Quantum cryptography
This is a chapter on quantum cryptography for the book "A Multidisciplinary Introduction to Information Security" to be published by CRC Press in 2011/2012. The chapter aims to introduce the topic to undergraduate-level and continuing-education stude…
Authors: Dag Roar Hjelme, Lars Lydersen, Vadim Makarov
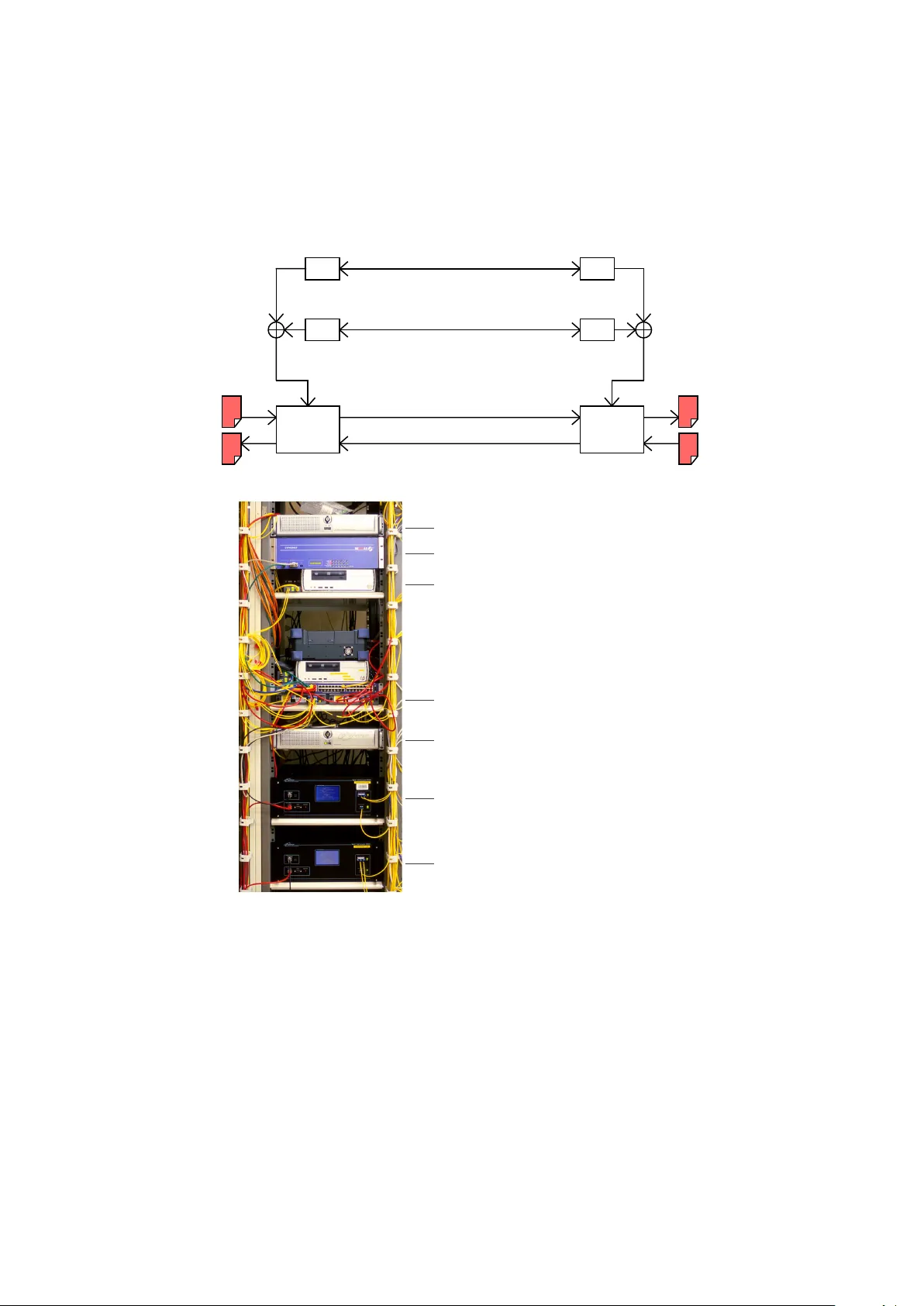
Chapter 5. Quan tum Cryptograph y Dag Roar Hjelme Departmen t of Electronics and T elecomm unications, Norw egian Univ ersity of Science and T ec hnology , NO-7491 T rondheim, Norwa y dag.hjelme@iet.n tn u.no Lars Lyde rsen Departmen t of Electronics and T elecommunications, Norw egian Univ ersity of Science and T ec hnology , NO-7491 T rondheim, Norwa y Univ ersit y Graduate Cen ter, NO-2027 Kjeller, Norw ay lars.lydersen@gmail.com V adim Mak aro v Departmen t of Electronics and T elecommunications, Norw egian Univ ersity of Science and T ec hnology , NO-7491 T rondheim, Norwa y Univ ersit y Graduate Cen ter, NO-2027 Kjeller, Norw ay mak arov@v ad1.com August 7, 2011 Abstract This is a c hapter on quan tum cryptograph y for the b o ok “A Mul- tidisciplinary In tro duction to Information Securit y” to b e pub- lished by CRC Press in 2011/2012. The chapter aims to introduce the topic to undergraduate-level and contin uing-education students sp ecializing in information and comm unication tec hnology . 5.1 In tro duction When information is transmitted in microscopic systems, suc h as single photons (single ligh t particles) or atoms, its information carriers ob ey quantum rather than classical physics. This offers many new possibilities for information pro- cessing, since it is possible to in ven t nov el information processes preven ted b y classical ph ysics. Quan tum cryptograph y is the most mature technology in the new field of quan tum information pro cessing. Unlik e cryptographic techniques where the securit y is based on unprov en mathematical assumptions, 1 the securit y of quan- tum cryptograph y is based on the la ws of ph ysics. T o day it is dev elop ed with an eye to w ards a future in whic h cracking of classical public-k ey ciphers migh t b ecome practically feasible. F or example, a quan tum computer might one da y b e able to crack to day’s codes. The one-time pad 2 remains unassailable ev en 1 F or instance, the security of RSA public-k ey cryptograph y (Chapter 3) rests on the widely- believed assumption that the factorization problem is computationally hard. Although no efficient factorization algorithm is publicly kno wn, it has not been pro ven that one does not exist. Shor’s algorithm for a quantum c omputer already allows efficien t factorization, how ever it remains an op en question if and when a scalable quantum computer is built. F urthermore, once a classical encryption is broken, the crack can b e applied to to day’s secrets r etr oactively. This is uncomfortable for many t yp es of secret information whose v alue persists for decades: go vernmen t and military communication, commercial secrets, as w ell as certain personal information such as financial and medical records. 2 It has b een prov en that a secure cipher needs to use the amount of secret k ey at least as large as the length of the message [16]. The one-time pad (Section 3.2) is one suc h cipher. 1 b y suc h future tec hniques. The w eakness of the one-time pad is that a secret, random, symmetric k ey as long as the mess age it is in tended to encrypt m ust b e securely distributed to the message’s intended receiv er. F urthermore, the k ey can only b e used once. Quan tum cryptograph y solv es this key distribution problem in a wa y unfeasible using only classical ph ysics, b y exploiting how single quan tum particles b eha v e. The working principles of quantum cryptography can simply b e explained b y considering information transmission using single photons. A single photon can represen t a quan tum bit, a so-called qubit. T o determine the qubit v alue one m ust measure the represen ting property of the photon (for example p olariza- tion). According to quan tum physics, suc h a measurement will inevitably alter the same prop erty . This is disastrous for any one trying to ea vesdrop on the transmission, since the sender and receiv er can easily detect the c hanges caused b y the measurement. Since the securit y can only b e determined after a trans- mission, this idea can not b e used to send the secret message itself. Ho wev er, it can b e used to transmit a secret, random, symmetric key for one-time-pad cryptograph y . If the transmission is in tercepted, the sender and receiver will detect the ea vesdropping attempt, 3 the key can be discarded and the sender can transmit another k ey un til a secure k ey is receiv ed. In spite of the simple principles b ehind quantum cryptograph y , the idea w as first conceived as late as 1970 in an unpublished man uscript written b y Stephen Wiesner. The sub ject receiv ed v ery little attention un til its resurrection b y a classic pap er published by Charles Bennett and Gilles Brassard in 1984. Curren tly , the tec hnology required for quantum cryptography is av ailable for real-w orld system implemen tations. The ob jective of this chapter is to present the w orking principle of quan tum cryptograph y and to give examples of quan tum cryptograph y proto cols and implemen tations using technology av ailable today . Throughout the c hapter we minimize the use of quan tum ph ysics formalism and no previous kno wledge of quan tum physics is required. References are pro vided for the interested reader who crav es for more details. A go o d starting p oin t is the excellen t review by Gisin et al. [6]; also the original pap er [1] explains the quan tum cryptograph y proto col v ery w ell. 5.2 Quan tum Bit All information can b e reduced to elementary units, which w e call bits. Each bit is a yes or no that can b e represented b y the num b er 0 or the num b er 1. Ho wev er, as we w ill see, reading and writing this information to a qubit is something quite differen t from reading and writing this information to a classical bit. W e can think of a (qu)bit as a box, where w e can store one of the tw o bit v alues b y putting a ball with one out of t wo colors in to the b ox as illustrated in Figure 5.1. T o read the bit v alue of the b ox, we simply op en the b o x and register the color of the ball inside. F or the classical bit, the color of the ball inside is alwa ys the same as the color of the ball stored in the box in the first 3 No such p ossibility exists if the key is exchanged using classical physics because classical bits can be read, and hence copied without the risk of destroying the original bit v alue. 2 X X Z (a) (b) Figure 5.1: Classical v ersus quan tum bit. (a) Classical bit: If we put the ball in a classical b ox, the color of the ball that p ops out is the same as the color w e put in. (b) Qubit: If we put the ball in a quan tum b ox and op en the wrong do or, the color of the ball that comes out is random. place. Ho wev er, this is not necessarily the case for qubits. 4 In the quantum formalism, the tw o differen t do ors of the b ox represent tw o differen t wa ys of measuring the qubit v alue. T o read the correct bit information we need to kno w whic h do or was used when the qubit was stored, and use the same do or. If we op en the wrong do or, the ball inside will ha v e a random color, and thus the information stored in the qubit will change to a random bit v alue. This also means that the stored information is destro y ed. One realization of the qubit is a polarized photon. One w ay of determining the p olarization of the photon is to send it through a p olarizing b eamsplit- ter, and measure at whic h output of the p olarizing b eamsplitter the photon is found. 5 Ho w ever, since the p olarizing b eamsplitter only separates b etw een orthogonal p olarizations, we cannot orien t the p olarizing b eamsplitter at tw o angles at the same time. Thus, w e can not read the qubit v alue unless we hav e additional information. F or example, if w e know that the p olarization is either horizon tal or vertical in a defined reference co ordinate system 6 w e can read the qubit v alue by orienting the b eamsplitter to the axis of the co ordinate system. If w e find a photon at one output of the beamsplitter w e know that the photon p olarization was horizontal; if we find it at another output the polarization w as v ertical (see Figure 5.2). That is, we need to know a priori which coordinate system is used in preparing the qubit to read it correctly . If we use another orien tation of the b eamsplitter, the result of the measurement will b e random just lik e when op ening the wrong door of the quan tum b ox in Figure 5.1. Note that once the photon has b een detected in one of the outputs after the b eam- splitter, the photon actually assumes the output polarization, with no trace of its original p olarization left – this is ho w the nature works at the quan tum level. 4 W e hav e borrow ed this wa y of visualizing a qubit from John Preskill [14]. 5 A p olarizing b eamsplitter is a device that separates orthogonal linear polarizations of incoming light into tw o directions. 6 In quantum physics the orientation of the b eamsplitter is called the basis. 3 (a) (b) (c) 100% 0% 50% 50% Figure 5.2: Qubit as a p olarized photon. (a) A photon source is follo wed by a linear polarizer to generate a qubit with the desired polarization, in this case a horizon tally p olarized photon. (b) When a horizontally polarized photon passes through a horizontally-v ertically oriented p olarizing b eamsplitter, it is alwa ys found at the exit of the b eamsplitter corresp onding to the horizon tal polariza- tion. (c) When a horizontally polarized photon passes through a diagonally orien ted beamsplitter, the photon has 50% probability to b e found at eac h exit (but the photon will only b e detected at one of the exits!). F urthermore, the photon will hav e a corresponding diagonal polarization afterwards. Therefore, the measuremen t has c hanged the state of the photon. 5.3 Quan tum Cop ying T o copy a qubit w e need to read the bit v alue, i.e., w e need to op en the quan tum b o x. Ho wev er, there is no wa y of kno wing whic h door w as used to store the bit v alue of the qubit. If we simply guess one of the do ors w e ma y damage the information stored in qubit. Th us generally , since quantum bits cannot b e p erfectly read, quan tum bits can not b e p erfectly copied either. 7 Usually , the abilit y to cop y information is considered to b e very useful. But, in secure comm unication, this w ould b e disastrous since the ea vesdropper could listen to the comm unication and keep a copy of the message. Ho wev er, qubits cannot b e copied. This non-copying prop ert y of quantum information can b e exploited for secure comm unication. Therefore qubits can be used to distribute a key from sender to recipient without the p ossibility for the eav esdropp er to obtain a cop y surreptitiously . 5.4 Quan tum Key Distribution Quan tum cryptograph y is not used directly to transmit the secret information, but is rather used to distribute a random secret k ey , see Figure 5.3. Once the k ey has successfully b een transmitted, it can b e used in a classical symmetric cipher (suc h as the one-time pad described in Section 3.2 or AES describ ed in Section 2.2.2) to encrypt and decrypt information. Let’s consider the quan tum k ey distribution proto col. 5.4.1 The BB84 Protocol T o explain the proto col, let us call the sender Alice, and the receiver Bob. Assume that Alice generates a random sequence of bits, co des them in qubits randomly using do or X or do or Z of the quan tum b ox, and sends the qubits o v er a quantum c hannel to Bob. Bob do es not know whic h do ors Alice used, 7 F or a strict quantum-mec hanical pro of of this fact, see [23]. The pro of is very short. 4 Alice Bob Encoder Decoder Message Message Public (insecure) channel Encoded message Random secret key Quantum key distribution channel Figure 5.3: Using quan tum key distribution in a symmetric encryption sc heme. The first step is distribution of a secret key betw een Alice and Bob. Then, the k ey can be used b y a symmetric cipher to enco de and deco de transmitted information. and therefore he randomly picks doors. The result is that Bob op ens the right do or only half the time. In those cases he reads the righ t information. Bob’s bits are called the ra w k ey at this stage. After Bob has op ened all the quan tum b o xes, both he and Alice publicly announce whic h doors were used to store and measure the qubits v alues. They then keep only the qubit v alues from the b o xes where they happened to use the same doors. This random sequence of bits no w shared by Alice and Bob is called the sifted k ey , and is ab out half as long as the original ra w k ey . What happens if the eav esdropp er Eve tries to op en some of the quan tum b o xes during the transmission? If Ev e b y c hance op ens the right do or she can cop y the information and send it to Bob. How ever, half of the time she will op en the wrong door and might c hange the v alue of the qubit. If Alice and Bob conduct a test and compare a small p ortion of their k ey , they can make sure that Bob receiv ed what Alice sen t. If Alice’s and Bob’s p ortion of the key matc hes, they can b e confident that Eve did not op en an y b oxes. On the other hand if their k eys do not agree, they kno w that Ev e tried to measure the k ey . What w e ha ve just described is the quan tum k ey distribution protocol BB84, first presented in 1984 by Bennett and Brassard. Giv en that Alice and Bob can only measure the fraction of errors in the key , often called the quantum bit err or r ate, the proto col either provides a prov ably secure k ey or informs Alice and Bob that the k ey distribution failed. 5.4.2 The BB84 Protocol Using P olarized Light The BB84 protocol can b e implemen ted using p olarized single photons as il- lustrated in Figure 5.4. Alice codes the qubit using horizon tal (bit v alue 0) and v ertical (bit v alue 1) p olarization, or she co des the qubit using − 45 ◦ (bit v alue 0) or +45 ◦ (bit v alue 1) polarization. 8 T o receiv e the qubits Bob uses t wo in terc hangeable p olarizing beamsplitters and tw o photon detectors 9 after the b eamsplitter. One p olarizing beamsplitter allows Bob to distinguish b et ween the horizon tal and vertical p olarizations and the other p olarizing beamsplitter allo ws Bob to distinguish b et ween the − 45 ◦ and +45 ◦ p olarizations. If Bob 8 These tw o wa ys of doing the coding represent the tw o do ors of the quan tum b oxes de- scribed earlier. 9 A photon detector is a device that gives a signal (‘click’) when a photon arriv es at the device. 5 Sifted key – – 1 0 0 – 1 0 0 – 1 – 0 0 0 1 0 0 1 1 0 0 0 1 0 0 Alice’ s bit sequence 0 1 1 0 0 1 1 0 0 1 1 1 0 Photon source Alice Bob 0 0 1 1 Photon detectors 0 1 1 1 1 Horizontal-vertical polarizers Diagonal polarizers Horizontal-vertical beamsplitter Diagonal beamsplitter Bob’ s measurement Bob’ s detection basis Sifted key Figure 5.4: BB84 protocol using p olarized light (reprin ted from [20]). uses a polarizing b eamsplitter compatible with the polarization choice of Alice he will read the state of polarization correctly , i.e., he op ened the right do or. If Bob uses a p olarizing beamsplitter incompatible with the p olarization c hoice of Alice he will not b e able to get any information about the state of polarization, i.e., he op ened the wrong do or. After receiving enough photons, constituting the raw key , Bob announces o v er a public classical comm unication c hannel (e.g., ov er an internet connection) the sequence of p olarizing b eamsplitters he used, but importantly not the result of the measuremen t. Alice compares this sequence to the sequence of bases (p olarization c hoice) she used and tells Bob on whic h o ccasions he used the righ t beamsplitter, 10 but importantly not the p olarization she sent. F or these bits, constituting the sifted key , Alice and Bob kno w that they hav e the same bit v alues pro vided that an ea v esdropp er did not p erturb the transmission. T o assess the security of the transmission, Alice and Bob select a random subset of the sifted key and compare it ov er the public channel. If the trans- mission were in tercepted or perturb ed, the correlation betw een their bit v alues will b e reduced, th us increasing the quantum bit error rate. All ea v esdropping strategies p erturb the system in some w ay . Therefore, if Alice and Bob do not measure any discrepancy in the subset of the key , they can b e confiden t that the transmission was not intercepted and they can use the remaining part of the k ey for encryption. 5.5 Practical Quan tum Cryptography An y implementation of quantum key distribution uses tec hnology av ailable to- da y , meaning that the system comp onen ts such as photon sources, transmission c hannel, p olarizing beamsplitters, and photon detectors, are imp erfect. This fact has sev eral imp ortan t implications. 10 Effectively publicly announcing which door of the b ox w as used to store eac h qubit. 6 One imperfection common to all comp onents is that photons sometimes get lost. In a practical system, the ma jority of the photons exiting Alice will get absorb ed in the transmission c hannel, and those that reac h the detector will often fail to cause a click. In practice only the photons that hav e registered as clic ks in Bob’s detectors con tribute bits to the ra w k ey . Another implication of imp erfections is that the qubits are prepared and detected not exactly in the basis as described b y theory . T echnological imp er- fections will lead to errors in the sifted k ey , errors that can not b e distinguished from errors resulting from any ea vesdropping attempts. Realistic error rates with to day’s technology are in the order of a few percent. This quan tum bit er- ror rate is often dominated b y false detection signals from the photon detectors, so-called dark c ounts. 11 5.5.1 Error Correction and Priv acy Amplification Alice and Bob can not b e sure whether the errors in the sifted key resulted from device imp erfections or from ea vesdropping. They ha ve to assume the w orst and assume all errors w ere due to eav esdropping. At this p oint in the protocol, Alice and Bob share classical information with high but not 100% correlation, and assume that the third party Ev e has partial knowledge of this information. This problem can b e solv ed b y classical information theory , which has metho ds of distilling a shorter, error-free k ey of whic h Ev e has no kno wledge about. First, Alice and Bob need to apply classical error correction techniques to ob- tain identical keys. 12 Ev e still kno ws some information ab out this key (actually she knows even more than b efore, b ecause Alice and Bob hav e had to rev eal more information while comm unicating publicly during the error correction). The last step in the quantum cryptograph y proto col therefore is a privacy am- plific ation procedure that shrinks the key and reduces the amount of information Ev e may kno w ab out it. Alice and Bob do priv acy amplification by applying a randomly chosen hash function of universal 2 -class to the error-corrected key . 13 As long as Bob has more information ab out Alice’s sifted key than Eve, priv acy amplification will pro duce a shorter final key about which Eve’s information is arbitrarily small. T o giv e a feel for the num b ers, with realistic quan tum bit error rate of 4%, assumed to b e dominated b y ea v esdropping, 2000 bit can b e distilled down to 754 secret bit about whic h Eve’s information is negligible (less than 10 − 6 bit). With quantum bit error rate of 8% we can distill 105 secret bit from the original 2000 bit [1]. The resulting w orkflo w of a general quantum k ey distribution algorithm is illustrated in Figure 5.5. 11 Dark counts are clicks in detector without an y photons presen t, and can thus b e observed at the detector output in the dark. 12 V ery high raw error rate of a few percent, while t ypical for quan tum cryptograph y , usually does not occur in classical telecomm unication. Therefore, sp ecial error correction algorithms hav e b een developed for quantum cryptography . 13 These hash functions and this application are different from those described in Chapter 4. While the security of cryptographic hash functions in Chapter 4 in not proven, here the security of the priv acy amplification procedure [2] is unconditional, i.e., strictly prov en against an adversary who p ossesses unlimited computing p ow er. 7 Shorter , error -free, secure key Quantum transmission (Figure 5.4) Privacy amplification Error correction Sifting Raw key Sifted key Error-free, partially secure key Equation from the security proof R = f (input parameters) A vailable secure key fraction R < 1 Estimate of error rate Information leakage during error correction Figure 5.5: Classical p ost-pro cessing in quan tum key distribution. Alice and Bob start with the ra w photon detection data, comm unicate ov er an authen- ticated classical c hannel while p erforming sifting, error correction and priv acy amplification pro cedures, and arrive at a secret shared key about which Ev e has negligible information. 5.5.2 Securit y Pro ofs The intuition as to wh y quan tum k ey distribution pro vides perfectly secret key is quite straigh tforward. How ever, the details of the pro ofs are v ery inv olved [15]. If one assumes that Ev e can only interact with one qubit at a time, 14 and that Alice and Bob are using a p erfect implemen tation of the proto col, it has b een pro v en that Eve will never kno w as muc h as Bob provided that the quantum bit error rate is less than 14.65%. If Ev e has unlimited p ow er and can coherently attac k an unlimited num b er of qubits, 15 i.e., she can do ev erything allo wed b y the known laws of physics, it has b een pro ven that a quantum bit error rate less than 11% is required for secure comm unication. As long as the error rate is b elo w this threshold, the securit y proof pro vides an equation that can b e used to compute the required amoun t of priv acy amplification (Figure 5.5). The security has been pro ven strictly for certain idealized models of equip- 14 This is a so-called individual attack. 15 This is a so-called coherent attack. 8 men t. Ho wev er, most of the current discussion is whether imperfections in real hardw are (not yet accounted by the pro ofs) ma y leav e lo opholes, and how to close these lo opholes [5]. 5.5.3 Authen tication One problem remains: ho w can Alice and Bob be sure they really talk to each other on the public c hannel and not to Eve, when they pro duce secret key? Eve could be in the middle b et w een Alice and Bob, represen ting herself as Bob to Alice and as Alice to Bob. The prev ention of this is kno wn and requires that Alice and Bob start from an initial short common secret (a few hundred bit), so as to be able to recognize eac h other during their first run of the proto col. 16 After the first successful key distribution, they can use a part of the secret key they pro duce to authen ticate in future runs. It has been prov en that quan tum k ey distribution pro vides muc h more secret key than it consumes in authen ti- cation. 17 In this sense, quantum key distribution is a quantum secret gro wing proto col. The need for initial authen tication is intrinsic and univ ersal to all flav ors of cryptograph y: ho w else can y ou verify that you are talking to the in tended part y and not to Eve? The initial trusted k ey and/or biometric authentication (b y , e.g., verifying a pen signature, talking to a kno wn p erson o ver phone or b eing physically present during the transaction) is found in some form in all cryptographic proto cols. 5.6 T ec hnology Essen tially tw o tec hnologies make quantum cryptograph y possible: single pho- ton sources and single photon detectors. In addition, a transmission channel for the single photon states, so-called quan tum c hannel, is needed. The rest of the system is realized using fairly standard telecommunication and electronic hardw are. 5.6.1 Single Photon Sources Single photon sources are difficult to realize. Therefore, most systems to day rely on fain t laser pulses. Conv entional laser pulses, e.g., from a semiconductor laser, are attenuated such that there is on the av erage less than one photon p er pulse. The problem with this approach is that there is a significan t probabilit y that there are tw o or more photons per pulse, unless the a verage photon num b er is far b elow one. The n umber of photons in the pulse follo ws P oisson statistics, 16 Unconditionally secure authentication is emplo y ed, using hash functions of ‘almost’ universal 2 -class [22]. The secret k ey is used to pick a function from the set of hash func- tions, then that function is applied to the message to compute a shorter authentication tag. The message and authentication tag are sent to the other comm unicating party . The latter computes an authentication tag on the received message using her copy of the secret key , and compares it with the received tag. If the tags are the same, this guaran tees that the messages are the same with a high probability . The use of one-time pad to pick the hash function guarantees against attacks on this authentication scheme. 17 While perfect encryption, e.g., the one-time pad needs m secret bits to encrypt an m -bit message, p erfect authen tication only needs in the order of log( m ) secret bits to authenticate an m -bit message. 9 whic h for instance means that in a pulse of a v erage photon num b er 0.1, there is a 0.9048 probability to find no photons, 0.0905 probabilit y to find one ph oton, and 0.0047 probability to find t wo or more photons. If Alice emits pulses containing more than one photon, Eve can take and store one of the photons in the pulse un til the basis is announced. Then she ma y perform a p erfect measurement in this basis, learning the bit v alue of the qubit sen t to Bob. Therefore, the presence of multiphoton pulses decreases the secret key rate. The fraction of m ultiphoton pulses relativ e to single-photon pulses can b e reduced b y decreasing the a verage photon n um b er, ho wev er when the av erage photon num b er is small it means that most bit slots are empty , also resulting in low er bit rate. In principle, the latter could b e comp ensated for by increasing the pulse rate. Ho w ever, another drawbac k rema ins, as the dark coun ts (false detection ev ents) in the single photon detectors are significant. The result is that the signal to noise ratio decreases, raising the quan tum bit error rate, as the a verage photon n um b er decreases. The ideal photon source is a device that emits single photons on demand. 18 Although progress is rep orted, practical devices are not yet a v ailable [17]. Nev ertheless, practical operation o ver tens of kilometers has b een ac hieved using faint laser pulse sources. Also, there are adv anced protocols 19 that allow secure op eration ov er longer than 100 km distance with the fain t laser pulse source. 5.6.2 Single Photon Detectors Single photon detection can b e realized in a num b er of wa ys, e.g., using pho- tom ultipliers, a v alanc he photo dio des, as well as several t yp es of more exotic sup erconducting devices that ha ve to b e cryogenically cooled below 4 K. 20 T o- da y the best and in fact the only practical choice for quantum cryptography is the av alanc he photo dio de [3]. An av alanche photo dio de is a semiconductor comp onen t, and to detect single photons it is op erated under a large v oltage. 21 If a single photon is absorb ed b y the semiconductor, it excites a single electron. The high electric field in the semiconductor ensures that this initial electron collides with the lattice and excites more electrons, th us b eing amplified in to an a v alanc he of electrons (sev eral thousands). This a v alanc he is large enough to b e detected as a curren t pulse b y an external circuit. Unfortunately , an av alanche can also o ccur without a photon, initiated by thermal excitation, tunneling, or emission of trapped carriers. The latter happens when electrons from a pre- vious a v alanc he get stuck in defects of the semiconductor lattice, then slowly released. This emission of trap p ed carriers limits the practical count rate. This is a serious limitation in the current systems using faint laser pulses, where a high pulse rate is desirable in order to achiev e acceptable bit rates. 5.6.3 Quan tum Channel Alice and Bob m ust be connected b y a quan tum channel. This c hannel must b e suc h that the qubit is protected from environmen tal noise. Standard single-mo de 18 Such a source is often called a photon gun. 19 F or example the decoy-state protocol [9]. 20 F or a wide review of photon detection techniques, see [7]. 21 The photodio de is reverse biased abov e its breakdo wn voltage. 10 optical fib er used for data and telecommunication is an almost ideal channel for single photon states (qubits). All optical fib ers hav e transmission losses limiting the n um b er of qubits arriving at the detector. This has direct impact on the key exc hange rate, as the raw key rate is directly proportional to the photon transmission probability of the link. Mo dern telecomm unication fib ers ha v e transmission losses of ab out 2 dB/km, 0.35 dB/km and 0.2 dB/km in the commonly used communication w av elength windows of 800 nm, 1300 nm and 1550 nm respectively . A t 1550 nm this means that at least 50% of the photons are lost at 15 km, or 99% of the photons are lost at 100 km. The longest successful quantum k ey distribution rep orted in lab oratory conditions to date is 250 km, at a v ery slow rate of 15 secret bit/s indeed [19]. T oday’s commercial systems are limited to 50–100 km. All fibers are sub ject to en vironmental fluctuations, suc h as a c hange in tem- p erature. This p erturbs a p olarization state, and therefore changes the qubit v alues. Thus, the error rate is increased b y the imp erfect c hannel. The global effect of this polarization state p erturbation is a transformation b etw een the fib er input and fib er output. If this transformation is stable, Alice and Bob can comp ensate for it by using a p olarization contr oller to align their systems by defining, e.g., the v ertical and diagonal p olarization direction. If the transforma- tion v aries slo wly , one can use an active feedback system to main tain alignmen t o v er time. Smart solutions are p ossible: early commercial systems used a so- called “plug and pla y” optical sc heme that cancelled p olarization perturbation without a need for activ e con trol [12]. As an alternative to fiber, a line-of-sigh t path via atmosphere can b e used as the quantum channel. Alice and Bob use small telescop es p ointed at one another to transmit photons. Av ailability and qualit y of such a link is ob viously affected b y weather conditions. Ho wev er, air neither perturbs polarization nor has a high loss. The longest transmission has b een achiev ed ov er 144 km b etw een hilltops on the Canary islands [21]; how ever links of 10–30 km may be more practical [10]. The success of these ground exp eriments suggests a p ossibilit y of distributing a secret key b et w een a ground station and a satellite. A lo w-orbit satellite can th us provide a global k ey distribution net work b y successively establishing key distribution links with places under its fligh t path. 22 5.6.4 Random Num b er Generator The key used for the one-time pad m ust b e p erfectly random. As computers are deterministic systems, they can not be used to create random num b ers for cryptographic systems. Therefore, the random n umbers must be created b y a truly random ph ysical process. One example is a single photon sent through a b eamsplitter: the photon is found in one of the t wo exits of the b eamsplitter. Whic h exit it is found at, is random according to quantum mechanics. There are certainly many other pro cesses that can b e used. While physical random num b er generators with bitrates of a few Mbit/s are emplo yed in current commercial quan tum key distribution systems, construction of high bit rate true random n um b er generators is still at an exp erimen tal stage. 22 This requires the satellite to operate as a trusted no de, as discussed later in this chapter. 11 5.7 Applications Although quan tum cryptography is quite technologically mature, and commer- cially it curren tly enjo ys a tiny nic he mark et, p ersp ectives of wider adoption are unclear. On the one hand, classical cryptographic systems based on as- sumptions on computational complexit y are very go o d and conv enient: w ell- dev elop ed, cheap, can work at high bitrates o ver unlimited distance. As w e ha v e discussed in the In tro duction of this chapter, their securit y is not guar- an teed against future adv ances in cryptanalysis (and strictly speaking not ev en guaran teed today), but their con venience is almost un b eatable. Should an y of them fall, this would not b e the first historical example when the ease of use w as preferred o ver stricter securit y [18]. On the other hand, a quantum key distribution link is limited b y distance and bitrate, and is curren tly relativ ely expensive to set up. In fact, sending a p erson (trusted courier) carrying a hard disk filled with random num b ers w ould pro vide a larger k ey supply than most quan tum key distribution links could deliv er ov er their op eration lifetime. Note that the quantum k ey distribution link also needs a short k ey for the initial authentication, so the trusted courier is inv olved an ywa y . Ho w ever, the ability to gro w k ey limitlessly from the short authen tication key mak es quan tum cryptography scale well in a net work of man y users, while in the hard disk distribution scenario the required storage capacit y w ould quic kly b ecome unrealistic [11]. 5.7.1 Commercial Systems with Dual Key Agreemen t In to da y’s commercial systems, quantum key distribution is used as an extra securit y lay er on top of classical key distribution and encryption, see Figure 5.6. Keys obtained from quantum key distribution are com bined with keys sent using public key cryptography , by encrypting one k ey using the other key as one-time pad (exclusiv e-OR binary function). The resulting com bined k ey is at least as secure as the stronger of the tw o original keys. Thus, to ea vesdrop the combined k ey , an attac k er w ould ha ve to crac k both public-k ey cryptograph y and quantum k ey distribution. This combined key is c hanged sev eral times a second, and used in a high-throughput symmetric cipher to encrypt a wideband netw ork link. Although an y symmetric cipher using k ey shorter than the encrypted mes- sage is not unconditionally secure, this architecture is dictated by the ease of in tegration into existing netw orks. Customers are used to ha ving classical cryp- tograph y that can encrypt the entire gigabit netw ork link. Nevertheless, it is argued that the securit y of the AES symmetric cipher impro ves when the key is c hanged frequen tly and th us less ciphertext is av ailable for cryptanalysis. The system has an option to additionally provide one-time-pad encryption to the users. In the commercially a v ailable units, the k ey generation sp eed and th us one-time pad av erage bandwidth is no faster than a few kbit/s, how ever lab oratory protot yp es ha ve b een demonstrated with up to 1 Mbit/s o ver 50 km fib er [4]. 5.7.2 Quan tum Key Distribution Net w orks T o increase the n umber of users and ov ercome the link distance limitation, t wo t yp es of netw orks are p ossible: with trusted no des, and with untrusted no des. 12 (a) (b) Symmetric cipher (AES 256 bit) Quantum key distribution (BB84) Public-key cryptography (RSA 2048 bit) Combined key Alice Bob Combined key Quantum key distribution to another node 3 km away Quantum key distribution to another node 17 km away Key manager W avelength-division multiplexers (passive optical devices combining quantum and classical channels into a single fiber) link-layer , 2 Gbit/s link-layer , 10 Gbit/s network-layer , 0.1 Gbit/s (virtual private network) Classical encryptors: Figure 5.6: Commercial quantum cryptograph y vintage 2010. (a) Dual key agreemen t scheme. Two secret k eys are distributed independently using quan- tum cryptography and public-k ey cryptograph y , then added mo dulo 2 (X-ored) together. The resulting k ey is used in a symmetric cipher to encrypt netw ork traffic. (b) Net work no de with quantum k ey distribution equipment, in a stan- dard 19 inch wide server rac k. Quantum k eys are generated b etw een this node and t w o other remote no des using ID Quan tique V ectis units, then passed to clas- sical equipment that encrypts all net work traffic with those remote no des. This no de was a part of SwissQuan tum testb ed net w ork in Genev a, and op erated con- tin uously for more than a year, see http://swissquantum.idquantique.com/ . 13 The trusted-node netw ork consists of p oin t-to-p oin t quan tum key distribution links b etw een no des. When tw o users wan t to establish a shared key , they find a path through in termediate no des, then one user sends his key to the other user through a c hain of one-time-pad encryptions using keys generated in each p oin t-to-p oin t link along the path. This t yp e of net work has been demonstrated in sev eral metrop olitan areas [8, 13]. The un trusted-no de net work can use optical switc hes at the no des to create an unin terrupted optical c hannel b et w een end users. This is realistic with to- da y’s technology , but the optical switc hes do not increase transmission distance and can th us only be used in a geographically compact netw ork. An alternative idea is to use so-called quantum r ep e aters at the un trusted no des, whic h in theory can increase the distance far beyond the 250 km limit. Ho wev er, quantum re- p eaters remain a future technology . The un trusted-no de netw ork configuration can realize the full potential of quantum cryptography , and perhaps provide a decisiv e adv antage ov er using trusted couriers and other k ey distribution meth- o ds. F or example, eac h user can get and store only initial authentication keys for ev ery other netw ork user, then grow more k ey material with an y user as needed. 5.8 Summary The feasibility of quan tum cryptography has no w been demonstrated o ver dis- tances up to 250 km, and in k ey distribution netw orks. Although the systems still suffer from low key transmission rates, they do provide means for secure comm unication if the public-key systems used today are not trusted. But fore- most, today quantum cryptograph y is developed with an eye tow ards a future in which crac king classical public-k ey ciphers migh t b ecome practically feasible. F or example, a quantum computer migh t one day b e able to crac k today’s co des. Quan tum cryptography is also an excellent example of the intimate interpla y b et w een fundamen tal and applied researc h. 5.9 F urther Reading and W eb Sites The w eb site http://www.iet.ntnu.no/groups/optics/qcr/ of our Quantum Hac king group presen ts ho w industrial implementations of the quantum key dis- tribution system can b e broken. The w eb site http://pqcrypto.org/ inv esti- gates what will happen to cryptology when the first w orking quantum computer has b een built. References [1] C. H. Bennett, F. Bess ette, L. Salv ail, G. Brassard, and J. Smolin. Exper- imen tal quan tum cryptography . Journal of Cryptolo gy , 5:3–28, 1992. [2] C. H. Bennett, G. Brassard, C. Cr ´ ep eau, and U. M. Maurer. Generalized priv acy amplification. IEEE T r ansactions on Information The ory , 41:1915– 1923, 1995. 14 [3] S. Cov a, M. Ghioni, A. Lotito, I. Rech, and F. Zappa. Evolution and prosp ects for single-photon a v alanche dio des and quenching circuits. Jour- nal of Mo dern Optics , 51:1267–1288, 2004. [4] A. R. Dixon, Z. L. Y uan, J. F. Dynes, A. W. Sharp e, and A. J. Shields. Con tin uous op eration of high bit rate quan tum k ey distribution. Applie d Physics L etters , 96:161102, 2010. [5] I. Gerhardt, Q. Liu, A. Lamas-Linares, J. Sk aar, C. Kurtsiefer, and V. Mak aro v. F ull-field implementation of a perfect ea v esdropp er on a quan- tum cryptograph y system. Natur e Communic ations , 2:349, 2011. [6] N. Gisin, G. Ribordy , W. Tittel, and H. Zbinden. Quan tum cryptography . R eviews of Mo dern Physics , 74:145–195, 2002. [7] R. H. Hadfield. Single-photon detectors for optical quantum information applications. Natur e Photonics , 3:696–705, 2009. [8] N. Horiuc hi. View from... UQCC 2010: Quan tum secure video. Natur e Photonics , 5:10–11, 2011. [9] W.-Y. Hwang. Quantum key distribution with high loss: T ow ard global secure comm unication. Physic al R eview L etters , 91:057901, 2003. [10] C. Kurtsiefer, P . Zarda, M. Halder, H. W einfurter, P . M. Gorman, P . R. T apster, and J. G. Rarit y . A step tow ards global k ey distribution. Natur e , 419:450, 2002. [11] L. Lydersen. Pr actic al se curity of quantum crypto gr aphy . Ph.D. thesis, Norw egian Univ ersity of Science and Tec hnology , 2011. [12] A. Muller, T. Herzog, B. Huttner, W. Tittel, H. Zbinden, and N. Gisin. “Plug and play” systems for quan tum cryptography . Applie d Physics L et- ters , 70:793–795, 1997. [13] M. Peev et al. The SECOQC quantum k ey distribution netw ork in Vienna. New Journal of Physics , 11:075001, 2009. [14] J. Preskill. Making weirdness work: Quantum information and compu- tation. In IEEE A er osp ac e Confer enc e 1998 pr o c e e dings , v olume 1, pages 37–46. 1998. [15] V. Scarani, H. Bec hmann-Pasquin ucci, N. J. Cerf, M. Du ˇ sek, N. L¨ utk enhaus, and M. Peev. The securit y of practical quan tum k ey dis- tribution. R eviews of Mo dern Physics , 81:1301–1350, 2009. [16] C. E. Shannon. Communication theory of secrecy systems. Bel l System T e chnic al Journal , 28:656–715, 1949. [17] A. J. Shields. Semiconductor quantum light sources. Natur e Photonics , 1:215–223, 2007. [18] S. Singh. The c o de b o ok . Random House, New Y ork, 1999. [19] D. Stuc ki et al. High rate, long-distance quan tum k ey distribution ov er 250 km of ultra lo w loss fibres. New Journal of Physics , 11:075003, 2009. 15 [20] W. Tittel, G. Rib ordy , and N. Gisin. Quantum cryptograph y . Physics World , 11:41–45, Marc h 1998. [21] R. Ursin et al. Entanglemen t-based quantum communication ov er 144 km. Natur e Physics , 3:481–486, 2007. [22] M. N. W egman and J. L. Carter. New hash functions and their use in authen tication and set equality . Journal of Computer and System Scienc es , 22:265–279, 1981. [23] W. K. W ootters and W. H. Zurek. A single quantum cannot b e cloned. Natur e , 299:802, 1982. 16
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment