith G ′ , w ritten G i G ′ , w hene v er there exists an injecti ve function f : V → V ′ such that, for eve ry v , v ′ ∈ V , h v , v ′ i ∈ E if and only if h f ( v ) , f ( v ′ ) i ∈ E ′ and for ev ery v ∈ V , L ( v ) = L ′ ( f ( v )) . As an example, a path w ith three nodes is a subgraph , but not an induced subgraph, of a ring of the same order . Finally , w e recall the notion of well-quas i-or d ering (wqo for short). A quasi order ( A , ≤ ) is a wqo if for ev ery infinite sequence of elements a 1 , a 2 , . . . , a i , . . . in A , there exis t two indice s i < j s.t. a i ≤ a j . Examples of wqo’ s are th e sub-mult iset relation, and bot h the sub graph and the induce d subgraph relation over gra phs with simple paths of bounded length [5]. 2.2 Ad Hoc Networks In our model of ad hoc networks a configuration is simply a graph and we assume that each node of the graph is a process that runs a common predefined protocol . A protocol is defined by a communicat ing automato n with a fi nite set Q of control states. Communicatio n is achiev ed via selecti ve broadcast . The ef fect of a broadcas t is in fact local to the vicinity of the sender . The initial configuratio n is any graph in which all the nodes are in an initial control state. Remark that ev en if Q is finite, there are infinitely many poss ible initial configuratio ns. W e next formali ze the above intu ition. Indivi dual Behavior T he protocol run by each node is defined via a process P = h Q , Σ , R , Q 0 i , where Q is a finite set of control states, Σ is a fi nite alphabe t, R ⊆ Q × ( { τ } ∪ { !! a , ?? a | a ∈ Σ } ) × Q is the transit ion relation , and Q 0 ⊆ Q is a set of initial control states. The label τ repres ents the capability of perfor ming an intern al actio n, and the label !! a (?? a ) represents the ca pabilit y of broadc asting (rec ei ving) a message a ∈ Σ . Network Semantics A n AHN associa ted to P = h Q , Σ , R , Q 0 i is defined via a transition system A P = h C , ⇒ , C 0 i , where C = G Q (undir ected graphs with labels in Q ) is the set of configurati ons, C 0 = G Q 0 (undir ected graphs with labels in Q 0 ) is th e subset of initia l configuratio ns, and ⇒⊆ C × C is the tra nsi- tion relatio n defined next. For q ∈ Q and a ∈ Σ , w e define the set R a ( q ) = { q ′ ∈ Q | h q , ?? a , q ′ i ∈ R } that contai ns states that can be reached from the state q upon reception of message a . For G = h V , E , L i and G ′ = h V ′ , E ′ , L ′ i , G ⇒ G ′ holds if f G and G ′ ha ve t he sa me underly ing structure, i.e., V = V ′ and E = E ′ , and one of the follo wing conditio ns on L and L ′ holds: • ∃ v ∈ V s.t. ( L ( v ) , τ , L ′ ( v )) ∈ R , and L ( u ) = L ′ ( u ) for all u in V \ { v } ; • ∃ v ∈ V s.t. ( L ( v ) , !! a , L ′ ( v )) ∈ R and for eve ry u ∈ V \ { v } – if h v , u i ∈ E and R a ( L ( u )) 6 = / 0 (rece ption of a in u is enabled) , then L ′ ( u ) ∈ R a ( L ( u )) . – L ( u ) = L ′ ( u ) , other wise. An exec ution is a sequence G 0 G 1 . . . such that G 0 ∈ G Q 0 and G i ⇒ G i + 1 for i ≥ 0. W e use ⇒ ∗ to denote the reflexi v e and transit iv e closure of ⇒ . Observ e tha t a broadcast mes sage a s ent by v is del i vere d onl y to the sub set of neighbors int erested i n it. Such a neighbor u updates its state with a ne w state tak en from R ( L ( u )) . A ll the other node s (i ncludi ng neighb ors not interested in a ) simply ignore the message. Also notice that the topology is static, i.e., the set of nodes and edges remain unchan ged during a run. Finally , for a set of Q -graphs T ⊆ G Q , the AHN A T P restric ted to T is defined by the transiti on system h C ∩ T , ⇒ T , C 0 ∩ T i w here the relatio n ⇒ T is the restric tion of ⇒ to ( C ∩ T ) × ( C ∩ T ) . 2.3 Example of Ad Hoc Network Pr otocol As an example of an ad hoc network protocol and of its semantics, consider a protocol consisting of the follo wing rules: ( A , τ , C ) , ( C , !! m , D ) , ( B , ?? m , C ) , and ( A , ?? m , C ) . As sho wn in Fig. 1, startin g from a 60 Paramete rized V erificatio n of Safety Properties in Ad Hoc Networks A A B B A B ⇒ C A B B A B ⇓ D C B C A B ∗ ⇐ D D D D D D Figure 1: Example of ex ecu tion configura tion with only A and B nodes, an A node first mov es to C and then send m to his/her neighb ors. In turn, they forw ard the message m to their neighbo rs, and so on. 2.4 Decision pr oblem W e define the decisi on problem of contr ol state r eac habili ty ( C OV E R ) as follows: Input: A process P = h Q , Σ , R , Q 0 i with A P = h C , ⇒ , C 0 i and a control state q ∈ Q ; Output: Y es, if there e xists G ∈ C 0 and G ′ ∈ C such that q ∈ L ( G ′ ) and G ⇒ ∗ G ′ , no otherwis e. Control state reachabi lity is strictly related to parameterize d verificatio n of safety properties. The input contro l state q can in fact be seen as an error state for the ex ecuti on of the protocol in some node of the netwo rk. If the answer to C OV E R is yes, then there exists a suffici ent number of processes, all execu ting the s ame pro tocol, and an initial top ology from wh ich we can gene rate a configuration in whic h the error is expose d. U nder this perspect i ve, C OV E R can be vie wed as instance of a parameteriz ed verification proble m. In [3] we ha v e prov ed that C OV E R is undecidab le. The proof is by redu ction from the halting problem for two-count er Minsky machines. A Minsky machine manipu lates two inte ger v ariabl es c 1 and c 2 , which are called counters , and it is composed of a finite set of instructio ns. Each of the instuction is either of the form (1) L : c i : = c i + 1; go to L ′ or (2 ) L : if c i = 0 the n goto L ′ else c i : = c i − 1; go to L ′′ where i ∈ { 1 , 2 } and L , L ′ , L ′′ are la bels preceding each instructio n. Furthermore th ere is a spec ial label L F from which nothing can be done. The haltin g problem consists then in decidi ng whether or not the execu tion that starts from L 0 with coun ters equal to 0 reaches L F . The intuitio n behind the reduction is as follo ws. In a first phase we explo it an expl oration protocol to impose a logical topology on top of the actual physical node connect ions. This logica l topology is compose d by a control nod e which is connect ed to two distinct lis ts of no des u sed to simula te the conte nt of the counters. E ach node in the list associate d to counter c i is either in state Z i or N Z i . The current v alue of the counter c i equals the number of N Z i nodes in the list. The length of each list is guesse d non-d eterminist ically during the exec ution of the first phase (i.e. befo re starting the simulation) and it corres ponds to the maximum value store in a counter for the simulatio n to succeed. I nitially , all nodes must encode zero (state Z i ). In the second phase the control node starts the simulation of the instructions . It operat es by sending reques ts that are propaga ted back and forth a list b y usin g broad cast sent by a node to i ts (unique) singl e- hop success or/pred ecessor node. The effect of these reques ts is to change the state of one node in zero state Z i to the non-zero state N Z i in case of increment, or the vice versa in the case of decrement. T he G. Delzanno , A. Sangnier , and G. Zav attar o 61 L 0 f irs t Z 1 Z 1 Z 1 Z 1 Z 1 Z 1 . . . f irs t Z 2 Z 2 Z 2 Z 2 Z 2 Z 2 . . . Figure 2: Butterfly-sh aped induced subgraph needed to simulate a Minsky machine . test-fo r -zero instruct ion on the counter c i is simply simulated by checkin g w hether there are no nodes in the zero state Z i in the i-th list. 2.5 Configurations with Bounded Path In [3] we hav e proved that C OV E R turns out to be decidab le if we restrict the possible topologies to the class of graphs w hose path is bounded by k (for a fixed k > 0). T he proof is based on the theory of W ell Structure d Tr ansitio n Systems [1, 2, 11] (WSTS ). A WSTS is a transition system equipped w ith a well- quasi orderi ng on states and a monotonic ity property: if a configura tion c 1 smaller than a configurat ion c 2 has a transition to a c onfigurat ion c ′ 1 , th en als o c 2 has a tra nsitio n to a con figuration c ′ 2 which is g reater than c ′ 1 . C ov erabi lity turns out to be decidable in WS TSs by using backward analysis, if it is possible to compute the predece ssors of a giv en state. In [3 ] we hav e observe d that ad hoc network protocols are monotoni c with respect to the induced subgra ph or dering relation , while this is not the c ase for the subgraph ordering relation . This is already an interes ting observ ation that distingu ishes selecti v e broadcast from point-to-po int communicatio n, which is m onoto nic with respect to the usual subgraph ordering . The proof of decidability is complete d by defining h o w to compute t he pr edecess ors, and by observ ing that th e ind uced su bgraph orde ring is a wqo for the class of graphs for which the length of simple paths is bounded by a constant (i.e. bounded path graphs ). This result is kno wn as Ding’ s Theorem [5]. 3 Configurations with Bounded Diameter As mentioned in the introduc tion, restrict ing protocol analysis to configuratio ns with bounde d p ath seems to hav e a limited application in a communication model with selecti ve broad cast. For these reason s, in [4] we hav e in v estige C OV E R for restricted classes of graphs that at least include the class of clique graphs. The first class we ha ve consider is that of graphs with bounded diameter . Fixed k > 0, a graph G has a k -bounded diameter if an d onl y if its d iameter is s maller than o r equ al to k . O bserv e that fo r e v ery k > 0, clique graphs belong to the class of graphs with a diameter bounded by k . Furthermore , giv en k > 0 the class of graphs with path bounded by k is included in the class of graphs w ith a diameter bounded by k . Graphs with k -boun ded diameter coinc ide with the so called k -clusters used in p artition ing algorithm for ad hoc networks [10]. Thus, this class is of particular rele v ance for the analysi s of selecti v e broadcas t communica tion. Intuiti v ely , the diameter corre spond s to the minimal number of broadcasts (hops ) need ed to send a message to all nodes connect ed by a path with the sender . 62 Paramete rized V erificatio n of Safety Properties in Ad Hoc Networks The C OV E R problem restricte d t o configurat ions wit h k -bounded diameter turns out to be undecidable for k > 1. The proof is similar to the proof of undecid ability for the general case reported in [3]: by reduct ion from the halting problem for two-coun ter Minsky machines. The main diff erence is that the logical topology to be imposed in the fi rst phase of the simulation of the Minsky machines should be with bounde d diameter (namely , diameter 2). The topolog y that w e ha ve con sidered is a sort o f b utterfly (see Figure 2) c onsisti ng of two list s (to represe nt the counters ) and in which all nodes in the lists are connected to a monitor node (to represent the program counter) . The second phase of the simulation, i.e. the actual exec ution of the instruc tions, proceeds similarly to the protoc ol describ ed abov e. The unique differ ence is that w e use a distinct f irst Z i node to distinguish the initial node of each list (this is needed as now all the list nodes are connected to the program counter node). Note that if we restrict our attentio n to graphs with a diameter bounded by 1, the abov e encoding does no t work an ymore . The class of graphs with d iameter 1 co rrespon ds to the s et of c lique graph s and, as said abov e, C OV E R turns out to be decid able w hen restric ting to clique topologies . Bounded diameter and bounded degr ee. From a non trivi al result on bounde d diameter graphs [13], we hav e obtained in [4] an interesting de- cidabl e subclass. Indeed, in [13] the authors show that, gi ven two integers k , d > 0, the number of graphs w hose diameter is smaller than k and whose degree is smaller than d is finite. The Moore bound M ( k , d ) = ( k ( k − 1 ) d − 2 ) / ( k − 2 ) is an upper bound for the size of the larg est undire cted graph in such a class. It follo ws that, for k , d > 0, and an ad hoc protocol w ith n states, if we restrict to configurations with a diameter bounded by k and a deg ree bounded by d , the state space is bounded by n M ( k , d ) , thus it is polynomia l in the size of the protocol. Consequen tly we can conclude that C OV E R restricted to configura tions with k -bounded diameter and d -bound ed deg ree is in P S P AC E . 4 Maximal Clique Graphs with Bounded Paths In this section w e describe classes of graphs that strictly increases both the classe s of clique graphs and the classes of bounded path graphs , for which we ha ve prov ed in [4] that C OV E R is decidable. W e hav e called thes e classes of graph s BP C n ( n -Bound ed Path max imal Cliq ues grap hs). Namely , for n > 0 BP C n contai ns both n -bounde d path graphs and any clique graph, while being strictly contained in the class of graphs w ith 2 n -boun ded diameter . These classes are defined on top of the notion of maximal clique gra phs associated to a configuratio n. Definition 4.1 Giv en a connec ted undirec ted graph G = h V , E , L i and • 6∈ L ( V ) , the maximal clique gra ph K G is the bipart ite graph h X , W , E ′ , L ′ i in which • X = V ; • W ⊆ 2 V is the set of maximal cliqu es of G ; • For v ∈ V , w ∈ W , h v , w i ∈ E ′ if f v ∈ w ; • L ′ ( v ) = L ( v ) for v ∈ V , and L ′ ( w ) = • for w ∈ W . Note that for each connected graph G there exists a unique maximal clique graph K G . An example of constr uction is gi ven by Figure 3 . One can also easily prov e that if G is a clique graph then in K G there is no path of length strictly greater than 3. Furthermore, from the maximality of the cliques in W if two G. Delzanno , A. Sangnier , and G. Zav attar o 63 G K G Figure 3: A graph G and its assoc iated clique graph K G . nodes v 1 , v 2 ∈ V are connect ed both to w 1 and w 2 ∈ W , then w 1 and w 2 are distinct cliques . W e use the notati on v 1 ∼ w v 2 to deno te that v 1 , v 2 belong to the same clique w . Definition 4.2 For n ≥ 1, the cl ass BP C n consis ts of the set of configurati ons whose associ ate maximal clique graph has n -boun ded paths (i.e. the length of the simple paths of K G is at most n ). The proof of decidability of C OV E R for BP C n graphs is based on an ordering defined on maximal clique graphs that correspon ds to the induced subgraph ordering defined on the correspond ing graphs. Such a ne w ordering is defined as follo ws. Definition 4.3 Ass ume G 1 = h V 1 , E 1 , L 1 i with K G 1 = h X 1 , W 1 , E ′ 1 , L ′ 1 i , a nd G 2 = h V 2 , E 2 , L 2 i with K G 2 = h X 2 , W 2 , E ′ 2 , L ′ 2 i with G 1 and G 2 both connected graphs. Then, G 1 ⊑ G 2 if f there exist two injecti v e functi ons f : X 1 → X 2 and g : W 1 → W 2 , such that (i) for e v ery v ∈ X 1 , and C ∈ W 1 , v ∈ C iff f ( v ) ∈ g ( C ) ; (ii) for e v ery v 1 , v 2 ∈ X 1 , an d C ∈ W 2 , if f ( v 1 ) ∼ C f ( v 2 ) , th en th ere ex ists C ′ ∈ W 1 s.t. f ( v 1 ) ∼ g ( C ′ ) f ( v 2 ) ; (iii) for eve ry v ∈ X 1 , L ′ 1 ( v ) = L ′ 2 ( f ( v )) ; (iv) for ev ery C ∈ W 1 , L ′ 1 ( C ) = L ′ 2 ( g ( C )) . The first condition ensures that (dis)conne cted nodes remain (dis)conn ected inside the image of g . In- deed, from po int (i) it follo ws that, for e v ery v 1 , v 2 ∈ X 1 , an d C ∈ W 1 , v 1 ∼ C v 2 if f f ( v 1 ) ∼ g ( C ) f ( v 2 ) . The second condi tion ensures that disconnec ted nodes remain discon nected outside the image of g . By condition (i) in the definition of ⊑ , we also hav e that G 1 ⊑ G 2 (via f and g ) implies that K G 1 is in the induced subgra ph relation with K G 2 (via f ∪ g ). T he relation between this new relation and the induce d subgraph orderi ng is e v en str onger , in fact we ha v e pro ved in [4] t hat the two coin cide: G 1 ⊑ G 2 if f G 1 is an induce d subgraph of G 2 . The main theorem in [4] states that for any n ≥ 1, ( BP C n , ⊑ ) is a well-quasi ordering . In the light of the corresp ondanc e result between ⊑ and the induced subgraph orderi ng, and the monotonicit y of ad hoc network protoco l with respect to the induced subgrap h orderin g relatio n (and the computab ility of the predeces sors) discusse d the previo us section, we hav e been able to prove in [4] the decidability of C OV E R for topologies restricted to graphs in BP C n (for a fixed n > 0). In [4 ] we hav e in v estigat ed also the comple xity of the decision procedure for C OV E R restricte d to topolo gies in BP C n . W e hav e f ound that this problem is not primiti v e r ecursi v e. The proof is by reduct ion from the cov erabil ity problem for reset nets, which is known to be an Ack ermann- hard problem [21]. 5 Conclusions In this pape r we ha ve reported th e m ain result that we hav e recent ly pro v ed in [3, 4 ] abou t th e decidability and comple xity bounda ries for the d ecidab ility an d the comple xity of the parametr ic verificatio n of safety proper ties in ad hoc networks . Namely , giv en an ad hoc networ k protocol express ed as a finite state 64 Paramete rized V erificatio n of Safety Properties in Ad Hoc Networks communica ting a utomaton , we are interested in checking the exi stence of an initi al networ k configurat ion that can g enerat e a computat ion leading to a configurati on in which at lea st one no de is in a gi ven (error) state. The problem is undecid able if no restricti ons are imposed to the possible initial configurat ions, but it turns out to be decidable for interesting classes of graphs in which the correspo nding maximal cliques are connected by paths of bounded length. These graphs include both cliques and bounded path graphs. The proble m returns to be undecidab le for bounde d diameter graphs. As a f uture work, we plan to st udy deci dabilit y and complex ity issues in pre sence of communi cation and node failu res. In particular , an interest ing case of communication failur e in the contex t of ad hoc netwo rks is due to conflicts deriv ing form the contempora neous emission of signals from two distinc t nodes that share some neighbors . W e plan to mov e to a truly concu rrent semantics for ad hoc netwo rk protoc ols in order to faithfull y represent this specific phenomenon . Refer ences [1] P . A. Ab dulla, C. ˇ Cer ¯ ans, B. Jon sson & Y .-K. T say (199 6): Gene ral decid ability theor ems for infinite- state systems . In : LICS’96 , IEEE Computer Society , pp. 313–32 1. [2] P . A. Abdu lla, C. ˇ Cer ¯ ans, B. Jonsson & Tsay . Y .-K. (2000 ): Algorithmic an alysis of pr ograms with well quasi-order ed domain s . Inf. Comput. 160(1 -2), p p. 109– 127. [3] G. Delzanno , A. Sangn ier & G. Za v attaro (2010): P arameterized V erification of Ad Hoc Netw orks . In: CONCUR’10 , Lecture Notes in Comp uter Science 6269, Springe r , pp . 313– 327. doi: 10.1007/ 978- 3- 642 - 15375- 4_22 [4] G. Delzann o, A. Sangnier & G. Za vattaro (2 011): On the P ower of Cliques in the P arameterized V erificatio n of Ad Hoc Networks . In: FOSSA CS’11 , Lecture No tes in Computer Scienc e 6604, Springer, p p. 441–4 55. doi: 10.1007/978- 3- 642 - 19805- 2_30 [5] G. Ding (19 92): Subg raphs an d well quasi or dering . J. of Graph Theory 16(5) , p p. 489 – 502. [6] E. A. Emerson & K. S. Namjo shi (199 8): On Mo del Checking for Non -Deterministic Infin ite-State Systems . In: LICS’98 , IEEE Computer S ociety , pp. 7 0–80 . [7] C. Ene & T . Mun tean (2 001): A Br oadca st b ased Calculus for Communicatin g S ystems . In: IPDPS ’01 , p . 149. [8] J. Esparza , A. Finkel & R. May r (199 9): On the V e rification of Br oadca st Pr otocols . In: LICS’99 , IEEE Computer Society , pp . 352–35 9. [9] A. Fehnker , L. v an Ho esel & A. Ma der (2007): Mo delling a nd verification of the LMAC pr otocol fo r w ir eless sensor networks . In: IFM’07 , Lecture No tes in Comp uter Science 4591, Spring er , pp. 253 –272. do i: 10. 1007/978- 3- 540 - 73210- 5_14 [10] Y . Fernan dess & D. Malkh i (20 02): K-clustering in wir eless ad hoc networks . In: POMC’02 , AC M, pp. 31–37 . d oi: 10.1145/584490 . 58449 7 [11] A. Finkel & P . Sch noebelen (200 1): W ell-structur ed transition systems everywher e! Theoretical Comp uter Science 256(1 -2), p p. 63–92. doi: 10.1016/S0304- 397 5(00) 00102- X [12] J.C. Go dskesen (2007): A Calculus for Mobile Ad Hoc Networks . In: COORDIN A TION ’07 , pp. 132–150. [13] A.J. Hoffman & R.R. Singleton (196 0): On Moore graphs with diameter 2 and 3 . IBM J. Res. Develop. 4, pp. 497– 504. doi: 10.1147/ rd.45.0497 [14] Ivan Lanese & Davide Sangiorgi (2 010): An o perational semantics for a calculus for wir eless systems . The- oretical Computer Science 411(1 9), p p. 1928–19 48. d oi: 10.1016/j.tcs.2010.01.023 [15] M. Mer ro (2009): An Observational Theory for Mobile Ad Hoc Network . Inf. Comput. 207(2 ), pp . 194–208. doi: 10.1016/j.ic.2007.11.010 G. Delzanno , A. Sangnier , and G. Zav attar o 65 [16] R. Meyer (2008): On boundedn ess in dep th in the pi-ca lculus . In: IFIP TCS’08 , IFIP 477–4 89, Sp ringer, p p. 477–4 89. [17] S. Nanz & C. Hankin (200 6): A F ramework for Security Analysis of Mobile W ir eless Networks . TCS 367(1 – 2), pp. 203–2 27. d oi: 10.1016/j.tcs.2006.08.036 [18] K.V .S. Prasad (199 5): A Calculus o f Br oadcasting Systems . Sci. of Comp. Prog. 25(2- 3), p p. 285– 327. doi: 10.1016/0167- 64 23(95 )00017- 8 [19] Miln er R. (1999 ): Commu nicating and Mobile Systems: the Pi-Calc ulus . Cambridg e Uni v . Press. [20] M. Saksena, O. W iblin g & B. Jonsson (2008): Graph grammar modeling and verificatio n of Ad Hoc R outing Pr otocols . In: T ACAS ’08 , Lecture No tes in Compu ter Scien ce 4963, Spring er , pp. 18 –32. doi: 10 .1007/ 978- 3- 540 - 78800- 3_3 [21] P . Schnoebelen (2010 ): Revisiting Ack ermann-Hardness for Lossy Counter Machines and R eset P etri Nets . In: MFCS’10 , Lecture Notes in Computer Science 6281, Springer, pp. 616 –628. do i: 10.1007/ 978- 3- 642 - 15155- 2_54 [22] A. Sing h, C. R. Ramakrishn an & S. A. Smolka ( 2006) : Mod eling the AOD V r outing pr otocol in o me ga- calculus . In: LISA T ’06 . [23] A. Singh , C. R. Ramakrishnan & S. A. Smolka (2008) : A Pr ocess Calculus for Mobile Ad Hoc Networks . In Springer, editor : COORDIN A TION ’08 , Lecture Notes in Computer Science 5052, pp. 296–3 14. [24] A. Singh, C. R. Ramakr ishnan & S. A. Smo lka (200 9): Query-Based model checking of Ad Hoc Network Pr otocols . In: CONCUR’09 , Lecture Notes in Computer Science 5710, Springer, pp. 603 –61. [25] T . W ies, D Zu fferey & T . A. Hen zinger ( 2010) : F orwar d a nalysis o f depth-b ound ed p r ocesses . In: FOSSA CS’10 , Lecture Notes in Computer Science 6014, Springer, pp. 94 –108 . doi: 10.1007/ 978- 3- 642 - 12032- 9_8
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment